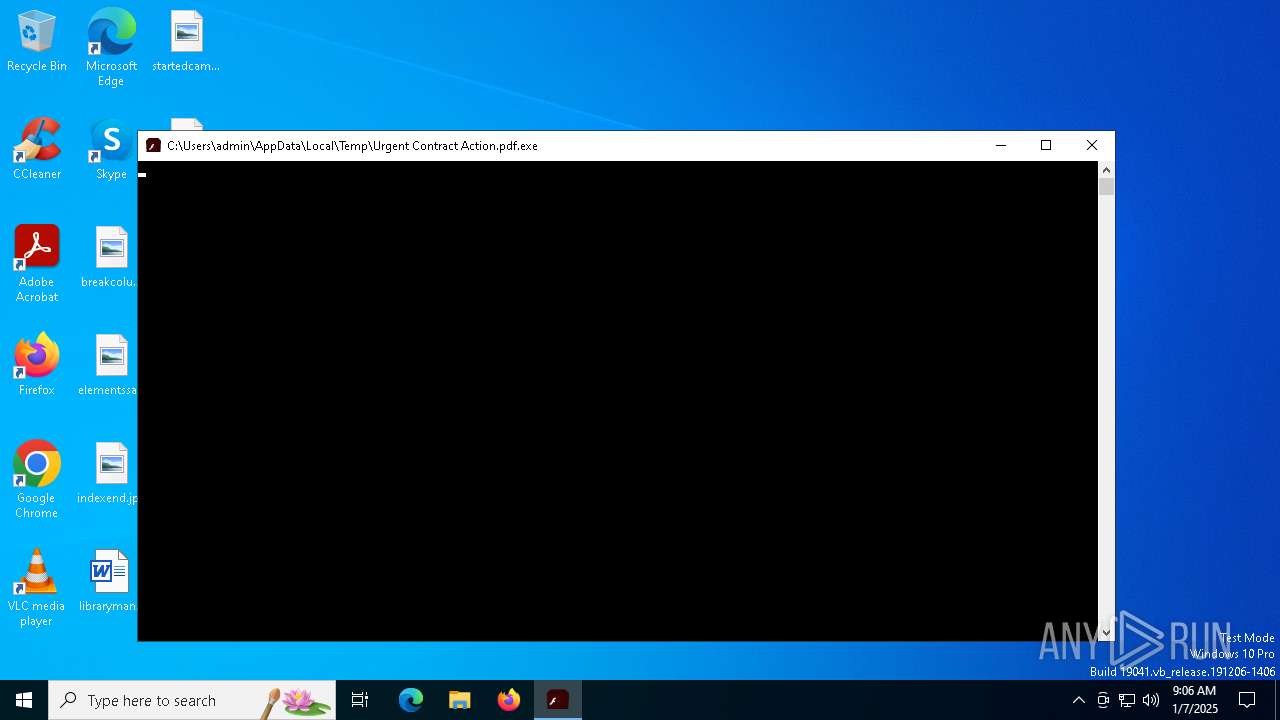
| File name: | Urgent Contract Action.pdf.exe |
| Full analysis: | https://app.any.run/tasks/57cef2a9-9089-46b2-8c39-c2fd6765abd2 |
| Verdict: | Malicious activity |
| Analysis date: | January 07, 2025, 09:06:30 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (console) Intel 80386, for MS Windows, 5 sections |
| MD5: | FBBDC39AF1139AEBBA4DA004475E8839 |
| SHA1: | DE5C8D858E6E41DA715DCA1C019DF0BFB92D32C0 |
| SHA256: | 630325CAC09AC3FAB908F903E3B00D0DADD5FDAA0875ED8496FCBB97A558D0DA |
| SSDEEP: | 12288:BHNTywFAvN86pLbqWRKHZKfErrZJyZ0yqsGO3XR63:vT56NbqWRwZaEr3yt2O3XR63 |
MALICIOUS
WebDav connection (SURICATA)
- rundll32.exe (PID: 936)
Executing a file with an untrusted certificate
- Urgent Contract Action.pdf.exe (PID: 936)
SUSPICIOUS
Connects to the server without a host name
- rundll32.exe (PID: 936)
Attempting to connect via WebDav
- rundll32.exe (PID: 936)
INFO
Checks proxy server information
- rundll32.exe (PID: 936)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:10:22 02:33:58+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 12288 |
| InitializedDataSize: | 43520 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x12c0 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 27.0.0.170 |
| ProductVersionNumber: | 27.0.0.170 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Adobe Systems Incorporated |
| FileDescription: | Adobe® Flash® Player Installer/Uninstaller 27.0 r0 |
| FileVersion: | 27,0,0,170 |
| InternalName: | Adobe® Flash® Player Installer/Uninstaller 27.0 |
| LegalCopyright: | Copyright © 1996-2017 Adobe Systems Incorporated |
| LegalTrademarks: | Adobe® Flash® Player |
| OriginalFileName: | FlashUtil.exe |
| ProductName: | Adobe® Flash® Player Installer/Uninstaller |
| ProductVersion: | 27,0,0,170 |
Total processes
129
Monitored processes
2
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||
|---|---|---|---|---|---|---|---|---|---|---|---|
| 936 | "C:\Users\admin\AppData\Local\Temp\Urgent Contract Action.pdf.exe" | C:\Users\admin\AppData\Local\Temp\Urgent Contract Action.pdf.exe | — | explorer.exe | |||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe® Flash® Player Installer/Uninstaller 27.0 r0 Version: 27,0,0,170 Modules
| |||||||||||
| 936 | C:\WINDOWS\system32\rundll32.exe C:\Windows\infpub.dat,#1 15 | C:\Windows\SysWOW64\rundll32.exe | — | ||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||
Total events
75
Read events
75
Write events
0
Delete events
0
Modification events
Executable files
3
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 936 | rundll32.exe | C:\Users\admin\Documents\Database1.accdb | binary | |
MD5:4509DEC4CDB66B3C0906102204B50C13 | SHA256:3CD54586A28BB3779D89DE88D920F2BC9D50FA0BB1F756CA46B8AFE23075420A | |||
| 936 | rundll32.exe | C:\Windows\667D.tmp | executable | |
MD5:347AC3B6B791054DE3E5720A7144A977 | SHA256:301B905EB98D8D6BB559C04BBDA26628A942B2C4107C07A02E8F753BDCFE347C | |||
| 936 | rundll32.exe | C:\Windows\cscc.dat | executable | |
MD5:EDB72F4A46C39452D1A5414F7D26454A | SHA256:0B2F863F4119DC88A22CC97C0A136C88A0127CB026751303B045F7322A8972F6 | |||
| 936 | rundll32.exe | C:\Windows\dispci.exe | executable | |
MD5:B14D8FAF7F0CBCFAD051CEFE5F39645F | SHA256:8EBC97E05C8E1073BDA2EFB6F4D00AD7E789260AFA2C276F0C72740B838A0A93 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
65
DNS requests
17
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2736 | RUXIMICS.exe | GET | 200 | 2.18.121.147:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | FR | binary | 1.01 Kb | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.18.121.147:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | FR | binary | 1.01 Kb | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.200.189.225:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | ID | binary | 973 b | whitelisted |
2736 | RUXIMICS.exe | GET | 200 | 23.200.189.225:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | ID | binary | 973 b | whitelisted |
5004 | svchost.exe | GET | 200 | 23.200.189.225:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | ID | binary | 973 b | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 312 b | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
5004 | svchost.exe | GET | 200 | 2.18.121.147:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | FR | binary | 1.01 Kb | whitelisted |
936 | rundll32.exe | OPTIONS | 400 | 2.18.121.147:80 | http://2.18.121.147/ | FR | html | 312 b | unknown |
6432 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | NL | binary | 418 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5004 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2736 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.18.121.147:80 | crl.microsoft.com | AKAMAI-AS | FR | unknown |
5004 | svchost.exe | 2.18.121.147:80 | crl.microsoft.com | AKAMAI-AS | FR | whitelisted |
2736 | RUXIMICS.exe | 2.18.121.147:80 | crl.microsoft.com | AKAMAI-AS | FR | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.200.189.225:80 | www.microsoft.com | Moratelindo Internet Exchange Point | ID | whitelisted |
5004 | svchost.exe | 23.200.189.225:80 | www.microsoft.com | Moratelindo Internet Exchange Point | ID | unknown |
2736 | RUXIMICS.exe | 23.200.189.225:80 | www.microsoft.com | Moratelindo Internet Exchange Point | ID | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| unknown |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
2 ETPRO signatures available at the full report