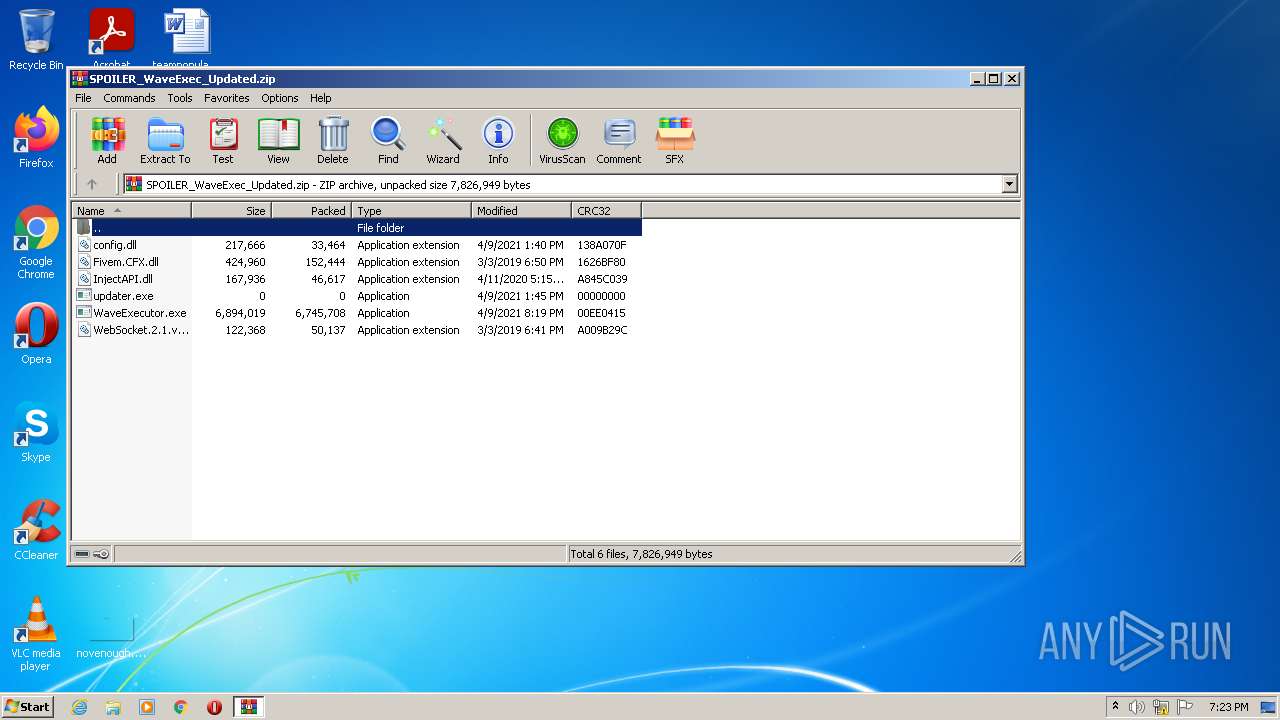
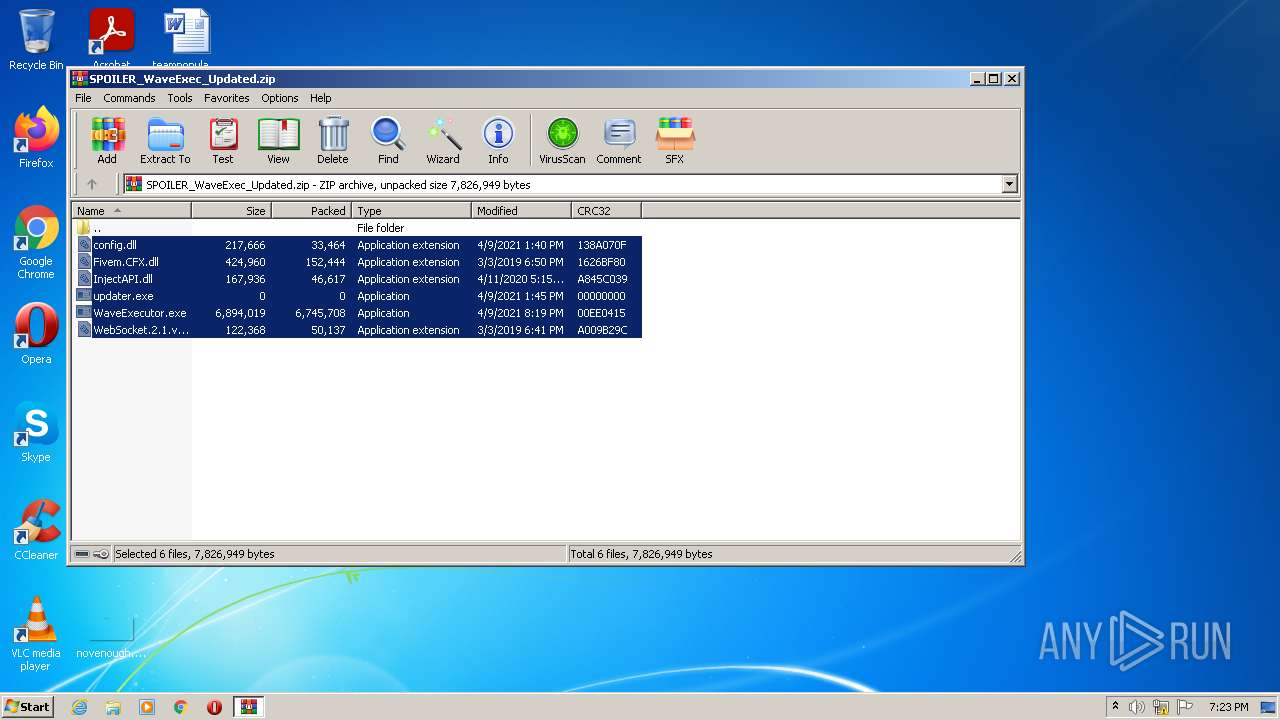
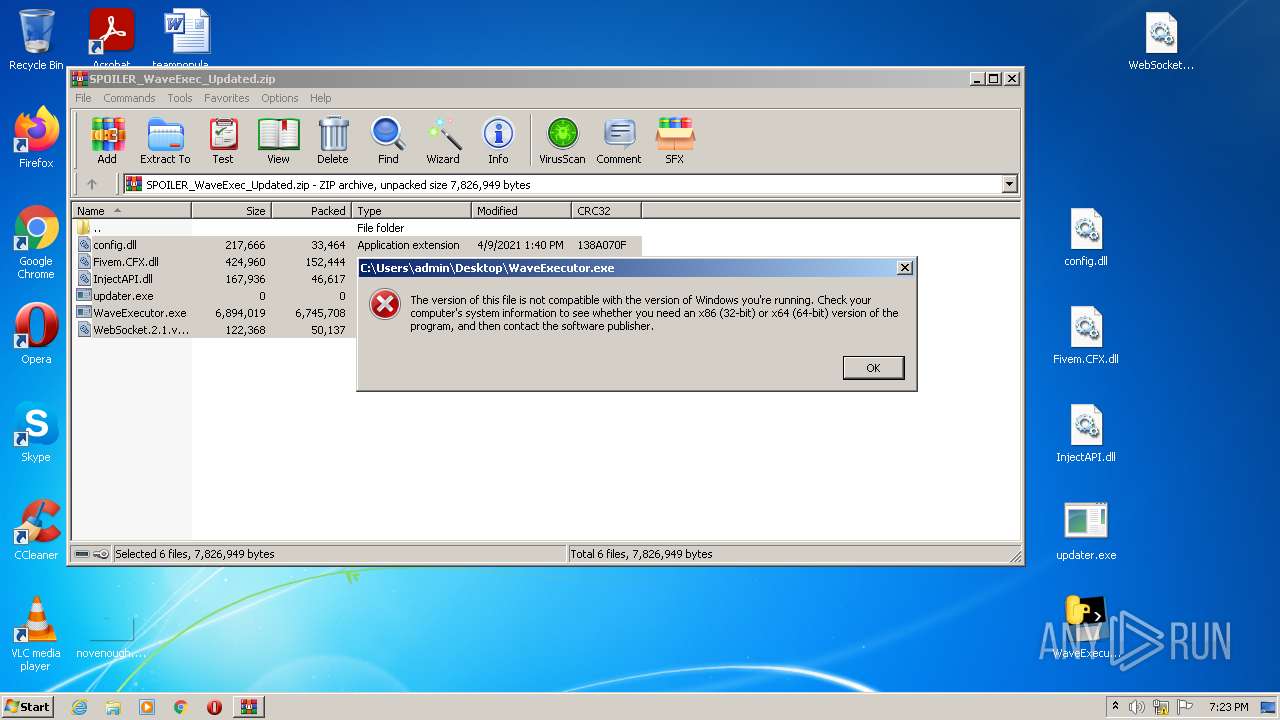
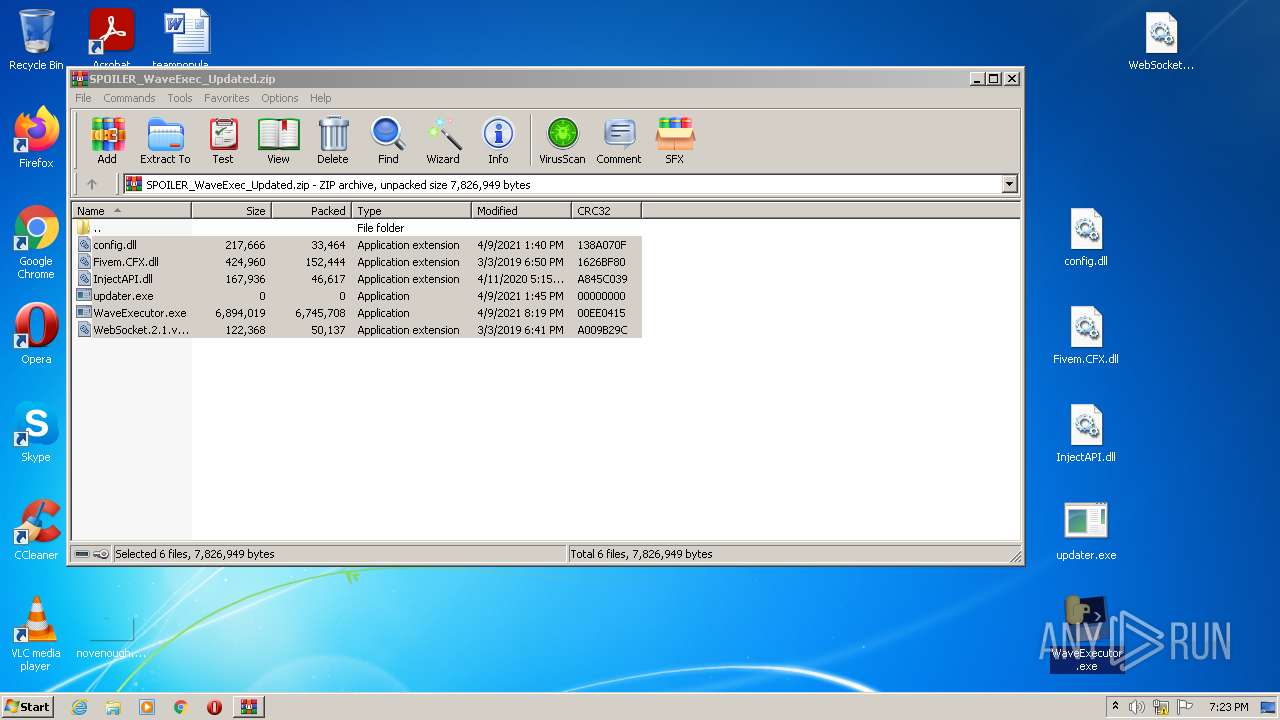
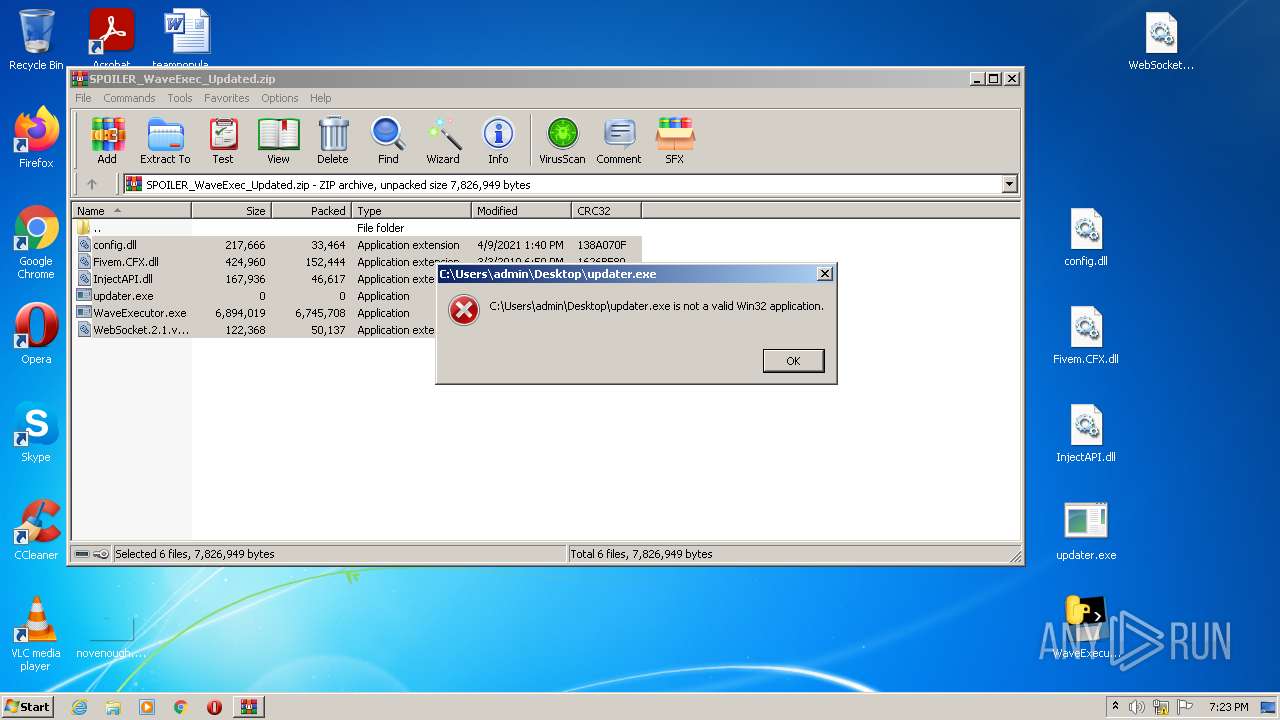
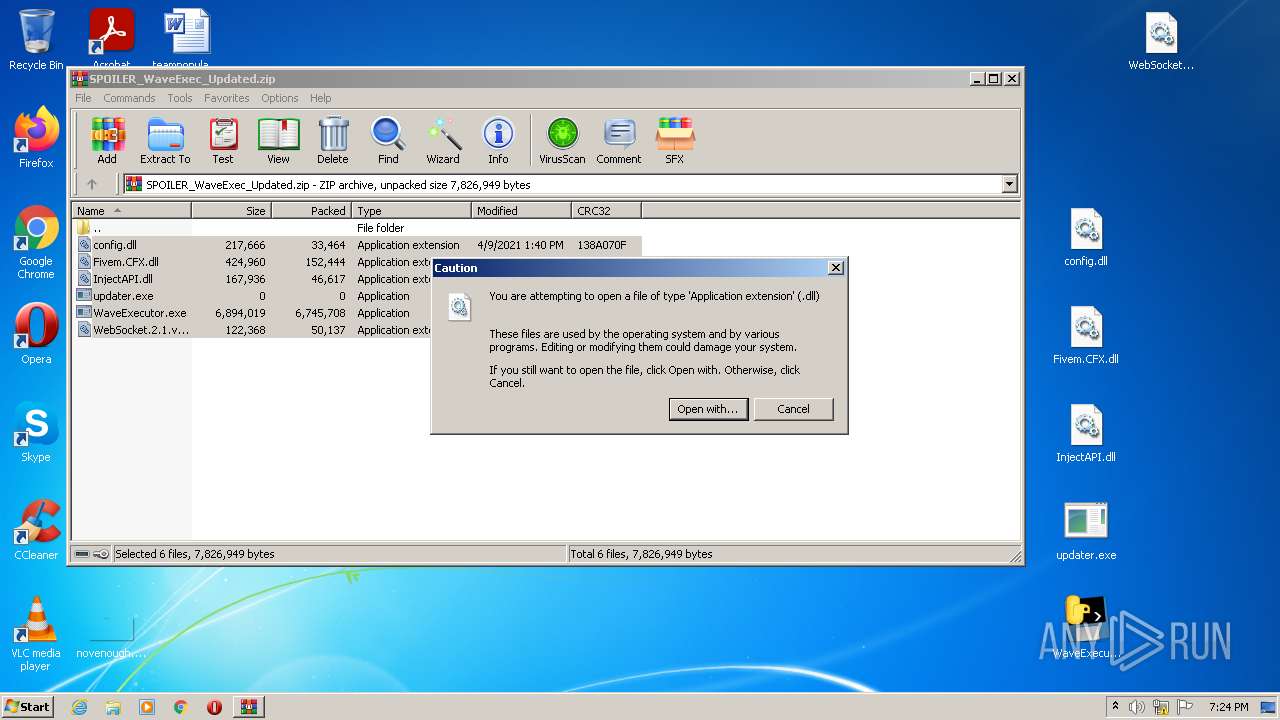
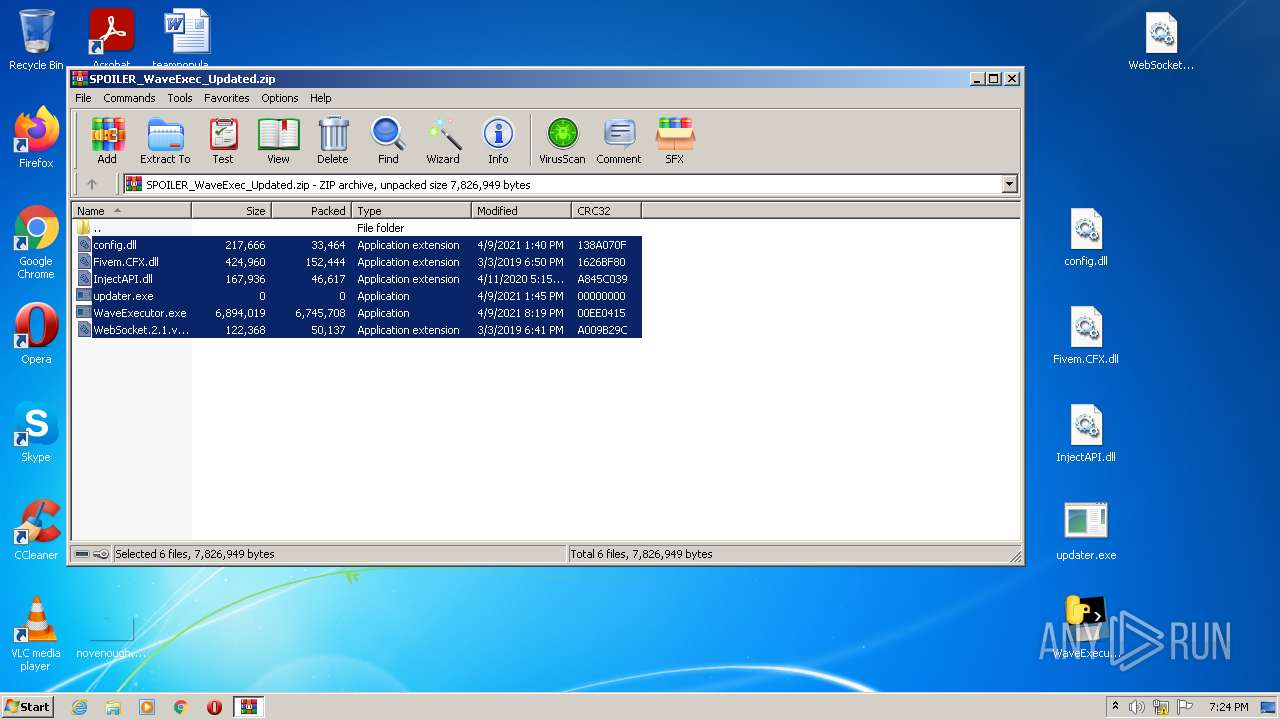
| download: | SPOILER_WaveExec_Updated.zip |
| Full analysis: | https://app.any.run/tasks/16f436b5-8f2d-4c03-97c2-7bc9c47d430f |
| Verdict: | Malicious activity |
| Analysis date: | August 12, 2022, 18:23:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
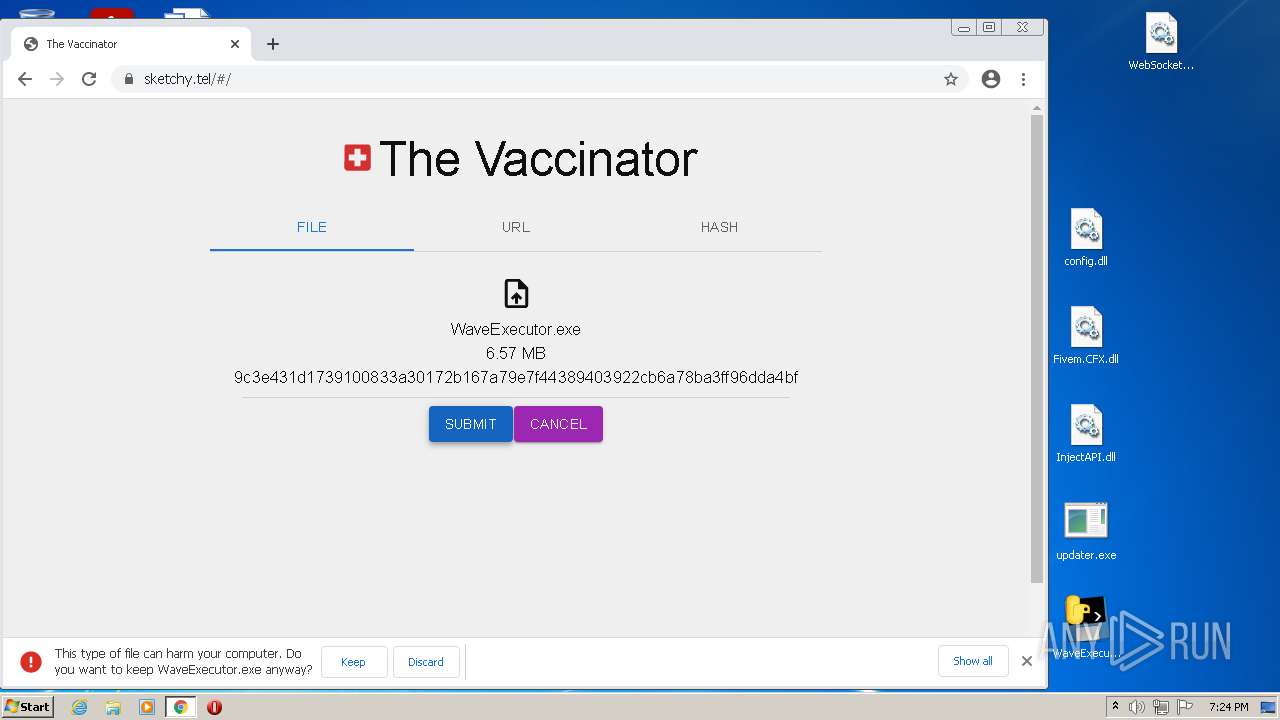
| MD5: | C1844CE63827175E9C4CCDABE1E4FE35 |
| SHA1: | 25159816F2D2C9FB01EE80AEFE1DD7ADEE9D6533 |
| SHA256: | 636C9704BBDC35C7FE70598066B4260F2E42CE0023394A7414F25690F38A4594 |
| SSDEEP: | 196608:+J2wpK577+0lgds2F7PeCRP4G/ozj0expGdPZJ:i2yKh7XuC25dZFozQ6aPn |
MALICIOUS
Drops executable file immediately after starts
- WinRAR.exe (PID: 3116)
- chrome.exe (PID: 1524)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3500)
SUSPICIOUS
Checks supported languages
- WinRAR.exe (PID: 3116)
Reads the computer name
- WinRAR.exe (PID: 3116)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3116)
- chrome.exe (PID: 1524)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 3116)
- chrome.exe (PID: 1524)
Reads default file associations for system extensions
- chrome.exe (PID: 1856)
Modifies files in Chrome extension folder
- chrome.exe (PID: 1524)
INFO
Reads the computer name
- rundll32.exe (PID: 632)
