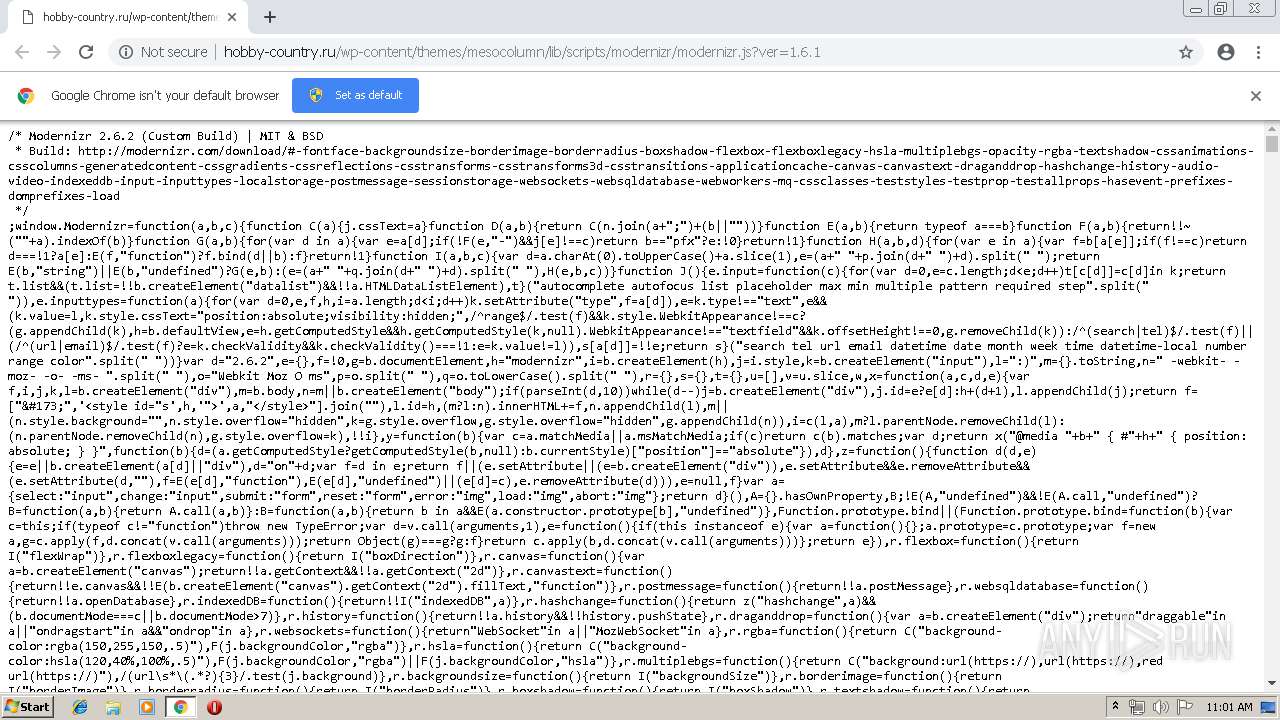
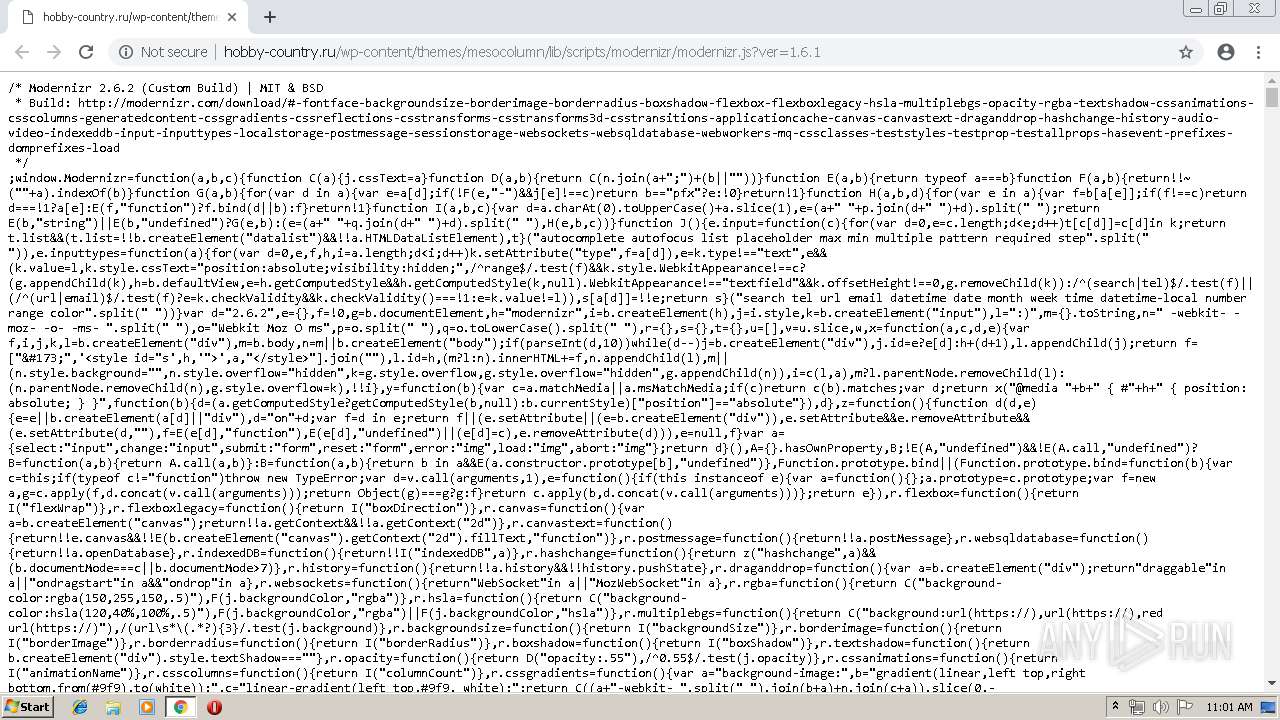
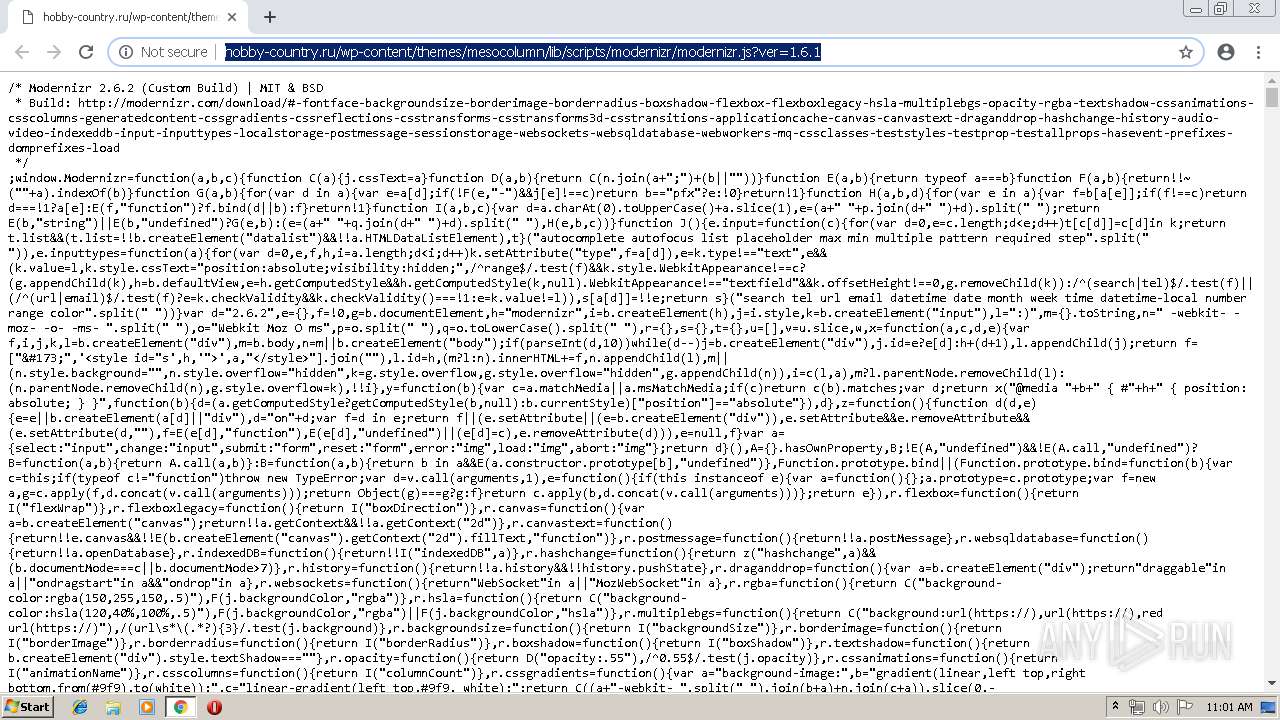
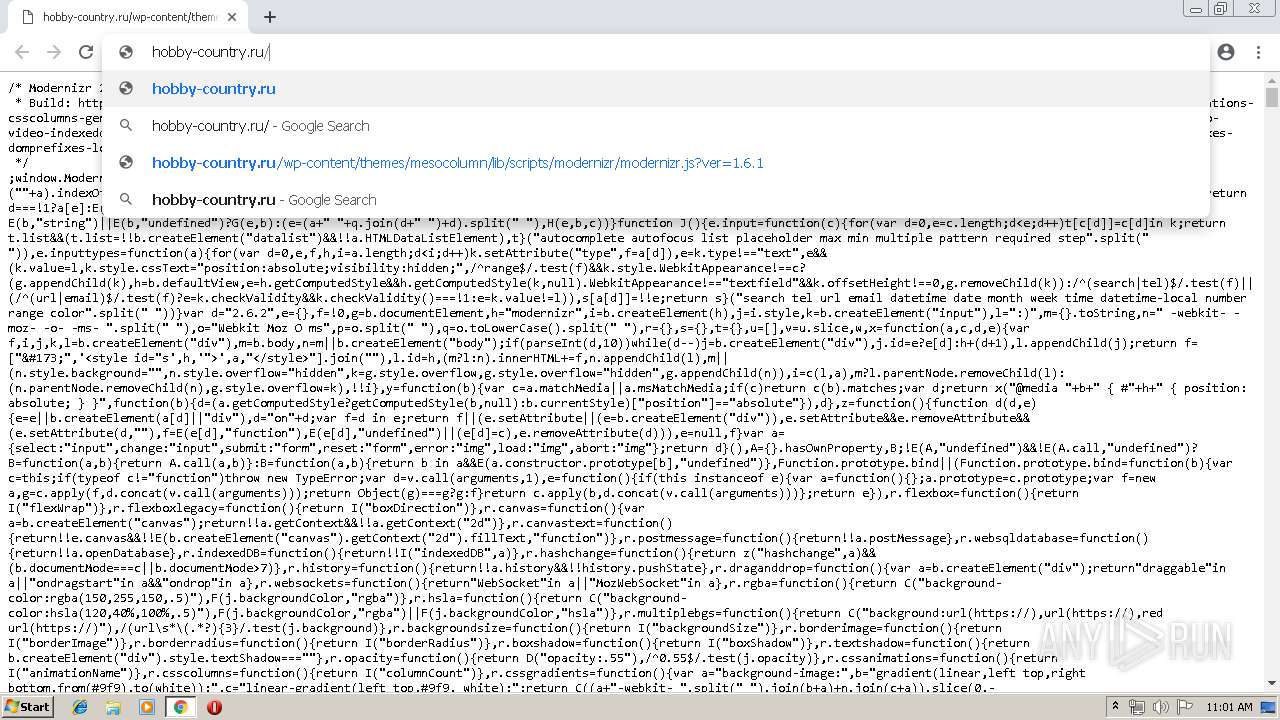
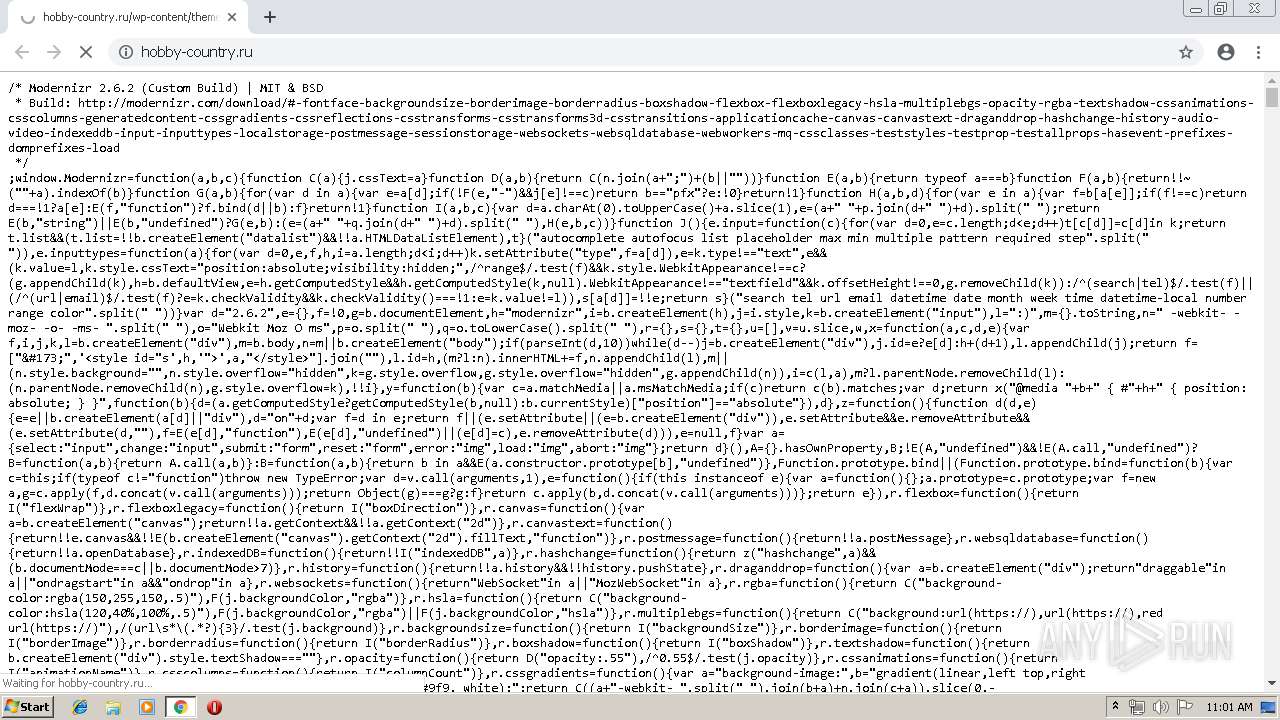
| URL: | http://hobby-country.ru/wp-content/themes/mesocolumn/lib/scripts/modernizr/modernizr.js?ver=1.6.1 |
| Full analysis: | https://app.any.run/tasks/f831e0bd-aa0f-46ad-a84a-0bbfb0471558 |
| Verdict: | Malicious activity |
| Analysis date: | April 23, 2019, 10:01:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 45FF575D2C6244178E3AD92437635CB7 |
| SHA1: | B5B18EF96591DF194890ED6FAE861A77ED93DB85 |
| SHA256: | 63589254C5BBBB34CE1CC1DE81F1357F3C79124130A3629B7B75E14203146EF4 |
| SSDEEP: | 3:N1KWKn5GZX6vSOAQrFade6NV5WBJrWaW5g:CW2Y9OAkFZ6/5WzN |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3888)
INFO
Application launched itself
- chrome.exe (PID: 3888)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 3888)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
62
Monitored processes
31
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,11386654071856108858,16858156815828479352,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=13051439283503718838 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13051439283503718838 --renderer-client-id=23 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2044 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,11386654071856108858,16858156815828479352,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=15795321865731001463 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15795321865731001463 --renderer-client-id=25 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5424 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,11386654071856108858,16858156815828479352,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7743291042983248886 --mojo-platform-channel-handle=3612 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,11386654071856108858,16858156815828479352,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=7806133884377563248 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7806133884377563248 --renderer-client-id=26 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5440 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 804 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,11386654071856108858,16858156815828479352,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=14477928771548421976 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14477928771548421976 --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=6312 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,11386654071856108858,16858156815828479352,131072 --enable-features=PasswordImport --service-pipe-token=431851497268286 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=431851497268286 --renderer-client-id=3 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2192 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1460 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3924 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1668 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,11386654071856108858,16858156815828479352,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=5637374274519997347 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5637374274519997347 --renderer-client-id=28 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=6092 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1712 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,11386654071856108858,16858156815828479352,131072 --enable-features=PasswordImport --service-pipe-token=3923432078359388444 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3923432078359388444 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1984 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2008 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,11386654071856108858,16858156815828479352,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=12113384557367518035 --mojo-platform-channel-handle=5412 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
610
Read events
506
Write events
99
Delete events
5
Modification events
| (PID) Process: | (3888) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3888) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3888) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3888) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3888) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1460) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3888-13200487284617000 |
Value: 259 | |||
| (PID) Process: | (3888) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3888) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3888) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (3888) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
319
Text files
206
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 3888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 3888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\47ee4d50-d972-4c29-8971-2d684da1b853.tmp | — | |
MD5:— | SHA256:— | |||
| 3888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3888 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
118
TCP/UDP connections
221
DNS requests
130
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3888 | chrome.exe | GET | 302 | 172.217.18.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 506 b | whitelisted |
3888 | chrome.exe | GET | 200 | 5.101.152.114:80 | http://hobby-country.ru/wp-content/plugins/theme-my-login/assets/styles/theme-my-login.min.css?ver=7.0.11 | RU | text | 462 b | suspicious |
3888 | chrome.exe | GET | 200 | 5.101.152.114:80 | http://hobby-country.ru/favicon.ico | RU | compressed | 65.9 Kb | suspicious |
3888 | chrome.exe | GET | 200 | 5.101.152.114:80 | http://hobby-country.ru/wp-content/themes/mesocolumn/lib/scripts/superfish-menu/css/superfish.css?ver=1.6.1 | RU | text | 1.70 Kb | suspicious |
3888 | chrome.exe | GET | 301 | 217.20.152.254:80 | http://stg.odnoklassniki.ru/share/odkl_share.css | RU | html | 179 b | whitelisted |
3888 | chrome.exe | GET | 200 | 5.101.152.114:80 | http://hobby-country.ru/wp-content/themes/mesocolumn/style.css | RU | text | 13.5 Kb | suspicious |
3888 | chrome.exe | GET | 200 | 173.194.139.6:80 | http://r1---sn-aigzrn7k.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.230.125.140&mm=28&mn=sn-aigzrn7k&ms=nvh&mt=1556013614&mv=m&pl=24&shardbypass=yes | US | crx | 842 Kb | whitelisted |
3888 | chrome.exe | GET | 200 | 5.101.152.114:80 | http://hobby-country.ru/ | RU | html | 19.9 Kb | suspicious |
3888 | chrome.exe | GET | 200 | 5.101.152.114:80 | http://hobby-country.ru/wp-content/plugins/scroll-button/assets/scroll_up_style.css?ver=1.0.0 | RU | text | 169 b | suspicious |
3888 | chrome.exe | GET | 301 | 217.20.152.254:80 | http://stg.odnoklassniki.ru/share/odkl_share.js?ver=4.9.10 | RU | html | 179 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3888 | chrome.exe | 5.101.152.114:80 | hobby-country.ru | Beget Ltd | RU | suspicious |
3888 | chrome.exe | 216.58.207.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3888 | chrome.exe | 172.217.21.205:443 | accounts.google.com | Google Inc. | US | whitelisted |
3888 | chrome.exe | 172.217.18.100:443 | www.google.com | Google Inc. | US | whitelisted |
3888 | chrome.exe | 172.217.16.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
3888 | chrome.exe | 172.217.18.14:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
3888 | chrome.exe | 173.194.139.6:80 | r1---sn-aigzrn7k.gvt1.com | Google Inc. | US | whitelisted |
3888 | chrome.exe | 172.217.18.99:443 | www.google.ch | Google Inc. | US | whitelisted |
— | — | 93.184.220.66:80 | platform.twitter.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
— | — | 217.20.152.254:80 | stg.odnoklassniki.ru | Limited liability company Mail.Ru | RU | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
hobby-country.ru |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r1---sn-aigzrn7k.gvt1.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.google.ch |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3888 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
3888 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
3888 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |