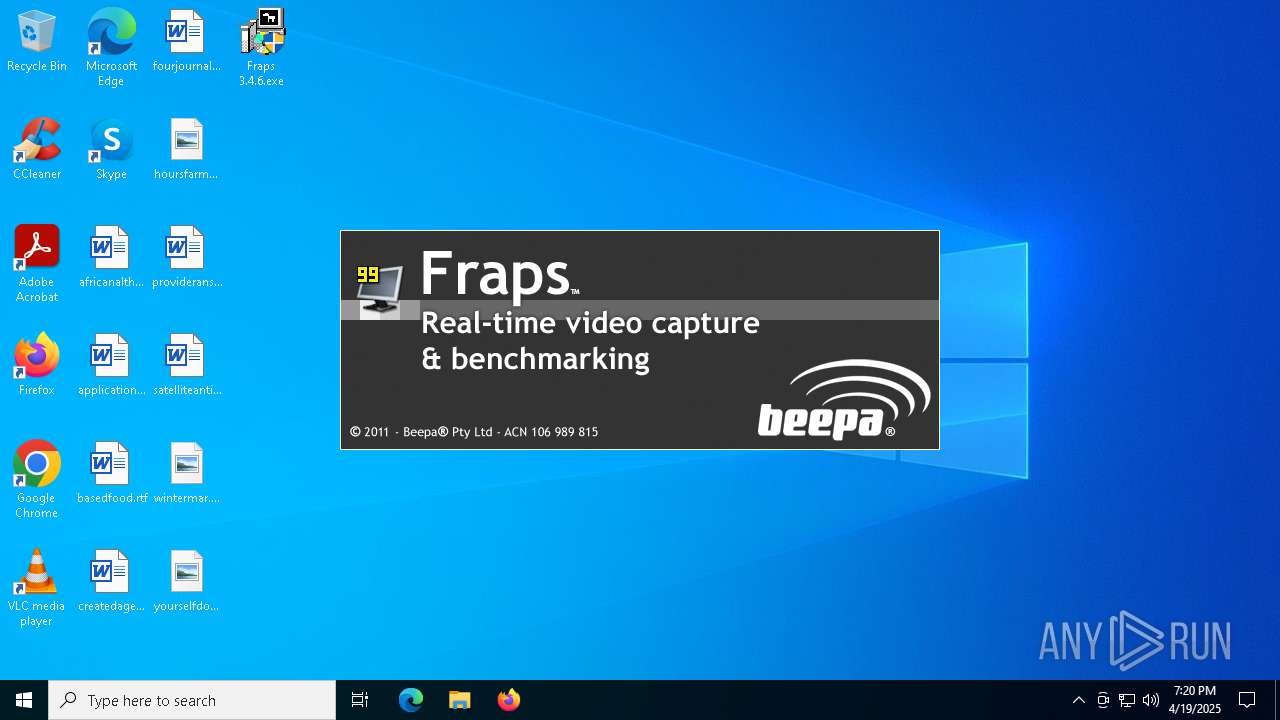
| File name: | Fraps 3.4.6.exe |
| Full analysis: | https://app.any.run/tasks/280de1f5-9d41-477e-872f-ef24f2699fec |
| Verdict: | Malicious activity |
| Analysis date: | April 19, 2025, 19:20:46 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | 4E5DFBB8D05A5A45D6FD365679FD6D09 |
| SHA1: | 2FBF34C8DFC90A32DDD3B36CED7BDF273B395375 |
| SHA256: | 6373E2B1AB55463CDEAF6BD07C69DA1D8B9810A2A927CC7A2D62247D44C21C01 |
| SSDEEP: | 98304:IZlskseN/ODHcJqgfAiwF59AKBDXDGDMZJgmmD6pY6r9s2qu5RAdaNQyxfEniN1S:ZhZAEjs8GBNMC |
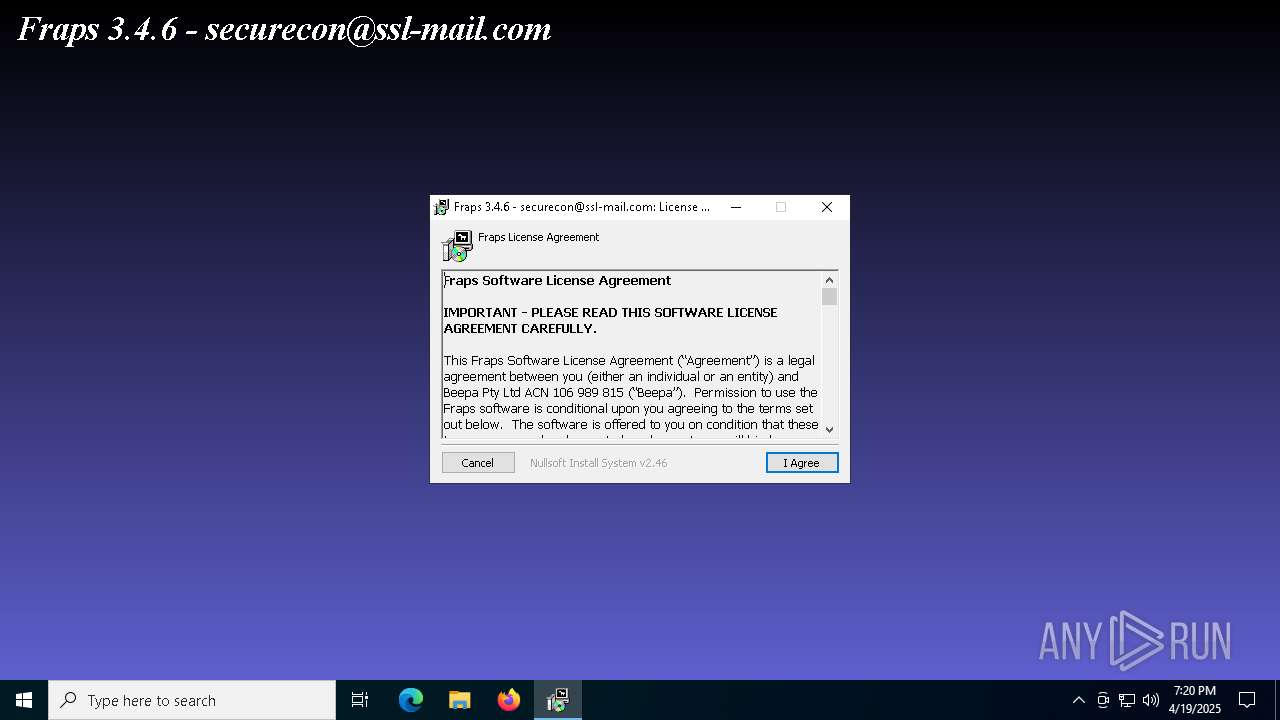
MALICIOUS
Executing a file with an untrusted certificate
- Fraps 3.4.6.exe (PID: 5576)
- Fraps 3.4.6.exe (PID: 6516)
- fraps.exe (PID: 7644)
- fraps.exe (PID: 8124)
- fraps.exe (PID: 8172)
SUSPICIOUS
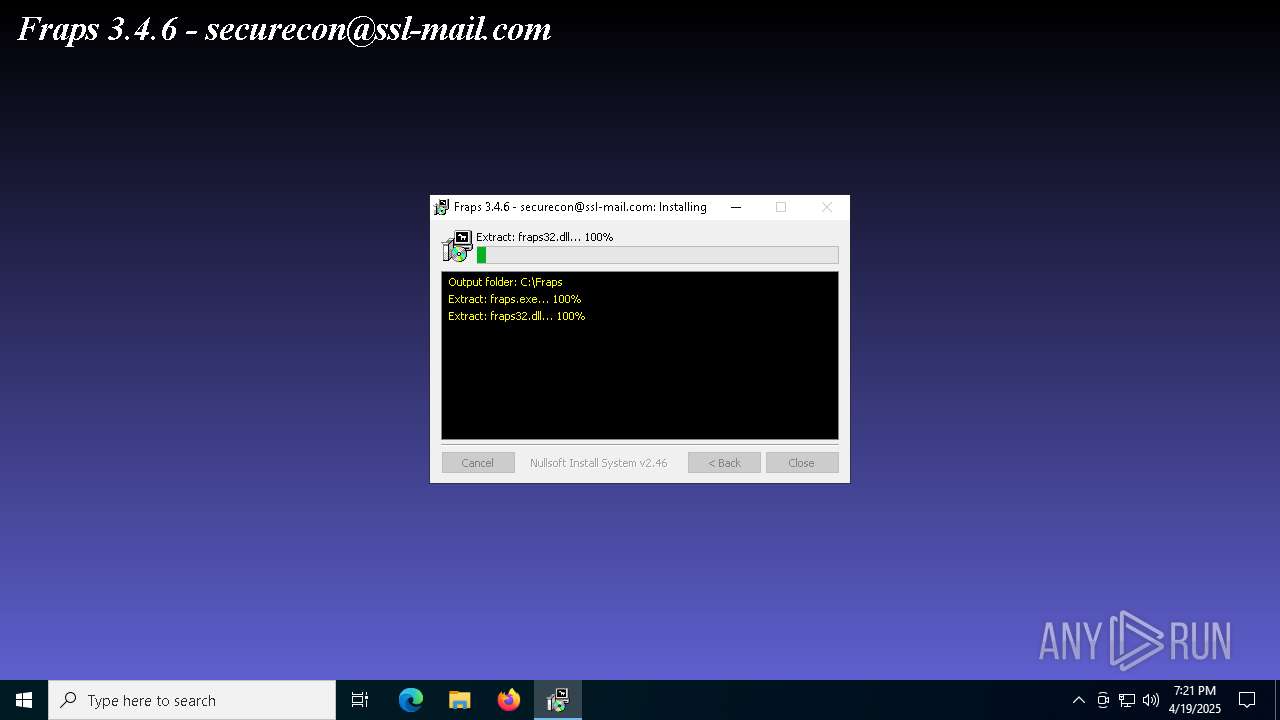
Executable content was dropped or overwritten
- Fraps 3.4.6.exe (PID: 6516)
There is functionality for taking screenshot (YARA)
- Fraps 3.4.6.exe (PID: 6516)
- fraps.exe (PID: 8172)
The process creates files with name similar to system file names
- Fraps 3.4.6.exe (PID: 6516)
Malware-specific behavior (creating "System.dll" in Temp)
- Fraps 3.4.6.exe (PID: 6516)