- chrome.exe (PID: 1524)
- chrome.exe (PID: 3680)
- chrome.exe (PID: 3720)
- chrome.exe (PID: 3408)
- chrome.exe (PID: 1856)
- chrome.exe (PID: 1568)
- chrome.exe (PID: 3096)
- chrome.exe (PID: 2680)
- chrome.exe (PID: 3368)
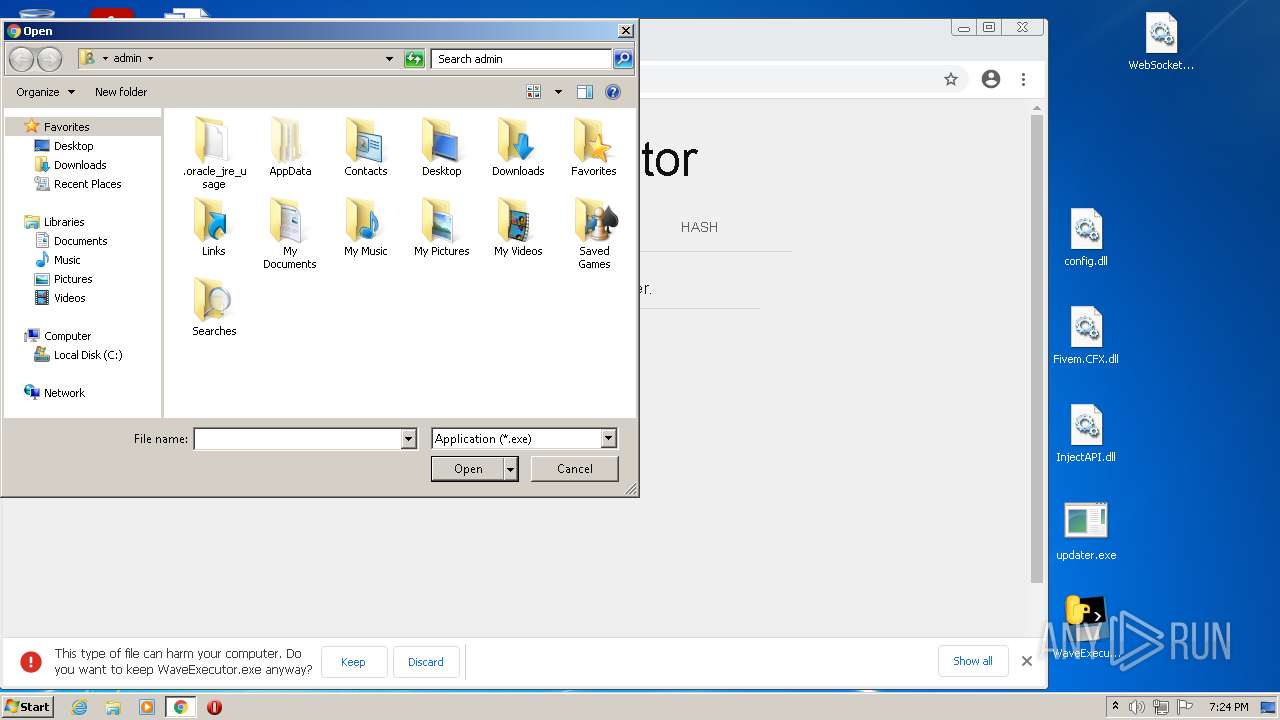
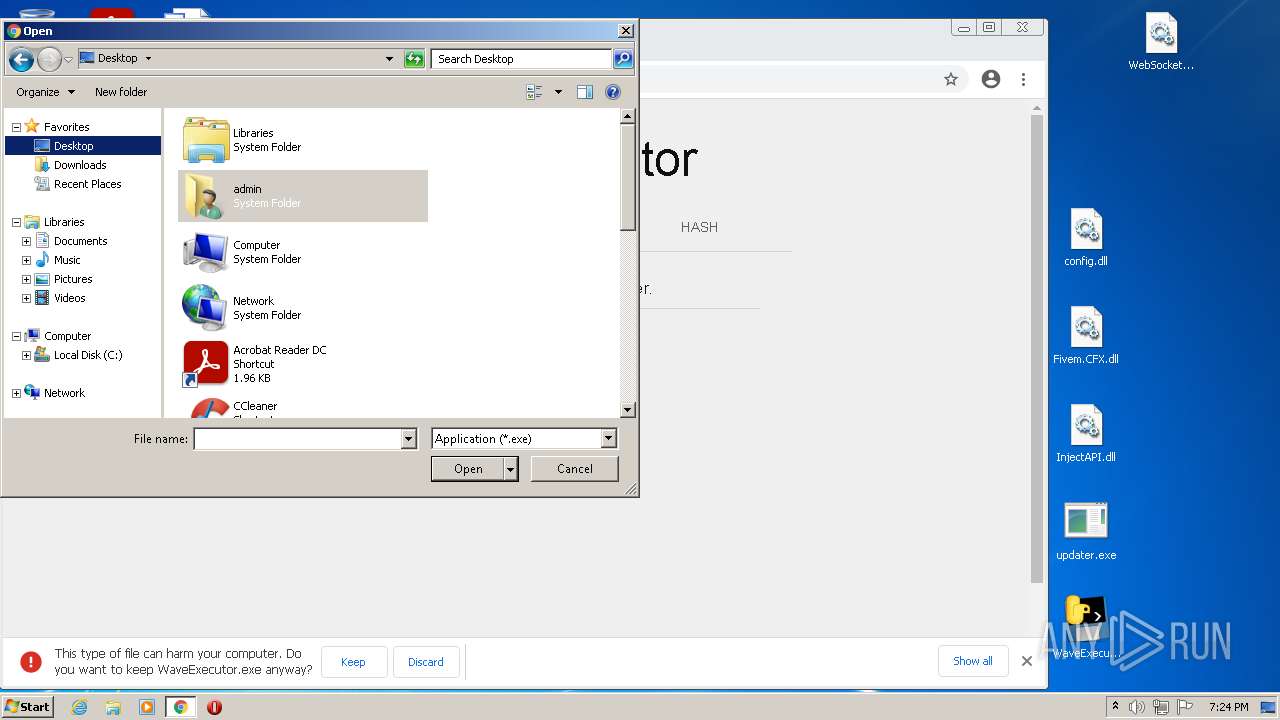
Manual execution by user
- rundll32.exe (PID: 632)
- chrome.exe (PID: 1524)
Checks supported languages
- rundll32.exe (PID: 632)
- chrome.exe (PID: 3120)
- chrome.exe (PID: 1524)
- chrome.exe (PID: 484)
- chrome.exe (PID: 3720)
- chrome.exe (PID: 3680)
- chrome.exe (PID: 2672)
- chrome.exe (PID: 3368)
- chrome.exe (PID: 2172)
- chrome.exe (PID: 3352)
- chrome.exe (PID: 3312)
- chrome.exe (PID: 2596)
- chrome.exe (PID: 2228)
- chrome.exe (PID: 2728)
- chrome.exe (PID: 2548)
- chrome.exe (PID: 2476)
- chrome.exe (PID: 3640)
- chrome.exe (PID: 2692)
- chrome.exe (PID: 3408)
- chrome.exe (PID: 2628)
- chrome.exe (PID: 888)
- chrome.exe (PID: 1880)
- chrome.exe (PID: 3180)
- chrome.exe (PID: 1788)
- chrome.exe (PID: 1856)
- chrome.exe (PID: 964)
- chrome.exe (PID: 1104)
- chrome.exe (PID: 3096)
- chrome.exe (PID: 1568)
- chrome.exe (PID: 2680)
- chrome.exe (PID: 2376)
- chrome.exe (PID: 2300)
- chrome.exe (PID: 984)
- chrome.exe (PID: 1544)
- chrome.exe (PID: 3840)
- chrome.exe (PID: 3652)
- chrome.exe (PID: 392)
- chrome.exe (PID: 1492)
- chrome.exe (PID: 3328)
- chrome.exe (PID: 2028)
- chrome.exe (PID: 2244)
- chrome.exe (PID: 3360)
- chrome.exe (PID: 2228)
