| File name: | osi.exe |
| Full analysis: | https://app.any.run/tasks/62370991-01a9-4041-994b-f1ac63157278 |
| Verdict: | Malicious activity |
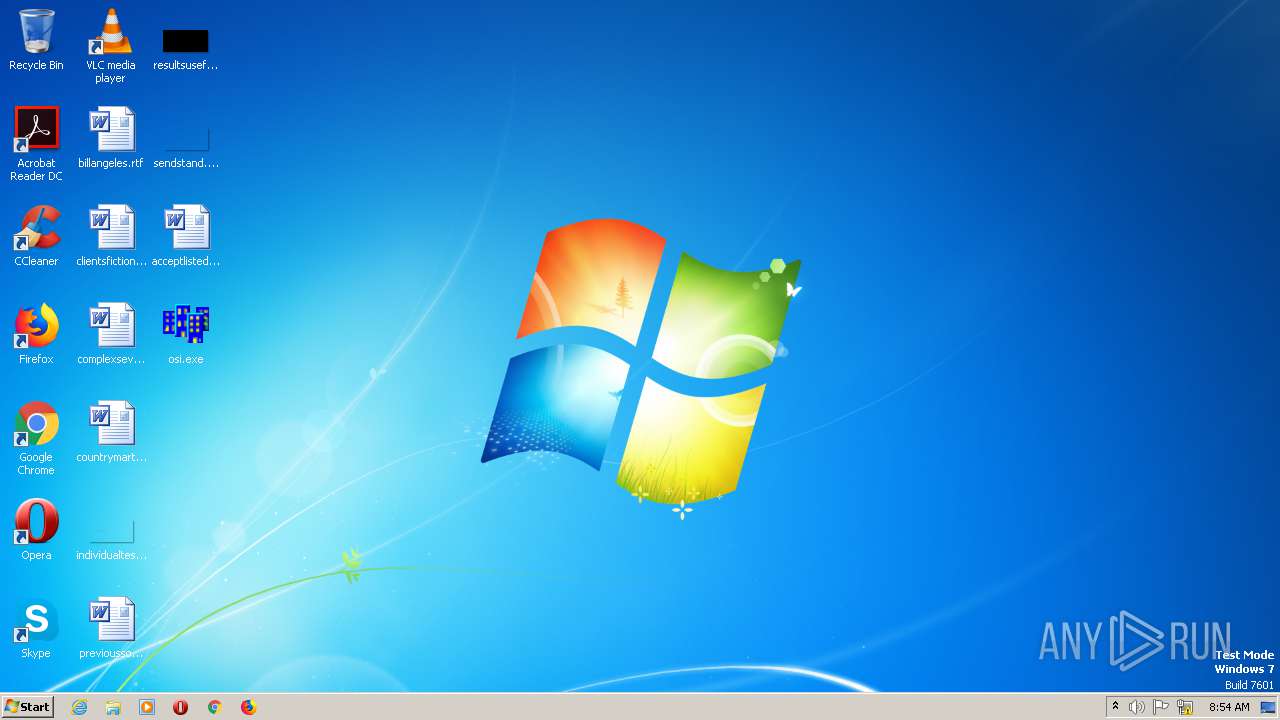
| Analysis date: | October 08, 2020, 08:54:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows |
| MD5: | 918B4DF1F8D7B1E18E3E8FCCDEF3F5DE |
| SHA1: | 9B8F84E2D239252C83D89C3179F53893574C97A1 |
| SHA256: | 62BD38C89D1A30B03BD89A788D9F2852659F77715C97E5C12445C33F43FA13E5 |
| SSDEEP: | 24576:oEhFMGyXUHAW3S69Y2iBwdFQ4cN9bIV9XUNbW4f:Tio4GrcbW4f |
MALICIOUS
Application was dropped or rewritten from another process
- cmd.exe (PID: 2812)
- GetX64BTIT.exe (PID: 1008)
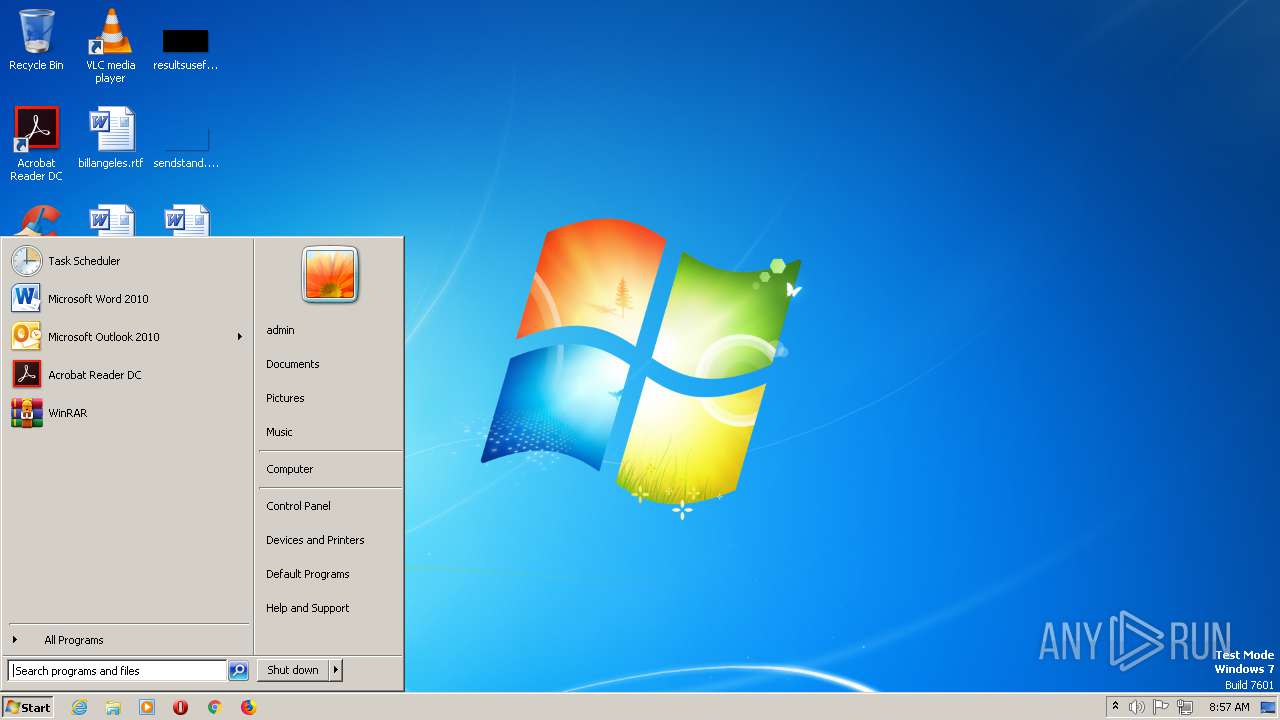
Loads the Task Scheduler DLL interface
- cmd.exe (PID: 2812)
Writes to a start menu file
- cmd.exe (PID: 2812)
SUSPICIOUS
Checks for external IP
- cmd.exe (PID: 2812)
Creates files in the Windows directory
- cmd.exe (PID: 2812)
Executable content was dropped or overwritten
- extrac32.exe (PID: 704)
- cmd.exe (PID: 2812)
Creates files in the user directory
- cmd.exe (PID: 2812)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .scr | | | Windows screen saver (31.7) |
|---|---|---|
| .exe | | | DOS Executable Borland C++ (31.5) |
| .dll | | | Win32 Dynamic Link Library (generic) (15.9) |
| .exe | | | Win32 Executable (generic) (10.9) |
| .exe | | | Generic Win/DOS Executable (4.8) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:10:06 18:06:34+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 5 |
| CodeSize: | 843776 |
| InitializedDataSize: | 77824 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x14b8 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Oct-2020 16:06:34 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000200 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 06-Oct-2020 16:06:34 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000CE000 | 0x000CD400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.51517 |
.data | 0x000CF000 | 0x00013000 | 0x0000E400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.9616 |
.tls | 0x000E2000 | 0x00001000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x000E3000 | 0x00001000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.210826 |
.idata | 0x000E4000 | 0x00003000 | 0x00002A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.98434 |
.edata | 0x000E7000 | 0x00001000 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.12645 |