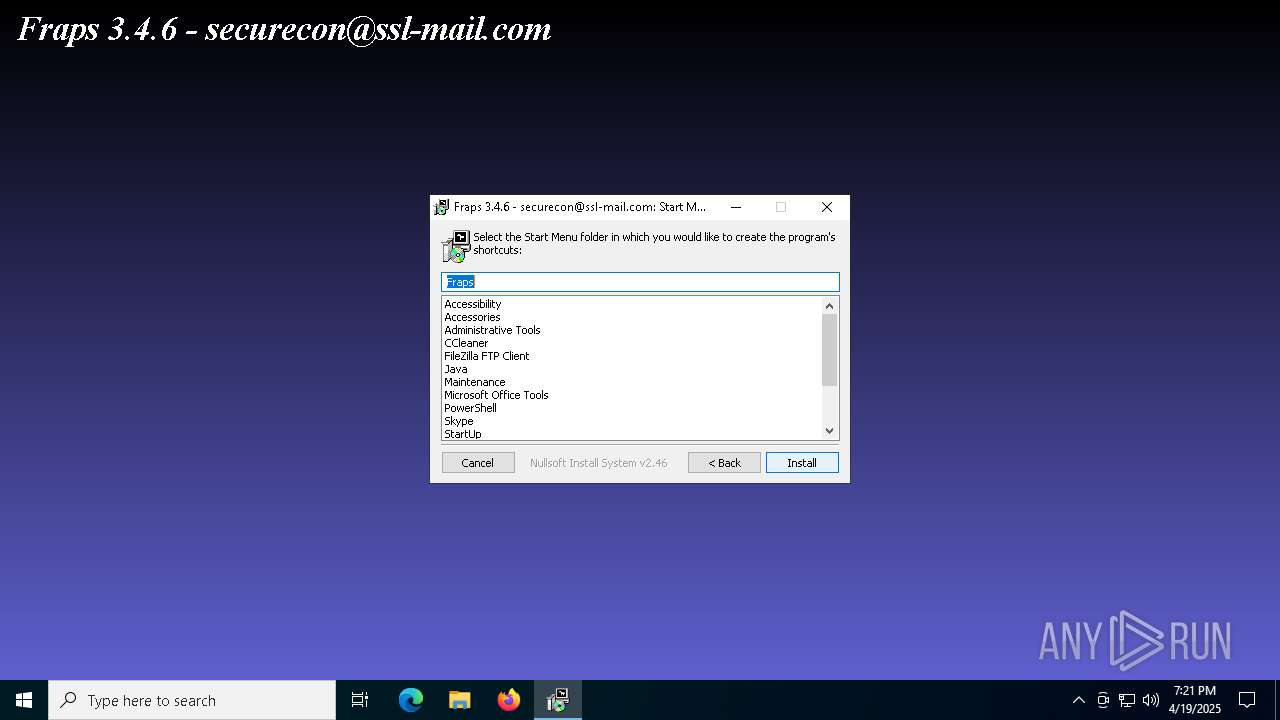
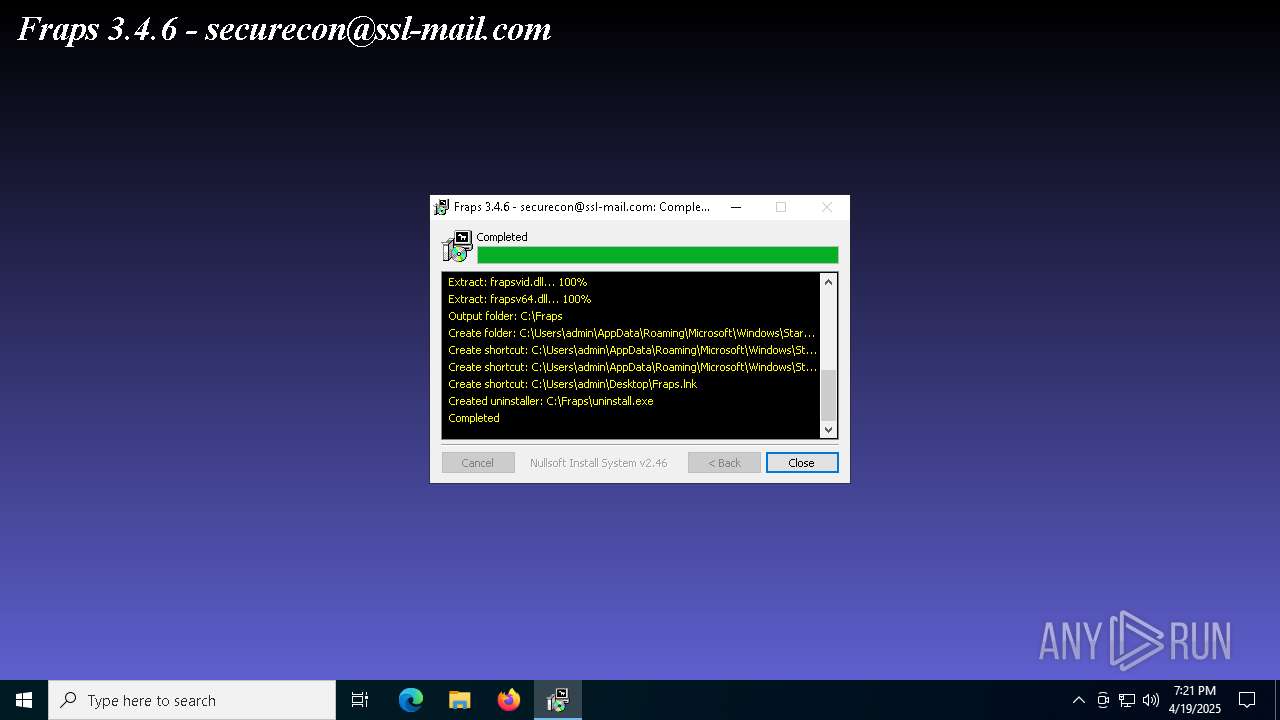
Creates a software uninstall entry
- Fraps 3.4.6.exe (PID: 6516)
Searches for installed software
- fraps.exe (PID: 8172)
Starts application with an unusual extension
- fraps.exe (PID: 8172)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 4132)
INFO
Checks supported languages
- Fraps 3.4.6.exe (PID: 6516)
- fraps.exe (PID: 7644)
- fraps.exe (PID: 8172)
- fraps64.dat (PID: 4108)
- PLUGScheduler.exe (PID: 4132)
The sample compiled with english language support
- Fraps 3.4.6.exe (PID: 6516)
Create files in a temporary directory
- Fraps 3.4.6.exe (PID: 6516)
Reads the computer name
- Fraps 3.4.6.exe (PID: 6516)
- fraps.exe (PID: 8172)
- fraps64.dat (PID: 4108)
- PLUGScheduler.exe (PID: 4132)
Creates files or folders in the user directory
- Fraps 3.4.6.exe (PID: 6516)
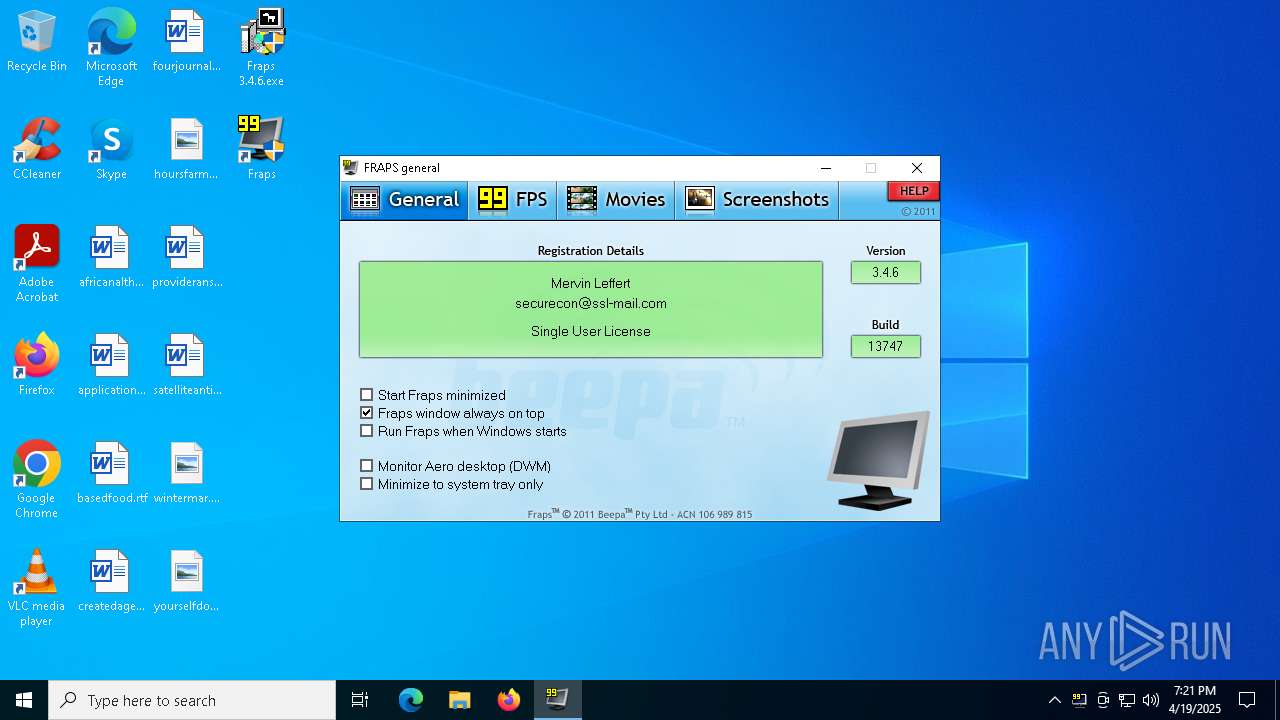
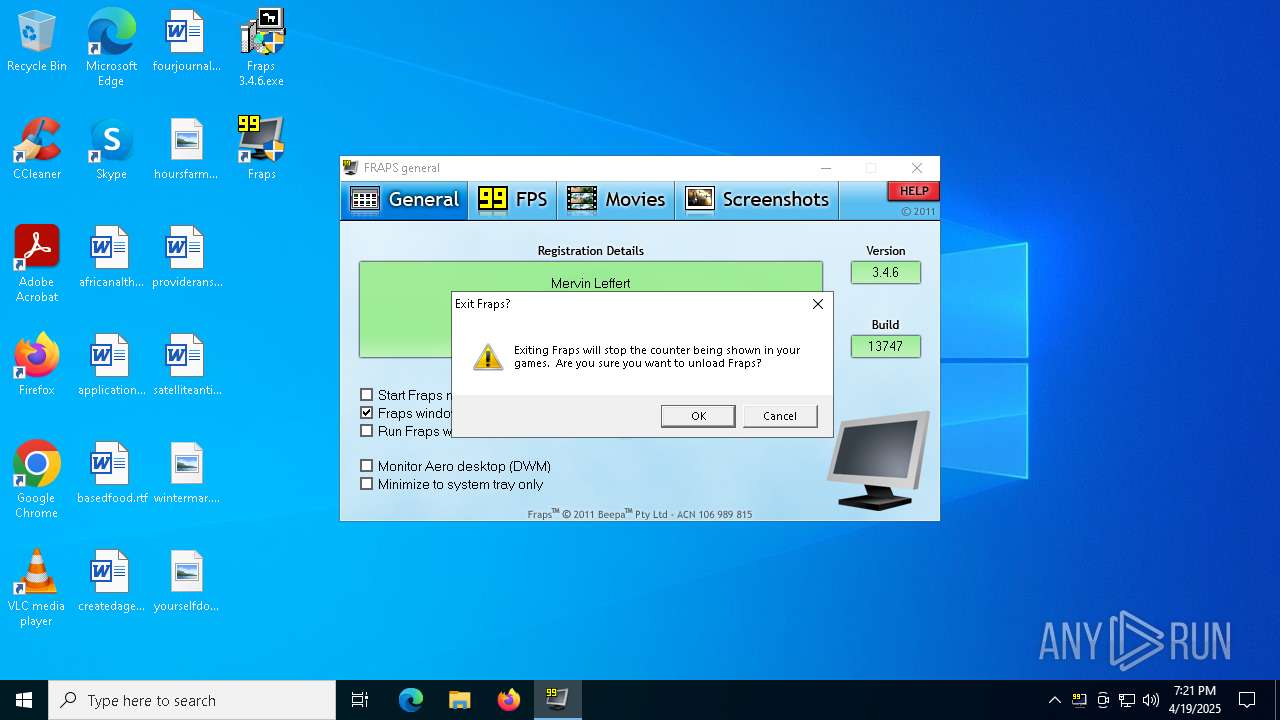
Manual execution by a user
- fraps.exe (PID: 8124)
- fraps.exe (PID: 8172)
Themida protector has been detected
- fraps.exe (PID: 8172)
Creates files in the program directory
- PLUGScheduler.exe (PID: 4132)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:12:05 22:50:52+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24064 |
| InitializedDataSize: | 164864 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x30fa |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.4.6.13747 |
| ProductVersionNumber: | 3.4.6.13747 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | ASCII |
| CompanyName: | Beepa Pty Ltd |
| FileDescription: | Fraps Installer |
| FileVersion: | 3.4.6.13747 |
| LegalCopyright: | Copyright © Beepa Pty Ltd 2011 |
| LegalTrademarks: | Fraps is a trademark of Beepa Pty Ltd |
| ProductName: | FRAPS |
Total processes
264
Monitored processes
9
Malicious processes
2
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
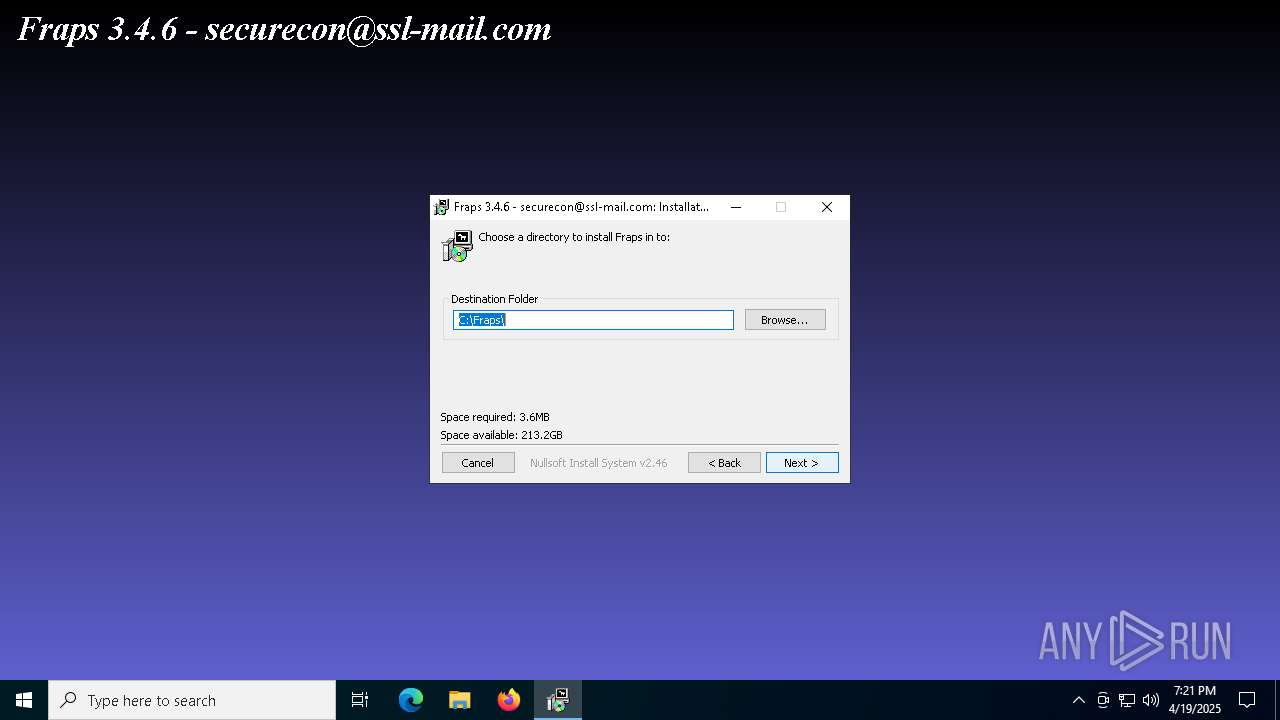
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 4108 | "C:\Fraps\fraps64.dat" | C:\Fraps\fraps64.dat | — | fraps.exe | |||||||||||
User: admin Company: Beepa P/L Integrity Level: HIGH Description: Fraps Exit code: 0 Version: 3, 4, 6, 13747 Modules
| |||||||||||||||
| 4132 | "C:\Program Files\RUXIM\PLUGscheduler.exe" | C:\Program Files\RUXIM\PLUGScheduler.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Update LifeCycle Component Scheduler Exit code: 0 Version: 10.0.19041.3623 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5576 | "C:\Users\admin\Desktop\Fraps 3.4.6.exe" | C:\Users\admin\Desktop\Fraps 3.4.6.exe | — | explorer.exe | |||||||||||
User: admin Company: Beepa Pty Ltd Integrity Level: MEDIUM Description: Fraps Installer Exit code: 3221226540 Version: 3.4.6.13747 Modules
| |||||||||||||||
| 6516 | "C:\Users\admin\Desktop\Fraps 3.4.6.exe" | C:\Users\admin\Desktop\Fraps 3.4.6.exe | explorer.exe | ||||||||||||
User: admin Company: Beepa Pty Ltd Integrity Level: HIGH Description: Fraps Installer Exit code: 0 Version: 3.4.6.13747 Modules
| |||||||||||||||
| 7220 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7252 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7644 | "C:\Fraps\fraps.exe" /exit | C:\Fraps\fraps.exe | — | Fraps 3.4.6.exe | |||||||||||
User: admin Company: Beepa P/L Integrity Level: HIGH Description: Fraps Exit code: 0 Version: 3, 4, 6, 13747 Modules
| |||||||||||||||
| 8124 | "C:\Fraps\fraps.exe" | C:\Fraps\fraps.exe | — | explorer.exe | |||||||||||
User: admin Company: Beepa P/L Integrity Level: MEDIUM Description: Fraps Exit code: 3221226540 Version: 3, 4, 6, 13747 Modules
| |||||||||||||||
| 8172 | "C:\Fraps\fraps.exe" | C:\Fraps\fraps.exe | explorer.exe | ||||||||||||
User: admin Company: Beepa P/L Integrity Level: HIGH Description: Fraps Exit code: 0 Version: 3, 4, 6, 13747 Modules
| |||||||||||||||
Total events
1 616
Read events
694
Write events
918
Delete events
4
Modification events
| (PID) Process: | (6516) Fraps 3.4.6.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows NT\CurrentVersion\drivers.desc |
| Operation: | write | Name: | frapsvid.dll |
Value: Fraps Video Decompressor | |||
| (PID) Process: | (6516) Fraps 3.4.6.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows NT\CurrentVersion\Drivers32 |
| Operation: | write | Name: | VIDC.FPS1 |
Value: frapsvid.dll | |||
| (PID) Process: | (6516) Fraps 3.4.6.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\MediaResources\icm\VIDC.FPS1 |
| Operation: | write | Name: | Description |
Value: Fraps Video Decompressor | |||
| (PID) Process: | (6516) Fraps 3.4.6.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\MediaResources\icm\VIDC.FPS1 |
| Operation: | write | Name: | Driver |
Value: frapsvid.dll | |||
| (PID) Process: | (6516) Fraps 3.4.6.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Fraps |
| Operation: | write | Name: | Install_Dir |
Value: C:\Fraps | |||
| (PID) Process: | (6516) Fraps 3.4.6.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Fraps |
| Operation: | write | Name: | DisplayName |
Value: Fraps (remove only) | |||
| (PID) Process: | (6516) Fraps 3.4.6.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Fraps |
| Operation: | write | Name: | UninstallString |
Value: "C:\Fraps\uninstall.exe" | |||
| (PID) Process: | (6516) Fraps 3.4.6.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Fraps |
| Operation: | write | Name: | NsisSM |
Value: Fraps | |||
| (PID) Process: | (6516) Fraps 3.4.6.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\Fraps |
| Operation: | write | Name: | NsisInst |
Value: D910CA323E1B0844CA7961A3F07A3918BA6F27E0 | |||
| (PID) Process: | (6516) Fraps 3.4.6.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\drivers.desc |
| Operation: | write | Name: | frapsv64.dll |
Value: Fraps Video Decompressor | |||
Executable files
11
Suspicious files
47
Text files
7
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6516 | Fraps 3.4.6.exe | C:\Users\admin\AppData\Local\Temp\nsdBF2C.tmp\AdvSplash.dll | executable | |
MD5:13CC92F90A299F5B2B2F795D0D2E47DC | SHA256:EB1CA2B3A6E564C32677D0CDC388E26B74EF686E071D7DBCA44D0BFA10488FEB | |||