- chrome.exe (PID: 3820)
- chrome.exe (PID: 2056)
- chrome.exe (PID: 3388)
- chrome.exe (PID: 1160)
- chrome.exe (PID: 2820)
- chrome.exe (PID: 1228)
- chrome.exe (PID: 2776)
- chrome.exe (PID: 1284)
- chrome.exe (PID: 3512)
- chrome.exe (PID: 2388)
- chrome.exe (PID: 2860)
- chrome.exe (PID: 2260)
- chrome.exe (PID: 1160)
- chrome.exe (PID: 3324)
- chrome.exe (PID: 3104)
- chrome.exe (PID: 3476)
- chrome.exe (PID: 3536)
- chrome.exe (PID: 2740)
- chrome.exe (PID: 2676)
- chrome.exe (PID: 3844)
- chrome.exe (PID: 3216)
- chrome.exe (PID: 2124)
- chrome.exe (PID: 2464)
- chrome.exe (PID: 2764)
- chrome.exe (PID: 2560)
Application launched itself
- chrome.exe (PID: 1524)
Reads the date of Windows installation
- chrome.exe (PID: 1568)
Reads settings of System Certificates
- chrome.exe (PID: 3680)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
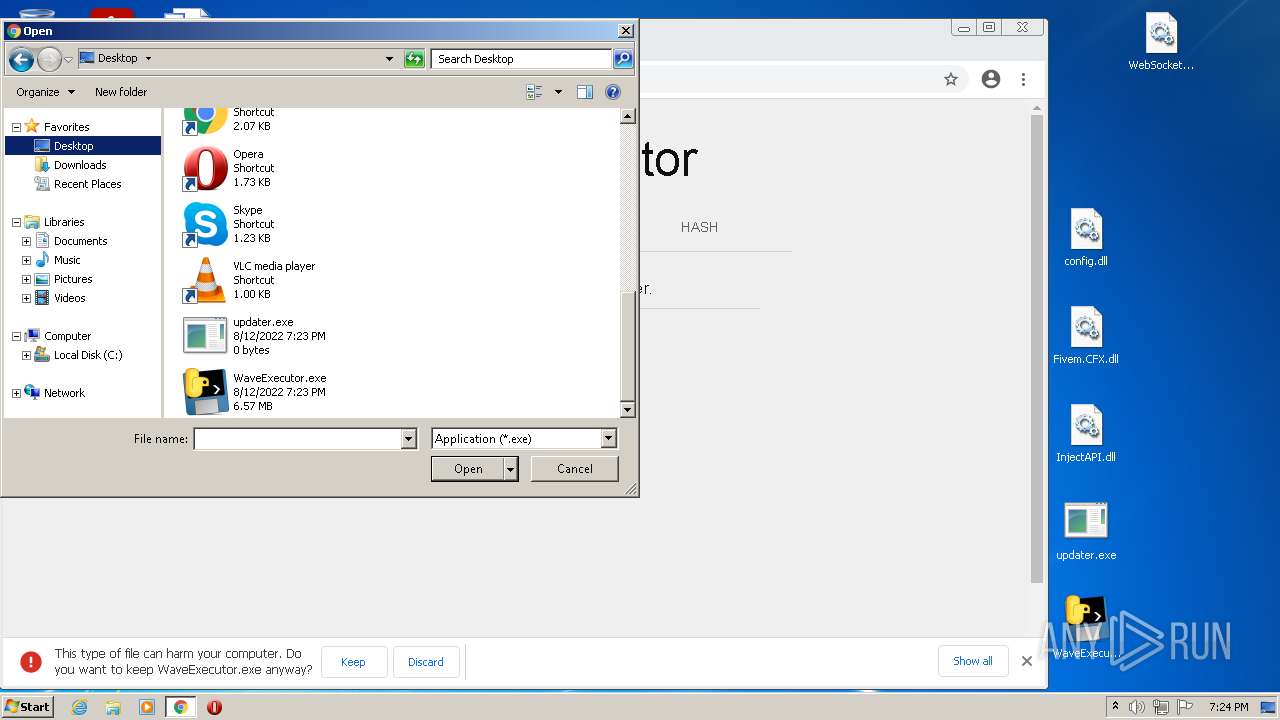
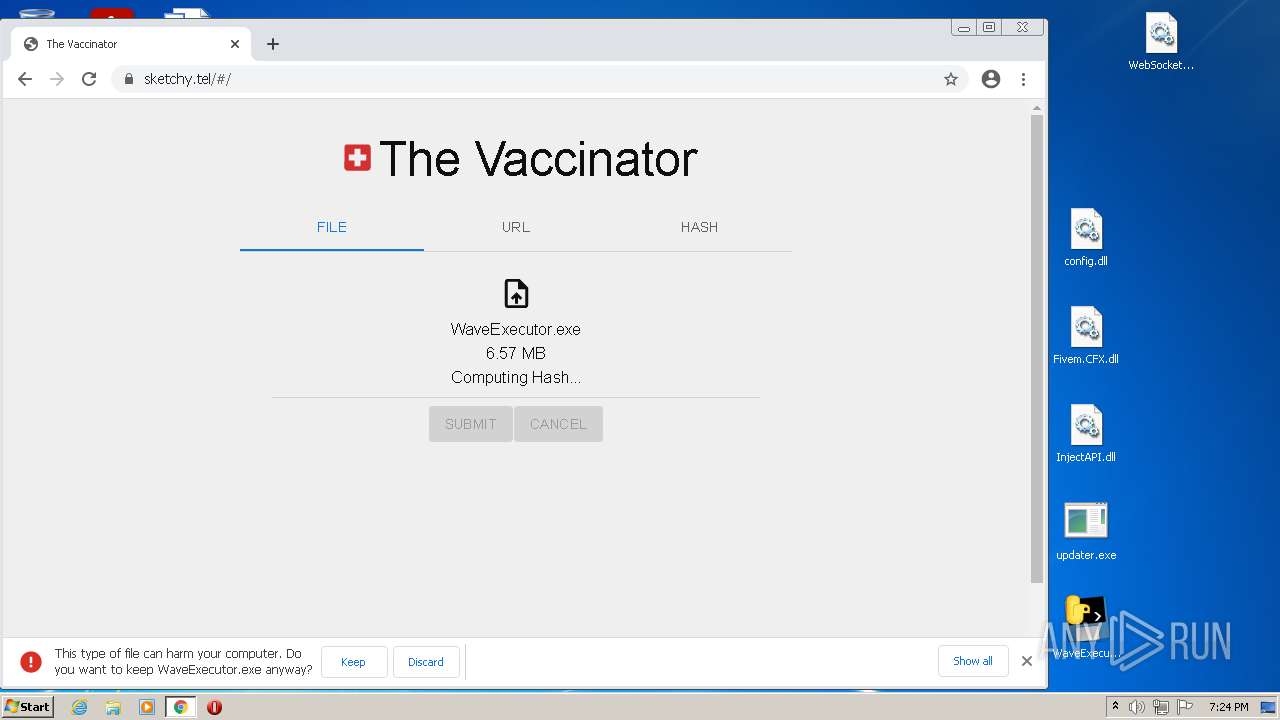
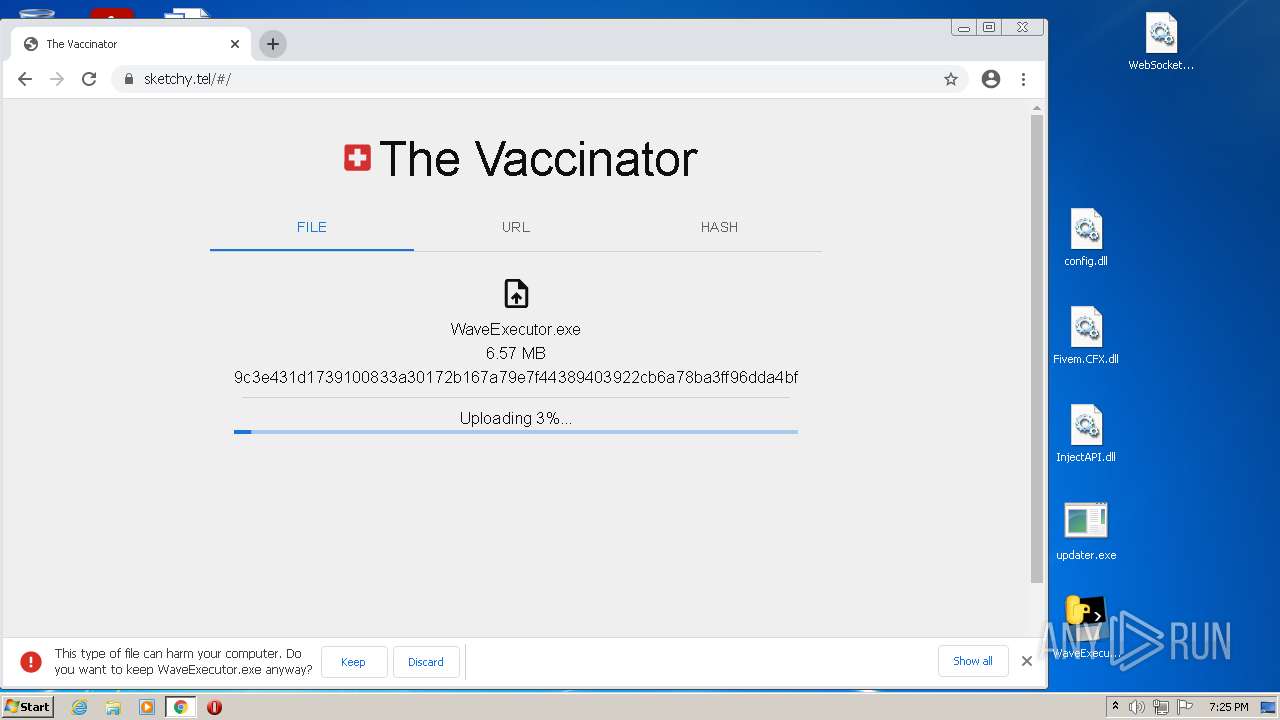
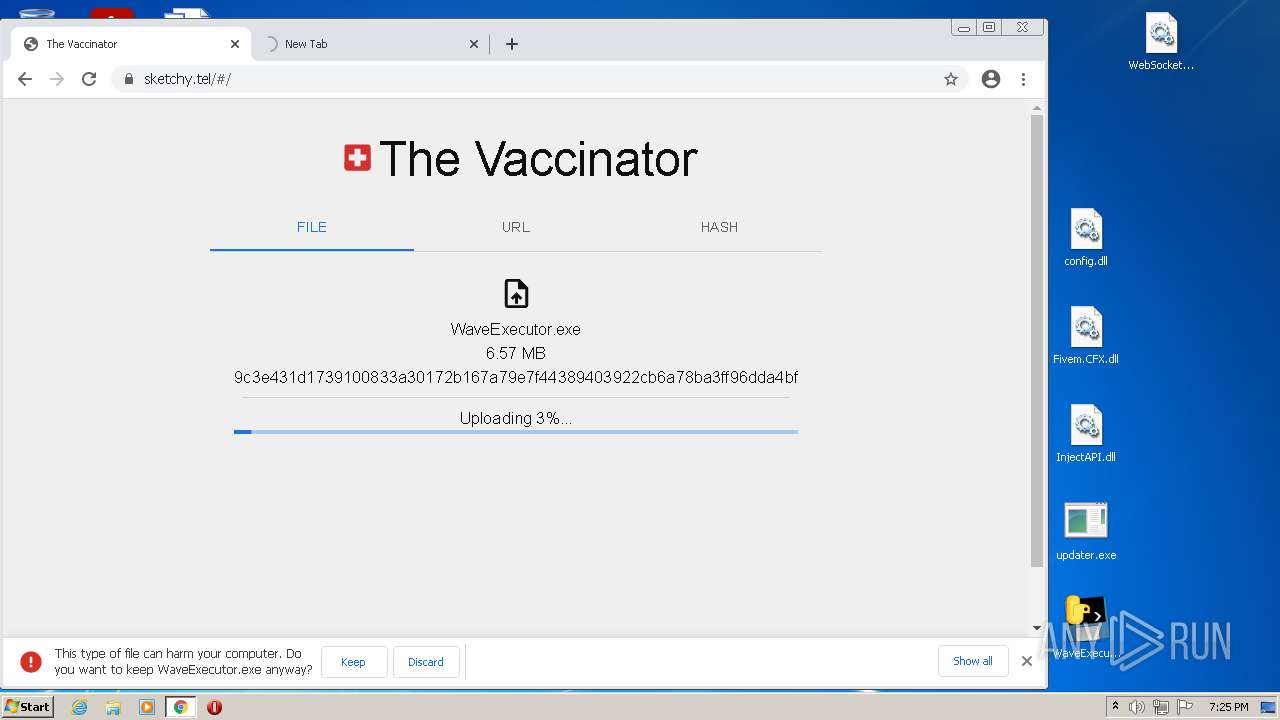
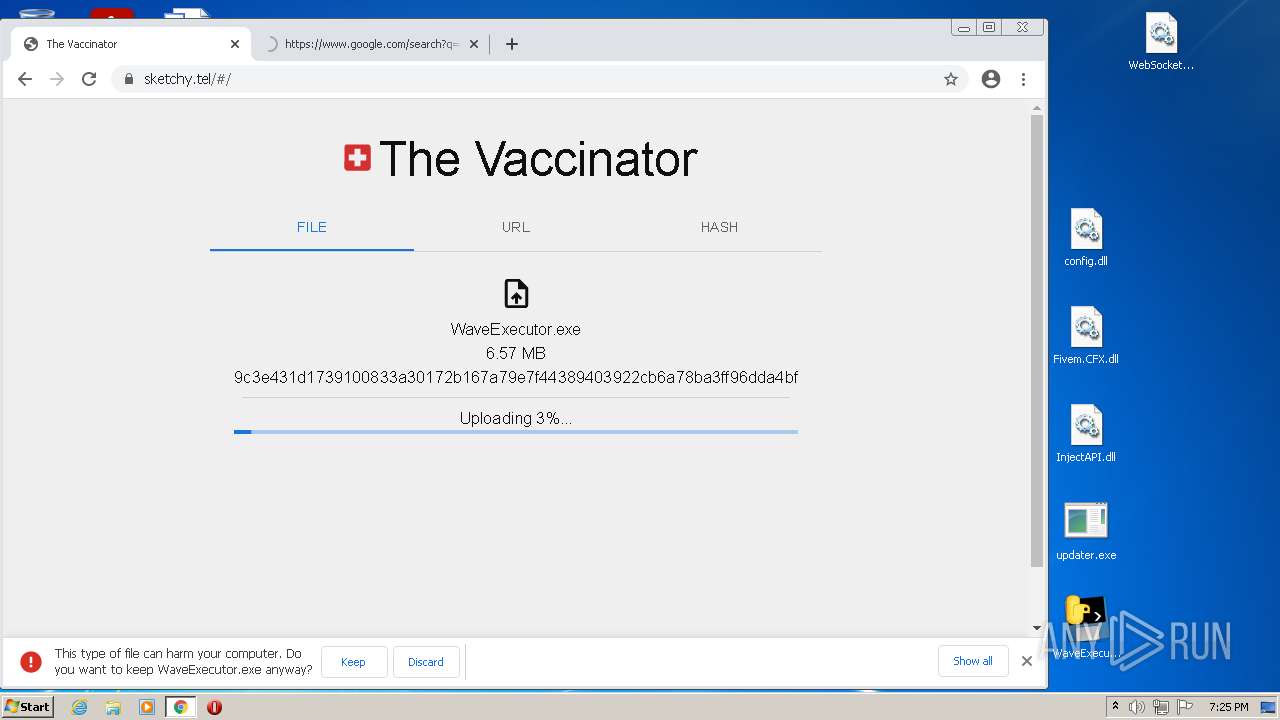
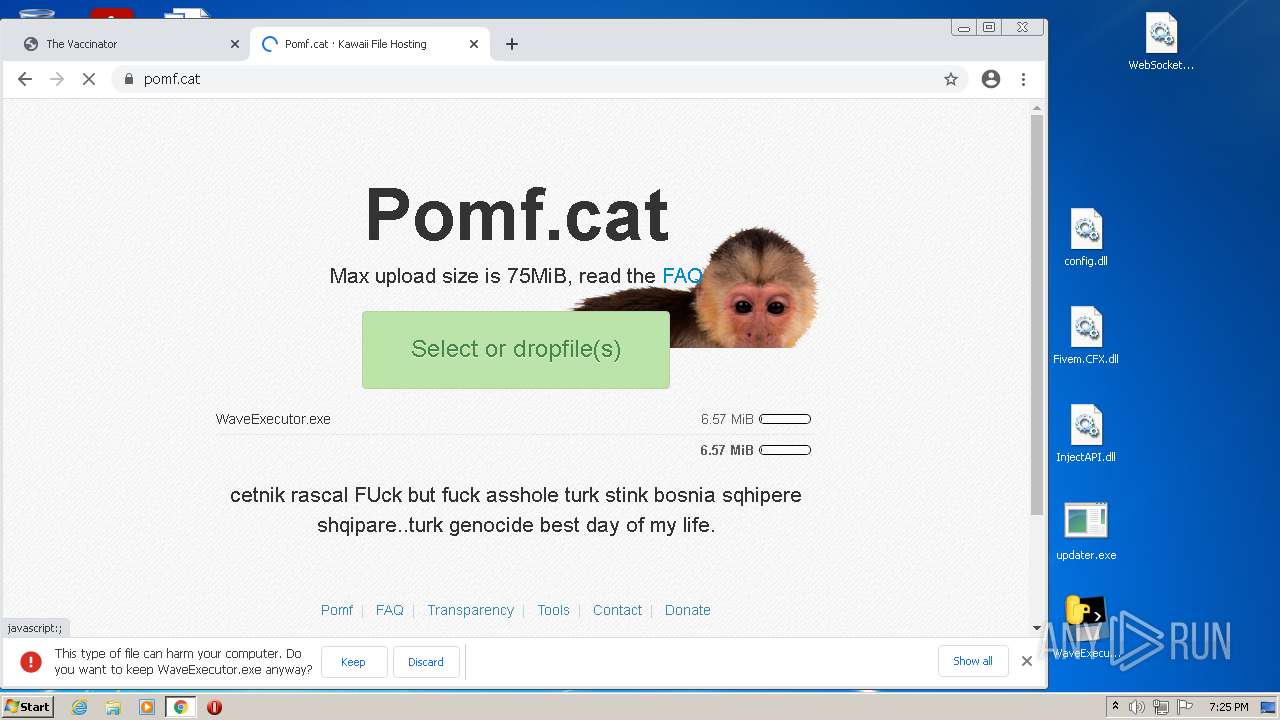
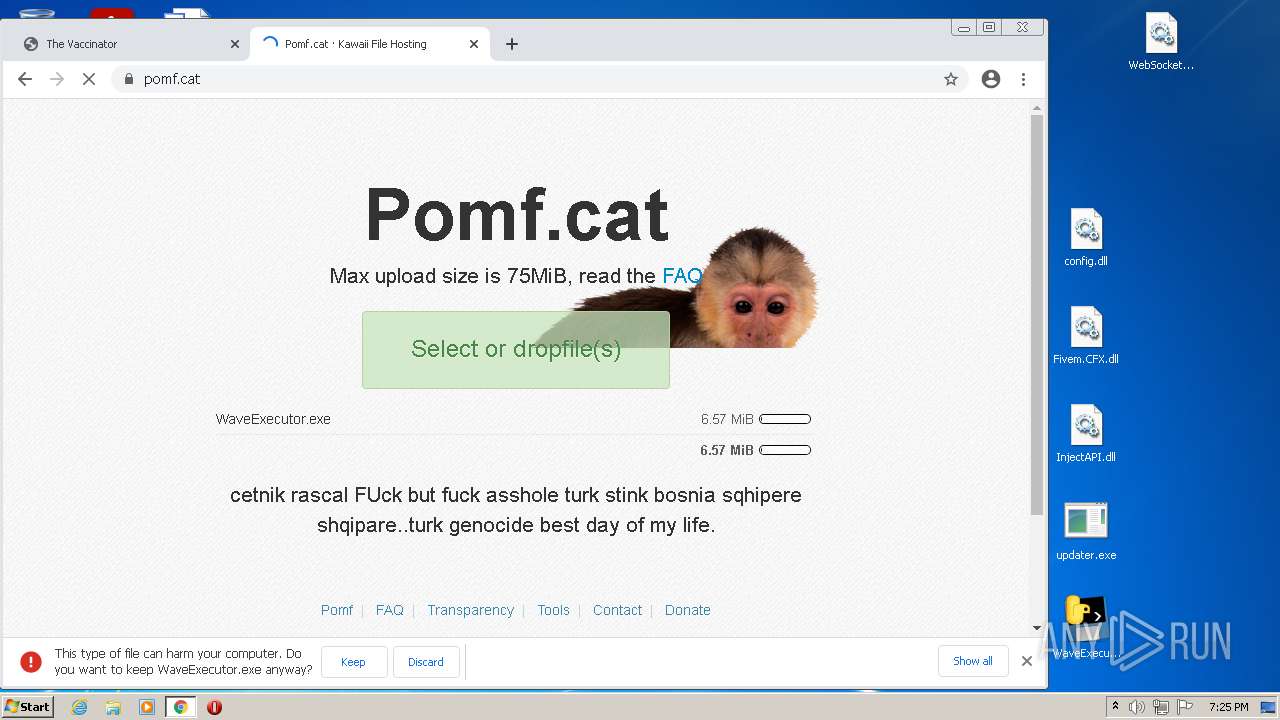
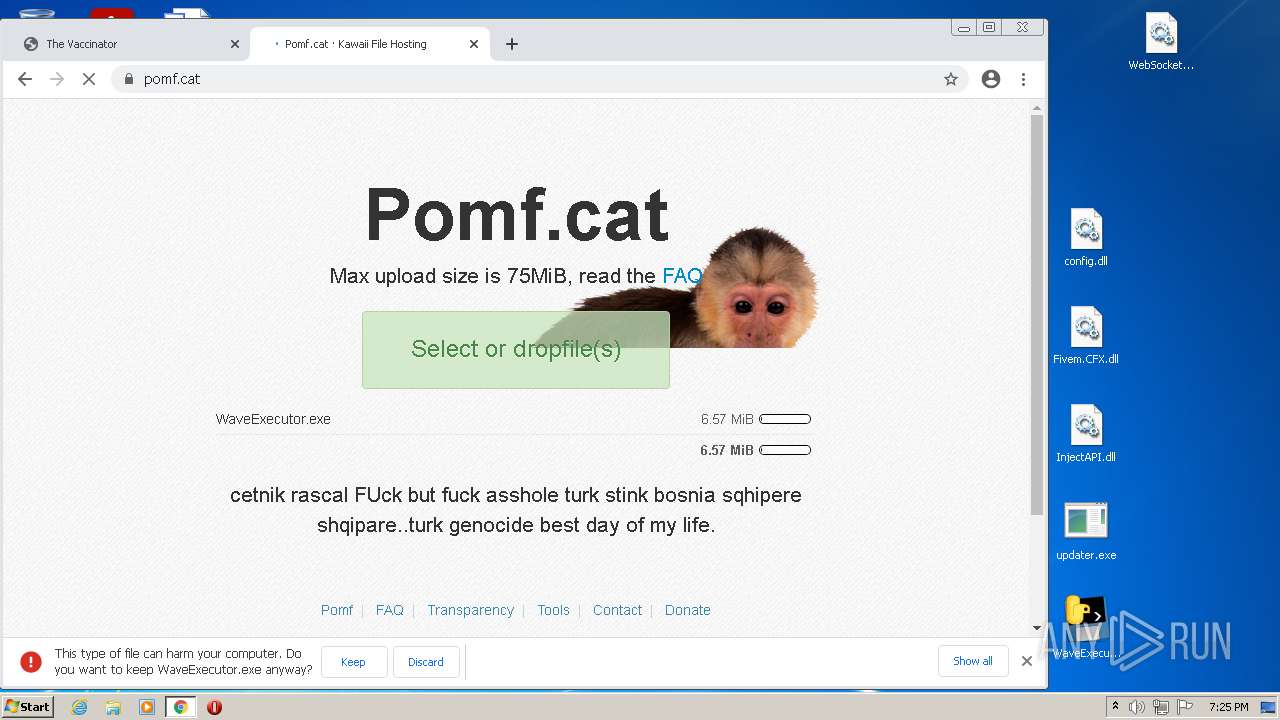
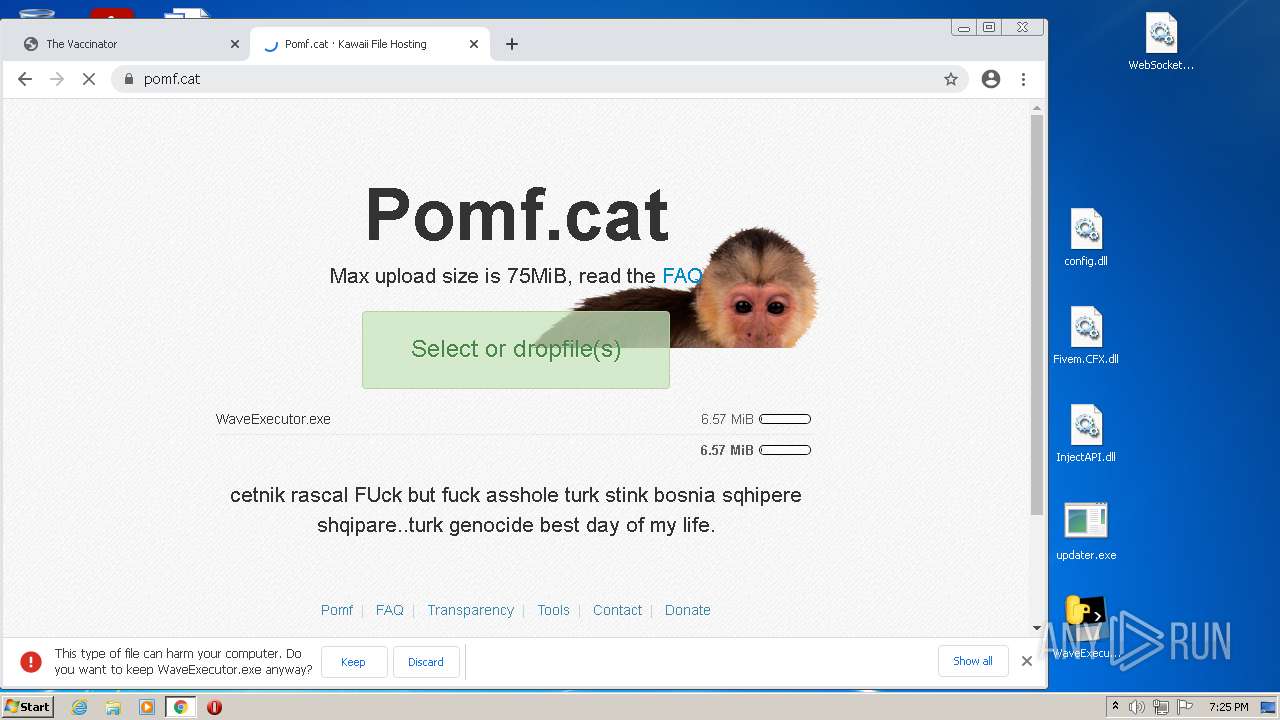
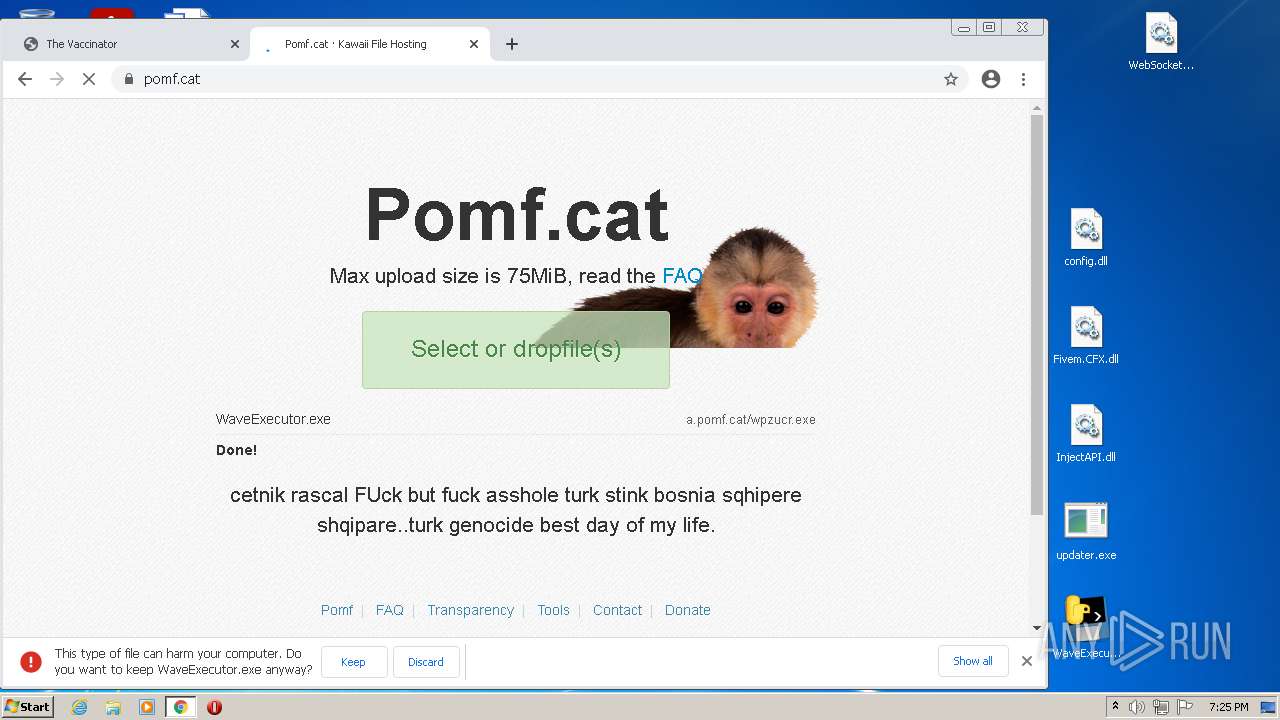
| ZipFileName: | WaveExecutor.exe |
|---|---|
| ZipUncompressedSize: | 6894019 |
| ZipCompressedSize: | 6745708 |
| ZipCRC: | 0x00ee0415 |
| ZipModifyDate: | 2021:04:09 21:19:12 |
| ZipCompression: | Deflated |
