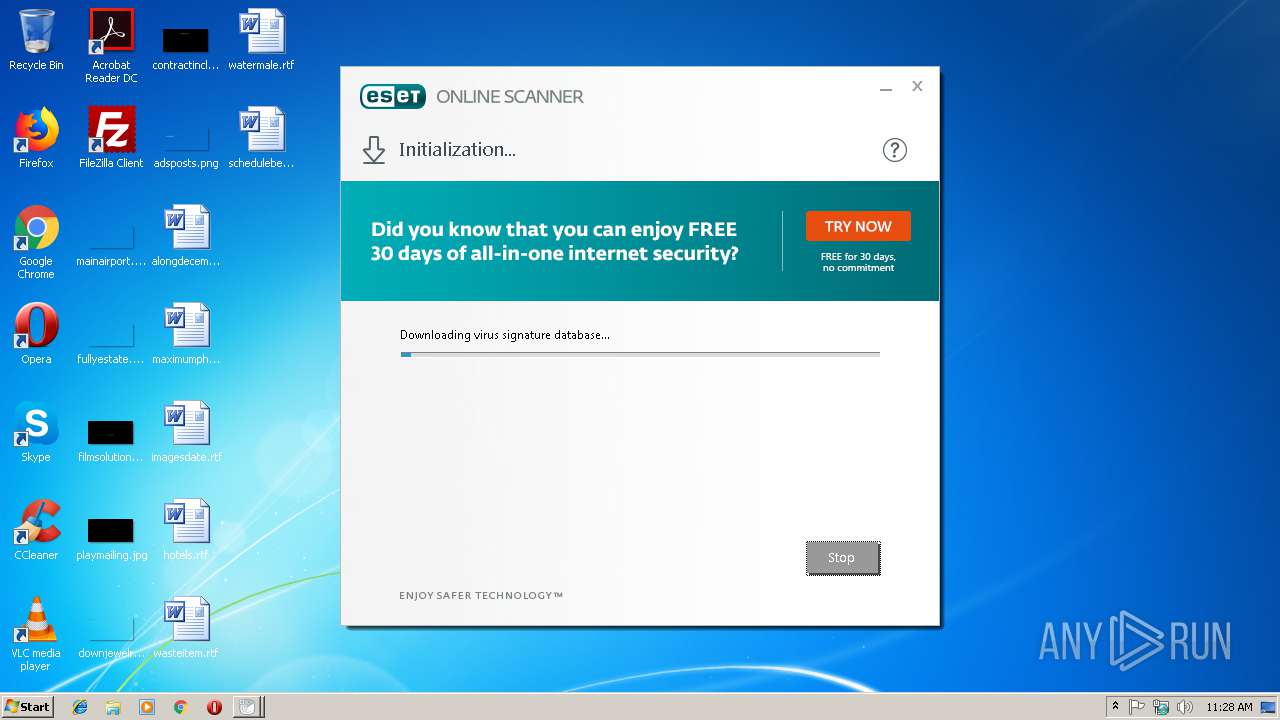
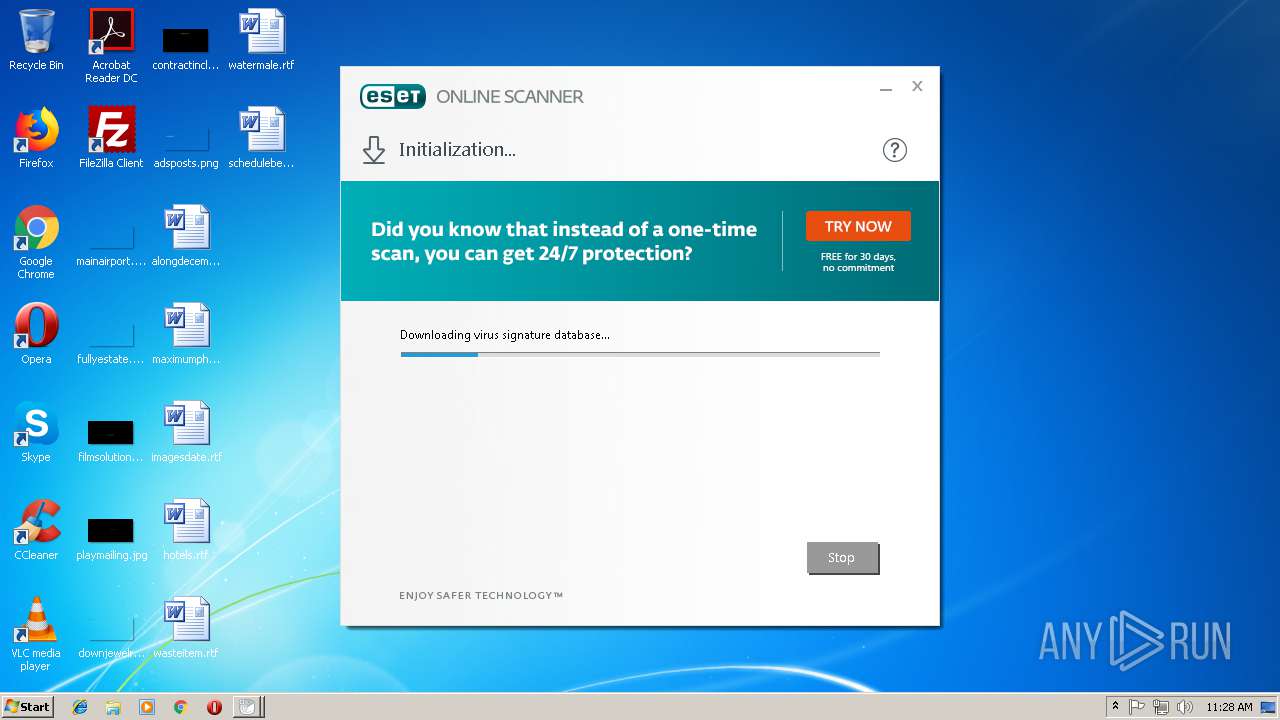
| download: | esetonlinescanner_enu.exe |
| Full analysis: | https://app.any.run/tasks/7f233c8b-881f-442f-93d5-7a2f152880df |
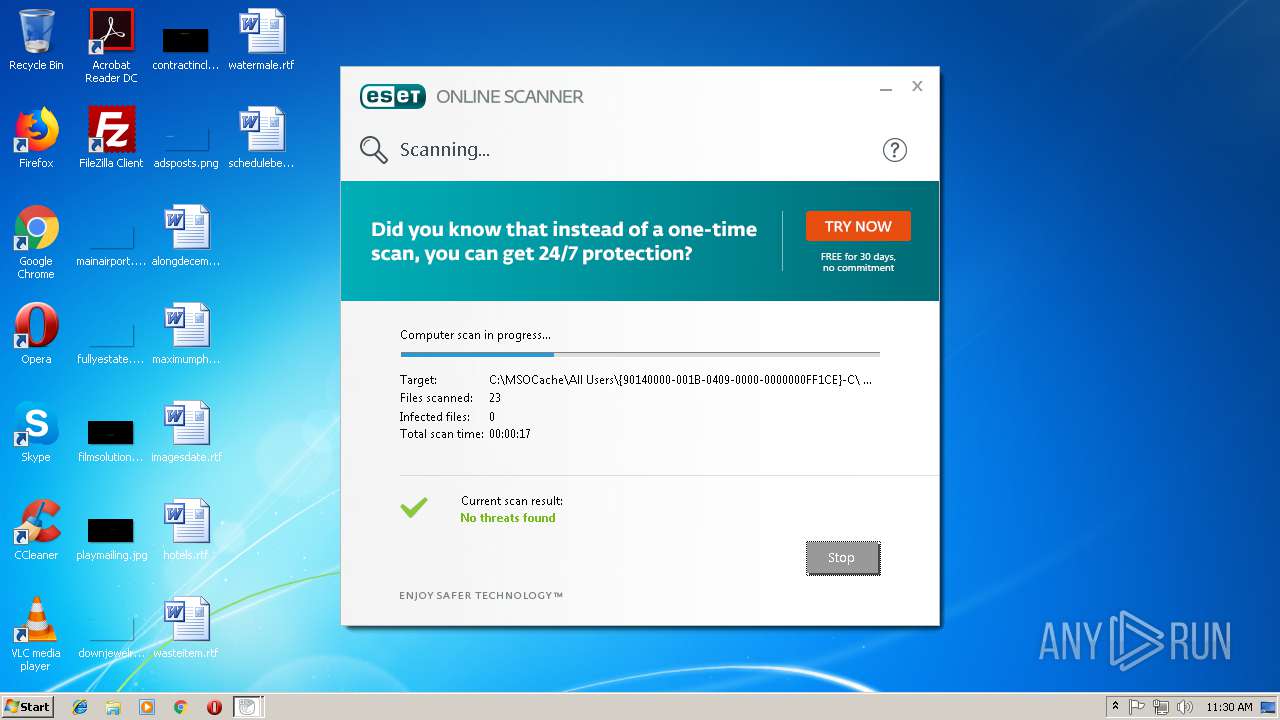
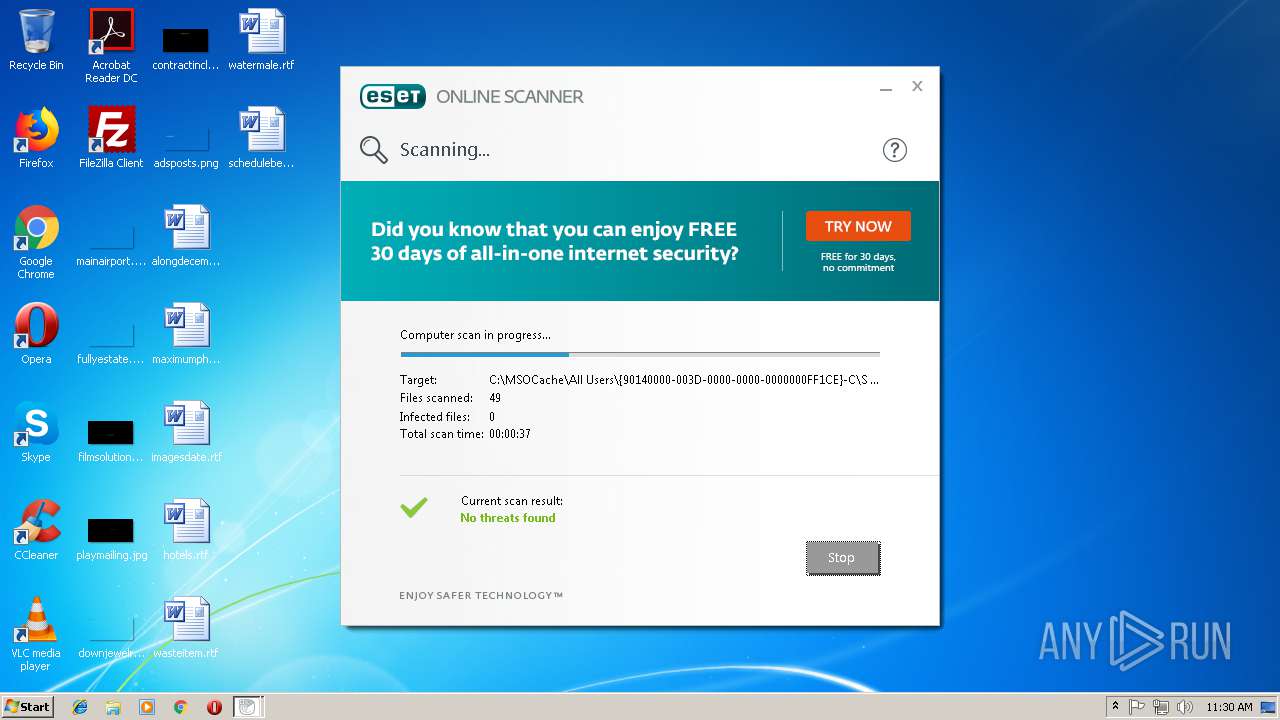
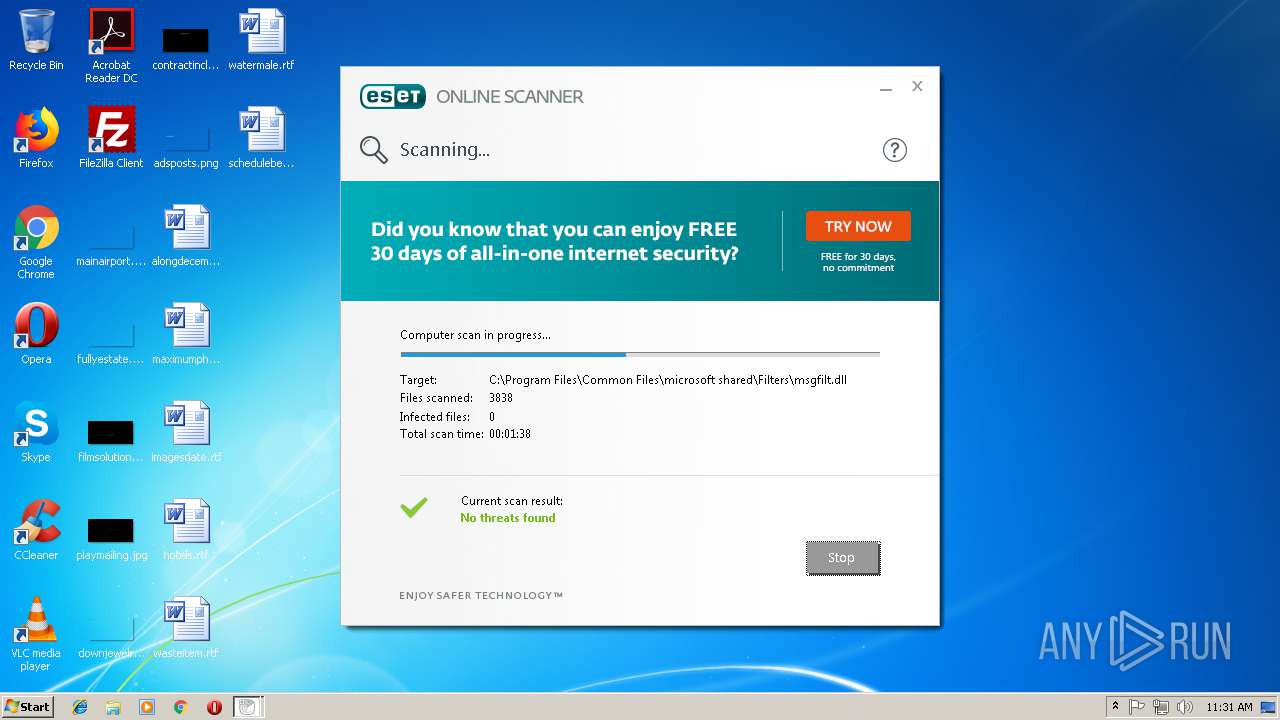
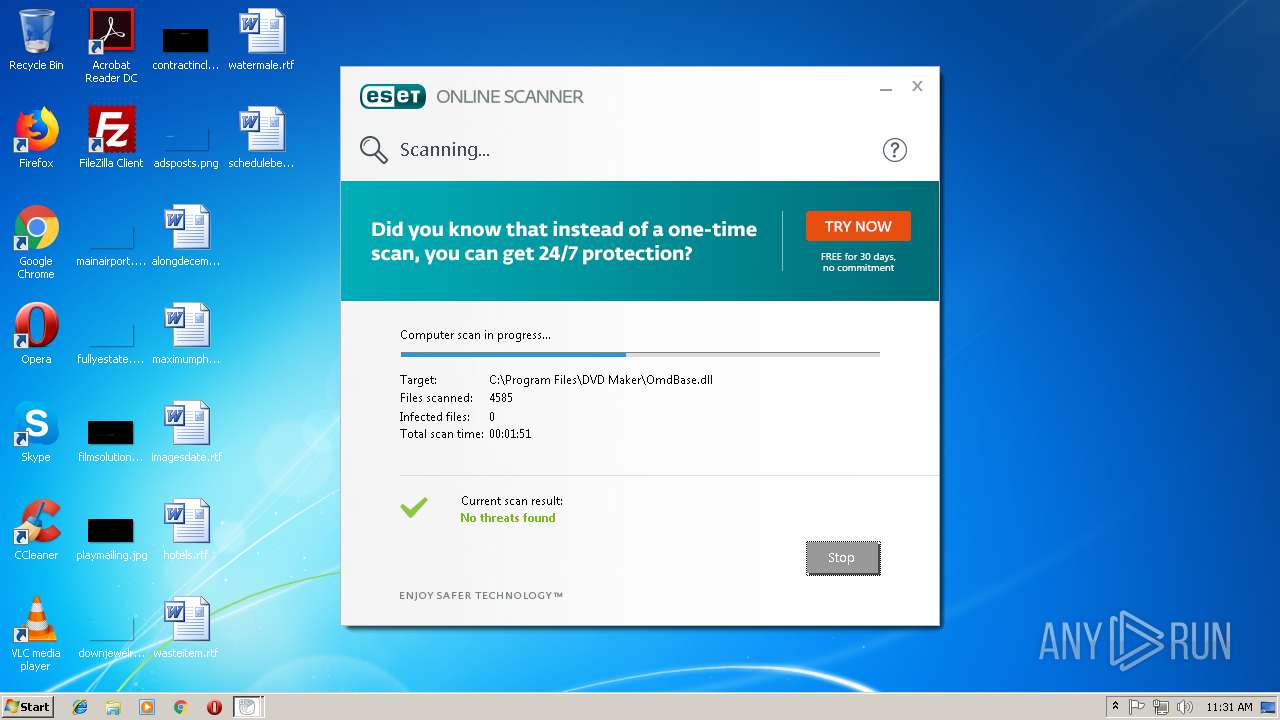
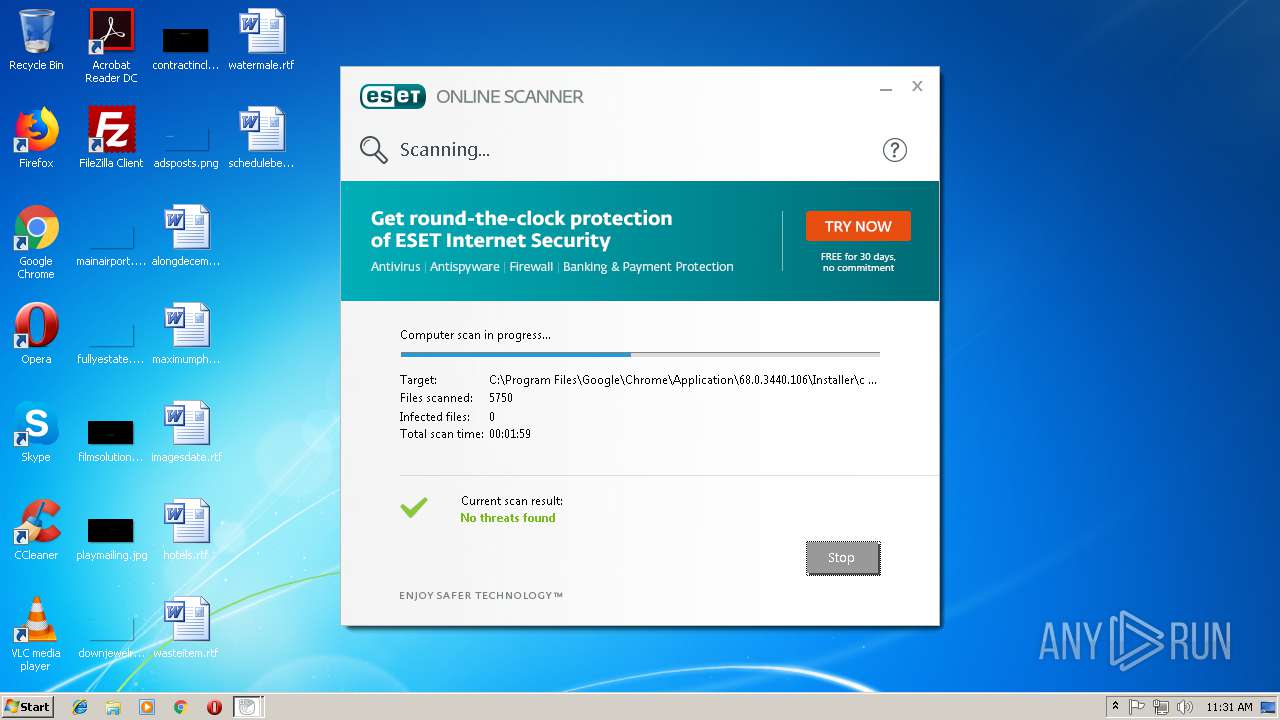
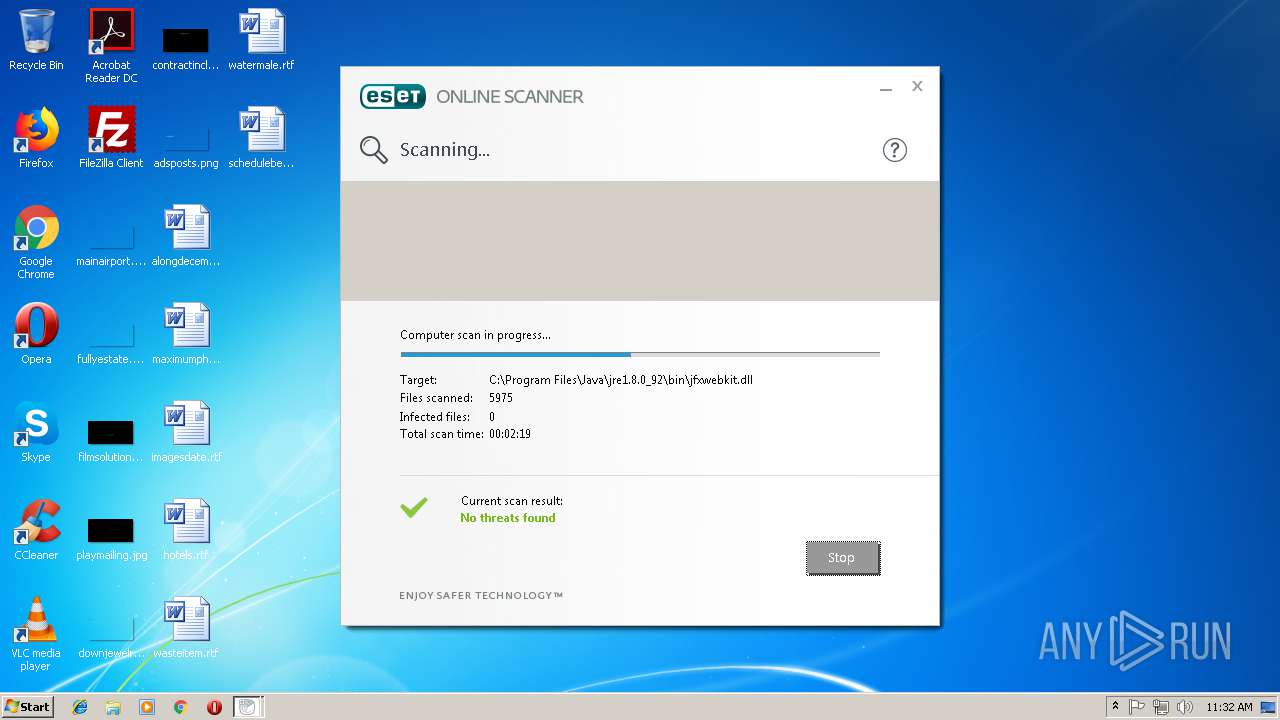
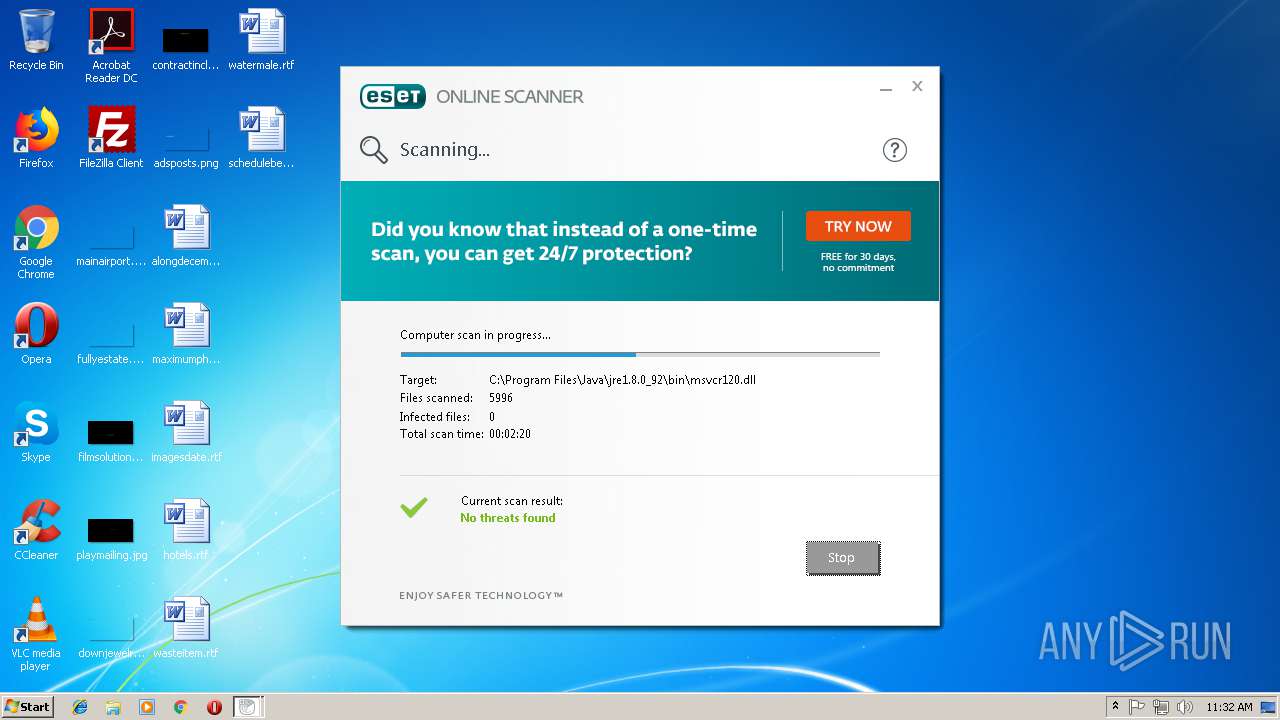
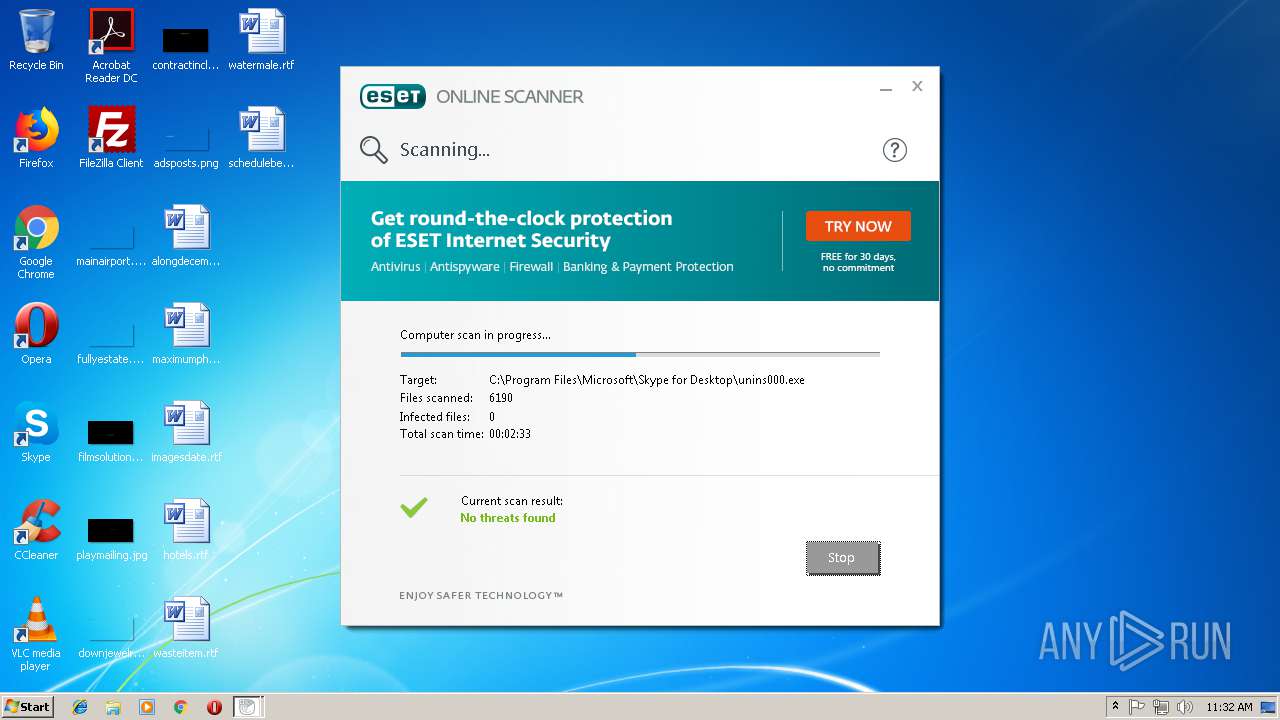
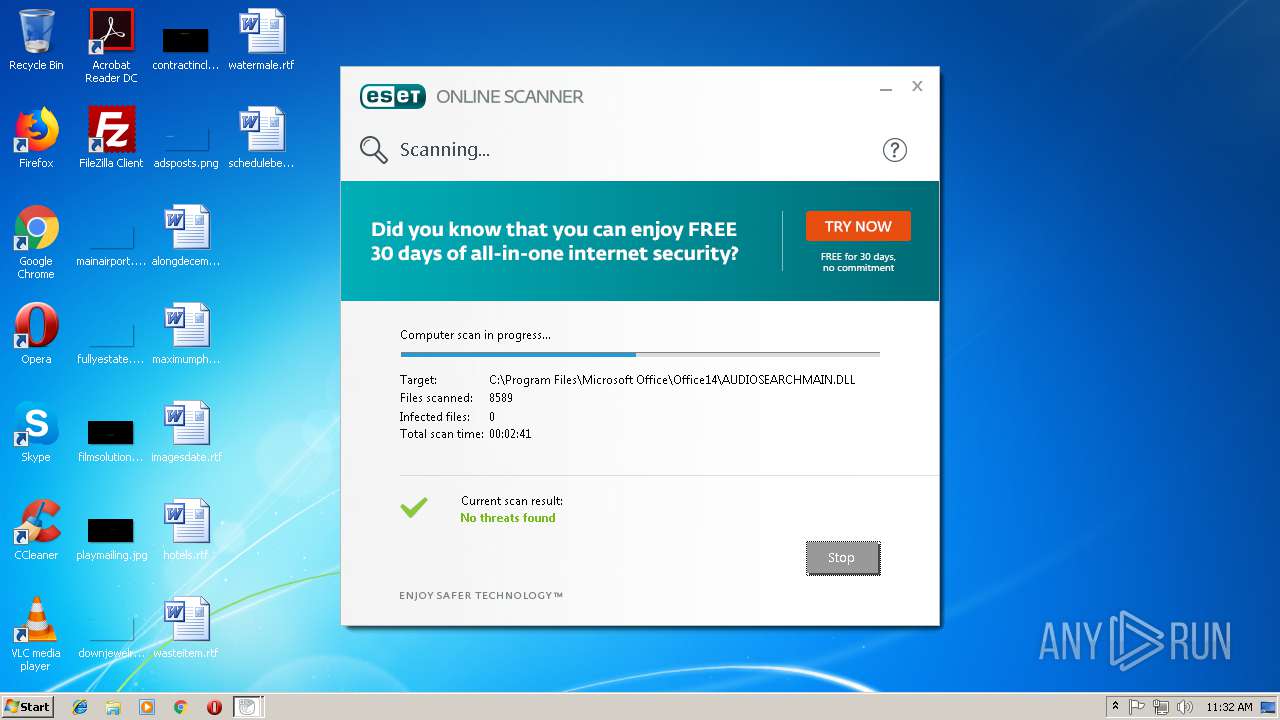
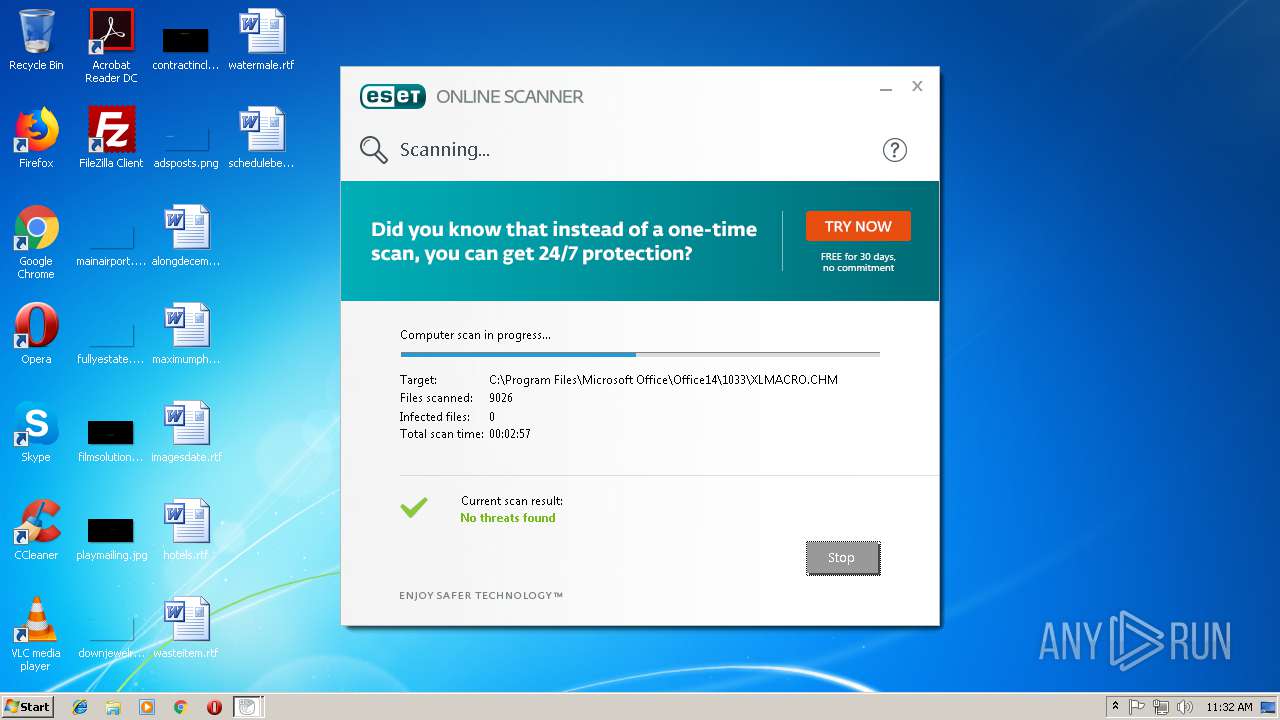
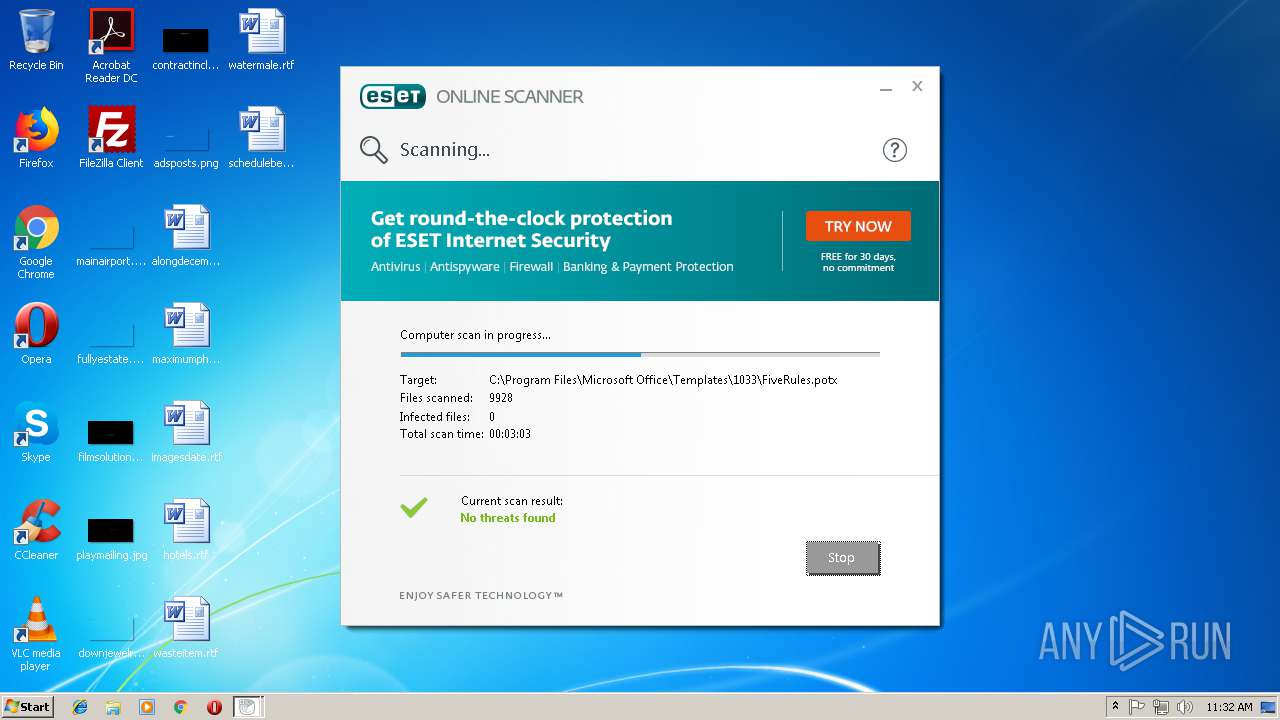
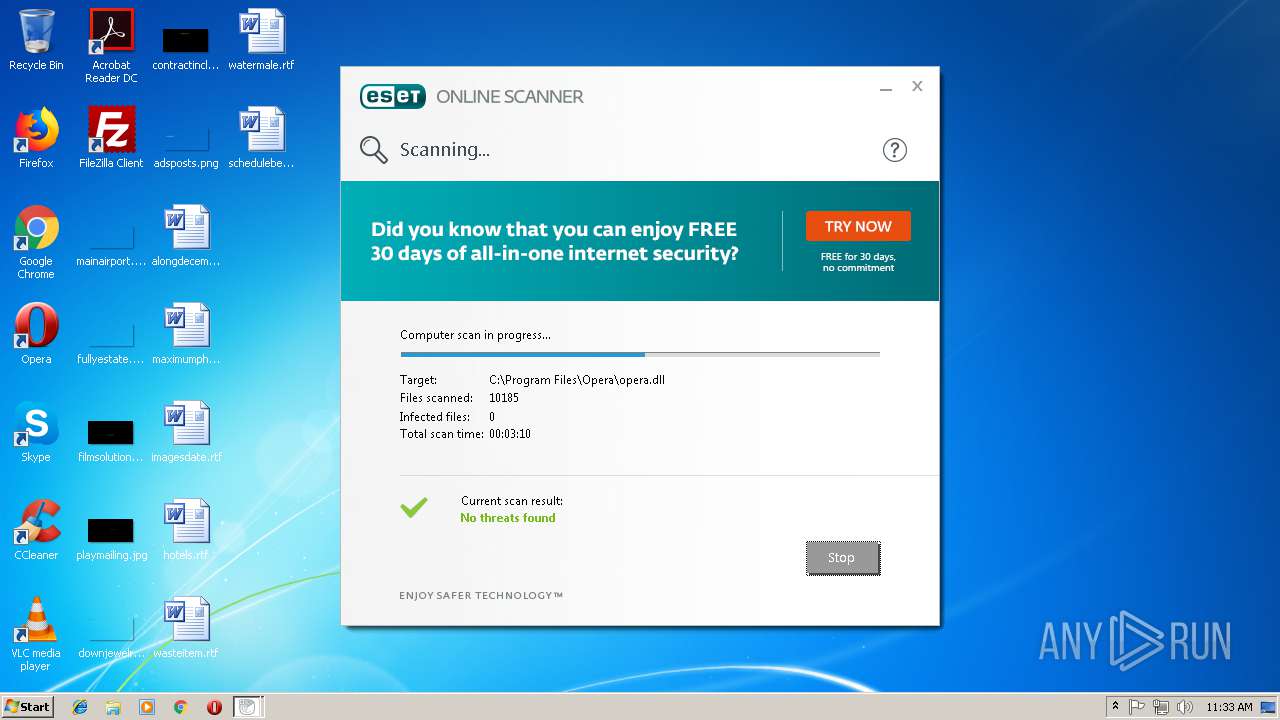
| Verdict: | Malicious activity |
| Analysis date: | December 04, 2018, 11:27:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B76DE37B5830F9ABA177B17259A5A4D8 |
| SHA1: | DD36414DA7BE895E6814DB5B2D0BAFFA7AB054DB |
| SHA256: | 6366D610B5307A21A16AAB1046F37FFF347F91E25B07021E85C9F1FD54F1D9B0 |
| SSDEEP: | 98304:Q63swaE6LZKv6NYmcU+3Q35TF/p6ZH7j7etsB6Z99FLOAkGkzdnEVomFHKnPe:QRSa35TFSfKFLOyomFHKnPe |
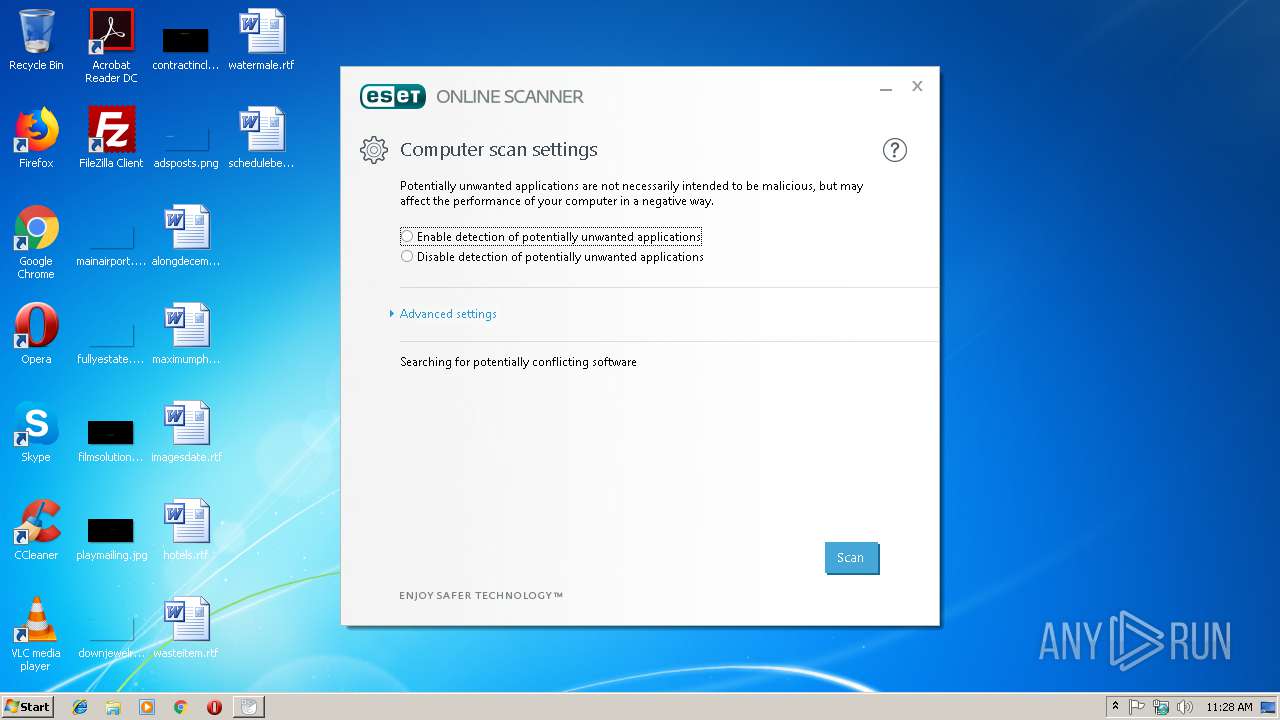
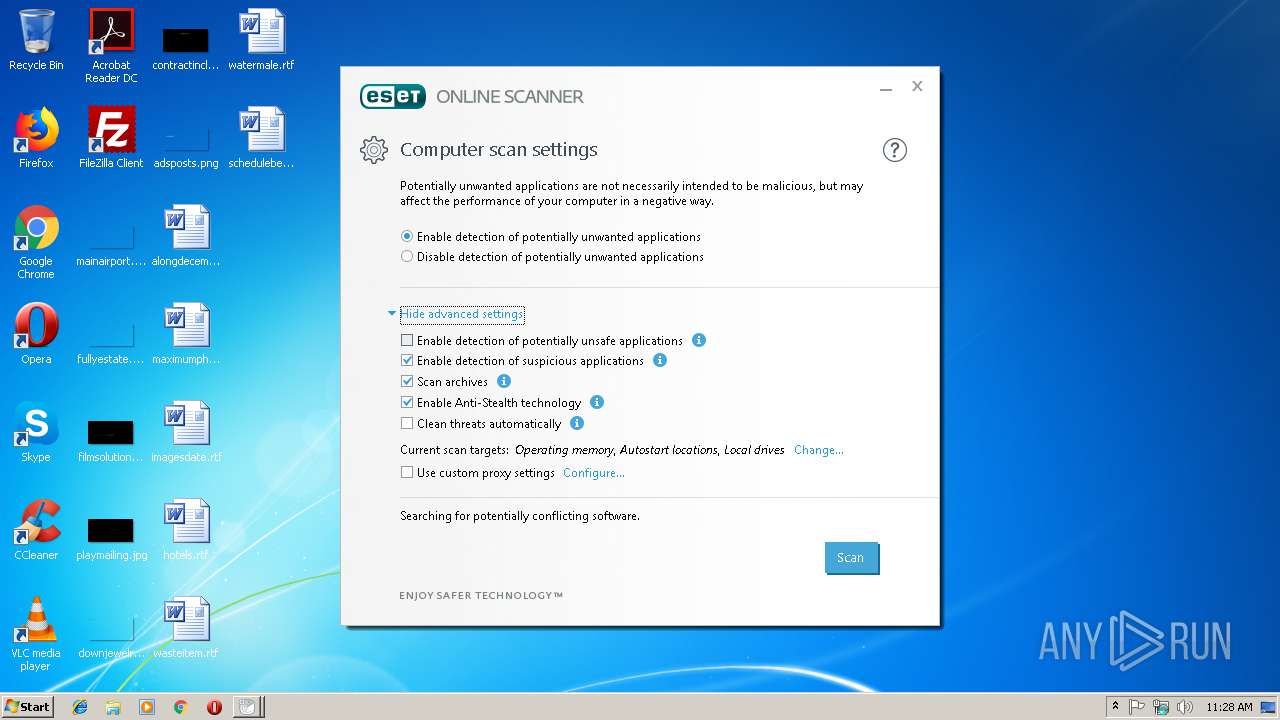
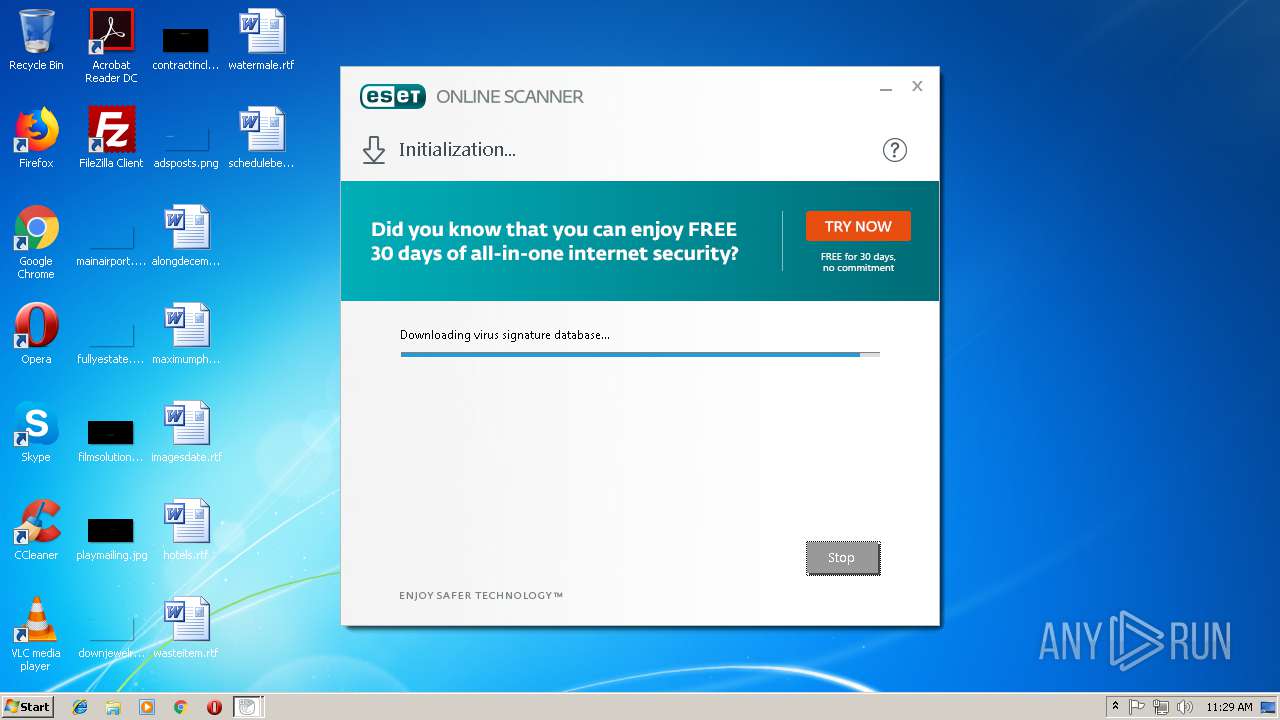
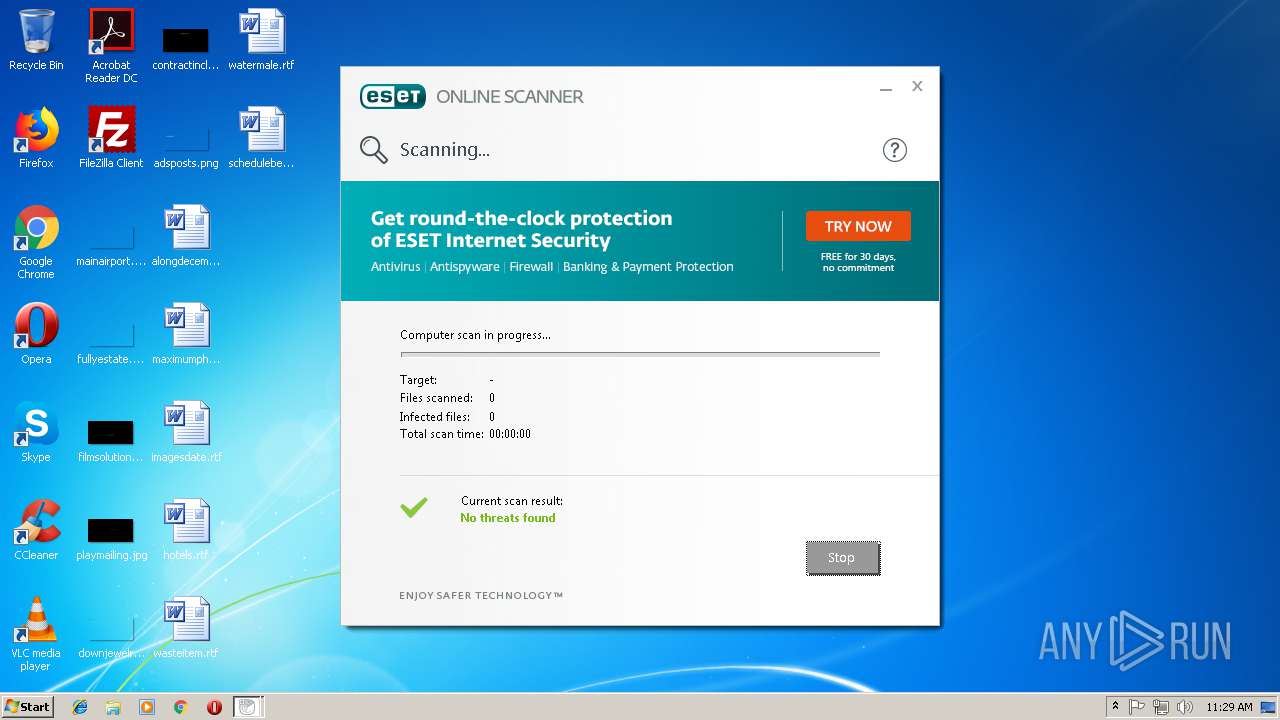
MALICIOUS
Loads dropped or rewritten executable
- esetonlinescanner_enu.exe (PID: 2716)
SUSPICIOUS
Creates files in the user directory
- esetonlinescanner_enu.exe (PID: 3064)
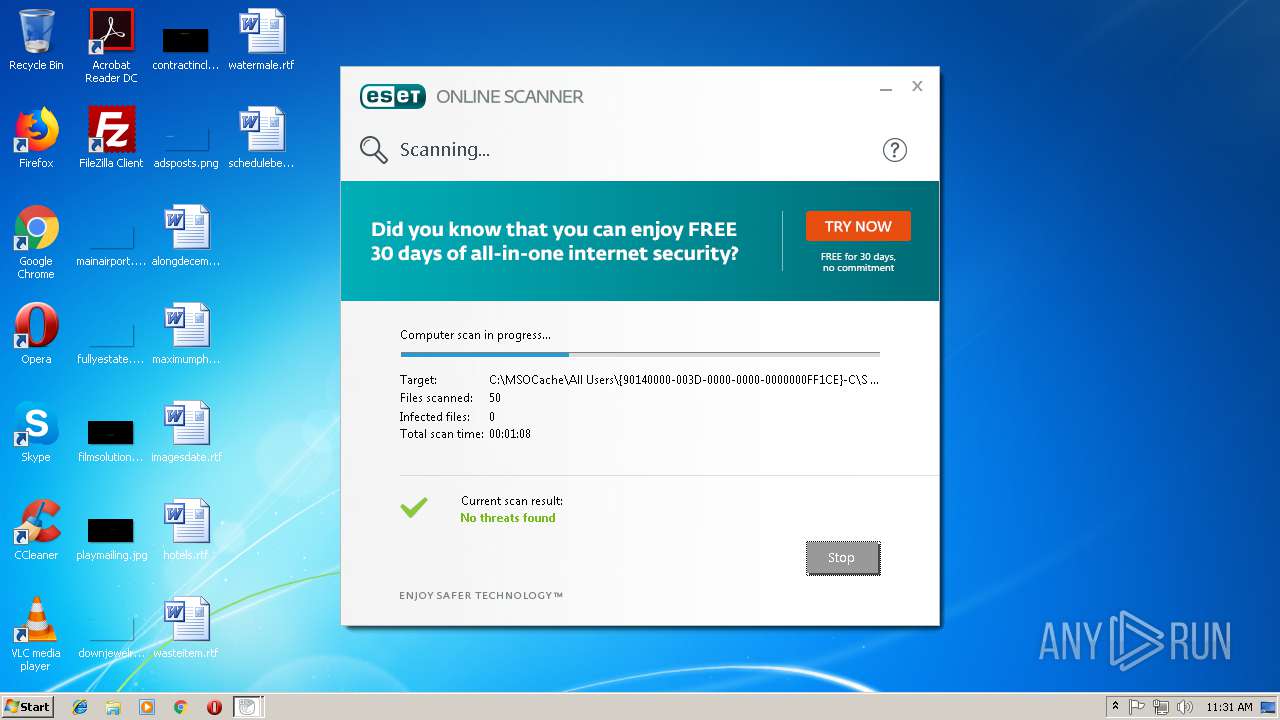
Reads Internet Cache Settings
- esetonlinescanner_enu.exe (PID: 2716)
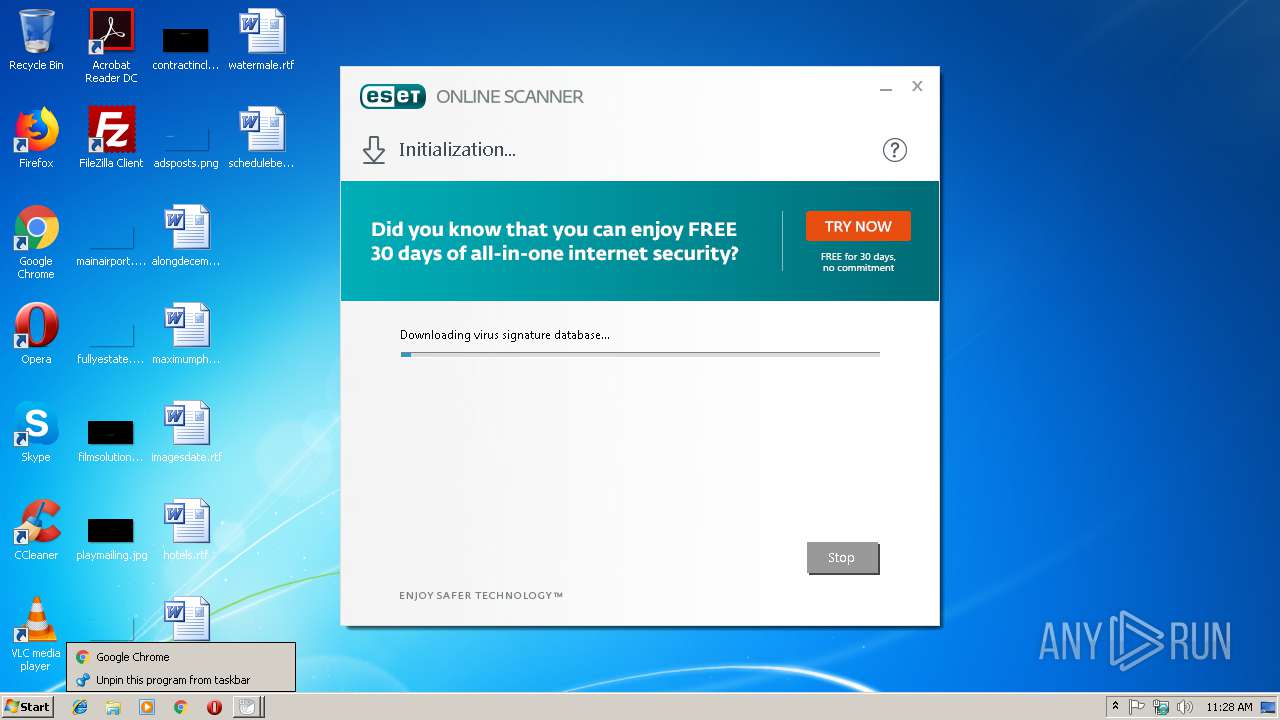
Application launched itself
- esetonlinescanner_enu.exe (PID: 3064)
Executable content was dropped or overwritten
- esetonlinescanner_enu.exe (PID: 2716)
