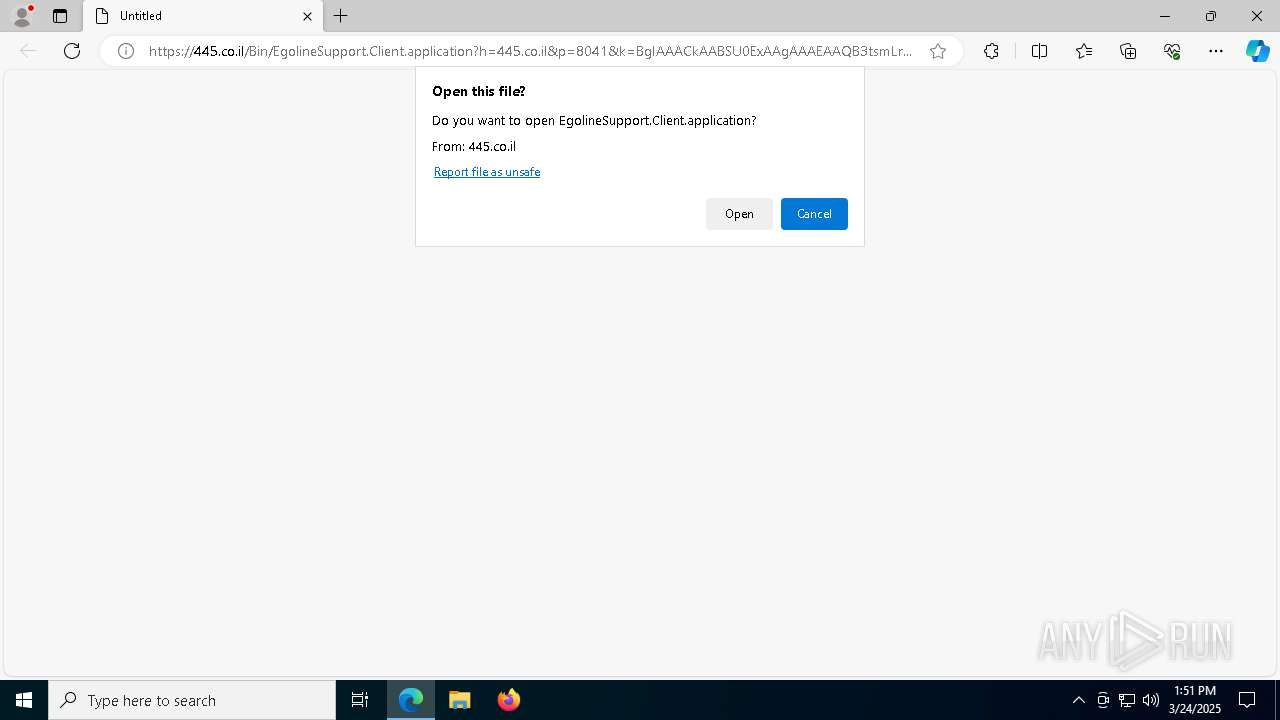
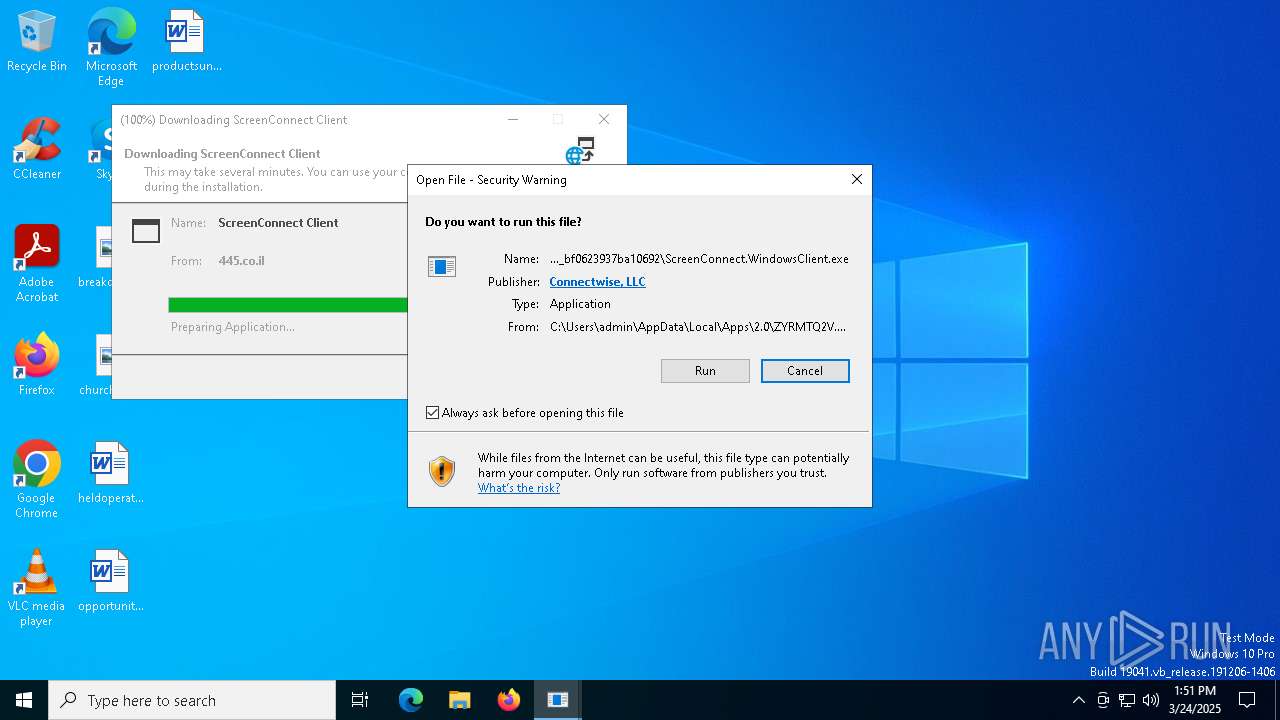
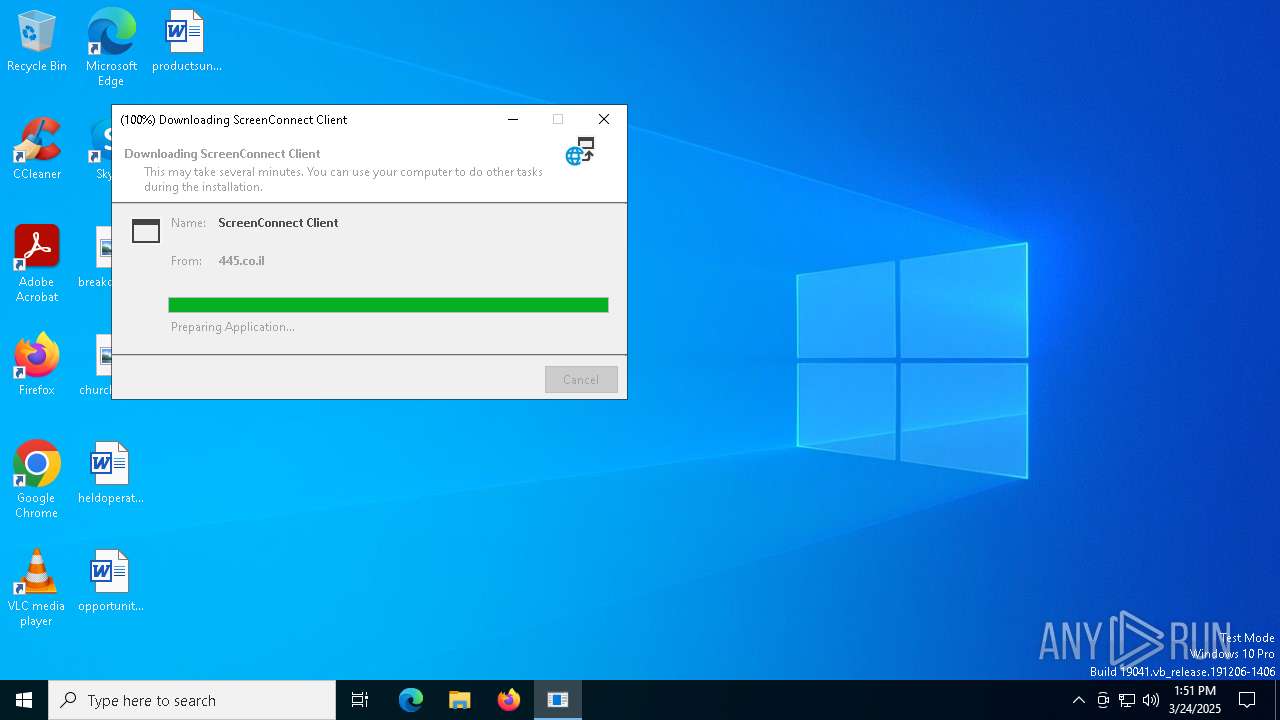
| URL: | https://445.co.il/Bin/EgolineSupport.Client.application?h=445.co.il&p=8041&k=BgIAAACkAABSU0ExAAgAAAEAAQB3tsmLrnXacgYd78dXvRv%2FNW2D8dNTYxhB4rhKYAi47b9LF19VyVogEb7dPfYComJGJW19oJfG4%2B4CLzEF12oT4V6ucc9ZBAPfZWP9L6nq6jOB82aUdYavDsGYa7J3dRnRghVYBK1pRVP7TV7vBRPEr8FAjGEhRzfG12cBAWfIdqDt5kAFG9iE5ly6XKf7OTu8qz1EJm0yVx65YCmOKMkH2%2FKh5gEkXnoS6LIgW%2BPS3smOklTolNdJSaRdidLivb8HeUJDgorfd2FVbnuwl6tr7XhN2UMvNHnW7GCSTCPLXC1AMNxs7cAkD8M7UnoGqg3tXUKQh3lp9MeIDw2f8hOt&s=e23921c1-94cc-4030-bebb-713b987343a6&i=Untitled%20Session&e=Support&y=Guest&r= |
| Full analysis: | https://app.any.run/tasks/885bd02a-ad2e-42cf-b9e1-91008ce2eacf |
| Verdict: | Malicious activity |
| Analysis date: | March 24, 2025, 13:51:20 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C73693AFD3943BC6238C0099D00DAAB0 |
| SHA1: | 3A90FD6339BDB139C66DB30D05816841088A1EDC |
| SHA256: | 632A7CABD403923DEB4E90C481B3D43413DD8E5E11B781E74D44ADC39C5947F5 |
| SSDEEP: | 12:2BGmqLCsS1fSDWg0VOWDssC7/ZBNOdbDVRyvNzOpSjlIRtM:2krSYWgmDNCtqV8ORK |
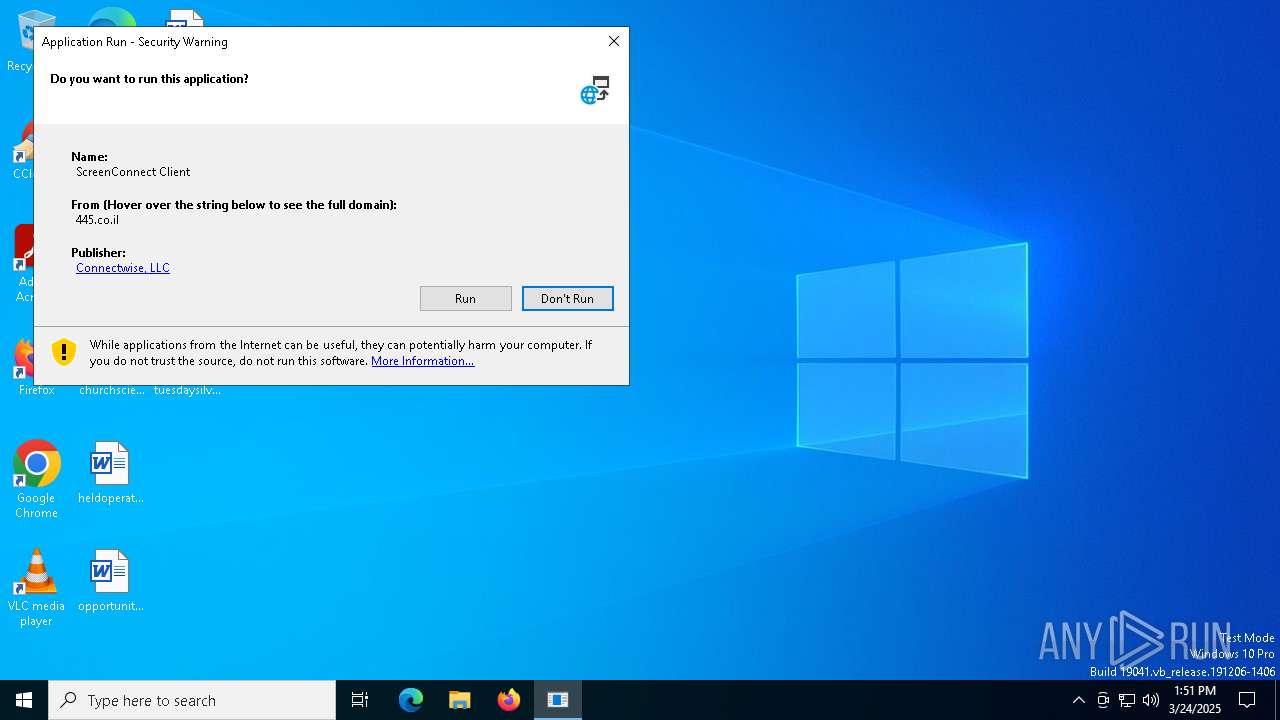
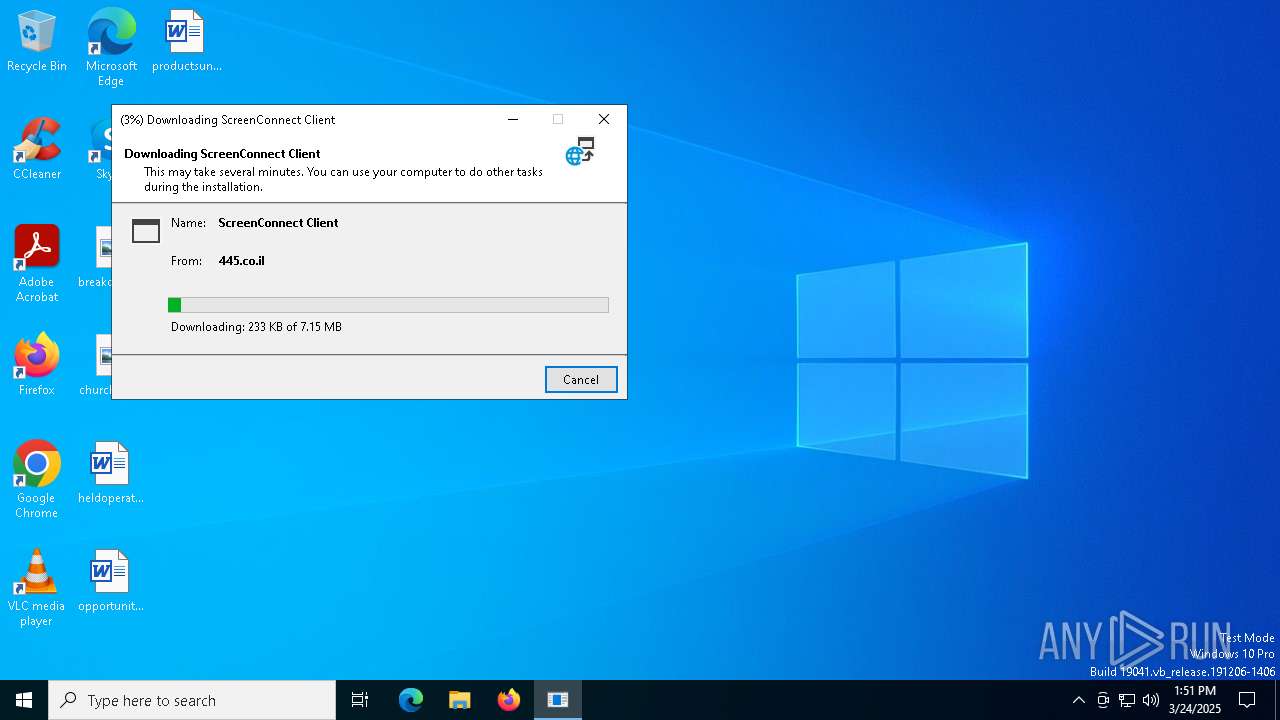
MALICIOUS
SCREENCONNECT has been detected (SURICATA)
- ScreenConnect.ClientService.exe (PID: 1660)
SUSPICIOUS
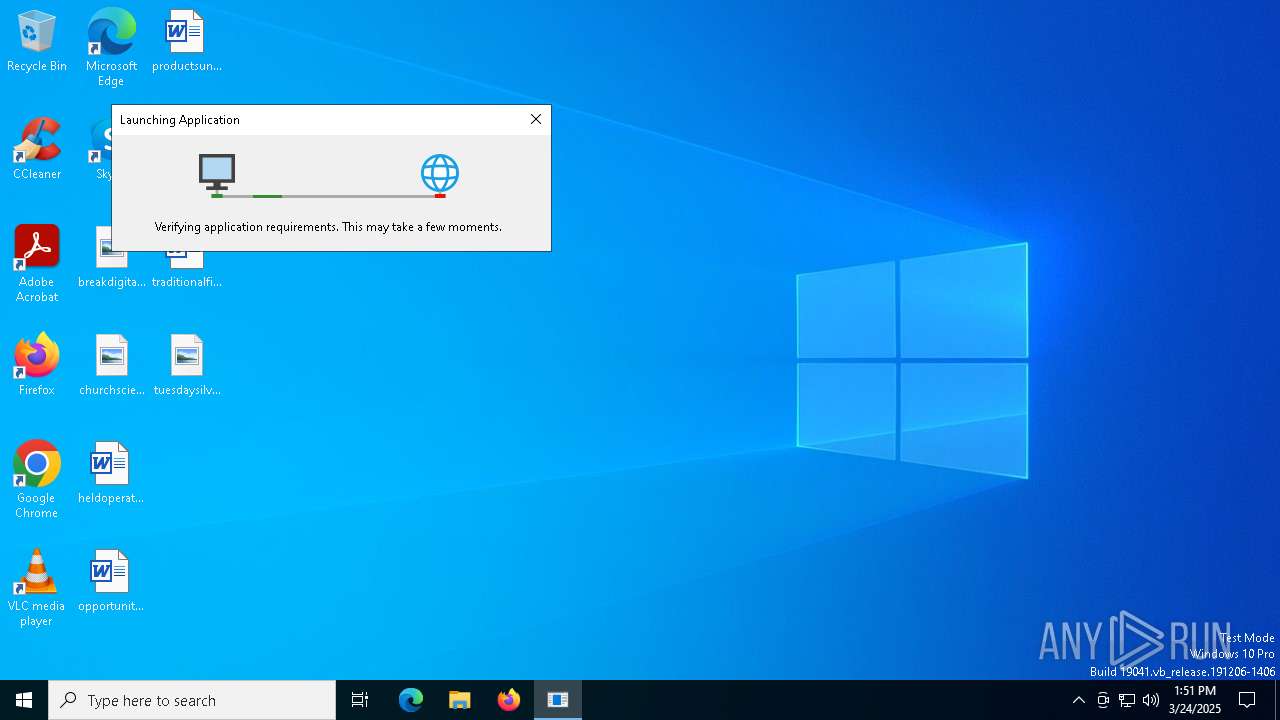
Uses RUNDLL32.EXE to load library
- msedge.exe (PID: 7196)
Executable content was dropped or overwritten
- dfsvc.exe (PID: 6272)
Reads security settings of Internet Explorer
- dfsvc.exe (PID: 6272)
The process creates files with name similar to system file names
- dfsvc.exe (PID: 6272)
Executes as Windows Service
- ScreenConnect.ClientService.exe (PID: 1660)
SCREENCONNECT mutex has been found
- ScreenConnect.ClientService.exe (PID: 1660)
Potential Corporate Privacy Violation
- ScreenConnect.ClientService.exe (PID: 1660)
Connects to unusual port
- ScreenConnect.ClientService.exe (PID: 1660)
INFO
Reads Environment values
- identity_helper.exe (PID: 4988)
- dfsvc.exe (PID: 6272)
Application launched itself
- msedge.exe (PID: 7196)
- msedge.exe (PID: 8016)
Reads the computer name
- identity_helper.exe (PID: 4988)
- dfsvc.exe (PID: 6272)
- ScreenConnect.ClientService.exe (PID: 1660)
Checks supported languages
- identity_helper.exe (PID: 4988)
- dfsvc.exe (PID: 6272)
- identity_helper.exe (PID: 4436)
- ScreenConnect.ClientService.exe (PID: 1660)
Checks proxy server information
- dfsvc.exe (PID: 6272)
Reads the software policy settings
- dfsvc.exe (PID: 6272)
Create files in a temporary directory
- dfsvc.exe (PID: 6272)
Creates files or folders in the user directory
- dfsvc.exe (PID: 6272)
Reads the machine GUID from the registry
- dfsvc.exe (PID: 6272)
- ScreenConnect.WindowsClient.exe (PID: 2644)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
181
Monitored processes
43
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 684 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4020 --field-trial-handle=2352,i,8235242058010160773,6136121977889065533,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1328 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x294,0x298,0x29c,0x290,0x2a4,0x7ffc886b5fd8,0x7ffc886b5fe4,0x7ffc886b5ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1512 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1660 | "C:\Users\admin\AppData\Local\Apps\2.0\ZYRMTQ2V.Q22\PPG1BX2D.337\scre..tion_25b0fbb6ef7eb094_0018.0003_bf0623937ba10692\ScreenConnect.ClientService.exe" "?e=Support&y=Guest&h=445.co.il&p=8041&s=e23921c1-94cc-4030-bebb-713b987343a6&k=BgIAAACkAABSU0ExAAgAAAEAAQB3tsmLrnXacgYd78dXvRv%2fNW2D8dNTYxhB4rhKYAi47b9LF19VyVogEb7dPfYComJGJW19oJfG4%2b4CLzEF12oT4V6ucc9ZBAPfZWP9L6nq6jOB82aUdYavDsGYa7J3dRnRghVYBK1pRVP7TV7vBRPEr8FAjGEhRzfG12cBAWfIdqDt5kAFG9iE5ly6XKf7OTu8qz1EJm0yVx65YCmOKMkH2%2fKh5gEkXnoS6LIgW%2bPS3smOklTolNdJSaRdidLivb8HeUJDgorfd2FVbnuwl6tr7XhN2UMvNHnW7GCSTCPLXC1AMNxs7cAkD8M7UnoGqg3tXUKQh3lp9MeIDw2f8hOt&r=&i=Untitled%20Session" "5" | C:\Users\admin\AppData\Local\Apps\2.0\ZYRMTQ2V.Q22\PPG1BX2D.337\scre..tion_25b0fbb6ef7eb094_0018.0003_bf0623937ba10692\ScreenConnect.ClientService.exe | services.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Version: 24.3.3.9011 Modules
| |||||||||||||||
| 2136 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2644 | "C:\Users\admin\AppData\Local\Apps\2.0\ZYRMTQ2V.Q22\PPG1BX2D.337\scre..tion_25b0fbb6ef7eb094_0018.0003_bf0623937ba10692\ScreenConnect.WindowsClient.exe" "RunRole" "ea02d625-0805-4e31-b1c1-8314866e53f0" "System" | C:\Users\admin\AppData\Local\Apps\2.0\ZYRMTQ2V.Q22\PPG1BX2D.337\scre..tion_25b0fbb6ef7eb094_0018.0003_bf0623937ba10692\ScreenConnect.WindowsClient.exe | — | ScreenConnect.ClientService.exe | |||||||||||
User: SYSTEM Company: ScreenConnect Software Integrity Level: SYSTEM Description: ScreenConnect Client Version: 24.3.3.9011 Modules
| |||||||||||||||
| 2692 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5160 --field-trial-handle=2352,i,8235242058010160773,6136121977889065533,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 4008 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6148 --field-trial-handle=2296,i,6089744857865095433,6895278052913908865,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 4108 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2492 --field-trial-handle=2352,i,8235242058010160773,6136121977889065533,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 4424 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://445.co.il/Bin/EgolineSupport.Client.application?h=445.co.il&p=8041&k=BgIAAACkAABSU0ExAAgAAAEAAQB3tsmLrnXacgYd78dXvRv%2FNW2D8dNTYxhB4rhKYAi47b9LF19VyVogEb7dPfYComJGJW19oJfG4%2B4CLzEF12oT4V6ucc9ZBAPfZWP9L6nq6jOB82aUdYavDsGYa7J3dRnRghVYBK1pRVP7TV7vBRPEr8FAjGEhRzfG12cBAWfIdqDt5kAFG9iE5ly6XKf7OTu8qz1EJm0yVx65YCmOKMkH2%2FKh5gEkXnoS6LIgW%2BPS3smOklTolNdJSaRdidLivb8HeUJDgorfd2FVbnuwl6tr7XhN2UMvNHnW7GCSTCPLXC1AMNxs7cAkD8M7UnoGqg3tXUKQh3lp9MeIDw2f8hOt&s=e23921c1-94cc-4030-bebb-713b987343a6&i=Untitled%20Session&e=Support&y=Guest&r=" | C:\Program Files\Internet Explorer\iexplore.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
16 486
Read events
16 249
Write events
211
Delete events
26
Modification events
| (PID) Process: | (7196) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7196) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7196) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7196) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7196) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 89273E2FAD8F2F00 | |||
| (PID) Process: | (7196) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 5E974E2FAD8F2F00 | |||
| (PID) Process: | (7196) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262924 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {22AC930F-BA8F-49F6-B5D7-D09AFD8C1DFA} | |||
| (PID) Process: | (7196) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262924 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {2BCFA9A5-D90D-4567-8A9F-4855296E0CC1} | |||
| (PID) Process: | (4424) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4424) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
27
Suspicious files
117
Text files
78
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10d0bf.TMP | — | |
MD5:— | SHA256:— | |||
| 7196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10d0bf.TMP | — | |
MD5:— | SHA256:— | |||
| 7196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10d0cf.TMP | — | |
MD5:— | SHA256:— | |||
| 7196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10d0cf.TMP | — | |
MD5:— | SHA256:— | |||
| 7196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10d12d.TMP | — | |
MD5:— | SHA256:— | |||
| 7196 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
41
DNS requests
40
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.167:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6272 | dfsvc.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
6272 | dfsvc.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAuTYAUbzPZmQpmJmNW6l84%3D | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 23.40.158.218:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1272 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
7728 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7728 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6272 | dfsvc.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.167:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 40.113.103.199:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 40.126.31.129:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 23.40.158.218:80 | ocsp.digicert.com | AKAMAI-AS | MX | whitelisted |
7196 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7472 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7472 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
445.co.il |
| unknown |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1660 | ScreenConnect.ClientService.exe | Potential Corporate Privacy Violation | REMOTE [ANY.RUN] ScreenConnect Server Response |