| ZipBitFlag: | - |
| ZipRequiredVersion: | 20 |
Total processes
107
Monitored processes
70
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1060,2610502973666087405,15808597835765422514,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3344 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 484 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1060,2610502973666087405,15808597835765422514,131072 --enable-features=PasswordImport --lang=en-US --instant-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1952 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 632 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Desktop\InjectAPI.dll | C:\Windows\system32\rundll32.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 888 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1060,2610502973666087405,15808597835765422514,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3048 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 964 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1060,2610502973666087405,15808597835765422514,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3044 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 984 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1060,2610502973666087405,15808597835765422514,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=544 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1104 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1060,2610502973666087405,15808597835765422514,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2424 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1160 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1060,2610502973666087405,15808597835765422514,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3968 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1160 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1060,2610502973666087405,15808597835765422514,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1804 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1228 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --field-trial-handle=1060,2610502973666087405,15808597835765422514,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3376 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
15 479
Read events
15 201
Write events
269
Delete events
9
Modification events
| (PID) Process: | (3116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3116) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\virtio_ivshmem_master_build.zip | |||
| (PID) Process: | (3116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\SPOILER_WaveExec_Updated.zip | |||
| (PID) Process: | (3116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3116) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
6
Suspicious files
127
Text files
131
Unknown types
9
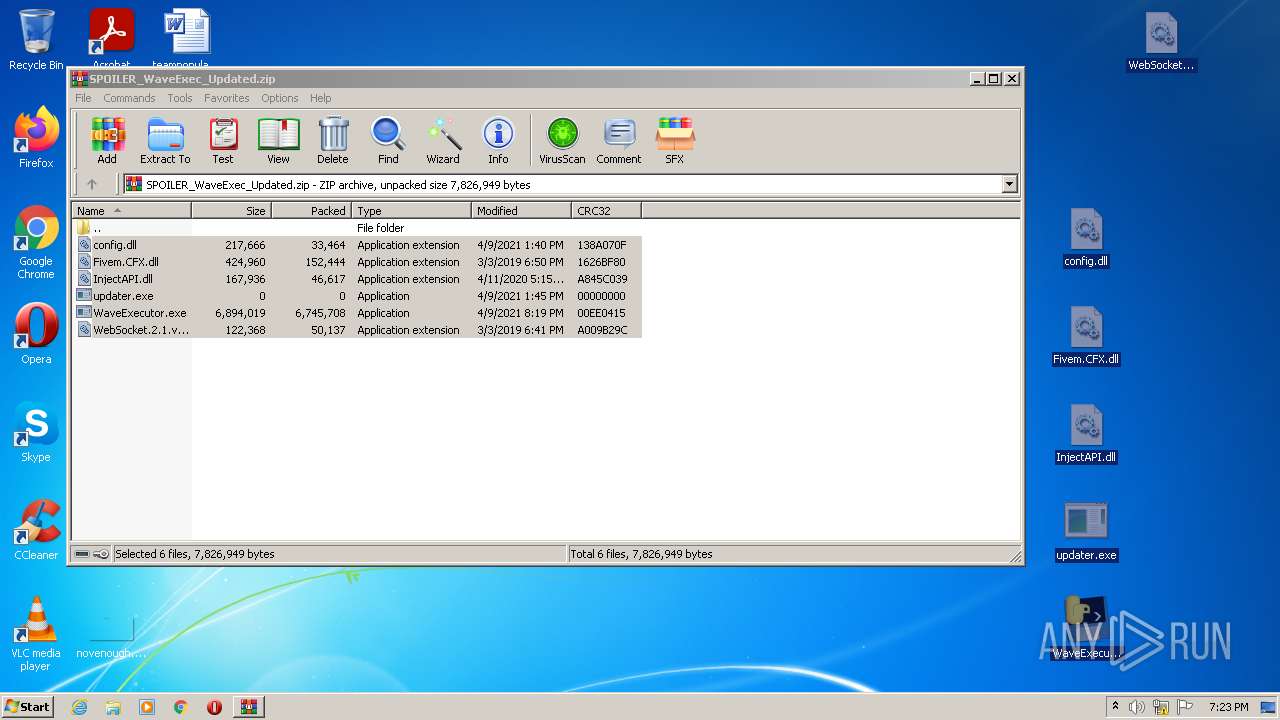
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-62F69AC5-5F4.pma | — | |
MD5:— | SHA256:— | |||
| 3116 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3116.28907\WaveExecutor.exe | executable | |
MD5:— | SHA256:— | |||
| 3116 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3116.28907\config.dll | text | |
MD5:— | SHA256:— | |||
| 3680 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cache\index | binary | |
MD5:— | SHA256:— | |||
| 3116 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3116.28907\WebSocket.2.1.version.dll | executable | |
MD5:D00FE9035E5936A65AD44D819CA7B392 | SHA256:F812A1DA84B579BE1032ACB06F13546220E1D26B79D9008659B5B4694353045D | |||
| 1524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | text | |
MD5:EF1D5606A483BB6C72C81A3F649BEB18 | SHA256:BA083E7585ADA9936944FE56BC0141A544F18A01C3424E5C9F02375B34FE3D45 | |||
| 3120 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 3680 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Cache\data_0 | vxd | |
MD5:CF89D16BB9107C631DAABF0C0EE58EFB | SHA256:D6A5FE39CD672781B256E0E3102F7022635F1D4BB7CFCC90A80FFFE4D0F3877E | |||
| 1524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RFdf4e0.TMP | text | |
MD5:B628564B8042F6E2CC2F53710AAECDC0 | SHA256:1D3B022BDEE9F48D79E3EC1E93F519036003642D3D72D10B05CFD47F43EFBF13 | |||
| 1524 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFdf2ad.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
45
DNS requests
21
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
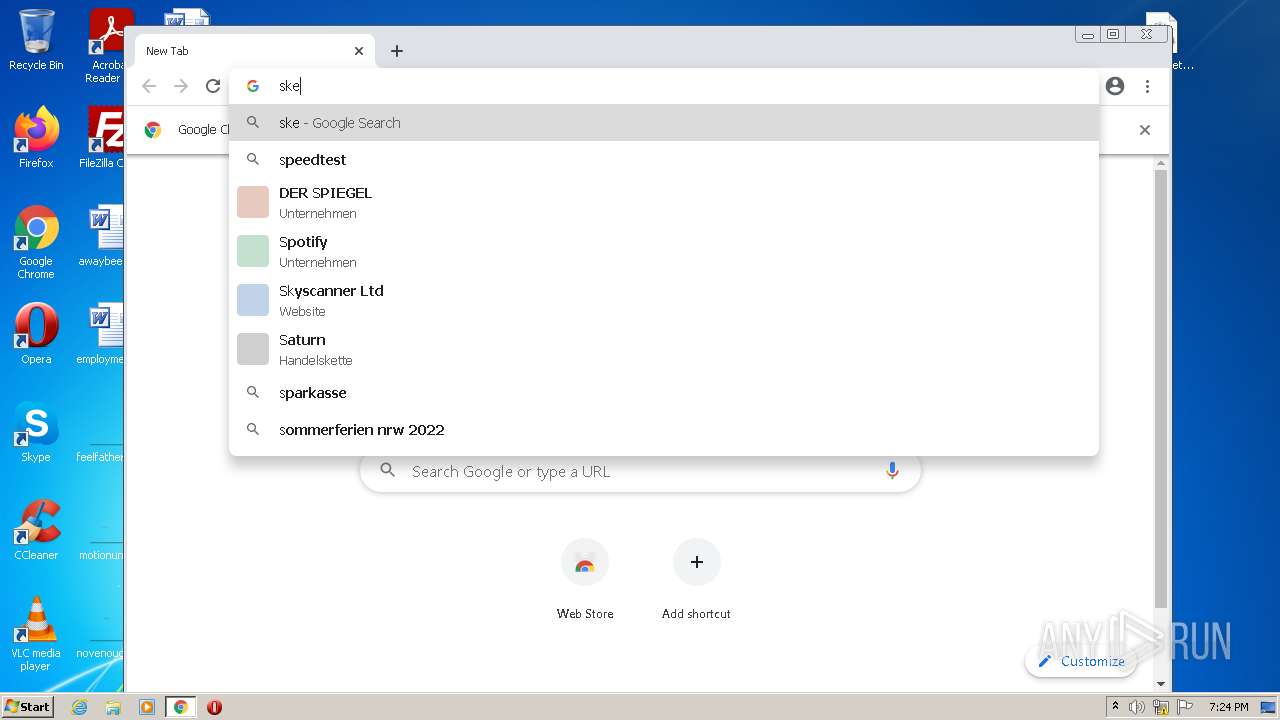