| 6516 | Fraps 3.4.6.exe | C:\Fraps\fraps.exe | executable | |
MD5:6D0E16F2D14FC2FE6AE81A676B498184 | SHA256:1B50B390C867A2430807F19DE901EEC8F6B27AD5BE7F0B29CB468E788C253733 | |||
| 6516 | Fraps 3.4.6.exe | C:\Users\admin\AppData\Local\Temp\nsdBF2C.tmp\StartMenu.dll | executable | |
MD5:A4173B381625F9F12AADB4E1CDAEFDB8 | SHA256:7755FF2707CA19344D489A5ACEC02D9E310425FA6E100D2F13025761676B875B | |||
| 6516 | Fraps 3.4.6.exe | C:\Users\admin\AppData\Local\Temp\beepa.bmp | image | |
MD5:1AA76C32A7033FEB98C3A84C258CC7F9 | SHA256:DA3C7D44B495CBF865CD6711FD7A610EB042CB0912E16D2D553135A9BAC7C408 | |||
| 6516 | Fraps 3.4.6.exe | C:\Fraps\fraps32.dll | executable | |
MD5:ACCBF8EB13DFDEDCA1439102EF779F38 | SHA256:6E47C183478D4B19CDF75F8F8491910D168279ABB408979C8300E8F4E5D6156F | |||
| 6516 | Fraps 3.4.6.exe | C:\Fraps\HELP\help_fps.htm | html | |
MD5:F335E9E4E8A45C7DCFC30B5B8B61D838 | SHA256:B1419A421EA79DE26A910C941C72D8EEF7F97F42E55C28E8F7DF9D31BE3A0889 | |||
| 6516 | Fraps 3.4.6.exe | C:\Fraps\frapslcd.dll | executable | |
MD5:7D0A6983497B8D869CCBF66D3FA0185D | SHA256:5B5E92EFDF6C62CD2D88918971B09DE84862396E85DC4AB31989A127E2C8D5FB | |||
| 6516 | Fraps 3.4.6.exe | C:\Fraps\README.HTM | html | |
MD5:E9DCDDD2E2FD79F1B17094C35303BA25 | SHA256:444E39F28657EC4E4078F95816EC6B2B3A74E484AE40BA8EC7E4FD35D67E1430 | |||
| 6516 | Fraps 3.4.6.exe | C:\Fraps\fraps64.dll | executable | |
MD5:7DF986DD7A6C6776FFDB5792092F594D | SHA256:03318410ACF83B8FE2BF282171405D885E4D4681F33A66C56E1CDE3D4A85E877 | |||
| 6516 | Fraps 3.4.6.exe | C:\Fraps\HELP\help_general.htm | html | |
MD5:CA2111DCBC54A05E596894F3B0B3E453 | SHA256:731AA299A4024B9574282C12FF9385B6BC972A360D327633259C5BFFF7BD8B86 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
18
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 96.16.53.133:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5180 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 96.16.53.133:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 96.16.53.133:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 96.16.53.133:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2924 | SearchApp.exe | 2.16.27.98:443 | www.bing.com | Akamai International B.V. | NL | whitelisted |
— | — | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
3028 | OfficeClickToRun.exe | 52.109.76.240:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
ecs.office.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |