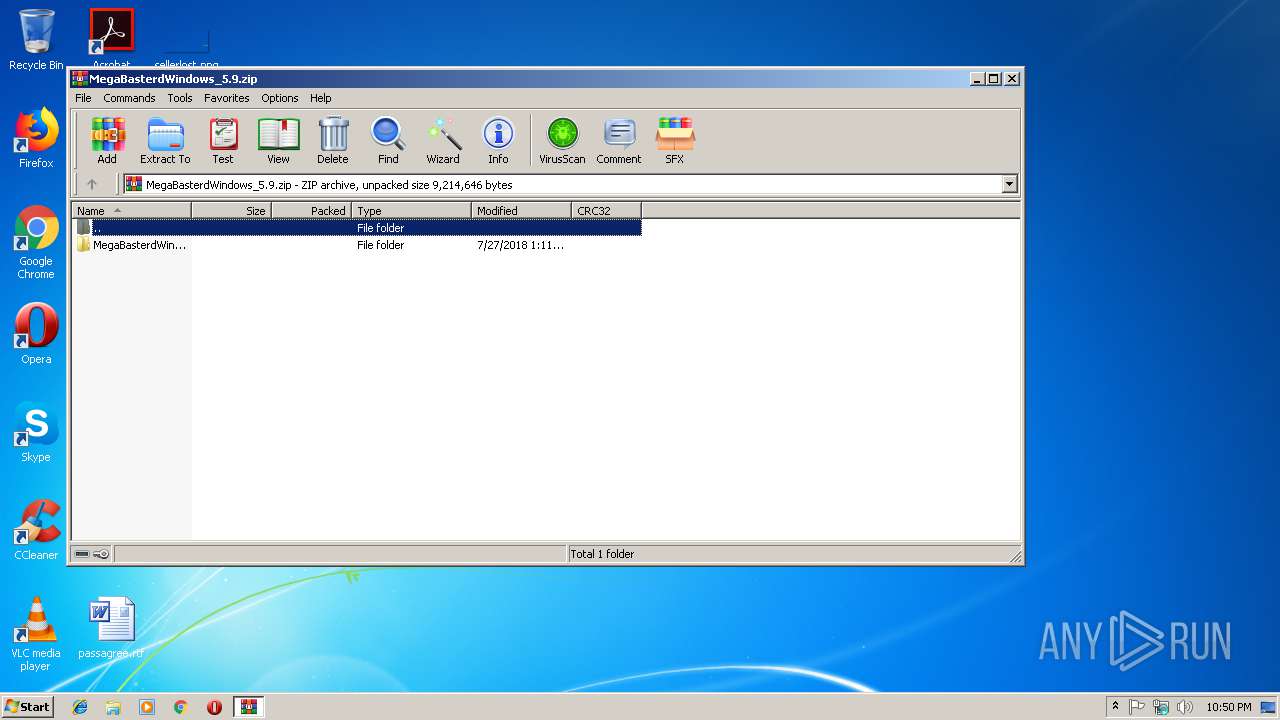
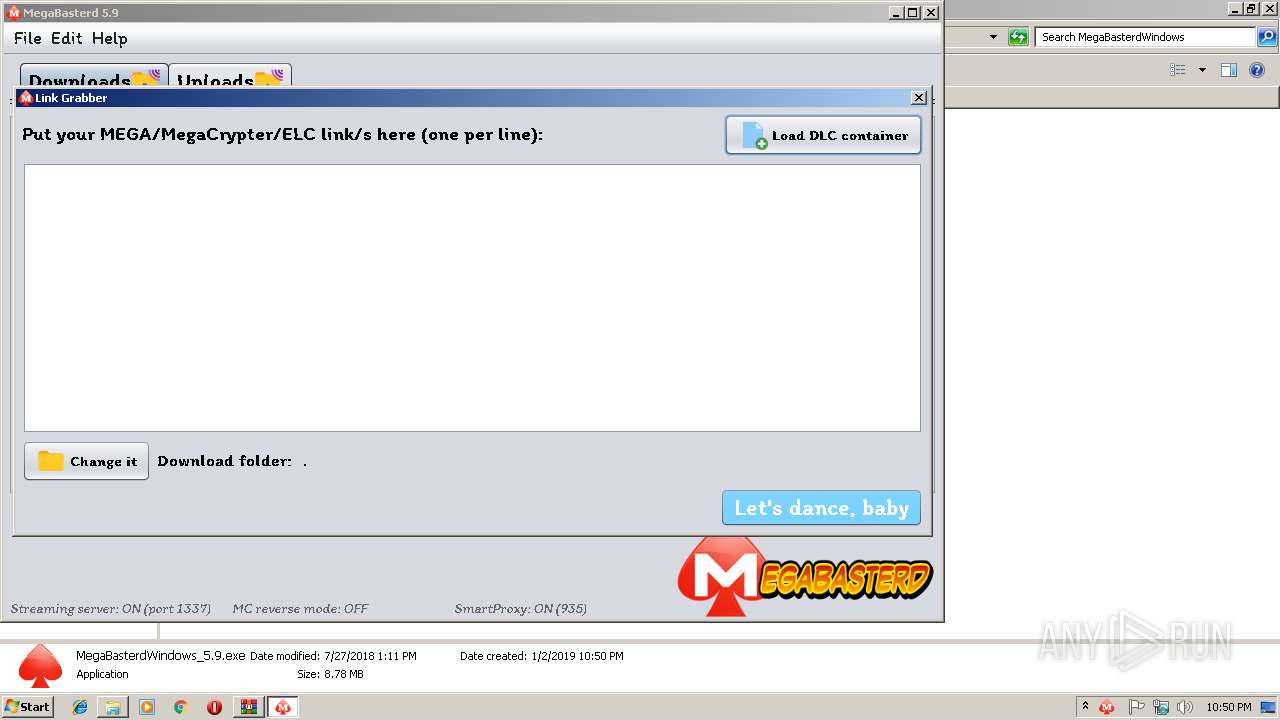
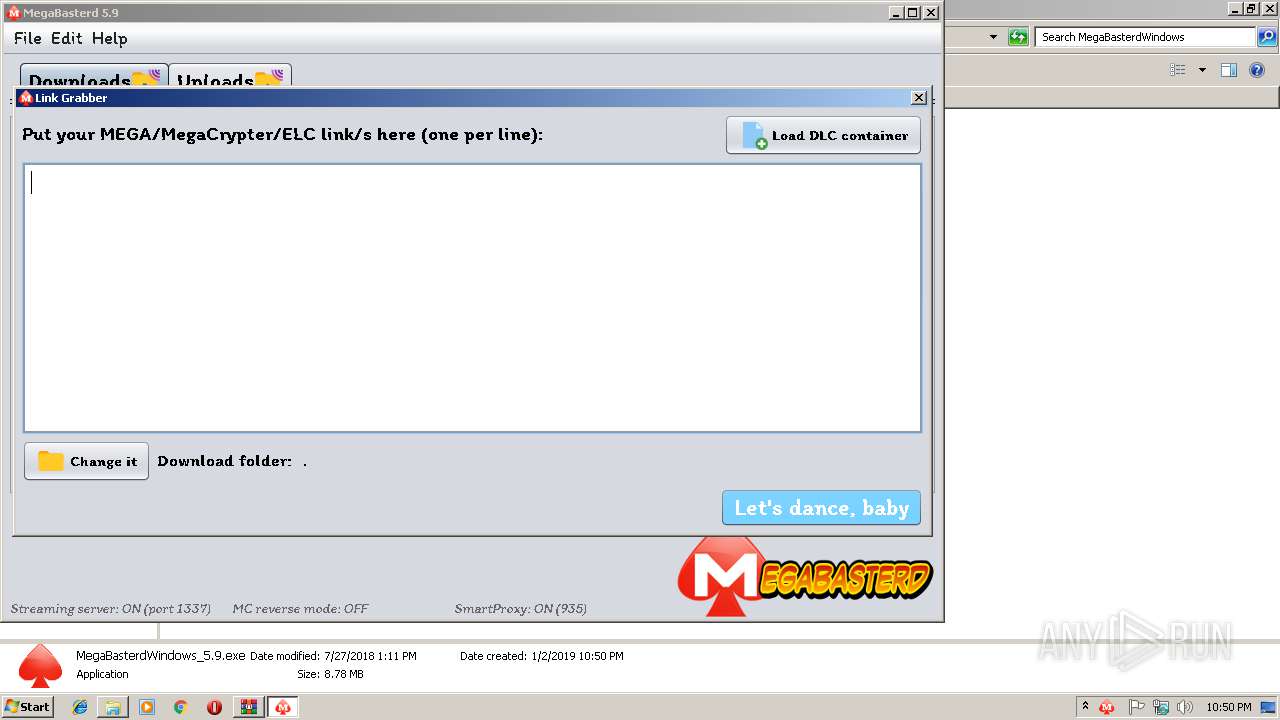
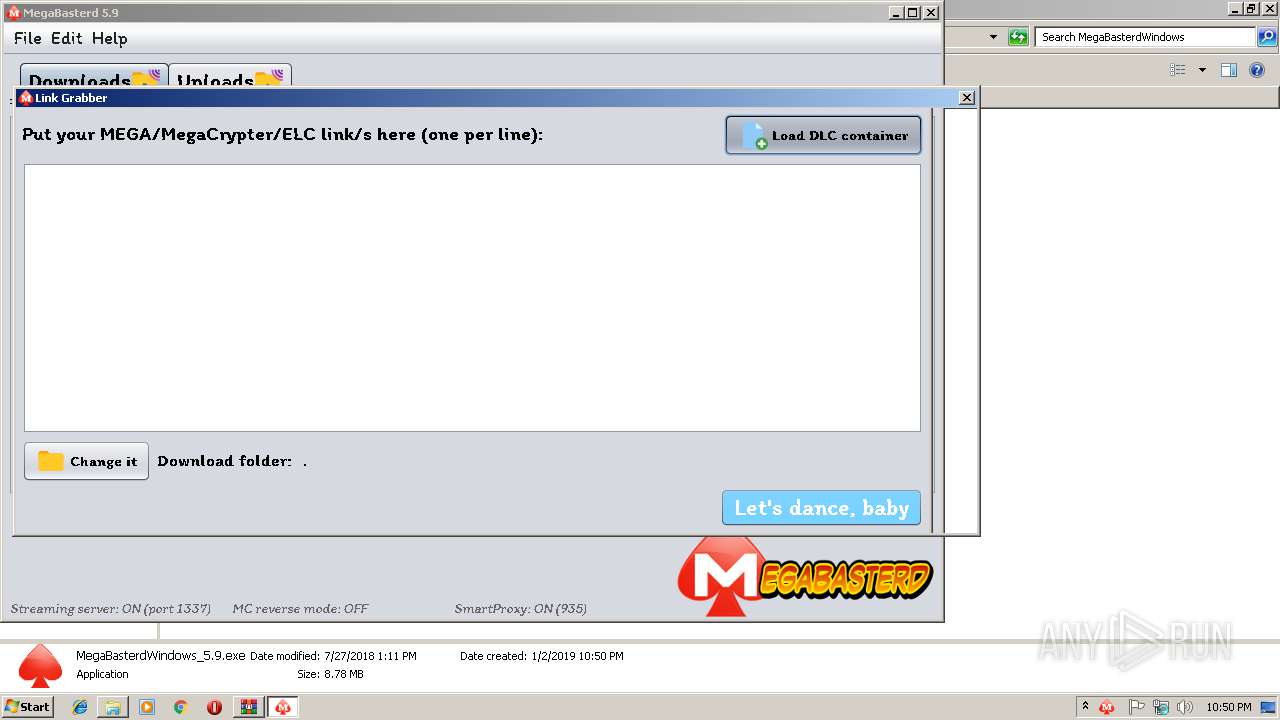
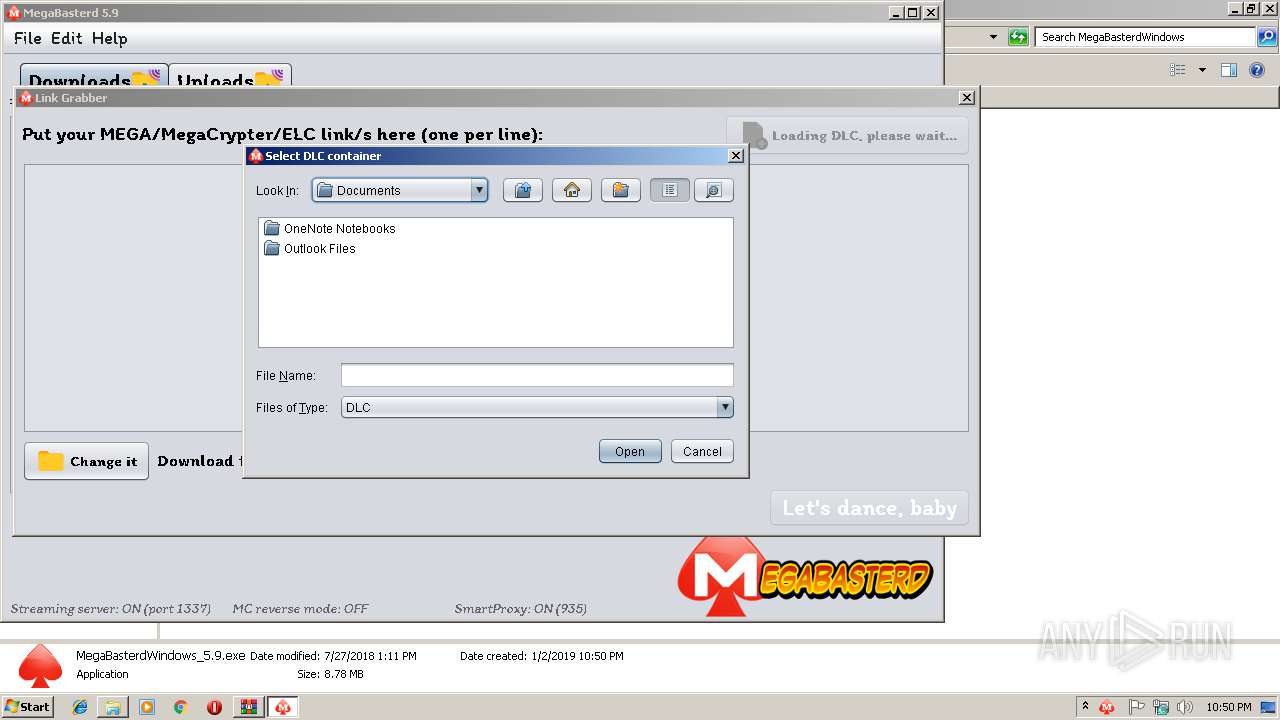
| File name: | MegaBasterdWindows_5.9.zip |
| Full analysis: | https://app.any.run/tasks/48a82032-ad92-4d47-9d20-4da446a93e9b |
| Verdict: | Malicious activity |
| Analysis date: | January 02, 2019, 22:49:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | E4DFB8BFA643AD5263BE67132C864F3E |
| SHA1: | D0AC7ABA4DCCEDE37531F634B1641752924D83F7 |
| SHA256: | 6370139137A7D4EE32651FAC53EF1AB271482B5B9E5DC9310263B039AA7EF1E3 |
| SSDEEP: | 196608:LvMFXFoYNaaUfHVFrv03kbZQ9Pio32ULRx4EWiboRLS90R0wiIAUYJq:I9FoYNaaGHVpukbZQBihULRx4lNRLSEl |
MALICIOUS
Application was dropped or rewritten from another process
- MegaBasterdWindows_5.9.exe (PID: 2916)
Loads dropped or rewritten executable
- javaw.exe (PID: 3448)
SUSPICIOUS
Creates files in the user directory
- javaw.exe (PID: 3448)
Executable content was dropped or overwritten
- javaw.exe (PID: 3448)
- WinRAR.exe (PID: 3220)
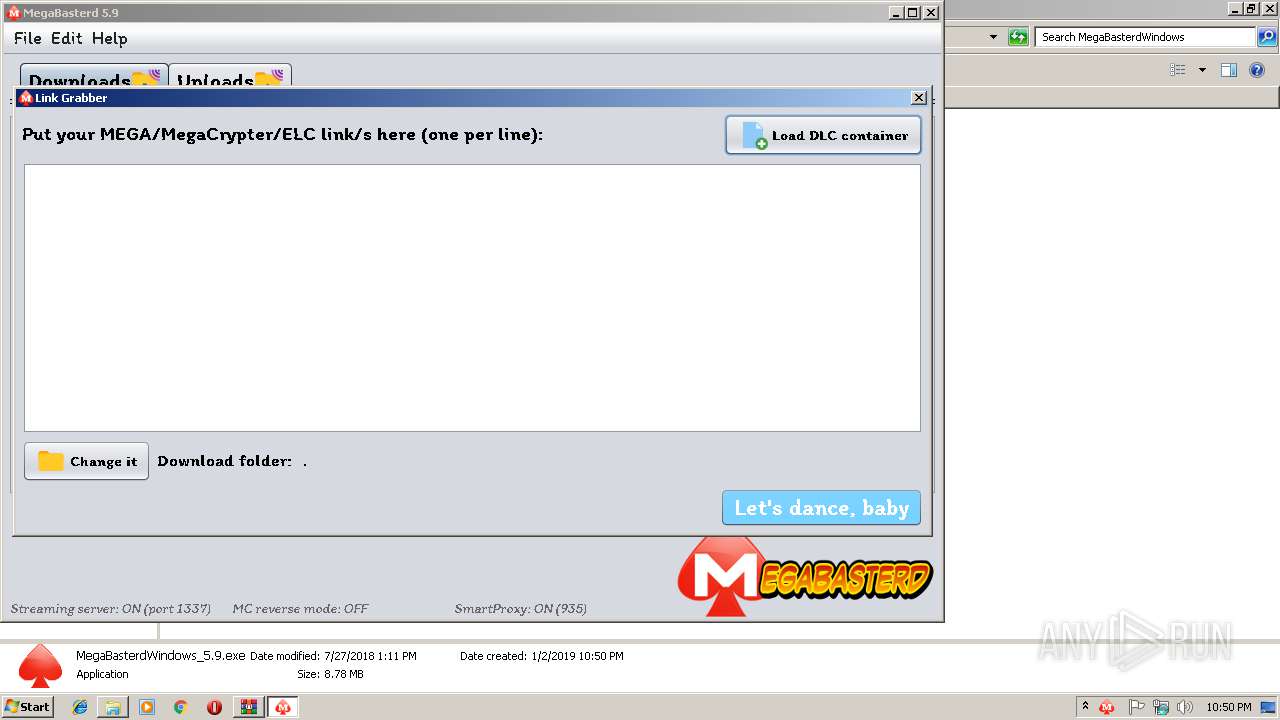
Executes JAVA applets
- MegaBasterdWindows_5.9.exe (PID: 2916)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 788 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2018:07:27 14:11:09 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | MegaBasterdWindows/ |
Total processes
33
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
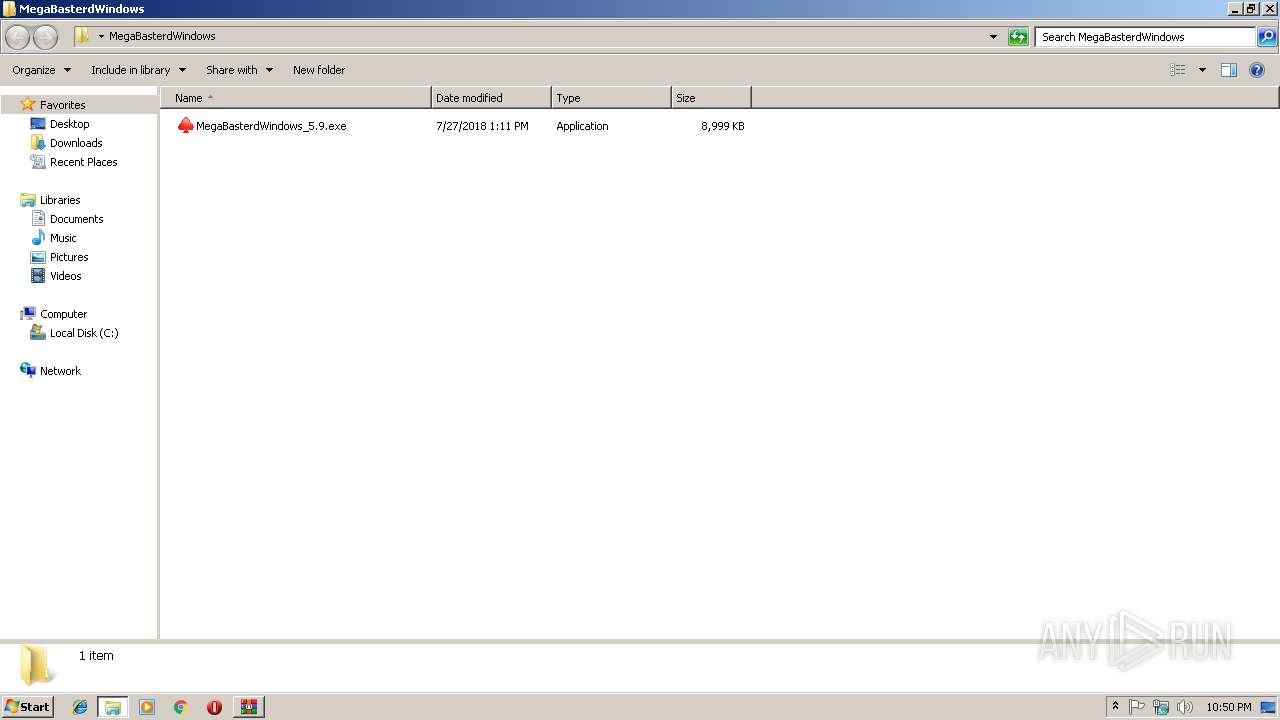
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
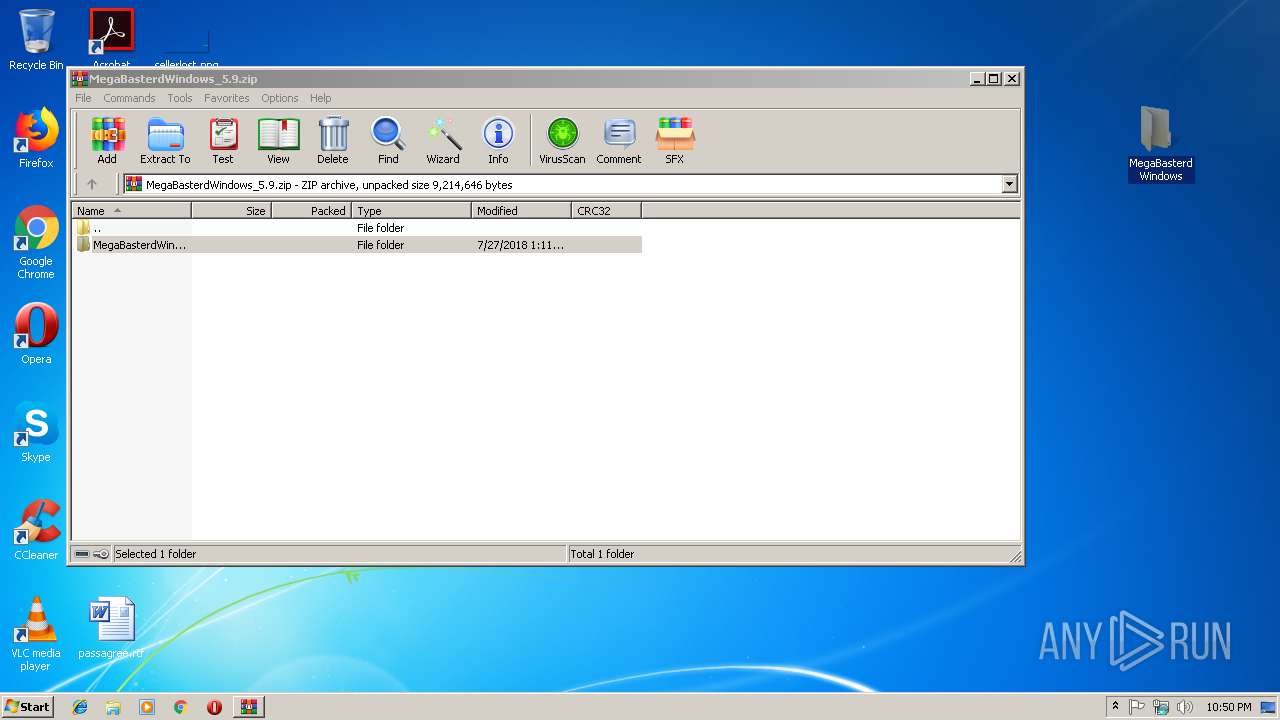
| 2916 | "C:\Users\admin\Desktop\MegaBasterdWindows\MegaBasterdWindows_5.9.exe" | C:\Users\admin\Desktop\MegaBasterdWindows\MegaBasterdWindows_5.9.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
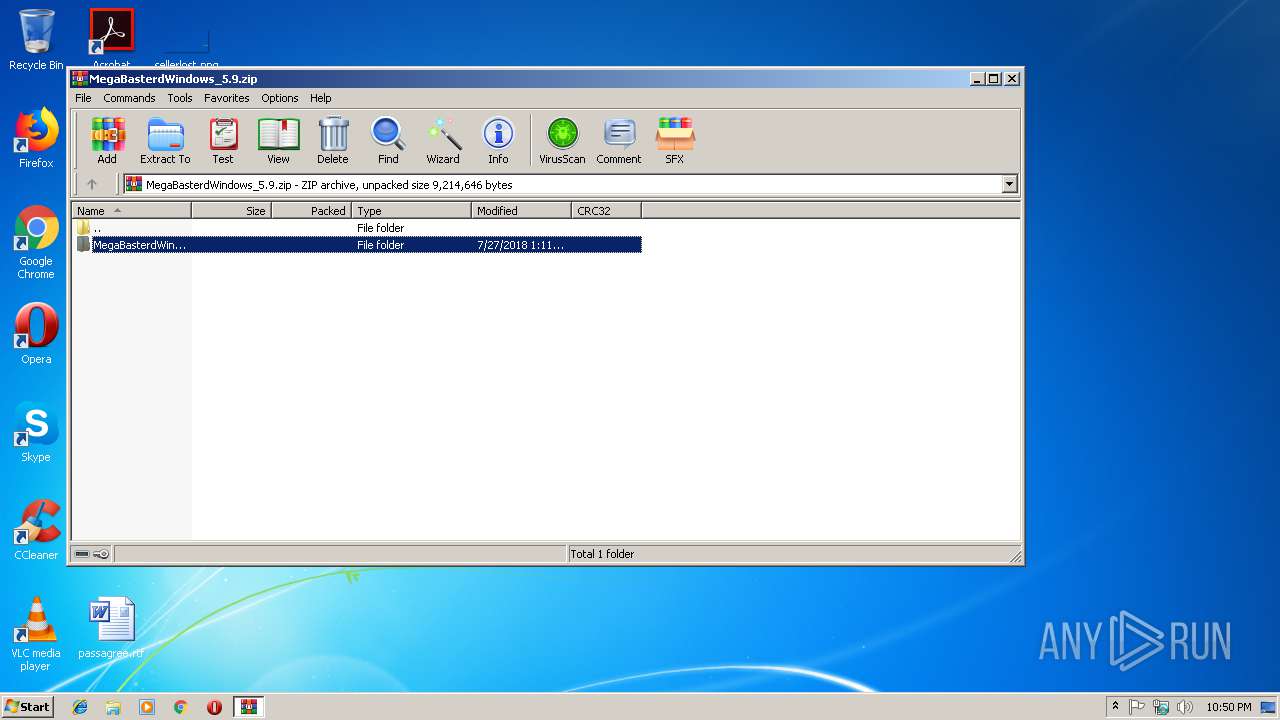
| 3220 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\MegaBasterdWindows_5.9.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
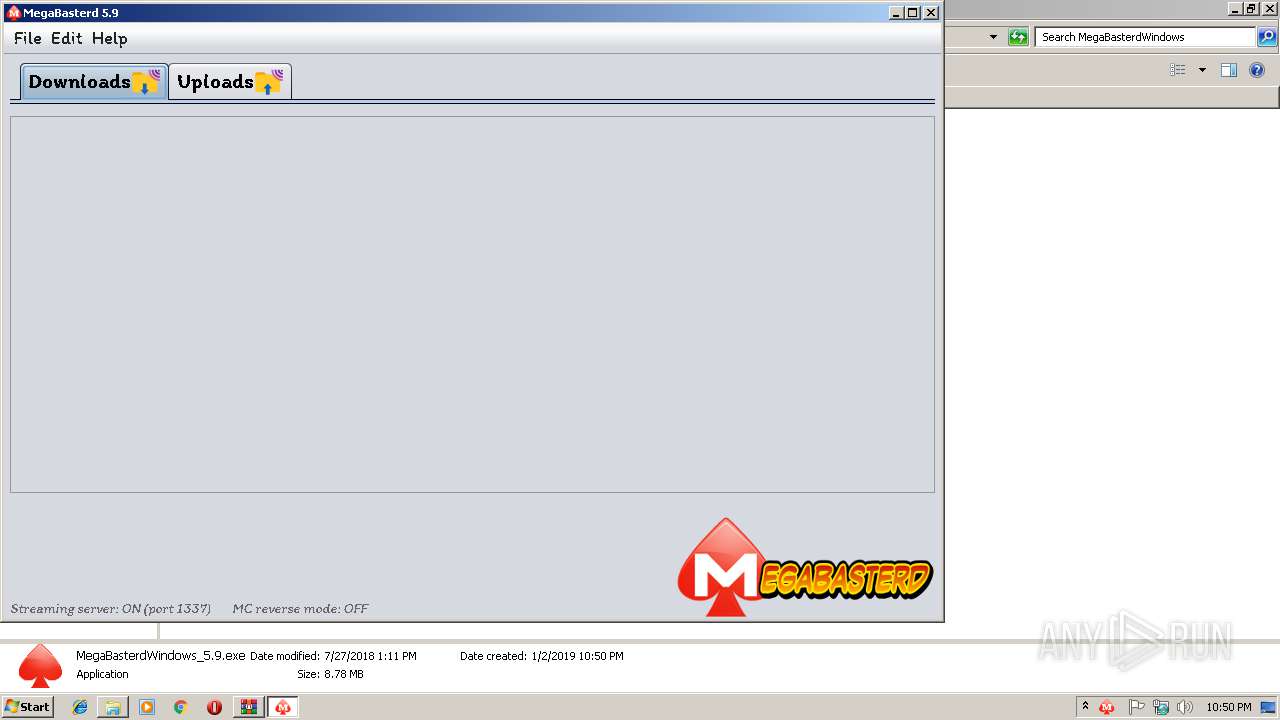
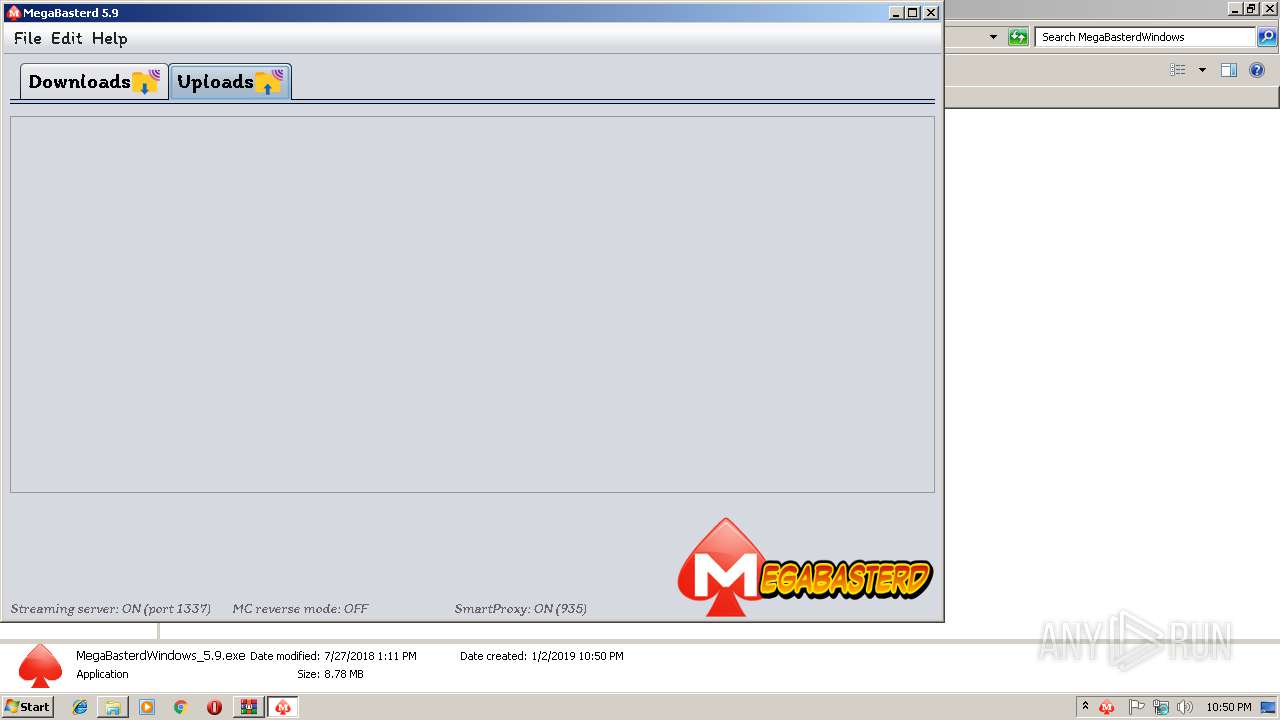
| 3448 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -jar "C:\Users\admin\Desktop\MegaBasterdWindows\MegaBasterdWindows_5.9.exe" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | MegaBasterdWindows_5.9.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
Total events
554
Read events
544
Write events
10
Delete events
0
Modification events
| (PID) Process: | (3220) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3220) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3220) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3220) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\MegaBasterdWindows_5.9.zip | |||
| (PID) Process: | (3220) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3220) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3220) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3220) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3448) javaw.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: javaw.exe | |||
| (PID) Process: | (3448) javaw.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
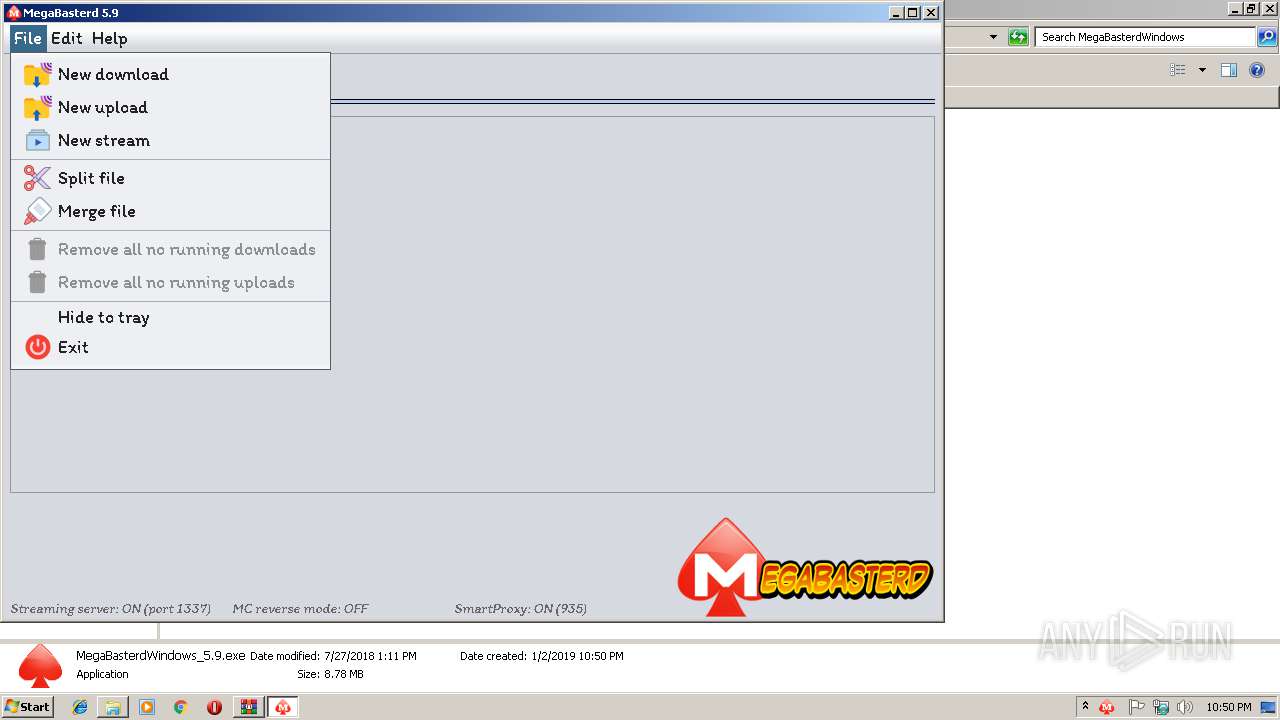
