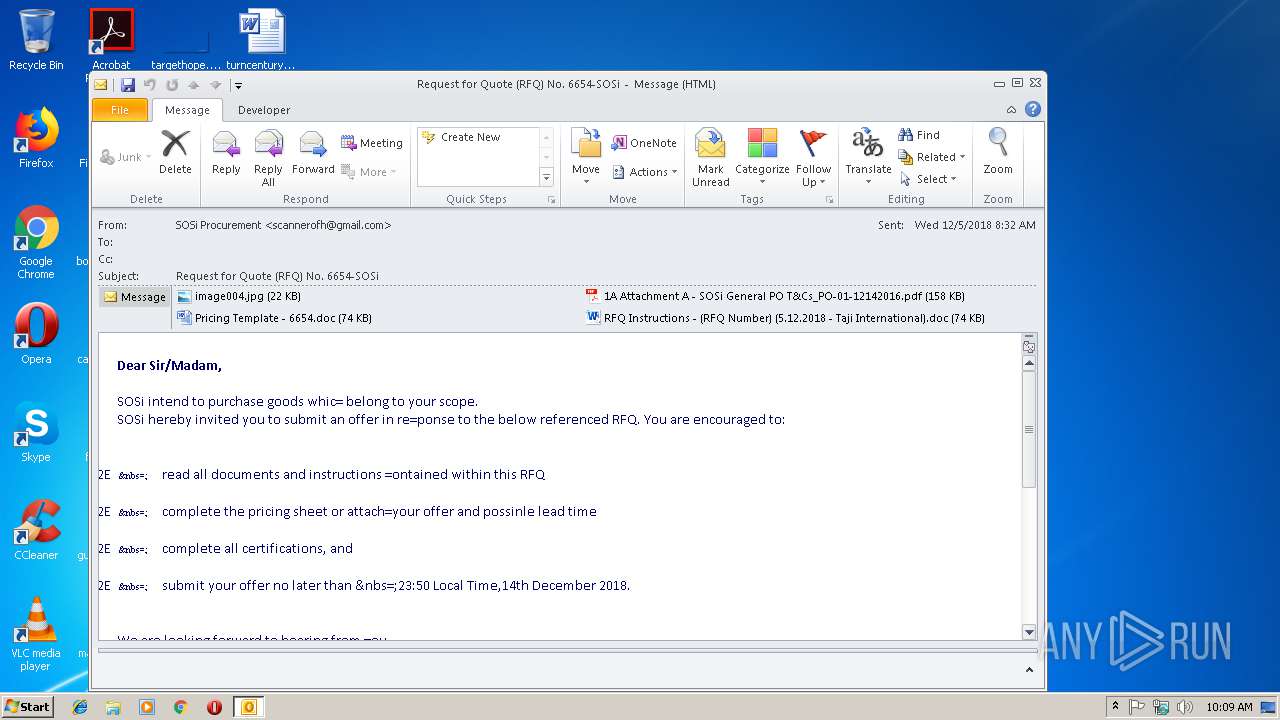
| File name: | Request for Quote (RFQ) No. 6654-SOSi.eml |
| Full analysis: | https://app.any.run/tasks/5320ae3a-0eae-4680-aacc-f45302d08660 |
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2018, 10:09:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | SMTP mail, ASCII text |
| MD5: | 2C893E97CA92CEA617A1743B5A188217 |
| SHA1: | F42FC3C1CA7B60B42899A71BFEAAAE7367681648 |
| SHA256: | 63395420E6C6BAD3A9F79116FEE0D1B86F8B52DAA4B76F93AEF2732436DDBEBE |
| SSDEEP: | 6144:NkM0HPIGY+Ms3d6SVuUe1X/+FXcuD62zfPD7DFl0mzpk4XgD+Mpx:uvIGzB3o2uzWFXd62zXD7kyk4QD1px |
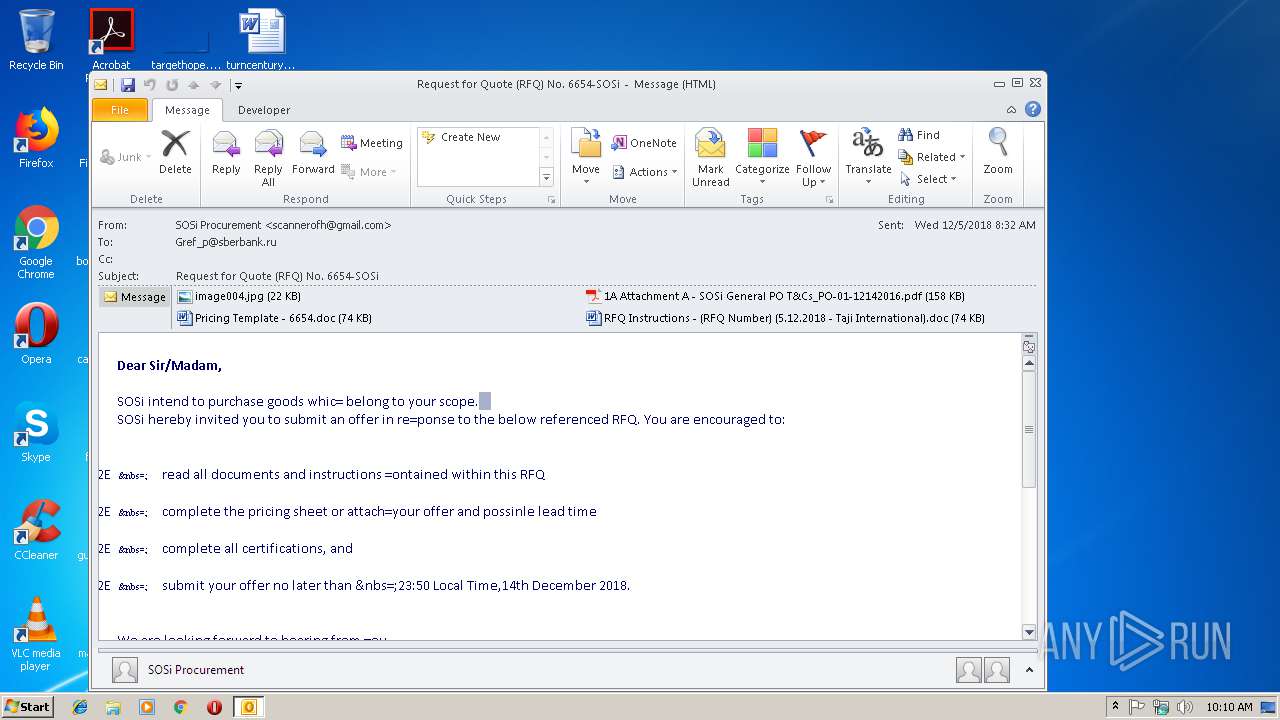
MALICIOUS
Suspicious connection from the Equation Editor
- EQNEDT32.EXE (PID: 3804)
SUSPICIOUS
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2864)
Starts Microsoft Office Application
- OUTLOOK.EXE (PID: 2864)
- WINWORD.EXE (PID: 2580)
Creates files in the user directory
- OUTLOOK.EXE (PID: 2864)
- EQNEDT32.EXE (PID: 3804)
Application launched itself
- WINWORD.EXE (PID: 2580)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2864)
- WINWORD.EXE (PID: 2824)
- WINWORD.EXE (PID: 2152)
- WINWORD.EXE (PID: 2580)
Creates files in the user directory
- WINWORD.EXE (PID: 2580)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 1) (100) |
|---|
Total processes
36
Monitored processes
5
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2152 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
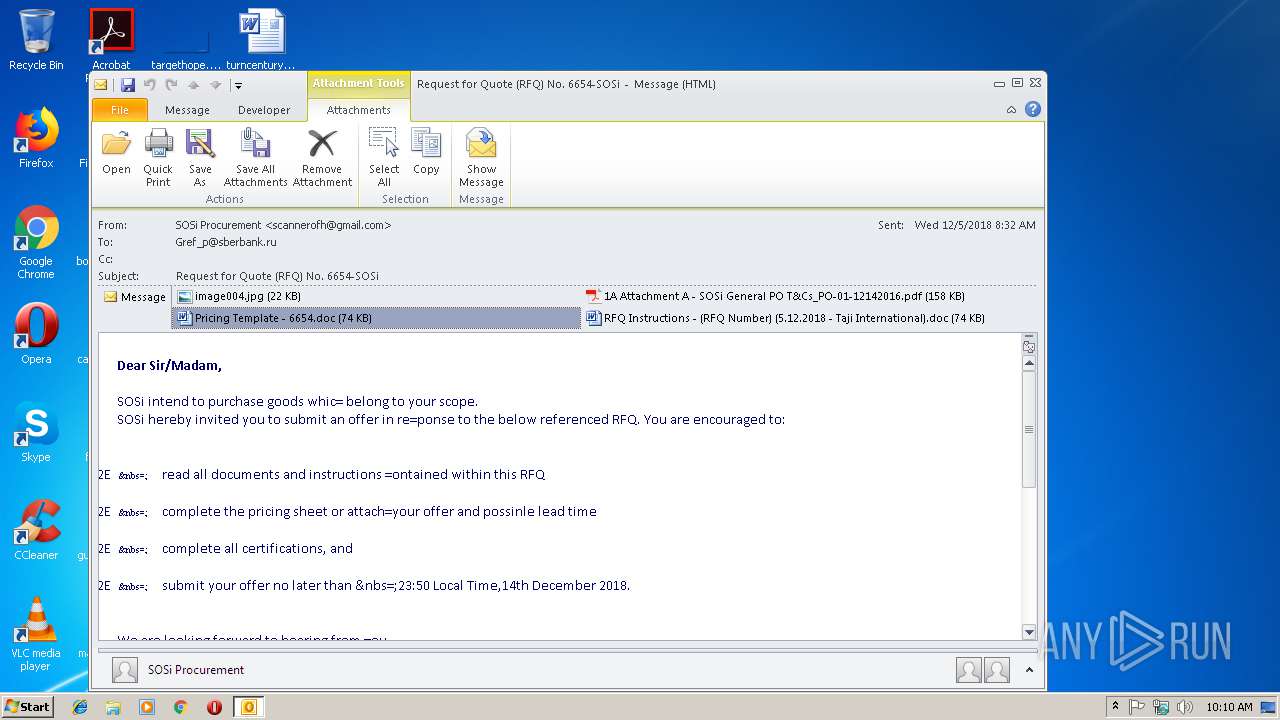
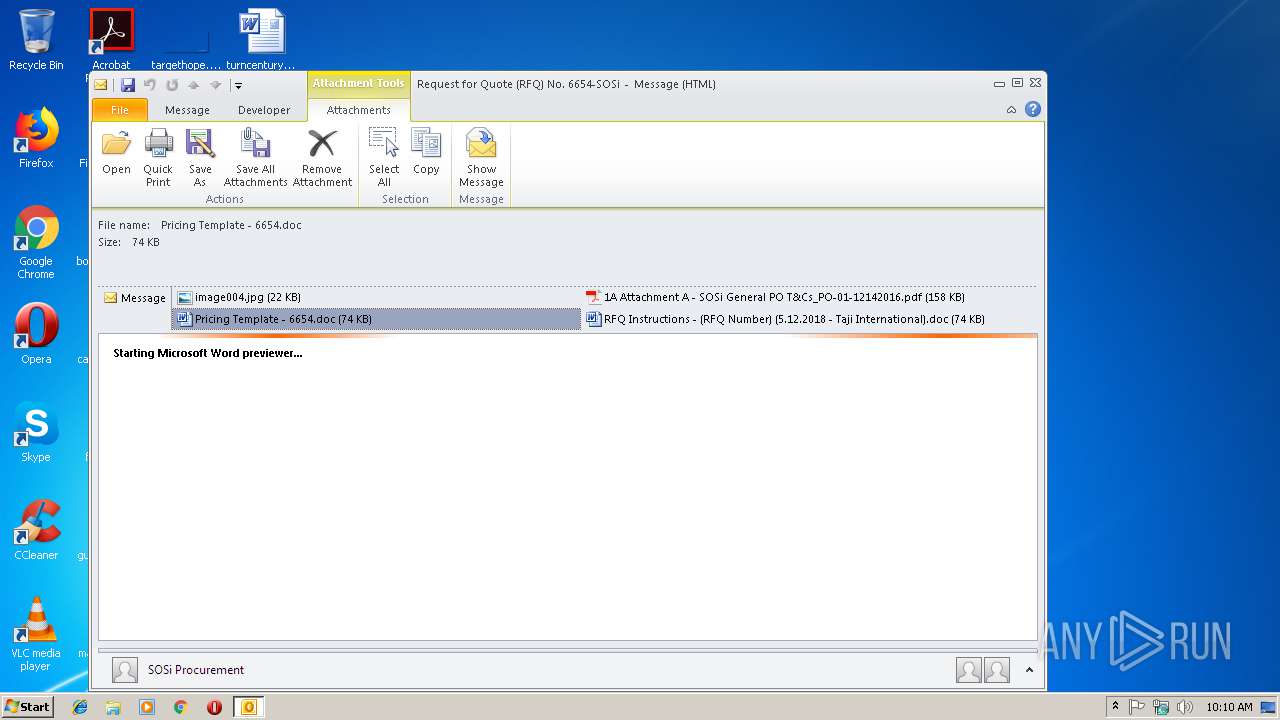
| 2580 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\WFYBA366\Pricing Template - 6654.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2824 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2864 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\Request for Quote (RFQ) No. 6654-SOSi.eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 3804 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
Total events
2 842
Read events
2 372
Write events
447
Delete events
23
Modification events
| (PID) Process: | (2864) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2864) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2864) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | i$ |
Value: 7F692400300B0000010000000000000000000000 | |||
| (PID) Process: | (2864) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: 300B000040B2FFCC4B8DD40100000000 | |||
| (PID) Process: | (2864) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (2864) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 219808800 | |||
| (PID) Process: | (2864) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (2864) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (2864) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (2864) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1300627477 | |||
Executable files
0
Suspicious files
1
Text files
28
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2864 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR9570.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2864 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\tmp9774.tmp | — | |
MD5:— | SHA256:— | |||
| 2864 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\WFYBA366\Pricing Template - 6654 (2).doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2580 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR4807.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2864 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\OICE_CFD4BD2C-D930-4667-88E7-FC3D77851E90.0\BE328396.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2580 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_BC836785-F13D-469D-A8B5-BFF75FBF36CB.0\E01E0C9.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2864 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2864 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\mapisvc.inf | text | |
MD5:48DD6CAE43CE26B992C35799FCD76898 | SHA256:7BFE1F3691E2B4FB4D61FBF5E9F7782FBE49DA1342DBD32201C2CC8E540DBD1A | |||
| 2864 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_WorkHours_1_9C18D7EA1A94D34EBF1D927853057A5A.dat | xml | |
MD5:807EF0FC900FEB3DA82927990083D6E7 | SHA256:4411E7DC978011222764943081500FFF0E43CBF7CCD44264BD1AB6306CA68913 | |||
| 2580 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_BC836785-F13D-469D-A8B5-BFF75FBF36CB.0\E01E0C9.doc | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3804 | EQNEDT32.EXE | GET | 404 | 67.199.248.10:80 | http://bit.ly/2zxTNE5 | US | xml | 345 b | shared |
2864 | OUTLOOK.EXE | GET | 404 | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | xml | 345 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2864 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
3804 | EQNEDT32.EXE | 67.199.248.10:80 | bit.ly | Bitly Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
bit.ly |
| shared |