| download: | NewActive.exe |
| Full analysis: | https://app.any.run/tasks/18e20aa3-3de7-4315-8531-cf96c8d37a33 |
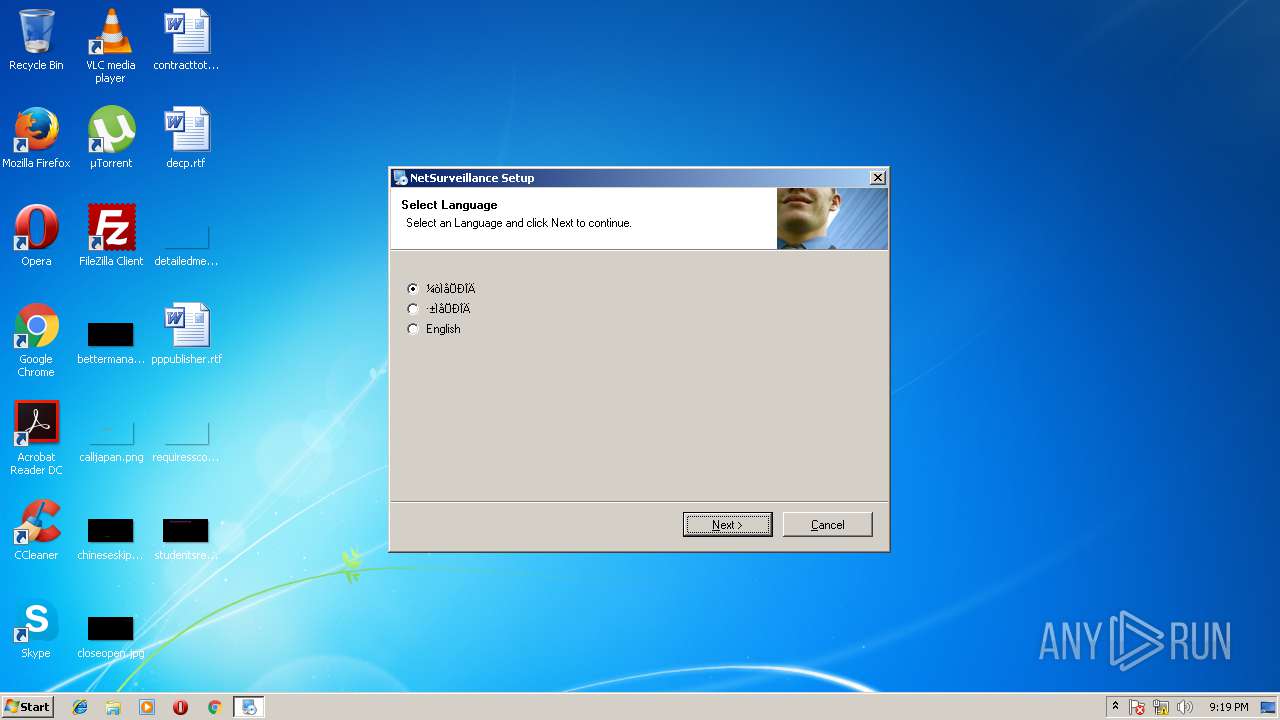
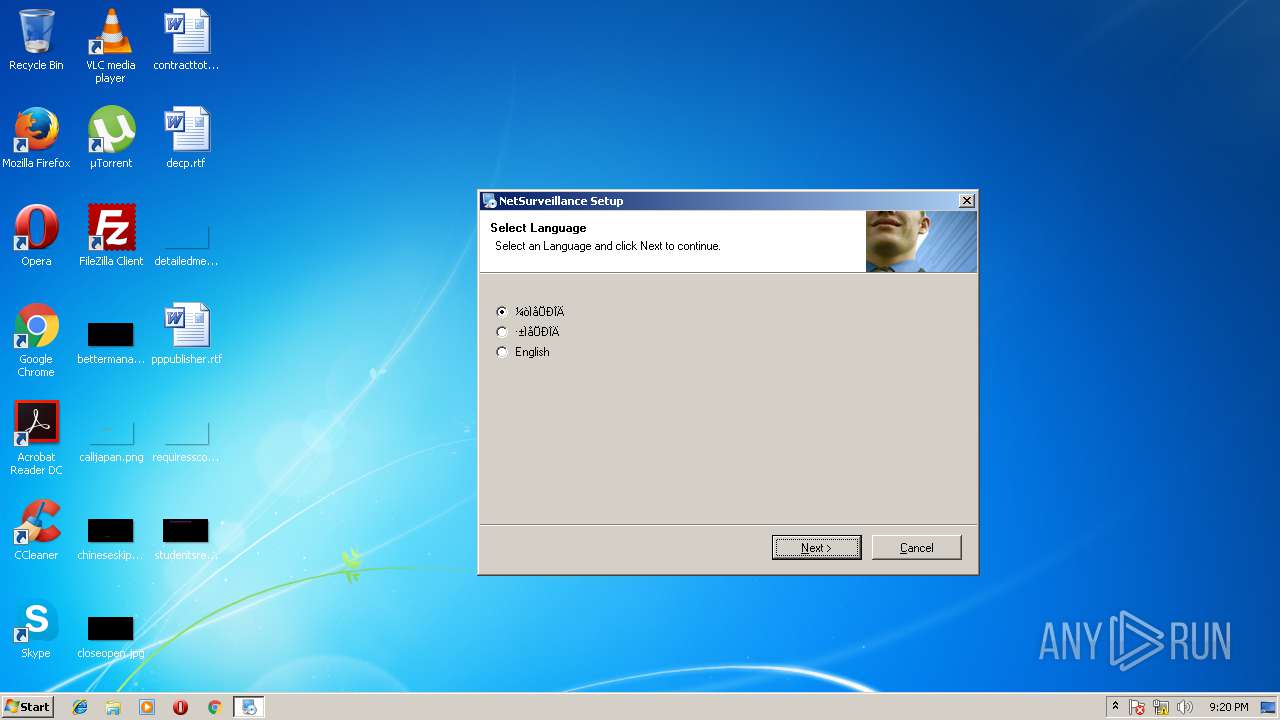
| Verdict: | Malicious activity |
| Analysis date: | June 07, 2018, 20:19:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 088C81181A70CEBE8152FD5DEC3FC0F0 |
| SHA1: | 27B3C97D077D7A681C883E34AAD010C45D28E2FF |
| SHA256: | 637864B8060F8C8ACDBEE10AC3AC616BFF23129C6DEB82B116A51C0E8973E0AE |
| SSDEEP: | 49152:wl8eOf6vOOzque2/5q8W41ionBl1ngK8ZGUyFSZrs4NkQKjdn1GF/4WnQ:wZPOOteYM41X2K80UsEsektjJ0/4g |
MALICIOUS
Application was dropped or rewritten from another process
- irsetup.exe (PID: 184)
Registers / Runs the DLL via REGSVR32.EXE
- irsetup.exe (PID: 184)
Loads dropped or rewritten executable
- regsvr32.exe (PID: 3220)
SUSPICIOUS
Creates files in the Windows directory
- irsetup.exe (PID: 184)
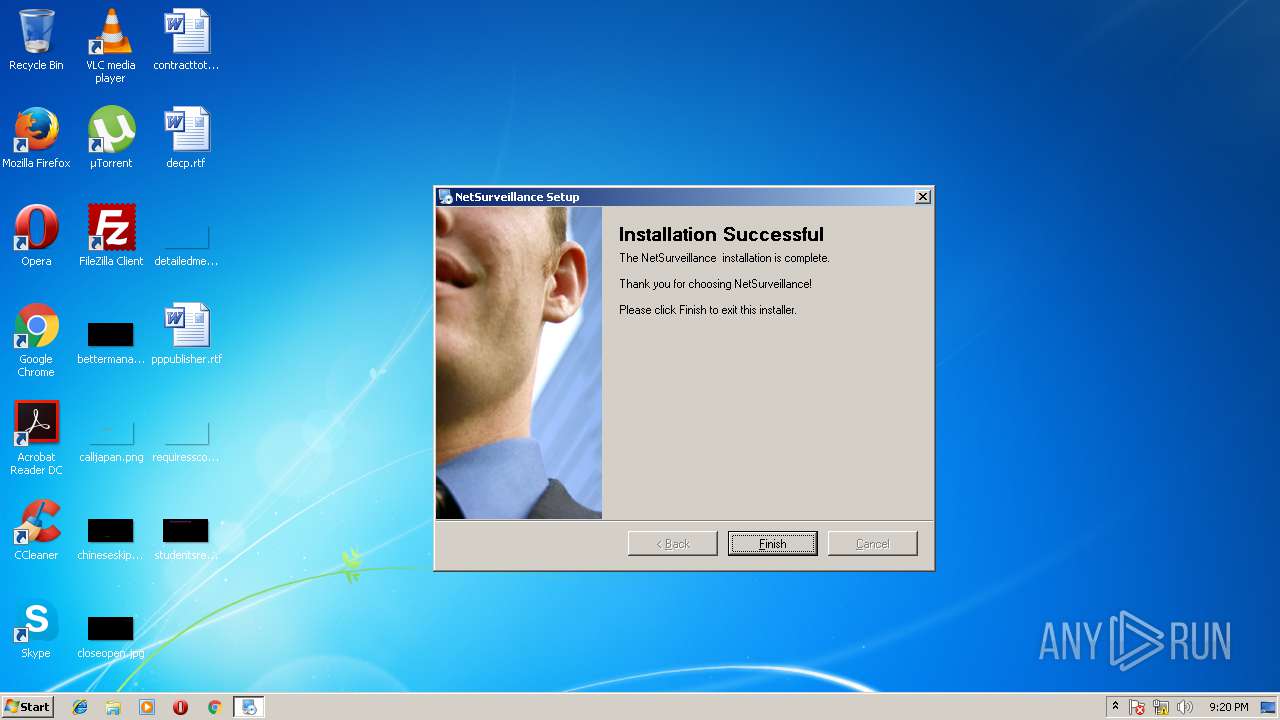
Creates a software uninstall entry
- irsetup.exe (PID: 184)
Executable content was dropped or overwritten
- NewActive.exe (PID: 3680)
- irsetup.exe (PID: 184)
Starts CMD.EXE for commands execution
- irsetup.exe (PID: 184)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3796)
Removes files from Windows directory
- irsetup.exe (PID: 184)
Creates files in the program directory
- irsetup.exe (PID: 184)
INFO
Dropped object may contain URL's
- irsetup.exe (PID: 184)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .ax | | | DirectShow filter (37.8) |