Executable files
2
Suspicious files
0
Text files
1
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3448 | javaw.exe | C:\Users\admin\Desktop\MegaBasterdWindows\megabasterd.db-journal | — | |
MD5:— | SHA256:— | |||
| 3448 | javaw.exe | C:\Users\admin\Desktop\MegaBasterdWindows\megabasterd.db-shm | — | |
MD5:— | SHA256:— | |||
| 3448 | javaw.exe | C:\Users\admin\Desktop\MegaBasterdWindows\megabasterd.db-wal | — | |
MD5:— | SHA256:— | |||
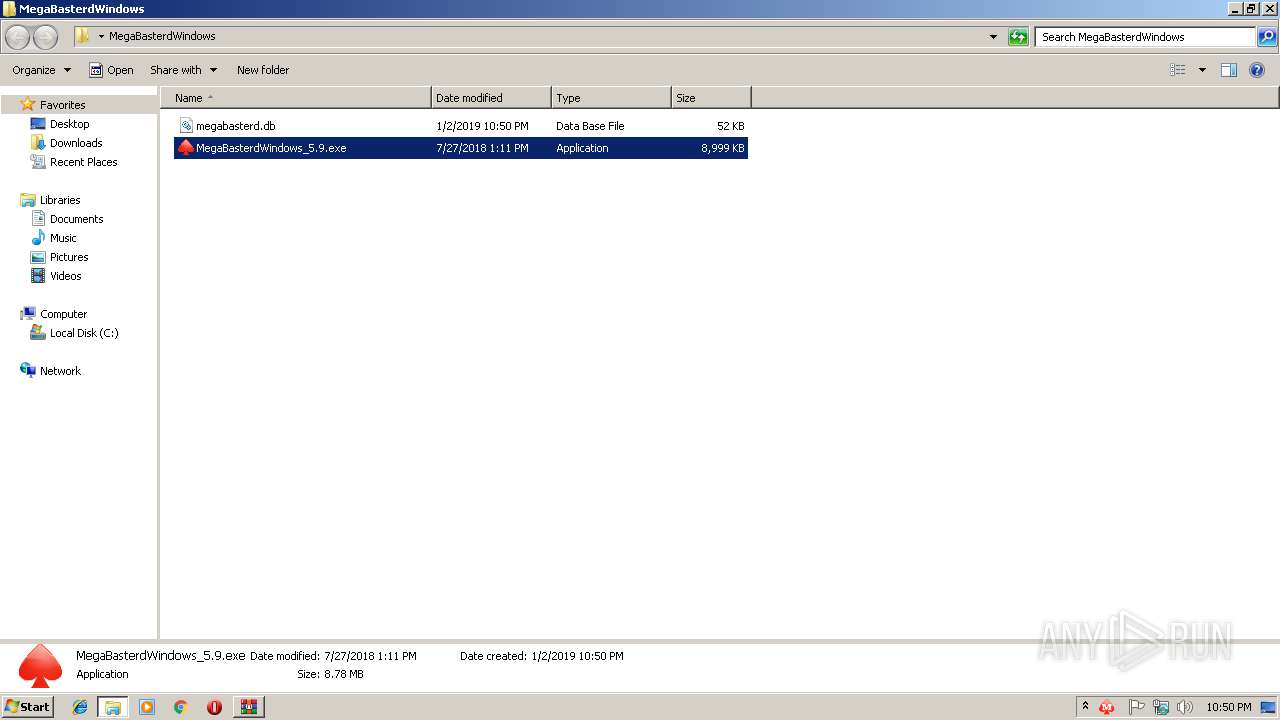
| 3448 | javaw.exe | C:\Users\admin\Desktop\MegaBasterdWindows\megabasterd.db | sqlite | |
MD5:— | SHA256:— | |||
| 3448 | javaw.exe | C:\Users\admin\AppData\Local\Temp\sqlite-3.21.0.1-61c5ab8f-1923-43df-965a-2386542d8816-sqlitejdbc.dll | executable | |
MD5:— | SHA256:— | |||
| 3220 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3220.42322\MegaBasterdWindows\MegaBasterdWindows_5.9.exe | executable | |
MD5:— | SHA256:— | |||
| 3448 | javaw.exe | C:\Users\admin\.oracle_jre_usage\90737d32e3abaa4.timestamp | text | |
MD5:— | SHA256:— | |||
| 3448 | javaw.exe | C:\Users\admin\AppData\Local\Temp\+~JF1019771273591406523.tmp | ttf | |
MD5:EE6755AE411FFBCCD2F24549D871C6B5 | SHA256:9164D7EB92CA717B53B07193E3445C96782222D24215151B8D2851B576B17645 | |||
| 3448 | javaw.exe | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-1302019708-1500728564-335382590-1000\83aa4cc77f591dfc2374580bbd95f6ba_90059c37-1320-41a4-b58d-2b75a9850d2f | dbf | |
MD5:C8366AE350E7019AEFC9D1E6E6A498C6 | SHA256:11E6ACA8E682C046C83B721EEB5C72C5EF03CB5936C60DF6F4993511DDC61238 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3448 | javaw.exe | 31.216.147.135:443 | g.api.mega.co.nz | Datacenter Luxembourg S.A. | LU | unknown |
3448 | javaw.exe | 151.101.0.133:443 | raw.githubusercontent.com | Fastly | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
raw.githubusercontent.com |
| shared |
g.api.mega.co.nz |
| shared |