| File name: | 62cdbbd726cbf2f58515c41799aaf6702416963dcb4217ab988e78c06f64ce3c.exe |
| Full analysis: | https://app.any.run/tasks/444c5d87-4266-4587-9e1a-9a22f2c92610 |
| Verdict: | Malicious activity |
| Analysis date: | September 09, 2019, 18:27:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B2458EE599350A22EA5B95A044181D57 |
| SHA1: | 876BF3B15C35A53964C87C093B6DCA74B89EB8E2 |
| SHA256: | 62CDBBD726CBF2F58515C41799AAF6702416963DCB4217AB988E78C06F64CE3C |
| SSDEEP: | 49152:cAU+a3dmbNQ/fizcBtgYgiRKCH03UAlSJSVW7/EQlmRGpLpRSsYi77LdGi:PUTtmbNQXioBtN303Uzn75mo5+i7XdGi |
MALICIOUS
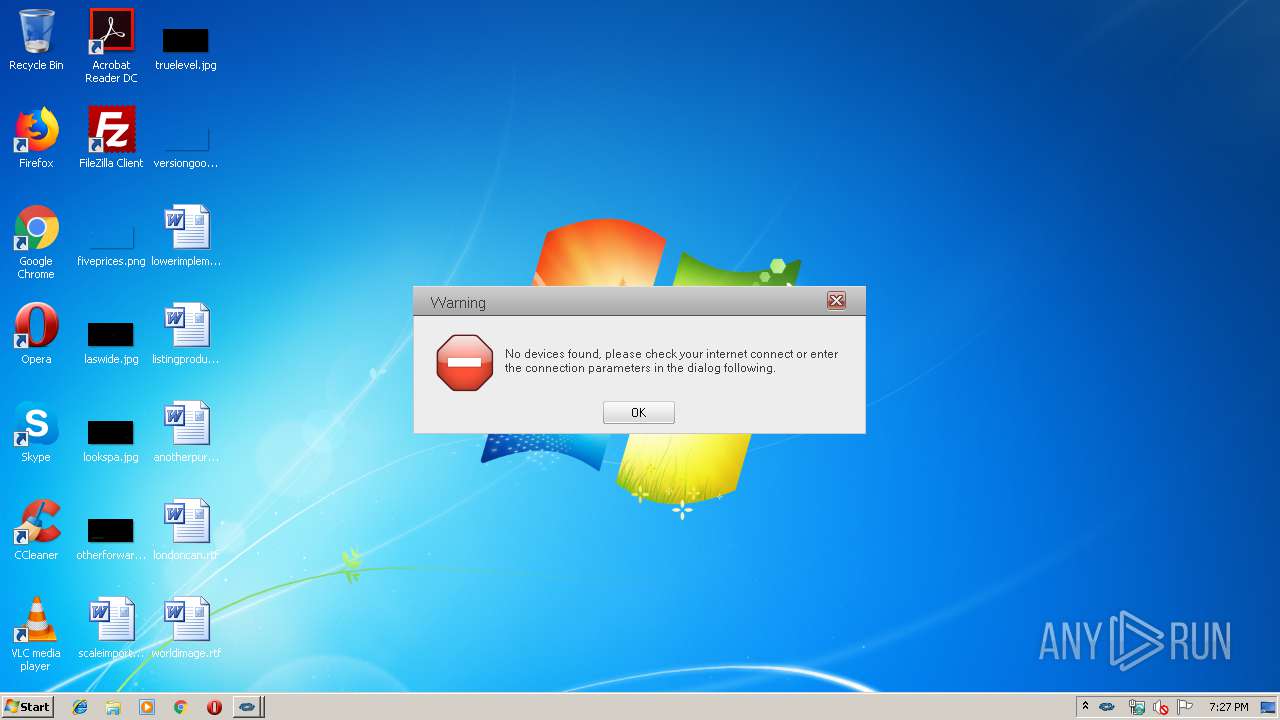
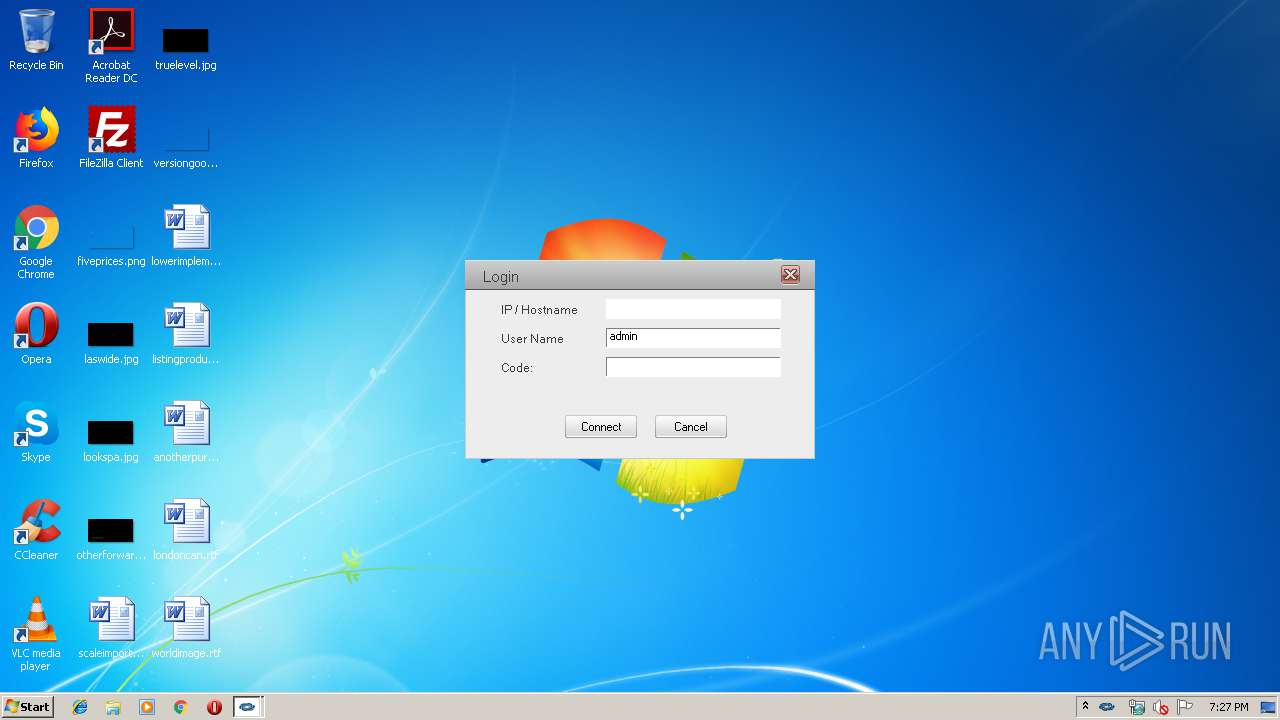
Application was dropped or rewritten from another process
- CoreAudio.exe (PID: 2800)
- CoreAudio.exe (PID: 3436)
- CoreAudio.exe (PID: 2320)
- CoreAudio.exe (PID: 2432)
- AirMedia.exe (PID: 3852)
- CoreAudio.exe (PID: 3484)
Loads dropped or rewritten executable
- rundll32.exe (PID: 3000)
- AirMedia.exe (PID: 3852)
SUSPICIOUS
Executable content was dropped or overwritten
- 62cdbbd726cbf2f58515c41799aaf6702416963dcb4217ab988e78c06f64ce3c.exe (PID: 3208)
Uses RUNDLL32.EXE to load library
- AirMedia.exe (PID: 3852)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (36.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (26.6) |
| .exe | | | Win64 Executable (generic) (23.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2014:06:04 11:23:18+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 245760 |
| InitializedDataSize: | 102400 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x28a29 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.8 |
| ProductVersionNumber: | 1.0.0.8 |
| FileFlagsMask: | 0x003f |
| FileFlags: | Private build, Special build |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (British) |
| CharacterSet: | Unicode |
| CompanyName: | Awind |
| FileDescription: | Awind Extractor |
| FileVersion: | 1.08 |
| InternalName: | Extractor |
| LegalCopyright: | Copyright (c) Awind inc 2012 |
| OriginalFileName: | Extractor.exe |
| ProductName: | Awind Extractor |
| ProductVersion: | 1.08 |
| SpecialBuild: | 96 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 04-Jun-2014 09:23:18 |
| Detected languages: |
|
| CompanyName: | Awind |
| FileDescription: | Awind Extractor |
| FileVersion: | 1.08 |
| InternalName: | Extractor |
| LegalCopyright: | Copyright (c) Awind inc 2012 |
| OriginalFilename: | Extractor.exe |
| ProductName: | Awind Extractor |
| ProductVersion: | 1.08 |
| SpecialBuild: | 96 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 04-Jun-2014 09:23:18 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0003BDD3 | 0x0003C000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.67483 |
.rdata | 0x0003D000 | 0x0000FD9C | 0x00010000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.0516 |
.data | 0x0004D000 | 0x00007780 | 0x00004000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.7818 |
.rsrc | 0x00055000 | 0x00004794 | 0x00005000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.03648 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.65542 | 86 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 2.67991 | 296 | Latin 1 / Western European | English - United Kingdom | RT_ICON |
3 | 3.02695 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
4 | 2.74274 | 180 | Latin 1 / Western European | English - United States | RT_CURSOR |
5 | 2.34038 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
6 | 2.34004 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
7 | 2.51649 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
8 | 2.45401 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
9 | 2.34864 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
10 | 2.34505 | 308 | Latin 1 / Western European | English - United States | RT_CURSOR |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.dll |
OLEACC.dll (delay-loaded) |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
WINSPOOL.DRV |
comdlg32.dll |
Total processes
45
Monitored processes
8
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2320 | "C:\Users\admin\AppData\Local\Temp\Crestron_self_extractor\CoreAudio.exe" Mute | C:\Users\admin\AppData\Local\Temp\Crestron_self_extractor\CoreAudio.exe | — | AirMedia.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225547 Modules
| |||||||||||||||
| 2432 | "C:\Users\admin\AppData\Local\Temp\Crestron_self_extractor\CoreAudio.exe" Mute | C:\Users\admin\AppData\Local\Temp\Crestron_self_extractor\CoreAudio.exe | — | AirMedia.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225547 Modules
| |||||||||||||||
| 2800 | "C:\Users\admin\AppData\Local\Temp\Crestron_self_extractor\CoreAudio.exe" Record | C:\Users\admin\AppData\Local\Temp\Crestron_self_extractor\CoreAudio.exe | — | AirMedia.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225547 Modules
| |||||||||||||||
| 3000 | C:\Windows\system32\rundll32.exe DXCap.dll,DXCap_Hook | C:\Windows\system32\rundll32.exe | — | AirMedia.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3208 | "C:\Users\admin\AppData\Local\Temp\62cdbbd726cbf2f58515c41799aaf6702416963dcb4217ab988e78c06f64ce3c.exe" | C:\Users\admin\AppData\Local\Temp\62cdbbd726cbf2f58515c41799aaf6702416963dcb4217ab988e78c06f64ce3c.exe | explorer.exe | ||||||||||||
User: admin Company: Awind Integrity Level: MEDIUM Description: Awind Extractor Exit code: 0 Version: 1.08 Modules
| |||||||||||||||
| 3436 | "C:\Users\admin\AppData\Local\Temp\Crestron_self_extractor\CoreAudio.exe" Volume | C:\Users\admin\AppData\Local\Temp\Crestron_self_extractor\CoreAudio.exe | — | AirMedia.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225547 Modules
| |||||||||||||||
| 3484 | "C:\Users\admin\AppData\Local\Temp\Crestron_self_extractor\CoreAudio.exe" Mute | C:\Users\admin\AppData\Local\Temp\Crestron_self_extractor\CoreAudio.exe | — | AirMedia.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225547 Modules
| |||||||||||||||
| 3852 | 62cdbbd726cbf2f58515c41799aaf6702416963dcb4217ab988e78c06f64ce3c | C:\Users\admin\AppData\Local\Temp\Crestron_self_extractor\AirMedia.exe | 62cdbbd726cbf2f58515c41799aaf6702416963dcb4217ab988e78c06f64ce3c.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: AirMedia Exit code: 0 Version: 1.0.6.8 Modules
| |||||||||||||||
Total events
423
Read events
391
Write events
32
Delete events
0
Modification events
| (PID) Process: | (3852) AirMedia.exe | Key: | HKEY_CURRENT_USER\Software\AWIND\DLCap |
| Operation: | write | Name: | Dwm.Composition.Backup |
Value: 0 | |||
| (PID) Process: | (3852) AirMedia.exe | Key: | HKEY_CURRENT_USER\Software\AWIND |
| Operation: | write | Name: | Acceleration.Level.Backup |
Value: 0 | |||
| (PID) Process: | (3852) AirMedia.exe | Key: | HKEY_CURRENT_USER\Software\AWIND\DLCap |
| Operation: | write | Name: | UACLevel.Backup |
Value: 0 | |||
| (PID) Process: | (3852) AirMedia.exe | Key: | HKEY_CURRENT_USER\Software\AWIND\DLCap |
| Operation: | write | Name: | SecureDesktop.Backup |
Value: 1 | |||
| (PID) Process: | (2800) CoreAudio.exe | Key: | HKEY_CURRENT_USER\Software\AWIND |
| Operation: | write | Name: | AudioCurrentVolume0 |
Value: 67 | |||
| (PID) Process: | (2800) CoreAudio.exe | Key: | HKEY_CURRENT_USER\Software\AWIND |
| Operation: | write | Name: | AudioCurrentMute0 |
Value: false | |||
| (PID) Process: | (3852) AirMedia.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3852) AirMedia.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3000) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: rundll32.exe | |||
| (PID) Process: | (3000) rundll32.exe | Key: | HKEY_CURRENT_USER\Software\AWIND\DXCap\X86 |
| Operation: | write | Name: | DXGI_Present |
Value: 186833 | |||
Executable files
16
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3208 | 62cdbbd726cbf2f58515c41799aaf6702416963dcb4217ab988e78c06f64ce3c.exe | C:\Users\admin\AppData\Local\Temp\Crestron_self_extractor\awiscale.dll | executable | |
MD5:— | SHA256:— | |||
| 3208 | 62cdbbd726cbf2f58515c41799aaf6702416963dcb4217ab988e78c06f64ce3c.exe | C:\Users\admin\AppData\Local\Temp\Crestron_self_extractor\EDesktopAPI.dll | executable | |
MD5:55EDF59FAA4A18A5C58112D1618C7B61 | SHA256:3A1925E505636015E14F7999F7696EF58FDE527A41FD4523770AC63771D08FC2 | |||
| 3208 | 62cdbbd726cbf2f58515c41799aaf6702416963dcb4217ab988e78c06f64ce3c.exe | C:\Users\admin\AppData\Local\Temp\Crestron_self_extractor\DXCap.dll | executable | |
MD5:AE385D23F55DE5BD3F1CC760DC9E4B91 | SHA256:03668F6DB5CE4C000059BE646DBD7A13F2143240AA442611DE688A0BD858C3D6 | |||
| 3208 | 62cdbbd726cbf2f58515c41799aaf6702416963dcb4217ab988e78c06f64ce3c.exe | C:\Users\admin\AppData\Local\Temp\Crestron_self_extractor\CoreAudioCap.dll | executable | |
MD5:72C7ACAC8D7671A686EA2BB94A5096FA | SHA256:D745E535C2365637822AABEB925E36682D3E0547C268ABA1DFA58DB2B6CC83AB | |||
| 3208 | 62cdbbd726cbf2f58515c41799aaf6702416963dcb4217ab988e78c06f64ce3c.exe | C:\Users\admin\AppData\Local\Temp\Crestron_self_extractor\wps.ini | text | |
MD5:— | SHA256:— | |||
| 3852 | AirMedia.exe | C:\Users\admin\AppData\Local\AirMedia\wps.ini | text | |
MD5:— | SHA256:— | |||
| 3208 | 62cdbbd726cbf2f58515c41799aaf6702416963dcb4217ab988e78c06f64ce3c.exe | C:\Users\admin\AppData\Local\Temp\Crestron_self_extractor\zlib1.dll | executable | |
MD5:C7D4D685A0AF2A09CBC21CB474358595 | SHA256:E96B397B499D9EAA3F52EAF496CA8941E80C0AD1544879CCADF02BF2C6A1ECFC | |||
| 3208 | 62cdbbd726cbf2f58515c41799aaf6702416963dcb4217ab988e78c06f64ce3c.exe | C:\Users\admin\AppData\Local\Temp\Crestron_self_extractor\CoreAudio.exe | executable | |
MD5:— | SHA256:— | |||
| 3208 | 62cdbbd726cbf2f58515c41799aaf6702416963dcb4217ab988e78c06f64ce3c.exe | C:\Users\admin\AppData\Local\Temp\Crestron_self_extractor\AirMedia.exe | executable | |
MD5:— | SHA256:— | |||
| 3208 | 62cdbbd726cbf2f58515c41799aaf6702416963dcb4217ab988e78c06f64ce3c.exe | C:\Users\admin\AppData\Local\Temp\Crestron_self_extractor\AudioProjection.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report