|---|---|---|
| .ocx | | | Windows ActiveX control (21.8) |
| .exe | | | Win32 EXE PECompact compressed (v2.x) (11) |
| .exe | | | Win32 EXE PECompact compressed (generic) (7.8) |
| .exe | | | Win32 Executable MS Visual C++ (generic) (5.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2004:10:13 17:10:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 20480 |
| InitializedDataSize: | 49152 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1d9d |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 7.0.1.0 |
| ProductVersionNumber: | 7.0.1.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Private build |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| Comments: | Created with Setup Factory 7.0 |
| CompanyName: | - |
| FileDescription: | Setup Application |
| FileVersion: | 7.0.1.0 |
| InternalName: | suf70_launch |
| LegalCopyright: | Setup Engine Copyright © 2004 Indigo Rose Corporation |
| LegalTrademarks: | Setup Factory is a trademark of Indigo Rose Corporation. |
| OriginalFileName: | suf70_launch.exe |
| PrivateBuild: | - |
| ProductName: | Setup Factory 7.0 Runtime |
| ProductVersion: | 7.0.1.0 |
| SpecialBuild: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 13-Oct-2004 15:10:17 |
| Detected languages: |
|
| Comments: | Created with Setup Factory 7.0 |
| CompanyName: | - |
| FileDescription: | Setup Application |
| FileVersion: | 7.0.1.0 |
| InternalName: | suf70_launch |
| LegalCopyright: | Setup Engine Copyright © 2004 Indigo Rose Corporation |
