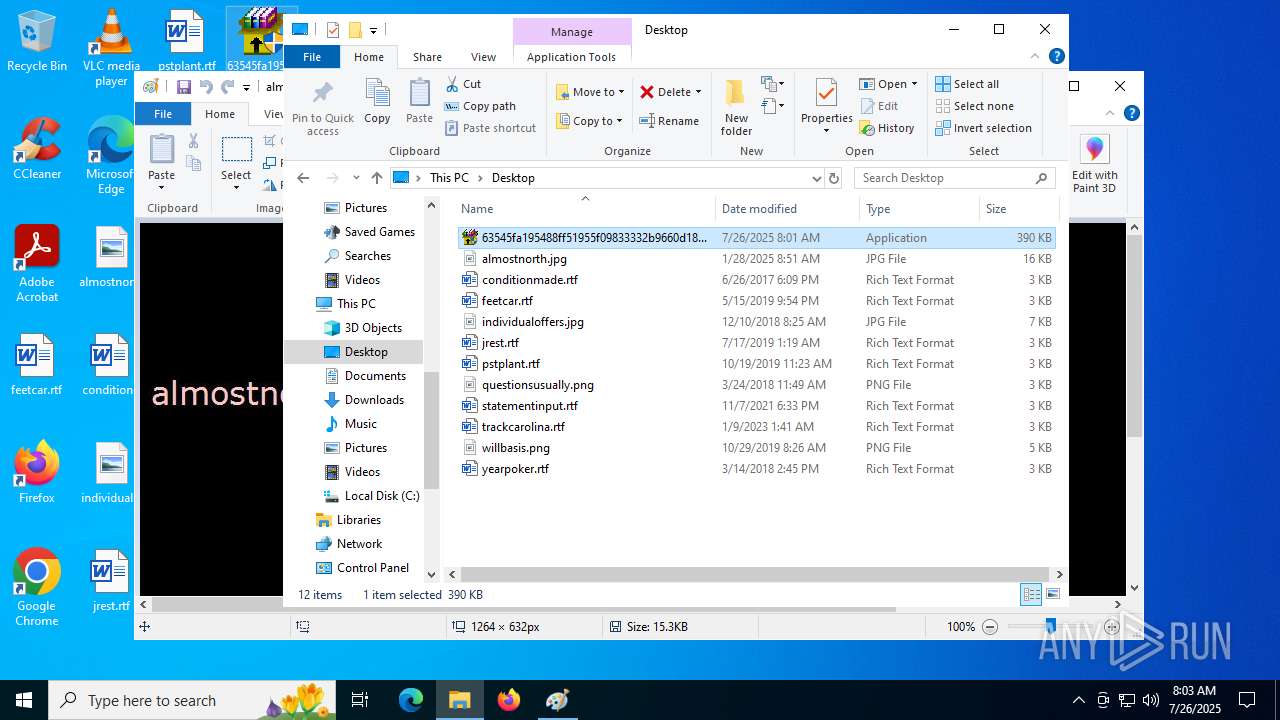
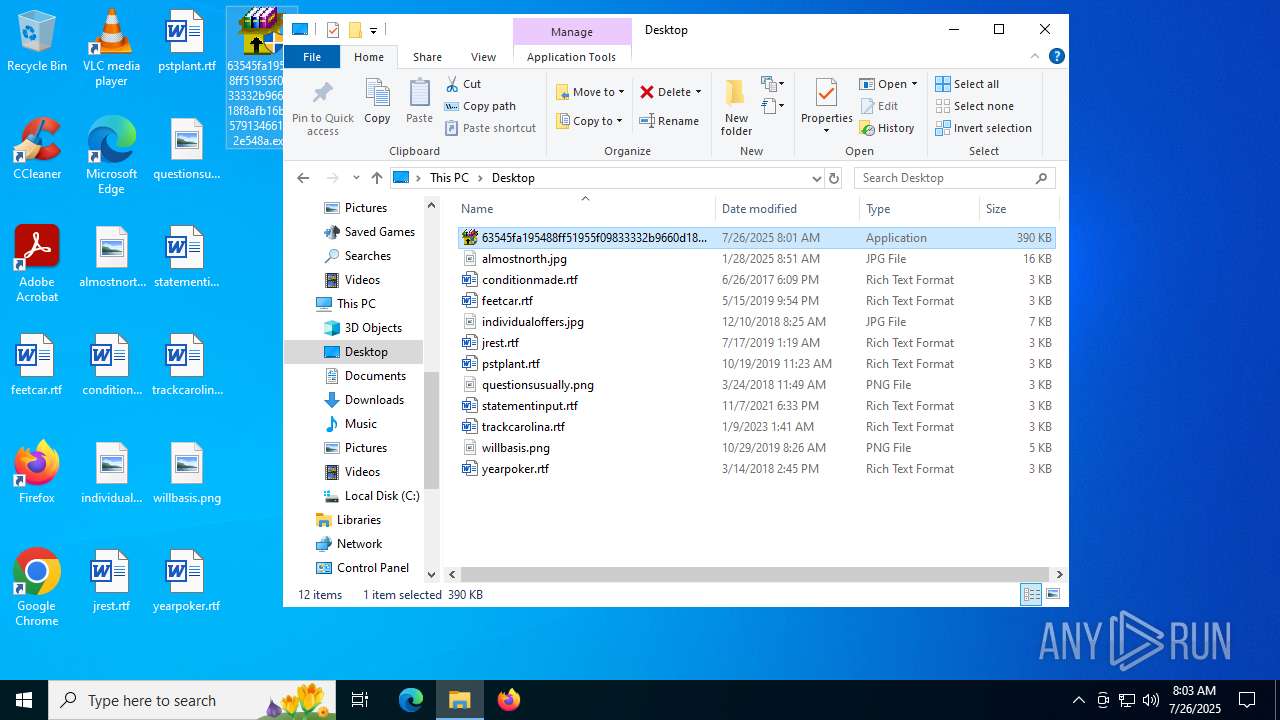
| File name: | 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe |
| Full analysis: | https://app.any.run/tasks/18565e99-3bdd-47ab-a4d3-4155c44e75b9 |
| Verdict: | Malicious activity |
| Analysis date: | July 26, 2025, 08:01:34 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | 5B7E6E352BACC93F7B80BC968B6EA493 |
| SHA1: | E686139D5ED8528117BA6CA68FE415E4FB02F2BE |
| SHA256: | 63545FA195488FF51955F09833332B9660D18F8AFB16BDF579134661962E548A |
| SSDEEP: | 12288:ef/X4NTS/x9jNG+w+9OqFoK323qdQYKU31:EXATS/x9jNg+95vdQa1 |
MALICIOUS
Uses Task Scheduler to run other applications
- cmd.exe (PID: 4412)
SUSPICIOUS
Reads security settings of Internet Explorer
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 984)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 3836)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 4708)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 4160)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 6796)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 2460)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 6104)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 6780)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 4512)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 5368)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 5744)
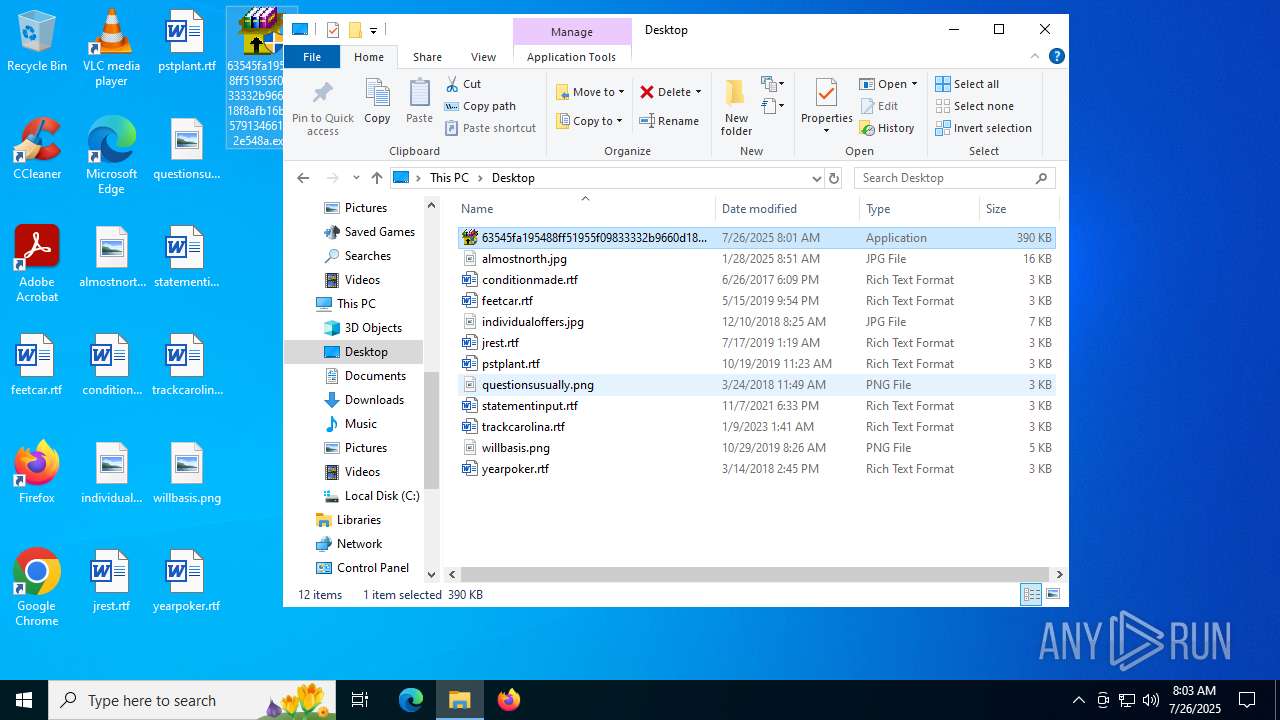
Executable content was dropped or overwritten
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 984)
- rundll32.exe (PID: 5252)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 3836)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 4160)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 6796)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 6104)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 2460)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 6780)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 4512)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 5368)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 5744)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 4708)
Starts application with an unusual extension
- rundll32.exe (PID: 5252)
Starts CMD.EXE for commands execution
- rundll32.exe (PID: 5252)
INFO
Checks supported languages
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 984)
- D28D.tmp (PID: 3844)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 3836)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 4708)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 6796)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 2460)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 4160)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 6104)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 6780)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 4512)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 5368)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 5744)
Reads the computer name
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 984)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 3836)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 4708)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 4160)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 6796)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 2460)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 6104)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 6780)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 4512)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 5368)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 5744)
Create files in a temporary directory
- rundll32.exe (PID: 5252)
Process checks computer location settings
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 984)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 4708)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 4160)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 6796)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 2460)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 6104)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 6780)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 4512)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 5368)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 5744)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 3836)
Launching a file from Task Scheduler
- cmd.exe (PID: 4412)
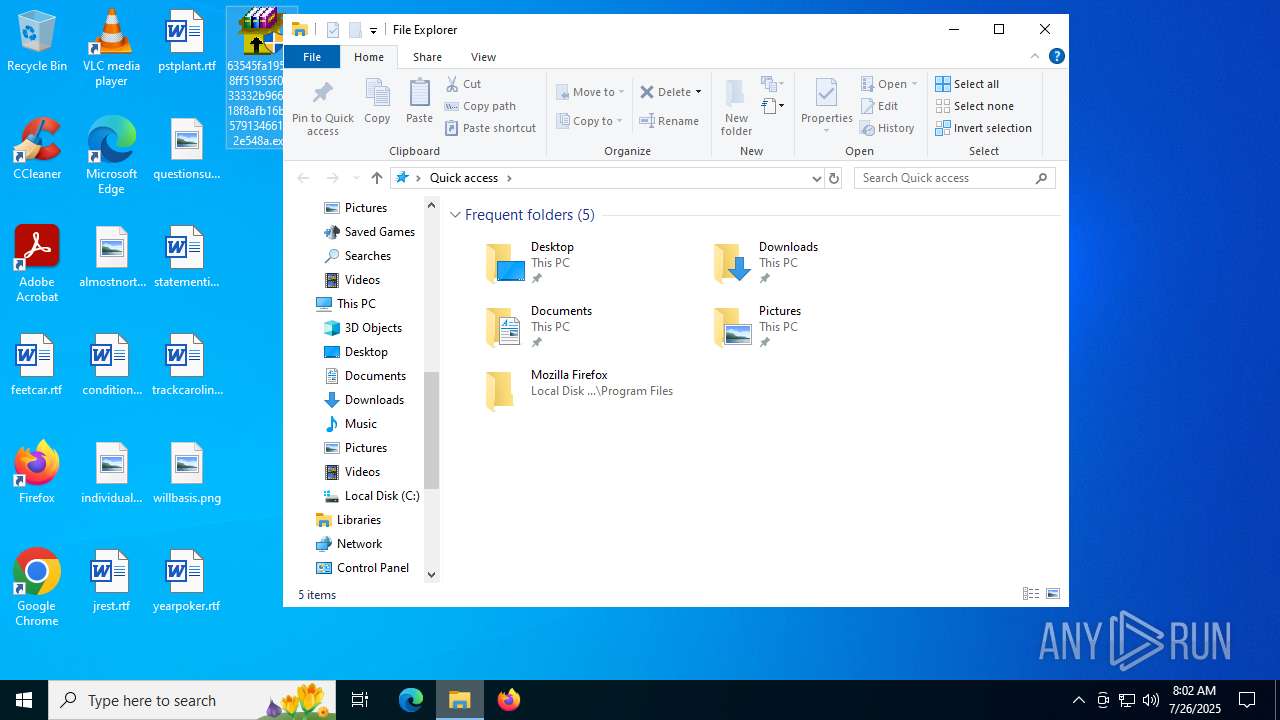
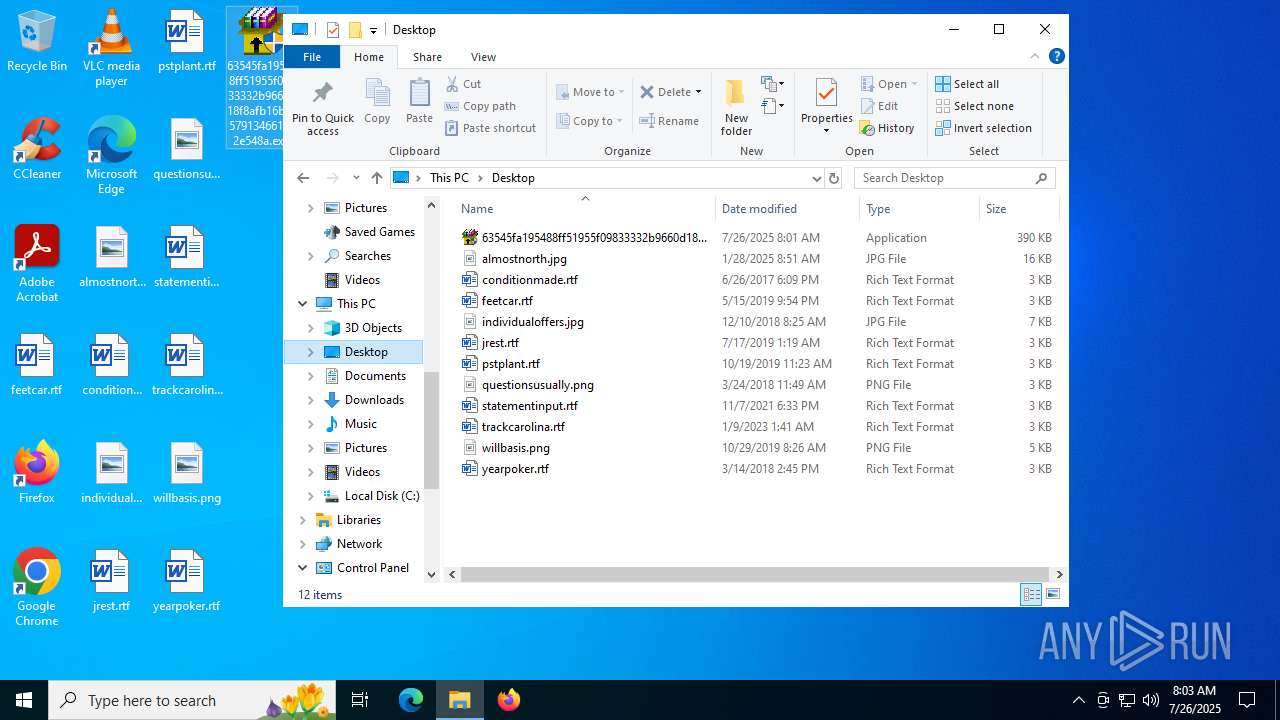
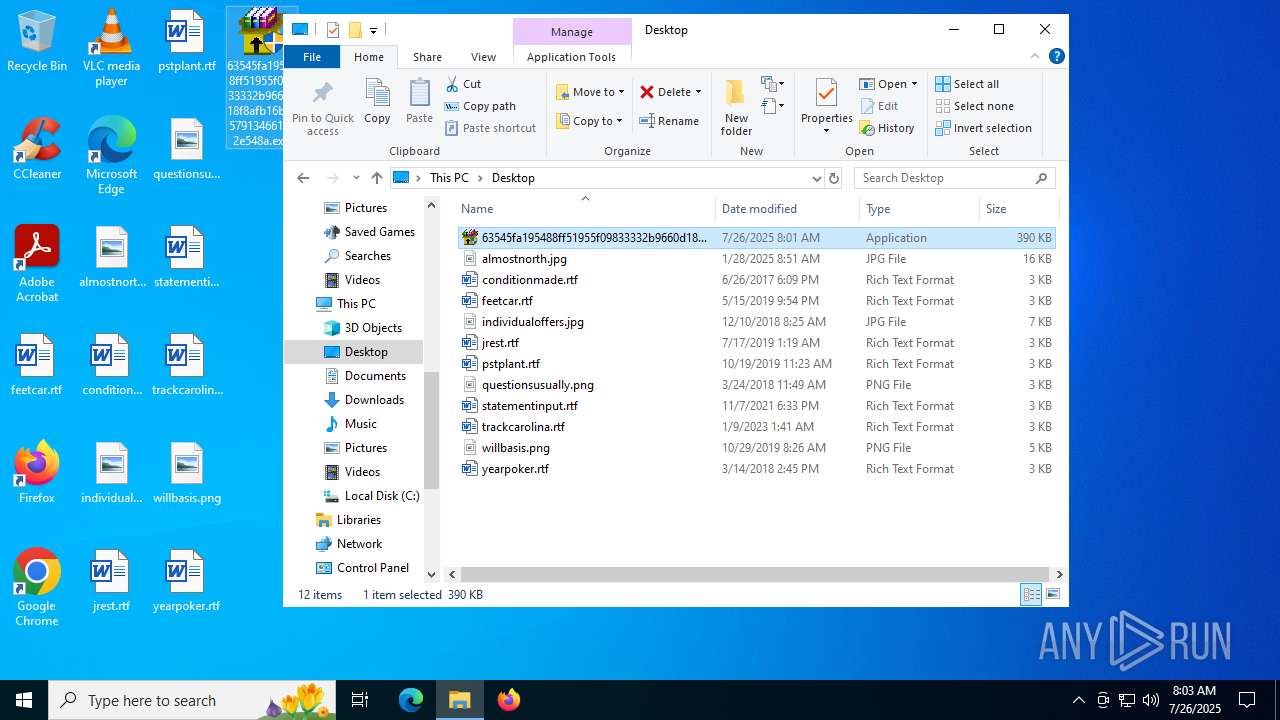
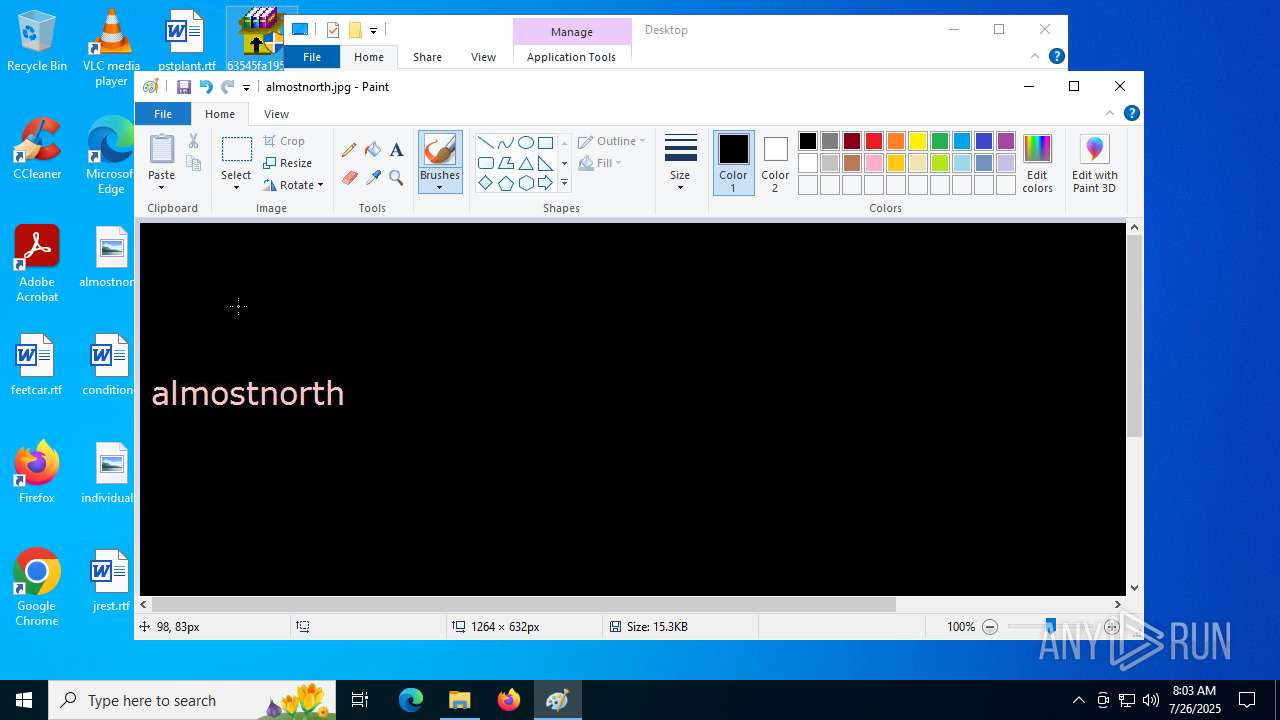
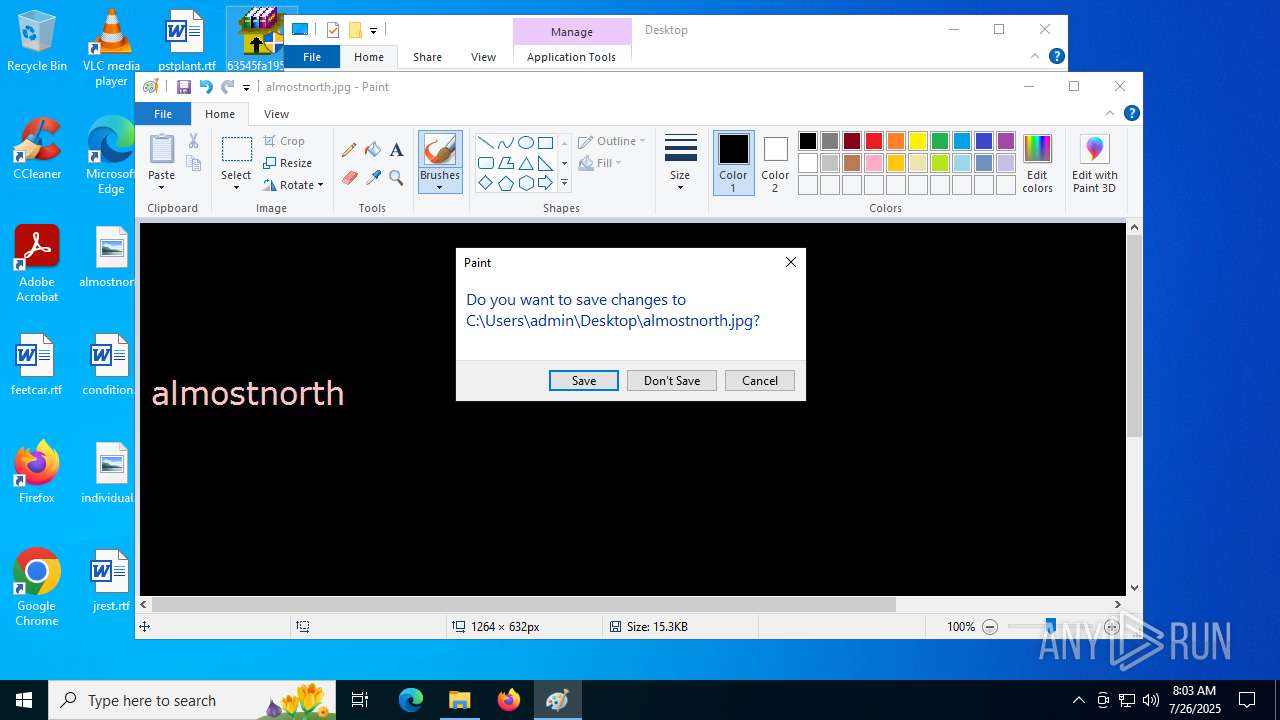
Manual execution by a user
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 6780)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 3836)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 4708)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 4160)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 2972)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 6796)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 2460)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 4456)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 2428)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 6104)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 3576)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 6780)
- mspaint.exe (PID: 6584)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 4512)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 1036)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 3556)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 5368)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 72)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 5744)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 3960)
- 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe (PID: 4788)
Checks proxy server information
- rundll32.exe (PID: 5252)
The sample compiled with english language support
- rundll32.exe (PID: 5252)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:01:16 20:40:23+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 17920 |
| InitializedDataSize: | 380416 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x128b |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
188
Monitored processes
41
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 72 | "C:\Users\admin\Desktop\63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe" | C:\Users\admin\Desktop\63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 984 | "C:\Users\admin\Desktop\63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe" | C:\Users\admin\Desktop\63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 42 Modules
| |||||||||||||||
| 1036 | "C:\Users\admin\Desktop\63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe" | C:\Users\admin\Desktop\63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1056 | "C:\Users\admin\Desktop\63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe" | C:\Users\admin\Desktop\63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 1132 | "C:\Windows\System32\rundll32.exe" C:\WINDOWS\perfc.dat #1 | C:\Windows\SysWOW64\rundll32.exe | — | 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1148 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | D28D.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2148 | schtasks /Create /SC once /TN "" /TR "C:\WINDOWS\system32\shutdown.exe /r /f" /ST 09:04 | C:\Windows\SysWOW64\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2148 | "C:\Windows\System32\rundll32.exe" C:\WINDOWS\perfc.dat #1 | C:\Windows\SysWOW64\rundll32.exe | — | 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2428 | "C:\Users\admin\Desktop\63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe" | C:\Users\admin\Desktop\63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2460 | "C:\Users\admin\Desktop\63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe" | C:\Users\admin\Desktop\63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 42 Modules
| |||||||||||||||
Total events
7 314
Read events
7 285
Write events
28
Delete events
1
Modification events
| (PID) Process: | (6584) mspaint.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Applets\Paint\View |
| Operation: | write | Name: | WindowPlacement |
Value: 2C00000000000000010000000000000000000000FFFFFFFFFFFFFFFF7F000000470000007F04000087020000 | |||
| (PID) Process: | (6584) mspaint.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Applets\Paint\View |
| Operation: | write | Name: | ShowThumbnail |
Value: 0 | |||
| (PID) Process: | (6584) mspaint.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Applets\Paint\View |
| Operation: | write | Name: | BMPWidth |
Value: 0 | |||
| (PID) Process: | (6584) mspaint.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Applets\Paint\View |
| Operation: | write | Name: | BMPHeight |
Value: 0 | |||
| (PID) Process: | (6584) mspaint.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Applets\Paint\View |
| Operation: | write | Name: | ThumbXPos |
Value: 0 | |||
| (PID) Process: | (6584) mspaint.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Applets\Paint\View |
| Operation: | write | Name: | ThumbYPos |
Value: 0 | |||
| (PID) Process: | (6584) mspaint.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Applets\Paint\View |
| Operation: | write | Name: | ThumbWidth |
Value: 0 | |||
| (PID) Process: | (6584) mspaint.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Applets\Paint\View |
| Operation: | write | Name: | ThumbHeight |
Value: 0 | |||
| (PID) Process: | (6584) mspaint.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Applets\Paint\View |
| Operation: | write | Name: | UnitSetting |
Value: 0 | |||
| (PID) Process: | (6584) mspaint.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Applets\Paint\View |
| Operation: | write | Name: | ShowRulers |
Value: 0 | |||
Executable files
13
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5252 | rundll32.exe | \Device\HarddiskVolume2 | — | |
MD5:— | SHA256:— | |||
| 5252 | rundll32.exe | \Device\Harddisk0\DR0 | — | |
MD5:— | SHA256:— | |||
| 5744 | 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe | C:\Windows\perfc.dat | executable | |
MD5:71B6A493388E7D0B40C83CE903BC6B04 | SHA256:027CC450EF5F8C5F653329641EC1FED91F694E0D229928963B30F6B0D7D3A745 | |||
| 6796 | 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe | C:\Windows\perfc.dat | executable | |
MD5:71B6A493388E7D0B40C83CE903BC6B04 | SHA256:027CC450EF5F8C5F653329641EC1FED91F694E0D229928963B30F6B0D7D3A745 | |||
| 984 | 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe | C:\Windows\perfc.dat | executable | |
MD5:71B6A493388E7D0B40C83CE903BC6B04 | SHA256:027CC450EF5F8C5F653329641EC1FED91F694E0D229928963B30F6B0D7D3A745 | |||
| 6780 | 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe | C:\Windows\perfc.dat | executable | |
MD5:71B6A493388E7D0B40C83CE903BC6B04 | SHA256:027CC450EF5F8C5F653329641EC1FED91F694E0D229928963B30F6B0D7D3A745 | |||
| 5252 | rundll32.exe | C:\Windows\dllhost.dat | executable | |
MD5:AEEE996FD3484F28E5CD85FE26B6BDCD | SHA256:F8DBABDFA03068130C277CE49C60E35C029FF29D9E3C74C362521F3FB02670D5 | |||
| 5252 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\D28D.tmp | executable | |
MD5:7E37AB34ECDCC3E77E24522DDFD4852D | SHA256:02EF73BD2458627ED7B397EC26EE2DE2E92C71A0E7588F78734761D8EDBDCD9F | |||
| 4708 | 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe | C:\Windows\perfc.dat | executable | |
MD5:71B6A493388E7D0B40C83CE903BC6B04 | SHA256:027CC450EF5F8C5F653329641EC1FED91F694E0D229928963B30F6B0D7D3A745 | |||
| 4160 | 63545fa195488ff51955f09833332b9660d18f8afb16bdf579134661962e548a.exe | C:\Windows\perfc.dat | executable | |
MD5:71B6A493388E7D0B40C83CE903BC6B04 | SHA256:027CC450EF5F8C5F653329641EC1FED91F694E0D229928963B30F6B0D7D3A745 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
49
DNS requests
17
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5724 | svchost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3672 | SIHClient.exe | GET | 200 | 2.21.54.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 92.123.133.198:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3672 | SIHClient.exe | GET | 200 | 2.21.54.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 23.60.189.126:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.21.54.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
684 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.2:445 | — | — | — | whitelisted |
4 | System | 192.168.100.2:139 | — | — | — | whitelisted |
4 | System | 192.168.100.2:137 | — | — | — | whitelisted |
5252 | rundll32.exe | 192.168.100.1:445 | — | — | — | unknown |
5724 | svchost.exe | 40.126.31.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |