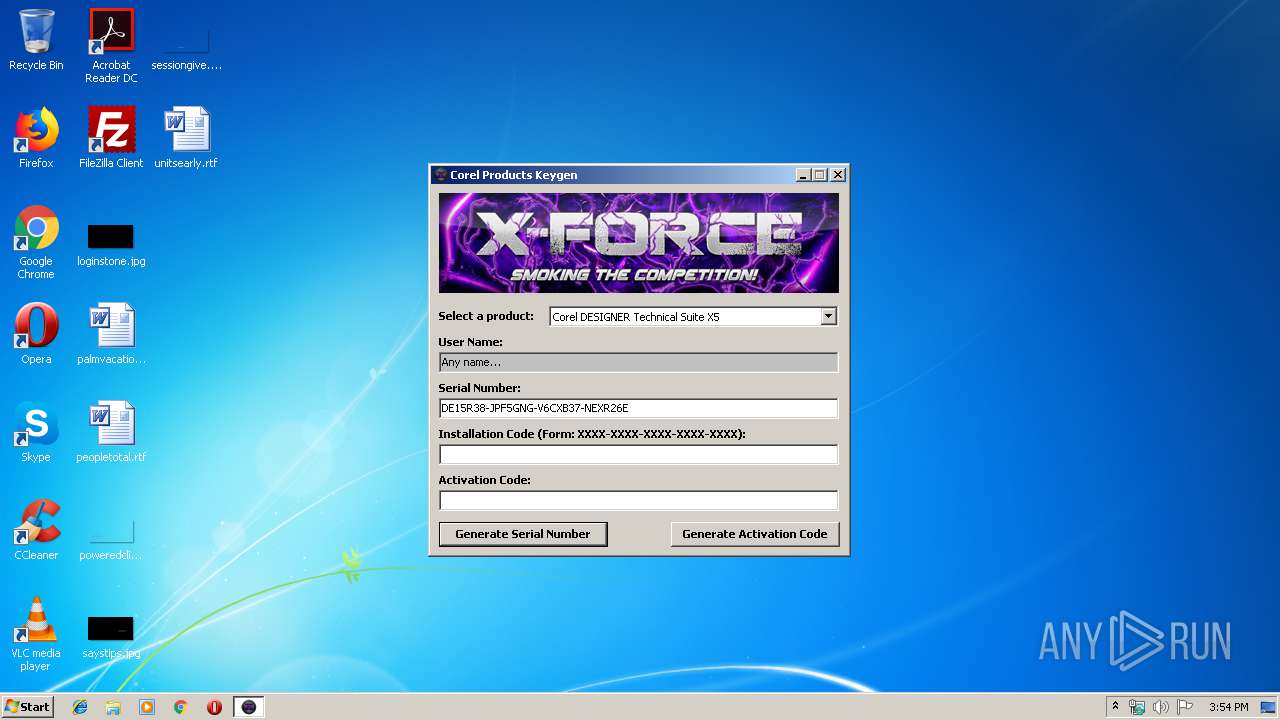
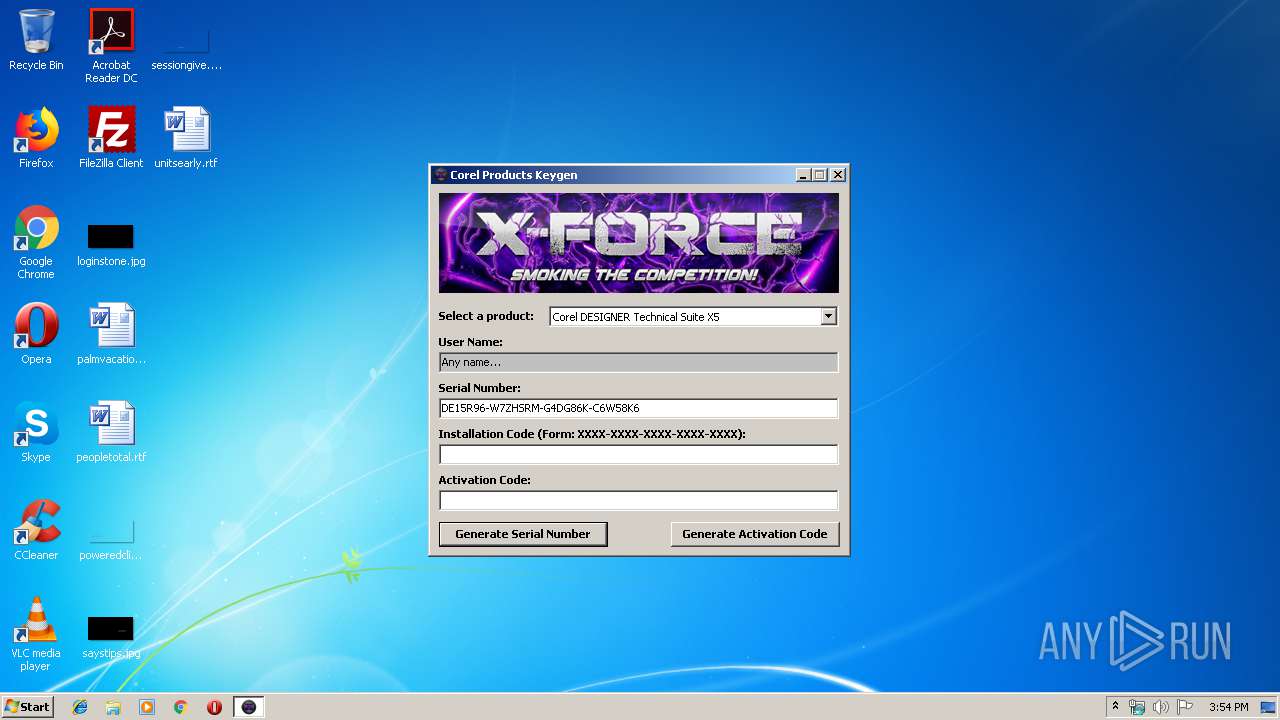
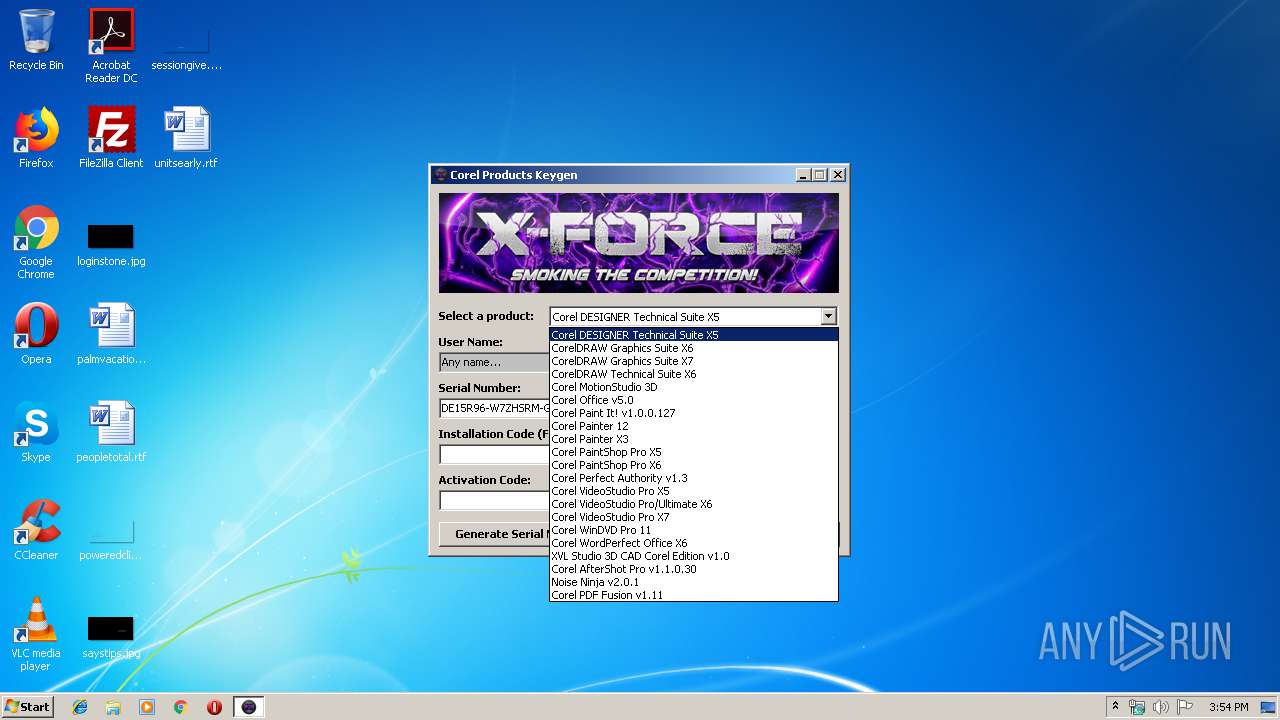
| File name: | Keygen.exe |
| Full analysis: | https://app.any.run/tasks/a71f6e2a-2deb-4c22-94a8-3251f9e85cf9 |
| Verdict: | Suspicious activity |
| Analysis date: | October 28, 2019, 15:53:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | E1CBC1FC15774DD100446BA16C76C18D |
| SHA1: | F1CED96D5BD0122232B5ACE268B74AE4814FED5B |
| SHA256: | 62D88B1966534371641B7C0126FC756CFCC553B1CC7714CD8D8D15B8C9ACB7FC |
| SSDEEP: | 24576:36OhA8FTgOsThObO5C4se0b+AwYb0qEFlrmKymlitott1GwWfS97S4fVv:KOhBhgdhbJoPwYQqEFhhySz4X0mA |
MALICIOUS
Application was dropped or rewritten from another process
- 0.exe (PID: 3584)
- 2.exe (PID: 3532)
- 1.exe (PID: 964)
- sppsvd.exe (PID: 2440)
- 0.exe (PID: 3008)
- smss.exe (PID: 1724)
Changes the autorun value in the registry
- reg.exe (PID: 1016)
SUSPICIOUS
Executable content was dropped or overwritten
- Keygen.exe (PID: 408)
- 1.exe (PID: 964)
- sppsvd.exe (PID: 2440)
Executes scripts
- 1.exe (PID: 964)
Starts CMD.EXE for commands execution
- WScript.exe (PID: 3140)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2660)
Creates files in the user directory
- smss.exe (PID: 1724)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 2660)
Reads internet explorer settings
- smss.exe (PID: 1724)
Reads Internet Cache Settings
- smss.exe (PID: 1724)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:12:05 23:50:52+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24064 |
| InitializedDataSize: | 164864 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x30fa |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Windows, Chinese (Simplified) |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 1.0.0.0 |
| LegalCopyright: | - |
| LegalTrademarks: | - |
| OriginalFileName: | Keygen.exe |
| ProductName: | Keygen |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Dec-2009 22:50:52 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | - |
| FileDescription: | - |
| FileVersion: | 1.0.0.0 |
| LegalCopyright: | - |
| LegalTrademarks: | 0 |
| OriginalFilename: | Keygen.exe |
| ProductName: | Keygen |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 05-Dec-2009 22:50:52 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005C4C | 0x00005E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.44011 |
.rdata | 0x00007000 | 0x0000129C | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.04684 |
.data | 0x00009000 | 0x00025C58 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.801 |
.ndata | 0x0002F000 | 0x00009000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00038000 | 0x00006730 | 0x00006800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.66494 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.10394 | 533 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 6.26612 | 4264 | UNKNOWN | English - United States | RT_ICON |
3 | 5.9993 | 3752 | UNKNOWN | English - United States | RT_ICON |
4 | 6.24459 | 2216 | UNKNOWN | English - United States | RT_ICON |
5 | 5.01502 | 1384 | UNKNOWN | English - United States | RT_ICON |
6 | 6.16057 | 1128 | UNKNOWN | English - United States | RT_ICON |
7 | 3.34146 | 744 | UNKNOWN | English - United States | RT_ICON |
8 | 3.04232 | 296 | UNKNOWN | English - United States | RT_ICON |
103 | 2.69402 | 118 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.68733 | 494 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
53
Monitored processes
15
Malicious processes
5
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 408 | "C:\Users\admin\AppData\Local\Temp\Keygen.exe" | C:\Users\admin\AppData\Local\Temp\Keygen.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 912 | taskkill /F /im 0.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 964 | "C:\Users\admin\AppData\Local\Temp\RarSFX1\1.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX1\1.exe | 0.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1016 | reg add "HKCU\Software\Microsoft\Windows\CurrentVersion\Run" /v exexc10 /t REG_SZ /d "C:\Users\admin\AppData\Local\Temp\RarSFX0\a\sppsvd.exe | C:\Windows\system32\reg.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1724 | "C:\Users\admin\AppData\Local\Temp\RarSFX2\smss.exe" | C:\Users\admin\AppData\Local\Temp\RarSFX2\smss.exe | sppsvd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Software Protection Platform Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2184 | "C:\Users\admin\AppData\Local\Temp\Keygen.exe" | C:\Users\admin\AppData\Local\Temp\Keygen.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2396 | ping -n 5 127.1 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2440 | "C:\Users\admin\AppData\Local\Temp\RarSFX0\a\sppsvd.exe" /start | C:\Users\admin\AppData\Local\Temp\RarSFX0\a\sppsvd.exe | WScript.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 2520 | taskkill /F /im sppsvd.exe | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2660 | cmd /c ""C:\Users\admin\AppData\Local\Temp\RarSFX0\1.bat" /start" | C:\Windows\System32\cmd.exe | WScript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 984
Read events
1 945
Write events
38
Delete events
1
Modification events
| (PID) Process: | (3584) 0.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3584) 0.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (408) Keygen.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Session Manager |
| Operation: | write | Name: | PendingFileRenameOperations |
Value: \??\C:\Users\admin\AppData\Local\Temp\RarSFX1\1.exe | |||
| (PID) Process: | (964) 1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (964) 1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3140) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3140) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3360) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (1016) reg.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | exexc10 |
Value: C:\Users\admin\AppData\Local\Temp\RarSFX0\a\sppsvd.exe | |||
| (PID) Process: | (2440) sppsvd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
7
Suspicious files
0
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1724 | smss.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@google[1].txt | — | |
MD5:— | SHA256:— | |||
| 964 | 1.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\0.vbs | text | |
MD5:— | SHA256:— | |||
| 408 | Keygen.exe | C:\Users\admin\AppData\Local\Temp\RarSFX1\1.exe | executable | |
MD5:— | SHA256:— | |||
| 964 | 1.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\1.bat | text | |
MD5:— | SHA256:— | |||
| 964 | 1.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\a\sppsvd.exe | executable | |
MD5:— | SHA256:— | |||
| 2440 | sppsvd.exe | C:\Users\admin\AppData\Local\Temp\RarSFX2\smss.exe | executable | |
MD5:— | SHA256:— | |||
| 964 | 1.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\0.exe | executable | |
MD5:— | SHA256:— | |||
| 408 | Keygen.exe | C:\Users\admin\AppData\Local\Temp\RarSFX1\2.exe | executable | |
MD5:8B704100BF6AD468FDF883822C35A42B | SHA256:46C3F11D79A267D74FB91BC0CE3CB5B7F5B7DBF16D905294711253942318E6EF | |||
| 2440 | sppsvd.exe | C:\Users\admin\AppData\Local\Temp\RarSFX2\Interop.SHDocVw.dll | executable | |
MD5:38195FDCDC07791E8A99BABFA3A30AE4 | SHA256:CB40ABDD94EA2386CBD2304B40A45A99451C58BB83D9E2CCC159CACA9C3AFF28 | |||
| 1724 | smss.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@google[2].txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
7
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1724 | smss.exe | GET | 200 | 143.95.252.46:80 | http://kupeer.com/m51games/? | US | — | — | malicious |
1724 | smss.exe | GET | 200 | 143.95.252.46:80 | http://kupeer.com/advnew/tdvt5.txt | US | text | 116 b | malicious |
1724 | smss.exe | GET | 301 | 172.217.23.174:80 | http://google.com/ | US | html | 219 b | malicious |
1724 | smss.exe | GET | — | 172.217.23.174:80 | http://google.com/ | US | — | — | malicious |
1724 | smss.exe | GET | 302 | 172.217.22.4:80 | http://www.google.com/ | US | html | 231 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1724 | smss.exe | 143.95.252.46:80 | kupeer.com | Colo4, LLC | US | malicious |
1724 | smss.exe | 172.217.23.174:80 | google.com | Google Inc. | US | whitelisted |
— | — | 143.95.252.46:80 | kupeer.com | Colo4, LLC | US | malicious |
— | — | 172.217.23.174:80 | google.com | Google Inc. | US | whitelisted |
— | — | 172.217.22.4:80 | www.google.com | Google Inc. | US | whitelisted |
1724 | smss.exe | 172.217.22.4:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
kupeer.com |
| malicious |
dns.msftncsi.com |
| shared |
google.com |
| malicious |
www.google.com |
| malicious |
Threats
Process | Message |
|---|---|
cmd.exe | Invalid parameter passed to C runtime function.
|