| LegalTrademarks: | Setup Factory is a trademark of Indigo Rose Corporation. |
| OriginalFilename: | suf70_launch.exe |
| PrivateBuild: | - |
| ProductName: | Setup Factory 7.0 Runtime |
| ProductVersion: | 7.0.1.0 |
| SpecialBuild: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 13-Oct-2004 15:10:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000489A | 0x00005000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.285 |
.rdata | 0x00006000 | 0x00000D64 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.71217 |
.data | 0x00007000 | 0x00003300 | 0x00003000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.02244 |
.rsrc | 0x0000B000 | 0x00006930 | 0x00007000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.41148 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.39248 | 1100 | UNKNOWN | English - United States | RT_VERSION |
2 | 4.31421 | 1384 | UNKNOWN | English - United States | RT_ICON |
3 | 5.9477 | 1128 | UNKNOWN | English - United States | RT_ICON |
4 | 3.78233 | 744 | UNKNOWN | English - United States | RT_ICON |
5 | 6.14953 | 2216 | UNKNOWN | English - United States | RT_ICON |
6 | 5.83714 | 4264 | UNKNOWN | English - United States | RT_ICON |
7 | 3.64397 | 1640 | UNKNOWN | English - United States | RT_ICON |
8 | 5.84115 | 3752 | UNKNOWN | English - United States | RT_ICON |
9 | 5.41049 | 9640 | UNKNOWN | English - United States | RT_ICON |
101 | 2.89097 | 132 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
