| File name: | dm-launcher.msi |
| Full analysis: | https://app.any.run/tasks/1801045b-4ba9-404a-b335-29d1ef5bda2a |
| Verdict: | Malicious activity |
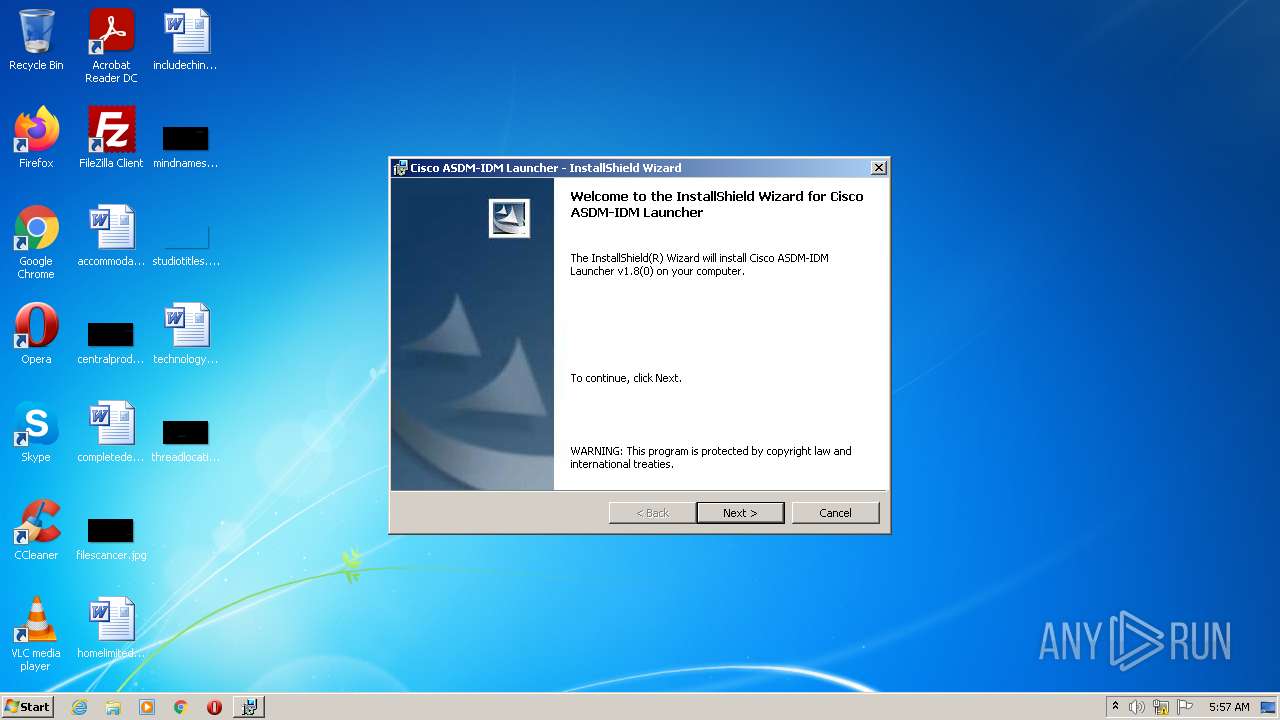
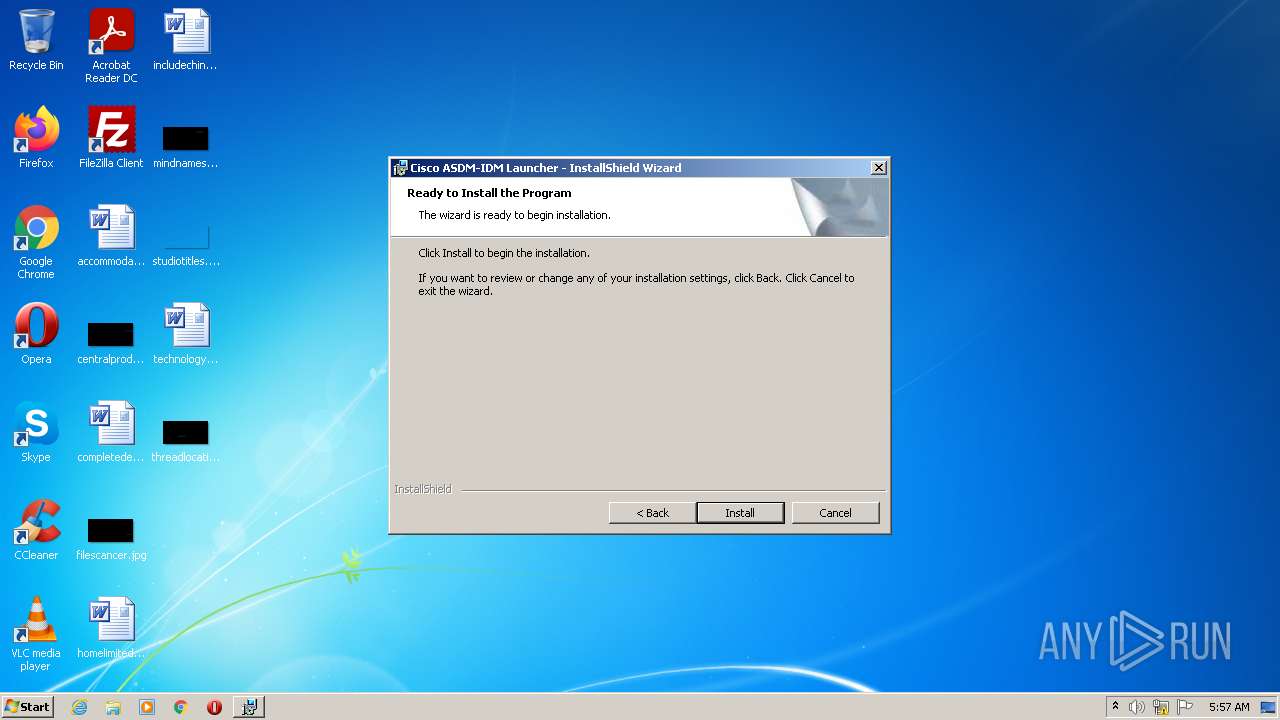
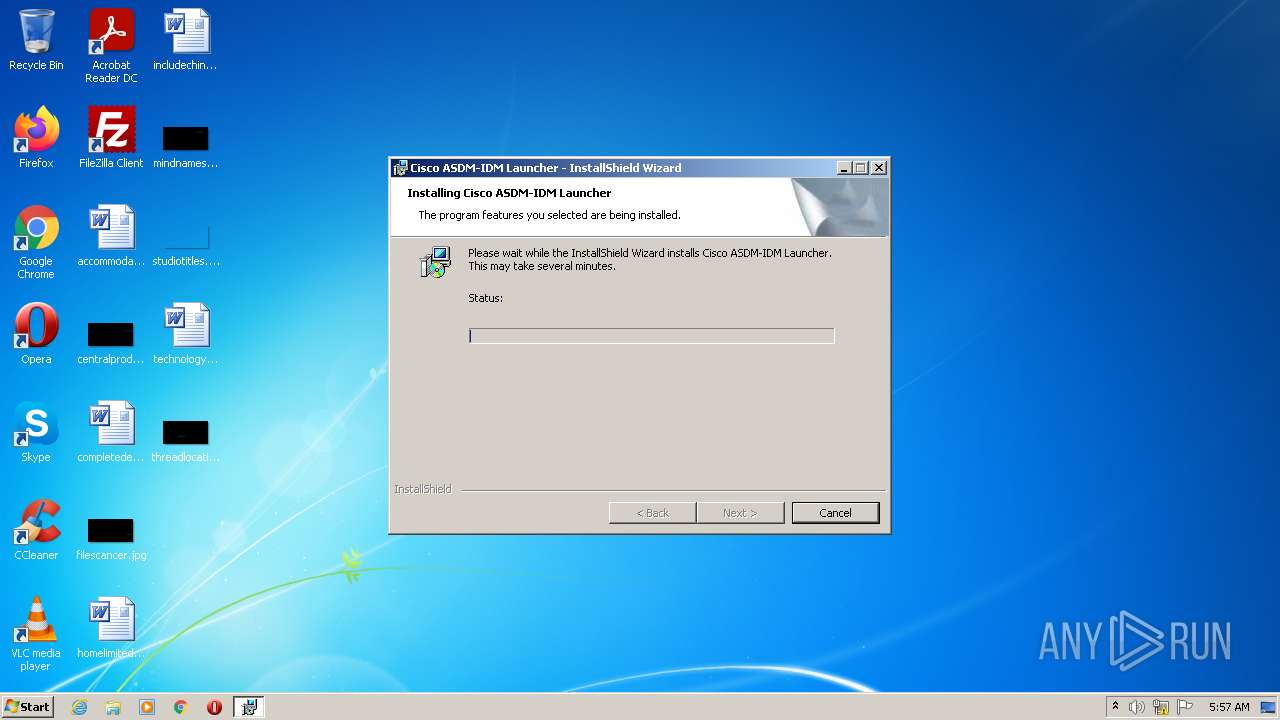
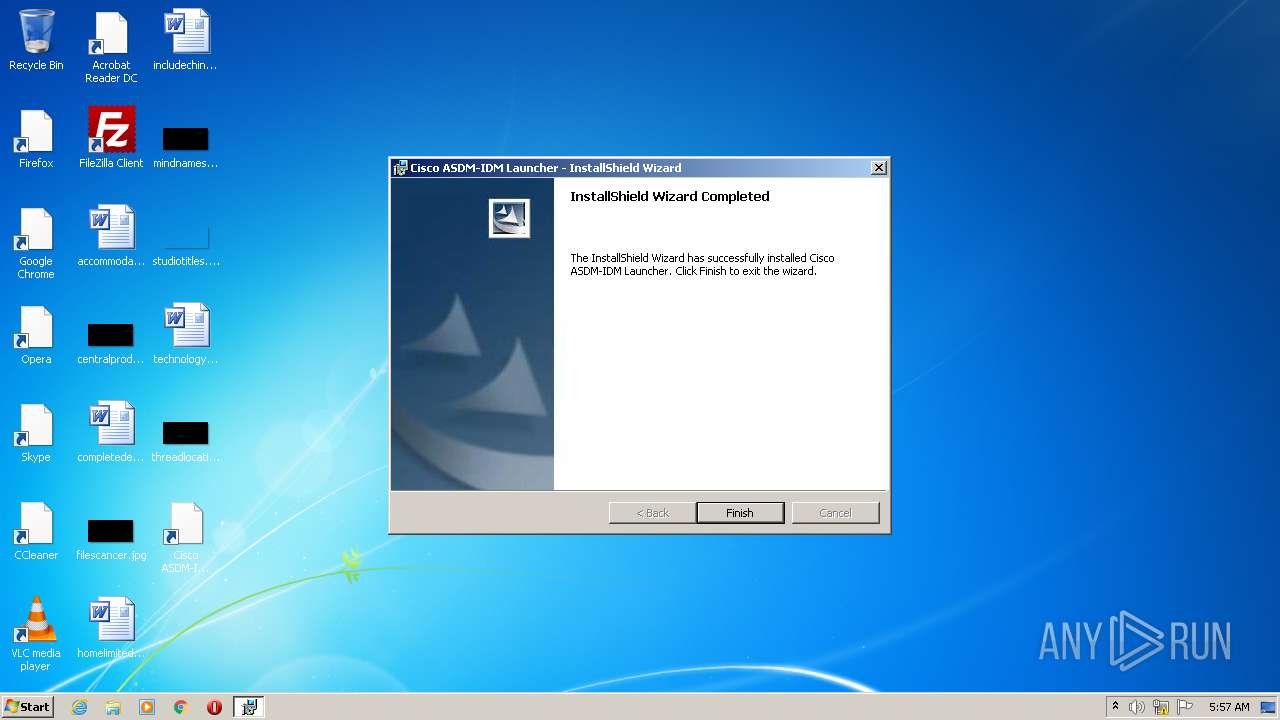
| Analysis date: | January 21, 2022, 05:57:00 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, MSI Installer, Number of Characters: 0, Last Saved By: InstallShield, Number of Words: 0, Title: Installation Database, Keywords: Installer,MSI,Database, Subject: Cisco ASDM-IDM Launcher, Author: Cisco Systems, Inc., Security: 1, Number of Pages: 200, Name of Creating Application: InstallShield 2011 - Premier Edition 17, Last Saved Time/Date: Tue Sep 20 18:27:18 2016, Create Time/Date: Tue Sep 20 18:27:18 2016, Last Printed: Tue Sep 20 18:27:18 2016, Revision Number: {05541D43-3B5F-4687-A7B9-26A01E3BEF6E}, Code page: 1252, Template: Intel;1033 |
| MD5: | 8EA862CE4946F06CB537CAFC80DB23CB |
| SHA1: | 26DF2EEEE815786B842D222ED7C1833684B6A7D6 |
| SHA256: | 62B887E44A60AD0872D7BDE19C98DA76B4F542963C347AA5B9FBABA5C619CB9D |
| SSDEEP: | 6144:g7+AwAbYMKgkMlCBvUAIrhWMTHXDCtnESCqg6GtbV3lHWOI0kpwbQHgxcdUP:g7+AwmR52cAq9XmqFvBV5QWc2cQ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executed as Windows Service
- msiexec.exe (PID: 3608)
- vssvc.exe (PID: 2300)
Reads Windows owner or organization settings
- msiexec.exe (PID: 1704)
- msiexec.exe (PID: 3608)
Reads the Windows organization settings
- msiexec.exe (PID: 1704)
- msiexec.exe (PID: 3608)
Application launched itself
- msiexec.exe (PID: 3608)
Searches for installed software
- msiexec.exe (PID: 3608)
Reads Environment values
- vssvc.exe (PID: 2300)
Creates a directory in Program Files
- msiexec.exe (PID: 3608)
Creates files in the program directory
- msiexec.exe (PID: 3608)
- javaw.exe (PID: 3704)
Creates files in the user directory
- msiexec.exe (PID: 3608)
Creates a software uninstall entry
- msiexec.exe (PID: 3608)
Executable content was dropped or overwritten
- msiexec.exe (PID: 3608)
Checks supported languages
- wscript.exe (PID: 2388)
- javaw.exe (PID: 3704)
- cmd.exe (PID: 2828)
Reads the computer name
- wscript.exe (PID: 2388)
- javaw.exe (PID: 3704)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 2388)
Executes scripts
- msiexec.exe (PID: 1704)
Check for Java to be installed
- javaw.exe (PID: 3704)
Uses ICACLS.EXE to modify access control list
- javaw.exe (PID: 3704)
INFO
Reads the computer name
- msiexec.exe (PID: 1704)
- msiexec.exe (PID: 3608)
- MsiExec.exe (PID: 3340)
- vssvc.exe (PID: 2300)
- icacls.exe (PID: 1852)
Check for Java to be installed
- msiexec.exe (PID: 1704)
Checks supported languages
- msiexec.exe (PID: 1704)
- msiexec.exe (PID: 3608)
- vssvc.exe (PID: 2300)
- MsiExec.exe (PID: 3340)
- icacls.exe (PID: 1852)
Checks Windows Trust Settings
- wscript.exe (PID: 2388)
Reads settings of System Certificates
- javaw.exe (PID: 3704)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (88.6) |
|---|---|---|
| .mst | | | Windows SDK Setup Transform Script (10) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| Template: | Intel;1033 |
|---|---|
| CodePage: | Windows Latin 1 (Western European) |
| RevisionNumber: | {05541D43-3B5F-4687-A7B9-26A01E3BEF6E} |
| LastPrinted: | 2016:09:20 17:27:18 |
| CreateDate: | 2016:09:20 17:27:18 |
| ModifyDate: | 2016:09:20 17:27:18 |
| Software: | InstallShield? 2011 - Premier Edition 17 |
| Pages: | 200 |
| Security: | Password protected |
| Author: | Cisco Systems, Inc. |
| Subject: | Cisco ASDM-IDM Launcher |
| Keywords: | Installer,MSI,Database |
| Comments: | - |
| Title: | Installation Database |
| Words: | - |
| LastModifiedBy: | InstallShield |
| Characters: | - |
Total processes
47
Monitored processes
8
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1704 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\dm-launcher.msi" | C:\Windows\System32\msiexec.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1852 | C:\Windows\system32\icacls.exe C:\ProgramData\Oracle\Java\.oracle_jre_usage /grant "everyone":(OI)(CI)M | C:\Windows\system32\icacls.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2300 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft� Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2388 | C:\Windows\System32\wscript.exe invisible.vbs run.bat | C:\Windows\System32\wscript.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft � Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2828 | C:\Windows\system32\cmd.exe /c ""C:\Program Files\Cisco Systems\ASDM\run.bat" " | C:\Windows\system32\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3340 | C:\Windows\system32\MsiExec.exe -Embedding 7133E9A0A8D0B7C2A41281CF852057D4 C | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3608 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
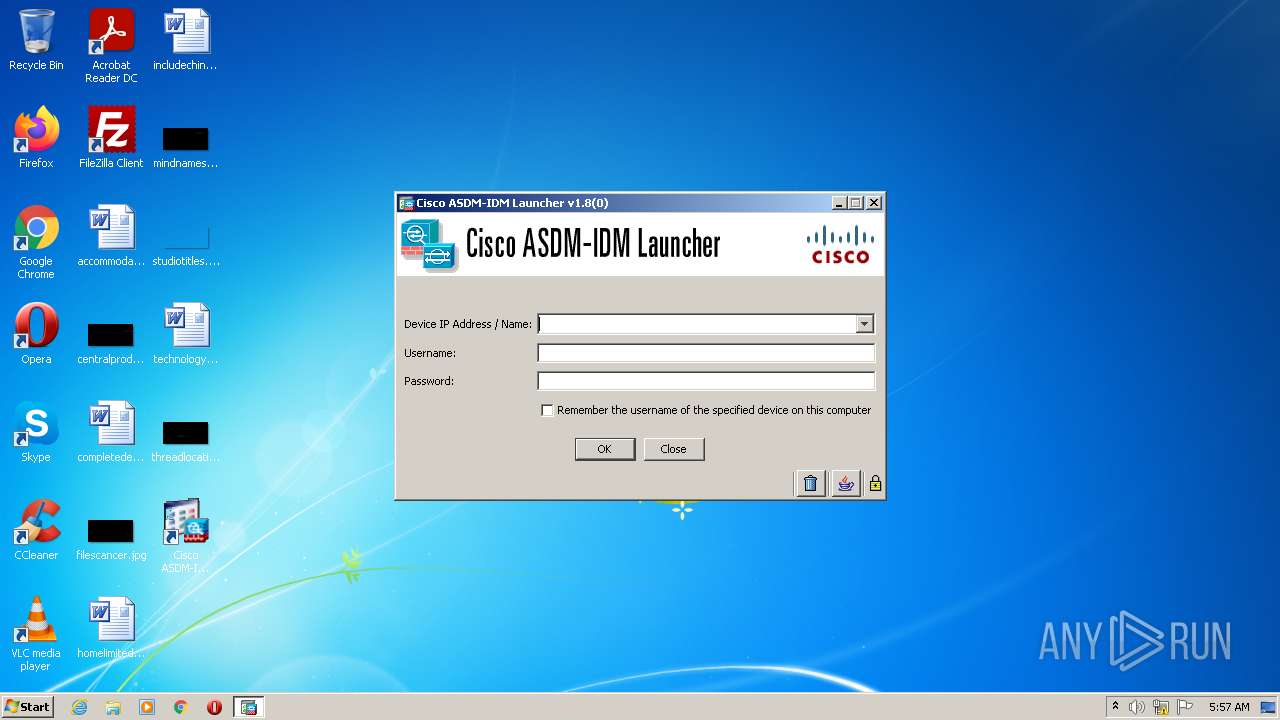
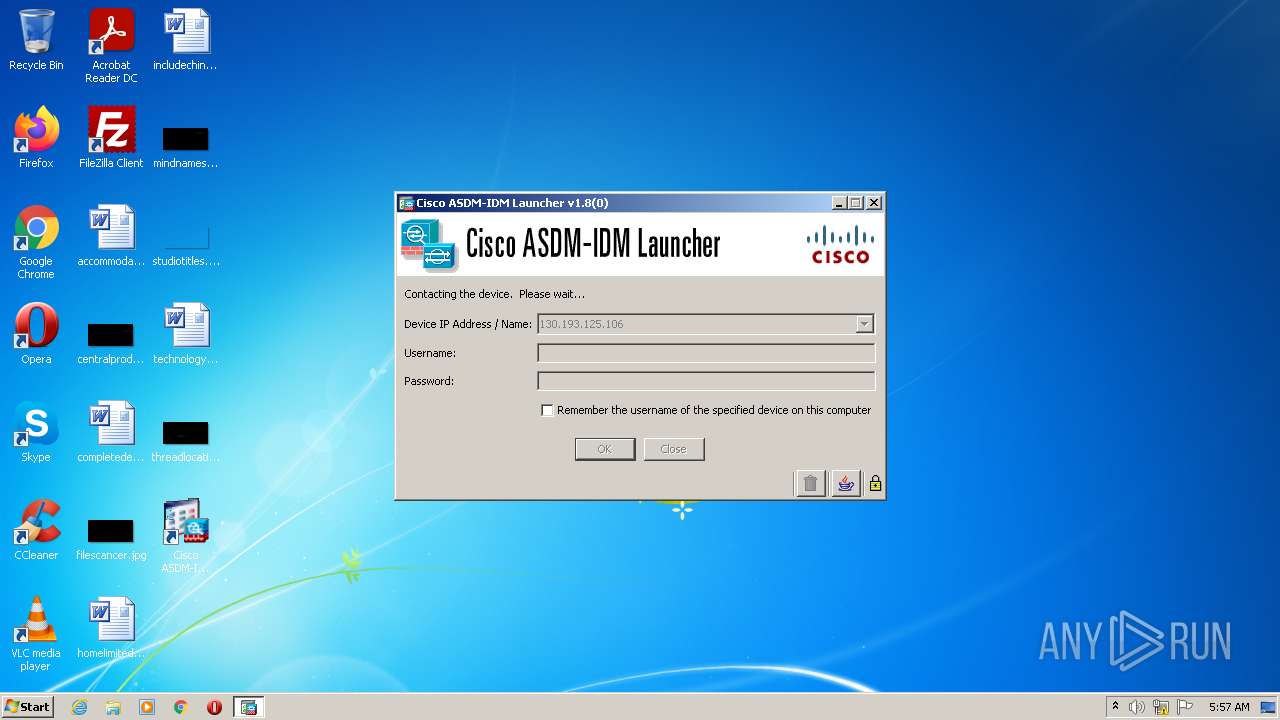
| 3704 | javaw.exe -Xms64m -Xmx512m -Dsun.swing.enableImprovedDragGesture=true -classpath lzma.jar;jploader.jar;asdm-launcher.jar;retroweaver-rt-2.0.jar com.cisco.launcher.Launcher | C:\Program Files\Common Files\Oracle\Java\javapath\javaw.exe | cmd.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.2710.9 Modules
| |||||||||||||||
Total events
9 507
Read events
9 207
Write events
286
Delete events
14
Modification events
| (PID) Process: | (3608) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4000000000000000101F38BB8B0ED801180E0000900B0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3608) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4000000000000000101F38BB8B0ED801180E0000900B0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3608) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 69 | |||
| (PID) Process: | (3608) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 400000000000000042437DBB8B0ED801180E0000900B0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3608) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000009CA57FBB8B0ED801180E0000C0050000E80300000100000000000000000000000A12A0940488EA469E852772052405670000000000000000 | |||
| (PID) Process: | (2300) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000005E918BBB8B0ED801FC08000028080000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2300) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000B8F38DBB8B0ED801FC080000C8020000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2300) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000B8F38DBB8B0ED801FC080000480C0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2300) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000B8F38DBB8B0ED801FC080000200F0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2300) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 4000000000000000125690BB8B0ED801FC080000480C0000E8030000000000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
7
Suspicious files
11
Text files
9
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3608 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 3608 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{94a0120a-8804-46ea-9e85-277205240567}_OnDiskSnapshotProp | binary | |
MD5:— | SHA256:— | |||
| 3608 | msiexec.exe | C:\Program Files\Cisco Systems\ASDM\asdm-launcher.jar | compressed | |
MD5:— | SHA256:— | |||
| 3608 | msiexec.exe | C:\Program Files\Cisco Systems\ASDM\run.bat | text | |
MD5:— | SHA256:— | |||
| 3608 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF90D80E98019705AC.TMP | gmc | |
MD5:— | SHA256:— | |||
| 3608 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:— | SHA256:— | |||
| 3608 | msiexec.exe | C:\Windows\Installer\MSI1868.tmp | binary | |
MD5:— | SHA256:— | |||
| 3608 | msiexec.exe | C:\Program Files\Cisco Systems\ASDM\lzma.jar | compressed | |
MD5:A0D9BEA88DE2FF4CEB53766F83C5C360 | SHA256:1B7A9654DADBBA978598970227C56A3B1AB18965D7925271BC05DD3ACE159689 | |||
| 3608 | msiexec.exe | C:\Program Files\Cisco Systems\ASDM\jploader.jar | compressed | |
MD5:— | SHA256:— | |||
| 3608 | msiexec.exe | C:\Windows\Installer\1414ee.msi | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
7
DNS requests
2
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3704 | javaw.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3704 | javaw.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 727 b | whitelisted |
3704 | javaw.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 727 b | whitelisted |
3704 | javaw.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
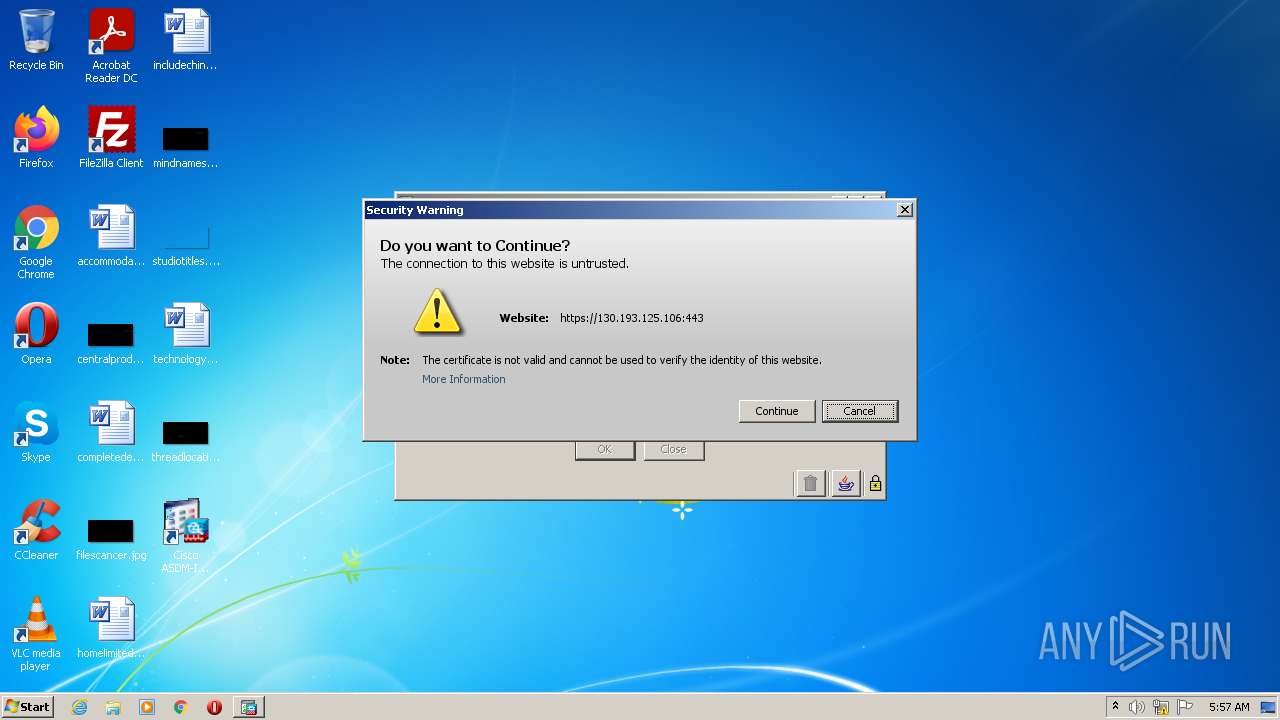
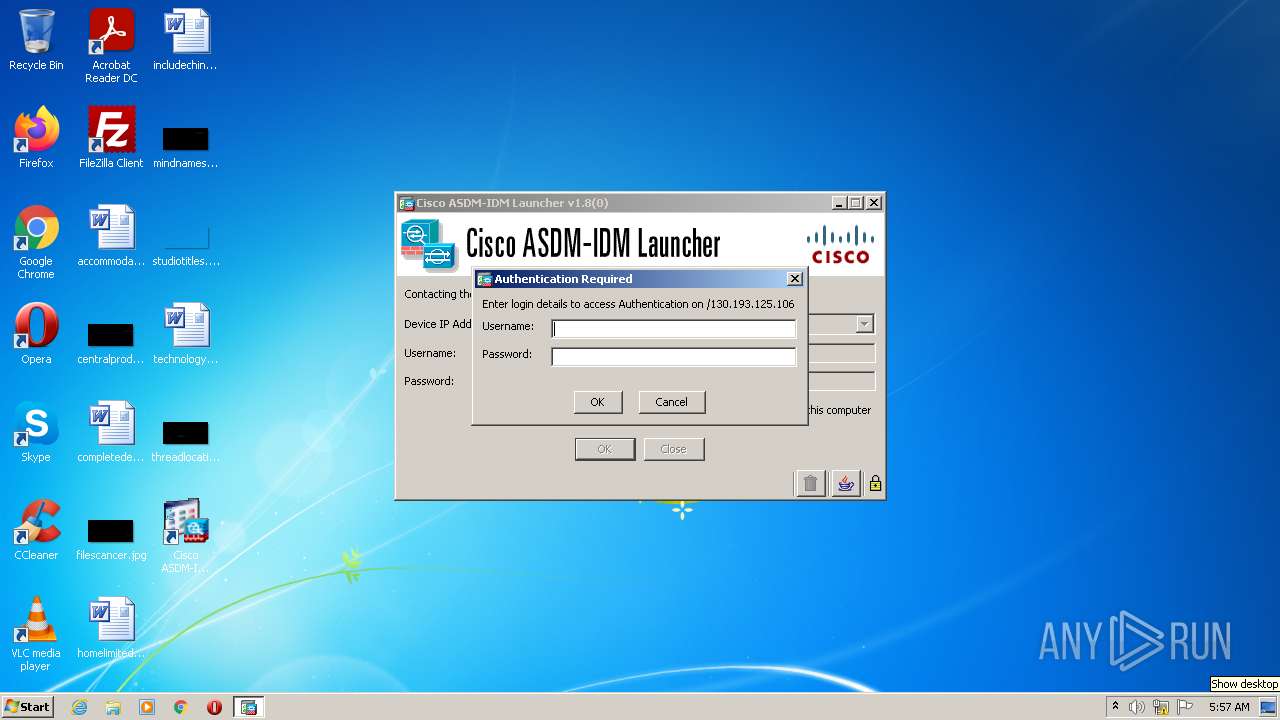
3704 | javaw.exe | 130.193.125.106:443 | — | GNC-Alfa CJSC | AM | unknown |
3704 | javaw.exe | 104.92.97.147:443 | javadl-esd-secure.oracle.com | Akamai Technologies, Inc. | NL | suspicious |
— | — | 130.193.125.106:443 | — | GNC-Alfa CJSC | AM | unknown |
3704 | javaw.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
javadl-esd-secure.oracle.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3704 | javaw.exe | Potentially Bad Traffic | ET POLICY Vulnerable Java Version 1.8.x Detected |
3704 | javaw.exe | Potentially Bad Traffic | ET POLICY Vulnerable Java Version 1.8.x Detected |