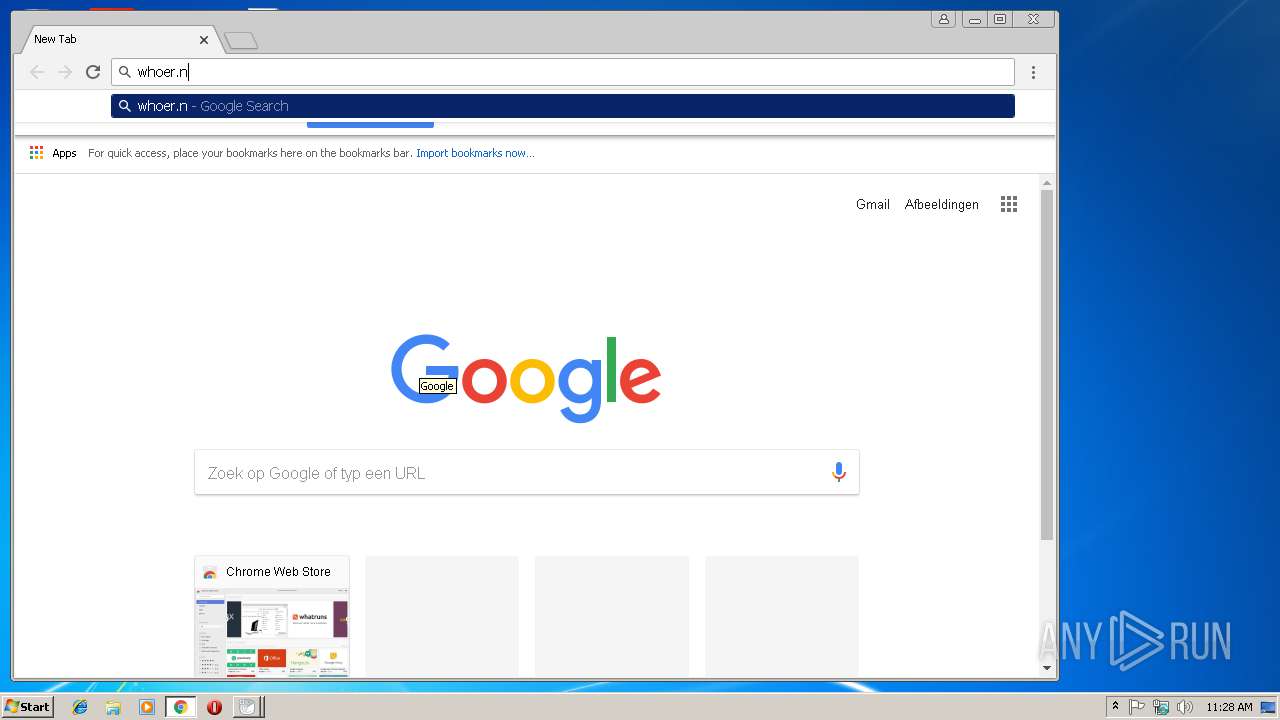
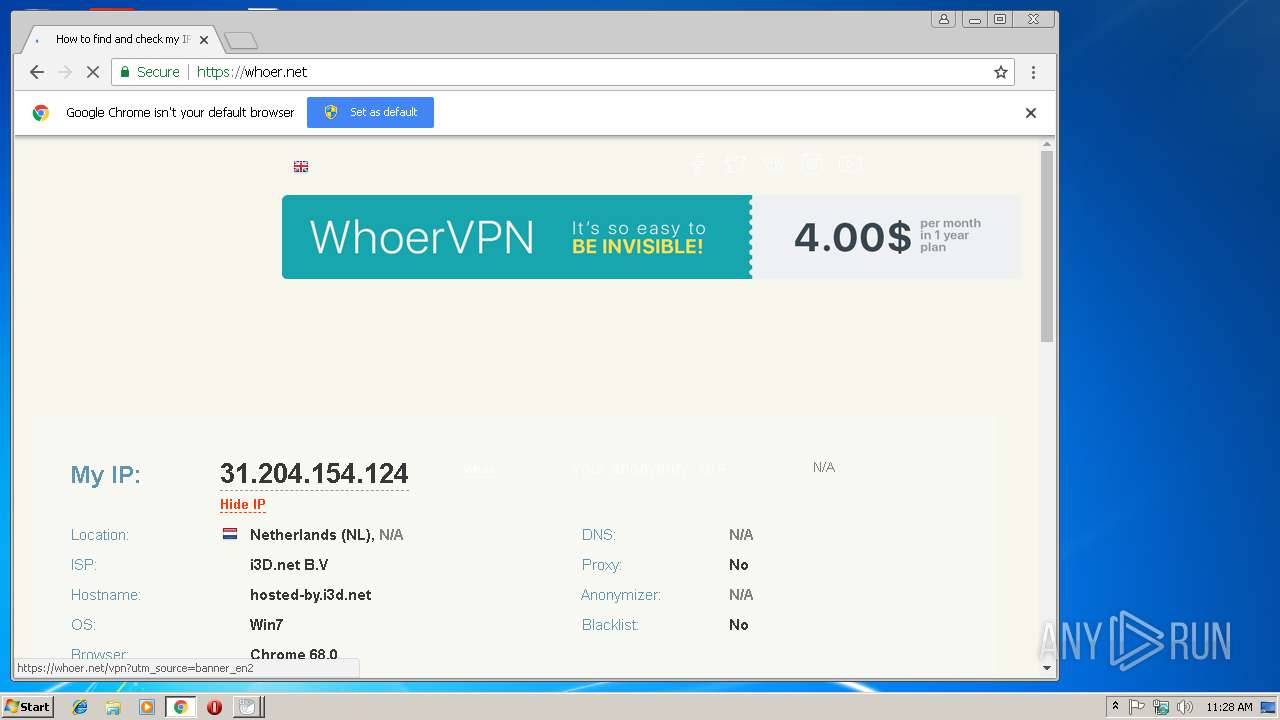
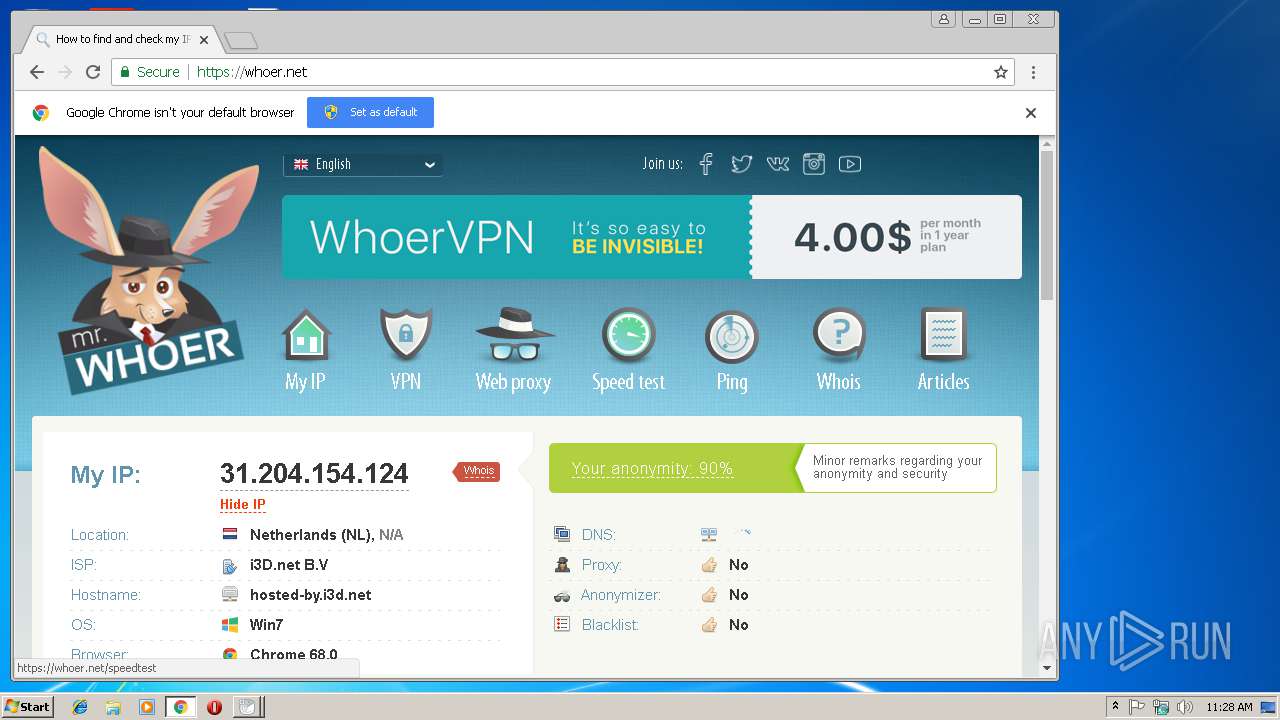
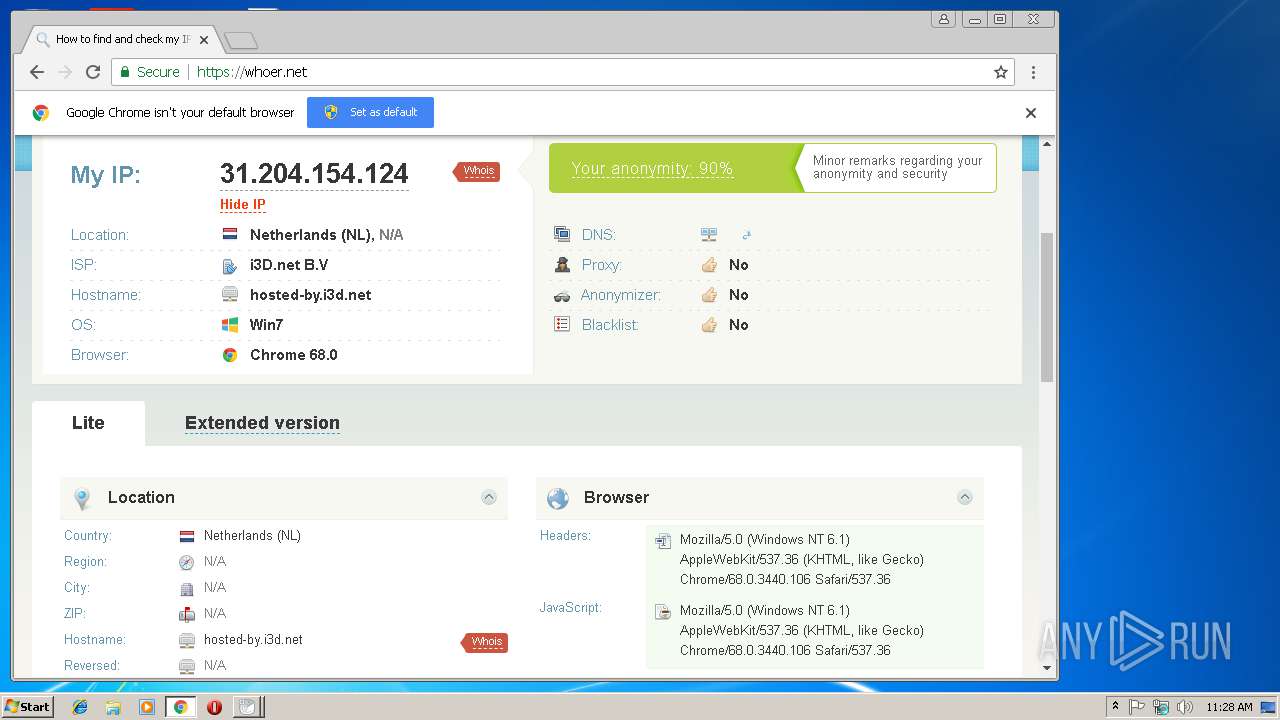
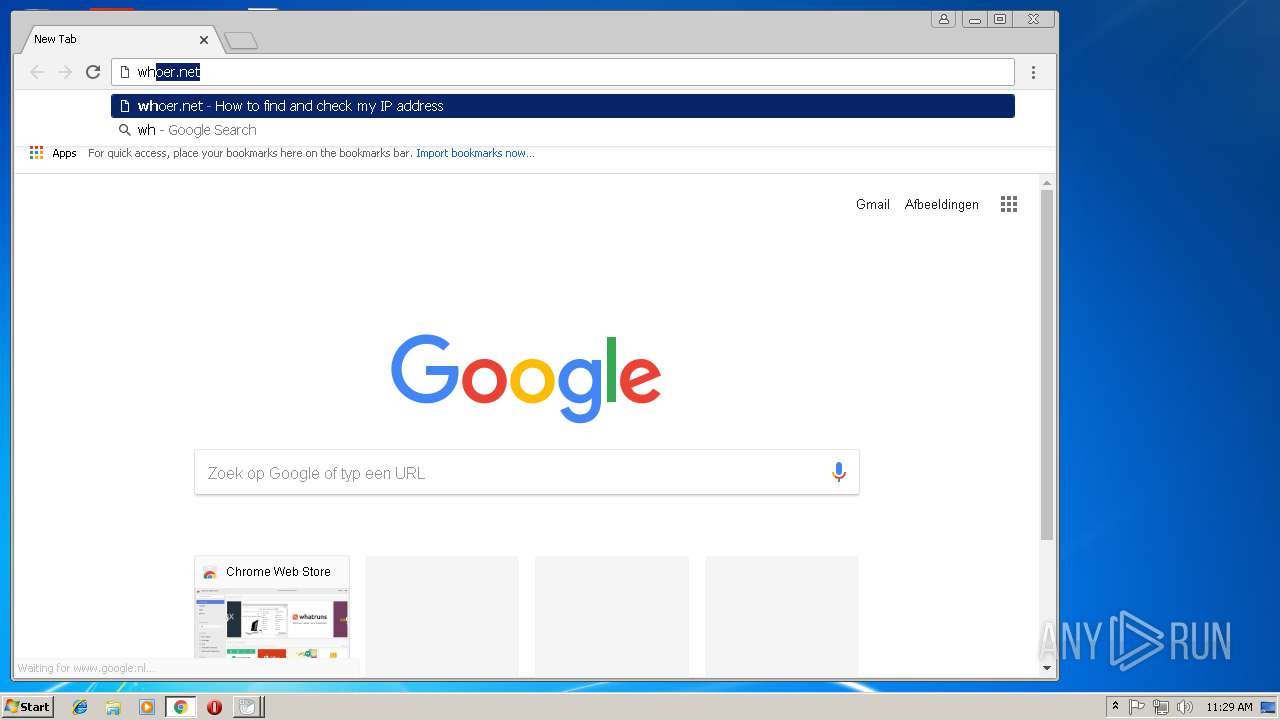
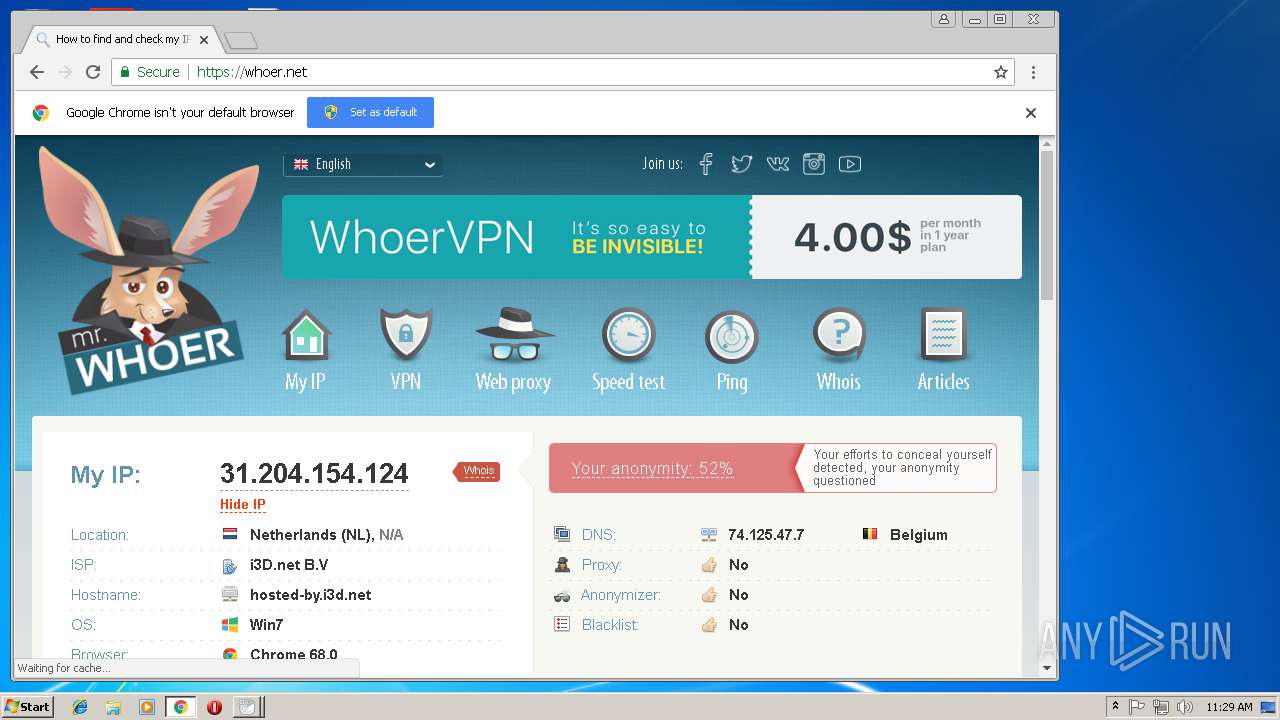
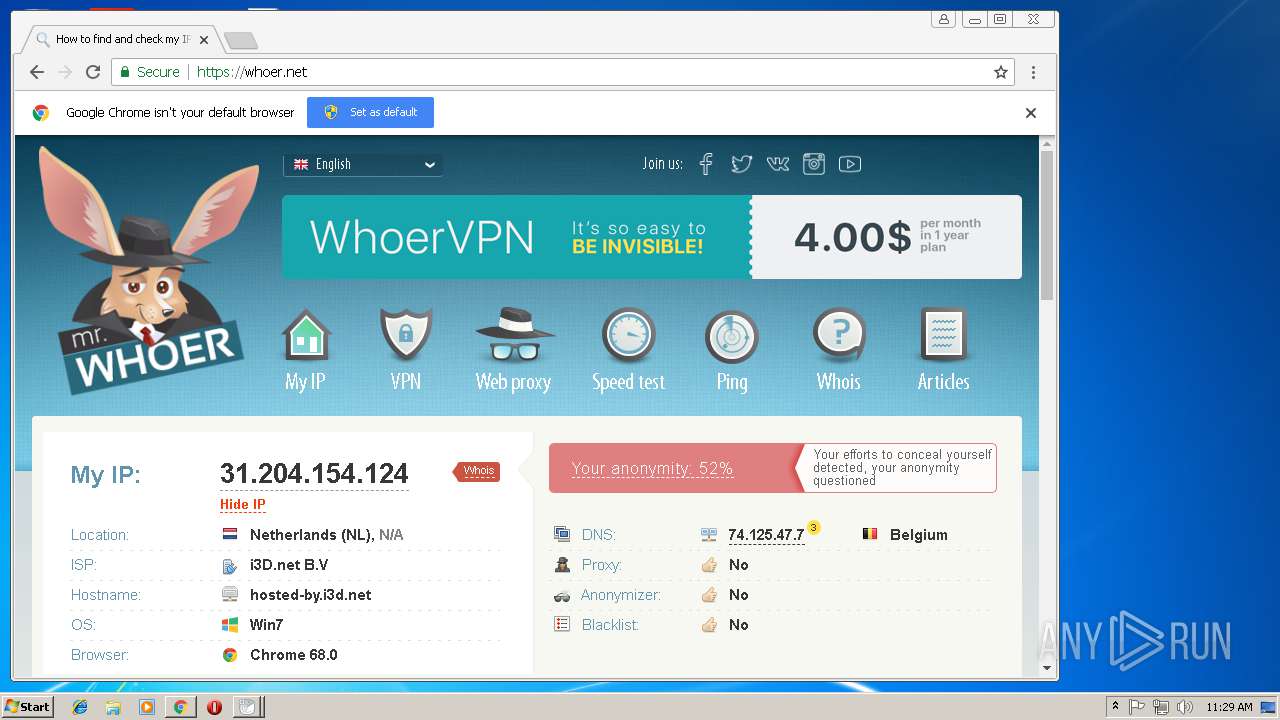
Checks for external IP
- chrome.exe (PID: 3652)
INFO
Application launched itself
- chrome.exe (PID: 3652)
- chrome.exe (PID: 2292)
Reads settings of System Certificates
- chrome.exe (PID: 3652)
- chrome.exe (PID: 2292)
Changes settings of System certificates
- chrome.exe (PID: 3652)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:05:14 11:24:00+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 1962496 |
| InitializedDataSize: | 5033472 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x19e79d |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.0.22.0 |
| ProductVersionNumber: | 2.0.22.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
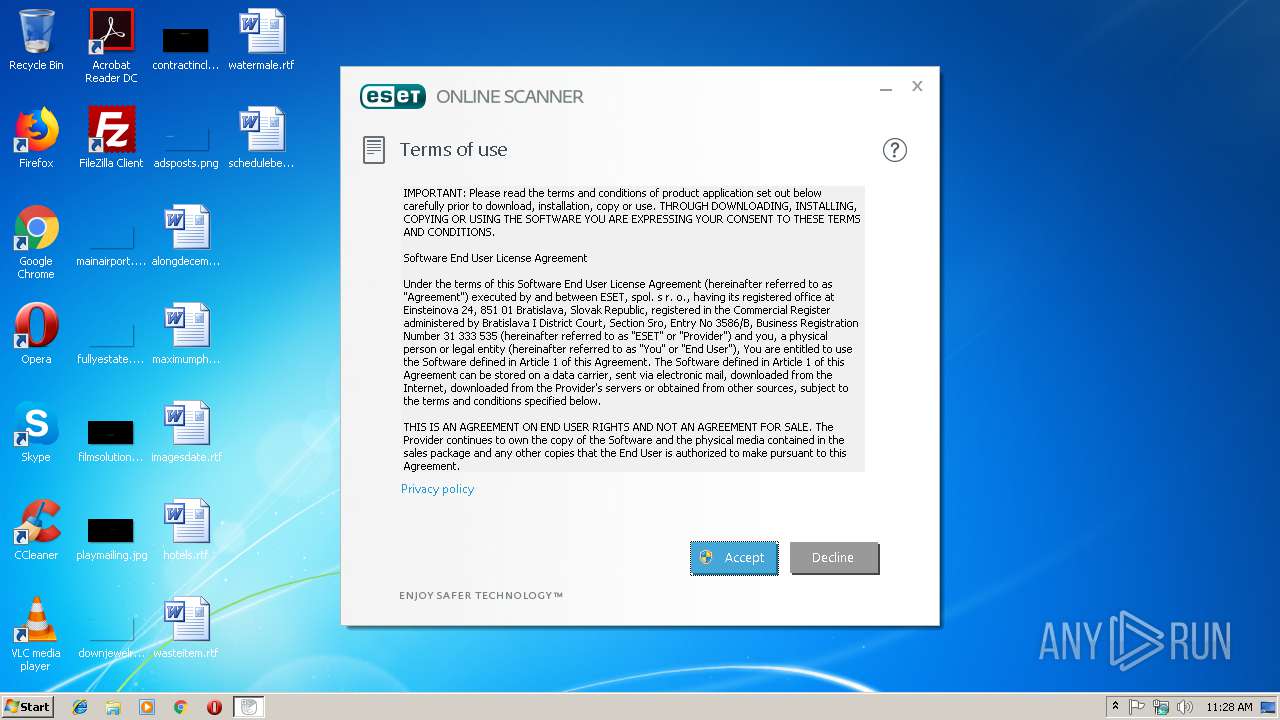
| CompanyName: | ESET spol. s r.o. |
| FileDescription: | ESET Online Scanner |
| FileVersion: | 2.0.22.0 |
| InternalName: | EOS_v2.exe |
| LegalCopyright: | Copyright (c) ESET 1992-2018. All rights reserved. |
| OriginalFileName: | ESETOnlineScanner.exe |
| ProductName: | ESET OnlineScanner |
| ProductVersion: | 2.0.22.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-May-2018 09:24:00 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | ESET spol. s r.o. |
| FileDescription: | ESET Online Scanner |
| FileVersion: | 2.0.22.0 |
| InternalName: | EOS_v2.exe |
| LegalCopyright: | Copyright (c) ESET 1992-2018. All rights reserved. |
| OriginalFilename: | ESETOnlineScanner.exe |
| ProductName: | ESET OnlineScanner |
