analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
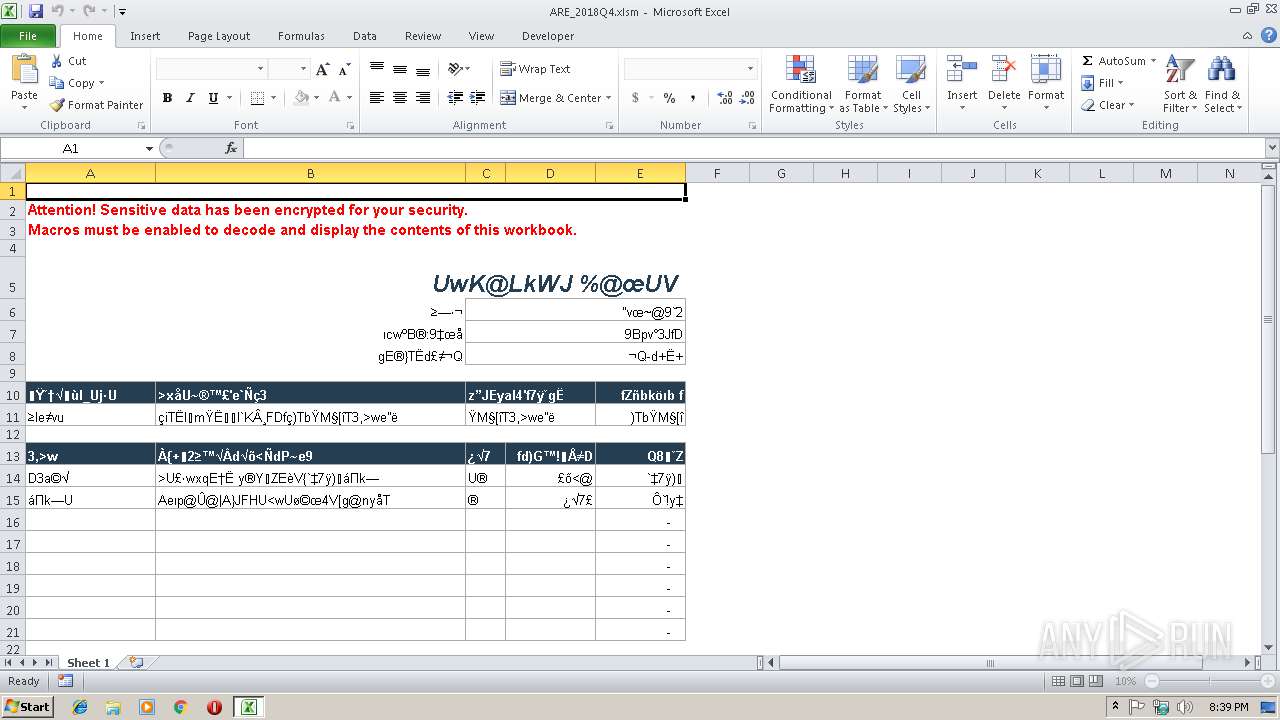
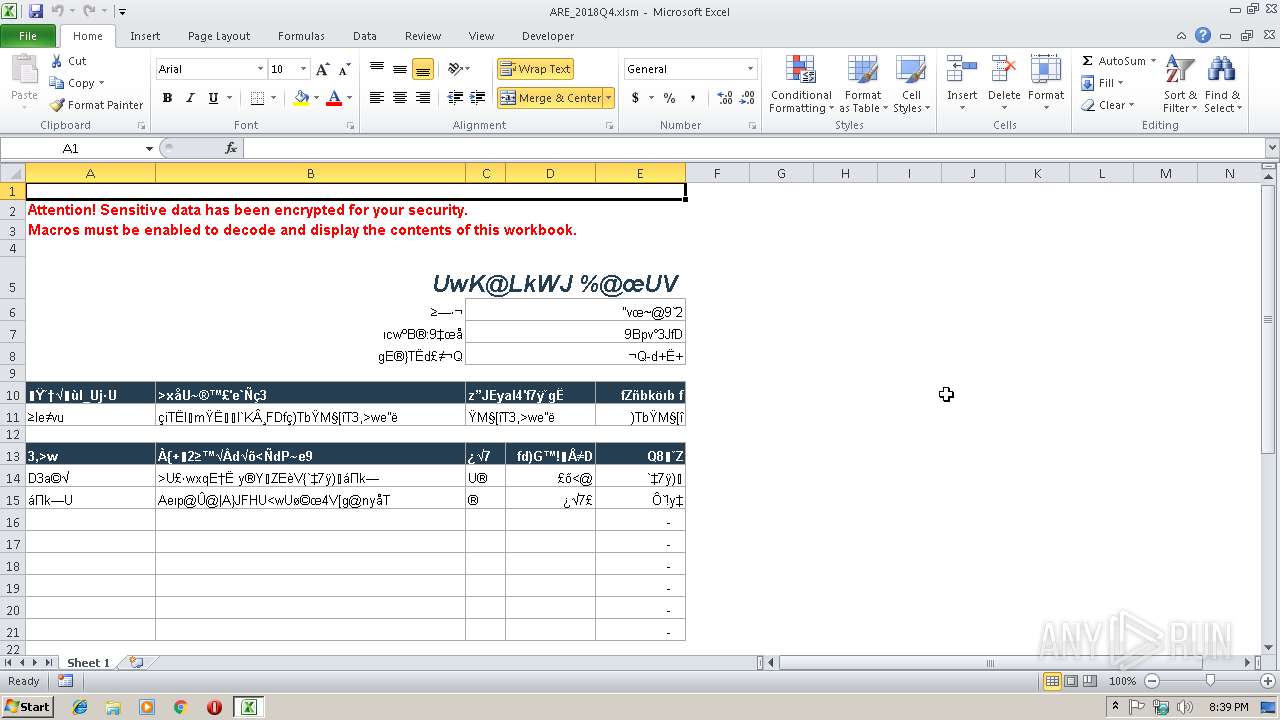
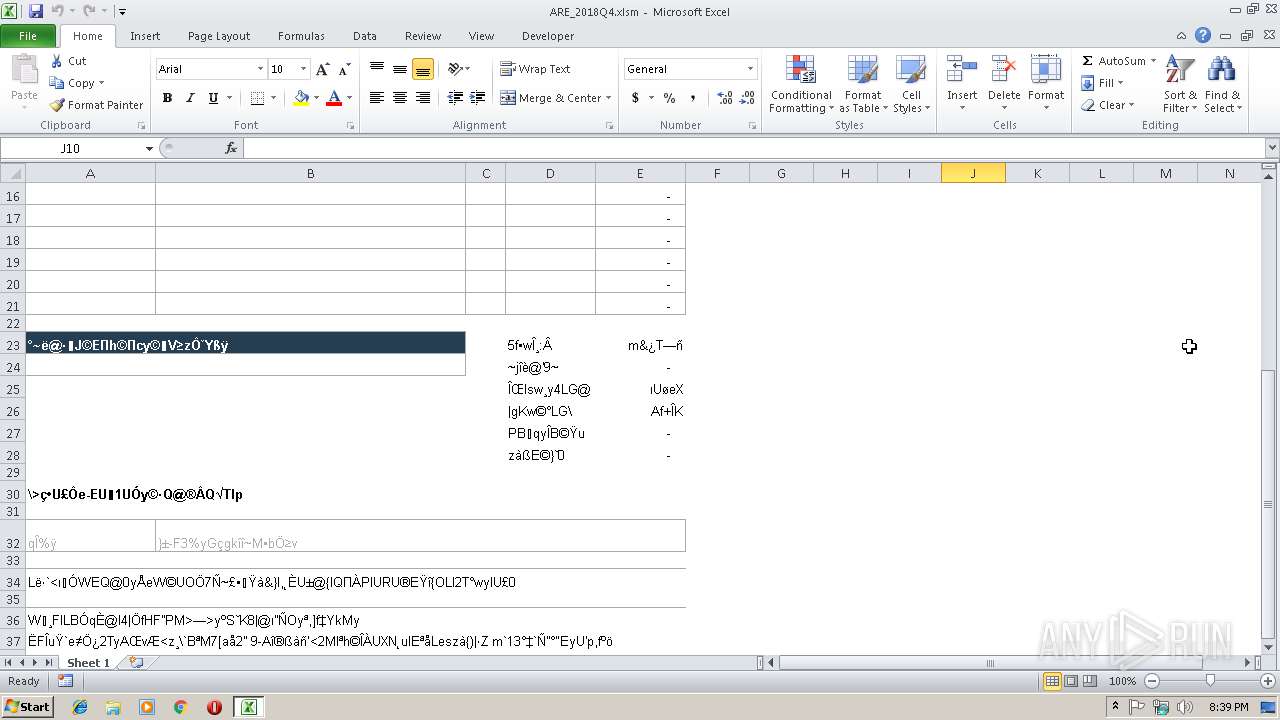
| File name: | ARE_2018Q4.xlsm |
| Full analysis: | https://app.any.run/tasks/5474dcc8-7cc4-4f24-8ddb-5839ed1629e0 |
| Verdict: | Malicious activity |
| Analysis date: | December 18, 2018, 20:38:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.spreadsheetml.sheet |
| File info: | Microsoft Excel 2007+ |
| MD5: | 9E954215D16299ACBA4CA5A735E4C446 |
| SHA1: | D5CAD9A28BA44DD6F29282E852ED737CDF810526 |
| SHA256: | 6388157C1ECA72254B2B2AF0B3F0B54B813C75D2B6CD1D815C82A501C0170277 |
| SSDEEP: | 384:4w/waEQ/HdfTW9ZiiI4+dh/D/CF4MMlTYlLITGY8ySAXelHdIZJC8RRwM:DvEQfdfekI+vjC2MM9mcGcSAXeUZJoM |
MALICIOUS
No malicious indicators.SUSPICIOUS
Unusual connect from Microsoft Office
- EXCEL.EXE (PID: 2952)
Reads Internet Cache Settings
- EXCEL.EXE (PID: 2952)
Reads internet explorer settings
- EXCEL.EXE (PID: 2952)
INFO
Changes internet zones settings
- iexplore.exe (PID: 4028)
Reads Internet Cache Settings
- iexplore.exe (PID: 2232)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2952)
Application launched itself
- iexplore.exe (PID: 4028)
Reads internet explorer settings
- iexplore.exe (PID: 2232)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xlam | | | Excel Macro-enabled Open XML add-in (42.4) |
|---|---|---|
| .xlsm | | | Excel Microsoft Office Open XML Format document (with Macro) (29.2) |
| .xlsx | | | Excel Microsoft Office Open XML Format document (17.3) |
| .zip | | | Open Packaging Conventions container (8.9) |
| .zip | | | ZIP compressed archive (2) |
EXIF
XMP
| Creator: | - |
|---|---|
| Title: | - |
XML
| ModifyDate: | 2016:12:15 17:05:11Z |
|---|---|
| CreateDate: | 2016:09:02 14:01:03Z |
| LastModifiedBy: | - |
| AppVersion: | 16.03 |
| HyperlinksChanged: | No |
| SharedDoc: | No |
| LinksUpToDate: | No |
| TitlesOfParts: |
|
| HeadingPairs: |
|
| ScaleCrop: | No |
| DocSecurity: | None |
| Application: | Microsoft Excel |
ZIP
| ZipFileName: | [Content_Types].xml |
|---|---|
| ZipUncompressedSize: | 1490 |
| ZipCompressedSize: | 394 |
| ZipCRC: | 0xc4b9cb2a |
| ZipModifyDate: | 2018:12:13 17:41:00 |
| ZipCompression: | Deflated |
| ZipBitFlag: | - |
| ZipRequiredVersion: | 20 |
Total processes
34
Monitored processes
3
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 2952 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | explorer.exe | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Version: 14.0.6024.1000 | ||||
| 4028 | "C:\Program Files\Internet Explorer\iexplore.exe" -Embedding | C:\Program Files\Internet Explorer\iexplore.exe | svchost.exe | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) | ||||
| 2232 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:4028 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | |
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) | ||||
Total events
1 027
Read events
934
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
2
Text files
14
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2952 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR69E6.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 4028 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 4028 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2952 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~DF888C50FB30B050AA.TMP | — | |
MD5:— | SHA256:— | |||
| 4028 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF7E26630DCF6D562E.TMP | — | |
MD5:— | SHA256:— | |||
| 2232 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\DOMStore\index.dat | dat | |
MD5:218A28022FA3B688165236E12A2C3356 | SHA256:4AFD7651592B2B3F95BE45C1556BCE120AD5F2BCCA6F989754650123CF414C5B | |||
| 4028 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF8D1FEA98D00745C2.TMP | — | |
MD5:— | SHA256:— | |||
| 2232 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\PP6KS563\js[1] | text | |
MD5:B7E6CC64FF3EB5D5A00FB0D877A24DDE | SHA256:909B2553E991DD98EAF88BB13F2B0CD4FA5EEB6DC4B5E969C236DDFD19F5EC5F | |||
| 2232 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\U2ZG9DE0\annotated_email[1].jpg | image | |
MD5:D81EBE4A093F2B7EE60046B277608D2D | SHA256:BA67A8464290F9A3A5D9AA845DFCB784412BE4C55E720964D2FE59799E84C91A | |||
| 2952 | EXCEL.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\88edd556-069d-4285-90d7-bad0971e9cc2[1].txt | html | |
MD5:A8DB70C7C9AF6F04CA7F2B0033DC143F | SHA256:9CDC180B2A40E7DB92FD881E38E686EA5F18FFC8C3BBDB8B52D72EA19C1C1C3A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
14
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2232 | iexplore.exe | GET | 404 | 54.146.151.112:80 | http://training.phishme.com/fonts/shared_landing/vodafonerg-webfont.woff)%20format(%22woff%22 | US | — | — | suspicious |
2232 | iexplore.exe | GET | 404 | 54.146.151.112:80 | http://training.phishme.com/fonts/shared_landing/vodafonergbd-webfont.woff)%20format(%22woff%22 | US | — | — | suspicious |
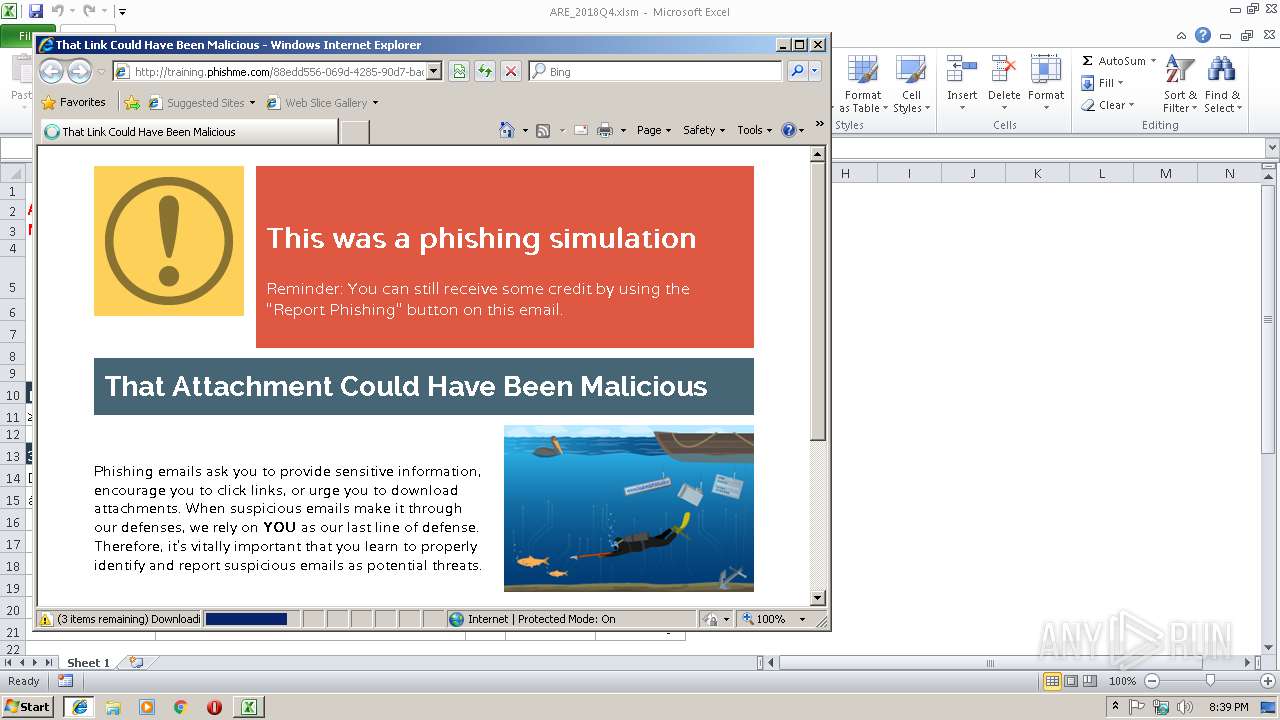
2952 | EXCEL.EXE | GET | 200 | 54.146.151.112:80 | http://training.phishme.com/88edd556-069d-4285-90d7-bad0971e9cc2 | US | html | 12.2 Kb | suspicious |
4028 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2232 | iexplore.exe | GET | 404 | 54.146.151.112:80 | http://training.phishme.com/shared_landing/fonts/MS-UIGothic.ttf)%20format(%22truetype%22 | US | — | — | suspicious |
4028 | iexplore.exe | GET | 404 | 54.146.151.112:80 | http://training.phishme.com/favicon.ico | US | — | — | suspicious |
2232 | iexplore.exe | GET | 200 | 54.146.151.112:80 | http://training.phishme.com/log_info?_=1545165565175&tid=88edd556-069d-4285-90d7-bad0971e9cc2 | US | — | — | suspicious |
2232 | iexplore.exe | GET | 200 | 54.146.151.112:80 | http://training.phishme.com/shared_landing/fonts/Raleway-Bold-webfont.eot? | US | eot | 26.5 Kb | suspicious |
2232 | iexplore.exe | GET | 200 | 54.146.151.112:80 | http://training.phishme.com/shared_landing/fonts/Montserrat-Bold-webfont.eot? | US | eot | 21.1 Kb | suspicious |
2232 | iexplore.exe | GET | 200 | 54.146.151.112:80 | http://training.phishme.com/log_info?_=1545165555018&tid=88edd556-069d-4285-90d7-bad0971e9cc2 | US | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4028 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2952 | EXCEL.EXE | 54.146.151.112:80 | training.phishme.com | Amazon.com, Inc. | US | unknown |
2232 | iexplore.exe | 54.146.151.112:80 | training.phishme.com | Amazon.com, Inc. | US | unknown |
2232 | iexplore.exe | 172.217.18.168:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
2232 | iexplore.exe | 54.230.95.17:80 | images.pmeimg.com | Amazon.com, Inc. | US | unknown |
4028 | iexplore.exe | 54.146.151.112:80 | training.phishme.com | Amazon.com, Inc. | US | unknown |
2232 | iexplore.exe | 151.101.2.110:443 | js-agent.newrelic.com | Fastly | US | suspicious |
2232 | iexplore.exe | 162.247.242.19:443 | bam.nr-data.net | New Relic | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
training.phishme.com |
| suspicious |
www.bing.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
images.pmeimg.com |
| shared |
js-agent.newrelic.com |
| whitelisted |
bam.nr-data.net |
| whitelisted |