KERNEL32.dll |
USER32.dll |
Total processes
43
Monitored processes
9
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
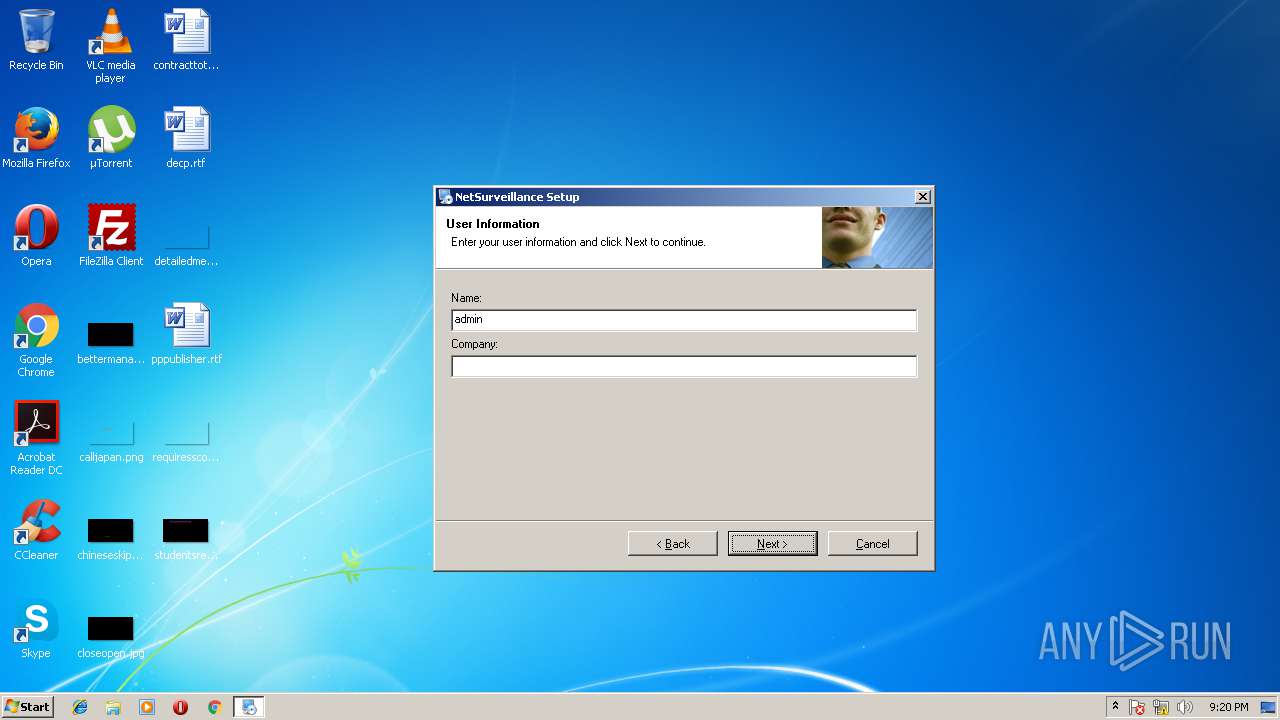
| 184 | __IRAOFF:520716 "__IRAFN:C:\Users\admin\AppData\Local\Temp\NewActive.exe" | C:\Users\admin\AppData\Local\Temp\_ir_sf7_temp_0\irsetup.exe | NewActive.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup Application Exit code: 0 Version: 7.0.1.0 Modules
| |||||||||||||||
| 2828 | reg add "HKEY_LOCAL_MACHINE\SOFTWARE\MozillaPlugins\JFWeb" /v Path /t REG_SZ /d "C:\Program Files\NetSurveillance\CMS\npWebPlugin.dll" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2872 | reg add "HKEY_LOCAL_MACHINE\SOFTWARE\MozillaPlugins\JFGuide" /v Path /t REG_SZ /d "C:\Program Files\NetSurveillance\CMS\npGuide.dll" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3032 | reg add "HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\MozillaPlugins\JFWeb" /v Path /t REG_SZ /d "C:\Program Files\NetSurveillance\CMS\npWebPlugin.dll" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3220 | "C:\Windows\System32\regsvr32.exe" /s "C:\Program Files\NetSurveillance\CMS\web.ocx" | C:\Windows\System32\regsvr32.exe | — | irsetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3680 | "C:\Users\admin\AppData\Local\Temp\NewActive.exe" | C:\Users\admin\AppData\Local\Temp\NewActive.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup Application Exit code: 0 Version: 7.0.1.0 Modules
| |||||||||||||||
| 3796 | cmd /c ""C:\Program Files\NetSurveillance\CMS\reg.bat" " | C:\Windows\system32\cmd.exe | — | irsetup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3896 | "C:\Users\admin\AppData\Local\Temp\NewActive.exe" | C:\Users\admin\AppData\Local\Temp\NewActive.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup Application Exit code: 3221226540 Version: 7.0.1.0 Modules
| |||||||||||||||
| 4028 | reg add "HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\MozillaPlugins\JFGuide" /v Path /t REG_SZ /d "C:\Program Files\NetSurveillance\CMS\npGuide.dll" /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
246
Read events
202
Write events
44
Delete events
0
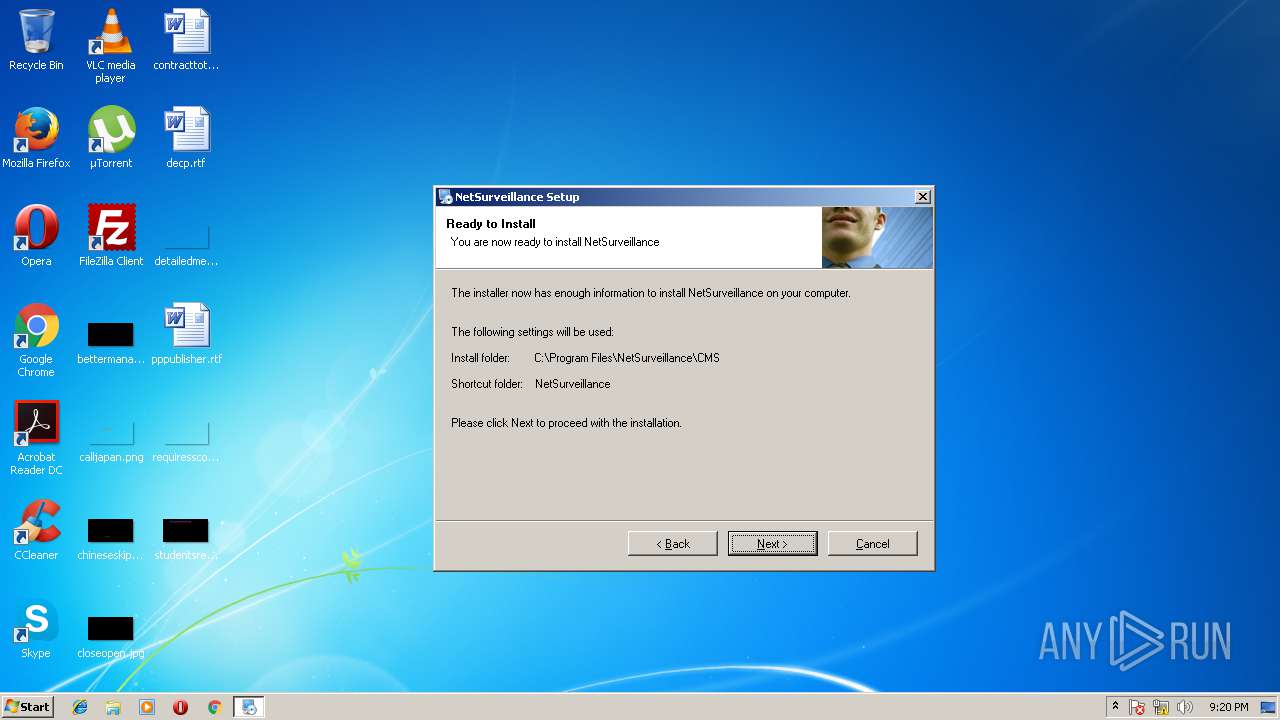
Modification events
| (PID) Process: | (184) irsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NetSurveillance |
| Operation: | write | Name: | DisplayName |
Value: NetSurveillance | |||
| (PID) Process: | (184) irsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NetSurveillance |
| Operation: | write | Name: | NoModify |
Value: 1 | |||
| (PID) Process: | (184) irsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NetSurveillance |
| Operation: | write | Name: | NoRepair |
Value: 1 | |||
| (PID) Process: | (184) irsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NetSurveillance |
| Operation: | write | Name: | UninstallString |
Value: "C:\Windows\NetSurveillance\uninstall.exe" "/U:C:\Windows\NetSurveillance\Uninstall\uninstall.xml" | |||
| (PID) Process: | (184) irsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NetSurveillance |
| Operation: | write | Name: | Contact |
Value: Ö§³Ö²¿ÃÅ | |||
| (PID) Process: | (184) irsetup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NetSurveillance |
| Operation: | write | Name: | DisplayIcon |
Value: "C:\Windows\NetSurveillance\uninstall.exe" | |||
| (PID) Process: | (184) irsetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (184) irsetup.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2872) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\MozillaPlugins\JFGuide |
| Operation: | write | Name: | Path |
Value: C:\Program Files\NetSurveillance\CMS\npGuide.dll | |||
| (PID) Process: | (3032) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\MozillaPlugins\JFWeb |
| Operation: | write | Name: | Path |
Value: C:\Program Files\NetSurveillance\CMS\npWebPlugin.dll | |||
Executable files
12
Suspicious files
2
Text files
54
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 184 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf7_temp_0\irsetup.dat | — | |
MD5:— | SHA256:— | |||
| 184 | irsetup.exe | C:\Windows\NetSurveillance\Uninstall\uni4506.tmp | — | |
MD5:— | SHA256:— | |||
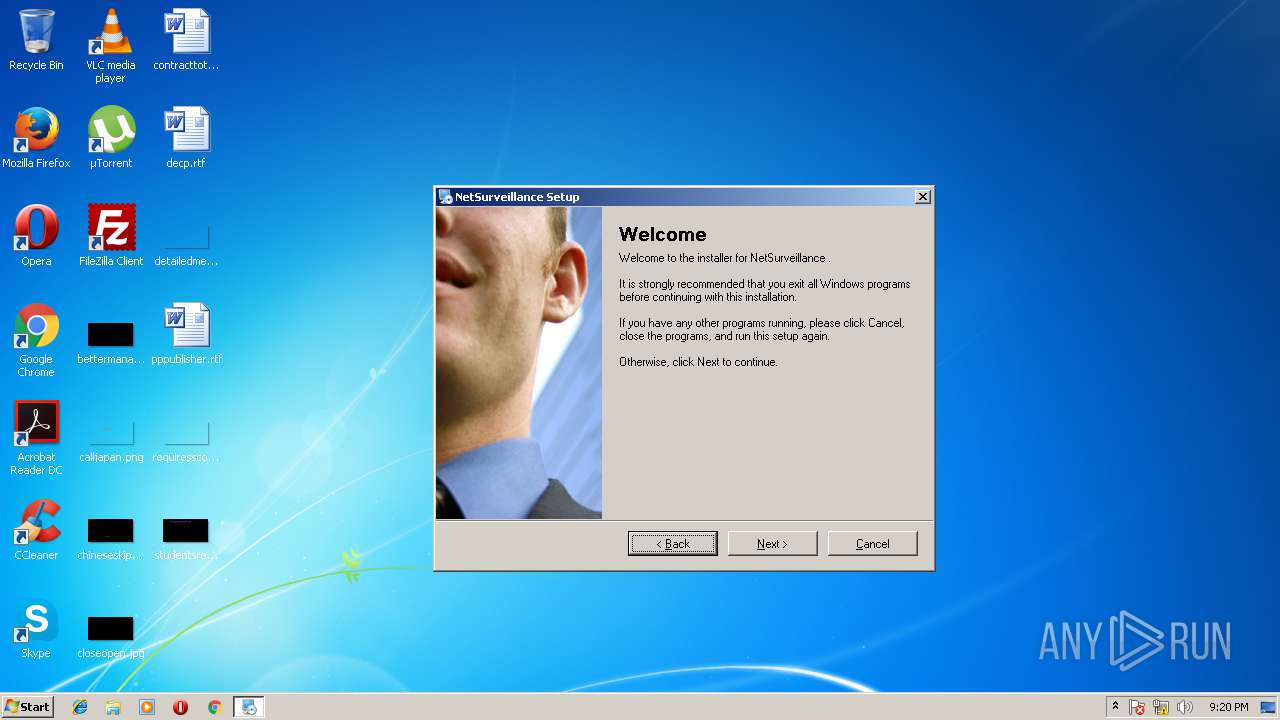
| 184 | irsetup.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf7_temp_0\IRIMG2.JPG | image | |
MD5:8D774F6D54492A39B8C10832BDFE44FA | SHA256:F68D37B790E727228A0846996024F7624CDDD463730CD087123A4BD9B3ED4389 | |||
| 184 | irsetup.exe | C:\Windows\NetSurveillance\Uninstall\uninstall.xml | text | |
MD5:84C48D7985B781D3784A4319FE34F04A | SHA256:FA6A97EDB7C2C20E82220F05EDEE434FA6A96EDAC0C7347454B7A6004C38A26E | |||
| 184 | irsetup.exe | C:\Program Files\NetSurveillance\CMS\dlg_right.bmp | image | |
MD5:43D2127525BDF1D889FB3446AB89C08C | SHA256:BFE6B2D6E7A25E8CA44A09476CCDFAC4AA87EC77D88CC39CE0FC2B389AA601C2 | |||
| 184 | irsetup.exe | C:\Program Files\NetSurveillance\CMS\mp_channel.JPG | image | |
MD5:0C47ED6CD47314B14314E876DC08DE0A | SHA256:2F6ED1882504D41908EF5E4106A392257010F24D2094D534457E5FA4C3A967D5 | |||
| 3680 | NewActive.exe | C:\Users\admin\AppData\Local\Temp\_ir_sf7_temp_0\irsetup.exe | executable | |
MD5:75CA7FF96BF5A316C3AF2DE6A412BD54 | SHA256:D95B5BF9CA97C1900DE5357743282BAB655D61D616606485088E1708559B7CF1 | |||
| 184 | irsetup.exe | C:\Program Files\NetSurveillance\CMS\plcb_over.JPG | image | |
MD5:FF5409B442314FA1A1DE9E9AE3D033E9 | SHA256:1E619B317E95BA0A737F5CCD01486E1DB54AA74F4E19679AA302E3D4F27BC694 | |||
| 184 | irsetup.exe | C:\Program Files\NetSurveillance\CMS\AlarmEnable.xml | text | |
MD5:27724336CB11023E70593C3AC145171F | SHA256:93D425EBFF335617F0BD4C2EF3DE3979B518E181DD19DE8CD9960D2BC9EBE50A | |||
| 184 | irsetup.exe | C:\Program Files\NetSurveillance\CMS\mp_thumb_active.JPG | image | |
MD5:9FC2D933E2DAAB1C5D5478E22C34B1B4 | SHA256:9500F7D8B4AEFB27CFACB9F44E56A14B1D73BFFBBA0F7E2787CD91C035EB45CC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report