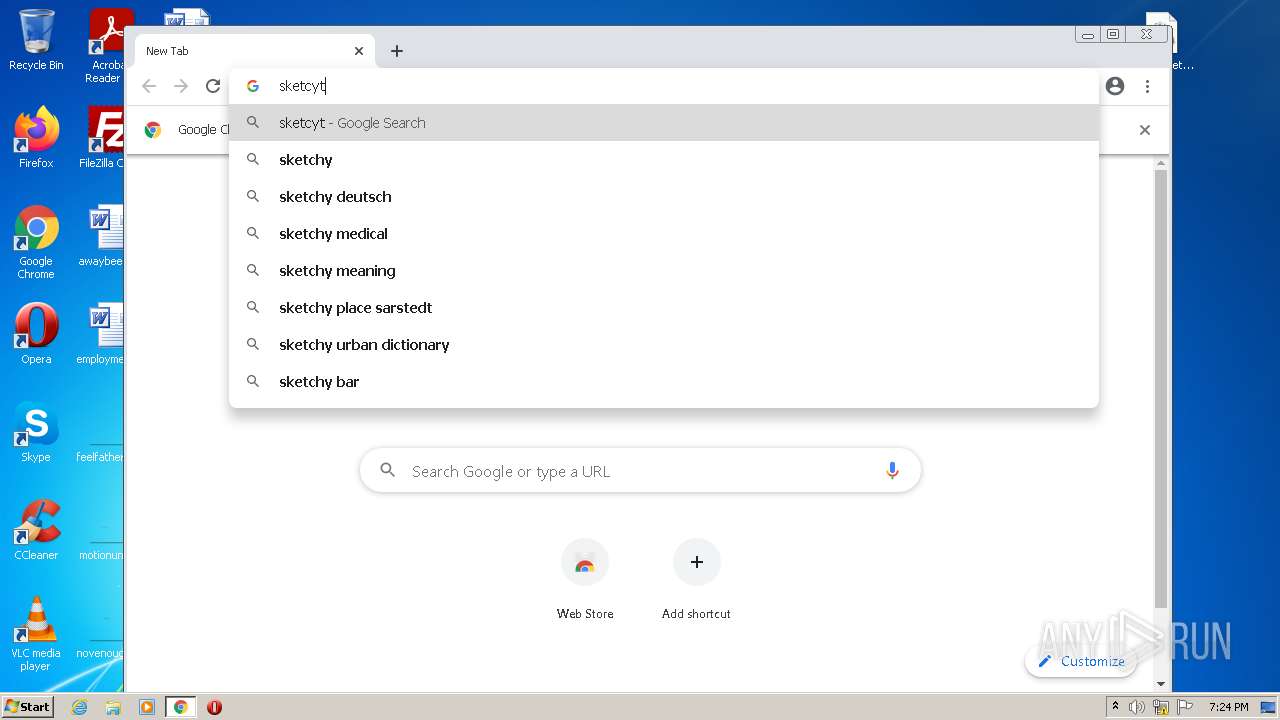
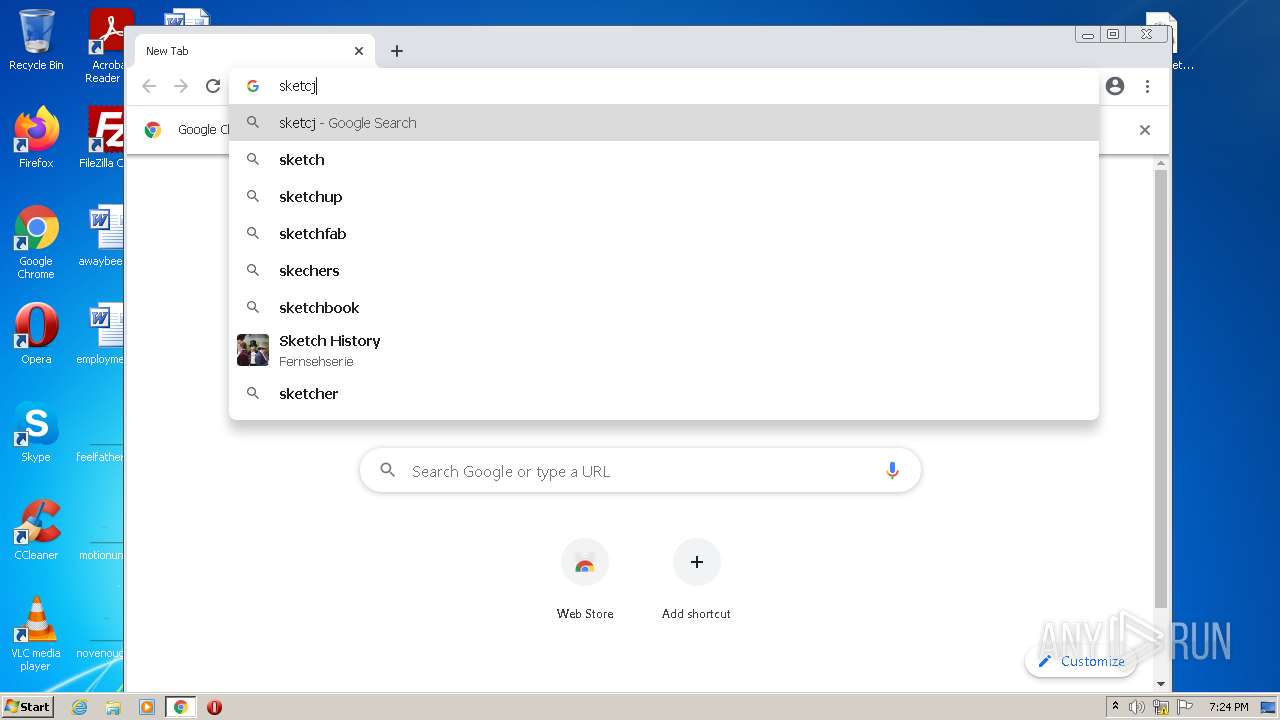
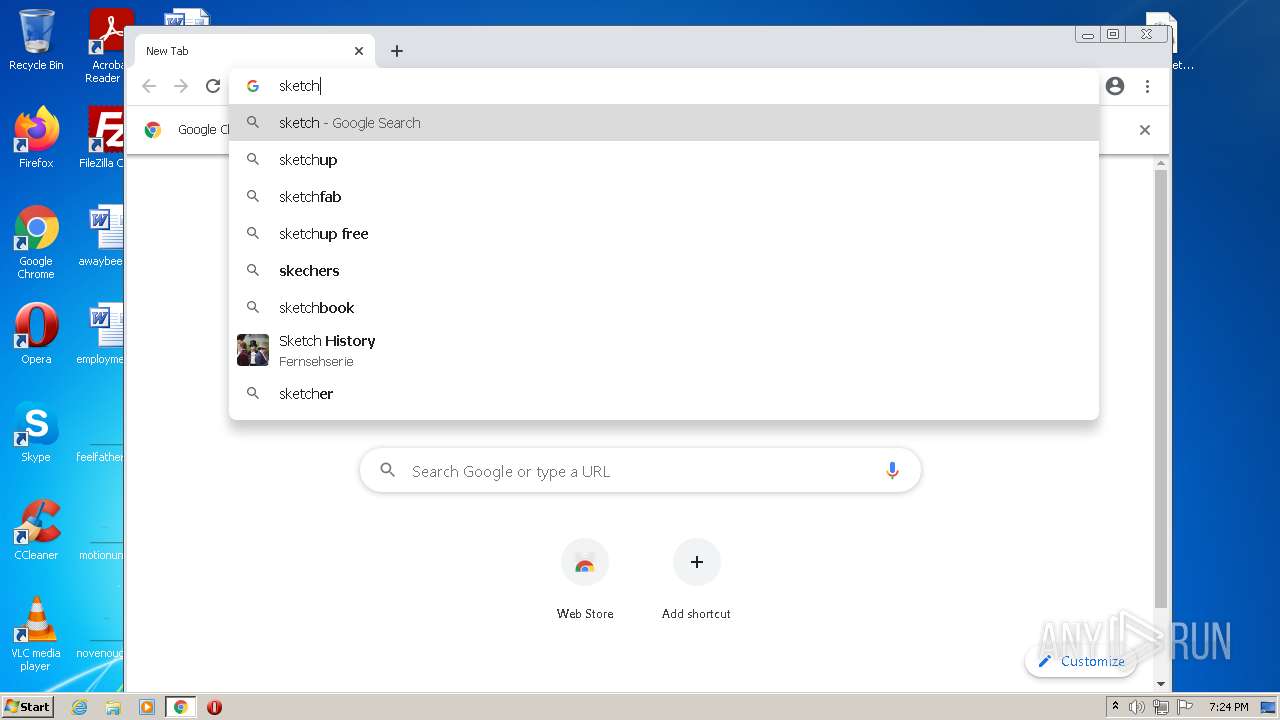
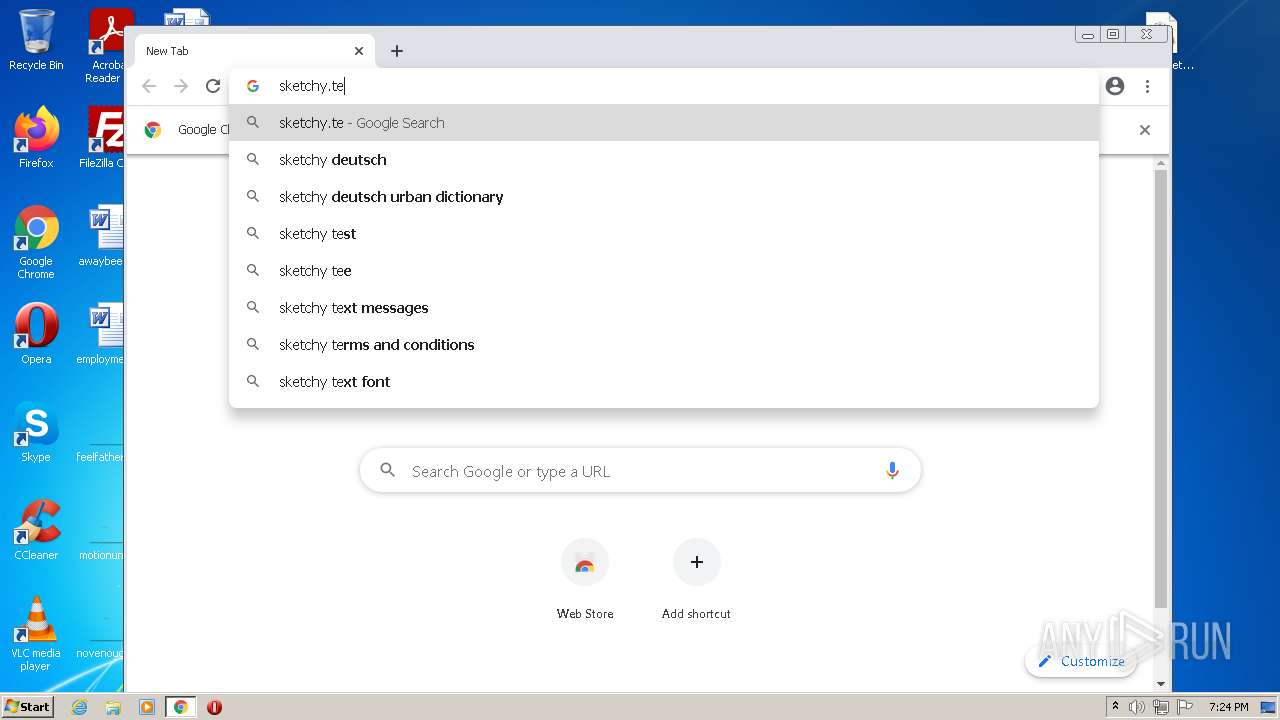
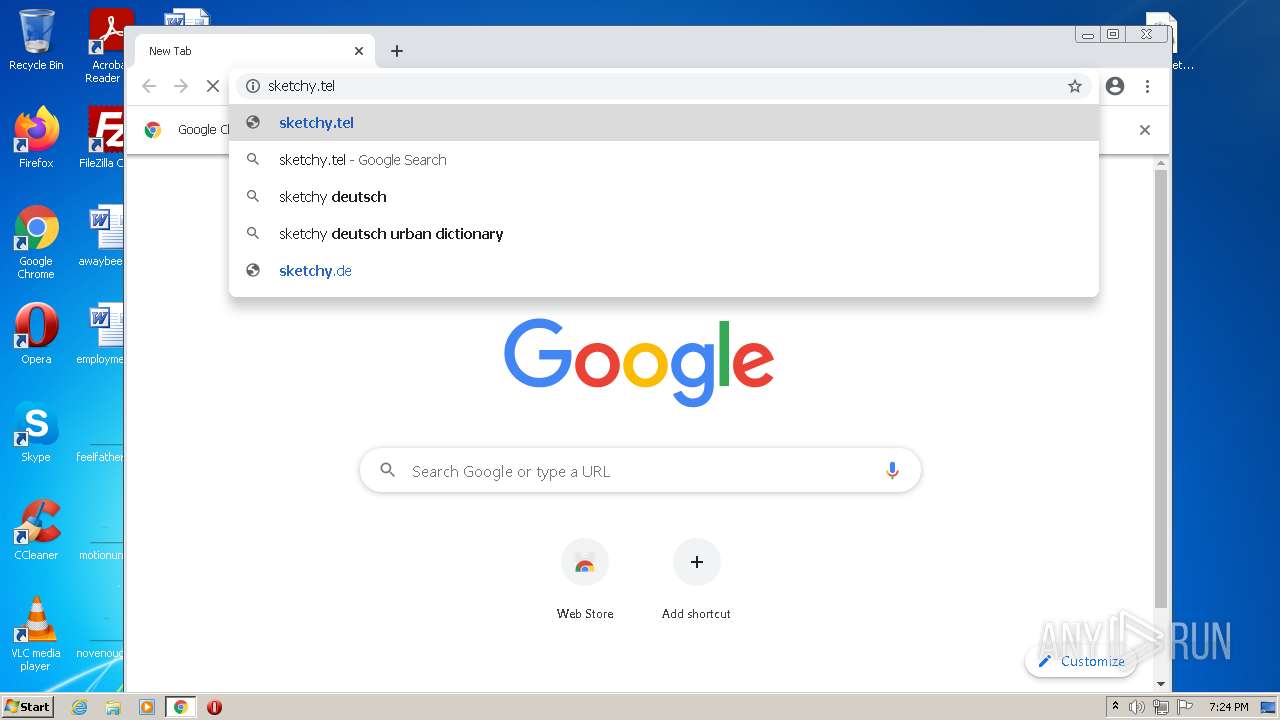
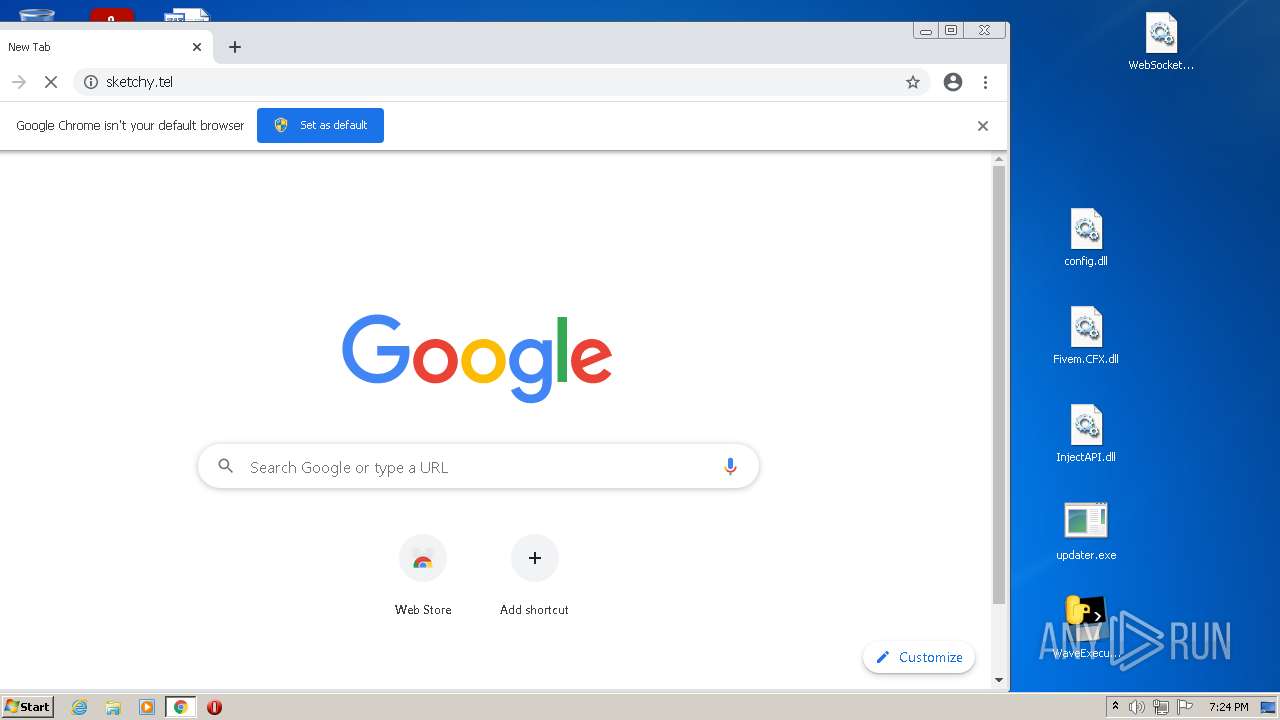
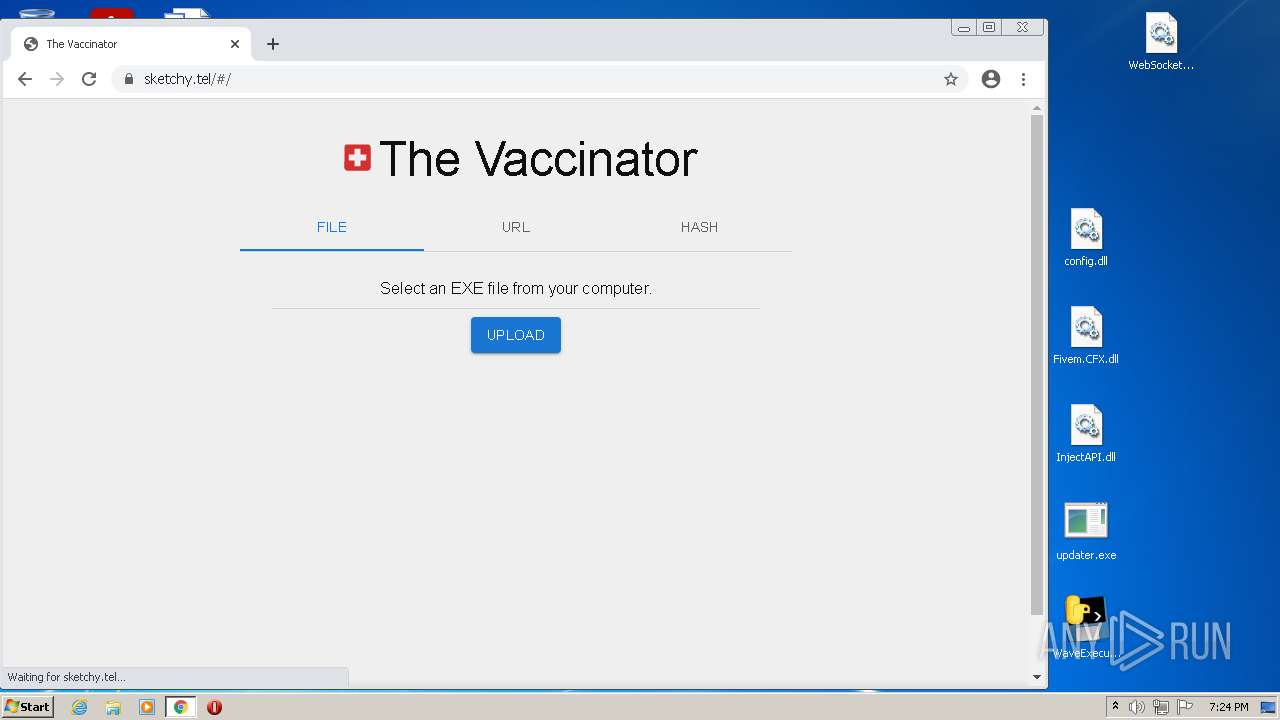
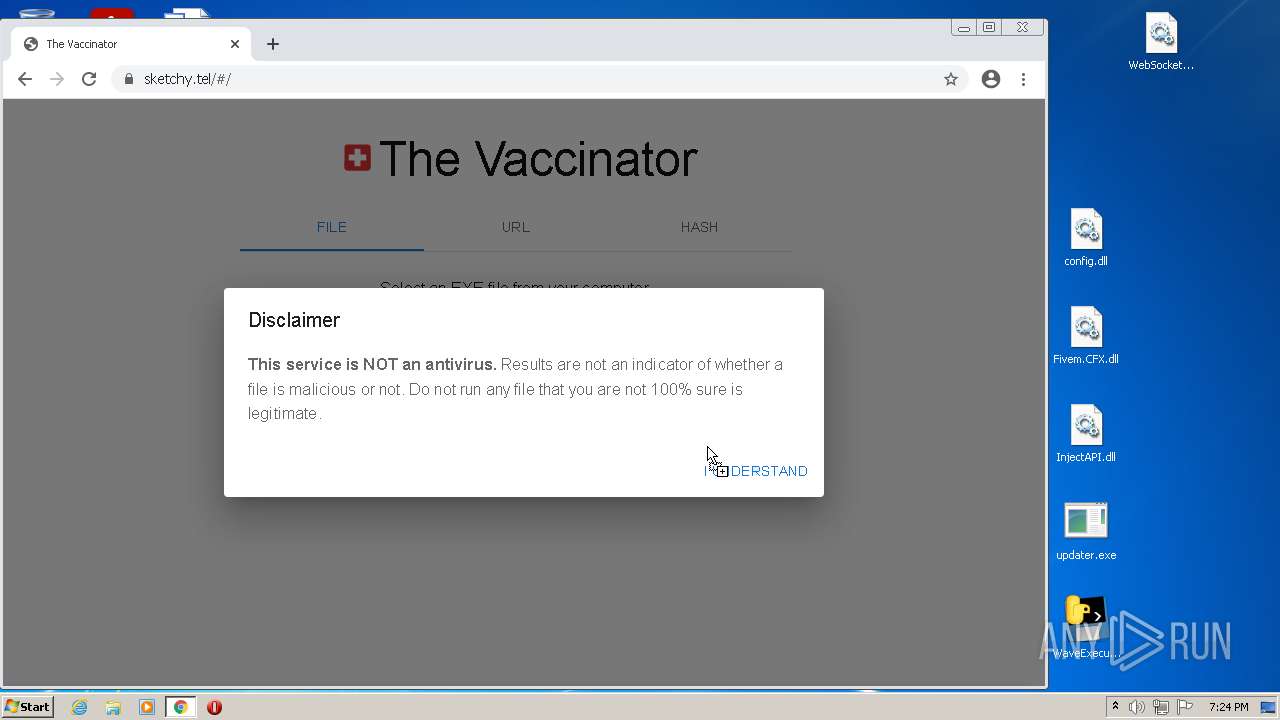
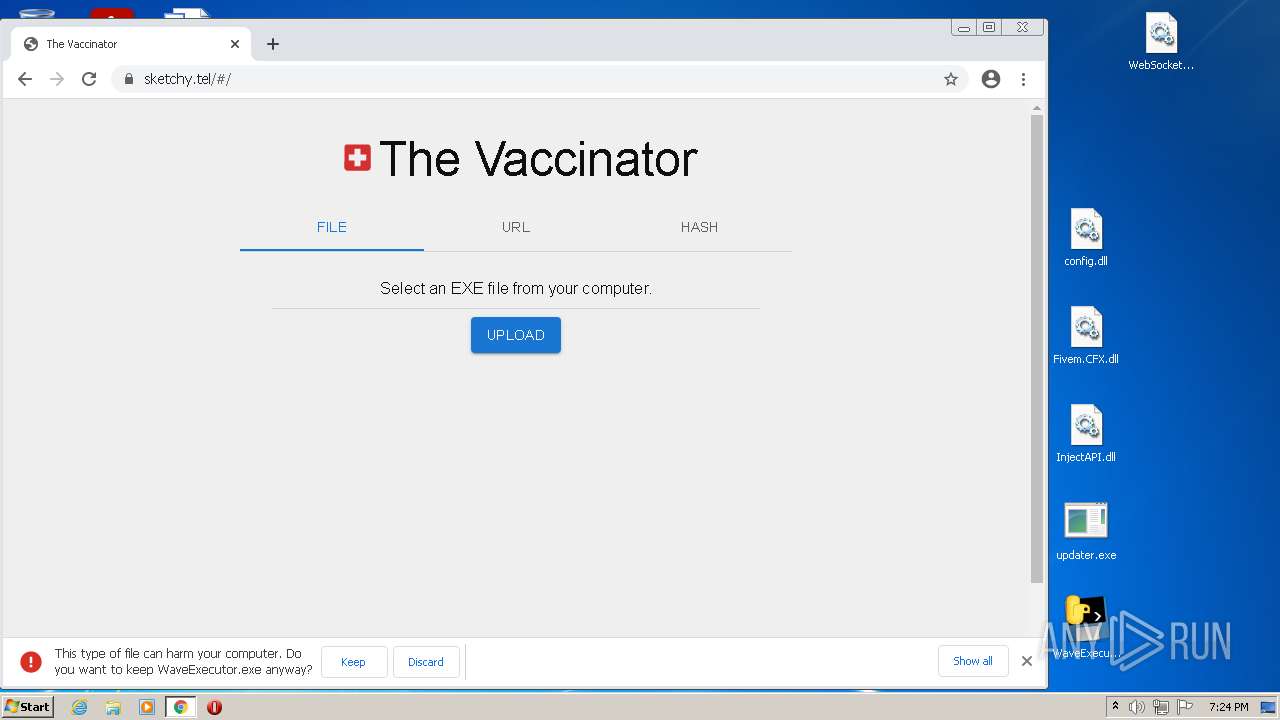
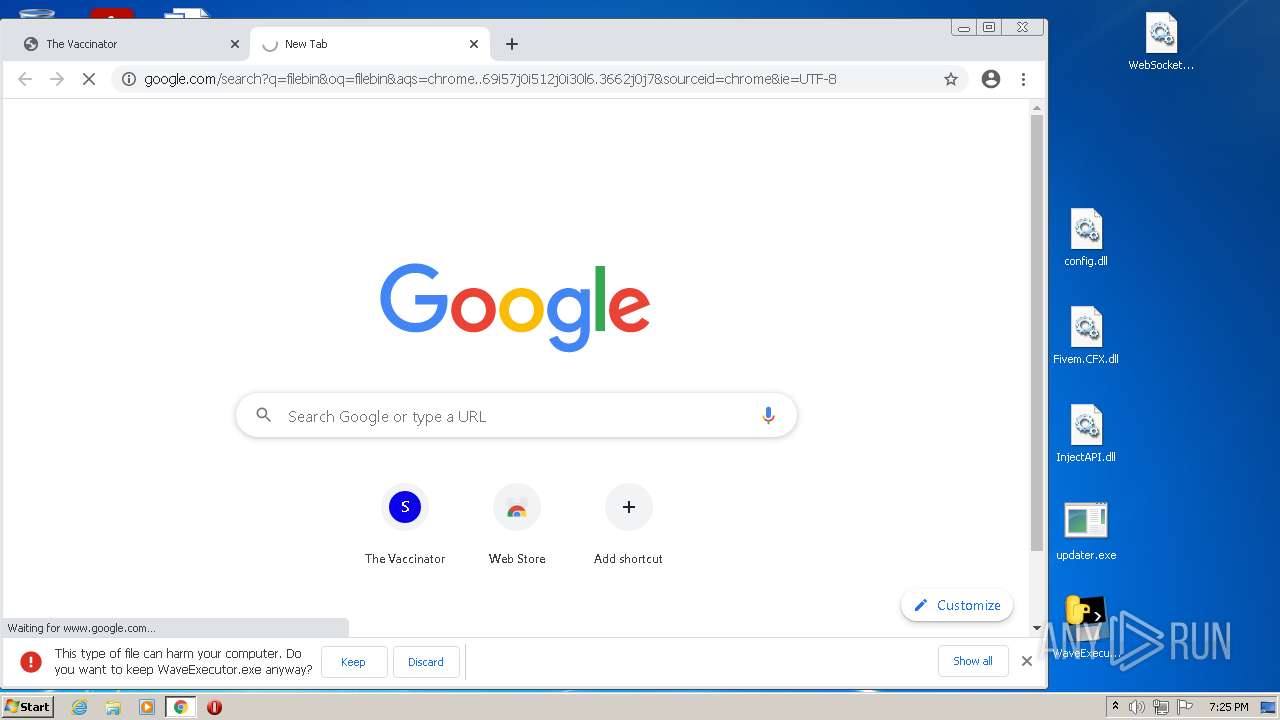
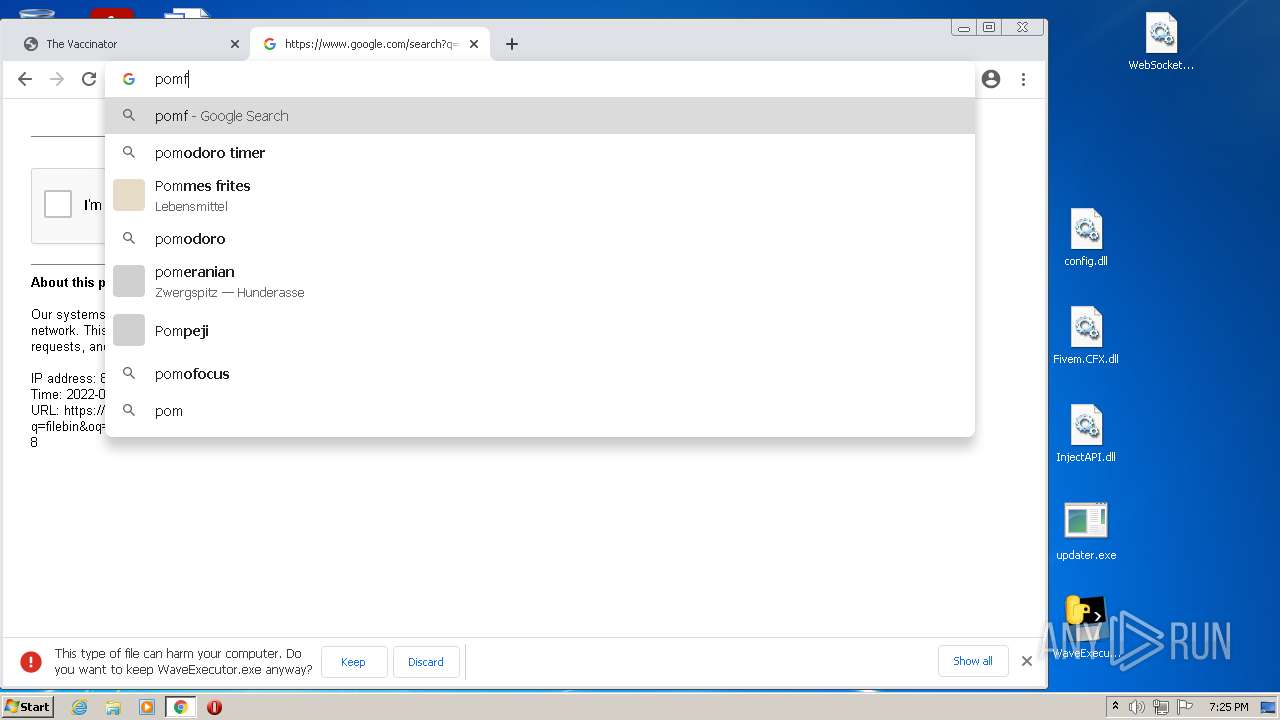
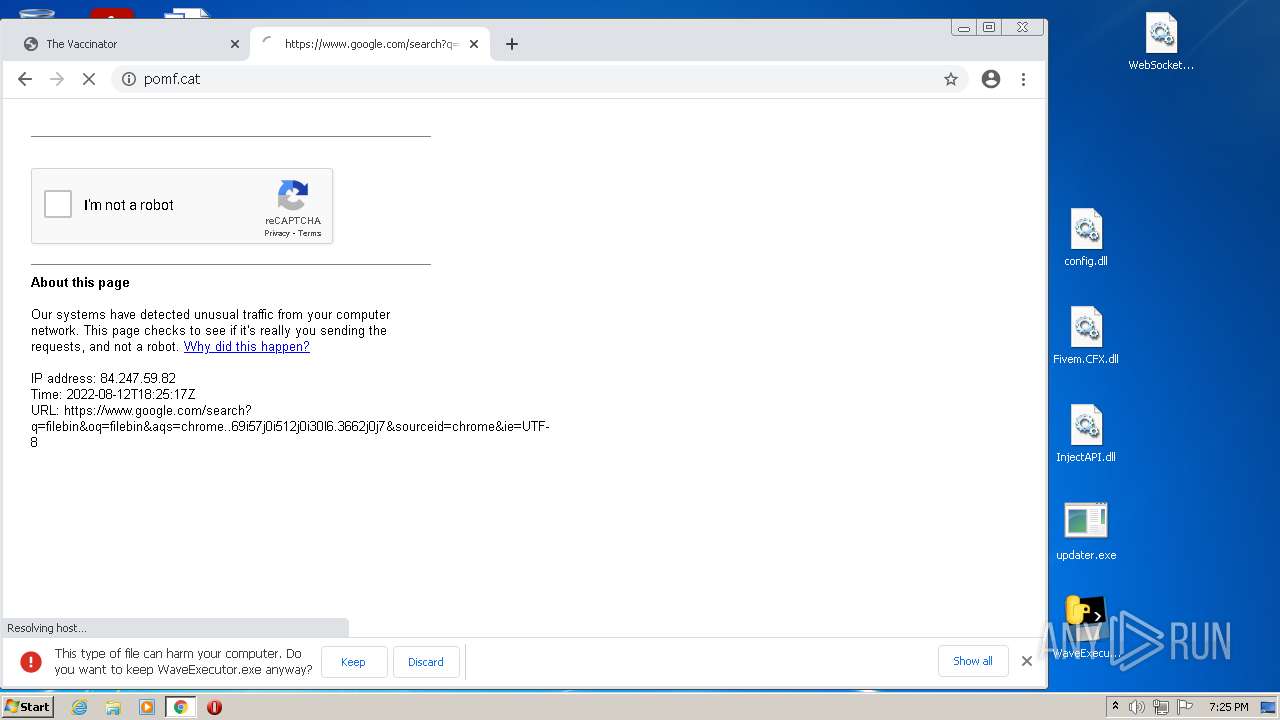
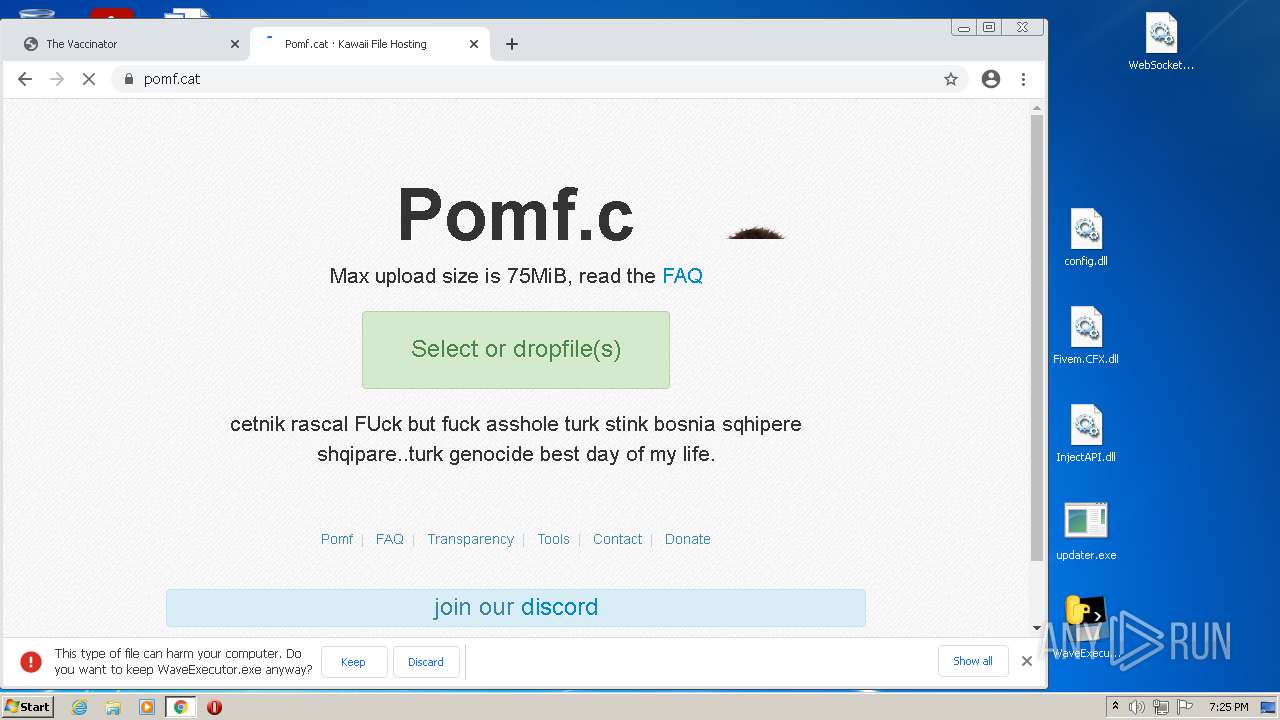
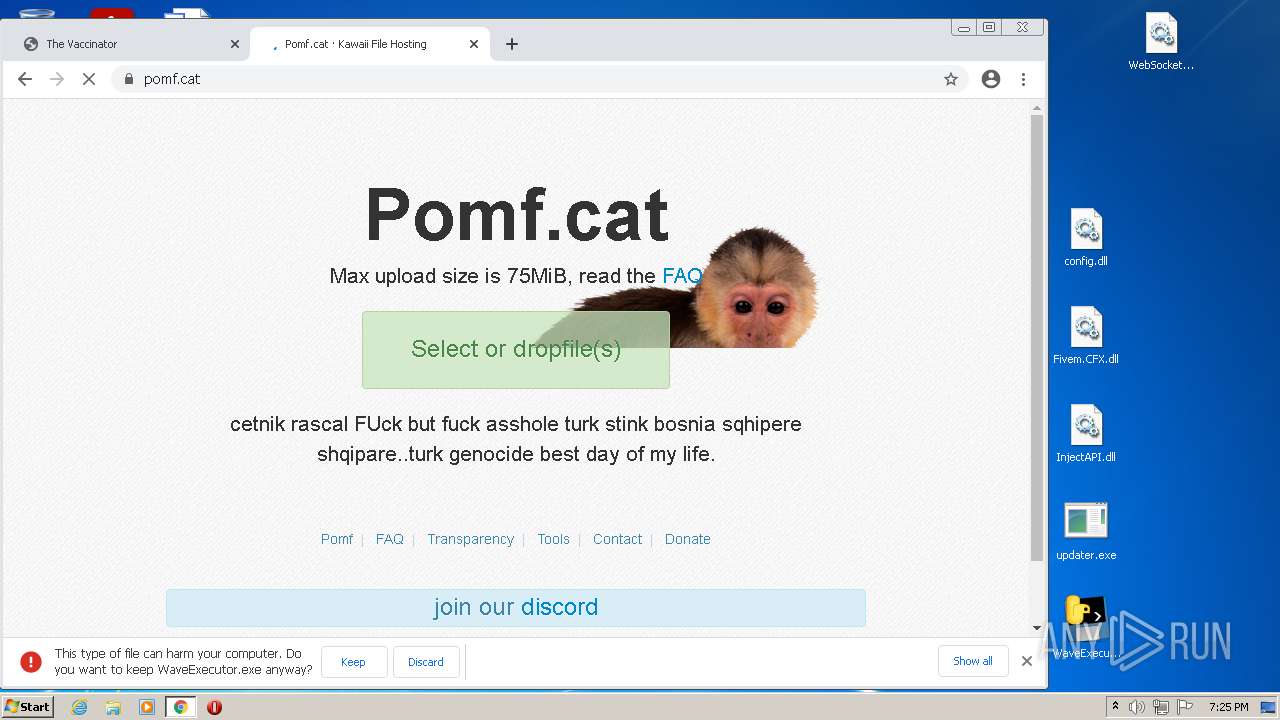
3680 | chrome.exe | GET | 301 | 104.21.2.49:80 | http://sketchy.tel/ | US | — | — | unknown |
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | — | — | whitelisted |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 53.3 Kb | whitelisted |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 9.68 Kb | whitelisted |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 43.5 Kb | whitelisted |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 14.7 Kb | whitelisted |
3680 | chrome.exe | GET | 200 | 8.248.137.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?0a325a35705c1f45 | US | compressed | 60.2 Kb | whitelisted |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 9.71 Kb | whitelisted |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 8.46 Kb | whitelisted |
