| File name: | Venom Software v6.exe |
| Full analysis: | https://app.any.run/tasks/c9505895-6f28-45d8-86b7-468f9bc97dad |
| Verdict: | Malicious activity |
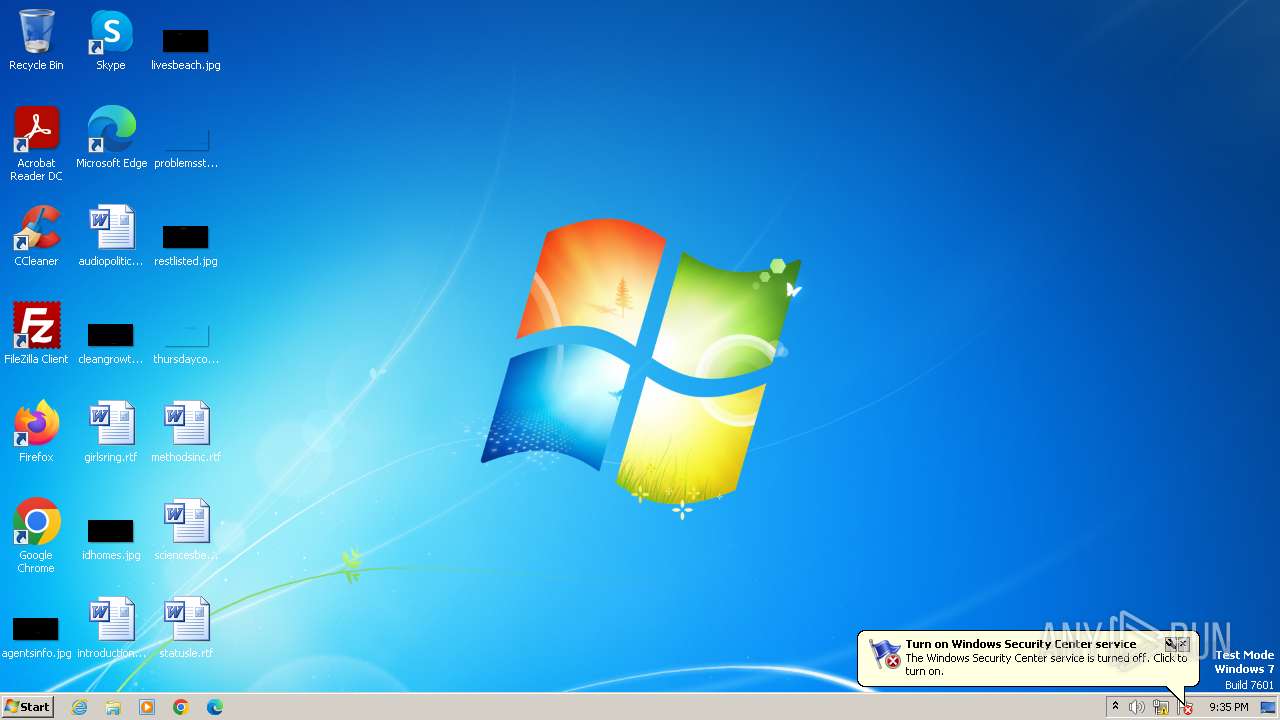
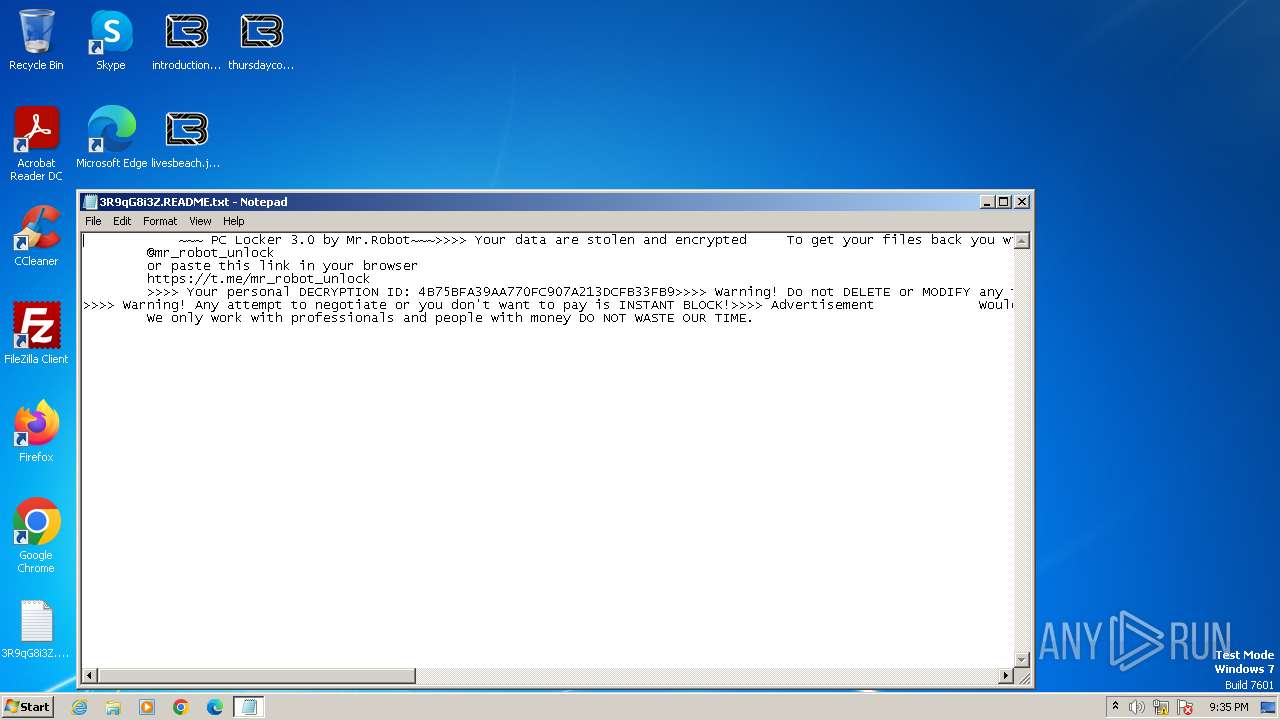
| Threats: | LockBit, a ransomware variant, encrypts data on infected machines, demanding a ransom payment for decryption. Used in targeted attacks, It's a significant risk to organizations. |
| Analysis date: | November 07, 2023, 21:35:00 |
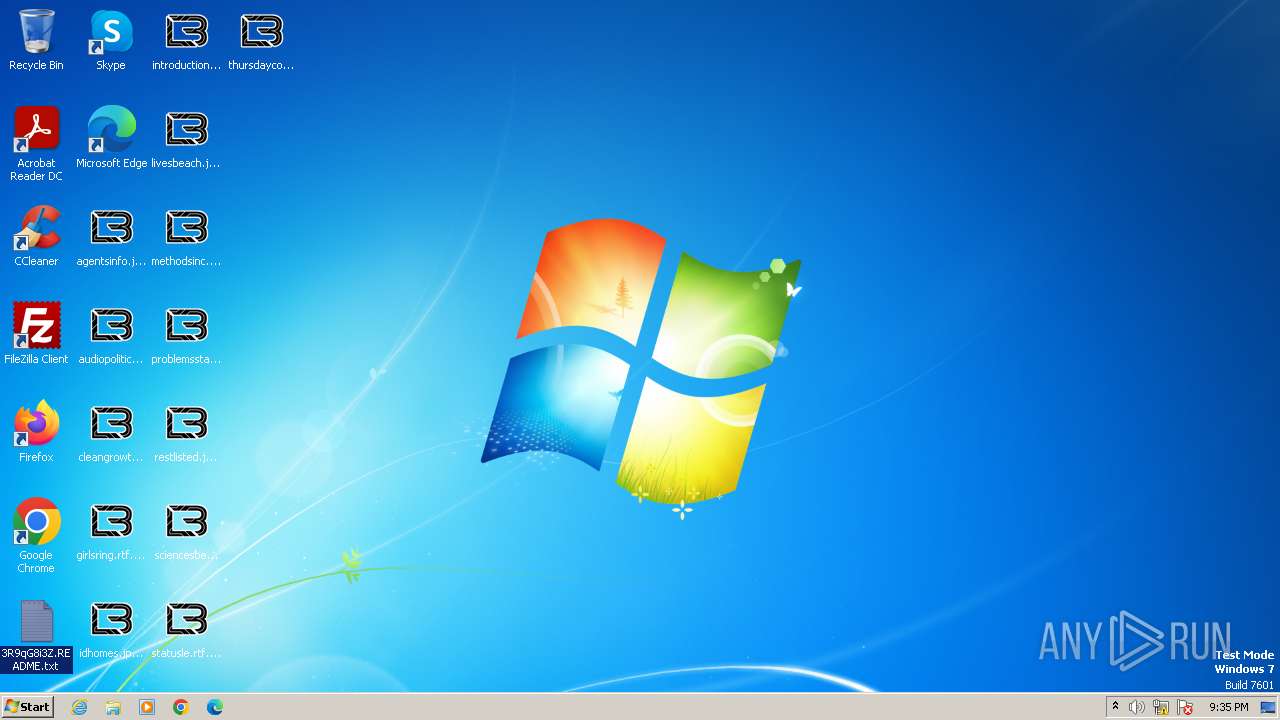
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 3D2C2704E07CCFAD40A40116F859CC78 |
| SHA1: | 327A36D3017DC98F3BB0FE2B83BB1C49CCCFAA5B |
| SHA256: | 62FC350397B98AC1F593EADAF0EBB6C31D272708D71C0EE9A2CE859E06BA2060 |
| SSDEEP: | 12288:vcgCzNHJj96xfKJStJkRm3bYXob0AnmFMcaGQx3ZVVVVVVVVVAtVVVUvPV+Kgfxl:KQKgLIQmFuGQx3lvPsKgJl |
MALICIOUS
Drops the executable file immediately after the start
- Venom Software v6.exe (PID: 3416)
- VenomV6.exe (PID: 3604)
