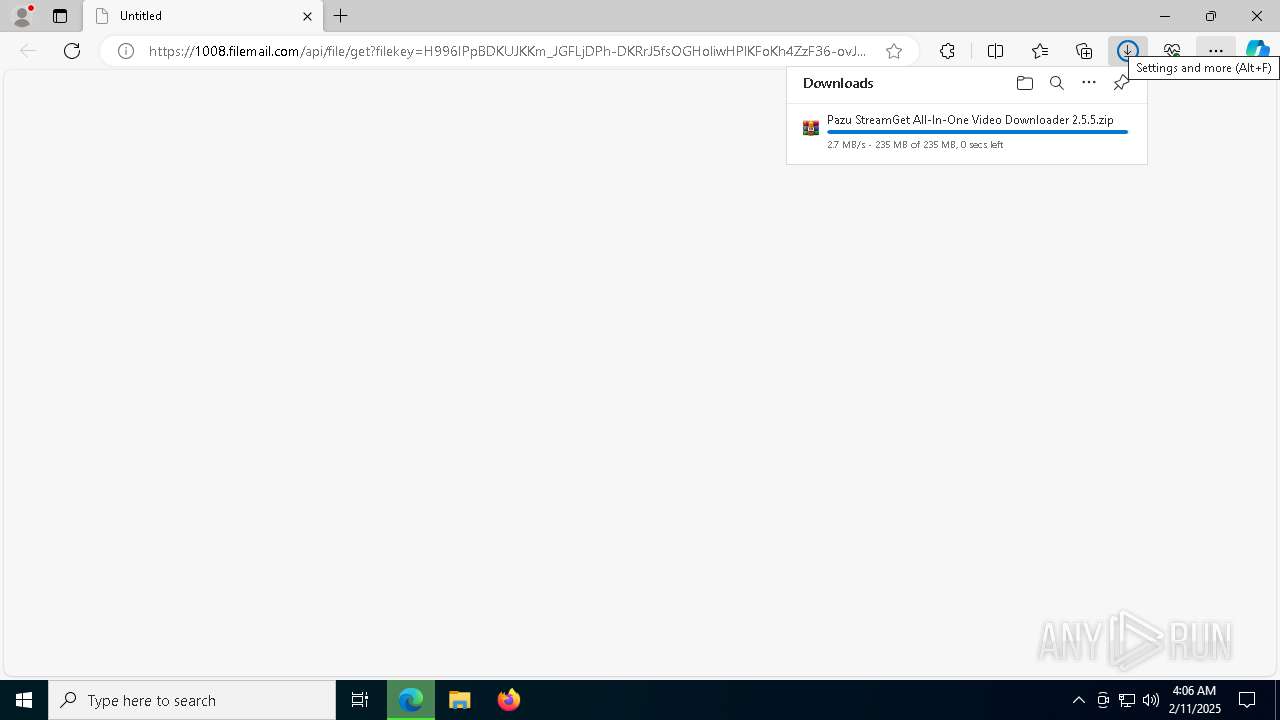
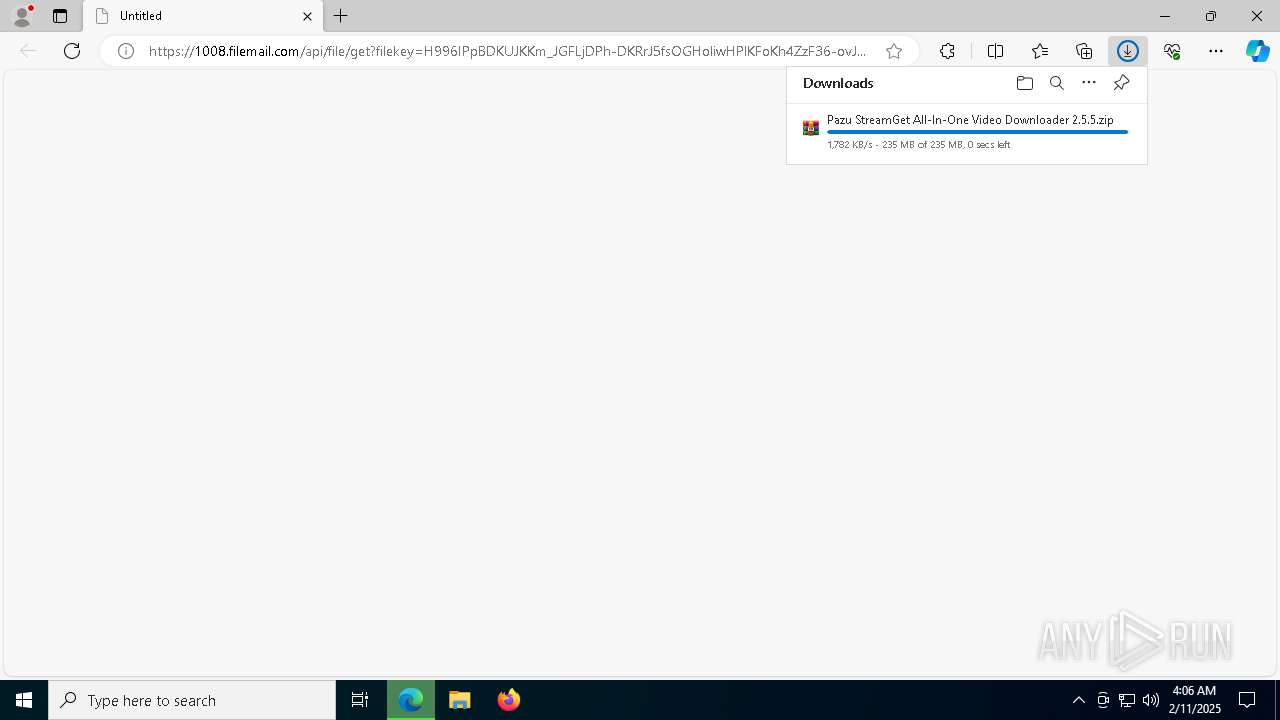
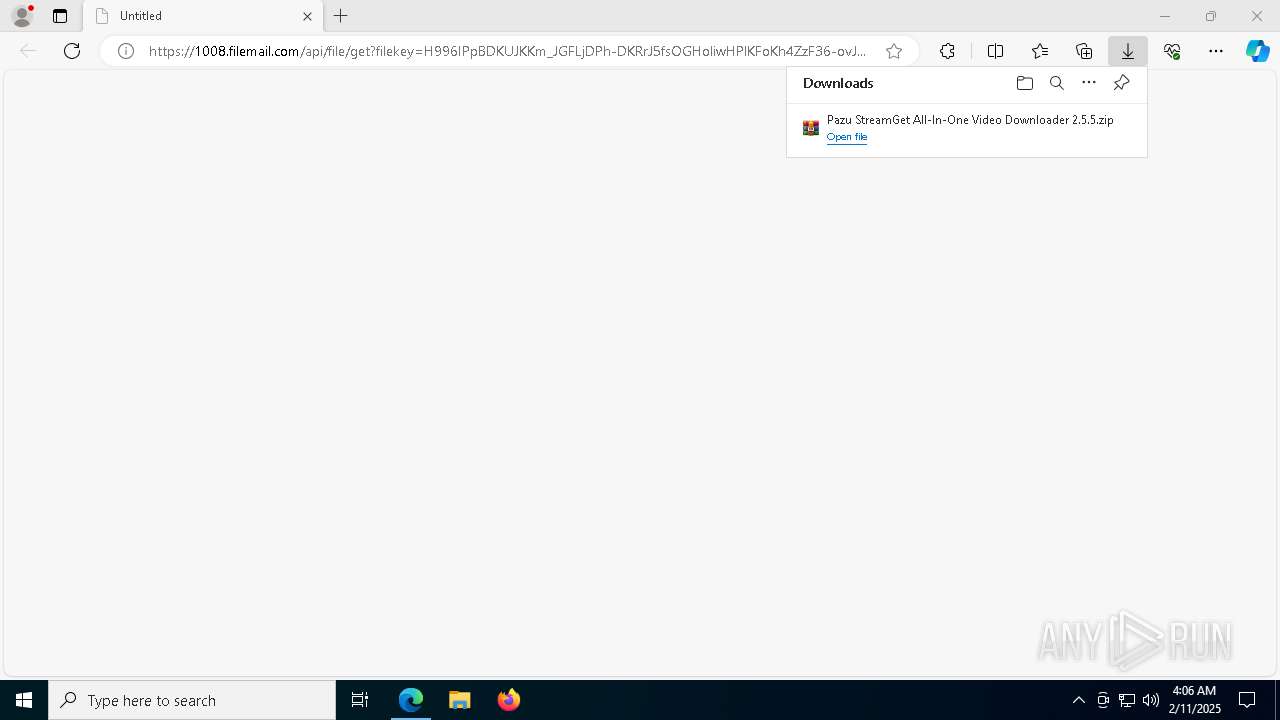
| URL: | https://1008.filemail.com/api/file/get?filekey=H996IPpBDKUJKKm_JGFLjDPh-DKRrJ5fsOGHoliwHPlKFoKh4ZzF36-ovJZLGvaHPh49Pn33OO7QP42g5dd1riOjaMlCCZnHINZ5flHOR18pjDQgIGA&pk_vid=26095fbbec41c1ac173924663030100c |
| Full analysis: | https://app.any.run/tasks/f40db372-07a8-414d-8b2e-9810da91179e |
| Verdict: | Malicious activity |
| Analysis date: | February 11, 2025, 04:04:16 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 860438BAEEF56E1427D99E0A614529CC |
| SHA1: | D9081DC69DCD1E1C64EC3DE39BFBCC06DA063AB1 |
| SHA256: | 62F880D6F0AAA38A984627FB001FED451A0763401D5F300796D071768DE5DB46 |
| SSDEEP: | 6:2+79KExnknkShGqTIowEqJKuiJKk0xUWsn:2ypnknpxqwFKJxUWs |
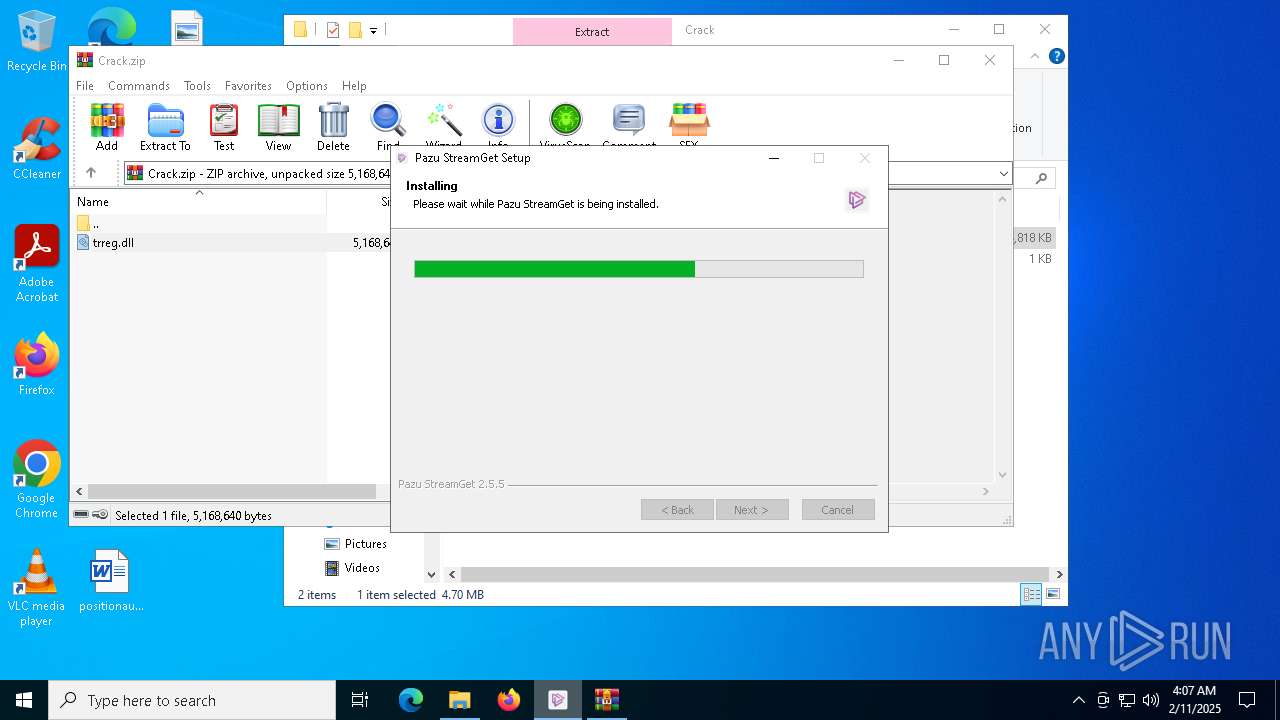
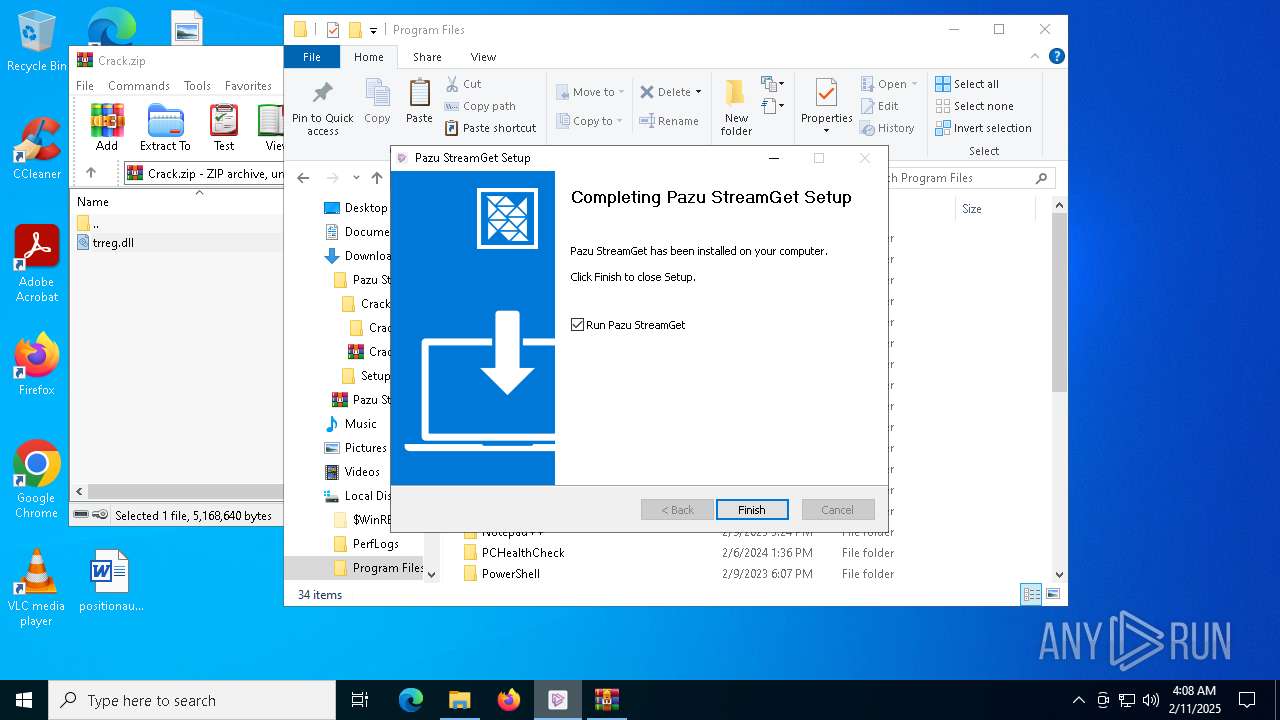
MALICIOUS
Changes powershell execution policy (Unrestricted)
- Pazu StreamGet.exe (PID: 6292)
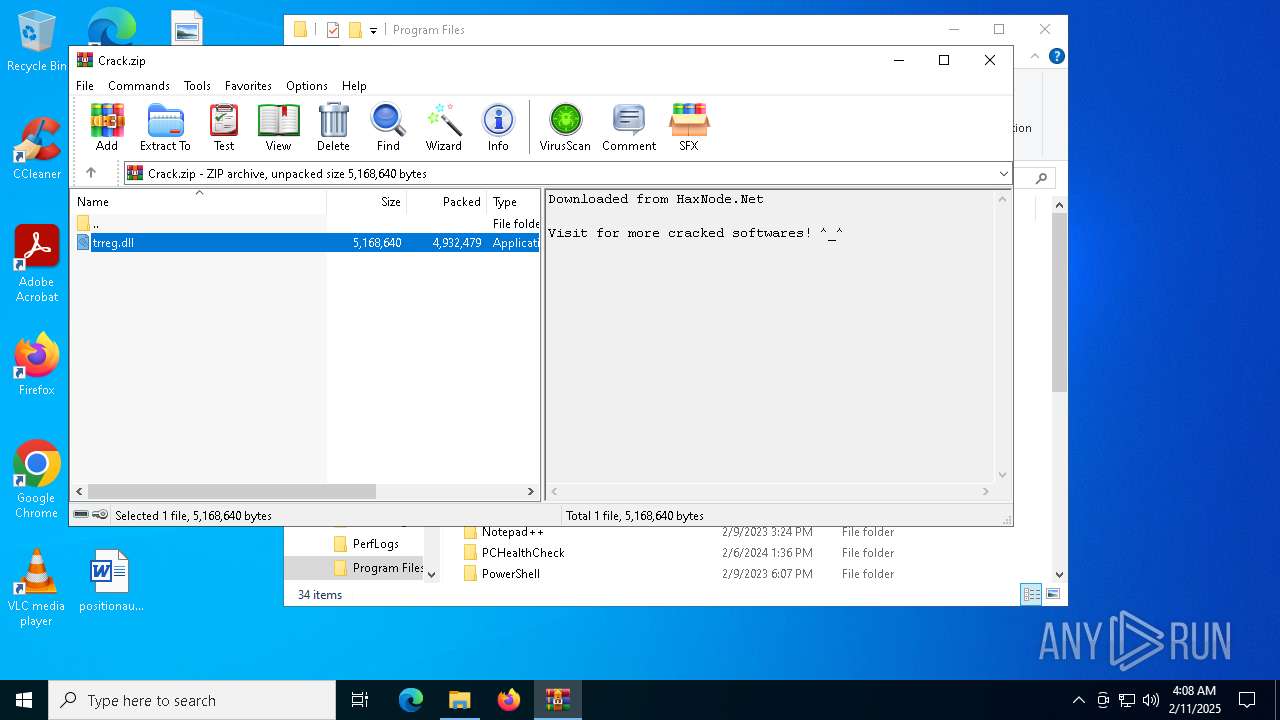
SUSPICIOUS
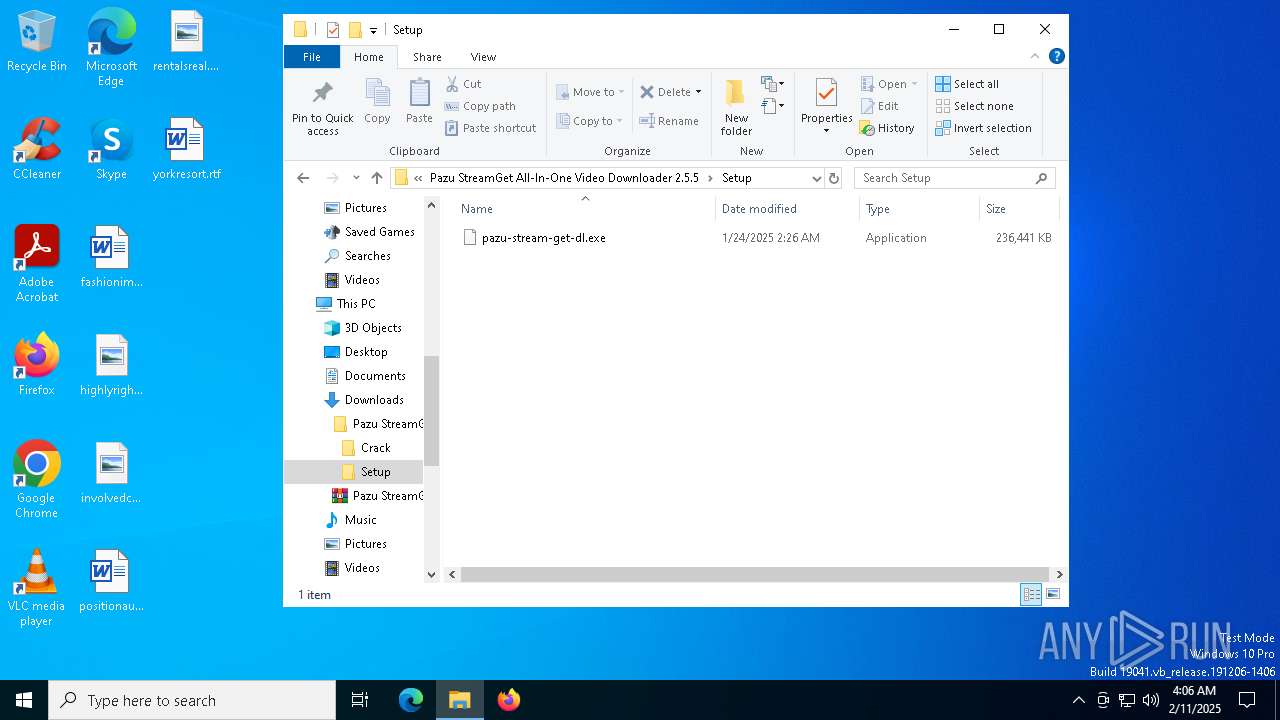
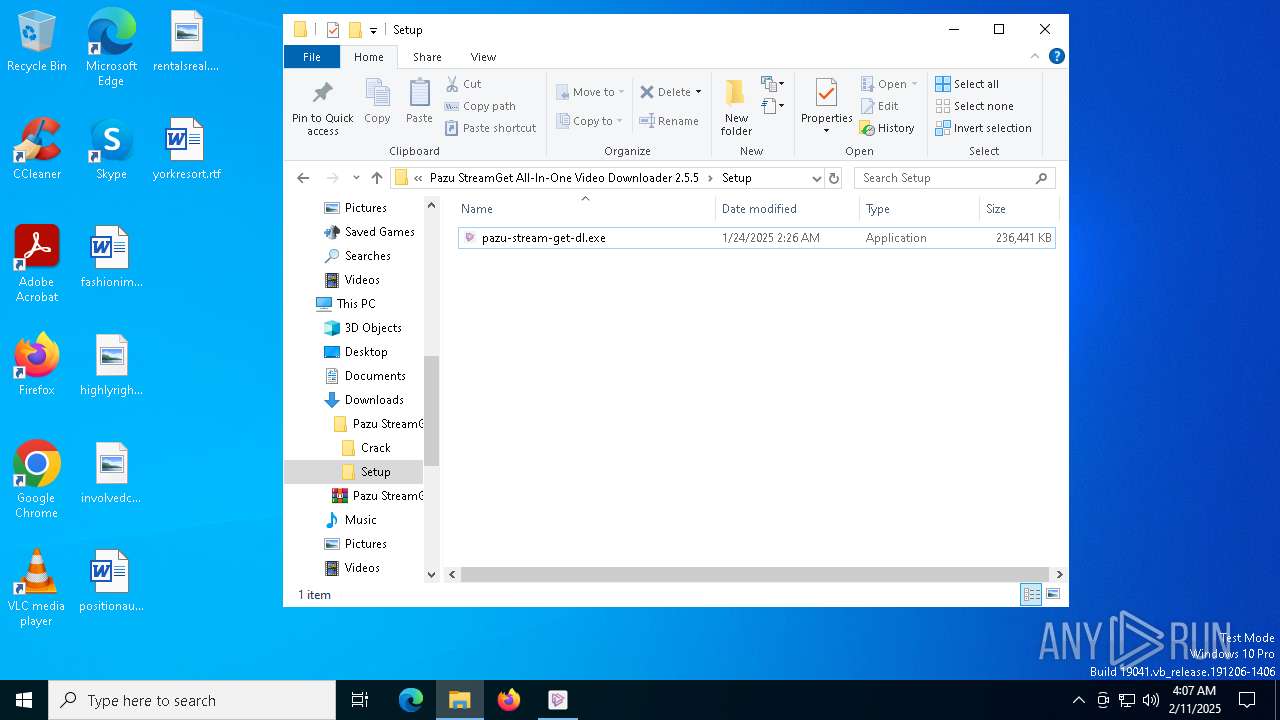
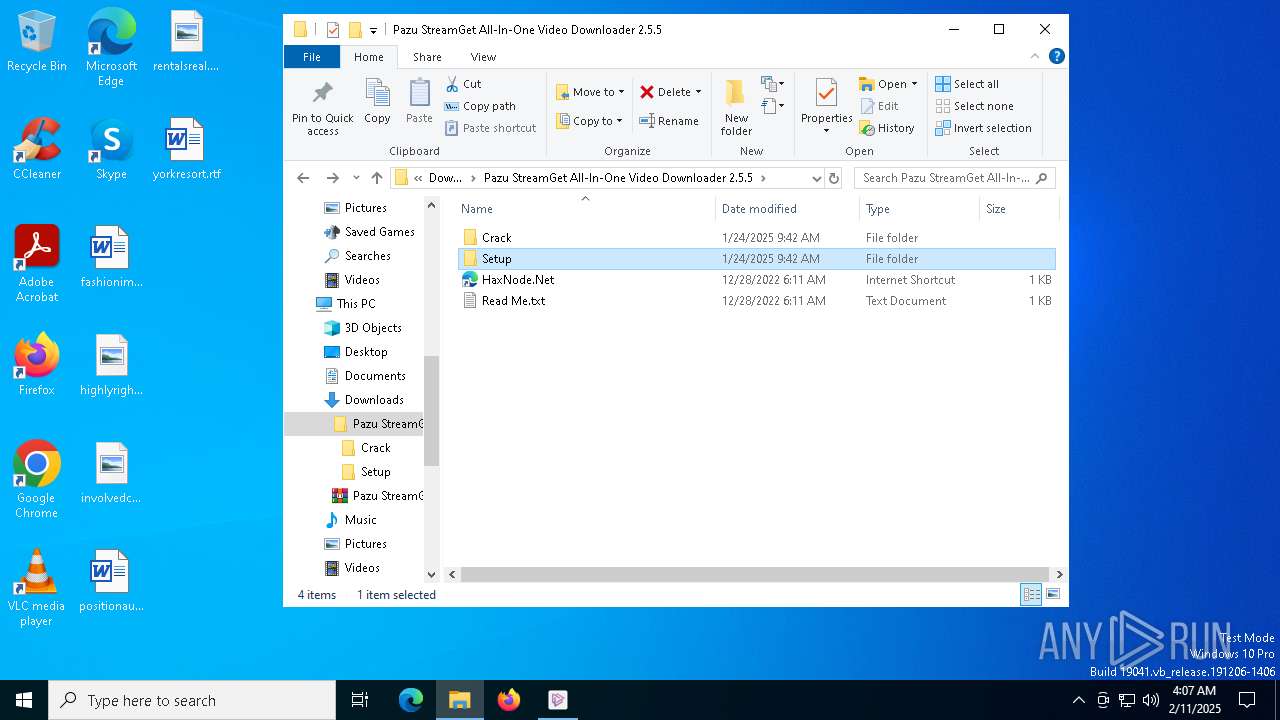
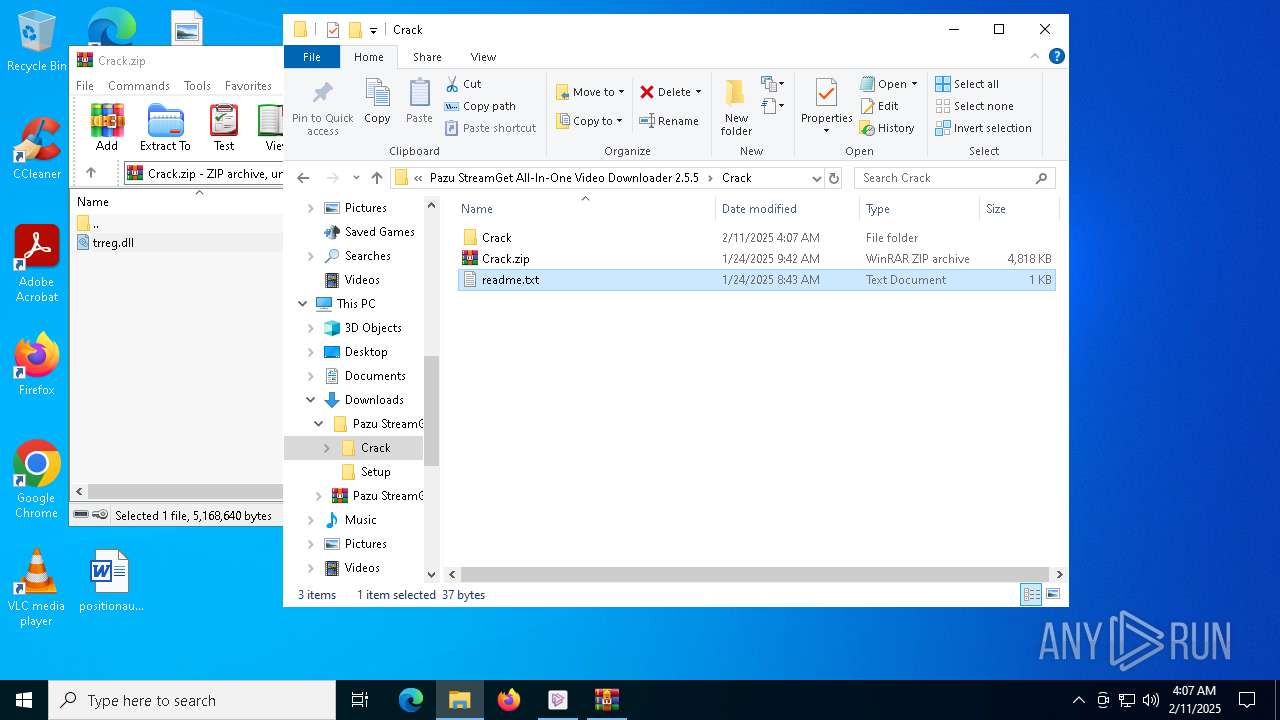
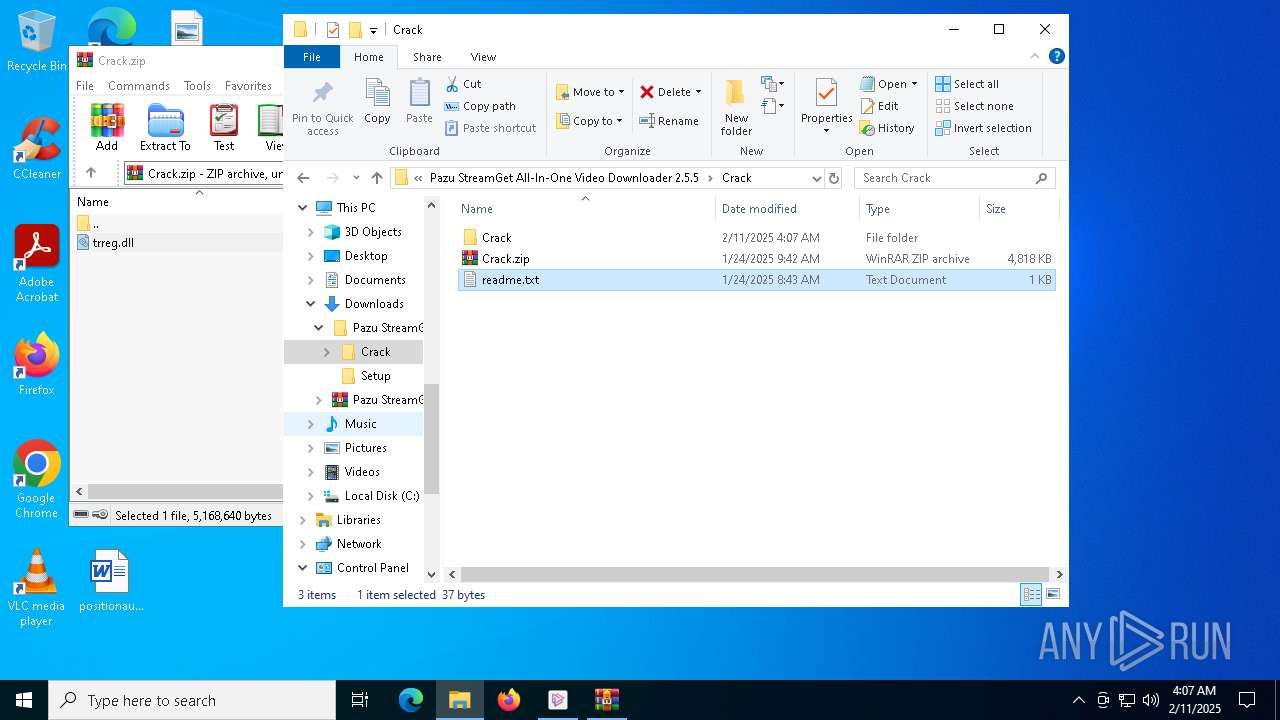
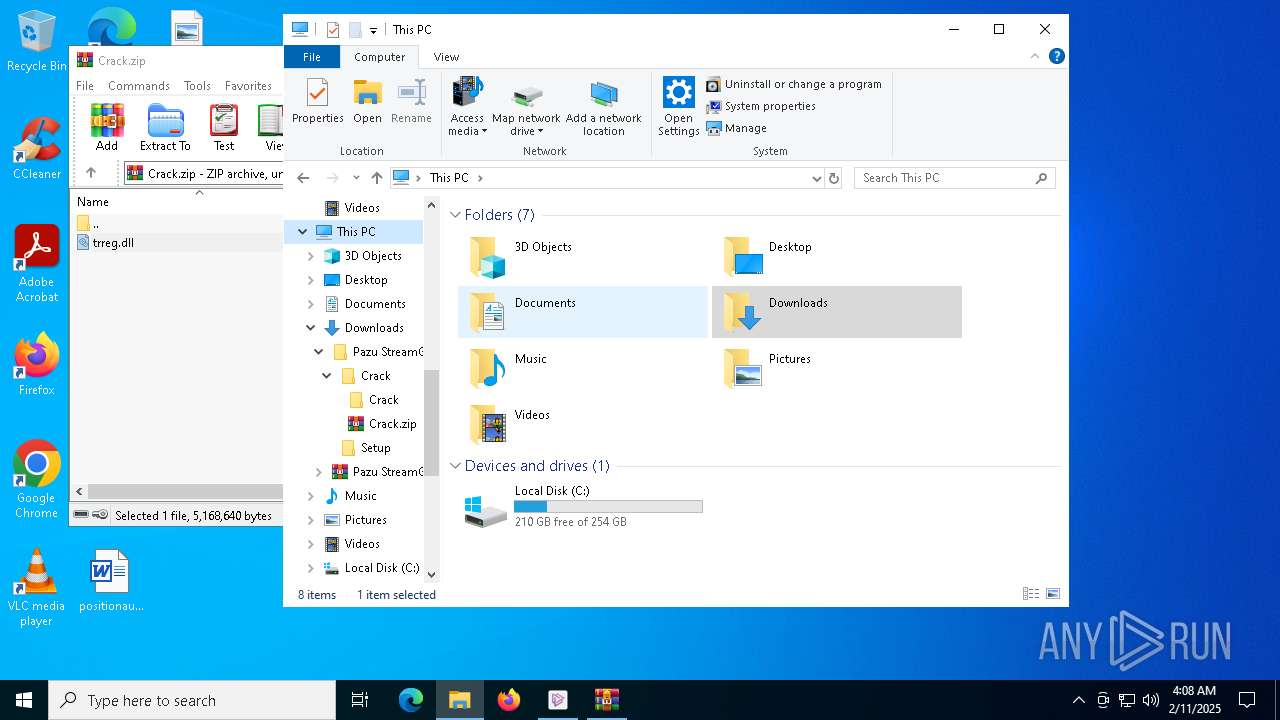
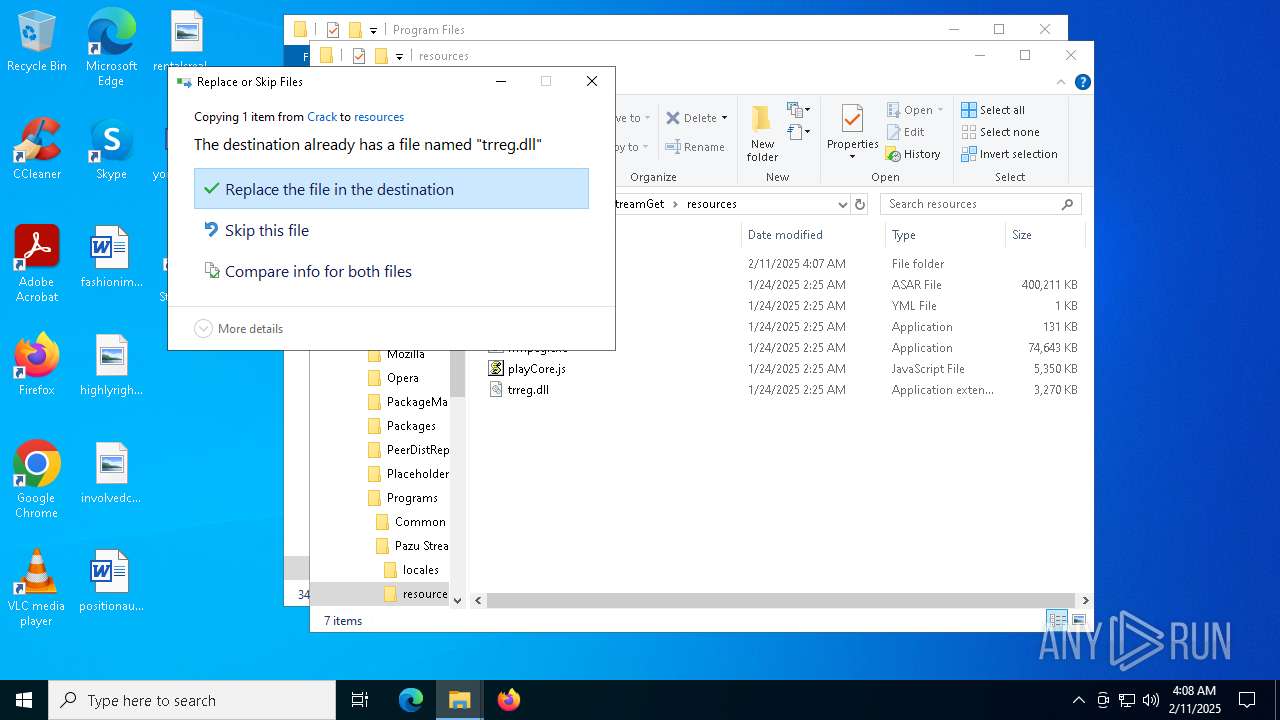
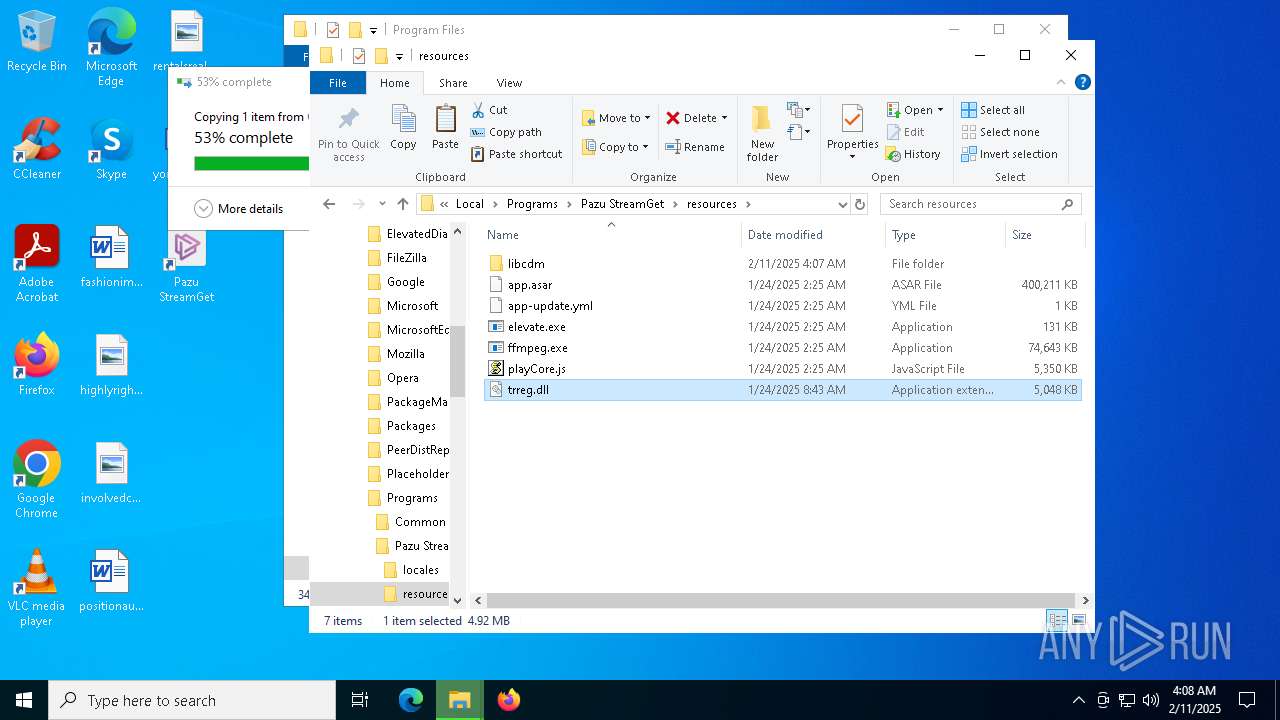
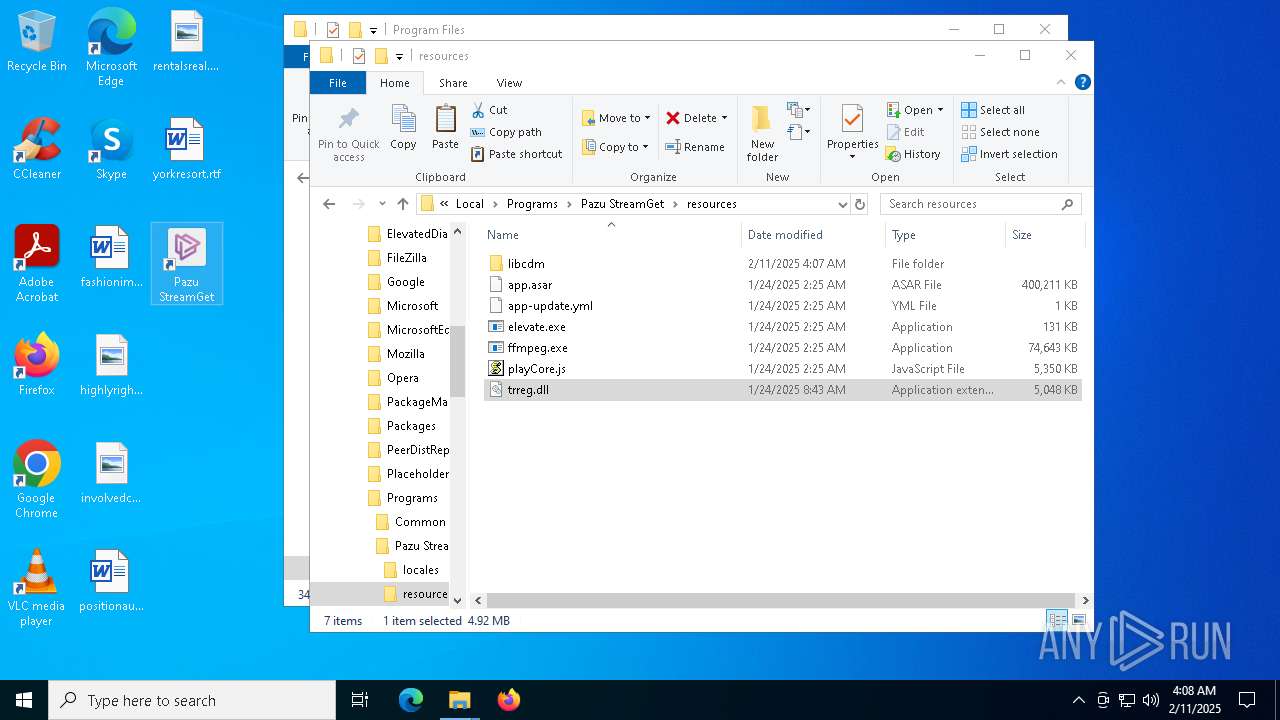
Executable content was dropped or overwritten
- pazu-stream-get-dl.exe (PID: 7440)
- Pazu StreamGet.exe (PID: 6292)
- Pazu StreamGet.exe (PID: 2680)
- Pazu StreamGet.exe (PID: 7132)
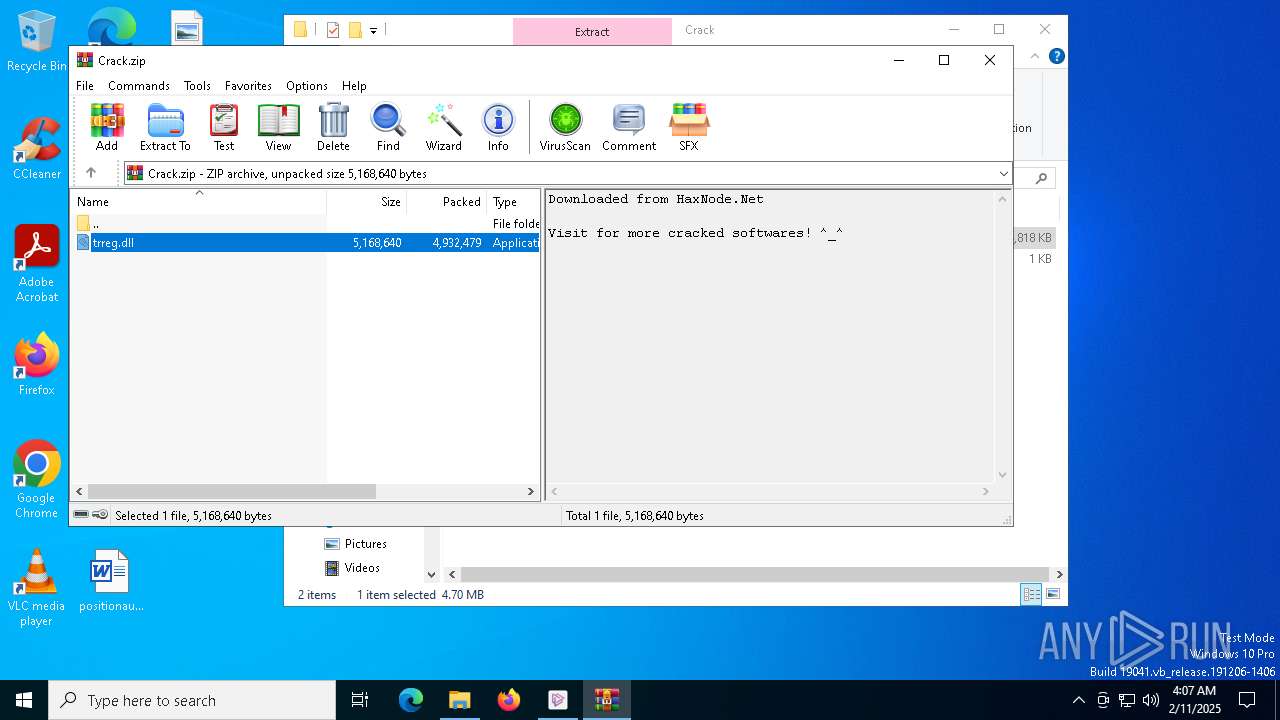
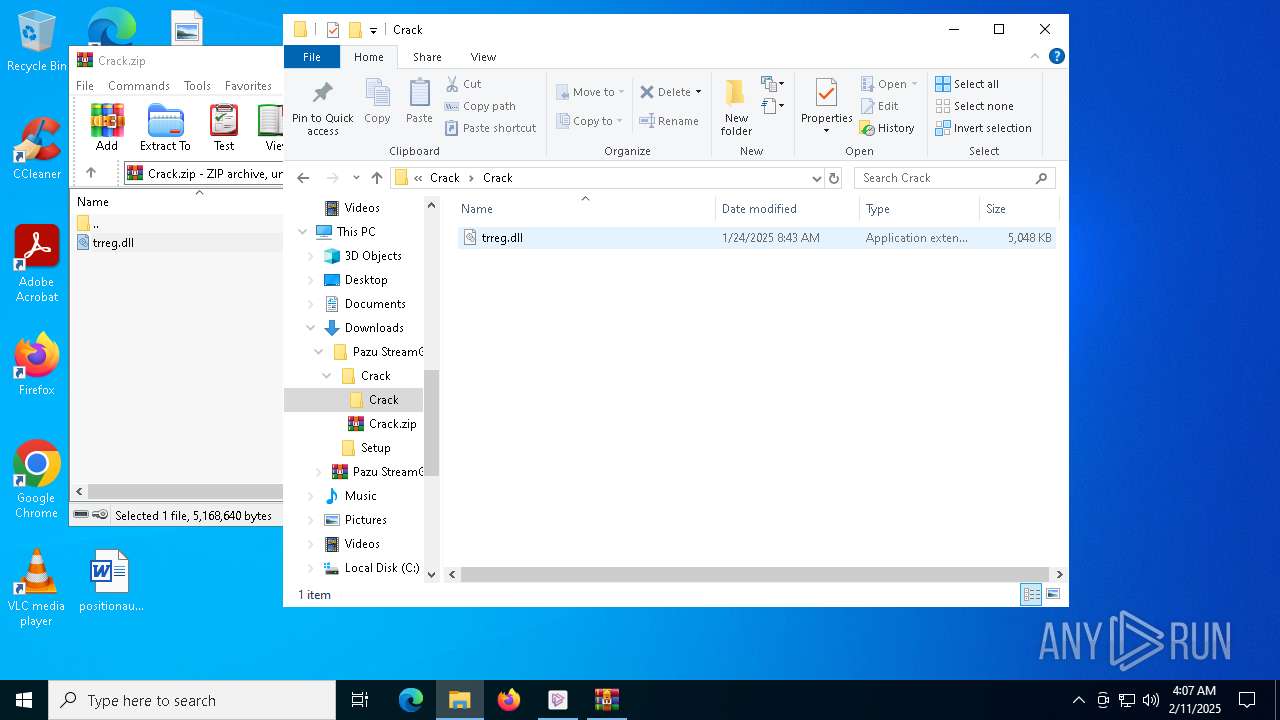
The process creates files with name similar to system file names
- pazu-stream-get-dl.exe (PID: 7440)
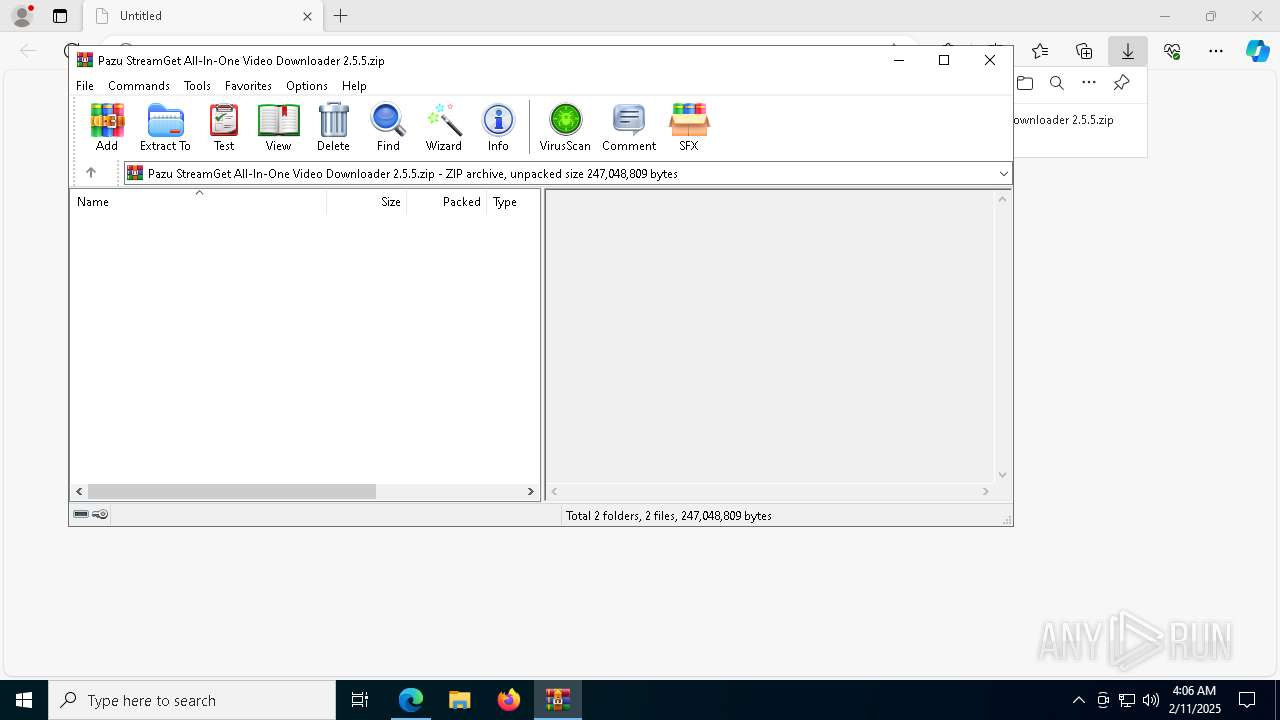
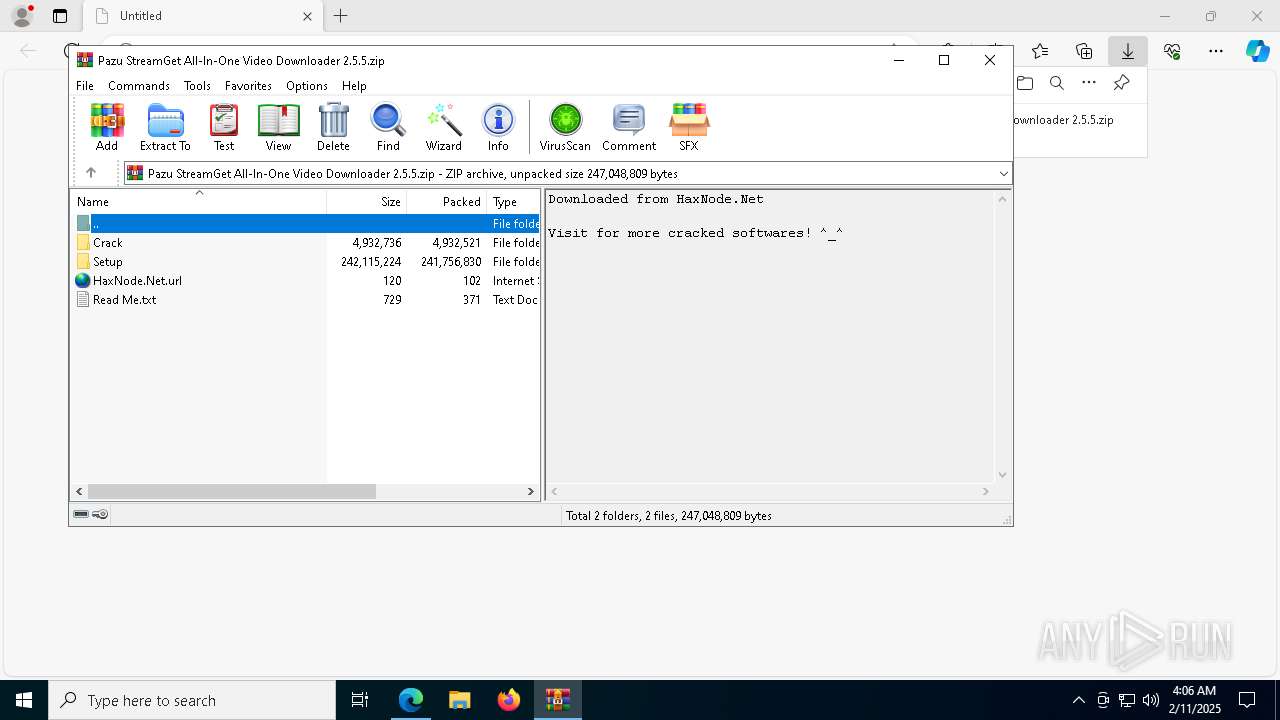
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 5640)
- pazu-stream-get-dl.exe (PID: 7440)
- Pazu StreamGet.exe (PID: 5032)
- ShellExperienceHost.exe (PID: 7400)
Get information on the list of running processes
- pazu-stream-get-dl.exe (PID: 7440)
- cmd.exe (PID: 7692)
Malware-specific behavior (creating "System.dll" in Temp)
- pazu-stream-get-dl.exe (PID: 7440)
There is functionality for taking screenshot (YARA)
- pazu-stream-get-dl.exe (PID: 7440)
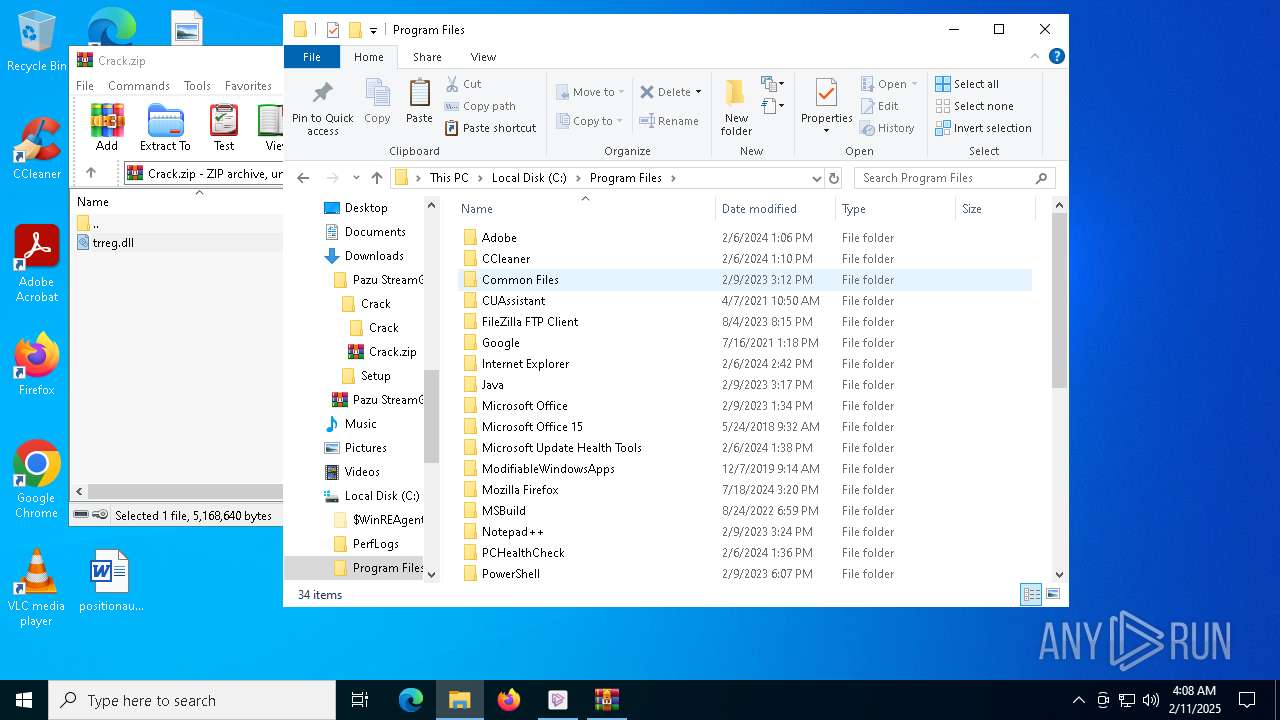
Process drops legitimate windows executable
- pazu-stream-get-dl.exe (PID: 7440)
- Pazu StreamGet.exe (PID: 6292)
Starts CMD.EXE for commands execution
- pazu-stream-get-dl.exe (PID: 7440)
- Pazu StreamGet.exe (PID: 6292)
Drops 7-zip archiver for unpacking
- pazu-stream-get-dl.exe (PID: 7440)
Creates a software uninstall entry
- pazu-stream-get-dl.exe (PID: 7440)
The process drops C-runtime libraries
- pazu-stream-get-dl.exe (PID: 7440)
- Pazu StreamGet.exe (PID: 6292)
Application launched itself
- Pazu StreamGet.exe (PID: 6292)
Starts POWERSHELL.EXE for commands execution
- Pazu StreamGet.exe (PID: 6292)
The process hides Powershell's copyright startup banner
- Pazu StreamGet.exe (PID: 6292)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 6032)
Starts application with an unusual extension
- cmd.exe (PID: 6164)
INFO
Reads the computer name
- identity_helper.exe (PID: 7476)
- identity_helper.exe (PID: 2100)
- pazu-stream-get-dl.exe (PID: 7440)
- Pazu StreamGet.exe (PID: 6292)
- Pazu StreamGet.exe (PID: 7240)
- Pazu StreamGet.exe (PID: 6520)
- Pazu StreamGet.exe (PID: 5032)
- ShellExperienceHost.exe (PID: 7400)
Reads Environment values
- identity_helper.exe (PID: 2100)
- identity_helper.exe (PID: 7476)
- Pazu StreamGet.exe (PID: 6292)
- Pazu StreamGet.exe (PID: 2680)
- Pazu StreamGet.exe (PID: 7132)
Checks supported languages
- pazu-stream-get-dl.exe (PID: 7440)
- identity_helper.exe (PID: 7476)
- identity_helper.exe (PID: 2100)
- Pazu StreamGet.exe (PID: 6292)
- chcp.com (PID: 4556)
- Pazu StreamGet.exe (PID: 7240)
- Pazu StreamGet.exe (PID: 6520)
- Pazu StreamGet.exe (PID: 2680)
- Pazu StreamGet.exe (PID: 7132)
- Pazu StreamGet.exe (PID: 5032)
- Pazu StreamGet.exe (PID: 6776)
- Pazu StreamGet.exe (PID: 8072)
- Pazu StreamGet.exe (PID: 3808)
- Pazu StreamGet.exe (PID: 7296)
- ShellExperienceHost.exe (PID: 7400)
Application launched itself
- msedge.exe (PID: 4628)
- msedge.exe (PID: 4704)
Local mutex for internet shortcut management
- WinRAR.exe (PID: 5640)
Reads Microsoft Office registry keys
- msedge.exe (PID: 4628)
Create files in a temporary directory
- pazu-stream-get-dl.exe (PID: 7440)
- Pazu StreamGet.exe (PID: 6292)
- Pazu StreamGet.exe (PID: 2680)
- Pazu StreamGet.exe (PID: 7132)
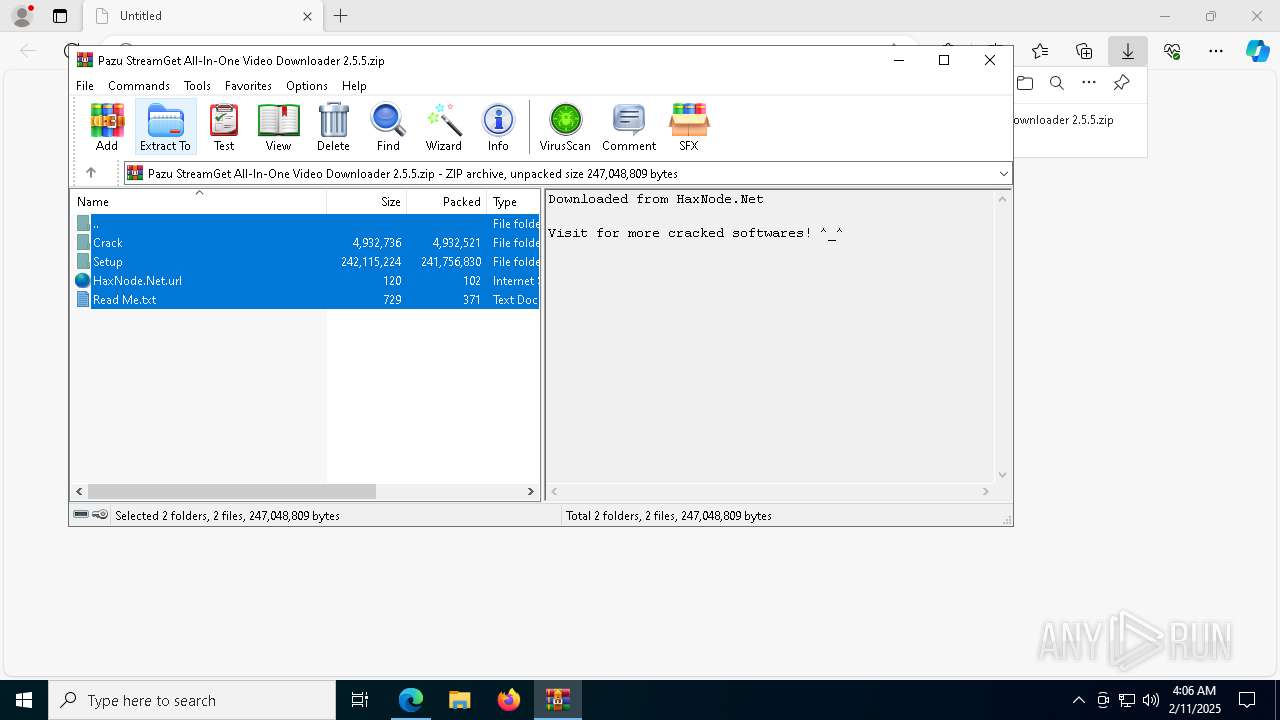
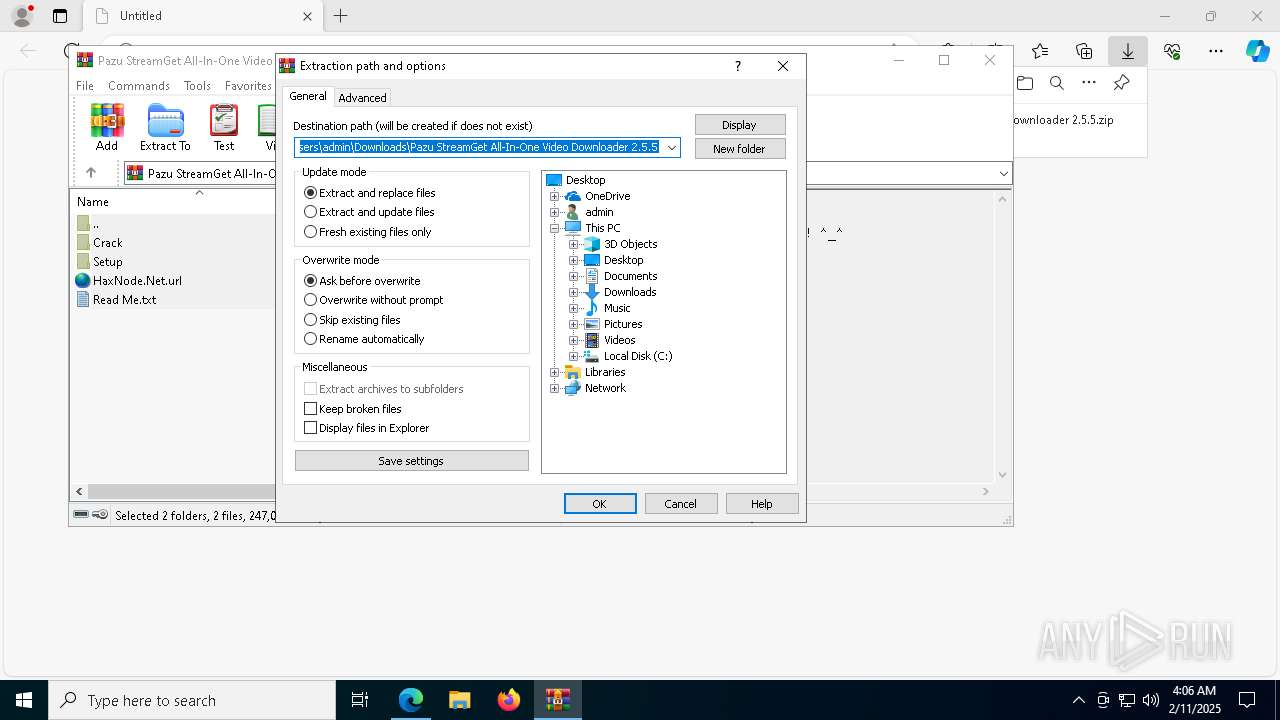
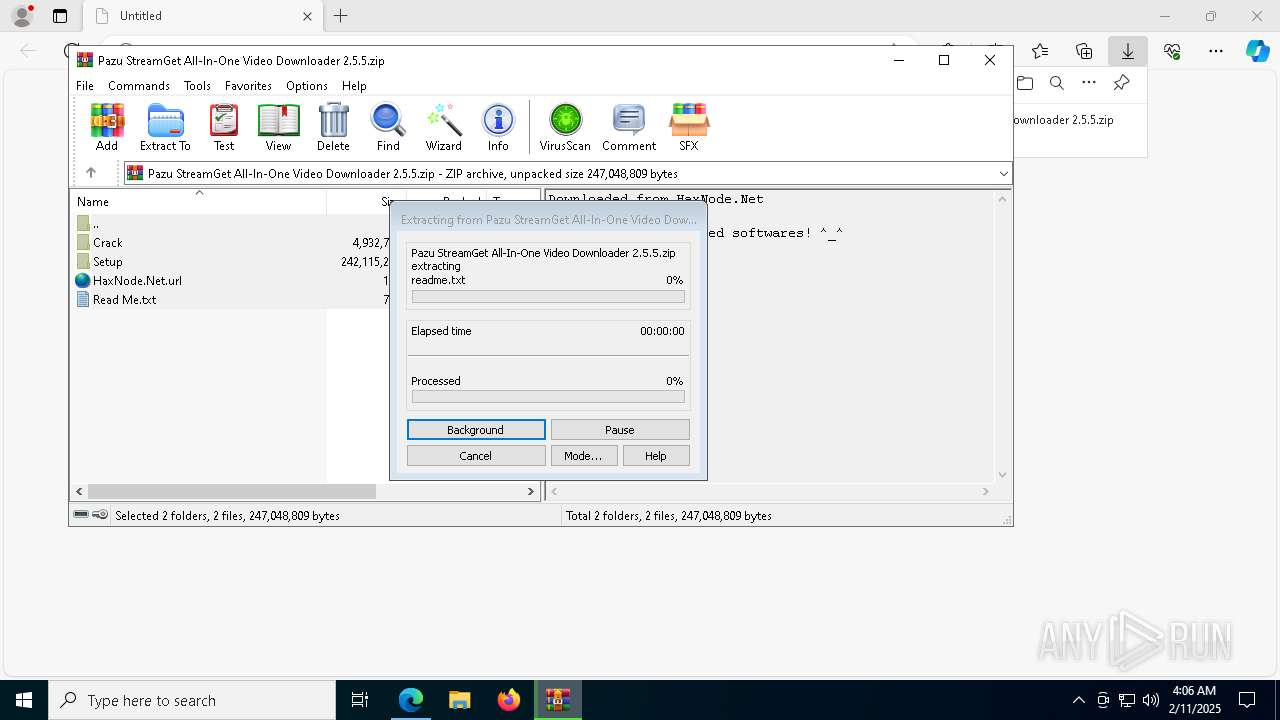
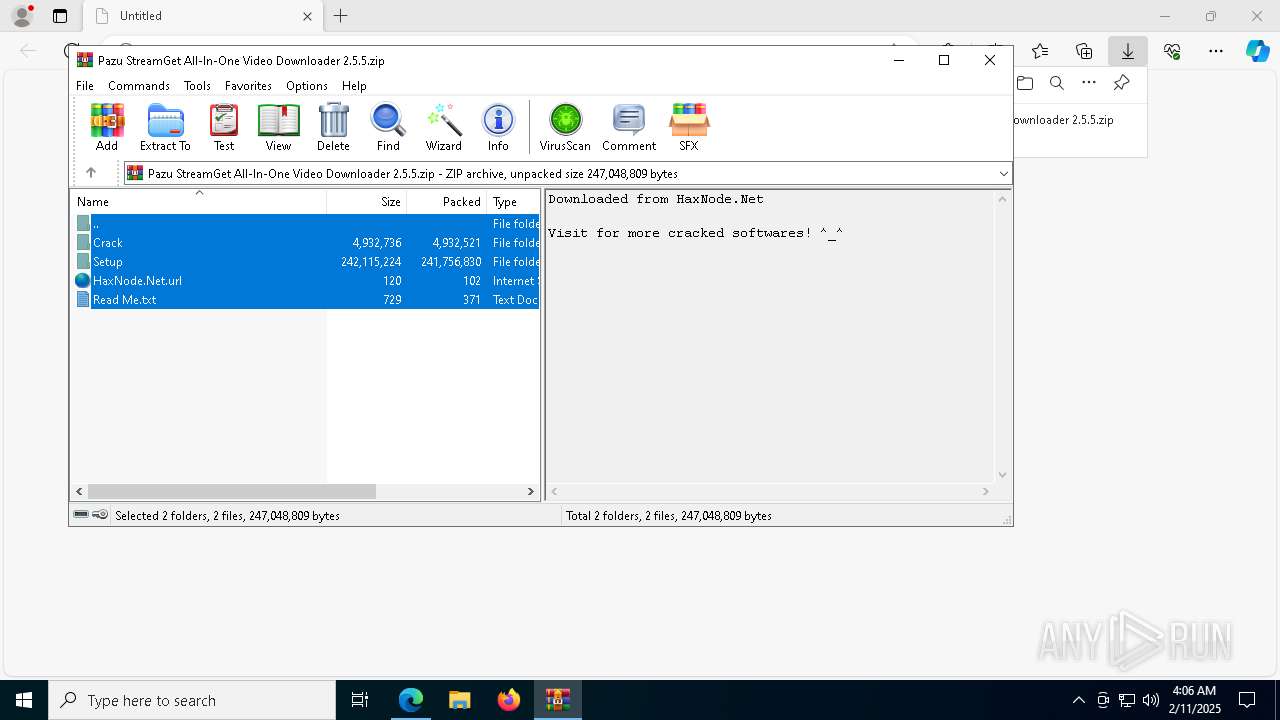
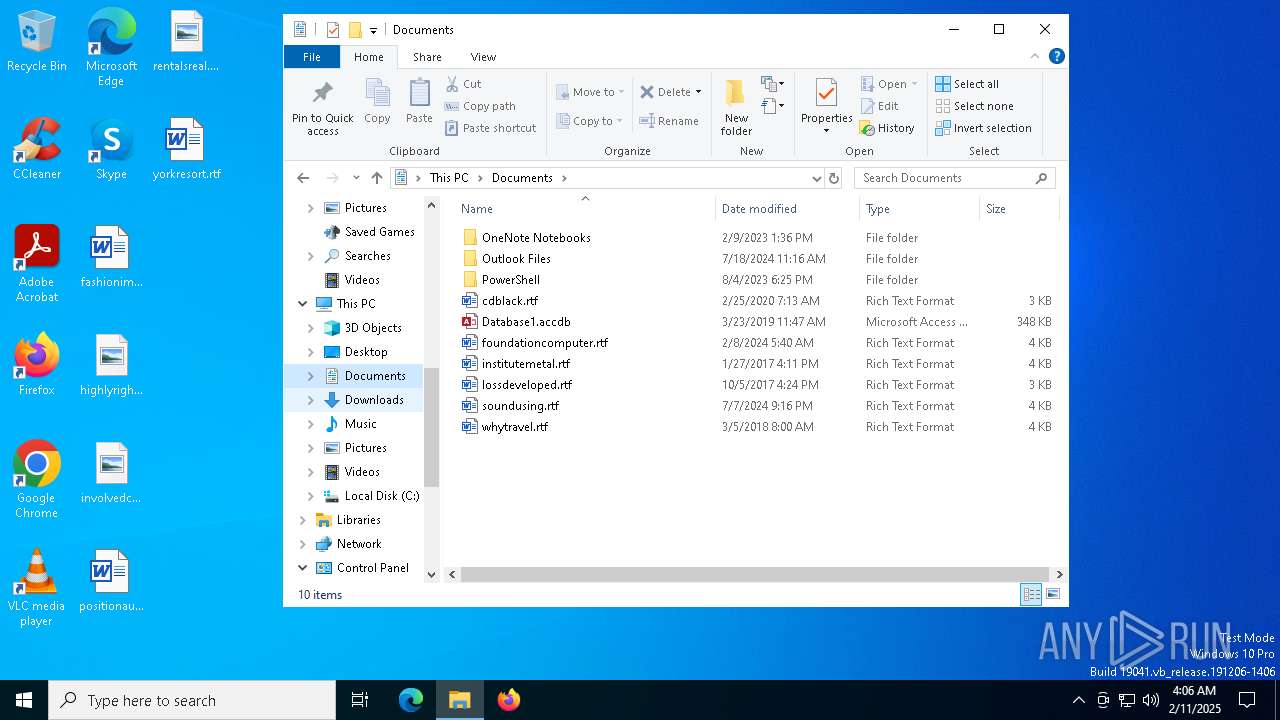
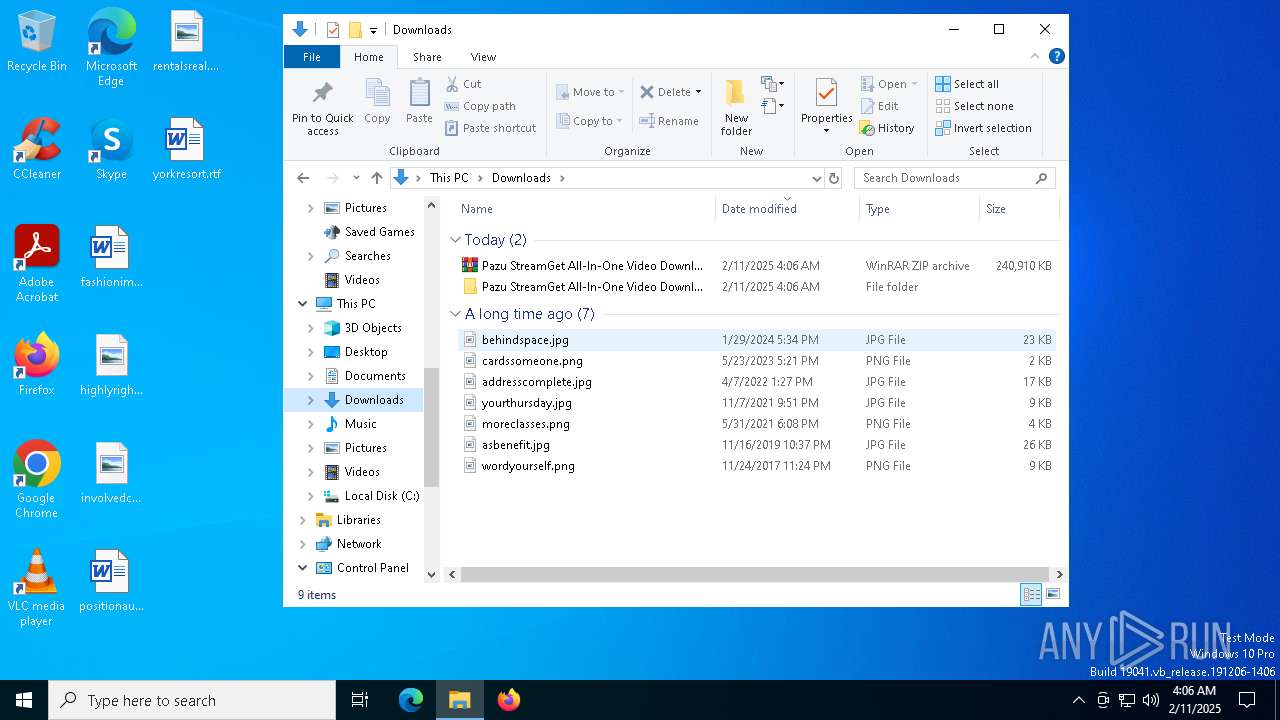
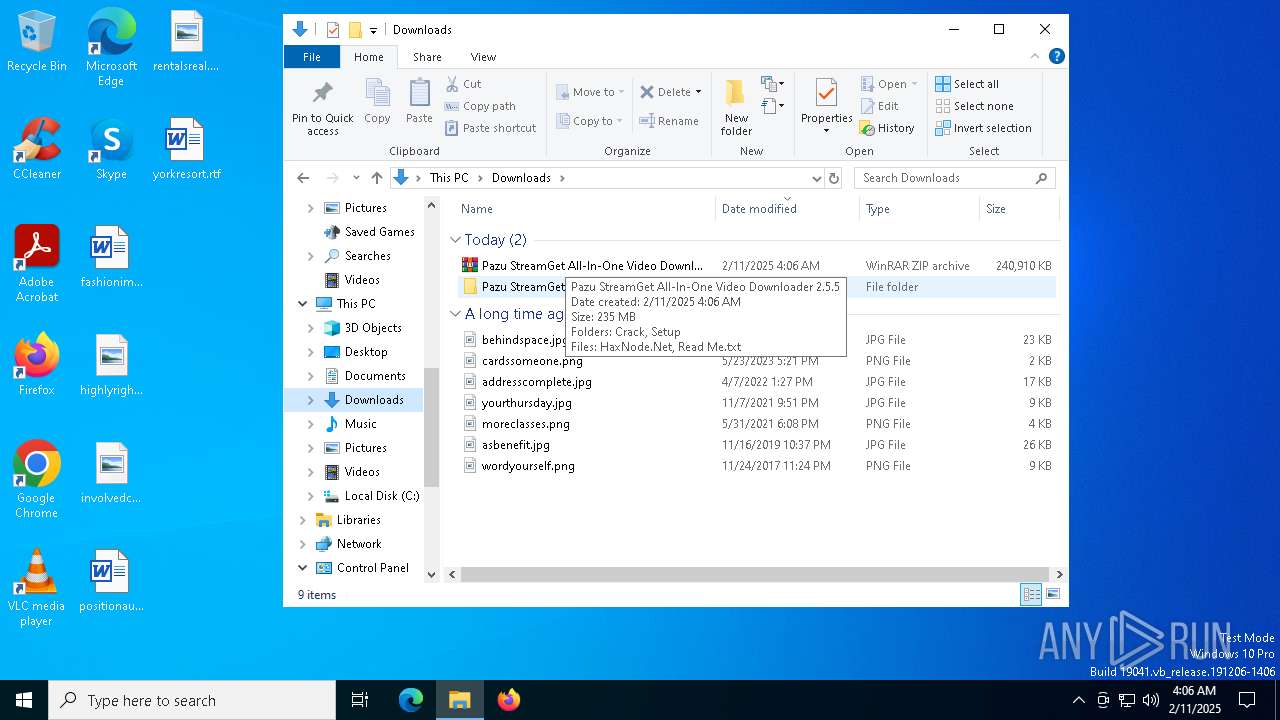
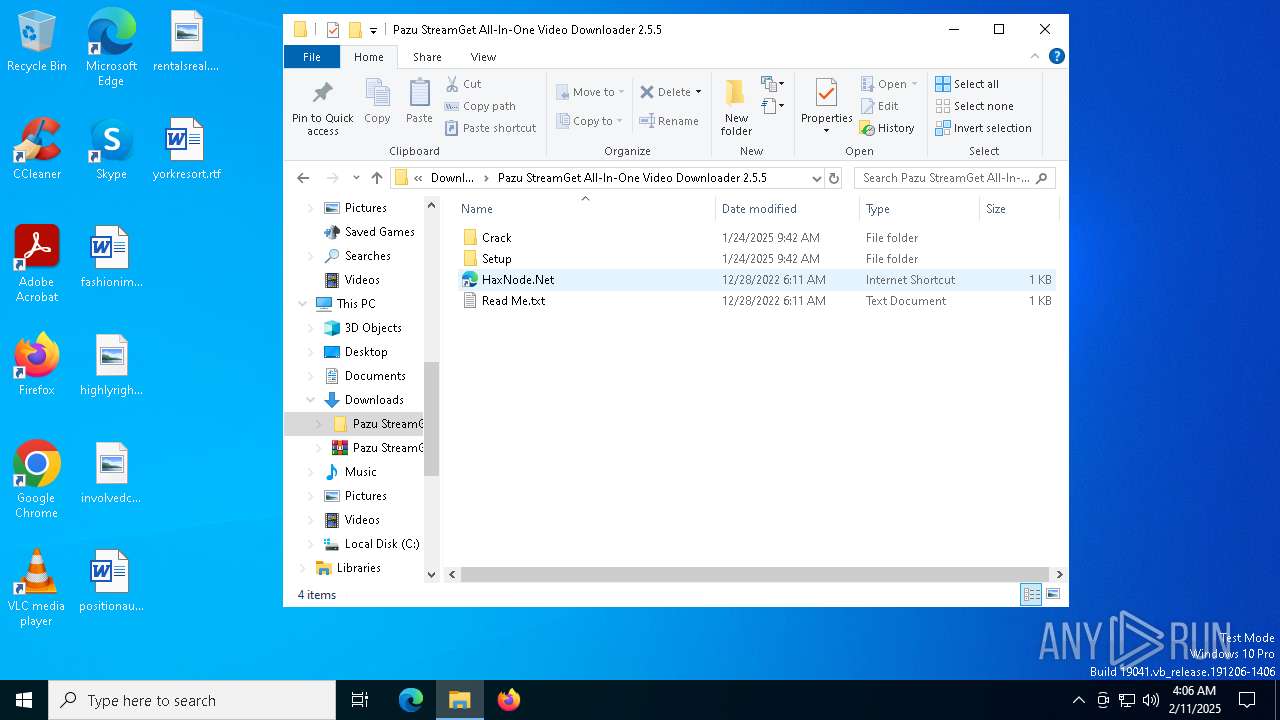
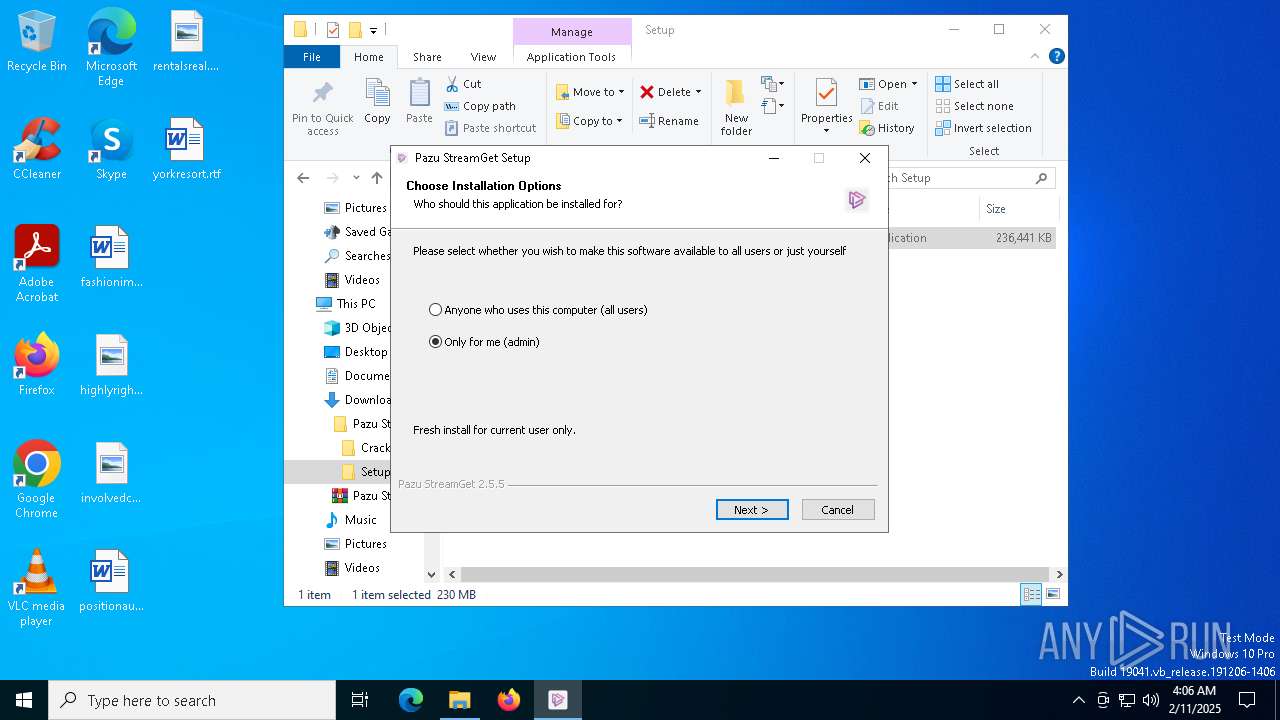
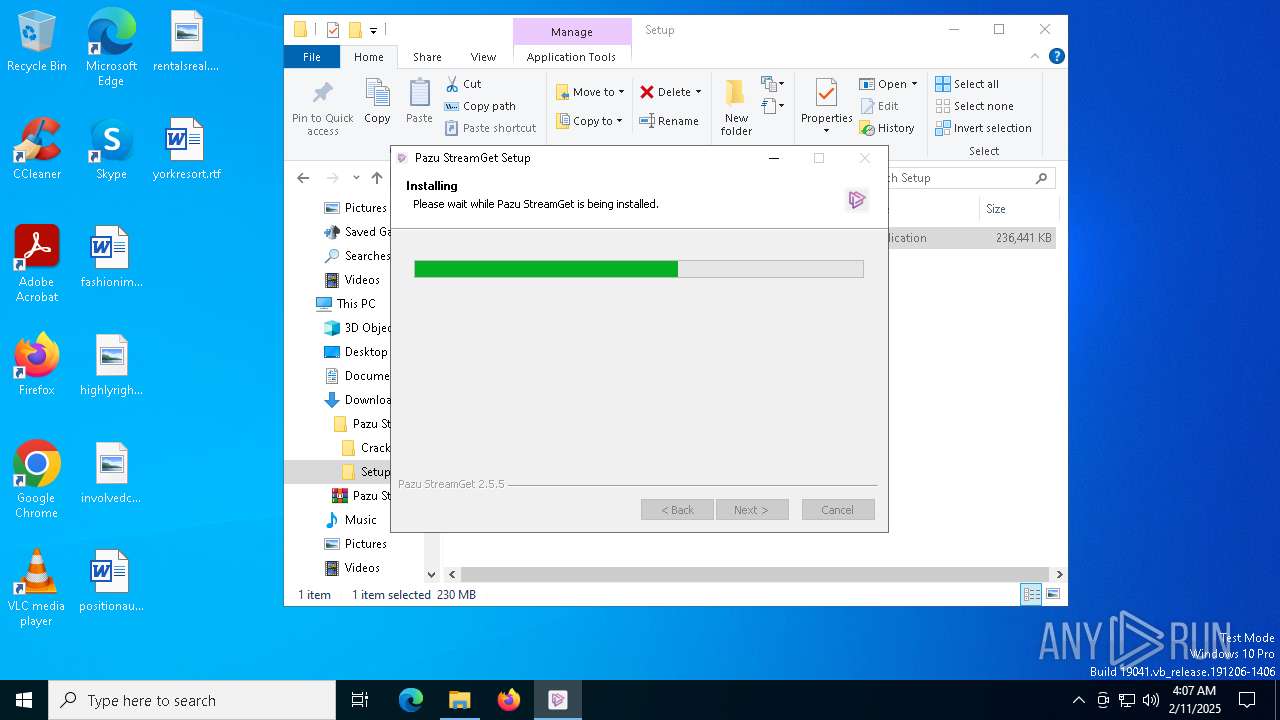
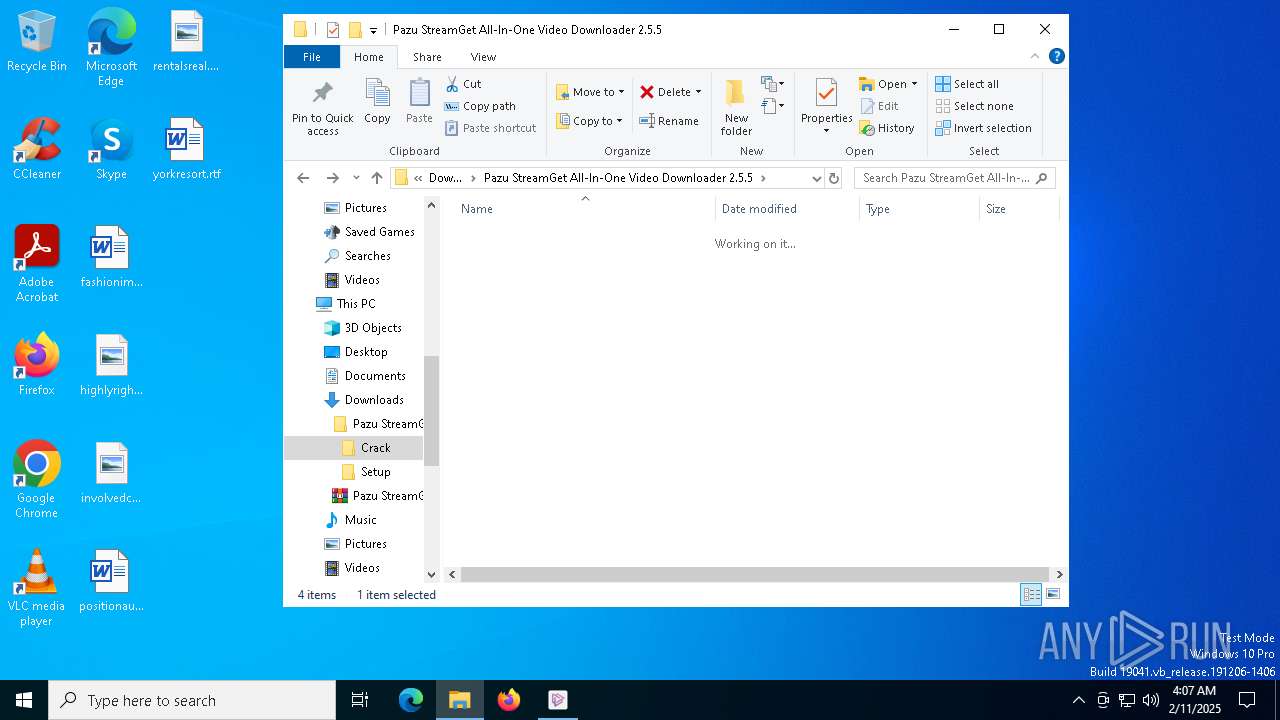
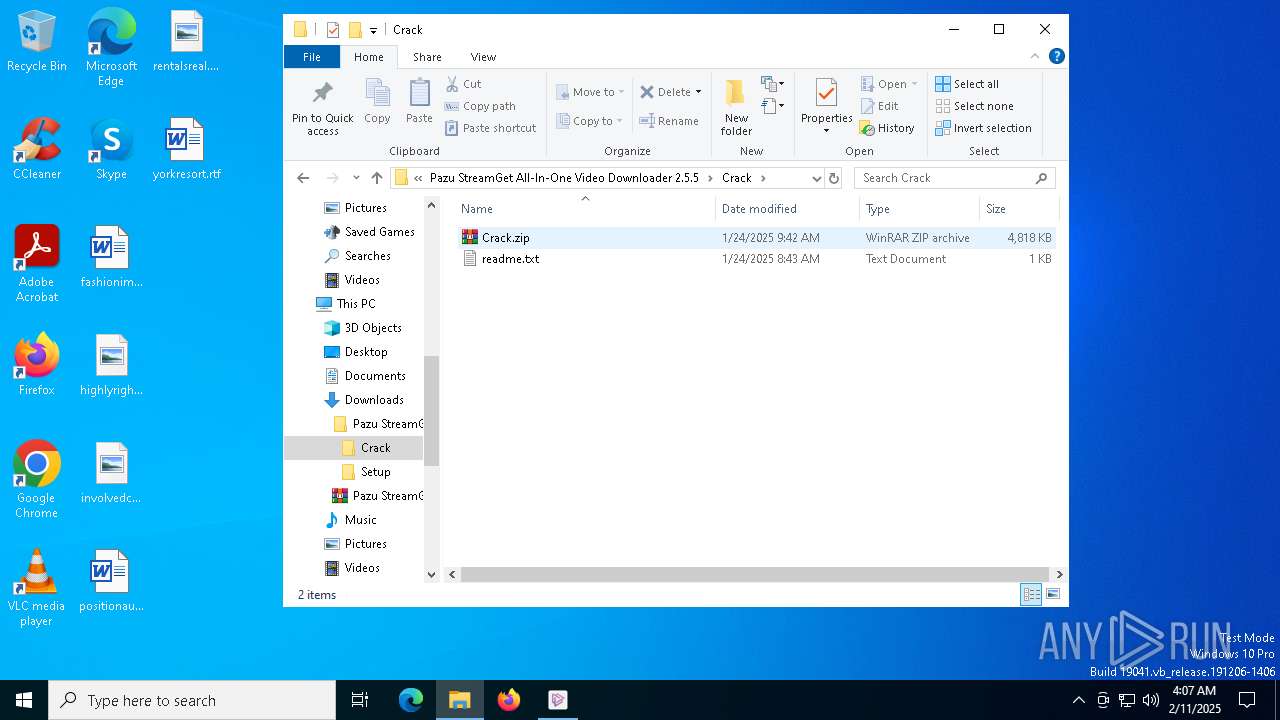
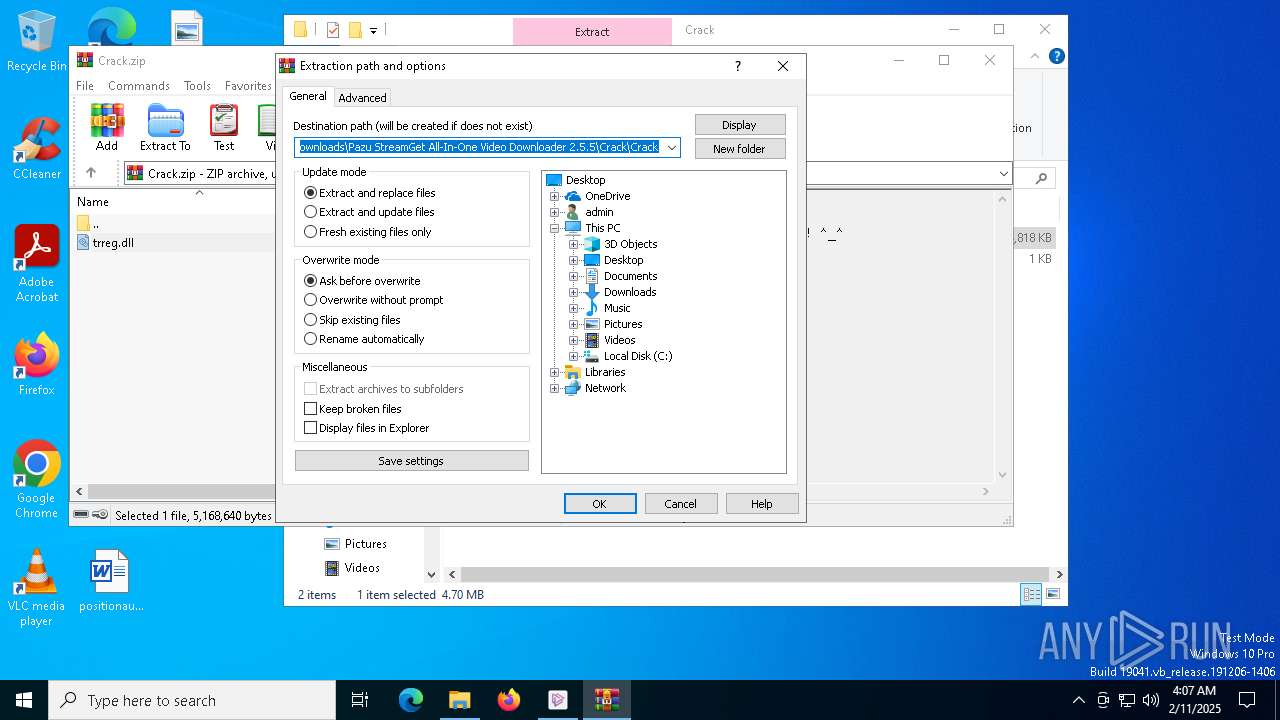
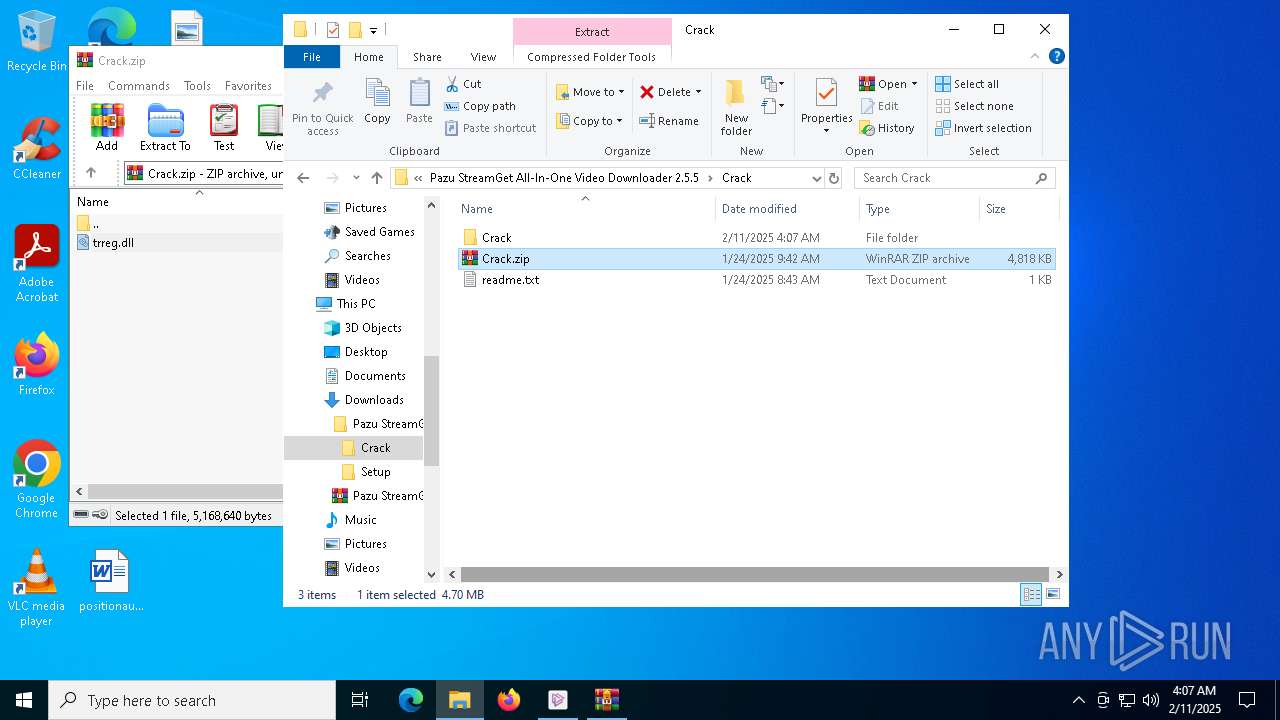
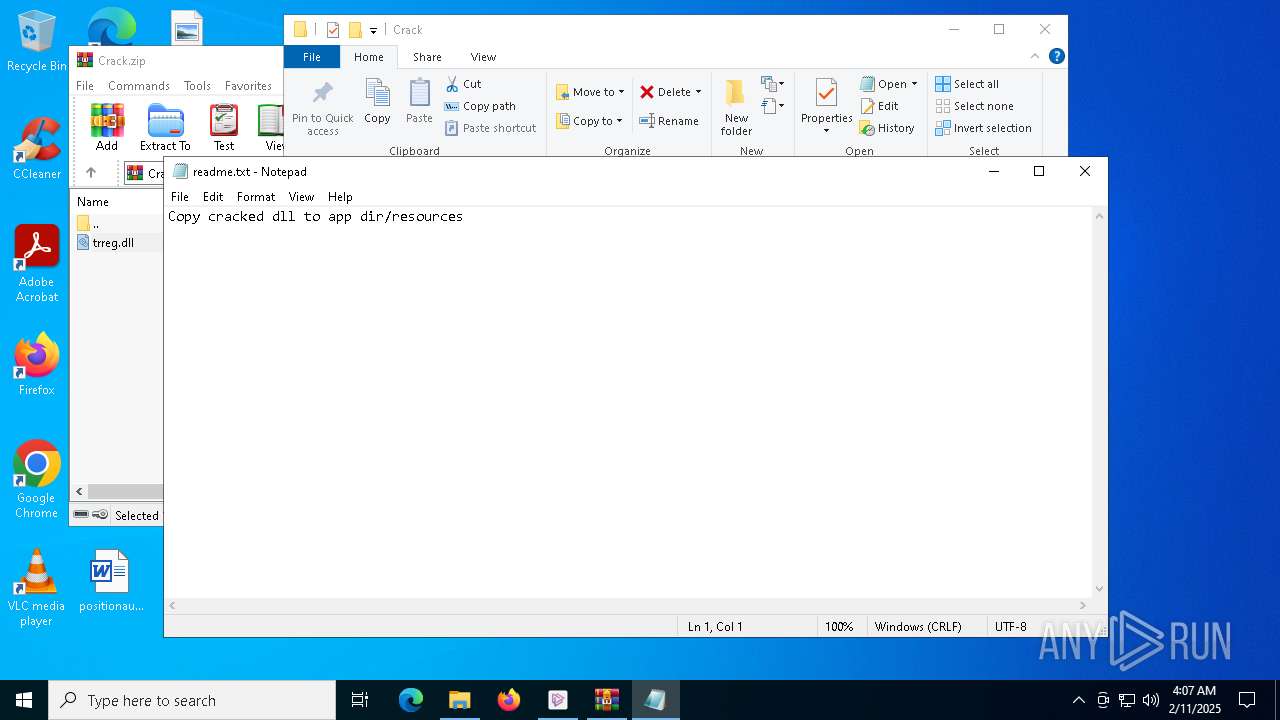
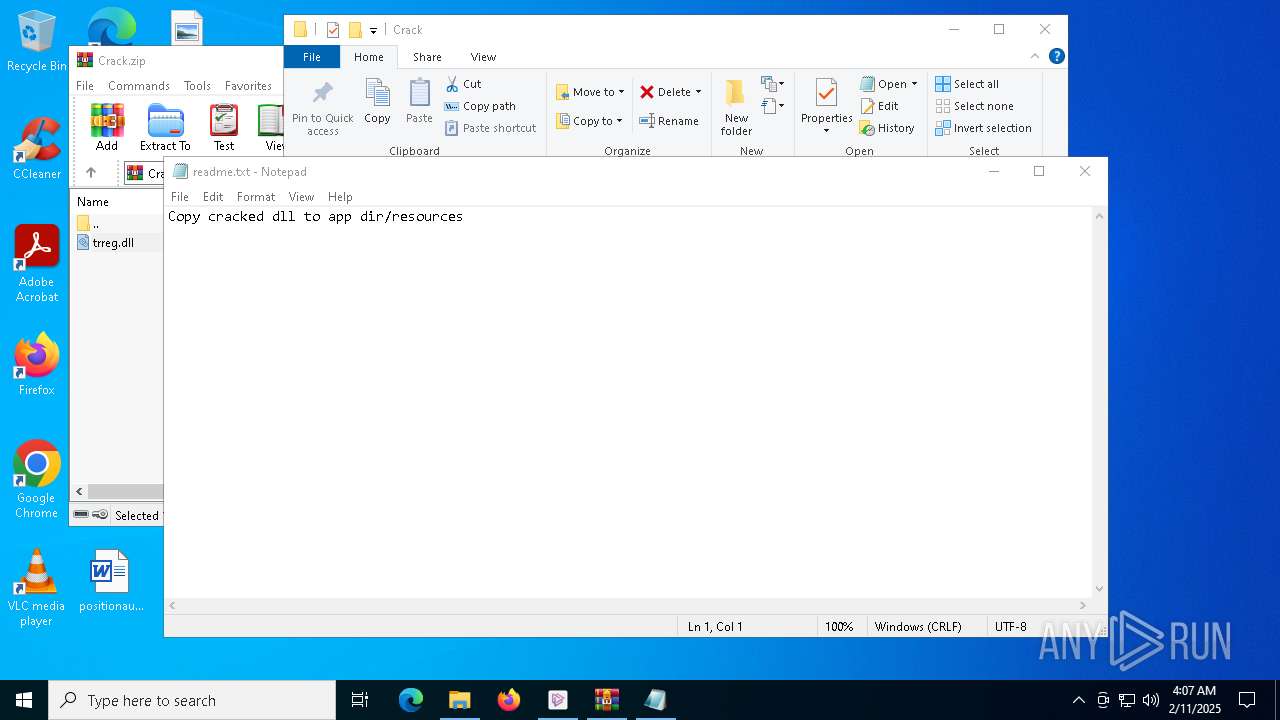
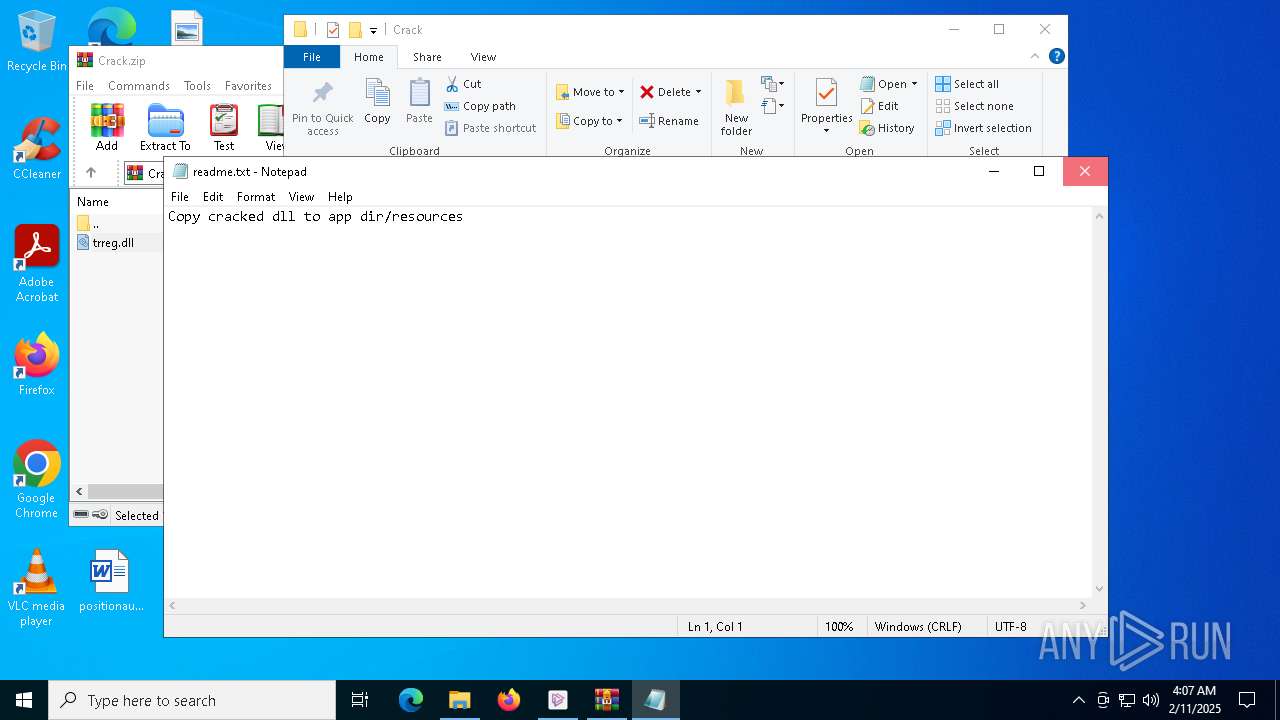
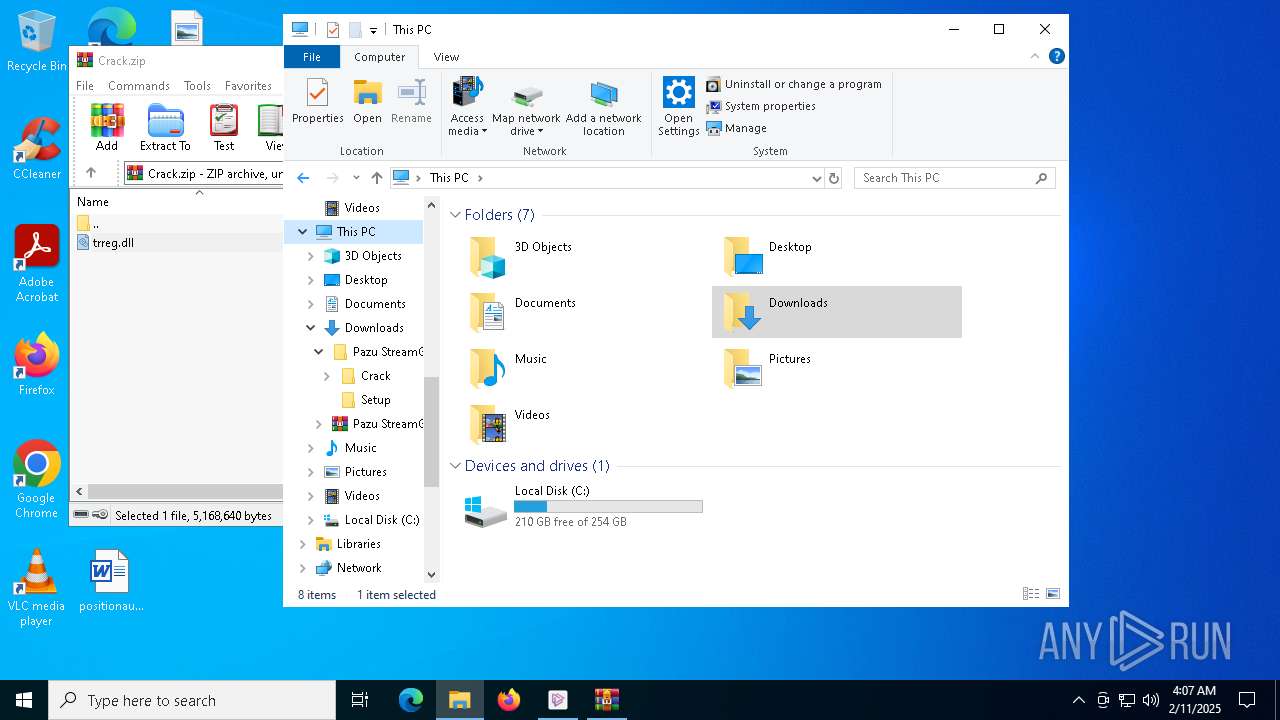
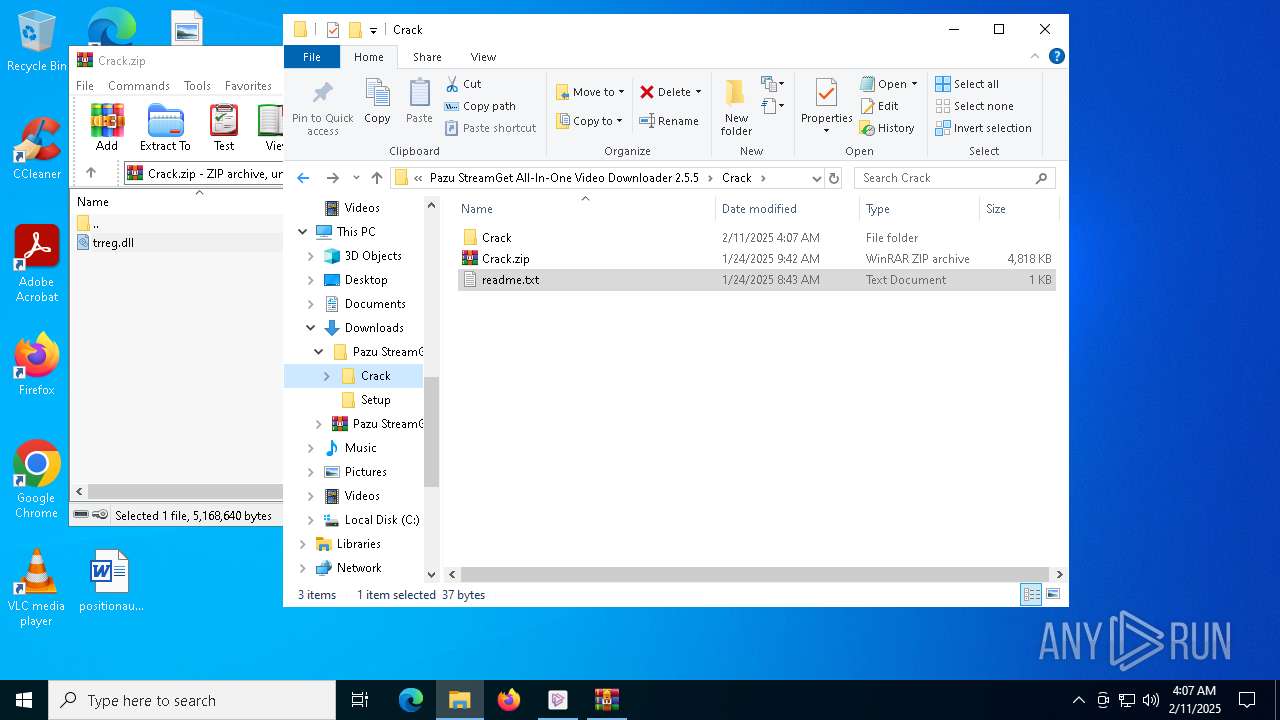
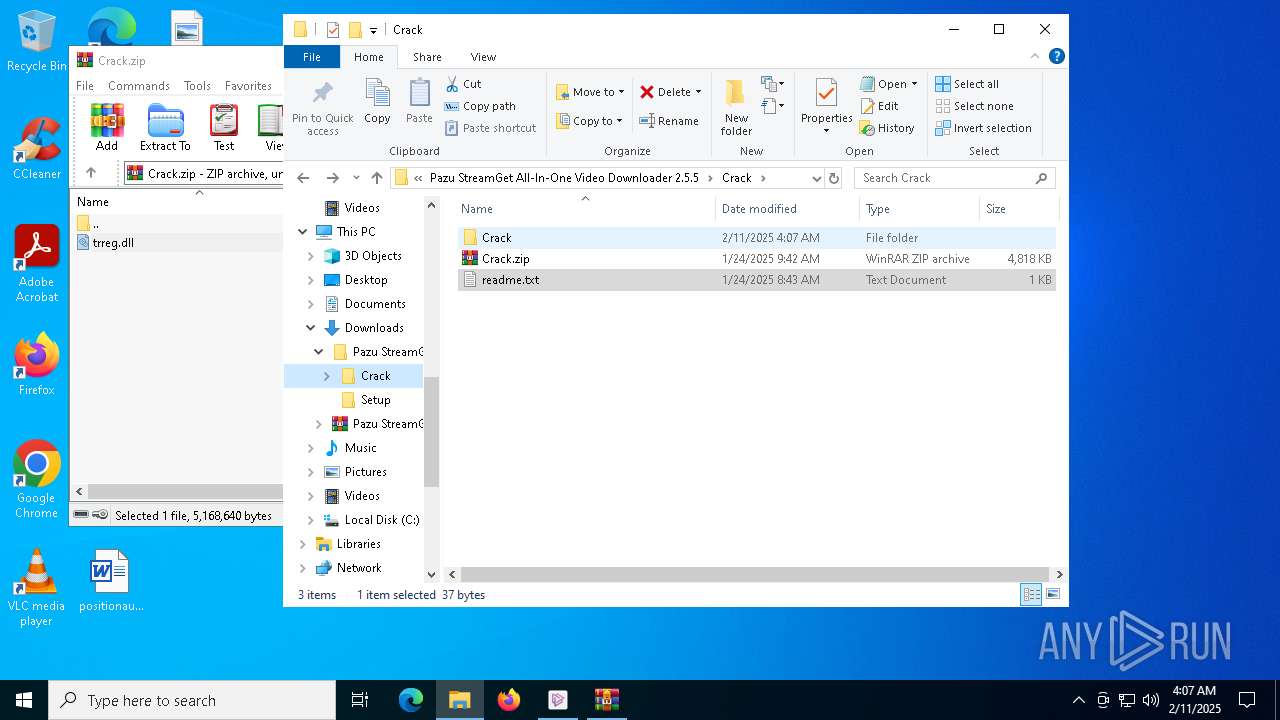
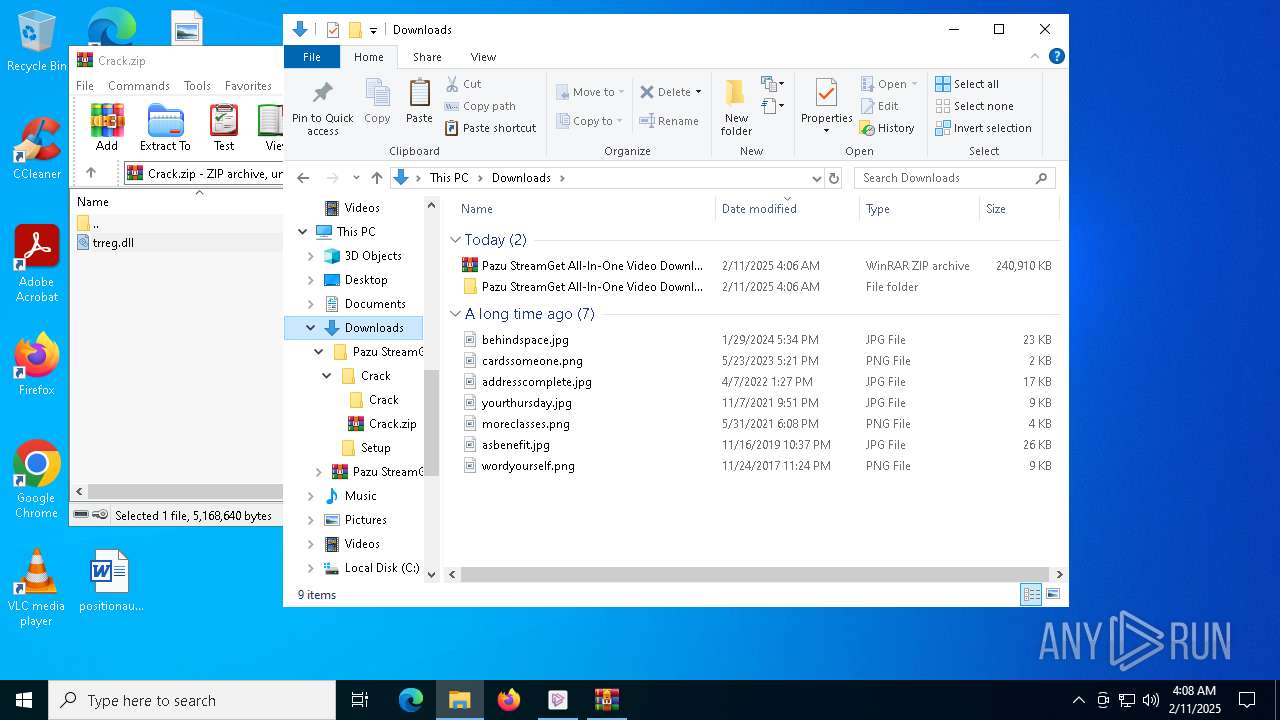
Manual execution by a user
- pazu-stream-get-dl.exe (PID: 7440)
- WinRAR.exe (PID: 5256)
- notepad.exe (PID: 7340)
- Pazu StreamGet.exe (PID: 6292)
- Pazu StreamGet.exe (PID: 2680)
- Pazu StreamGet.exe (PID: 7132)
The sample compiled with english language support
- pazu-stream-get-dl.exe (PID: 7440)
- msedge.exe (PID: 6808)
- Pazu StreamGet.exe (PID: 6292)
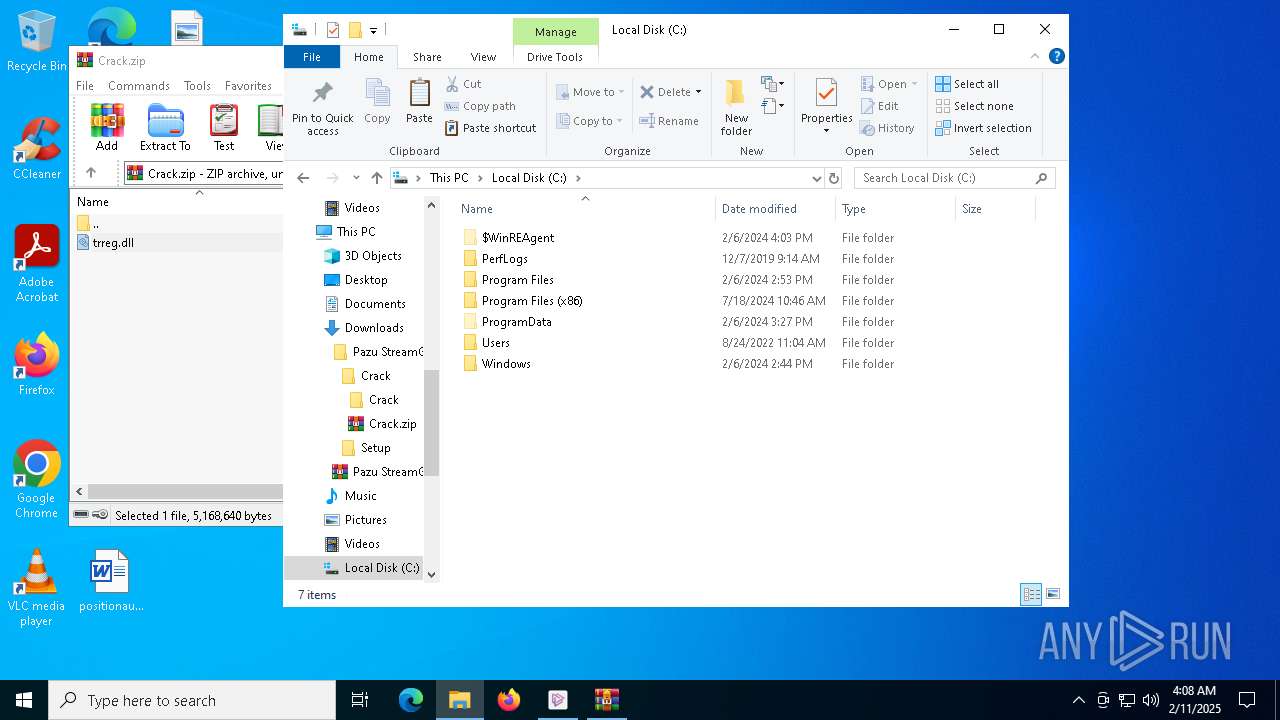
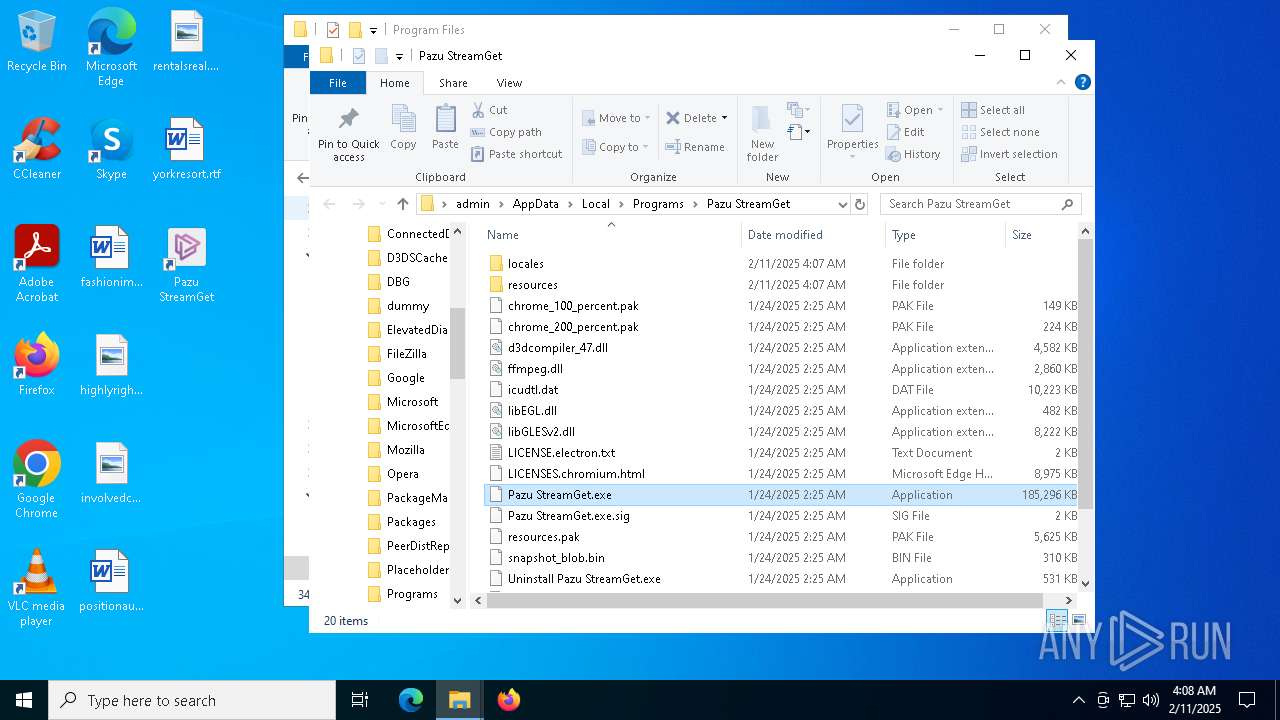
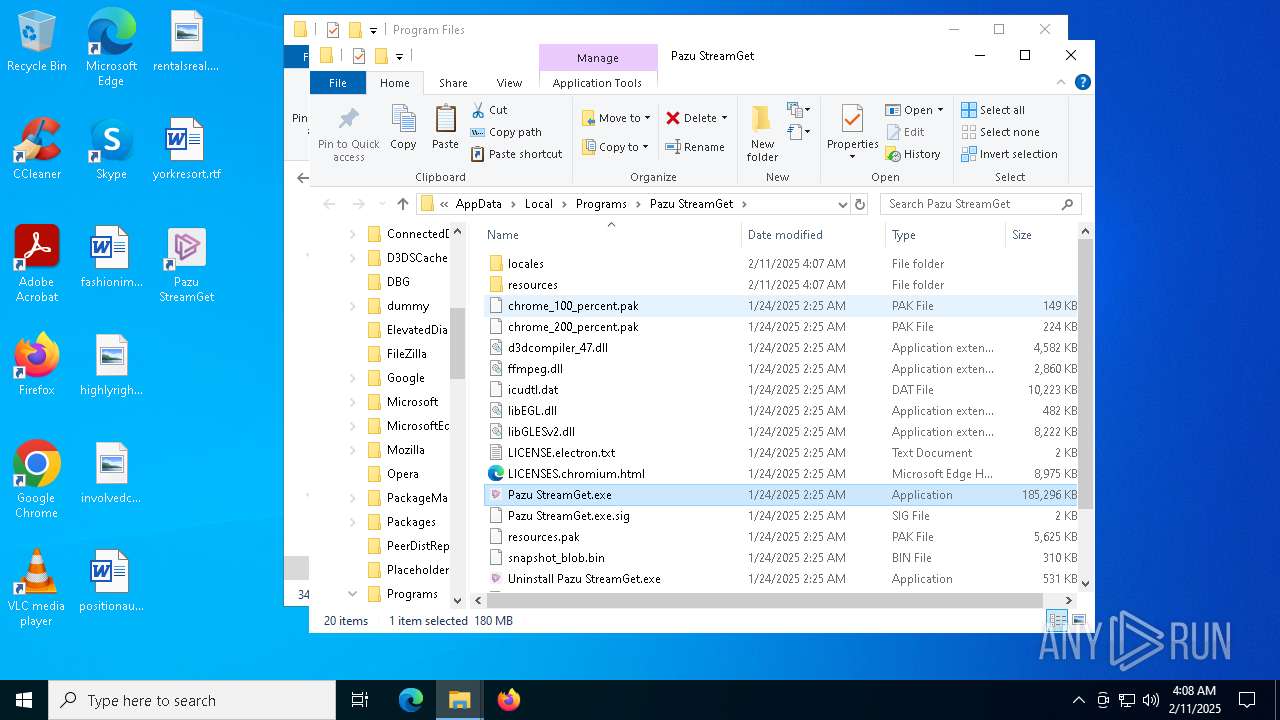
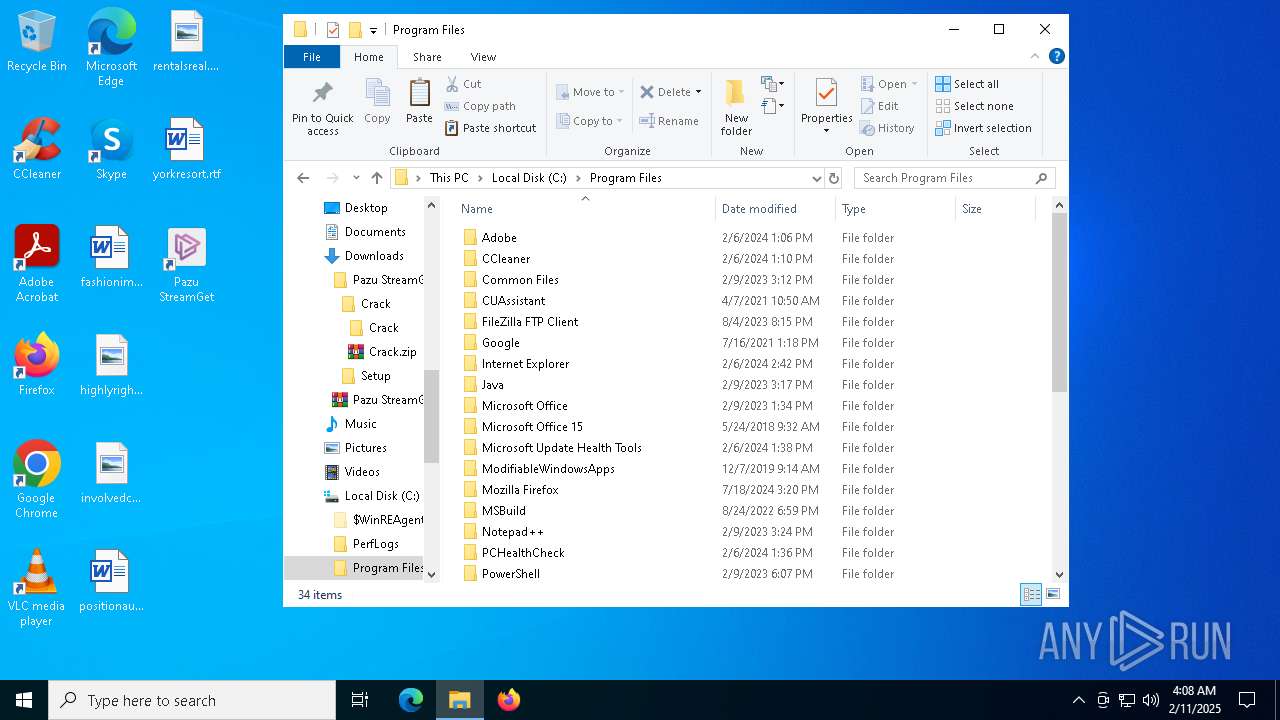
Creates files or folders in the user directory
- pazu-stream-get-dl.exe (PID: 7440)
- Pazu StreamGet.exe (PID: 6292)
- Pazu StreamGet.exe (PID: 2680)
- Pazu StreamGet.exe (PID: 6520)
- Pazu StreamGet.exe (PID: 7132)
The sample compiled with chinese language support
- pazu-stream-get-dl.exe (PID: 7440)
- Pazu StreamGet.exe (PID: 6292)
Reads security settings of Internet Explorer
- notepad.exe (PID: 7340)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5256)
- msedge.exe (PID: 6808)
Reads product name
- Pazu StreamGet.exe (PID: 6292)
- Pazu StreamGet.exe (PID: 2680)
- Pazu StreamGet.exe (PID: 7132)
Process checks computer location settings
- Pazu StreamGet.exe (PID: 6292)
- Pazu StreamGet.exe (PID: 2680)
- Pazu StreamGet.exe (PID: 7132)
- Pazu StreamGet.exe (PID: 3808)
- Pazu StreamGet.exe (PID: 5032)
- Pazu StreamGet.exe (PID: 6776)
- Pazu StreamGet.exe (PID: 8072)
- Pazu StreamGet.exe (PID: 7296)
Changes the display of characters in the console
- cmd.exe (PID: 6164)
Checks proxy server information
- Pazu StreamGet.exe (PID: 6292)
Reads the machine GUID from the registry
- Pazu StreamGet.exe (PID: 6292)
Reads CPU info
- Pazu StreamGet.exe (PID: 6292)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 4864)
- powershell.exe (PID: 7008)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
294
Monitored processes
152
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 776 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5496 --field-trial-handle=2376,i,6966326665561164648,8614912177678588608,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
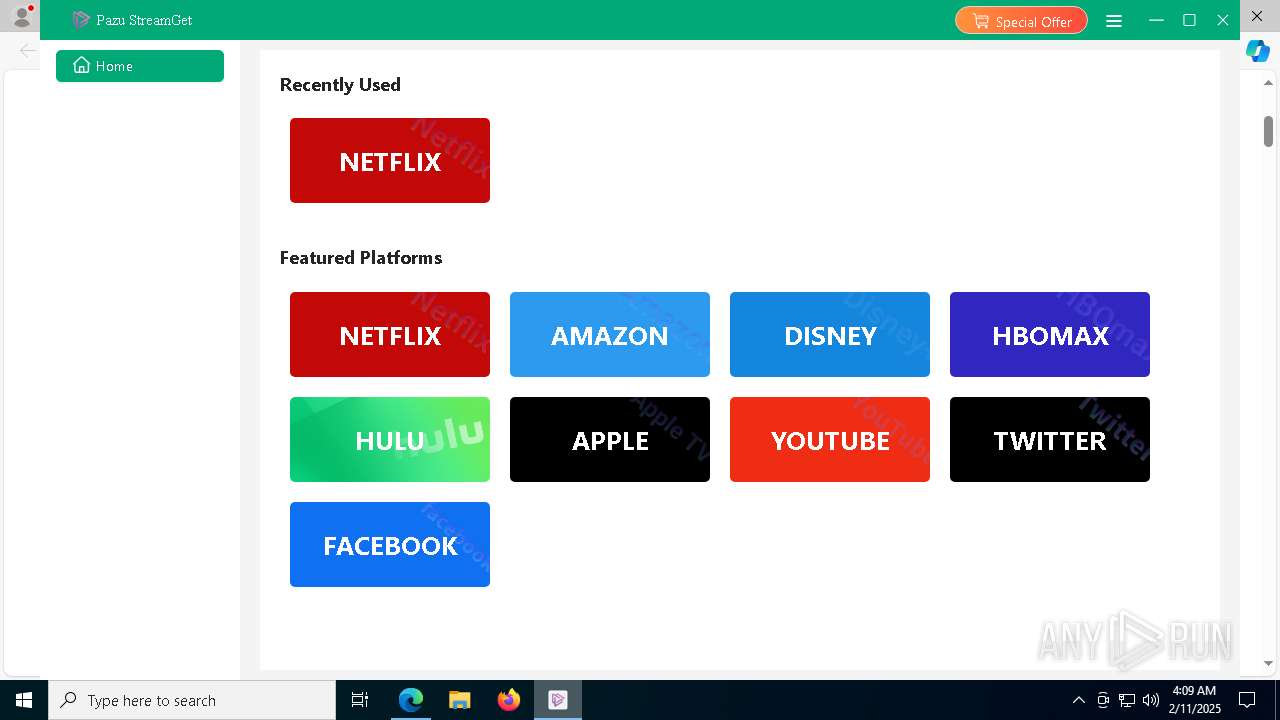
| 836 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --single-argument https://www.pazu-video.com/streamget-all-in-one-for-windows/tutorial.html | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | Pazu StreamGet.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 876 | powershell.exe -NoLogo -InputFormat Text -NoExit -ExecutionPolicy Unrestricted -Command - | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Pazu StreamGet.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1192 | powershell.exe -NoLogo -InputFormat Text -NoExit -ExecutionPolicy Unrestricted -Command - | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Pazu StreamGet.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1200 | powershell.exe -NoLogo -InputFormat Text -NoExit -ExecutionPolicy Unrestricted -Command - | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | Pazu StreamGet.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1216 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1228 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5644 --field-trial-handle=2496,i,481348761500101144,9443811992353791994,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1476 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1612 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=33 --mojo-platform-channel-handle=5200 --field-trial-handle=2376,i,6966326665561164648,8614912177678588608,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1856 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
105 394
Read events
105 258
Write events
93
Delete events
43
Modification events
| (PID) Process: | (4628) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: A921E1336C8C2F00 | |||
| (PID) Process: | (4628) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 4CAEF4336C8C2F00 | |||
| (PID) Process: | (4628) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4628) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4628) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4628) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4628) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328428 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {1B89CC30-7F68-4282-AD9C-65D23D3F65E4} | |||
| (PID) Process: | (4628) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328428 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {05B050D3-D61C-4A9A-98A4-F9CB94A37A48} | |||
| (PID) Process: | (4628) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 07A133346C8C2F00 | |||
| (PID) Process: | (4628) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
Executable files
328
Suspicious files
872
Text files
187
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4628 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1354f9.TMP | — | |
MD5:— | SHA256:— | |||
| 4628 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4628 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1354f9.TMP | — | |
MD5:— | SHA256:— | |||
| 4628 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4628 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1354f9.TMP | — | |
MD5:— | SHA256:— | |||
| 4628 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4628 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1354f9.TMP | — | |
MD5:— | SHA256:— | |||
| 4628 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4628 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF135509.TMP | — | |
MD5:— | SHA256:— | |||
| 4628 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
49
TCP/UDP connections
117
DNS requests
119
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5064 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
7932 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1739801490&P2=404&P3=2&P4=LnVTeQv7HvinIkNeScyT0q1DjKwiTryC6OlK85vRb3LAlrrD5JttLaumn6Kz9Hry6uADwAbMc12%2beK2bgKDuow%3d%3d | unknown | — | — | whitelisted |
6484 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5872 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7932 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/e74ec02c-7f50-4b67-9a51-6cc67399bc04?P1=1739801491&P2=404&P3=2&P4=BCnE4NTa4EfXhQLTebnrOrKDCaCzS%2bERtZneQoOs%2bAVLUu81oDqO0nz4Vwvk4bGJiAxAr82aqegRc6dH%2bBasLQ%3d%3d | unknown | — | — | whitelisted |
7932 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1739801490&P2=404&P3=2&P4=LnVTeQv7HvinIkNeScyT0q1DjKwiTryC6OlK85vRb3LAlrrD5JttLaumn6Kz9Hry6uADwAbMc12%2beK2bgKDuow%3d%3d | unknown | — | — | whitelisted |
7932 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1739801490&P2=404&P3=2&P4=LnVTeQv7HvinIkNeScyT0q1DjKwiTryC6OlK85vRb3LAlrrD5JttLaumn6Kz9Hry6uADwAbMc12%2beK2bgKDuow%3d%3d | unknown | — | — | whitelisted |
7932 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/e74ec02c-7f50-4b67-9a51-6cc67399bc04?P1=1739801491&P2=404&P3=2&P4=BCnE4NTa4EfXhQLTebnrOrKDCaCzS%2bERtZneQoOs%2bAVLUu81oDqO0nz4Vwvk4bGJiAxAr82aqegRc6dH%2bBasLQ%3d%3d | unknown | — | — | whitelisted |
7932 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1739801490&P2=404&P3=2&P4=LnVTeQv7HvinIkNeScyT0q1DjKwiTryC6OlK85vRb3LAlrrD5JttLaumn6Kz9Hry6uADwAbMc12%2beK2bgKDuow%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3568 | svchost.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1412 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1412 | RUXIMICS.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5064 | SearchApp.exe | 104.126.37.155:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
1412 | RUXIMICS.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4628 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6352 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6352 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
1008.filemail.com |
| malicious |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6352 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Observed File Sharing Service Download Domain (filemail.com) |
6352 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Downloading from a file sharing service is observed |