| File name: | launcher.exe |
| Full analysis: | https://app.any.run/tasks/dd5c6f91-73b7-4f33-851c-cf93236a20ce |
| Verdict: | Malicious activity |
| Analysis date: | November 14, 2023, 06:47:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | B51C8E2023188114A3AFB85DF73B886F |
| SHA1: | 1BC44F4A748FE2611A00004CA55F2567FA0890F8 |
| SHA256: | 62D183E9BFA8EEDFCB7F2AD75C419F38088E8A600DDE6286F122BD7B567144F5 |
| SSDEEP: | 3072:QyKWt7In6VPxqGqS+xqGqS+xqGqS+xqGqS/AP9xqGqS65H:1M6BxqGqfxqGqfxqGqfxqGqqOxqGqx |
MALICIOUS
No malicious indicators.SUSPICIOUS
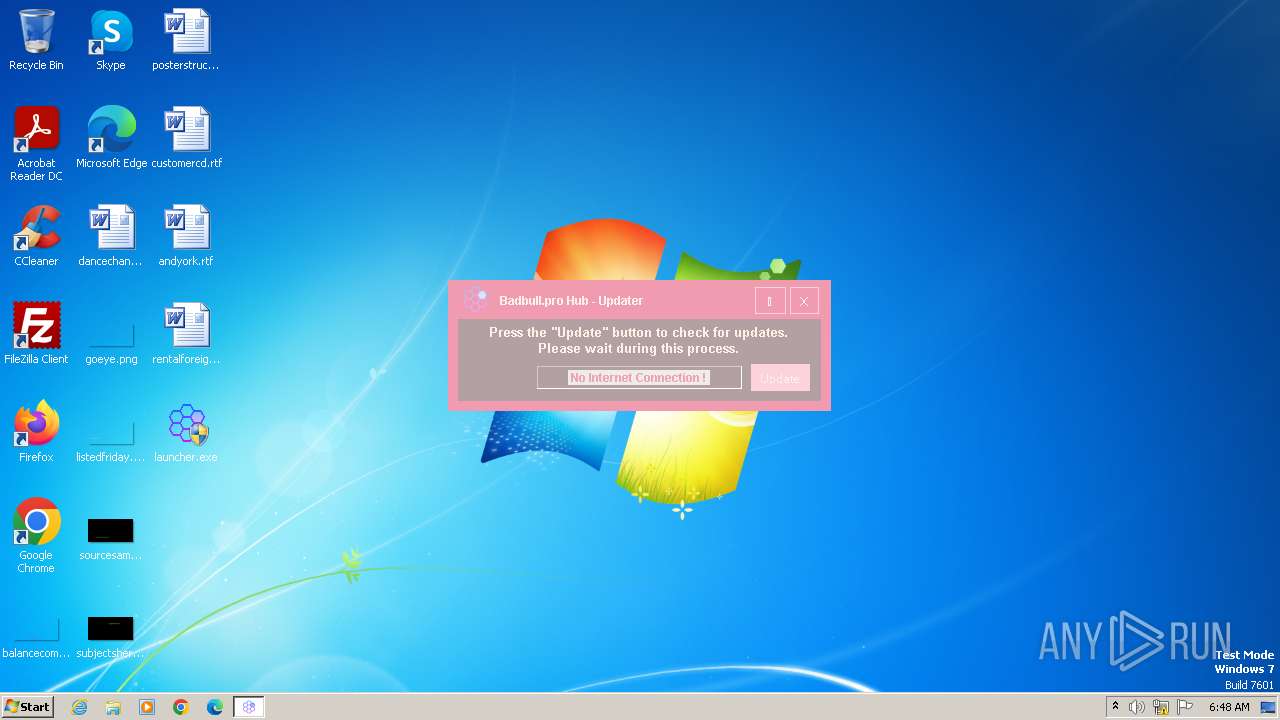
Reads the Internet Settings
- launcher.exe (PID: 3724)
- launcher.exe (PID: 2900)
Powershell version downgrade attack
- powershell.exe (PID: 4084)
- powershell.exe (PID: 3596)
Reads settings of System Certificates
- launcher.exe (PID: 3724)
- launcher.exe (PID: 2900)
Starts POWERSHELL.EXE for commands execution
- launcher.exe (PID: 3724)
- launcher.exe (PID: 2900)
INFO
Checks supported languages
- launcher.exe (PID: 2900)
- launcher.exe (PID: 3724)
Reads the computer name
- launcher.exe (PID: 2900)
- launcher.exe (PID: 3724)
Reads Environment values
- launcher.exe (PID: 2900)
- launcher.exe (PID: 3724)
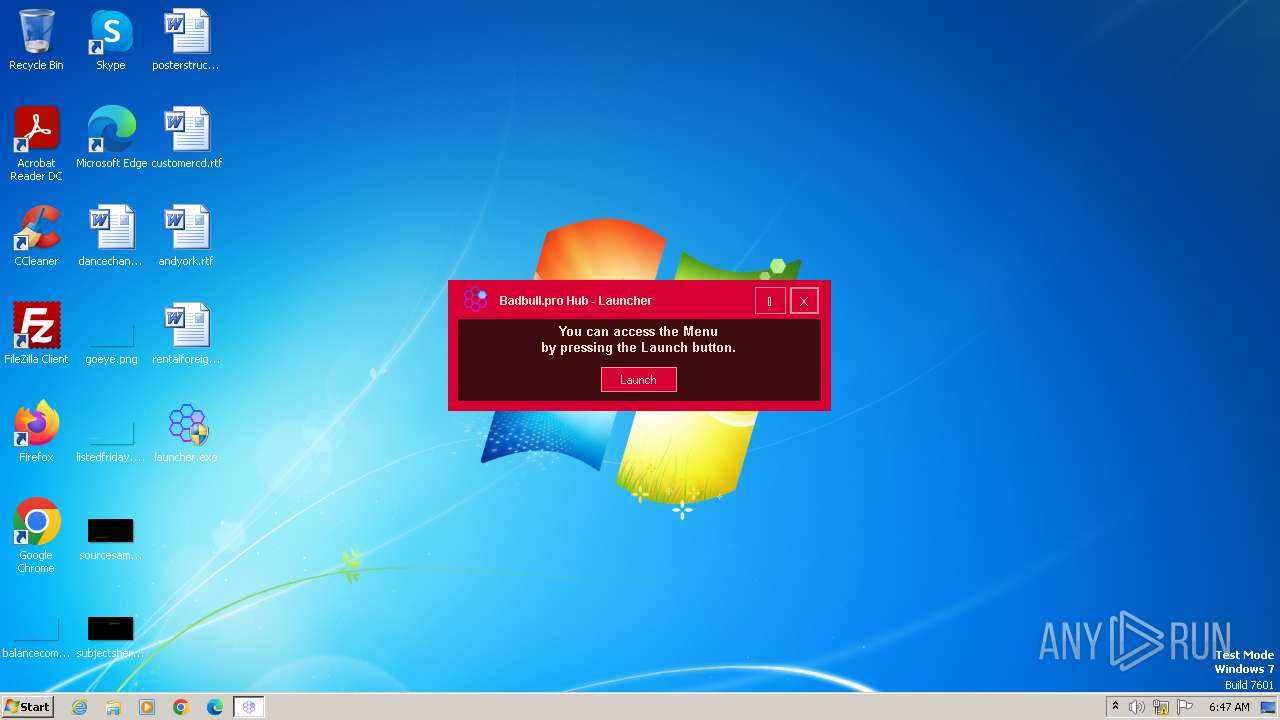
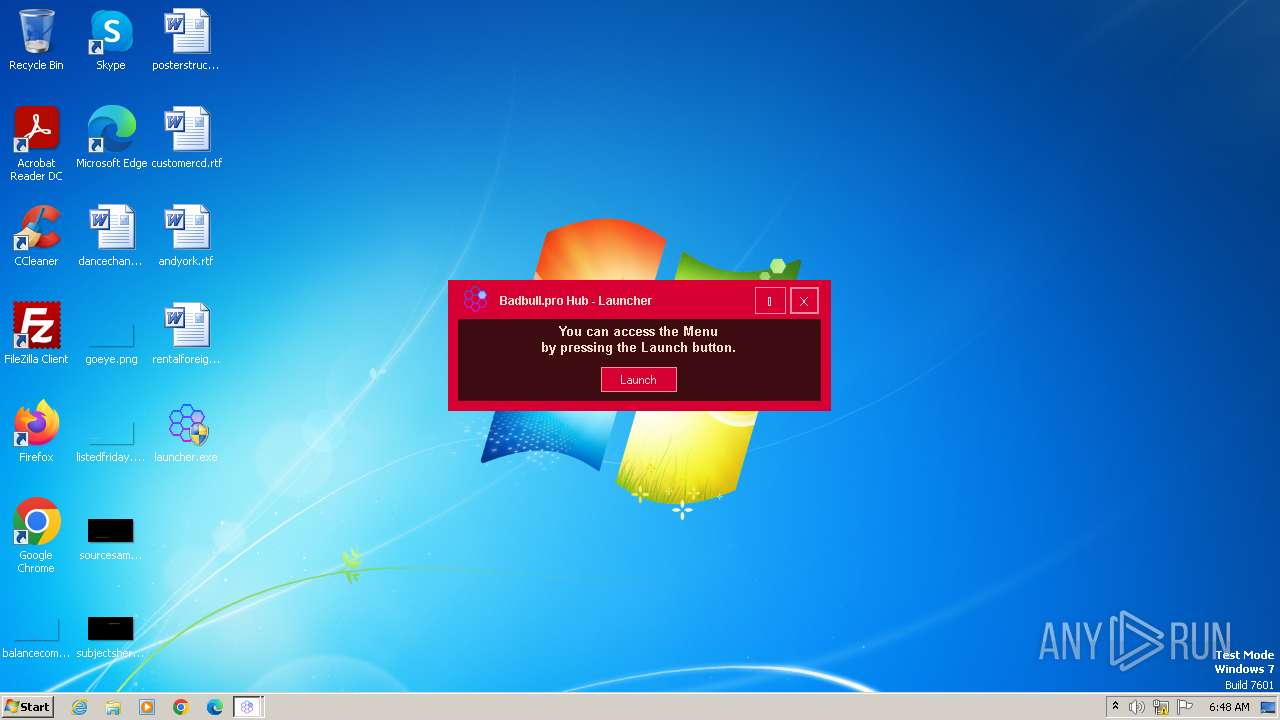
Manual execution by a user
- launcher.exe (PID: 3944)
- launcher.exe (PID: 3724)
Reads the machine GUID from the registry
- launcher.exe (PID: 3724)
- launcher.exe (PID: 2900)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (62) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.5) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Win16/32 Executable Delphi generic (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2081:07:22 08:57:07+02:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 125440 |
| InitializedDataSize: | 21504 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2085e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
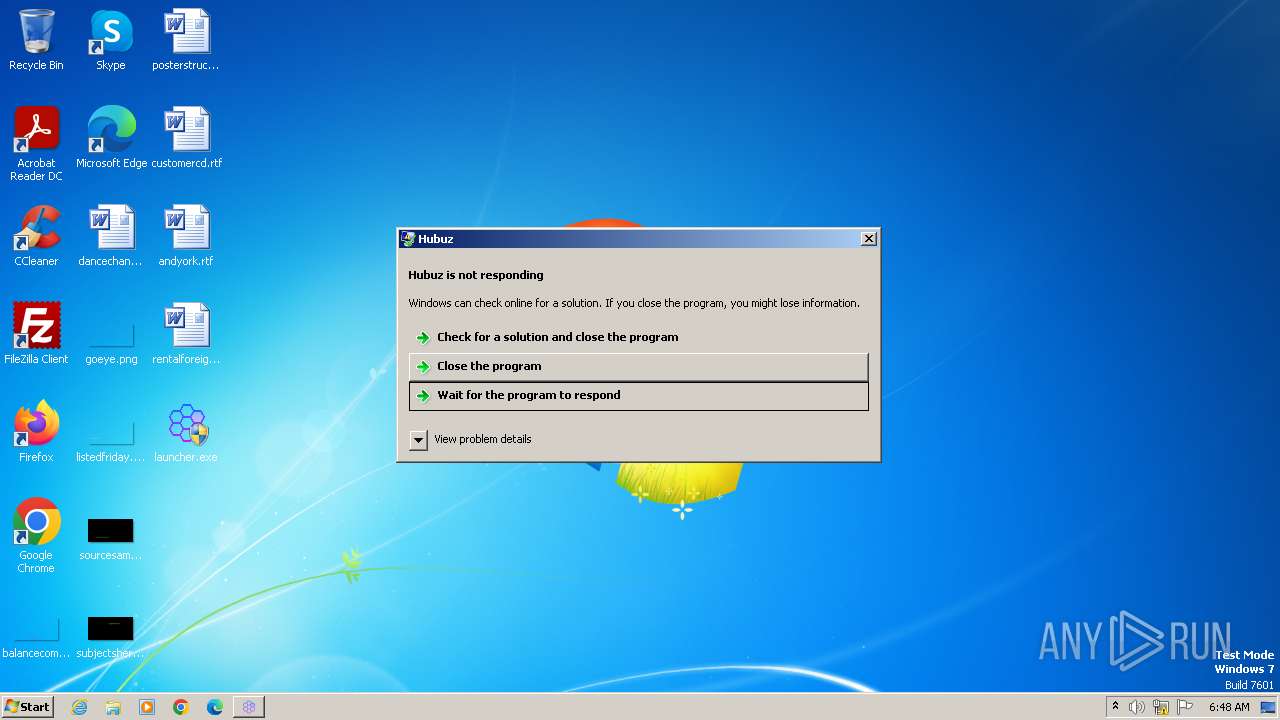
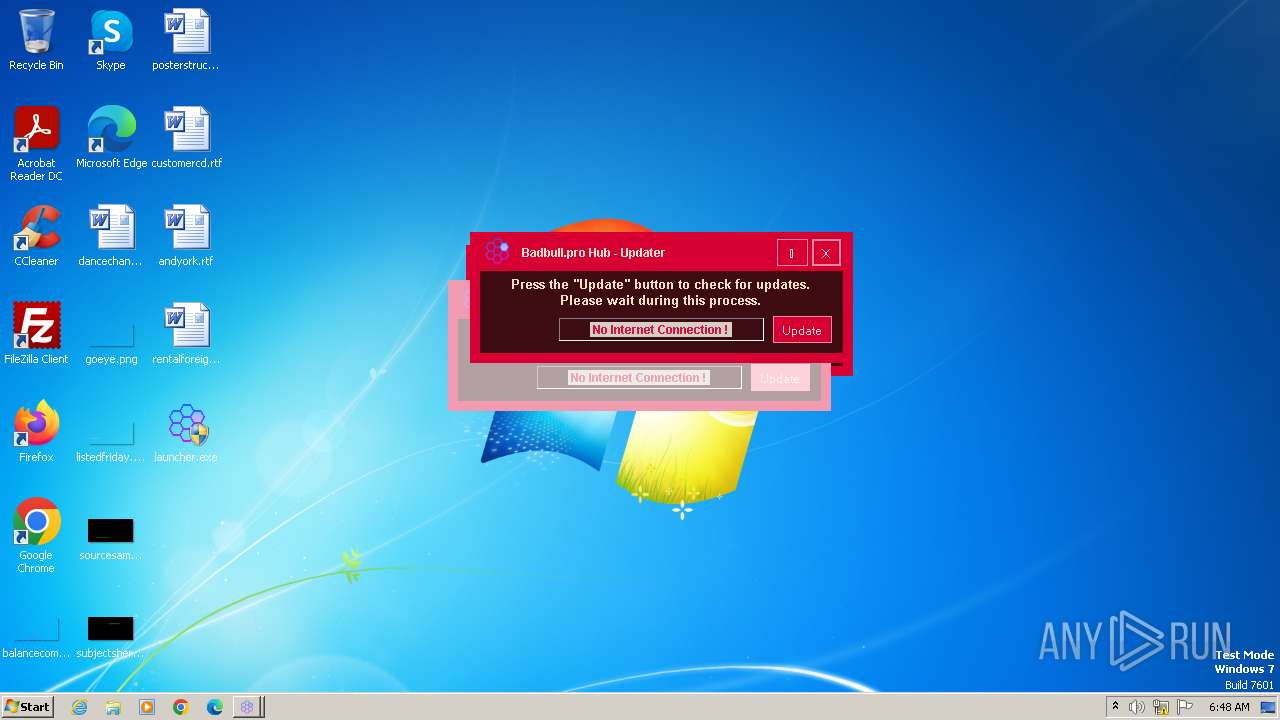
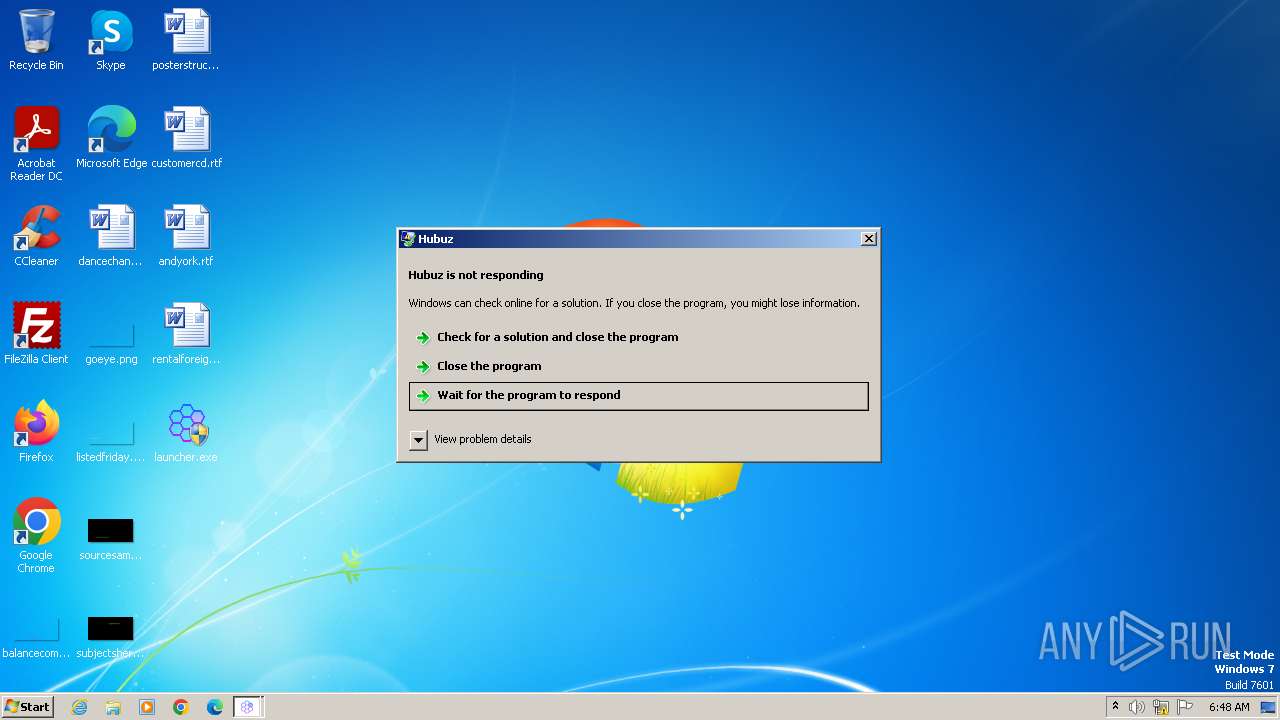
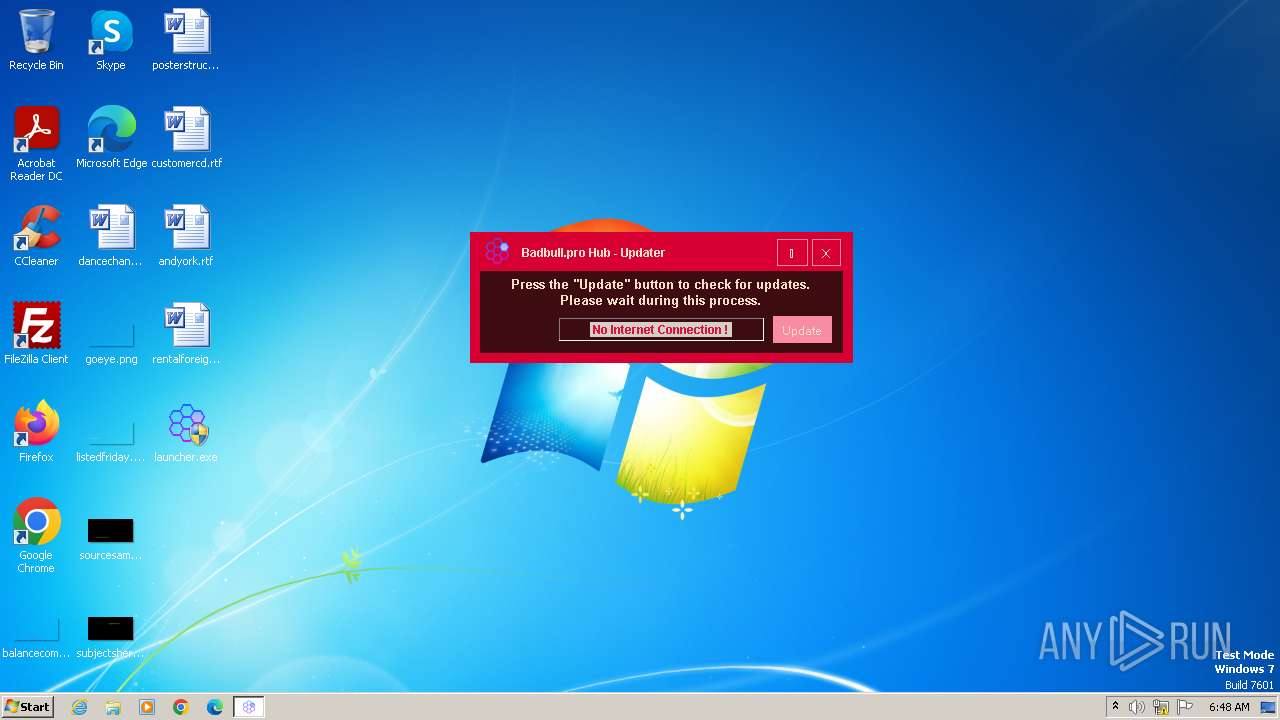
| FileDescription: | Hubuz |
| FileVersion: | 1.0.0.0 |
| InternalName: | BadBull Pro Hub.exe |
| LegalCopyright: | Copyright © 2023 |
| LegalTrademarks: | - |
| OriginalFileName: | BadBull Pro Hub.exe |
| ProductName: | Hubuz |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
50
Monitored processes
6
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2900 | "C:\Users\admin\Desktop\launcher.exe" | C:\Users\admin\Desktop\launcher.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Hubuz Exit code: 3489660927 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3416 | "C:\Users\admin\Desktop\launcher.exe" | C:\Users\admin\Desktop\launcher.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Hubuz Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3596 | "powershell.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | launcher.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3724 | "C:\Users\admin\Desktop\launcher.exe" | C:\Users\admin\Desktop\launcher.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Hubuz Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3944 | "C:\Users\admin\Desktop\launcher.exe" | C:\Users\admin\Desktop\launcher.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Hubuz Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 4084 | "powershell.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | launcher.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
8 238
Read events
8 106
Write events
132
Delete events
0
Modification events
| (PID) Process: | (2900) launcher.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17A\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3596) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17A\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3724) launcher.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17A\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (4084) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17A\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
6
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3596 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\N2T7ZQMSZEV5U043JX1G.temp | binary | |
MD5:C681106A4168B935996B10134404F885 | SHA256:89AB4ECFBB5C1FD07CF99465E36B1A08F51E2512AA60DDD616D4A37753FC112D | |||
| 4084 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\8IB40Y23ACG8WH278MLE.temp | binary | |
MD5:C681106A4168B935996B10134404F885 | SHA256:89AB4ECFBB5C1FD07CF99465E36B1A08F51E2512AA60DDD616D4A37753FC112D | |||
| 4084 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:C681106A4168B935996B10134404F885 | SHA256:89AB4ECFBB5C1FD07CF99465E36B1A08F51E2512AA60DDD616D4A37753FC112D | |||
| 4084 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF170995.TMP | binary | |
MD5:C681106A4168B935996B10134404F885 | SHA256:89AB4ECFBB5C1FD07CF99465E36B1A08F51E2512AA60DDD616D4A37753FC112D | |||
| 3596 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF168cc4.TMP | binary | |
MD5:C681106A4168B935996B10134404F885 | SHA256:89AB4ECFBB5C1FD07CF99465E36B1A08F51E2512AA60DDD616D4A37753FC112D | |||
| 3596 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:C681106A4168B935996B10134404F885 | SHA256:89AB4ECFBB5C1FD07CF99465E36B1A08F51E2512AA60DDD616D4A37753FC112D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
6
DNS requests
1
Threats
2
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2900 | launcher.exe | 142.250.185.164:443 | www.google.com | GOOGLE | US | whitelisted |
3724 | launcher.exe | 142.250.185.164:443 | www.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| whitelisted |
Threats
2 ETPRO signatures available at the full report