856 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ac5q25btpqhkjhcekqoslcldvuya_1.3.36.141/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.141_win_ehzjmd5kjmert7jdgsrj4xqxj4.crx3 | US | binary | 5.64 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3680 | chrome.exe | 142.250.186.46:443 | clients2.google.com | Google Inc. | US | whitelisted |
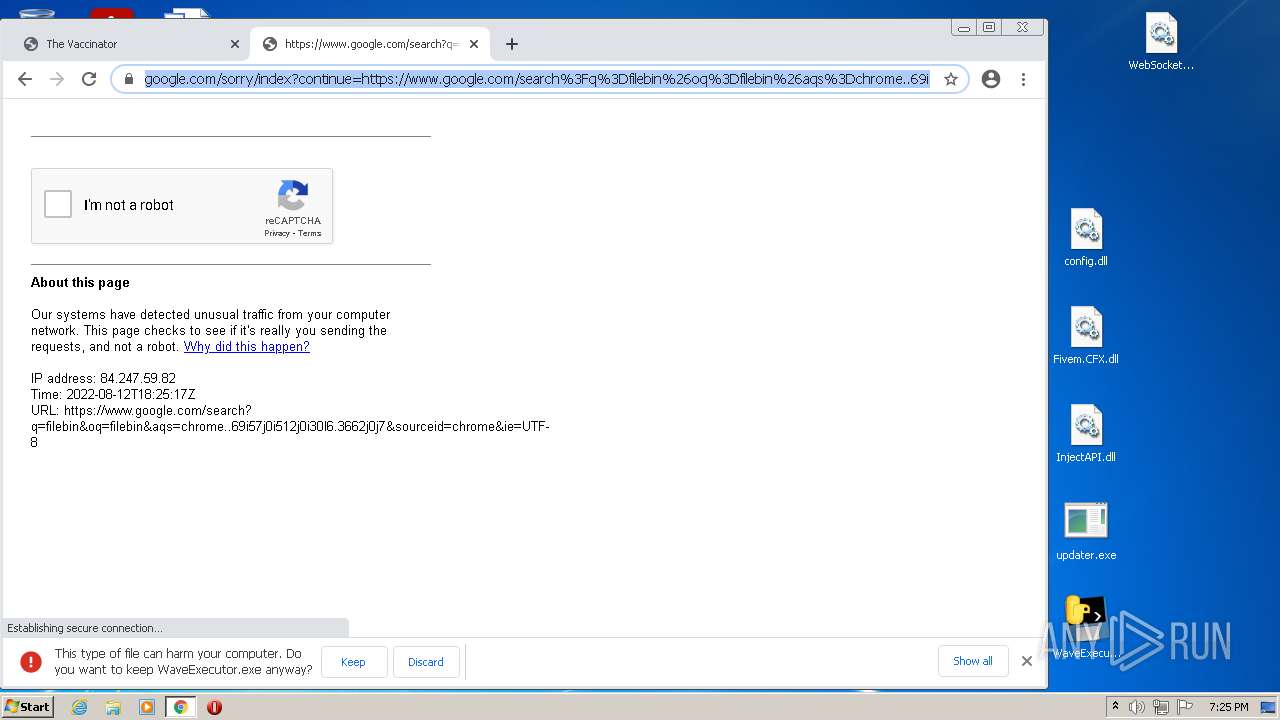
3680 | chrome.exe | 142.250.186.36:443 | www.google.com | Google Inc. | US | whitelisted |
3680 | chrome.exe | 142.250.185.110:443 | encrypted-tbn0.gstatic.com | Google Inc. | US | whitelisted |
3680 | chrome.exe | 142.250.184.227:443 | update.googleapis.com | Google Inc. | US | whitelisted |
3680 | chrome.exe | 142.250.185.109:443 | accounts.google.com | Google Inc. | US | suspicious |
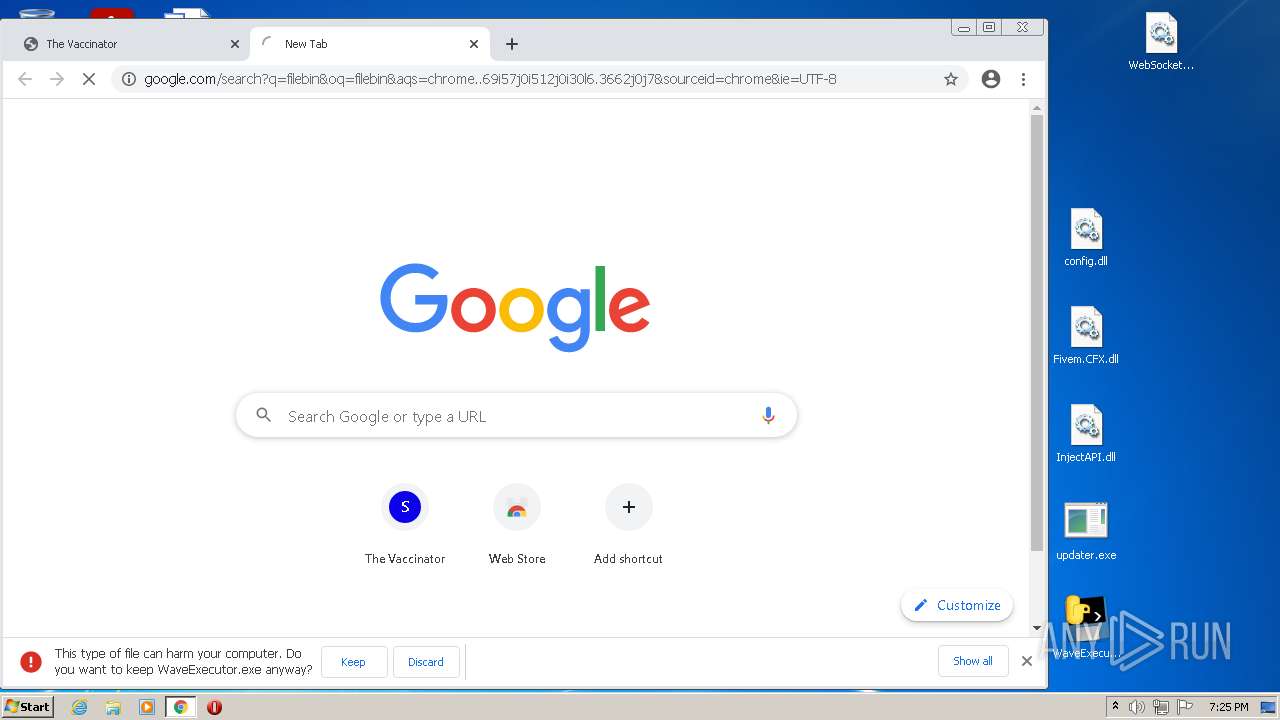
3680 | chrome.exe | 104.21.2.49:80 | sketchy.tel | Cloudflare Inc | US | unknown |
3680 | chrome.exe | 34.104.35.123:80 | edgedl.me.gvt1.com | — | US | whitelisted |
3680 | chrome.exe | 142.250.185.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3680 | chrome.exe | 142.250.185.97:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
3680 | chrome.exe | 172.217.18.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| malicious |
clients2.google.com |
| whitelisted |
accounts.google.com |
| shared |
clients2.googleusercontent.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
encrypted-tbn0.gstatic.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
sketchy.tel |
| unknown |
update.googleapis.com |
| whitelisted |
edgedl.me.gvt1.com |
| whitelisted |