| File name: | 635b01bda7f9753ba72dfa5efed266f10addb19273eb2bcaf8d8cfd3c06d1fa9 |
| Full analysis: | https://app.any.run/tasks/e4024e38-c9a6-4f17-b730-08da85af7a4d |
| Verdict: | Malicious activity |
| Analysis date: | December 29, 2024, 22:15:52 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 936, Author: , Template: Normal.dotm, Last Saved By: , Revision Number: 2, Name of Creating Application: Microsoft Office Word, Create Time/Date: Sun Dec 29 03:29:00 2024, Last Saved Time/Date: Sun Dec 29 03:29:00 2024, Number of Pages: 1, Number of Words: 0, Number of Characters: 0, Security: 0 |
| MD5: | C3E4D0F03CE34C94986741AE9CDF6104 |
| SHA1: | 38B95EB3BEC13067F3B39D5DAA048B68C1C25FBB |
| SHA256: | 635B01BDA7F9753BA72DFA5EFED266F10ADDB19273EB2BCAF8D8CFD3C06D1FA9 |
| SSDEEP: | 384:giIR3DLxvkuTxcyvuFJWLuY7BM5U02m7M7+jGo0j9wFS:gR3DBkuiyGFZ1Bo7KX3U |
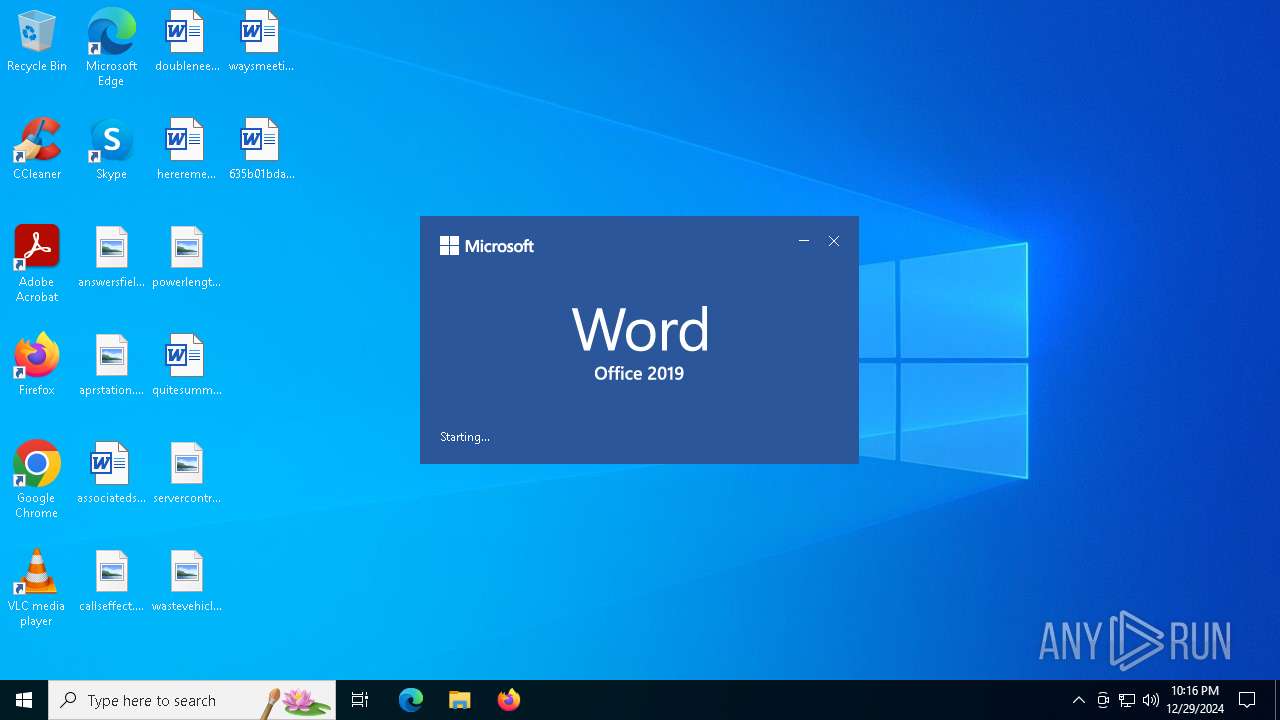
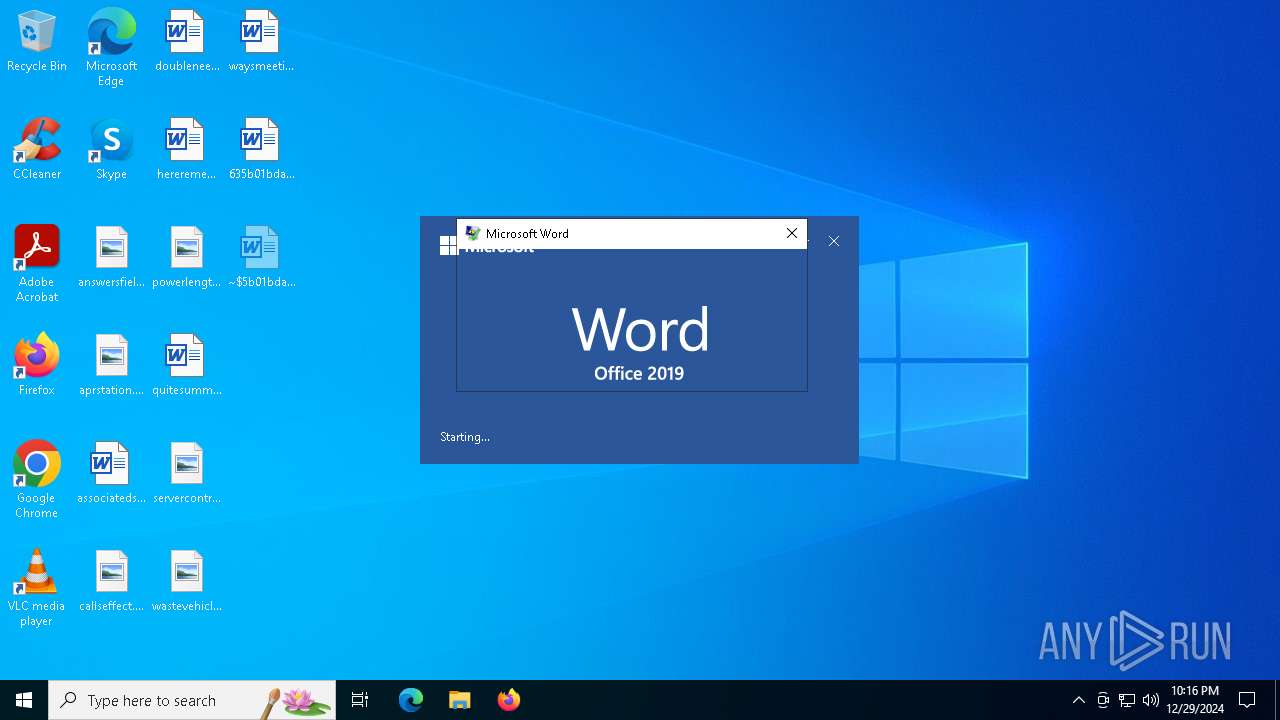
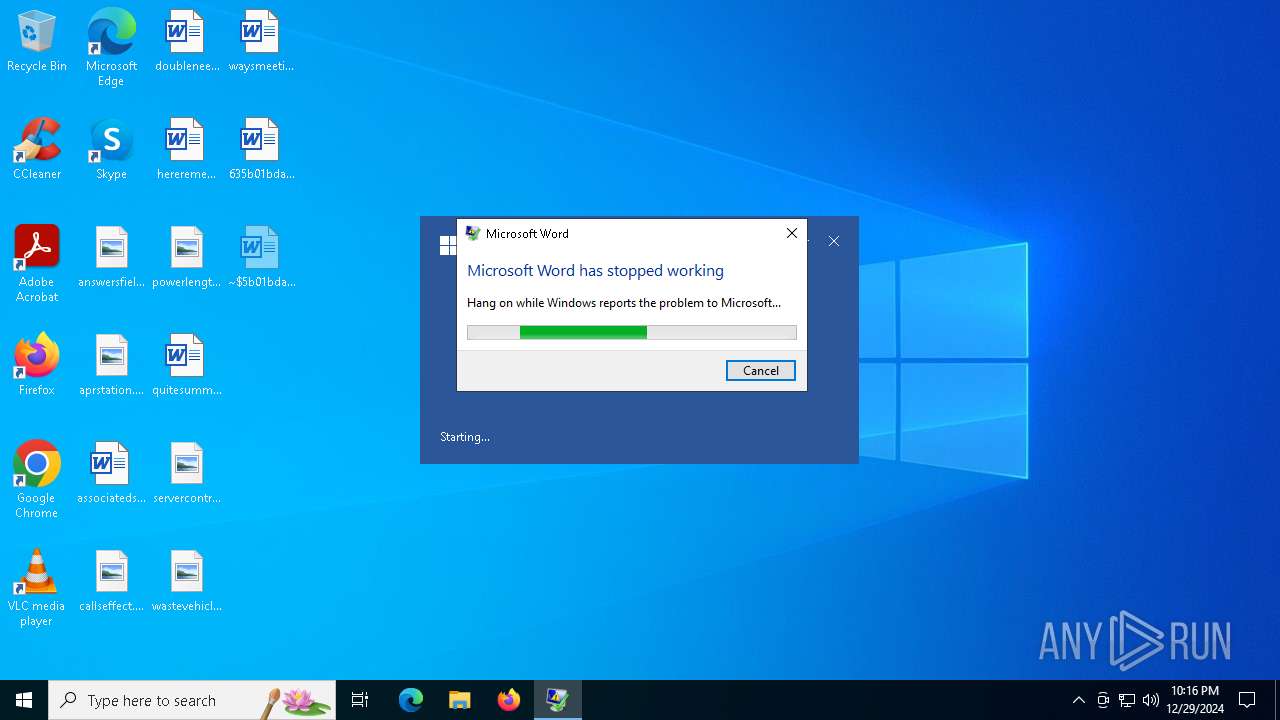
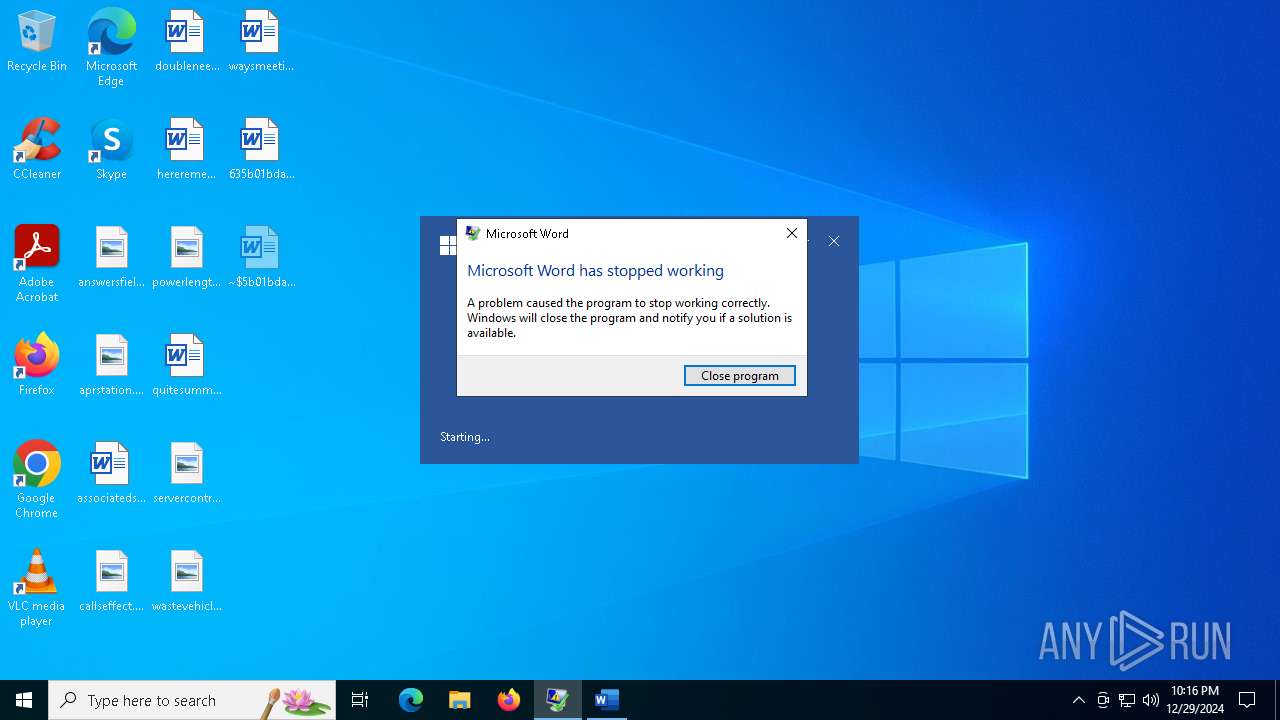
MALICIOUS
Unusual execution from MS Office
- WINWORD.EXE (PID: 4528)
SUSPICIOUS
No suspicious indicators.INFO
An automatically generated document
- WINWORD.EXE (PID: 4528)
Creates files in the program directory
- DWWIN.EXE (PID: 3620)
Reads the software policy settings
- DWWIN.EXE (PID: 3620)
Reads Microsoft Office registry keys
- DWWIN.EXE (PID: 3620)
Checks proxy server information
- DWWIN.EXE (PID: 3620)
Drops encrypted VBS script (Microsoft Script Encoder)
- WINWORD.EXE (PID: 4528)
The process uses the downloaded file
- WINWORD.EXE (PID: 4528)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (35.9) |
|---|---|---|
| .xls | | | Microsoft Excel sheet (33.7) |
| .doc | | | Microsoft Word document (old ver.) (21.3) |
EXIF
FlashPix
| Identification: | Word 8.0 |
|---|---|
| LanguageCode: | English (US) |
| DocFlags: | 1Table, ExtChar, Far east |
| System: | Windows |
| Word97: | No |
| Title: | - |
| Subject: | - |
| Author: | Ӿ?? ?? |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | Ӿ?? ?? |
| Software: | Microsoft Office Word |
| CreateDate: | 2024:12:29 03:29:00 |
| ModifyDate: | 2024:12:29 03:29:00 |
| Security: | None |
| CodePage: | Windows Simplified Chinese (PRC, Singapore) |
| Company: | - |
| CharCountWithSpaces: | - |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| CompObjUserTypeLen: | 28 |
| CompObjUserType: | Microsoft Word 97-2003 ?ĵ? |
| LastPrinted: | 0000:00:00 00:00:00 |
| RevisionNumber: | 2 |
| TotalEditTime: | - |
| Words: | - |
| Characters: | - |
| Pages: | 1 |
| Paragraphs: | - |
| Lines: | - |
Total processes
123
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3620 | C:\WINDOWS\system32\dwwin.exe -x -s 3116 | C:\Windows\System32\DWWIN.EXE | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Error Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4528 | "C:\Program Files\Microsoft Office\Root\Office16\WINWORD.EXE" /n C:\Users\admin\Desktop\635b01bda7f9753ba72dfa5efed266f10addb19273eb2bcaf8d8cfd3c06d1fa9.doc /o "" | C:\Program Files\Microsoft Office\root\Office16\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 4 Version: 16.0.16026.20146 Modules
| |||||||||||||||
Total events
14 215
Read events
13 984
Write events
225
Delete events
6
Modification events
| (PID) Process: | (4528) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\ClientTelemetry\Sampling |
| Operation: | write | Name: | 0 |
Value: 017012000000001000B24E9A3E02000000000000000600000000000000 | |||
| (PID) Process: | (4528) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\Common\CrashPersistence\WINWORD\4528 |
| Operation: | write | Name: | 0 |
Value: 0B0E109366AD2526235342ADCD4E978A5D7219230046C4C1A3F5F3C7D6ED016A04102400449A7D64B29D01008500A907556E6B6E6F776EC906022222CA0DC2190000C91003783634C511B023D2120B770069006E0077006F00720064002E00650078006500C51620C517808004C91808323231322D44656300 | |||
| (PID) Process: | (4528) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | en-US |
Value: 2 | |||
| (PID) Process: | (4528) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | de-de |
Value: 2 | |||
| (PID) Process: | (4528) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | fr-fr |
Value: 2 | |||
| (PID) Process: | (4528) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | es-es |
Value: 2 | |||
| (PID) Process: | (4528) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | it-it |
Value: 2 | |||
| (PID) Process: | (4528) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ja-jp |
Value: 2 | |||
| (PID) Process: | (4528) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | ko-kr |
Value: 2 | |||
| (PID) Process: | (4528) WINWORD.EXE | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\LanguageResources\EnabledEditingLanguages |
| Operation: | write | Name: | pt-br |
Value: 2 | |||
Executable files
1
Suspicious files
20
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3620 | DWWIN.EXE | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_WINWORD.EXE_64935fc192ac76250153abb995bdb75cadecdc_00000000_dea4e046-b249-4a42-a311-5317b59dd41c\Report.wer | — | |
MD5:— | SHA256:— | |||
| 4528 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Content.Word\~WRS{421165C1-A4B1-48B1-9451-28C358E47781}.tmp | binary | |
MD5:FB294ADA09B99EF2DEFEDC229C6C3EF7 | SHA256:8B2E62CCAF3758D056D38071A1C4E0F0C9402FEC9F951801E394020235F8C099 | |||
| 3620 | DWWIN.EXE | C:\ProgramData\Microsoft\Windows\WER\Temp\WER6D06.tmp.xml | xml | |
MD5:A8FDB55832AE85C8667897B527A23442 | SHA256:F83C9C205BE602E13D8F104B909FF3782236D4A39DE749CCB07F380335FD2BC5 | |||
| 4528 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF3439559A4B2CE231.TMP | document | |
MD5:C3E4D0F03CE34C94986741AE9CDF6104 | SHA256:635B01BDA7F9753BA72DFA5EFED266F10ADDB19273EB2BCAF8D8CFD3C06D1FA9 | |||
| 4528 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFC7FC5CD23936B53E.TMP | document | |
MD5:C3E4D0F03CE34C94986741AE9CDF6104 | SHA256:635B01BDA7F9753BA72DFA5EFED266F10ADDB19273EB2BCAF8D8CFD3C06D1FA9 | |||
| 3620 | DWWIN.EXE | C:\ProgramData\Microsoft\Windows\WER\Temp\WER6CD6.tmp.WERInternalMetadata.xml | xml | |
MD5:E781DFF5AD1692156E9DD976A229D7D6 | SHA256:DCF1B918F8D66AD8D6369295C1E8B8C5C6A77F23D7E74582FF8BC180A1795957 | |||
| 4528 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF91FA34B5DDBA702B.TMP | gmc | |
MD5:BF619EAC0CDF3F68D496EA9344137E8B | SHA256:076A27C79E5ACE2A3D47F9DD2E83E4FF6EA8872B3C2218F66C92B89B55F36560 | |||
| 4528 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF4E747D499B839F83.TMP | gmc | |
MD5:BF619EAC0CDF3F68D496EA9344137E8B | SHA256:076A27C79E5ACE2A3D47F9DD2E83E4FF6EA8872B3C2218F66C92B89B55F36560 | |||
| 4528 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\Content.Word\~WRS{9626C1AD-2B4E-45AC-94E8-7B257777E4C0}.tmp | binary | |
MD5:830FBF83999E052538EAF156AB6ECB17 | SHA256:D5098A2CEAE815DB29CD53C76F85240C95DC4D2E3FEDDD71D628617064C29869 | |||
| 4528 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\AddInClassifierCache\OfficeSharedEntities.bin | text | |
MD5:CC90D669144261B198DEAD45AA266572 | SHA256:89C701EEFF939A44F28921FD85365ECD87041935DCD0FE0BAF04957DA12C9899 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
24
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3040 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 52.109.89.18:443 | https://officeclient.microsoft.com/config16/?lcid=1033&syslcid=1033&uilcid=1033&build=16.0.16026&crev=3 | unknown | xml | 178 Kb | unknown |
— | — | GET | 200 | 23.32.238.120:443 | https://omex.cdn.office.net/addinclassifier/officesharedentities | unknown | text | 314 Kb | whitelisted |
— | — | GET | 200 | 52.113.194.132:443 | https://ecs.office.com/config/v2/Office/word/16.0.16026.20146/Production/CC?&Clientid=%7bD61AB268-C26A-439D-BB15-2A0DEDFCA6A3%7d&Application=word&Platform=win32&Version=16.0.16026.20146&MsoVersion=16.0.16026.20002&SDX=fa000000002.2.0.1907.31003&SDX=fa000000005.1.0.1909.30011&SDX=fa000000006.1.0.1909.13002&SDX=fa000000008.1.0.1908.16006&SDX=fa000000009.1.0.1908.6002&SDX=fa000000016.1.0.1810.13001&SDX=fa000000029.1.0.1906.25001&SDX=fa000000033.1.0.1908.24001&SDX=wa104381125.1.0.1810.9001&ProcessName=winword.exe&Audience=Production&Build=ship&Architecture=x64&Language=en-US&SubscriptionLicense=false&PerpetualLicense=2019&LicenseCategory=6&LicenseSKU=Professional2019Retail&OsVersion=10.0&OsBuild=19045&Channel=CC&InstallType=C2R&SessionId=%7b25AD6693-2326-4253-ADCD-4E978A5D7219%7d&LabMachine=false | unknown | binary | 398 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
3040 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.23.209.187:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4528 | WINWORD.EXE | 52.109.76.240:443 | officeclient.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3620 | DWWIN.EXE | 104.208.16.94:443 | watson.events.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
watson.events.data.microsoft.com |
| whitelisted |
omex.cdn.office.net |
| whitelisted |
ecs.office.com |
| whitelisted |
self.events.data.microsoft.com |
| unknown |