.rsrc | 0x000E8000 | 0x0000A000 | 0x00009200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.23317 |
.reloc | 0x000F2000 | 0x0000F000 | 0x0000EA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.61032 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.05955 | 744 | UNKNOWN | English - United States | RT_ICON |
2 | 2.80231 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
3 | 3.00046 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
4 | 2.56318 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
5 | 2.6949 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
6 | 2.62527 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
7 | 2.91604 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
8 | 2.6633 | 308 | UNKNOWN | UNKNOWN | RT_CURSOR |
4073 | 2.84705 | 296 | UNKNOWN | UNKNOWN | RT_STRING |
4074 | 3.28291 | 376 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
ADVAPI32.DLL |
COMCTL32.DLL |
GDI32.DLL |
KERNEL32.DLL |
OLE32.DLL |
OLEAUT32.DLL |
SHELL32.DLL |
USER32.DLL |
VERSION.DLL |
Exports
Title | Ordinal | Address |
|---|---|---|
__GetExceptDLLinfo | 1 | 0x00001511 |
@@Dirty@Initialize | 2 | 0x000026EC |
@@Dirty@Finalize | 3 | 0x000026FC |
___CPPdebugHook | 4 | 0x000CF098 |
_Form1 | 5 | 0x000DD2D0 |
Total processes
38
Monitored processes
4
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 704 | "C:\Windows\system32\extrac32.exe" | C:\Windows\SysWOW64\extrac32.exe | osi.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® CAB File Extract Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1008 | "C:\Users\admin\AppData\Local\Temp\GetX64BTIT.exe" | C:\Users\admin\AppData\Local\Temp\GetX64BTIT.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1132 | "C:\Users\admin\Desktop\osi.exe" | C:\Users\admin\Desktop\osi.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2812 | "C:\Users\admin\AppData\Local\Temp\cmd.exe" | C:\Users\admin\AppData\Local\Temp\cmd.exe | extrac32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
47
Read events
28
Write events
19
Delete events
0
Modification events
| (PID) Process: | (704) extrac32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (704) extrac32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000007F000000010000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (704) extrac32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (704) extrac32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (704) extrac32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (704) extrac32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (704) extrac32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (704) extrac32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (704) extrac32.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (704) extrac32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
3
Suspicious files
2
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1008 | GetX64BTIT.exe | C:\Users\admin\AppData\Local\Temp\x64btit.txt | binary | |
MD5:— | SHA256:— | |||
| 704 | extrac32.exe | C:\Users\admin\AppData\Local\Temp\e60824e5.png | image | |
MD5:— | SHA256:— | |||
| 2812 | cmd.exe | C:\Windows\Tasks\notepad.job | binary | |
MD5:— | SHA256:— | |||
| 704 | extrac32.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\BDW1XBVN\3zBLzB6[1].png | image | |
MD5:— | SHA256:— | |||
| 2812 | cmd.exe | C:\Users\admin\AppData\Local\Temp\GetX64BTIT.exe | executable | |
MD5:B4CD27F2B37665F51EB9FE685EC1D373 | SHA256:91F1023142B7BABF6FF75DAD984C2A35BDE61DC9E61F45483F4B65008576D581 | |||
| 704 | extrac32.exe | C:\Users\admin\AppData\Local\Temp\cmd.exe | executable | |
MD5:AD7B9C14083B52BC532FBA5948342B98 | SHA256:17F746D82695FA9B35493B41859D39D786D32B23A9D2E00F4011DEC7A02402AE | |||
| 2812 | cmd.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\97b7721c.exe | executable | |
MD5:AD7B9C14083B52BC532FBA5948342B98 | SHA256:17F746D82695FA9B35493B41859D39D786D32B23A9D2E00F4011DEC7A02402AE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
45
DNS requests
3
Threats
81
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | HEAD | 200 | 151.101.12.193:443 | https://i.imgur.com/3zBLzB6.png | US | — | — | malicious |
2812 | cmd.exe | GET | — | 91.229.76.124:80 | http://91.229.76.124/tor/server/fp/29ffa7a881abadca4eeedd16128537bb028d5153 | UA | — | — | suspicious |
2812 | cmd.exe | GET | — | 199.58.81.140:80 | http://199.58.81.140/tor/status-vote/current/consensus | CA | — | — | suspicious |
2812 | cmd.exe | GET | — | 94.16.143.200:80 | http://94.16.143.200/tor/server/fp/36cf8dd24f352538f6e20c37e2b2f108975201b9 | CH | — | — | suspicious |
2812 | cmd.exe | GET | — | 109.236.90.209:80 | http://109.236.90.209/tor/server/fp/cf7d2b4becd17e04fa0d604229888f91d1665c01 | NL | — | — | malicious |
2812 | cmd.exe | GET | — | 37.120.146.88:80 | http://37.120.146.88/tor/server/fp/03910f285a33f365838ec66ef2c2ef754d046760 | RO | — | — | suspicious |
2812 | cmd.exe | GET | — | 51.15.187.209:80 | http://51.15.187.209/tor/server/fp/11dadacc370978a1fa1d23a4f14f823548c55bd2 | FR | — | — | suspicious |
2812 | cmd.exe | GET | — | 54.39.176.60:80 | http://54.39.176.60/tor/server/fp/f2e60de0f39bea826b50eb619a014adce9619359 | FR | — | — | suspicious |
2812 | cmd.exe | GET | — | 199.249.230.104:80 | http://199.249.230.104/tor/server/fp/d734e137dd5362d5068ae3e0211eb297b76c1615 | US | — | — | suspicious |
2812 | cmd.exe | GET | — | 208.1.62.240:80 | http://208.1.62.240/tor/server/fp/afc69acd47e4cbd5cf8ea47f9b5622c91bf2da60 | US | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 151.101.12.193:443 | i.imgur.com | Fastly | US | malicious |
704 | extrac32.exe | 151.101.12.193:443 | i.imgur.com | Fastly | US | malicious |
2812 | cmd.exe | 199.58.81.140:80 | — | Koumbit | CA | suspicious |
2812 | cmd.exe | 45.154.35.219:443 | — | — | — | suspicious |
2812 | cmd.exe | 94.16.143.200:80 | — | Quickline AG | CH | suspicious |
2812 | cmd.exe | 51.15.187.209:80 | — | Online S.a.s. | FR | suspicious |
2812 | cmd.exe | 137.74.61.103:443 | — | OVH SAS | FR | unknown |
2812 | cmd.exe | 129.6.15.28:13 | time-a.nist.gov | National Bureau of Standards | US | unknown |
2812 | cmd.exe | 91.229.76.124:80 | — | PE Freehost | UA | suspicious |
2812 | cmd.exe | 92.223.72.168:443 | — | G-Core Labs S.A. | RU | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
i.imgur.com |
| malicious |
api.ipify.org |
| shared |
time-a.nist.gov |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2812 | cmd.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 387 |
2812 | cmd.exe | Potential Corporate Privacy Violation | ET POLICY TOR Consensus Data Requested |
2812 | cmd.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 827 |
2812 | cmd.exe | Potential Corporate Privacy Violation | ET P2P Tor Get Server Request |
2812 | cmd.exe | Misc Attack | ET TOR Known Tor Exit Node Traffic group 103 |
2812 | cmd.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 103 |
2812 | cmd.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 641 |
2812 | cmd.exe | Potential Corporate Privacy Violation | ET P2P Tor Get Server Request |
2812 | cmd.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 202 |
2812 | cmd.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 805 |