| ProductVersion: | 2.0.22.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 14-May-2018 09:24:00 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x001DF1EC | 0x001DF200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.57292 |
.rdata | 0x001E1000 | 0x000A7872 | 0x000A7A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.14551 |
.data | 0x00289000 | 0x0001006C | 0x00008400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.58578 |
.rsrc | 0x0029A000 | 0x003F0510 | 0x003F0600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.36694 |
.reloc | 0x0068B000 | 0x00024BF0 | 0x00024C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.51395 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.17085 | 2167 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.8322 | 1128 | UNKNOWN | Slovak - Slovakia | RT_ICON |
3 | 5.58404 | 2440 | UNKNOWN | Slovak - Slovakia | RT_ICON |
4 | 7.97004 | 27921 | UNKNOWN | Slovak - Slovakia | RT_ICON |
5 | 5.21009 | 4264 | UNKNOWN | Slovak - Slovakia | RT_ICON |
6 | 4.79771 | 9640 | UNKNOWN | Slovak - Slovakia | RT_ICON |
7 | 2.35054 | 108 | UNKNOWN | English - United States | RT_STRING |
8 | 5.4776 | 872 | UNKNOWN | Slovak - Slovakia | RT_ICON |
9 | 4.7607 | 872 | UNKNOWN | Slovak - Slovakia | RT_ICON |
10 | 3.02695 | 308 | UNKNOWN | English - United States | RT_CURSOR |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
IMM32.dll |
KERNEL32.dll |
MSIMG32.dll |
OLEACC.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
Total processes
55
Monitored processes
23
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=900,4593041952671594990,916124403969100404,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=6430F467A6DF9083AF01AF182AF0768E --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6430F467A6DF9083AF01AF182AF0768E --renderer-client-id=9 --mojo-platform-channel-handle=2120 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=900,4593041952671594990,916124403969100404,131072 --enable-features=PasswordImport --service-pipe-token=4912D83D1B798E701CF57E9554787541 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4912D83D1B798E701CF57E9554787541 --renderer-client-id=6 --mojo-platform-channel-handle=2084 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2288 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2264 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,16408626558361357191,8625231365925564541,131072 --enable-features=PasswordImport --service-pipe-token=F418848C8220CD93ED60387895A6795D --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=F418848C8220CD93ED60387895A6795D --renderer-client-id=3 --mojo-platform-channel-handle=2056 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6f3900b0,0x6f3900c0,0x6f3900cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2612 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=900,4593041952671594990,916124403969100404,131072 --enable-features=PasswordImport --service-pipe-token=A3ABF3F3CAB704F3D06BC82602F2BF02 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=A3ABF3F3CAB704F3D06BC82602F2BF02 --renderer-client-id=3 --mojo-platform-channel-handle=2020 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2716 | "C:\Users\admin\AppData\Local\Temp\esetonlinescanner_enu.exe" EULA | C:\Users\admin\AppData\Local\Temp\esetonlinescanner_enu.exe | esetonlinescanner_enu.exe | ||||||||||||
User: admin Company: ESET spol. s r.o. Integrity Level: HIGH Description: ESET Online Scanner Exit code: 0 Version: 2.0.22.0 Modules
| |||||||||||||||
| 2796 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6f4300b0,0x6f4300c0,0x6f4300cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2828 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=964,16408626558361357191,8625231365925564541,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=C598B84038679ABC6C6D01918EABE239 --mojo-platform-channel-handle=992 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
827
Read events
668
Write events
153
Delete events
6
Modification events
| (PID) Process: | (3064) esetonlinescanner_enu.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\esetonlinescanner_enu_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3064) esetonlinescanner_enu.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\esetonlinescanner_enu_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3064) esetonlinescanner_enu.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\esetonlinescanner_enu_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3064) esetonlinescanner_enu.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\esetonlinescanner_enu_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3064) esetonlinescanner_enu.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\esetonlinescanner_enu_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3064) esetonlinescanner_enu.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\esetonlinescanner_enu_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3064) esetonlinescanner_enu.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\esetonlinescanner_enu_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3064) esetonlinescanner_enu.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\esetonlinescanner_enu_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3064) esetonlinescanner_enu.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\esetonlinescanner_enu_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3064) esetonlinescanner_enu.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\esetonlinescanner_enu_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
4
Suspicious files
146
Text files
179
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
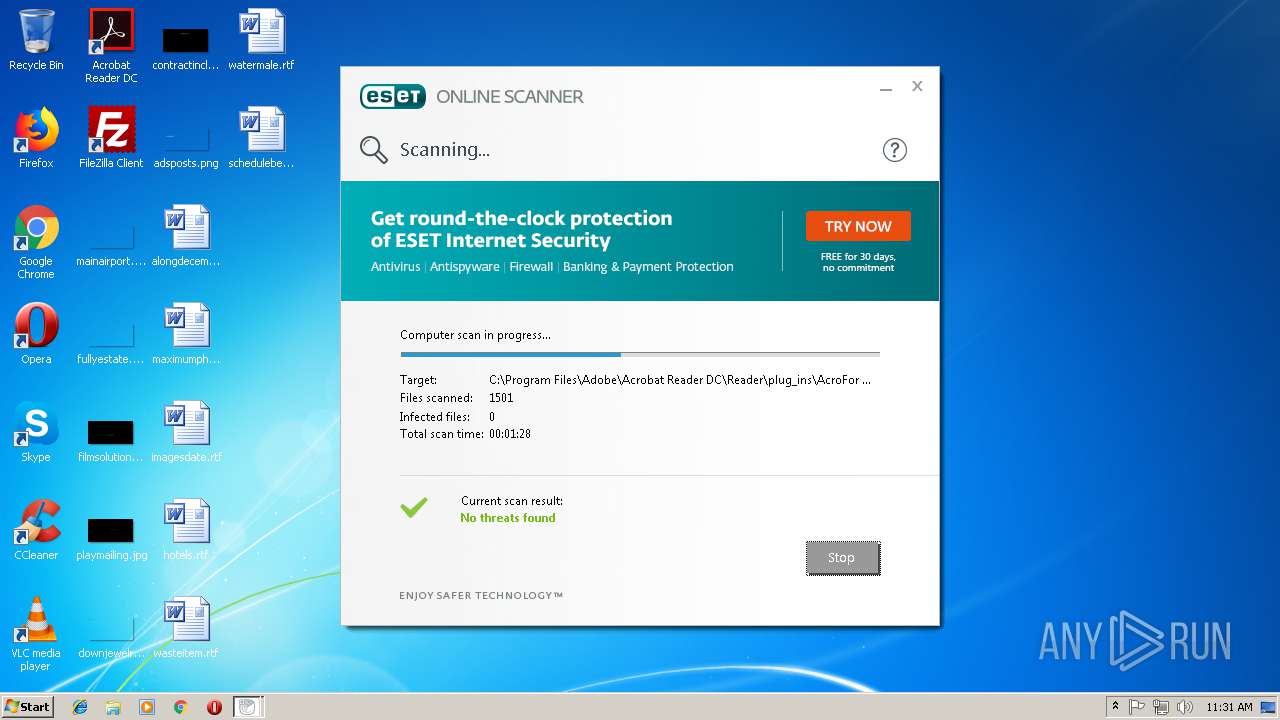
| 3064 | esetonlinescanner_enu.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\EOS_inside_banners_01[1].png | — | |
MD5:— | SHA256:— | |||
| 3064 | esetonlinescanner_enu.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\EOS_inside_banners_02[1].png | — | |
MD5:— | SHA256:— | |||
| 3064 | esetonlinescanner_enu.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\EOS_inside_banners_03[1].png | — | |
MD5:— | SHA256:— | |||
| 3064 | esetonlinescanner_enu.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\ver[1].txt | — | |
MD5:— | SHA256:— | |||
| 2716 | esetonlinescanner_enu.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\detectav[1].xml | — | |
MD5:— | SHA256:— | |||
| 2716 | esetonlinescanner_enu.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\EOS_inside_banners_01[1].png | — | |
MD5:— | SHA256:— | |||
| 2716 | esetonlinescanner_enu.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\EOS_inside_banners_02[1].png | — | |
MD5:— | SHA256:— | |||
| 2716 | esetonlinescanner_enu.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\EOS_inside_banners_03[1].png | — | |
MD5:— | SHA256:— | |||
| 2716 | esetonlinescanner_enu.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\detectavdb_windefend[1].dat | — | |
MD5:— | SHA256:— | |||
| 3804 | esetonlinescanner_enu.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\detectav[1].xml | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
41
TCP/UDP connections
39
DNS requests
21
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2716 | esetonlinescanner_enu.exe | POST | — | 91.228.166.51:80 | http://onlinescanner.eset.com:80/query/chsquery.php | SK | — | — | whitelisted |
2716 | esetonlinescanner_enu.exe | POST | — | 91.228.166.51:80 | http://onlinescanner.eset.com:80/query/chsquery.php | SK | — | — | whitelisted |
2716 | esetonlinescanner_enu.exe | GET | 301 | 91.228.167.30:80 | http://banner.eset.com/banner-onlinescanner?lng=1033 | SK | html | 261 b | whitelisted |
3804 | esetonlinescanner_enu.exe | POST | — | 91.228.166.51:80 | http://onlinescanner.eset.com:80/query/chsquery.php | SK | — | — | whitelisted |
3804 | esetonlinescanner_enu.exe | POST | — | 91.228.166.51:80 | http://onlinescanner.eset.com:80/query/chsquery.php | SK | — | — | whitelisted |
3804 | esetonlinescanner_enu.exe | GET | 301 | 91.228.167.30:80 | http://banner.eset.com/banner-onlinescanner?lng=1033 | SK | html | 261 b | whitelisted |
— | — | POST | — | 91.228.166.51:80 | http://onlinescanner.eset.com:80/query/chsquery.php | SK | — | — | whitelisted |
2716 | esetonlinescanner_enu.exe | GET | 200 | 91.228.166.82:80 | http://download.eset.com/special/detectav/detectav.xml | SK | xml | 503 b | whitelisted |
3804 | esetonlinescanner_enu.exe | GET | 200 | 91.228.166.82:80 | http://download.eset.com/special/detectav/detectav.xml | SK | xml | 503 b | whitelisted |
3064 | esetonlinescanner_enu.exe | GET | 301 | 91.228.167.30:80 | http://banner.eset.com/banner-onlinescanner?lng=1033 | SK | html | 261 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3064 | esetonlinescanner_enu.exe | 91.228.166.51:80 | onlinescanner.eset.com | ESET, spol. s r.o. | SK | unknown |
3064 | esetonlinescanner_enu.exe | 91.228.165.134:80 | go.eset.eu | ESET, spol. s r.o. | SK | unknown |
3064 | esetonlinescanner_enu.exe | 91.228.167.30:80 | banner.eset.com | ESET, spol. s r.o. | SK | unknown |
3064 | esetonlinescanner_enu.exe | 91.228.166.82:443 | download.eset.com | ESET, spol. s r.o. | SK | suspicious |
2716 | esetonlinescanner_enu.exe | 91.228.166.51:80 | onlinescanner.eset.com | ESET, spol. s r.o. | SK | unknown |
2716 | esetonlinescanner_enu.exe | 91.228.166.82:80 | download.eset.com | ESET, spol. s r.o. | SK | suspicious |
2716 | esetonlinescanner_enu.exe | 91.228.167.30:80 | banner.eset.com | ESET, spol. s r.o. | SK | unknown |
2716 | esetonlinescanner_enu.exe | 91.228.166.82:443 | download.eset.com | ESET, spol. s r.o. | SK | suspicious |
3804 | esetonlinescanner_enu.exe | 91.228.166.51:80 | onlinescanner.eset.com | ESET, spol. s r.o. | SK | unknown |
3804 | esetonlinescanner_enu.exe | 91.228.166.82:80 | download.eset.com | ESET, spol. s r.o. | SK | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
onlinescanner.eset.com |
| whitelisted |
banner.eset.com |
| whitelisted |
go.eset.eu |
| suspicious |
download.eset.com |
| whitelisted |
update.eset.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.google.de |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3652 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Possible External IP Lookup whoer.net |
2716 | esetonlinescanner_enu.exe | Web Application Attack | SC WEB_APPLICATION_ATTACK Suspicious Generic - Path Traversal for Unix in Zip archive |