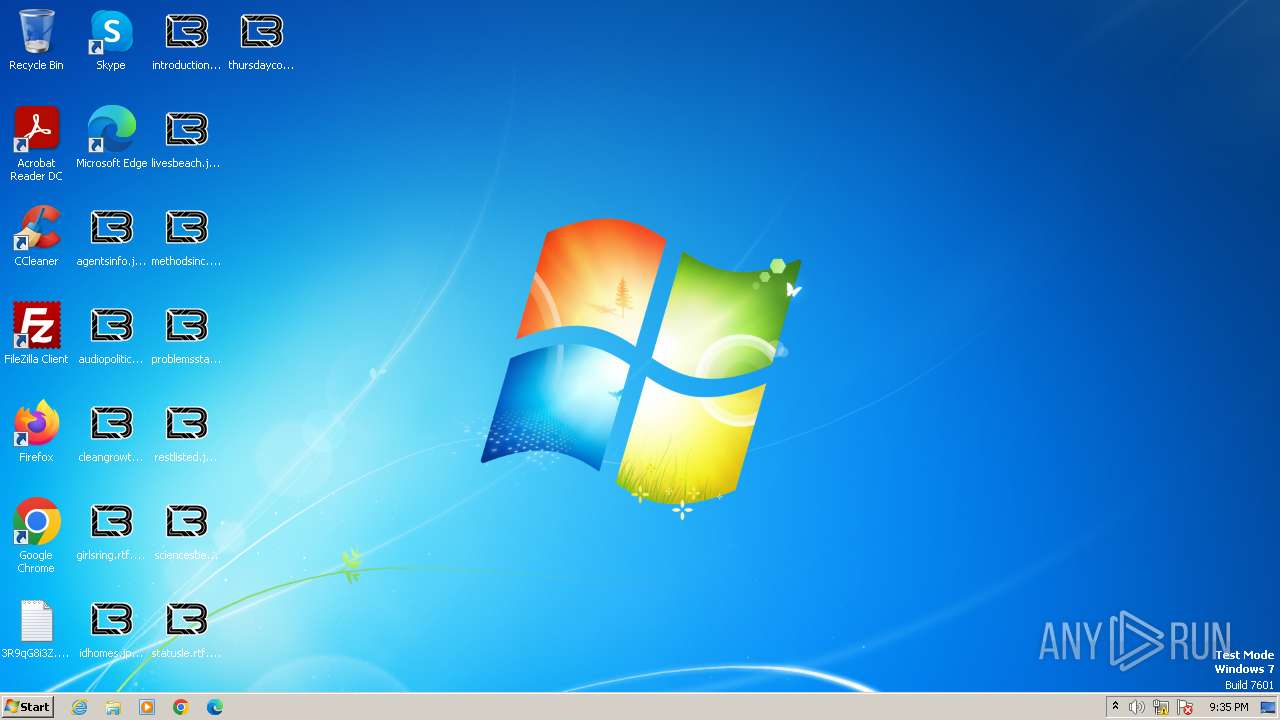
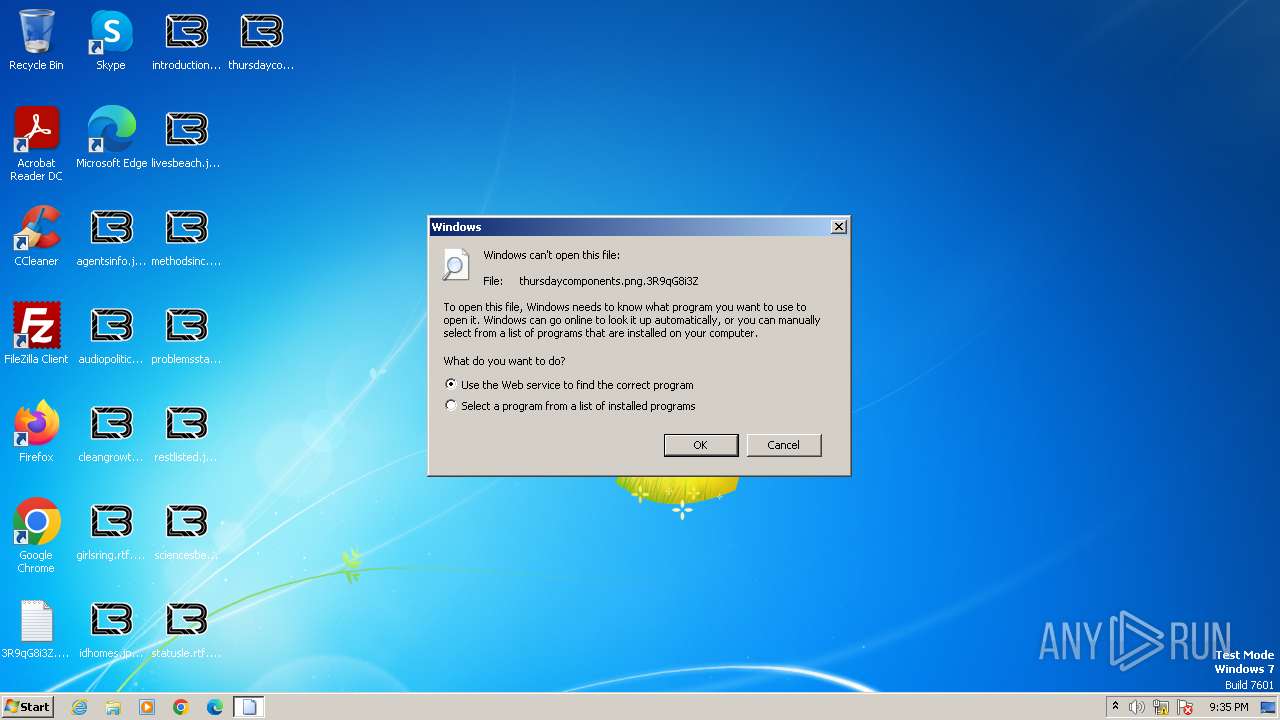
Renames files like ransomware
- VenomV6.exe (PID: 3604)
Steals credentials from Web Browsers
- VenomV6.exe (PID: 3604)
[YARA] LockBit is detected
- VenomV6.exe (PID: 3604)
Known privilege escalation attack
- dllhost.exe (PID: 3276)
Actions looks like stealing of personal data
- VenomV6.exe (PID: 3604)
SUSPICIOUS
Reads Microsoft Outlook installation path
- Venom Software v6.exe (PID: 3416)
Reads the Internet Settings
- Venom Software v6.exe (PID: 3416)
Reads Internet Explorer settings
- Venom Software v6.exe (PID: 3416)
Reads browser cookies
- VenomV6.exe (PID: 3604)
Write to the desktop.ini file (may be used to cloak folders)
- VenomV6.exe (PID: 3604)
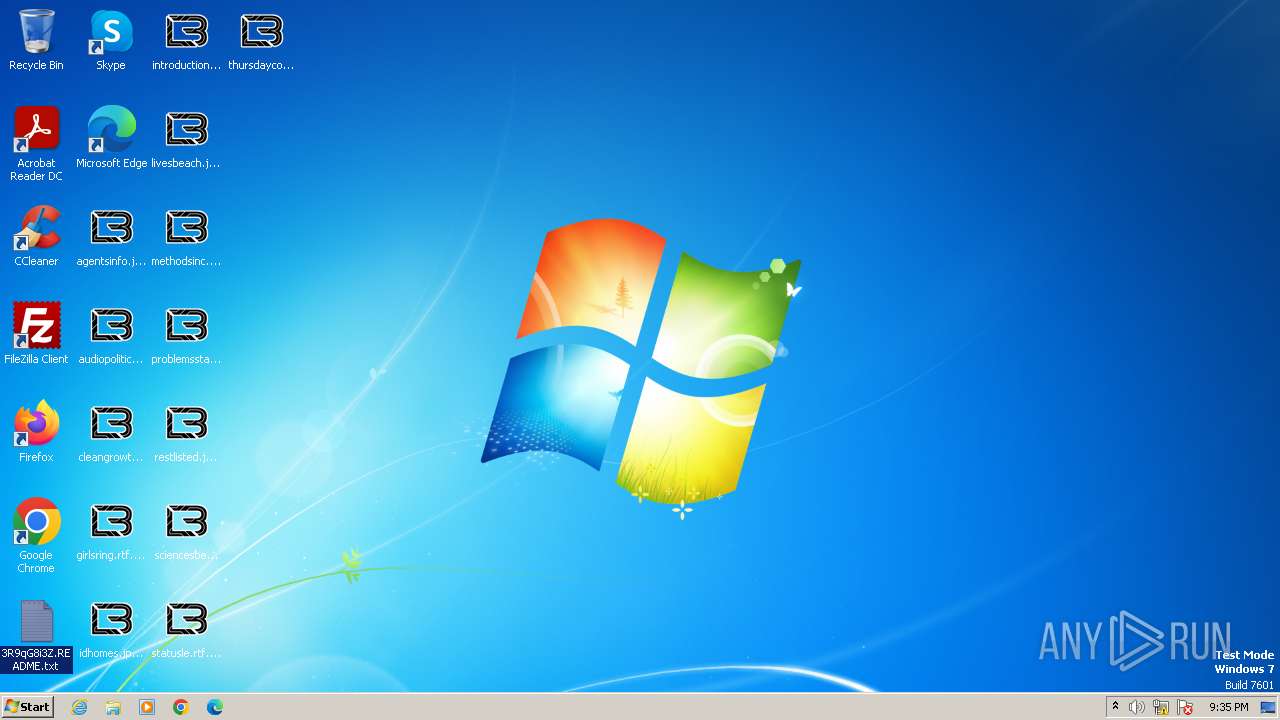
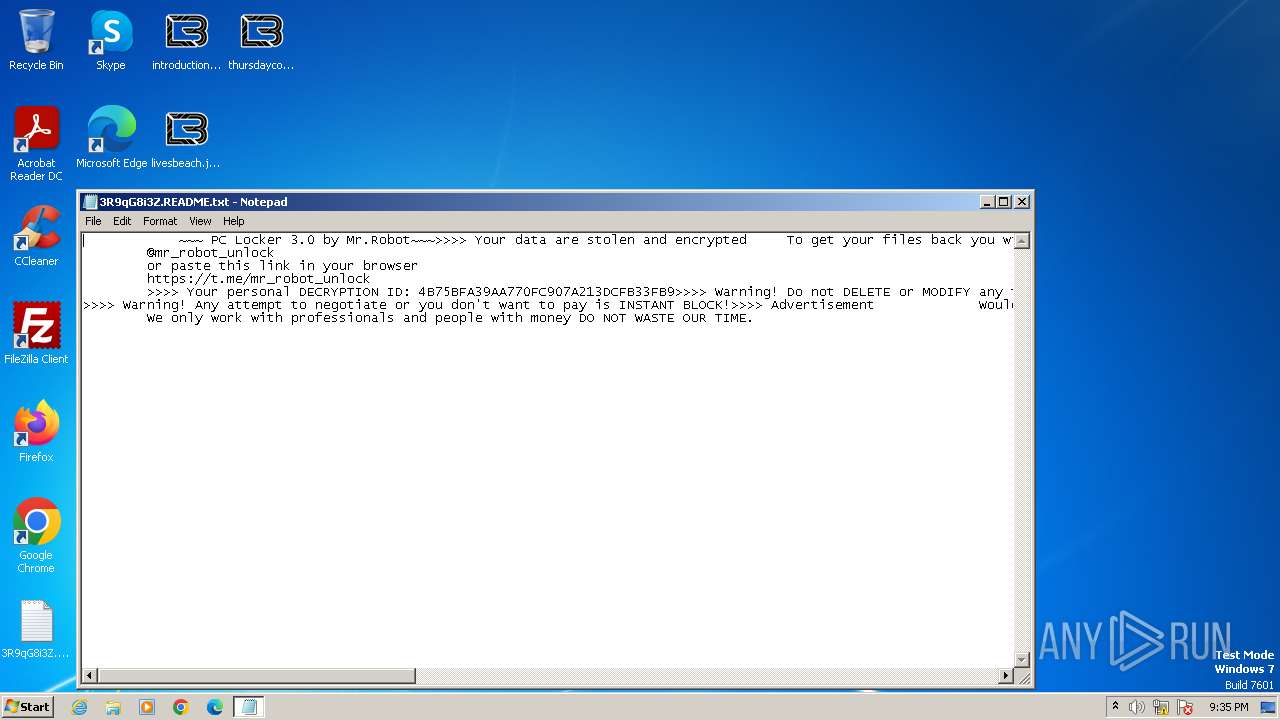
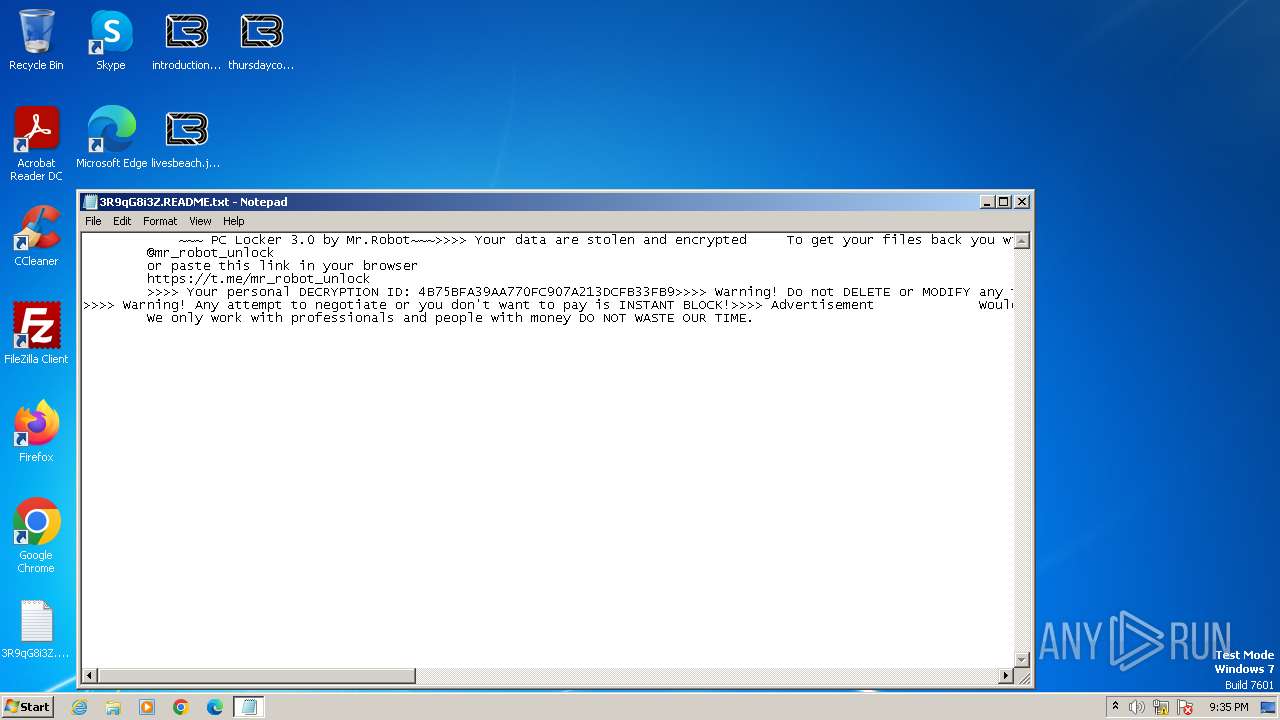
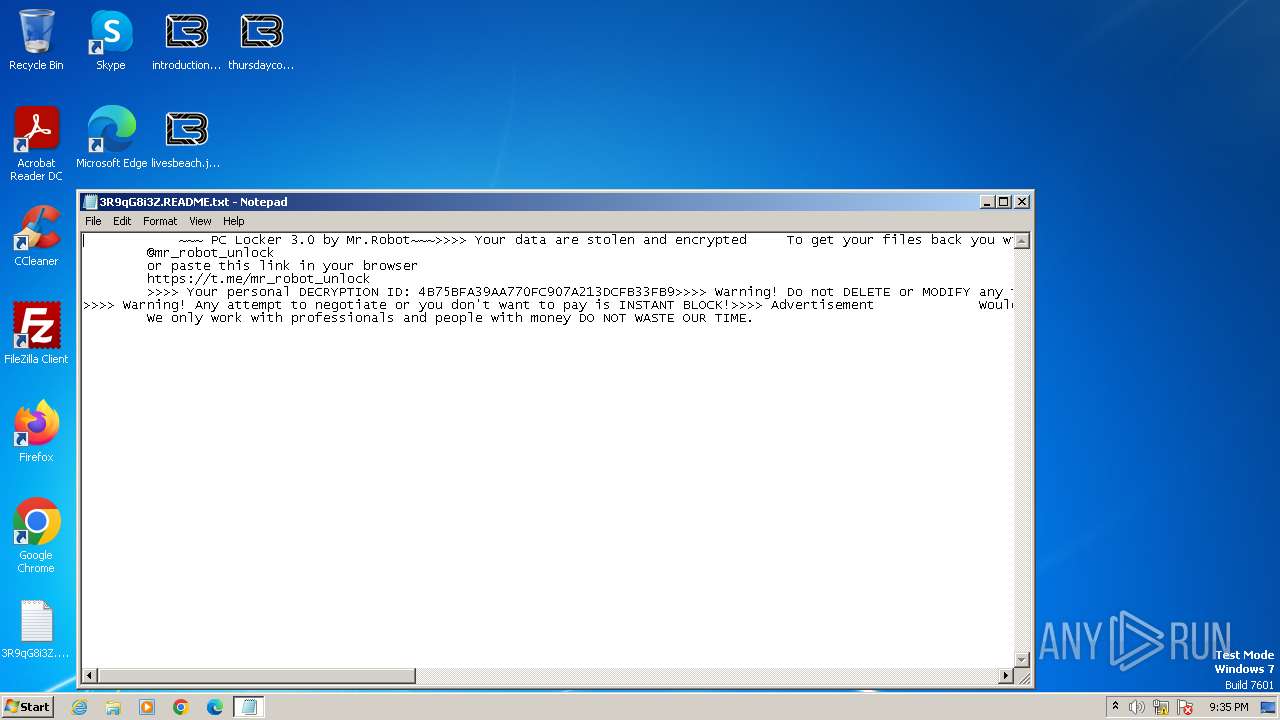
Creates files like ransomware instruction
- VenomV6.exe (PID: 3604)
INFO
Reads the computer name
- Venom Software v6.exe (PID: 3416)
- VenomV6.exe (PID: 3496)
- VenomV6.exe (PID: 3604)
Checks supported languages
- Venom Software v6.exe (PID: 3416)
- VenomV6.exe (PID: 3496)
- VenomV6.exe (PID: 3604)
Checks proxy server information
- Venom Software v6.exe (PID: 3416)
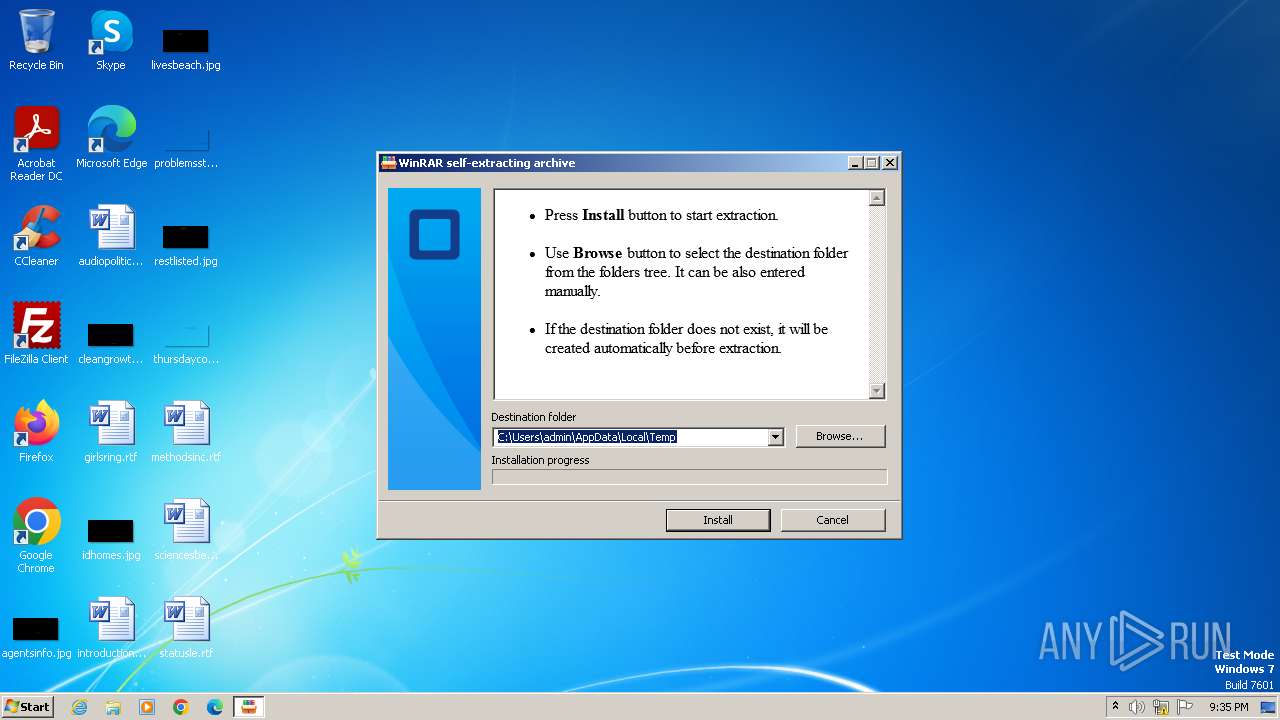
Create files in a temporary directory
- Venom Software v6.exe (PID: 3416)
- VenomV6.exe (PID: 3604)
Reads the machine GUID from the registry
- Venom Software v6.exe (PID: 3416)
- VenomV6.exe (PID: 3496)
- VenomV6.exe (PID: 3604)
Checks transactions between databases Windows and Oracle
- VenomV6.exe (PID: 3496)
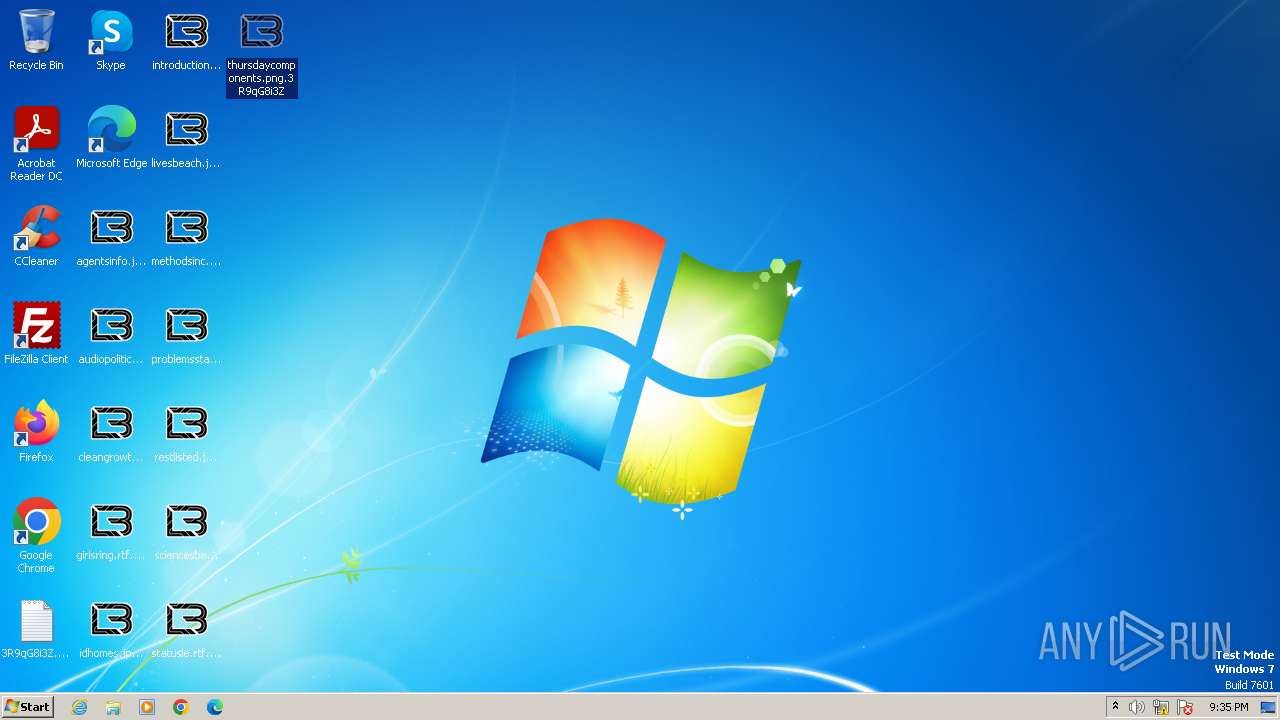
Creates files or folders in the user directory
- VenomV6.exe (PID: 3604)
Creates files in the program directory
- VenomV6.exe (PID: 3604)
Manual execution by a user
- notepad.exe (PID: 3684)
- notepad.exe (PID: 3588)
- notepad.exe (PID: 3648)
- rundll32.exe (PID: 4052)
- notepad.exe (PID: 3536)
- notepad.exe (PID: 3872)
- notepad.exe (PID: 4028)
Dropped object may contain TOR URL's
- VenomV6.exe (PID: 3604)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:10:03 09:51:19+02:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.33 |
| CodeSize: | 214528 |
| InitializedDataSize: | 263680 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x21d50 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
52
Monitored processes
11
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3276 | C:\Windows\system32\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3416 | "C:\Users\admin\AppData\Local\Temp\Venom Software v6.exe" | C:\Users\admin\AppData\Local\Temp\Venom Software v6.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3496 | "C:\Users\admin\AppData\Local\Temp\VenomV6.exe" | C:\Users\admin\AppData\Local\Temp\VenomV6.exe | — | Venom Software v6.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3536 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\3R9qG8i3Z.README.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3588 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\3R9qG8i3Z.README.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3604 | "C:\Users\admin\AppData\Local\Temp\VenomV6.exe" | C:\Users\admin\AppData\Local\Temp\VenomV6.exe | dllhost.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3648 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\3R9qG8i3Z.README.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3684 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\3R9qG8i3Z.README.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3872 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\3R9qG8i3Z.README.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4028 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\Desktop\3R9qG8i3Z.README.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 137
Read events
2 118
Write events
19
Delete events
0
Modification events
| (PID) Process: | (3416) Venom Software v6.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3416) Venom Software v6.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3416) Venom Software v6.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3416) Venom Software v6.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3416) Venom Software v6.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3416) Venom Software v6.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3276) dllhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3276) dllhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3276) dllhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3276) dllhost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
10
Suspicious files
1 054
Text files
771
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3604 | VenomV6.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-1000\AAAAAAAAAAA | binary | |
MD5:84AC1E61B61A9670216055094E91A5FE | SHA256:69A963974F567CB7594E2307366855B3E074B4FE7A321AE840727ED2B1FADB41 | |||
| 3604 | VenomV6.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-1000\CCCCCCCCCCC | binary | |
MD5:84AC1E61B61A9670216055094E91A5FE | SHA256:69A963974F567CB7594E2307366855B3E074B4FE7A321AE840727ED2B1FADB41 | |||
| 3604 | VenomV6.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-1000\EEEEEEEEEEE | binary | |
MD5:84AC1E61B61A9670216055094E91A5FE | SHA256:69A963974F567CB7594E2307366855B3E074B4FE7A321AE840727ED2B1FADB41 | |||
| 3604 | VenomV6.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-1000\desktop.ini | binary | |
MD5:84AC1E61B61A9670216055094E91A5FE | SHA256:69A963974F567CB7594E2307366855B3E074B4FE7A321AE840727ED2B1FADB41 | |||
| 3604 | VenomV6.exe | C:\Users\3R9qG8i3Z.README.txt | text | |
MD5:7018F084F557F70F89ABC79045642289 | SHA256:A50C618836BDA5868C2D35C7832DE134AC7BF1A081F9B8C5529B00B6445F6017 | |||
| 3604 | VenomV6.exe | C:\3R9qG8i3Z.README.txt | text | |
MD5:7018F084F557F70F89ABC79045642289 | SHA256:A50C618836BDA5868C2D35C7832DE134AC7BF1A081F9B8C5529B00B6445F6017 | |||
| 3604 | VenomV6.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-1000\BBBBBBBBBBB | binary | |
MD5:84AC1E61B61A9670216055094E91A5FE | SHA256:69A963974F567CB7594E2307366855B3E074B4FE7A321AE840727ED2B1FADB41 | |||
| 3416 | Venom Software v6.exe | C:\Users\admin\AppData\Local\Temp\VenomV6.exe | executable | |
MD5:3D49478072BF18339EF810C8EA7546B2 | SHA256:E3300E30997C5A355F02CA6972711B2CA843D00A393B62C75818A43C27FF128D | |||
| 3416 | Venom Software v6.exe | C:\Users\admin\AppData\Local\Temp\settings.xml | text | |
MD5:D09AA30A9DB577B6EF7A4AC13DC8A5BE | SHA256:47982A9078391D08D3A6ABD2315049AA9A2ED3927333F5305E654E6F87A70035 | |||
| 3604 | VenomV6.exe | C:\ProgramData\3R9qG8i3Z.ico | image | |
MD5:88D9337C4C9CFE2D9AFF8A2C718EC76B | SHA256:95E059EF72686460884B9AEA5C292C22917F75D56FE737D43BE440F82034F438 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |