| download: | v113.exe |
| Full analysis: | https://app.any.run/tasks/b86e82c0-032f-42a1-b5c1-57b9411cc9fe |
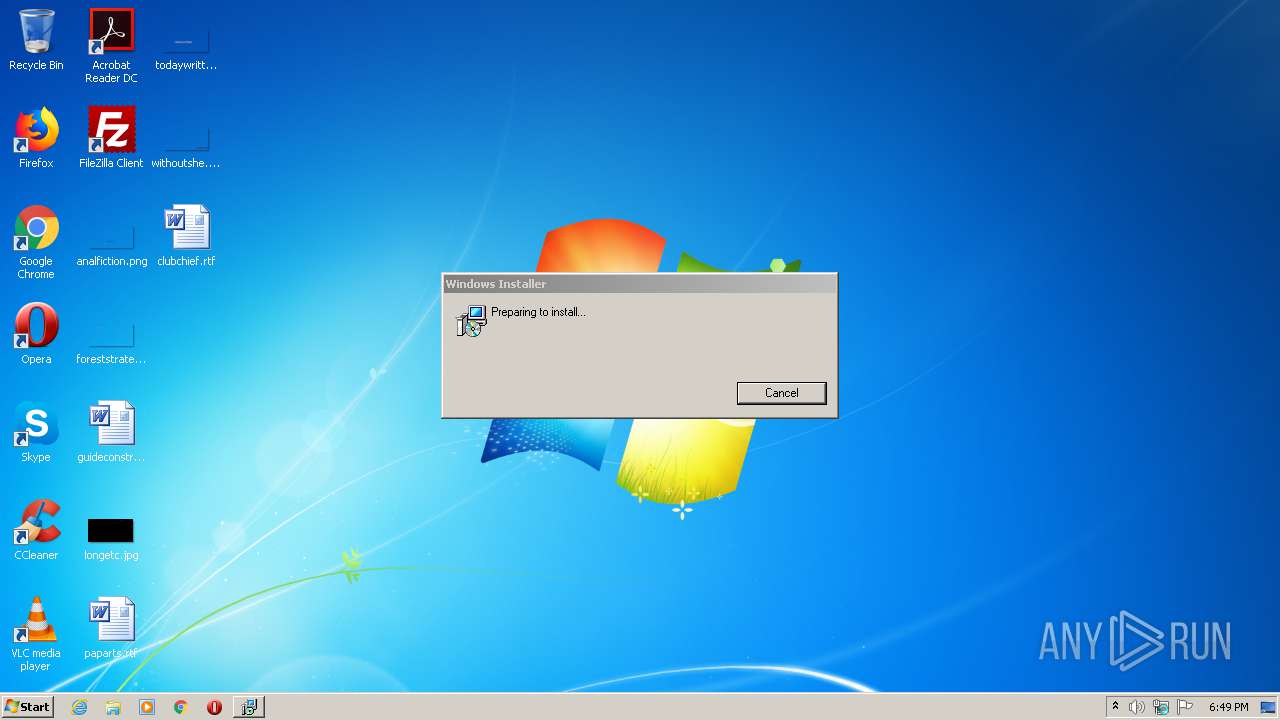
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2021, 17:49:24 |
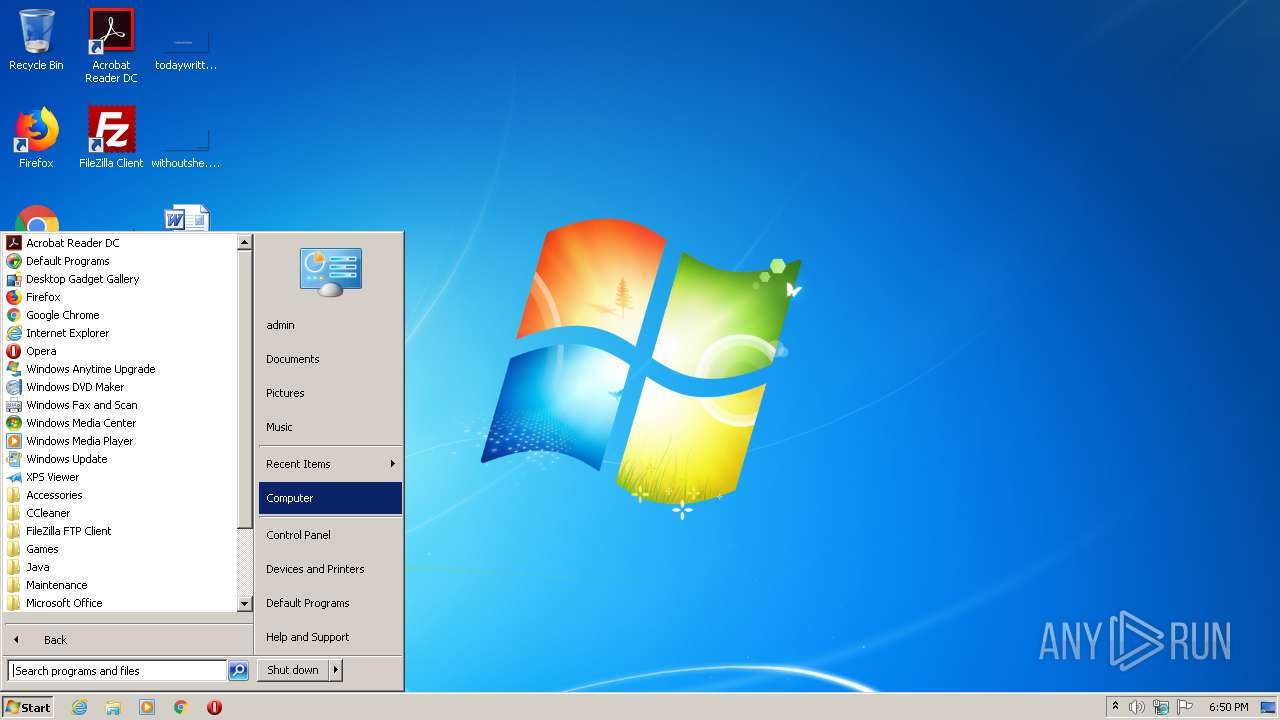
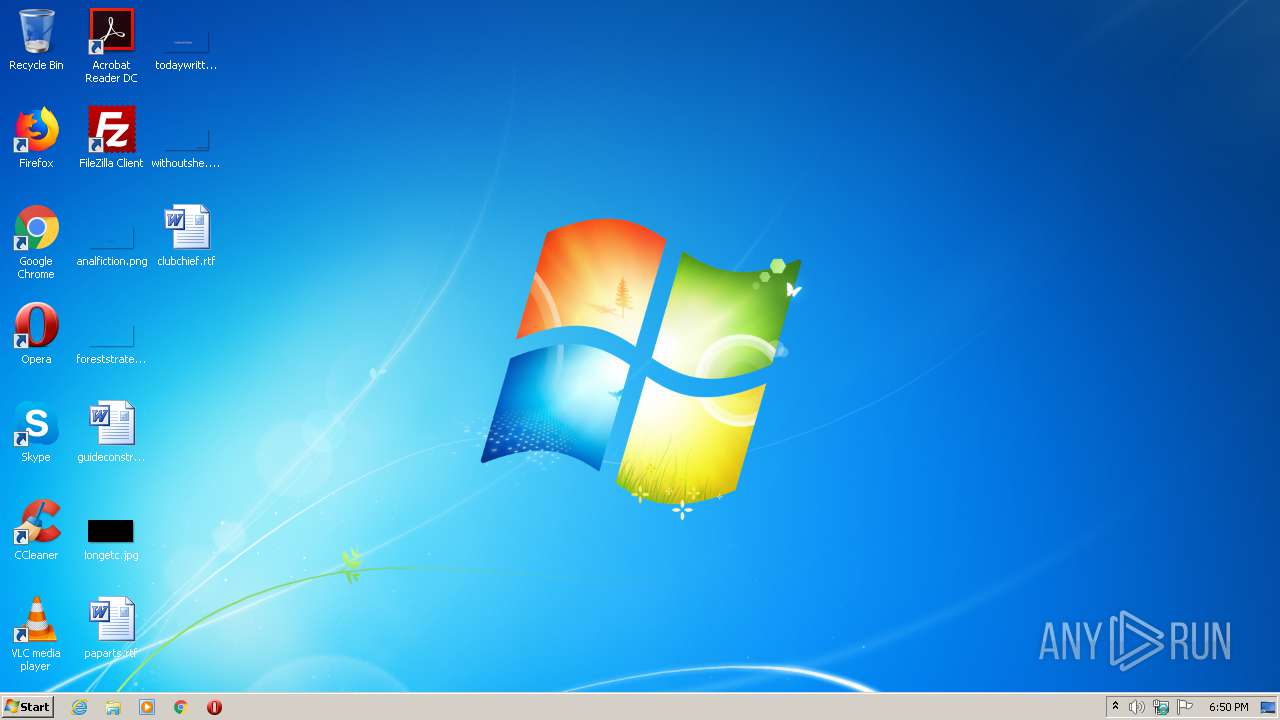
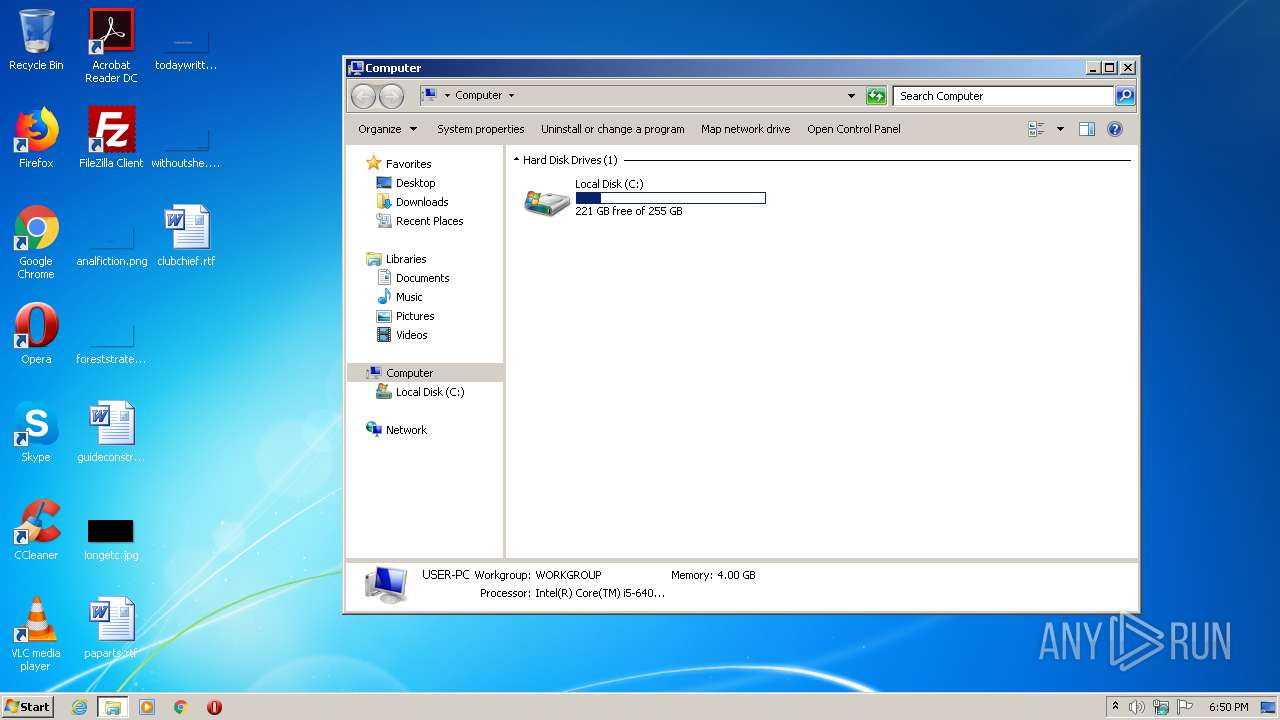
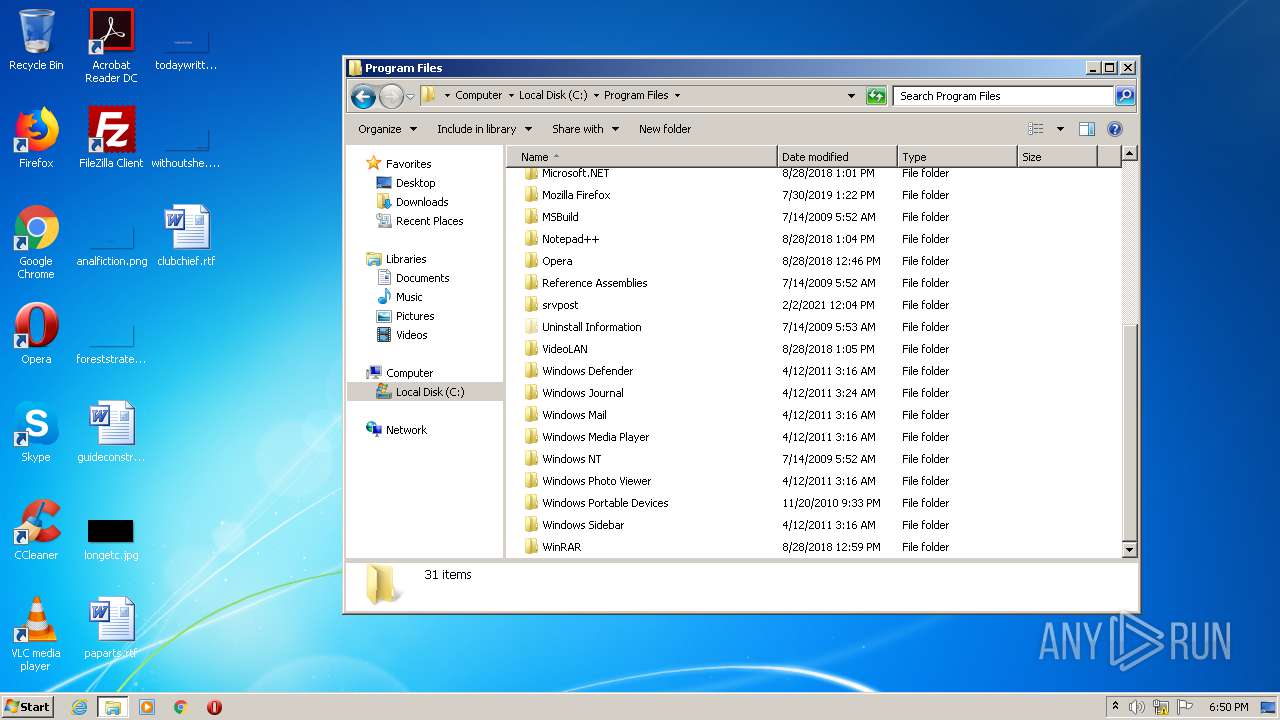
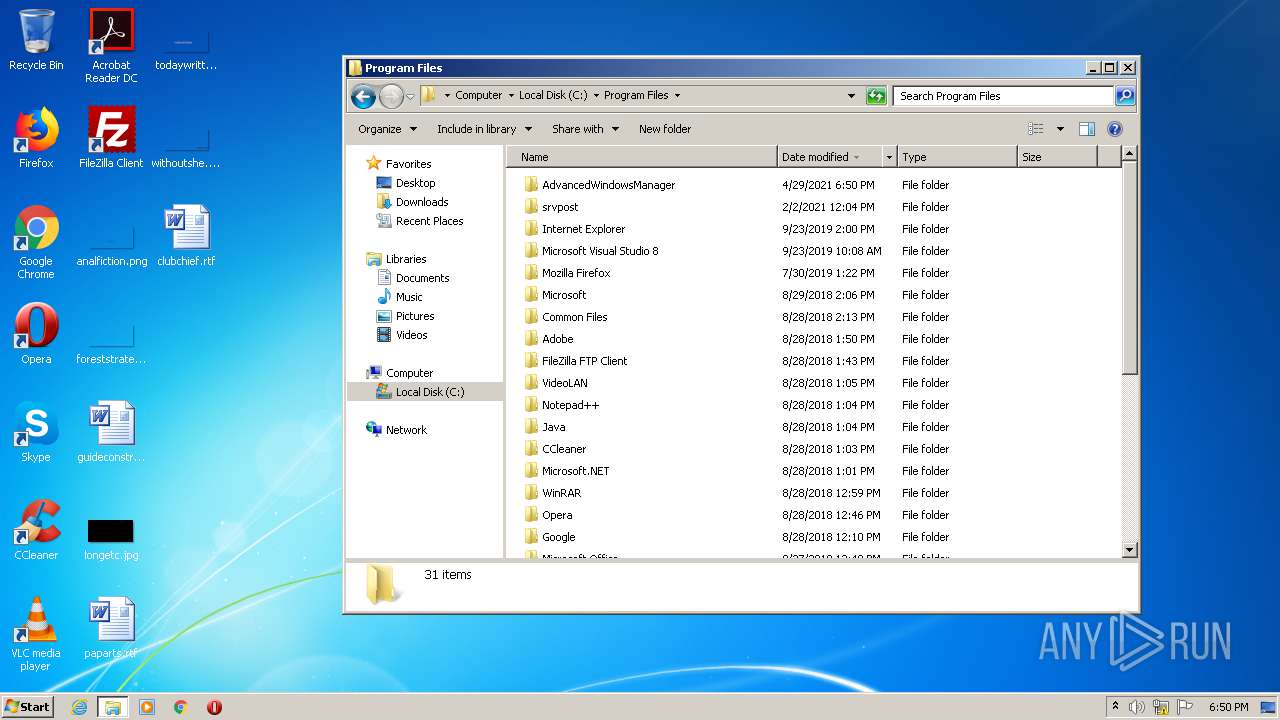
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 8CAD036C5CFED94D5319A060C488E38F |
| SHA1: | 731455086204F014C97EA3C1483DD6029961FF27 |
| SHA256: | 62F773773392C101F673A8D3DB805D5AA3A45DBBB12E2B32BC746470AC520B0F |
| SSDEEP: | 98304:KKC4/jxH8S506fsWCDIOX3LFiU+3xOfXLBnkGK+NXZi:L/jxH8SCixOPLBuG |
MALICIOUS
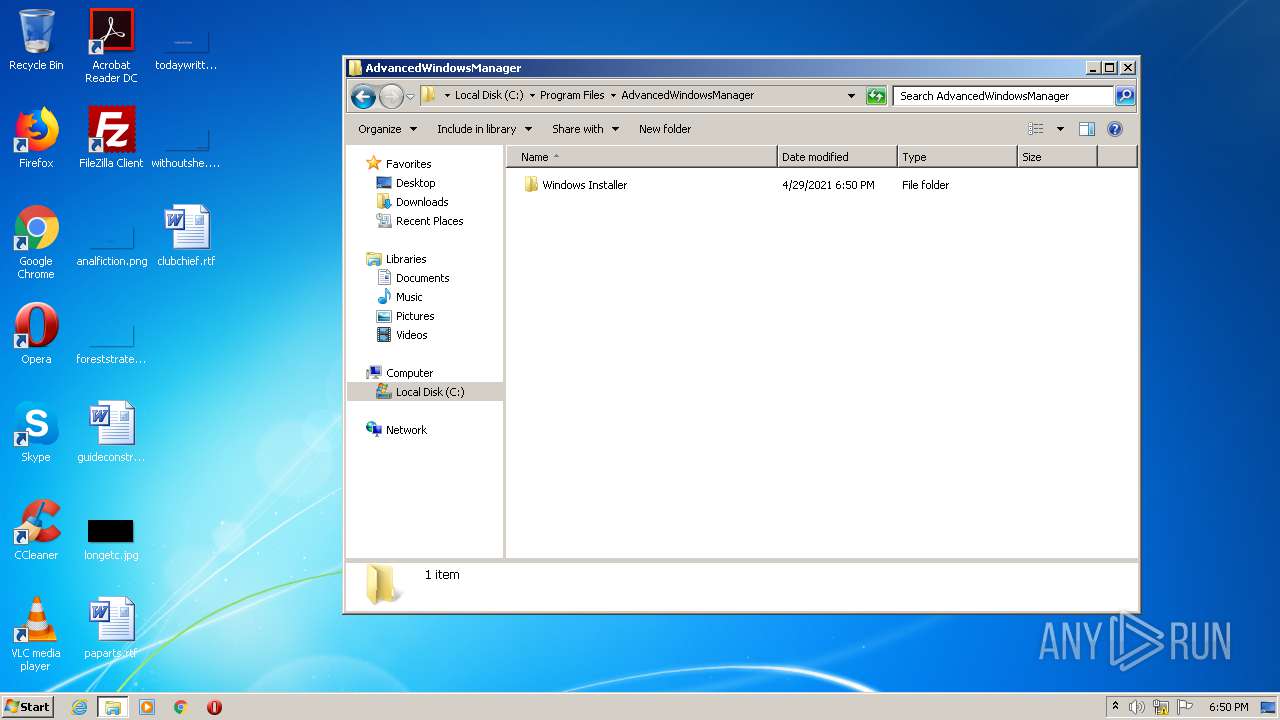
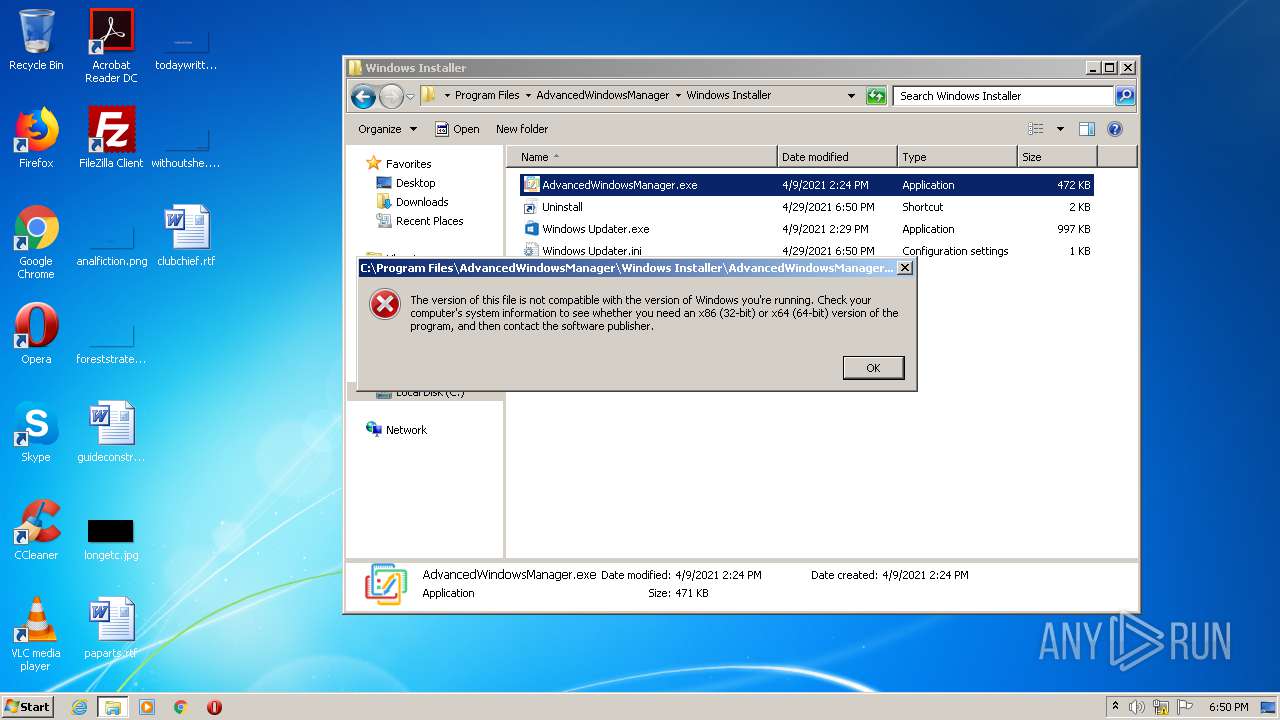
Drops executable file immediately after starts
- v113.exe (PID: 2472)
- MsiExec.exe (PID: 3760)
Changes settings of System certificates
- v113.exe (PID: 2472)
Loads dropped or rewritten executable
- v113.exe (PID: 2472)
Loads the Task Scheduler COM API
- MsiExec.exe (PID: 1472)
SUSPICIOUS
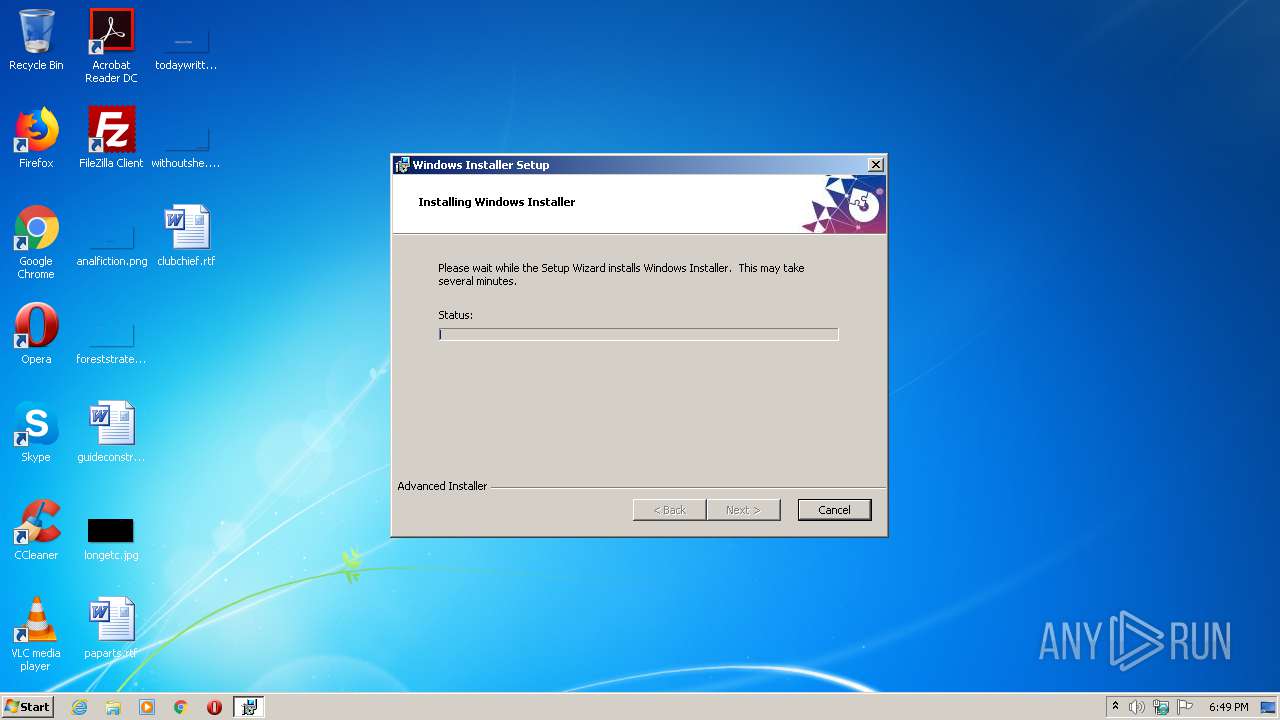
Executable content was dropped or overwritten
- v113.exe (PID: 2472)
- msiexec.exe (PID: 1108)
- MsiExec.exe (PID: 3760)
Adds / modifies Windows certificates
- v113.exe (PID: 2472)
Creates files in the user directory
- v113.exe (PID: 2472)
Drops a file that was compiled in debug mode
- v113.exe (PID: 2472)
- msiexec.exe (PID: 1108)
- MsiExec.exe (PID: 3760)
Reads Environment values
- MsiExec.exe (PID: 3920)
- v113.exe (PID: 2472)
- MsiExec.exe (PID: 2760)
- MsiExec.exe (PID: 3760)
- MsiExec.exe (PID: 2916)
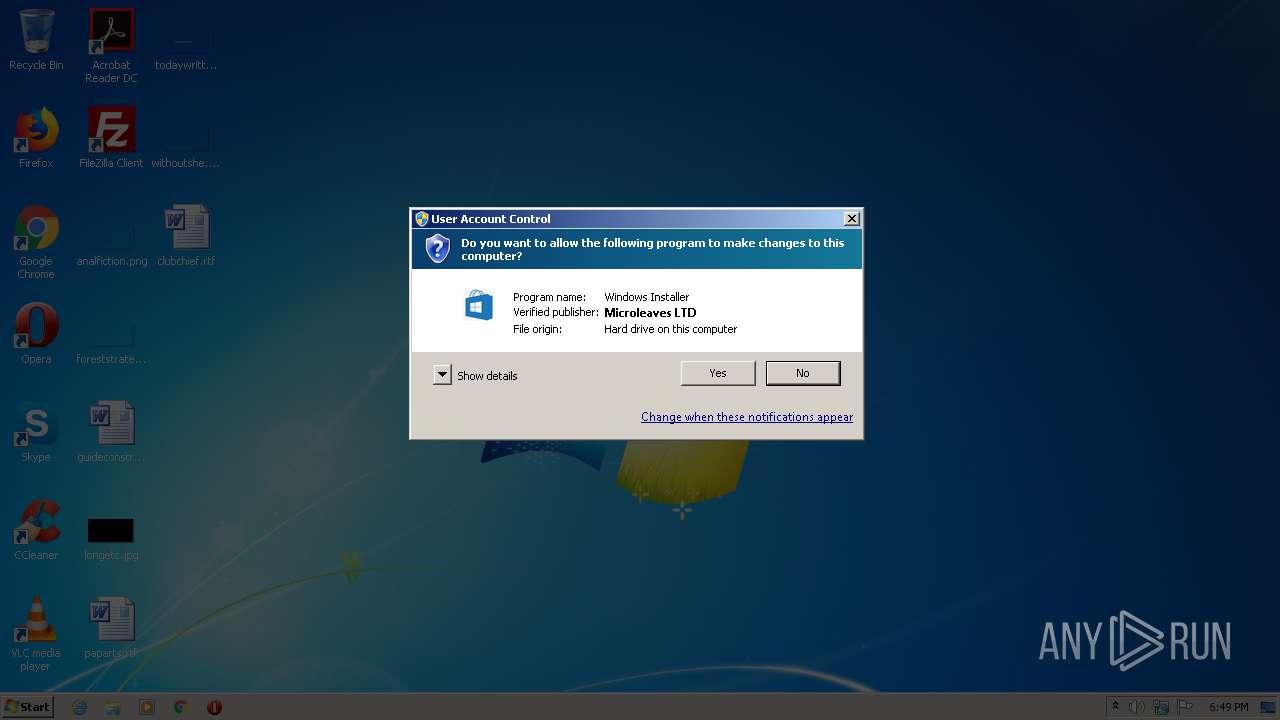
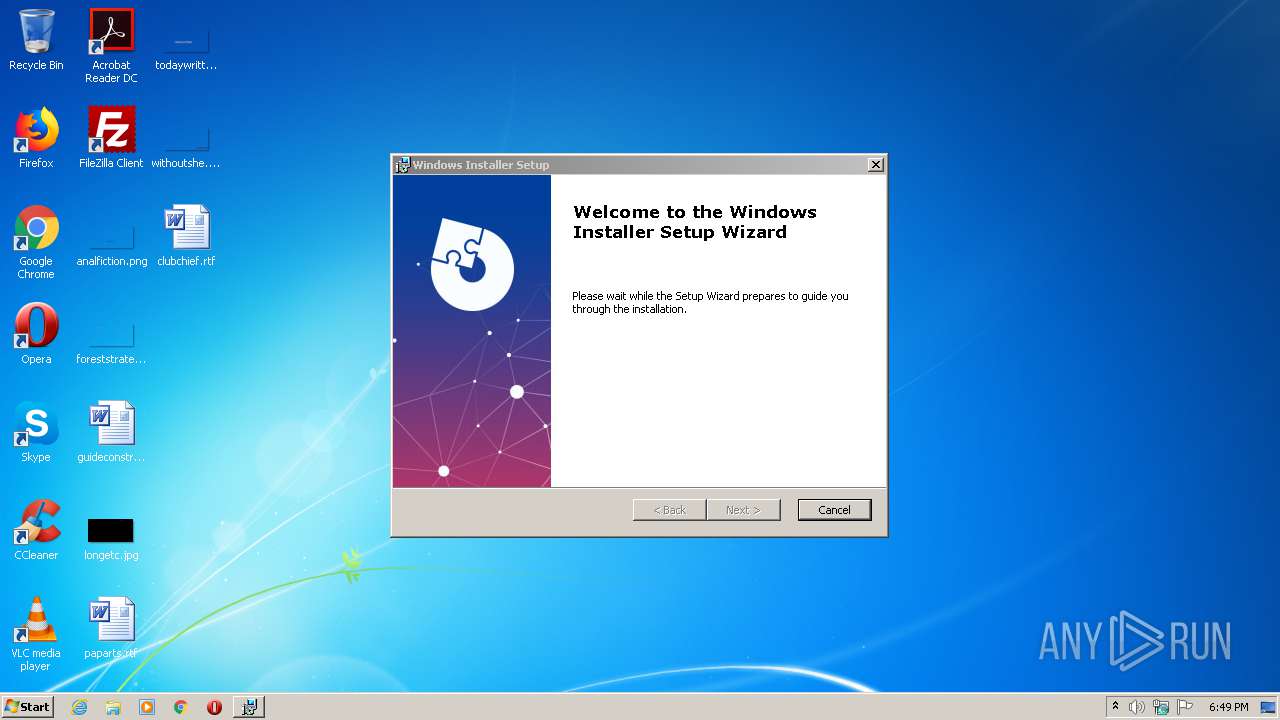
Starts Microsoft Installer
- v113.exe (PID: 2472)
Uses TASKKILL.EXE to kill process
- MsiExec.exe (PID: 2760)
Drops a file with a compile date too recent
- v113.exe (PID: 2472)
INFO
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2760)
- MsiExec.exe (PID: 2916)
- MsiExec.exe (PID: 3920)
- MsiExec.exe (PID: 3760)
- MsiExec.exe (PID: 1472)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
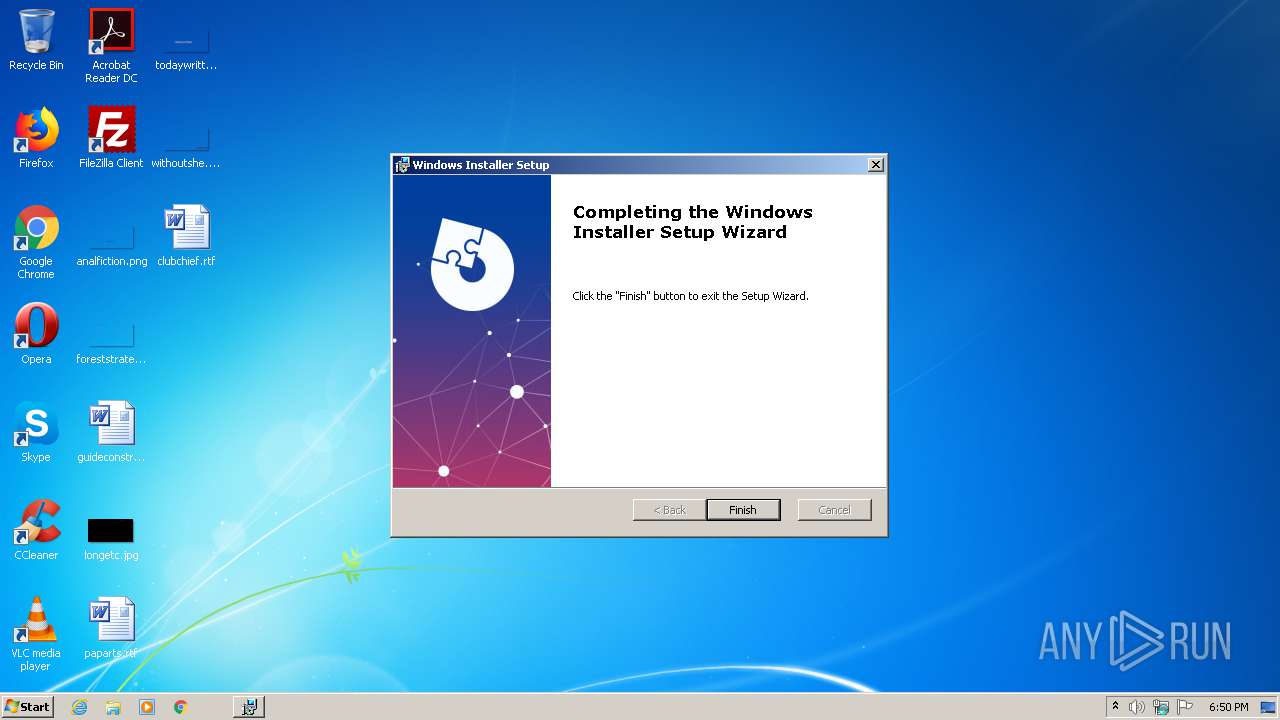
| ProductVersion: | 5.0.3 |
|---|---|
| ProductName: | Windows Installer |
| OriginalFileName: | Installer.exe |
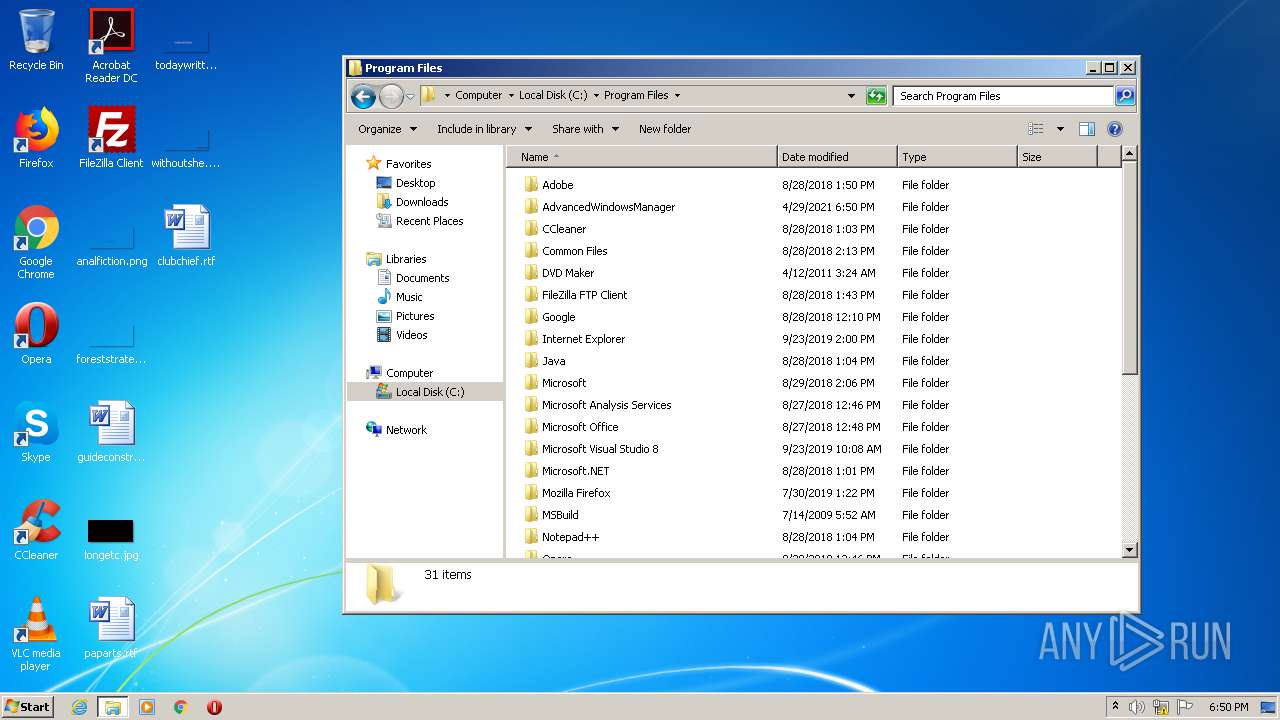
| LegalCopyright: | Copyright (C) 2021 AdvancedWindowsManager |
| InternalName: | Installer |
| FileVersion: | 5.0.3 |
| FileDescription: | Windows Installer Installer |
| CompanyName: | AdvancedWindowsManager |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Dynamic link library |
| FileOS: | Win32 |
| FileFlags: | Debug |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 5.0.3.0 |
| FileVersionNumber: | 5.0.3.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 6 |
| EntryPoint: | 0x122d48 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 606720 |
| CodeSize: | 1534976 |
| LinkerVersion: | 14.28 |
| PEType: | PE32 |
| TimeStamp: | 2021:03:25 14:08:12+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
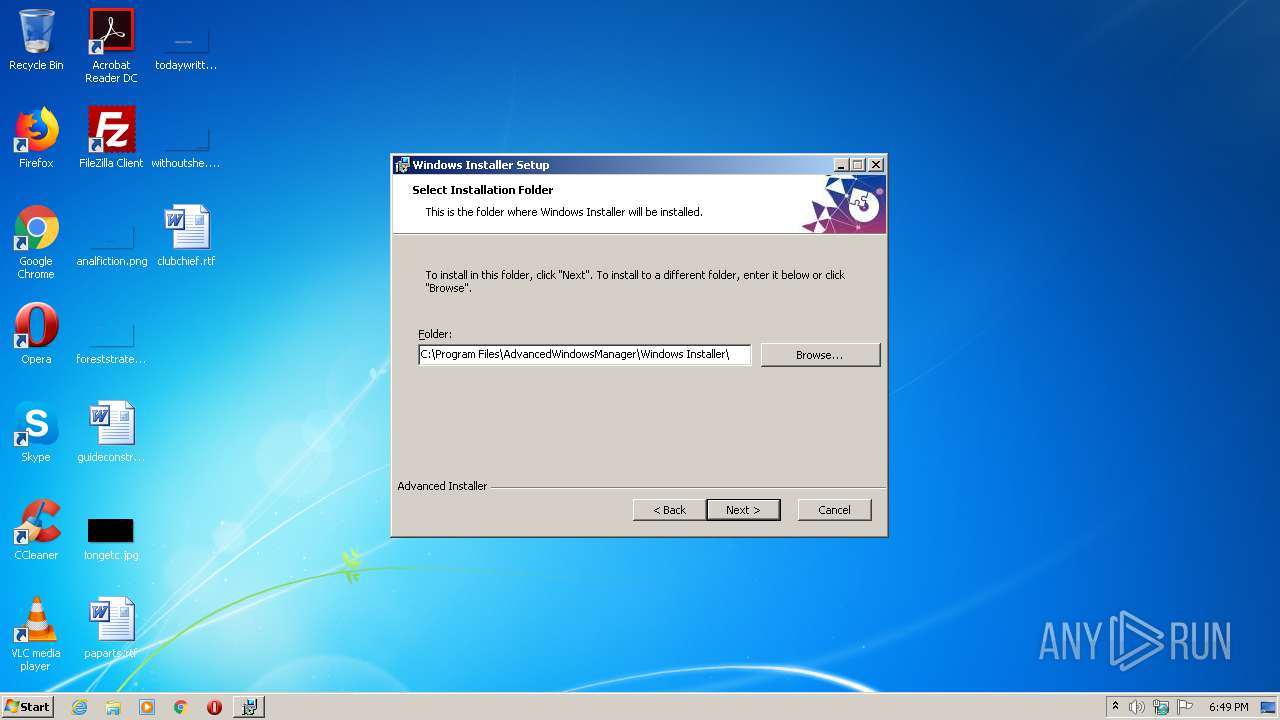
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Mar-2021 13:08:12 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | AdvancedWindowsManager |
| FileDescription: | Windows Installer Installer |
| FileVersion: | 5.0.3 |
| InternalName: | Installer |
| LegalCopyright: | Copyright (C) 2021 AdvancedWindowsManager |
| OriginalFileName: | Installer.exe |
| ProductName: | Windows Installer |
| ProductVersion: | 5.0.3 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 25-Mar-2021 13:08:12 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00176A3F | 0x00176C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.44961 |
.rdata | 0x00178000 | 0x0005DC38 | 0x0005DE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.58326 |
.data | 0x001D6000 | 0x00006E40 | 0x00005400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.06132 |
.rsrc | 0x001DD000 | 0x00017BD8 | 0x00017C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.12876 |
.reloc | 0x001F5000 | 0x00019318 | 0x00019400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.56758 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.18998 | 1909 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 5.28192 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 5.20644 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 4.9716 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 7.96422 | 26415 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 3.37783 | 1116 | Latin 1 / Western European | English - United States | RT_STRING |
10 | 3.34881 | 836 | Latin 1 / Western European | English - United States | RT_STRING |
11 | 3.31743 | 760 | Latin 1 / Western European | English - United States | RT_STRING |
12 | 3.23118 | 1432 | Latin 1 / Western European | English - United States | RT_STRING |
13 | 3.38539 | 938 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
KERNEL32.dll |
msi.dll (delay-loaded) |
Total processes
55
Monitored processes
8
Malicious processes
1
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1108 | "C:\Windows\system32\msiexec.exe" /i "C:\Users\admin\AppData\Roaming\AdvancedWindowsManager\Windows Installer 5.0.3\install\7EB1504\System Updater.msi" AI_SETUPEXEPATH=C:\Users\admin\AppData\Local\Temp\v113.exe SETUPEXEDIR=C:\Users\admin\AppData\Local\Temp\ EXE_CMD_LINE="/exenoupdates /forcecleanup /wintime 1619717211 " | C:\Windows\system32\msiexec.exe | v113.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1472 | C:\Windows\system32\MsiExec.exe -Embedding FB0058AA6AF333298D5231F5CE5F81E4 M Global\MSI0000 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2472 | "C:\Users\admin\AppData\Local\Temp\v113.exe" | C:\Users\admin\AppData\Local\Temp\v113.exe | explorer.exe | ||||||||||||
User: admin Company: AdvancedWindowsManager Integrity Level: HIGH Description: Windows Installer Installer Exit code: 0 Version: 5.0.3 Modules
| |||||||||||||||
| 2612 | "C:\Users\admin\AppData\Local\Temp\v113.exe" | C:\Users\admin\AppData\Local\Temp\v113.exe | — | explorer.exe | |||||||||||
User: admin Company: AdvancedWindowsManager Integrity Level: MEDIUM Description: Windows Installer Installer Exit code: 3221226540 Version: 5.0.3 Modules
| |||||||||||||||
| 2760 | C:\Windows\system32\MsiExec.exe -Embedding DDB6B749817B33C2B1B25CFD6EBA3185 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2916 | C:\Windows\system32\MsiExec.exe -Embedding D9ADDB3CF392C74F0EC91581D4019692 C | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3760 | C:\Windows\system32\MsiExec.exe -Embedding 5EDC8557745EC1D0238386DE340E9F02 U | C:\Windows\system32\MsiExec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3920 | C:\Windows\system32\MsiExec.exe -Embedding A72EFC27A07D2481E97653C1F117C0C4 C | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
520
Read events
470
Write events
50
Delete events
0
Modification events
| (PID) Process: | (2472) v113.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2472) v113.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\0563B8630D62D75ABBC8AB1E4BDFB5A899B24D43 |
| Operation: | write | Name: | Blob |
Value: 04000000010000001000000087CE0B7B2A0E4900E158719B37A893720F00000001000000140000006DCA5BD00DCF1C0F327059D374B29CA6E3C50AA60300000001000000140000000563B8630D62D75ABBC8AB1E4BDFB5A899B24D431D00000001000000100000004F5F106930398D09107B40C3C7CA8F1C0B000000010000001200000044006900670069004300650072007400000014000000010000001400000045EBA2AFF492CB82312D518BA7A7219DF36DC80F6200000001000000200000003E9099B5015E8F486C00BCEA9D111EE721FABA355A89BCF1DF69561E3DC6325C5300000001000000230000003021301F06096086480186FD6C020130123010060A2B0601040182373C0101030200C0090000000100000034000000303206082B0601050507030106082B0601050507030206082B0601050507030406082B0601050507030306082B06010505070308190000000100000010000000749966CECC95C1874194CA7203F9B6202000000001000000BB030000308203B73082029FA00302010202100CE7E0E517D846FE8FE560FC1BF03039300D06092A864886F70D01010505003065310B300906035504061302555331153013060355040A130C446967694365727420496E6331193017060355040B13107777772E64696769636572742E636F6D312430220603550403131B4469676943657274204173737572656420494420526F6F74204341301E170D3036313131303030303030305A170D3331313131303030303030305A3065310B300906035504061302555331153013060355040A130C446967694365727420496E6331193017060355040B13107777772E64696769636572742E636F6D312430220603550403131B4469676943657274204173737572656420494420526F6F7420434130820122300D06092A864886F70D01010105000382010F003082010A0282010100AD0E15CEE443805CB187F3B760F97112A5AEDC269488AAF4CEF520392858600CF880DAA9159532613CB5B128848A8ADC9F0A0C83177A8F90AC8AE779535C31842AF60F98323676CCDEDD3CA8A2EF6AFB21F25261DF9F20D71FE2B1D9FE1864D2125B5FF9581835BC47CDA136F96B7FD4B0383EC11BC38C33D9D82F18FE280FB3A783D6C36E44C061359616FE599C8B766DD7F1A24B0D2BFF0B72DA9E60D08E9035C678558720A1CFE56D0AC8497C3198336C22E987D0325AA2BA138211ED39179D993A72A1E6FAA4D9D5173175AE857D22AE3F014686F62879C8B1DAE45717C47E1C0EB0B492A656B3BDB297EDAAA7F0B7C5A83F9516D0FFA196EB085F18774F0203010001A3633061300E0603551D0F0101FF040403020186300F0603551D130101FF040530030101FF301D0603551D0E0416041445EBA2AFF492CB82312D518BA7A7219DF36DC80F301F0603551D2304183016801445EBA2AFF492CB82312D518BA7A7219DF36DC80F300D06092A864886F70D01010505000382010100A20EBCDFE2EDF0E372737A6494BFF77266D832E4427562AE87EBF2D5D9DE56B39FCCCE1428B90D97605C124C58E4D33D834945589735691AA847EA56C679AB12D8678184DF7F093C94E6B8262C20BD3DB32889F75FFF22E297841FE965EF87E0DFC16749B35DEBB2092AEB26ED78BE7D3F2BF3B726356D5F8901B6495B9F01059BAB3D25C1CCB67FC2F16F86C6FA6468EB812D94EB42B7FA8C1EDD62F1BE5067B76CBDF3F11F6B0C3607167F377CA95B6D7AF112466083D72704BE4BCE97BEC3672A6811DF80E70C3366BF130D146EF37F1F63101EFA8D1B256D6C8FA5B76101B1D2A326A110719DADE2C3F9C39951B72B0708CE2EE650B2A7FA0A452FA2F0F2 | |||
| (PID) Process: | (2472) v113.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\5FB7EE0633E259DBAD0C4C9AE6D38F1A61C7DC25 |
| Operation: | write | Name: | Blob |
Value: 040000000100000010000000D474DE575C39B2D39C8583C5C065498A0F0000000100000014000000E35EF08D884F0A0ADE2F75E96301CE6230F213A80300000001000000140000005FB7EE0633E259DBAD0C4C9AE6D38F1A61C7DC251D00000001000000100000008F76B981D528AD4770088245E2031B630B0000000100000012000000440069006700690043006500720074000000140000000100000014000000B13EC36903F8BF4701D498261A0802EF63642BC36200000001000000200000007431E5F4C3C1CE4690774F0B61E05440883BA9A01ED00BA6ABD7806ED3B118CF5300000001000000230000003021301F06096086480186FD6C020130123010060A2B0601040182373C0101030200C0090000000100000034000000303206082B0601050507030106082B0601050507030206082B0601050507030406082B0601050507030306082B06010505070308190000000100000010000000BA4F3972E7AED9DCCDC210DB59DA13C92000000001000000C9030000308203C5308202ADA003020102021002AC5C266A0B409B8F0B79F2AE462577300D06092A864886F70D0101050500306C310B300906035504061302555331153013060355040A130C446967694365727420496E6331193017060355040B13107777772E64696769636572742E636F6D312B30290603550403132244696769436572742048696768204173737572616E636520455620526F6F74204341301E170D3036313131303030303030305A170D3331313131303030303030305A306C310B300906035504061302555331153013060355040A130C446967694365727420496E6331193017060355040B13107777772E64696769636572742E636F6D312B30290603550403132244696769436572742048696768204173737572616E636520455620526F6F7420434130820122300D06092A864886F70D01010105000382010F003082010A0282010100C6CCE573E6FBD4BBE52D2D32A6DFE5813FC9CD2549B6712AC3D5943467A20A1CB05F69A640B1C4B7B28FD098A4A941593AD3DC94D63CDB7438A44ACC4D2582F74AA5531238EEF3496D71917E63B6ABA65FC3A484F84F6251BEF8C5ECDB3892E306E508910CC4284155FBCB5A89157E71E835BF4D72093DBE3A38505B77311B8DB3C724459AA7AC6D00145A04B7BA13EB510A984141224E656187814150A6795C89DE194A57D52EE65D1C532C7E98CD1A0616A46873D03404135CA171D35A7C55DB5E64E13787305604E511B4298012F1793988A202117C2766B788B778F2CA0AA838AB0A64C2BF665D9584C1A1251E875D1A500B2012CC41BB6E0B5138B84BCB0203010001A3633061300E0603551D0F0101FF040403020186300F0603551D130101FF040530030101FF301D0603551D0E04160414B13EC36903F8BF4701D498261A0802EF63642BC3301F0603551D23041830168014B13EC36903F8BF4701D498261A0802EF63642BC3300D06092A864886F70D010105050003820101001C1A0697DCD79C9F3C886606085721DB2147F82A67AABF183276401057C18AF37AD911658E35FA9EFC45B59ED94C314BB891E8432C8EB378CEDBE3537971D6E5219401DA55879A2464F68A66CCDE9C37CDA834B1699B23C89E78222B7043E35547316119EF58C5852F4E30F6A0311623C8E7E2651633CBBF1A1BA03DF8CA5E8B318B6008892D0C065C52B7C4F90A98D1155F9F12BE7C366338BD44A47FE4262B0AC497690DE98CE2C01057B8C876129155F24869D8BC2A025B0F44D42031DBF4BA70265D90609EBC4B17092FB4CB1E4368C90727C1D25CF7EA21B968129C3C9CBF9EFC805C9B63CDEC47AA252767A037F300827D54D7A9F8E92E13A377E81F4A | |||
| (PID) Process: | (1108) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2760) MsiExec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2760) MsiExec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1472) MsiExec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Caphyon\Advanced Installer\Scheduled Tasks\{FDBC5875-BBA4-4DA5-9048-A196A21FE49A} |
| Operation: | write | Name: | NewTask |
Value: 1 | |||
| (PID) Process: | (1472) MsiExec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Caphyon\Advanced Installer\Scheduled Tasks\{FDBC5875-BBA4-4DA5-9048-A196A21FE49A} |
| Operation: | write | Name: | NewTask_ID |
Value: AdvancedWindowsManager #1 | |||
| (PID) Process: | (1472) MsiExec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Caphyon\Advanced Installer\Scheduled Tasks\{FDBC5875-BBA4-4DA5-9048-A196A21FE49A} |
| Operation: | write | Name: | AdvancedWindowsManager12 |
Value: 1 | |||
| (PID) Process: | (1472) MsiExec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Caphyon\Advanced Installer\Scheduled Tasks\{FDBC5875-BBA4-4DA5-9048-A196A21FE49A} |
| Operation: | write | Name: | AdvancedWindowsManager12_ID |
Value: AdvancedWindowsManager #3 | |||
Executable files
10
Suspicious files
0
Text files
67
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1108 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI1DC3.tmp | — | |
MD5:— | SHA256:— | |||
| 1108 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI1E9E.tmp | — | |
MD5:— | SHA256:— | |||
| 1108 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI1EBF.tmp | — | |
MD5:— | SHA256:— | |||
| 1108 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI1EFE.tmp | — | |
MD5:— | SHA256:— | |||
| 1108 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI2067.tmp | — | |
MD5:— | SHA256:— | |||
| 1108 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI20B7.tmp | — | |
MD5:— | SHA256:— | |||
| 1108 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI7174\embeddeduiproxy.dll | executable | |
MD5:— | SHA256:— | |||
| 2472 | v113.exe | C:\Users\admin\AppData\Local\AdvinstAnalytics\57adf5f3482b9a503e2bed2b\5.0.3\{63B54F37-1F55-4ADC-81C7-313C4032CE90}.session | text | |
MD5:— | SHA256:— | |||
| 2472 | v113.exe | C:\Users\admin\AppData\Local\AdvinstAnalytics\57adf5f3482b9a503e2bed2b\5.0.3\tracking.ini | text | |
MD5:— | SHA256:— | |||
| 2472 | v113.exe | C:\Users\admin\AppData\Roaming\AdvancedWindowsManager\Windows Installer 5.0.3\install\7EB1504\System Updater.msi | executable | |
MD5:9FC8CC919F8719F753EFF0EBD661523D | SHA256:4B31415F1494ED54BA885B005340ADBBA2E13848836368ACFCEF5E46B888D9AC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3760 | MsiExec.exe | 52.23.109.145:443 | collect.installeranalytics.com | Amazon.com, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
collect.installeranalytics.com |
| malicious |