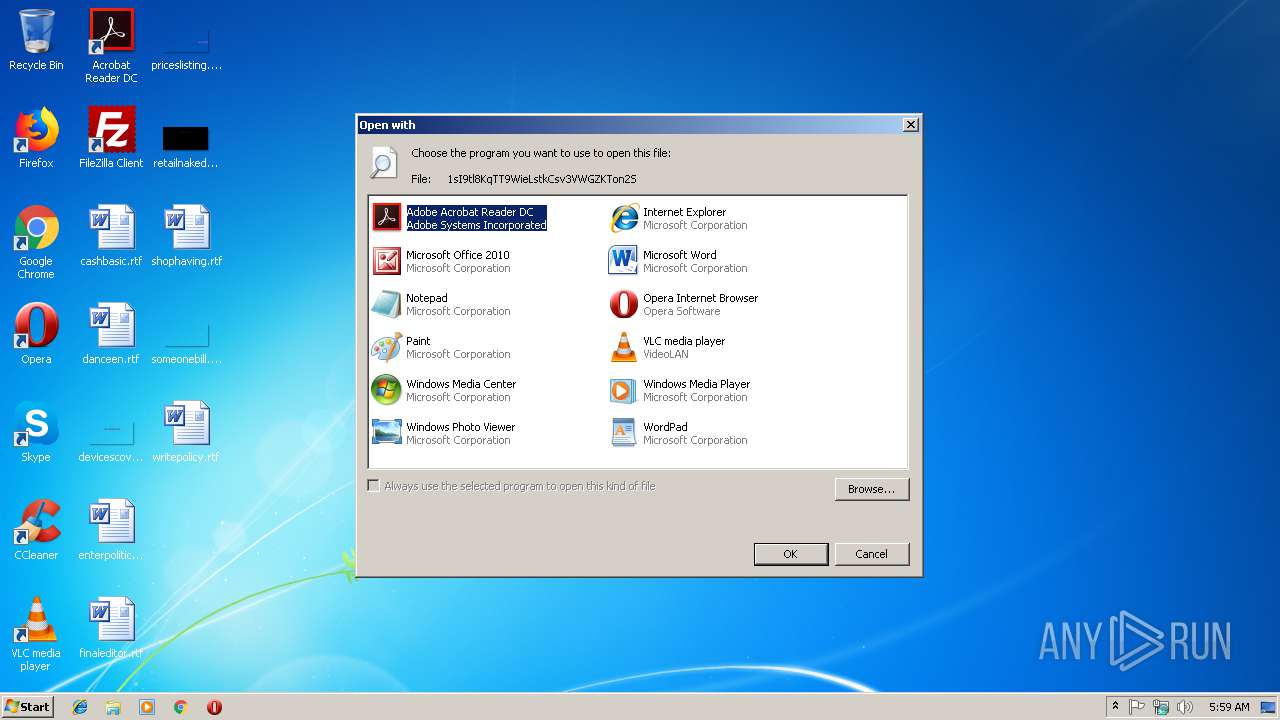
| File name: | 1sI9tl8KqTT9WieLstkCsv3VWGZKTon2S |
| Full analysis: | https://app.any.run/tasks/bf7b3423-7ed2-4f51-a3a7-ab56c8c7c341 |
| Verdict: | Malicious activity |
| Analysis date: | February 19, 2019, 05:59:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines |
| MD5: | 8A3C097409CCB54AC8159F87D345E019 |
| SHA1: | 73FF8E91B2A654265452CD13AC17675F7EE2A9EF |
| SHA256: | 62BAFB49BD2D79AF119054A27A613F3A3606377DA2122E8F3A5BAD5496C2834C |
| SSDEEP: | 1536:T7fn2jSuNTeFJ1NMT00QiOQz3UrffDKH8Z:TajSuN+NmGQzkrffDE8Z |
MALICIOUS
No malicious indicators.SUSPICIOUS
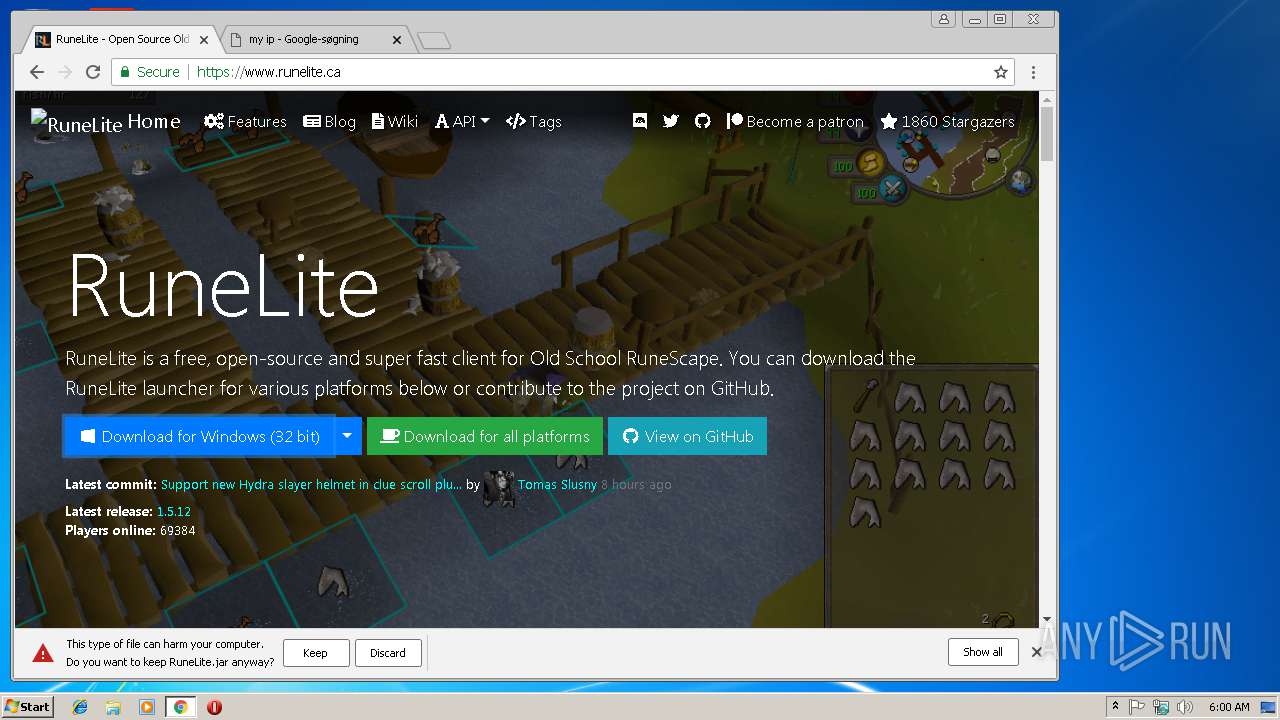
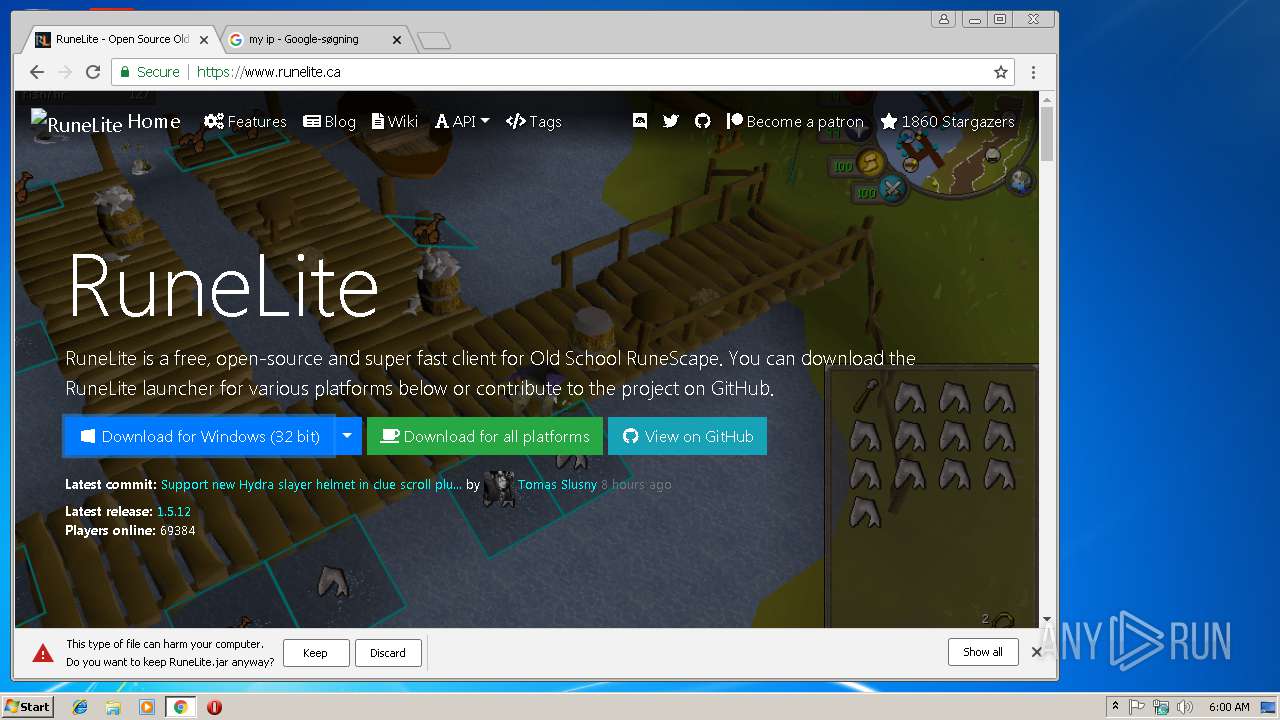
Executes JAVA applets
- chrome.exe (PID: 2804)
INFO
Application launched itself
- chrome.exe (PID: 2804)
Reads settings of System Certificates
- chrome.exe (PID: 2804)
Reads Internet Cache Settings
- chrome.exe (PID: 2804)
Creates files in the user directory
- chrome.exe (PID: 2804)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
EXIF
HTML
| viewport: | width=300, initial-scale=1 |
|---|---|
| Description: | Google Drive is a free way to keep your files backed up and easy to reach from any phone, tablet or computer. Start with 15 GB of Google storage – free. |
| googleSiteVerification: | LrdTUW9psUAMbh4Ia074-BPEVmcpBxF6Gwf0MSgQXZs |
| Title: | Meet Google Drive – One place for all your files |
Total processes
62
Monitored processes
29
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
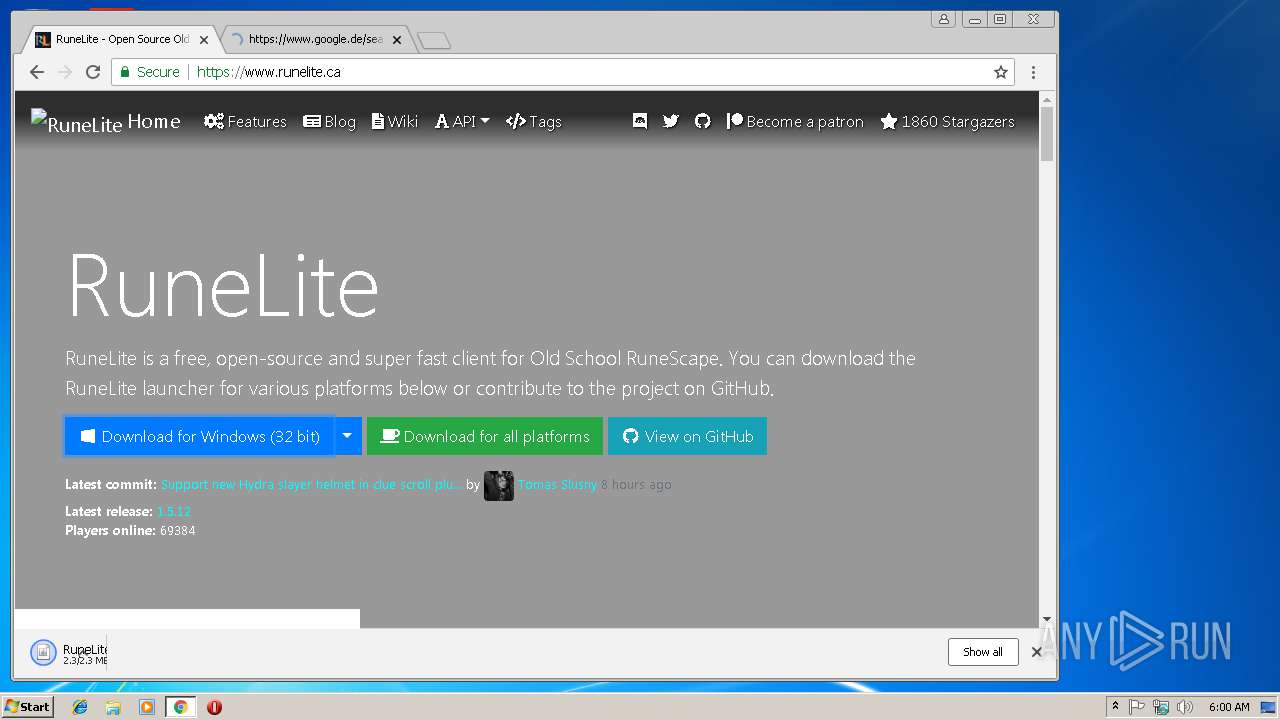
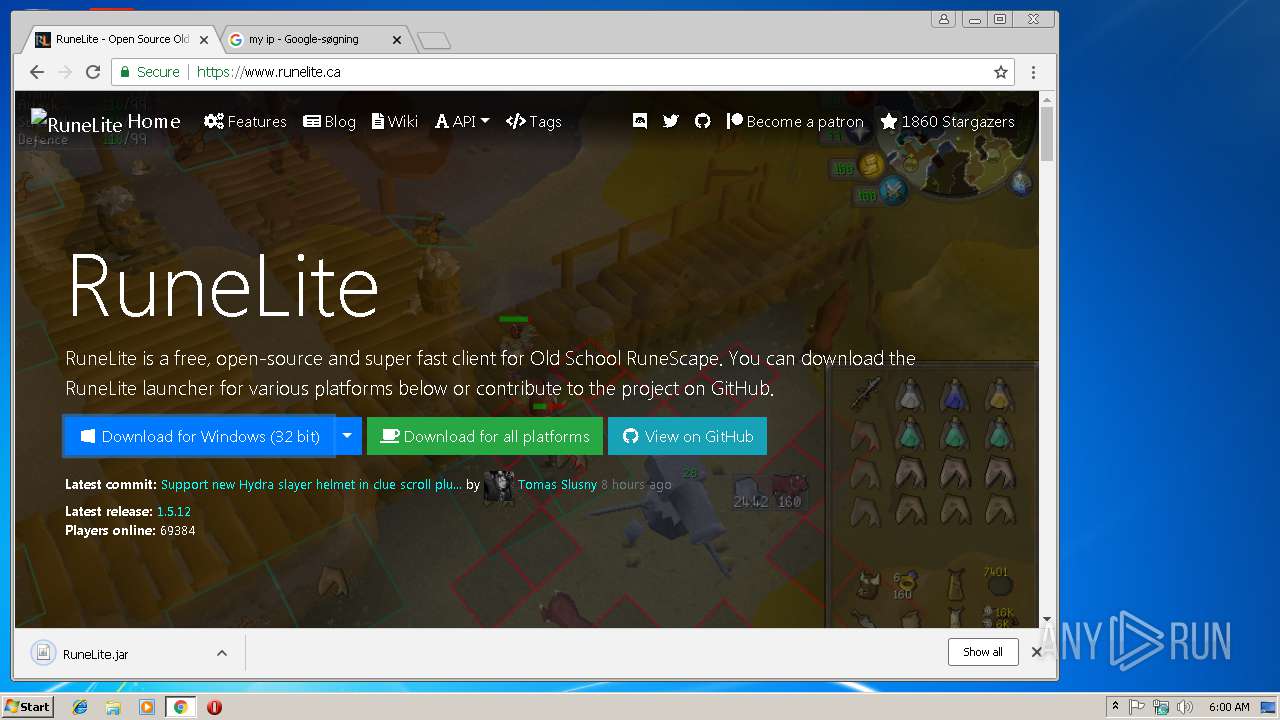
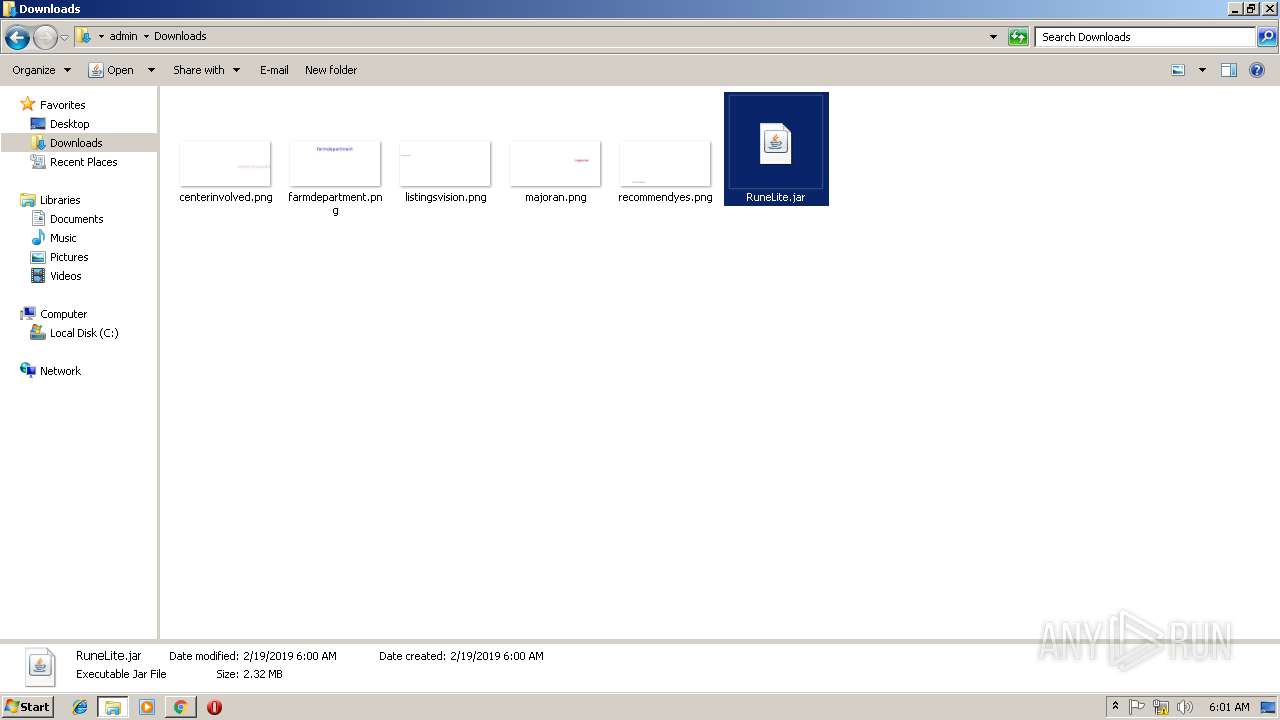
| 1668 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -jar "C:\Users\admin\Downloads\RuneLite.jar" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | explorer.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 4294967295 Version: 8.0.920.14 Modules
| |||||||||||||||
| 1744 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -jar "C:\Users\admin\Downloads\RuneLite.jar" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | explorer.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 4294967295 Version: 8.0.920.14 Modules
| |||||||||||||||
| 2092 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -jar "C:\Users\admin\Downloads\RuneLite.jar" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | explorer.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 4294967295 Version: 8.0.920.14 Modules
| |||||||||||||||
| 2112 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -jar "C:\Users\admin\Downloads\RuneLite.jar" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | explorer.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 4294967295 Version: 8.0.920.14 Modules
| |||||||||||||||
| 2172 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -jar "C:\Users\admin\Downloads\RuneLite.jar" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | explorer.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 4294967295 Version: 8.0.920.14 Modules
| |||||||||||||||
| 2204 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,2711759363646038479,13200592699440873029,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=7E68AE451339EC16EE359F19692272A4 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7E68AE451339EC16EE359F19692272A4 --renderer-client-id=13 --mojo-platform-channel-handle=4136 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2304 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -jar "C:\Users\admin\Downloads\RuneLite.jar" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | explorer.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 4294967295 Version: 8.0.920.14 Modules
| |||||||||||||||
| 2368 | "C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe" -jar "C:\Users\admin\Downloads\RuneLite.jar" | C:\Program Files\Java\jre1.8.0_92\bin\javaw.exe | explorer.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 4294967295 Version: 8.0.920.14 Modules
| |||||||||||||||
| 2404 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1008,2711759363646038479,13200592699440873029,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7984F6EEAF2CF259AAF1326F38B4968F --mojo-platform-channel-handle=2528 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1008,2711759363646038479,13200592699440873029,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=C557FE30DCCEB7054B42CD1D77795608 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=C557FE30DCCEB7054B42CD1D77795608 --renderer-client-id=6 --mojo-platform-channel-handle=3556 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
1 188
Read events
1 086
Write events
98
Delete events
4
Modification events
| (PID) Process: | (2932) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe |
Value: Adobe Acrobat Reader DC | |||
| (PID) Process: | (2932) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\eHome\ehshell.exe |
Value: Windows Media Center | |||
| (PID) Process: | (2932) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\mspaint.exe |
Value: Paint | |||
| (PID) Process: | (2932) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\NOTEPAD.EXE |
Value: Notepad | |||
| (PID) Process: | (2932) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\PROGRA~1\MICROS~1\Office14\OIS.EXE |
Value: Microsoft Office 2010 | |||
| (PID) Process: | (2932) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Opera\Opera.exe |
Value: Opera Internet Browser | |||
| (PID) Process: | (2932) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Windows Photo Viewer\PhotoViewer.dll |
Value: Windows Photo Viewer | |||
| (PID) Process: | (2932) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\VideoLAN\VLC\vlc.exe |
Value: VLC media player | |||
| (PID) Process: | (2932) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE |
Value: Microsoft Word | |||
| (PID) Process: | (2932) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
2
Suspicious files
79
Text files
142
Unknown types
2
Dropped files
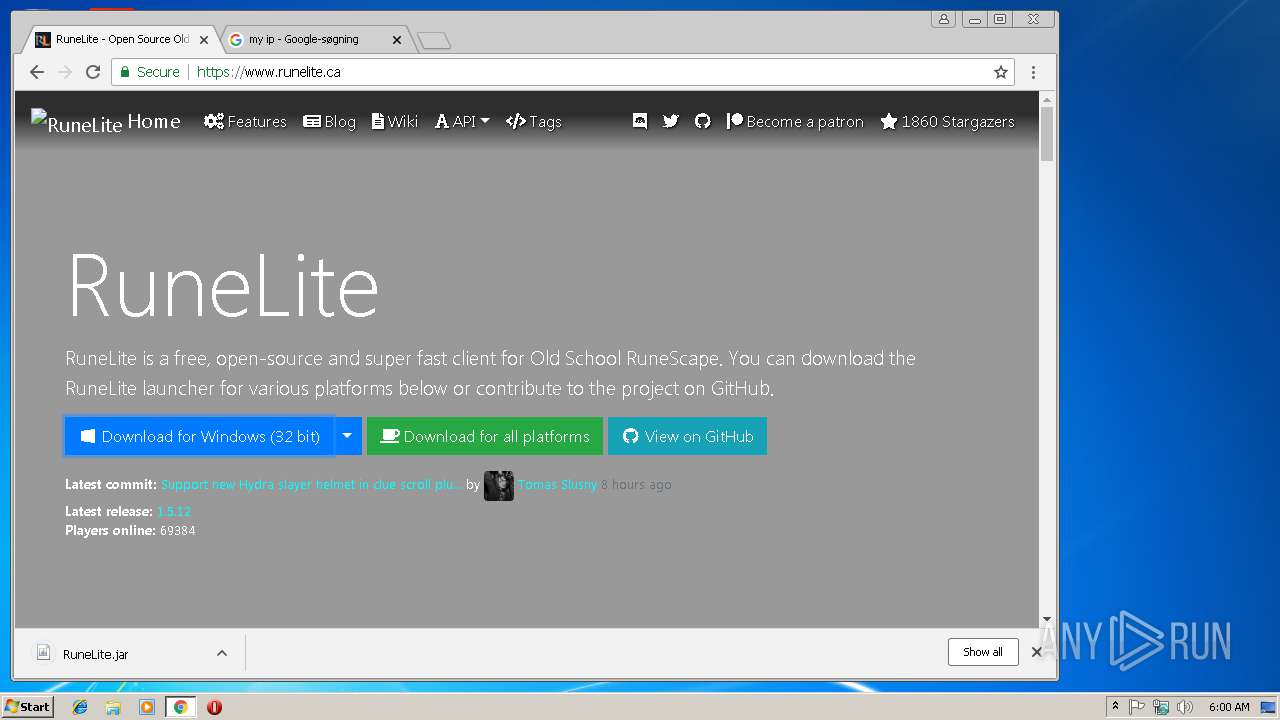
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2804 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\8efaae2b-2473-45c3-9106-3078fab0d1c8.tmp | — | |
MD5:— | SHA256:— | |||
| 2804 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2804 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2804 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\1dc3a9fe-384e-44ef-af97-ad6fe751b61c.tmp | — | |
MD5:— | SHA256:— | |||
| 2804 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 2804 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\CacheStorage\e6622492fa163609ddd4212f54512baa07929ed3\caecb3bd-7969-4305-84d6-3a376453ec73\index-dir\temp-index | — | |
MD5:— | SHA256:— | |||
| 2804 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF2481c3.TMP | text | |
MD5:— | SHA256:— | |||
| 2804 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2804 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2804 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF248202.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
62
DNS requests
36
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
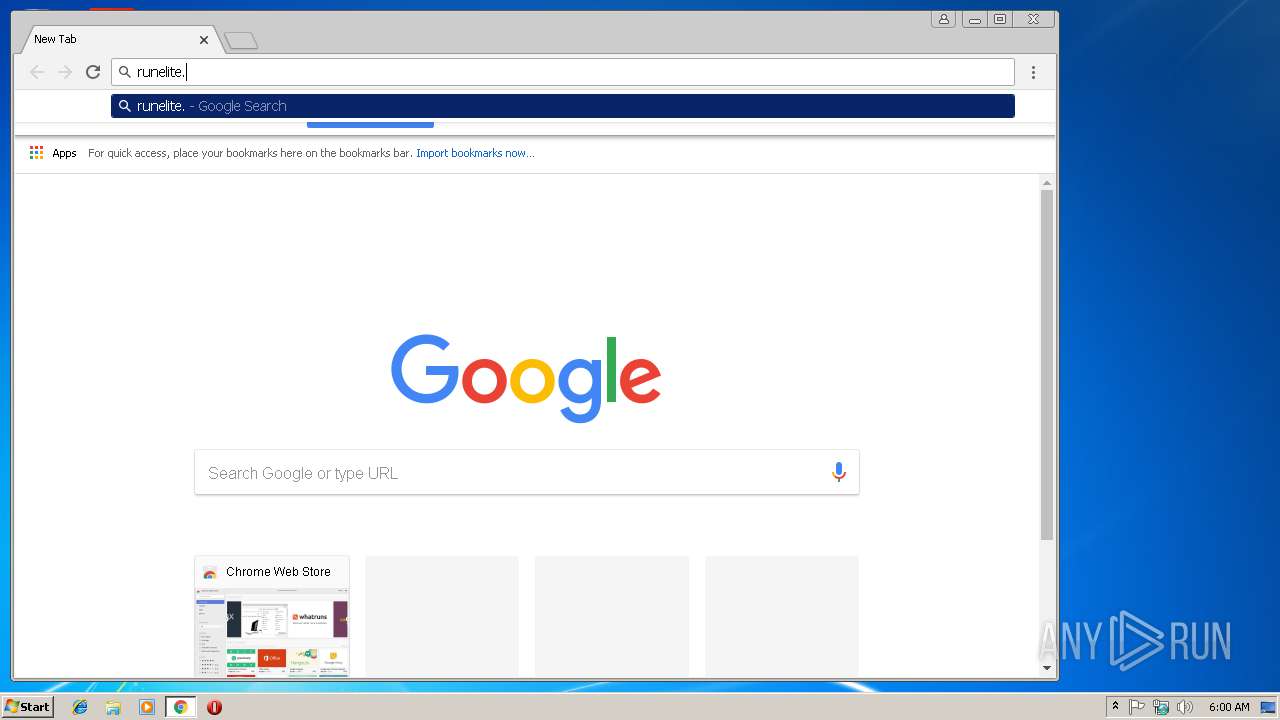
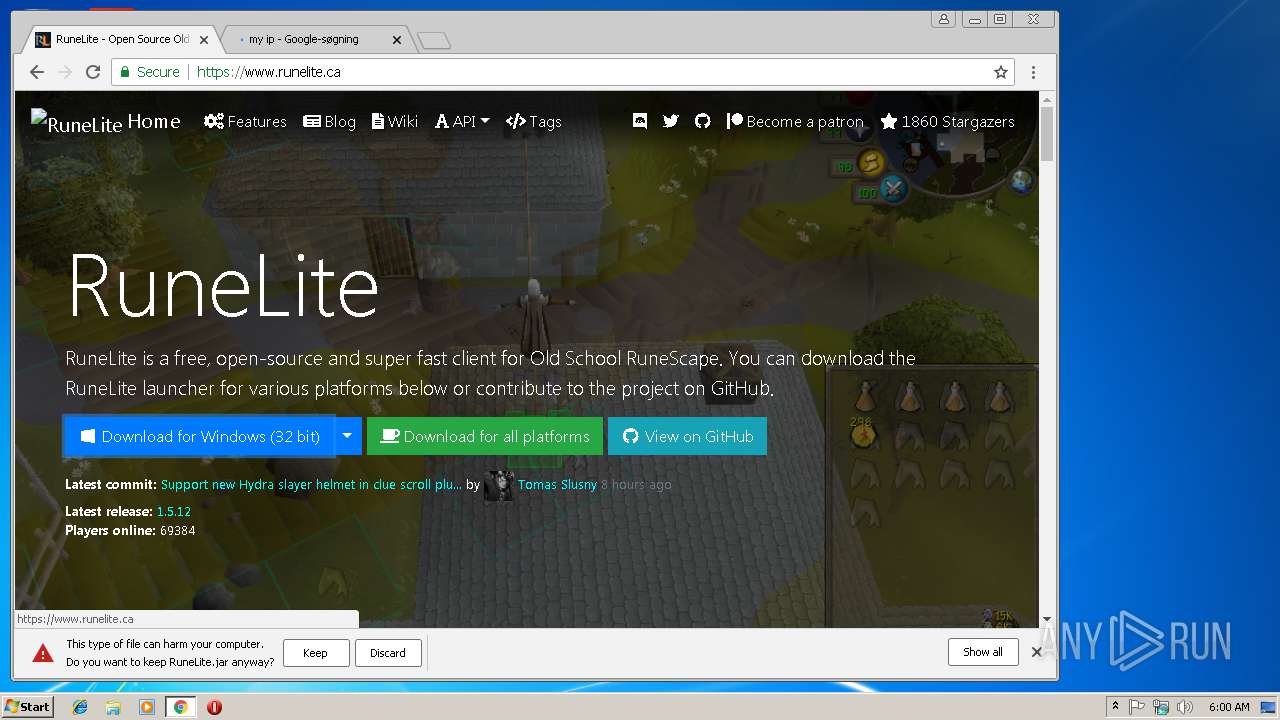
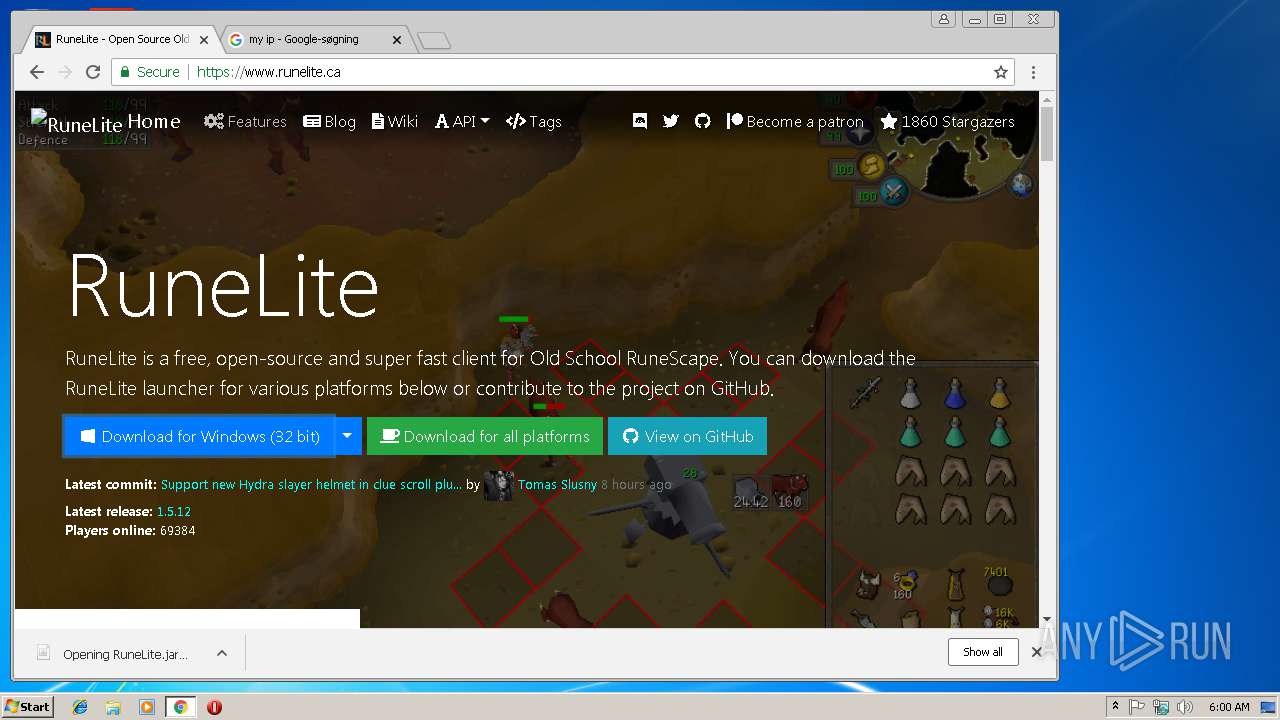
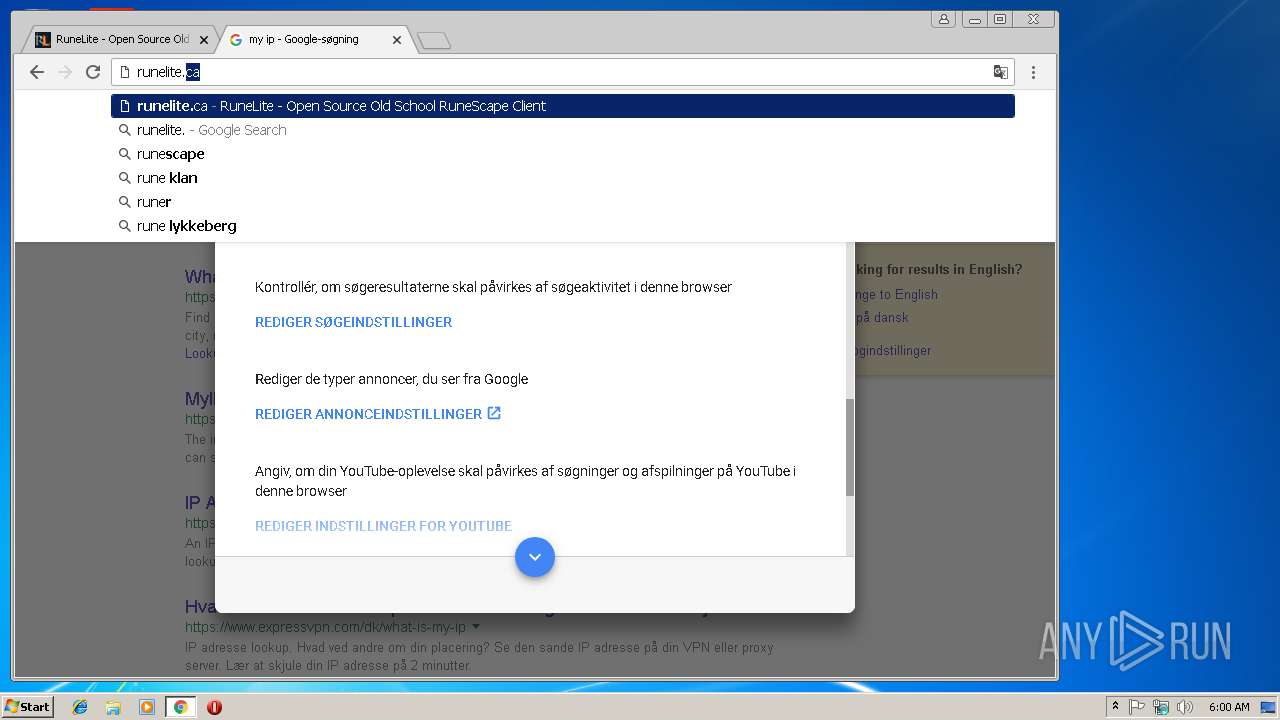
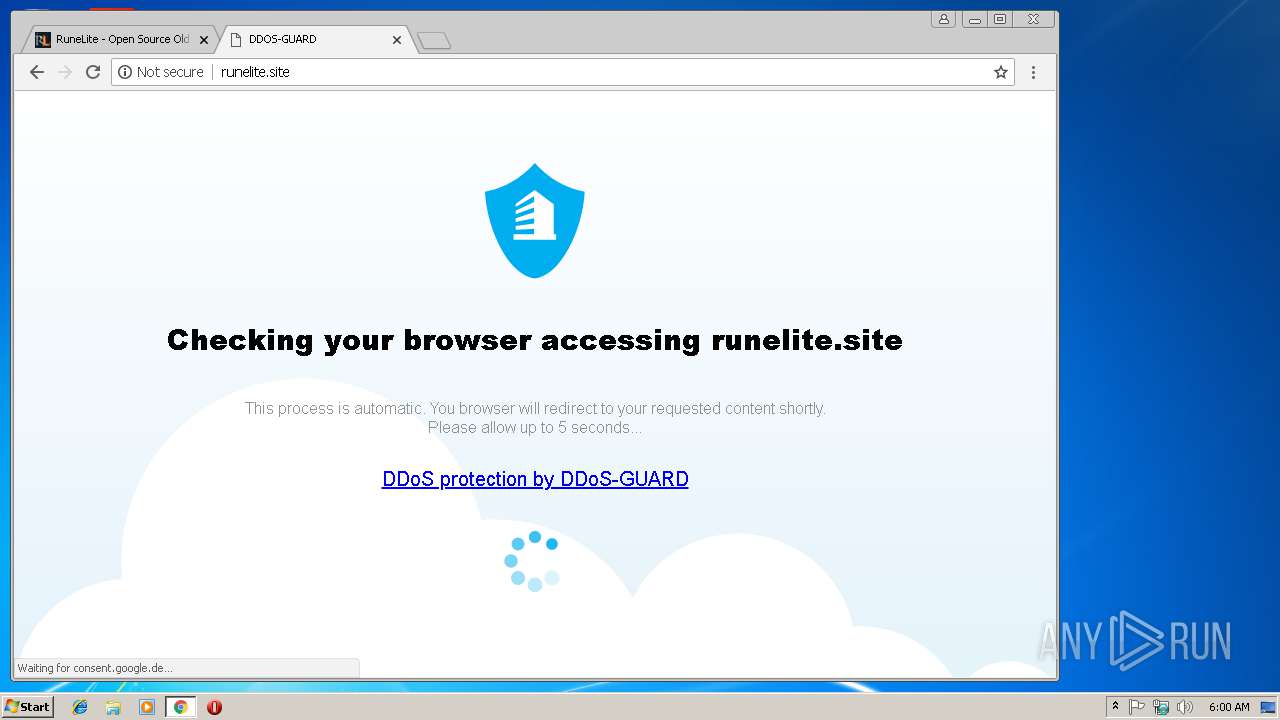
2304 | javaw.exe | GET | 403 | 185.178.208.164:80 | http://runelite.site/launcher/bootstrap.json | RU | html | 9.34 Kb | suspicious |
2092 | javaw.exe | GET | 403 | 185.178.208.164:80 | http://runelite.site/launcher/bootstrap.json | RU | html | 9.34 Kb | suspicious |
3724 | javaw.exe | GET | 403 | 185.178.208.164:80 | http://runelite.site/launcher/bootstrap.json | RU | html | 9.34 Kb | suspicious |
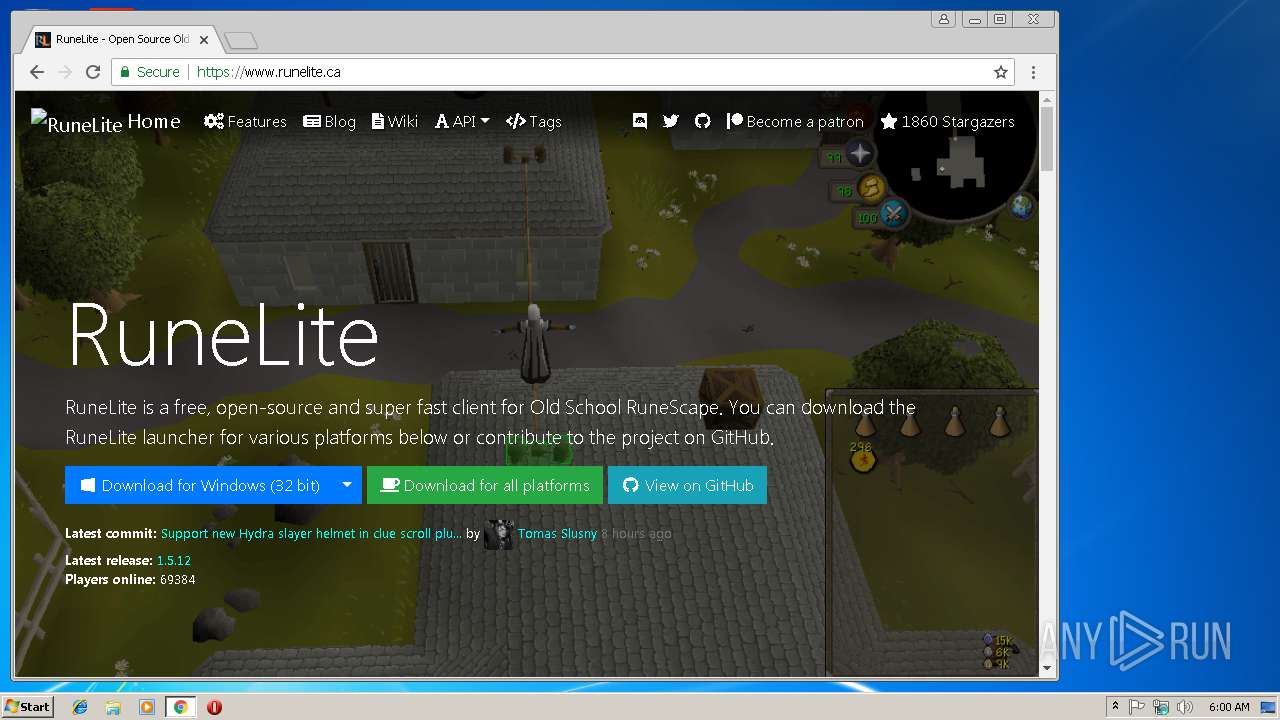
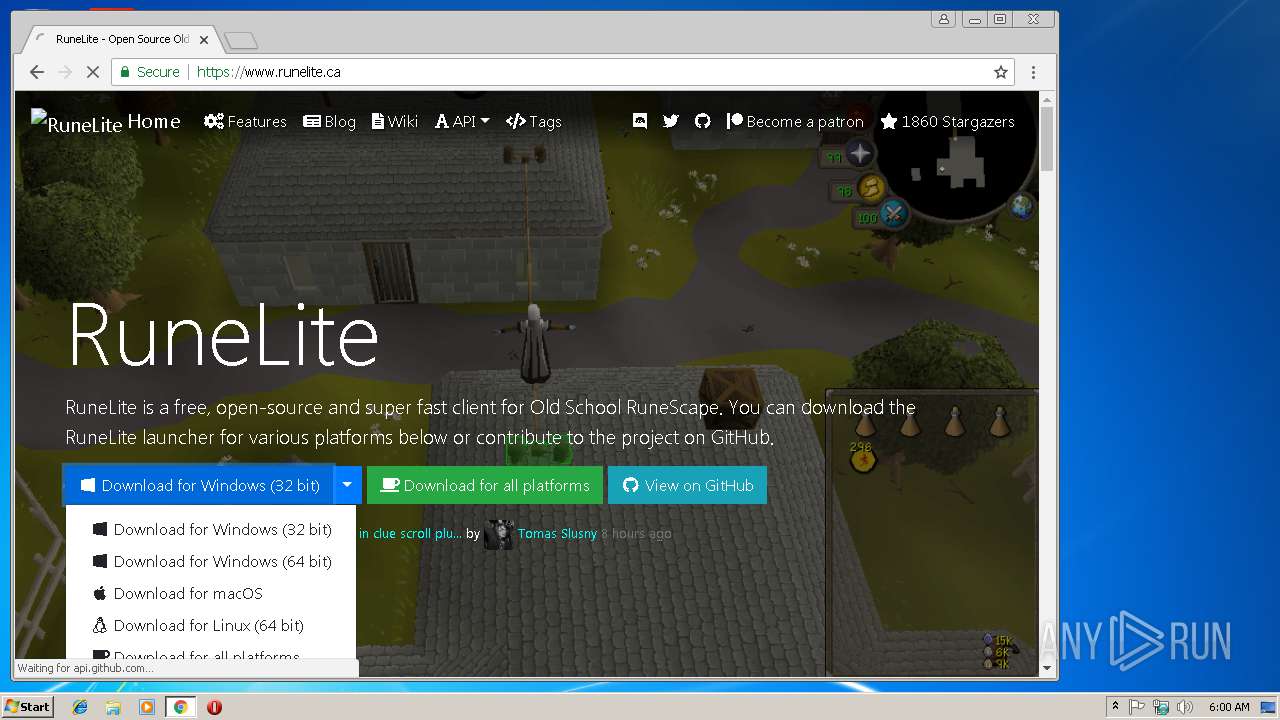
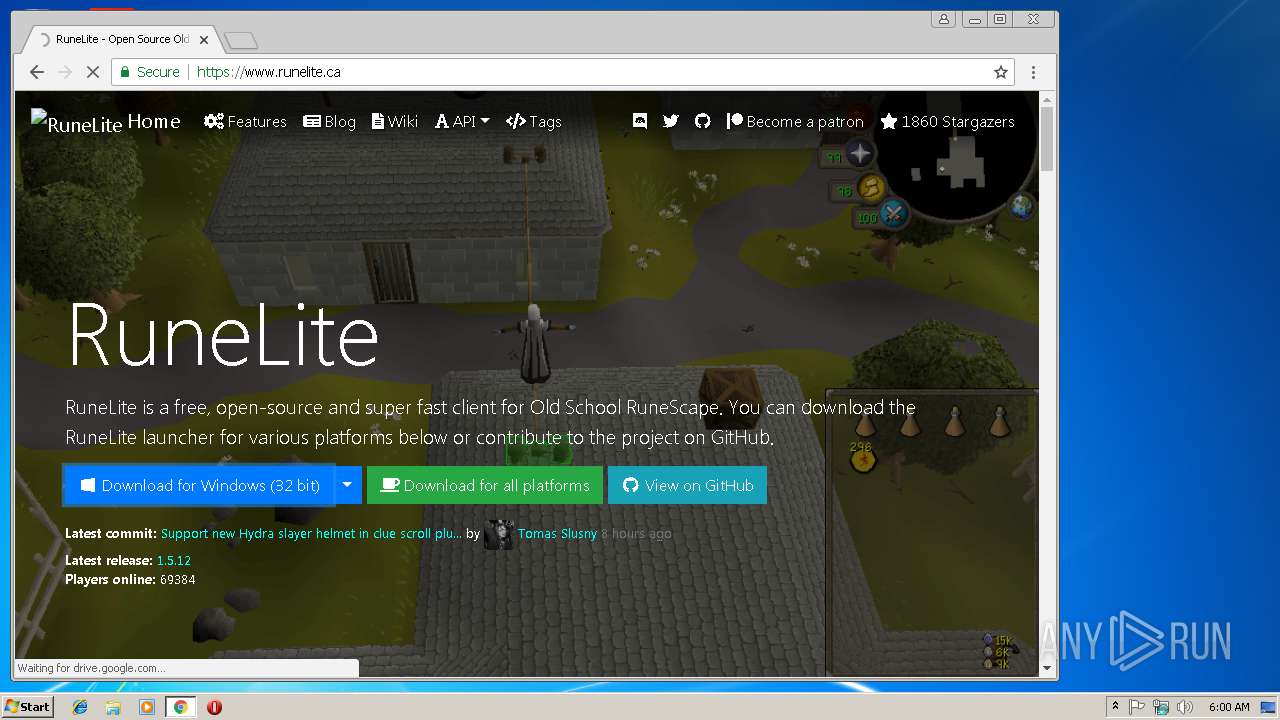
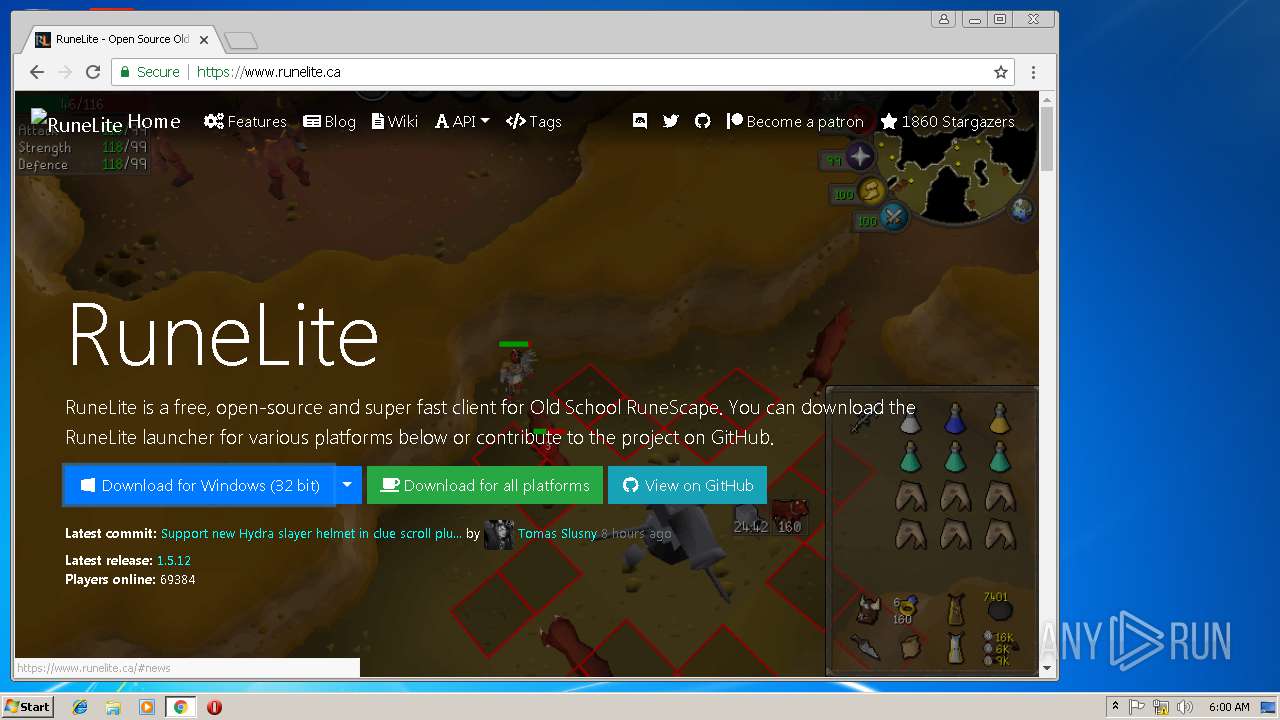
2804 | chrome.exe | GET | 301 | 104.28.26.223:80 | http://runelite.ca/ | US | html | 1.14 Kb | shared |
2804 | chrome.exe | POST | 301 | 185.129.100.99:80 | http://ddgu.ddos-guard.net/ddgu/ | RU | html | 183 b | whitelisted |
3220 | javaw.exe | GET | 403 | 185.178.208.164:80 | http://runelite.site/launcher/bootstrap.json | RU | html | 9.34 Kb | suspicious |
2804 | chrome.exe | GET | 403 | 185.178.208.164:80 | http://runelite.site/favicon.ico | RU | html | 3.22 Kb | suspicious |
2804 | chrome.exe | GET | 403 | 185.178.208.164:80 | http://runelite.site/ | RU | html | 3.22 Kb | suspicious |
2804 | chrome.exe | GET | 301 | 185.178.208.164:80 | http://runelite.site/ddgu_JQ9Xi8A/?u=Lw==&i=ODc1YjZlZWYyNmYzYWY2MTc0YzIwOTNiODdkZDJmZmMuNDI3MDM5Mzg0Mw&s=pZXSr06MnQQR9xn6A87CSbtmxt4 | RU | html | 136 b | suspicious |
2368 | javaw.exe | GET | 403 | 185.178.208.164:80 | http://runelite.site/launcher/bootstrap.json | RU | html | 9.34 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2804 | chrome.exe | 172.217.21.234:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2804 | chrome.exe | 172.217.23.164:443 | www.google.com | Google Inc. | US | whitelisted |
2804 | chrome.exe | 104.28.26.223:80 | runelite.ca | Cloudflare Inc | US | shared |
2804 | chrome.exe | 104.28.26.223:443 | runelite.ca | Cloudflare Inc | US | shared |
2804 | chrome.exe | 192.30.253.117:443 | api.github.com | GitHub, Inc. | US | shared |
2804 | chrome.exe | 151.101.2.109:443 | cdn.polyfill.io | Fastly | US | suspicious |
2804 | chrome.exe | 104.31.83.238:443 | api.runelite.net | Cloudflare Inc | US | shared |
2804 | chrome.exe | 151.101.0.133:443 | avatars3.githubusercontent.com | Fastly | US | malicious |
2804 | chrome.exe | 172.217.22.110:443 | drive.google.com | Google Inc. | US | whitelisted |
2804 | chrome.exe | 216.58.207.65:443 | doc-0c-as-docs.googleusercontent.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.gstatic.com |
| whitelisted |
www.google.de |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
runelite.ca |
| unknown |
www.runelite.ca |
| unknown |
cdn.polyfill.io |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2804 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Known External IP Lookup Service Domain in SNI |
2804 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Known External IP Lookup Service Domain in SNI |