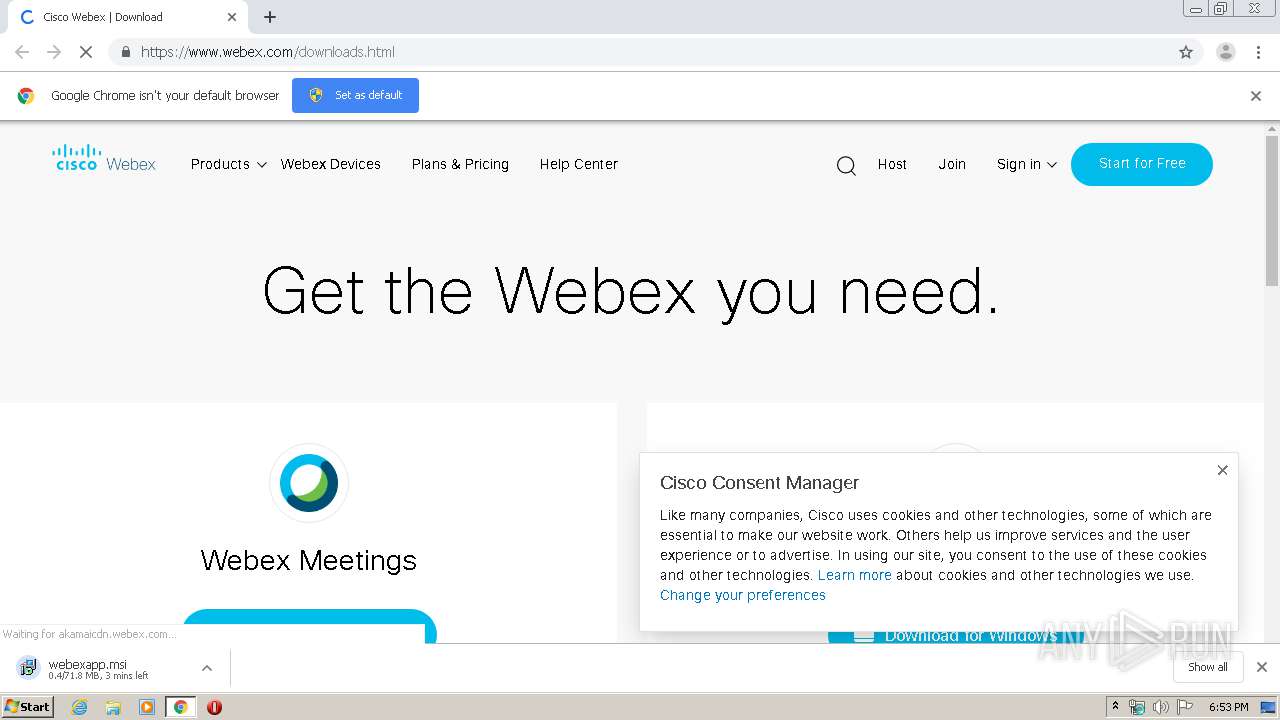
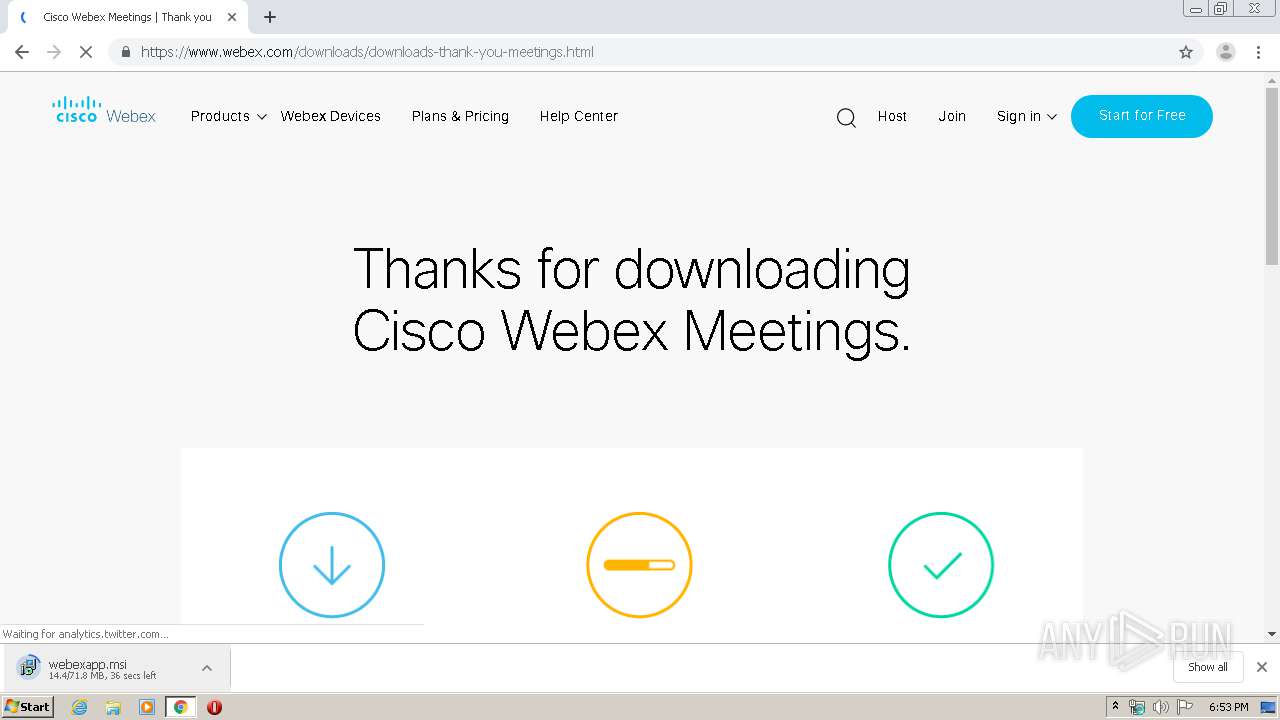
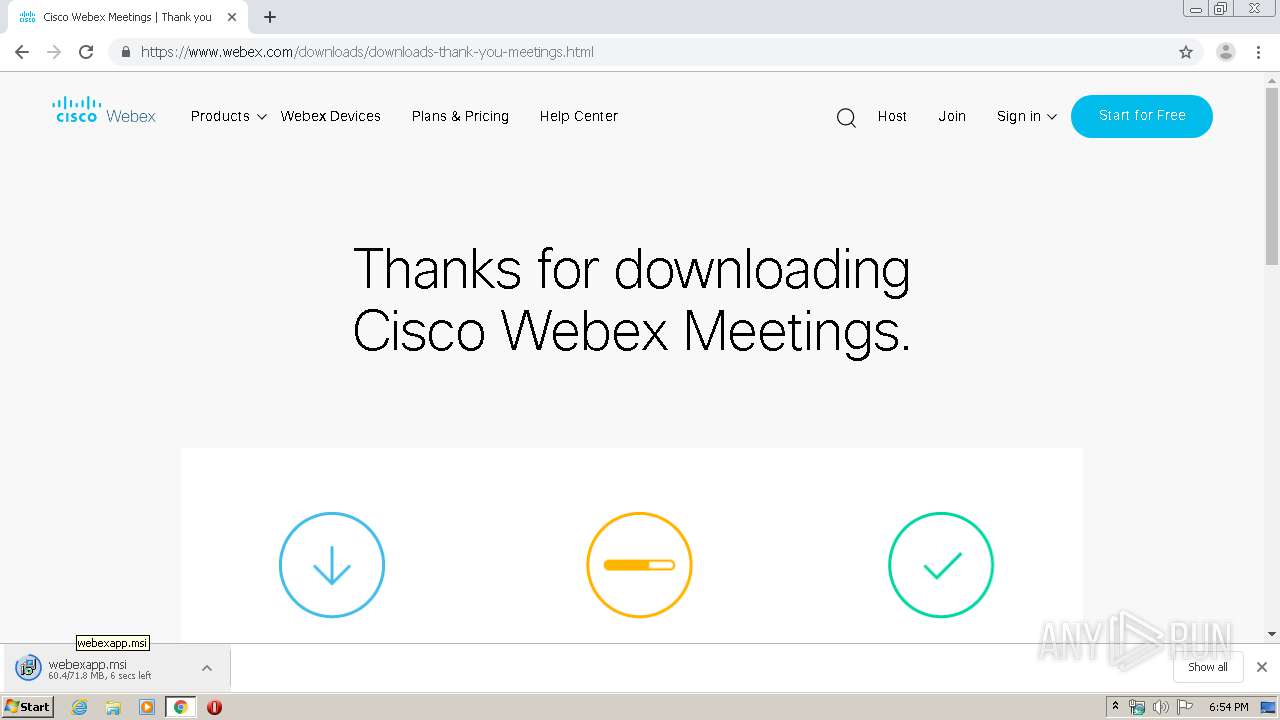
| URL: | https://www.webex.com/downloads.html |
| Full analysis: | https://app.any.run/tasks/502a5735-388b-4851-8121-96546e7c7c06 |
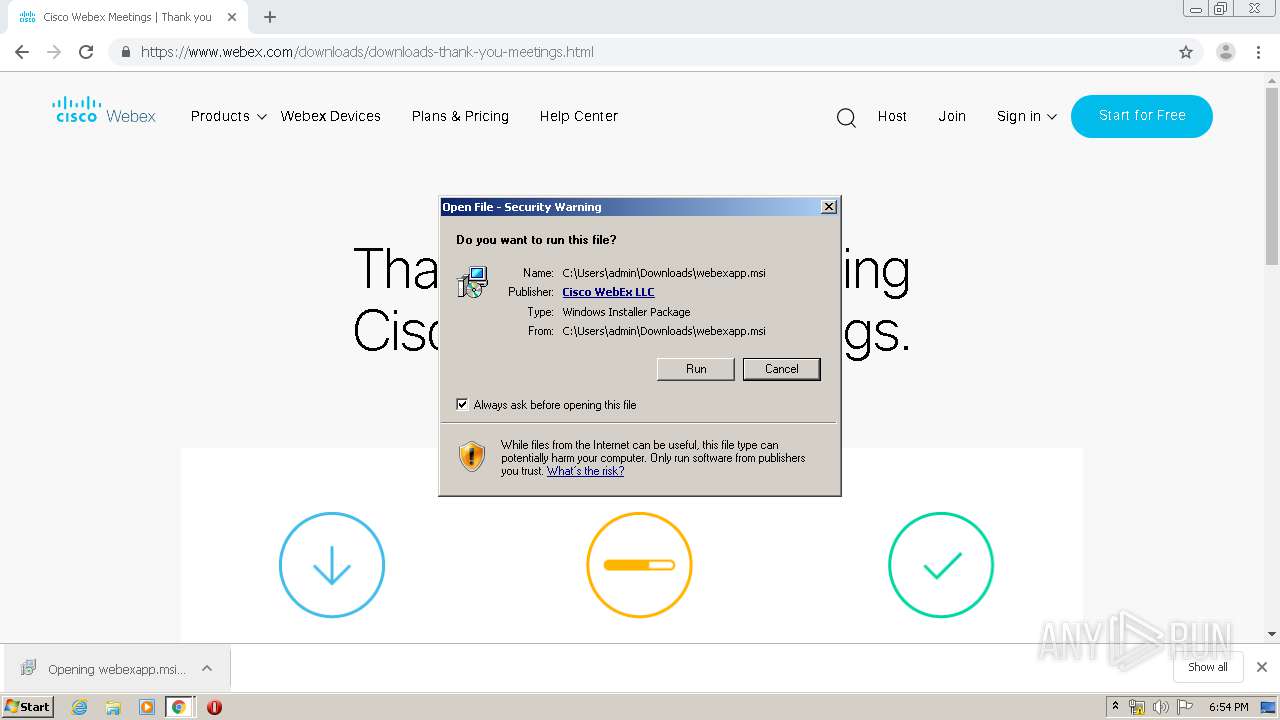
| Verdict: | Malicious activity |
| Analysis date: | February 06, 2020, 18:53:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 1FF110EA2F895FCB1274A91C01DBED0A |
| SHA1: | 0EA09610B57B165EDCF0663F0D66296B22352E2D |
| SHA256: | 62B1F51B95F16B12D3E15C396EAD541214C18BB2F6668A91CFA281A05328C579 |
| SSDEEP: | 3:N8DSLUhKXLQ:2OLUcs |
MALICIOUS
Application was dropped or rewritten from another process
- ptOIEx.exe (PID: 3412)
- ptsrv.exe (PID: 1516)
- ptWbxONI.exe (PID: 3956)
- webex.exe (PID: 780)
- CiscoWebExStart.exe (PID: 3048)
- WbxDLInst.exe (PID: 3500)
- WbxDLDrv.exe (PID: 4076)
Loads dropped or rewritten executable
- ptWbxONI.exe (PID: 3956)
- ptsrv.exe (PID: 1516)
- WbxDLInst.exe (PID: 3500)
- WbxDLDrv.exe (PID: 4076)
- ptOIEx.exe (PID: 3412)
- spoolsv.exe (PID: 1188)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3144)
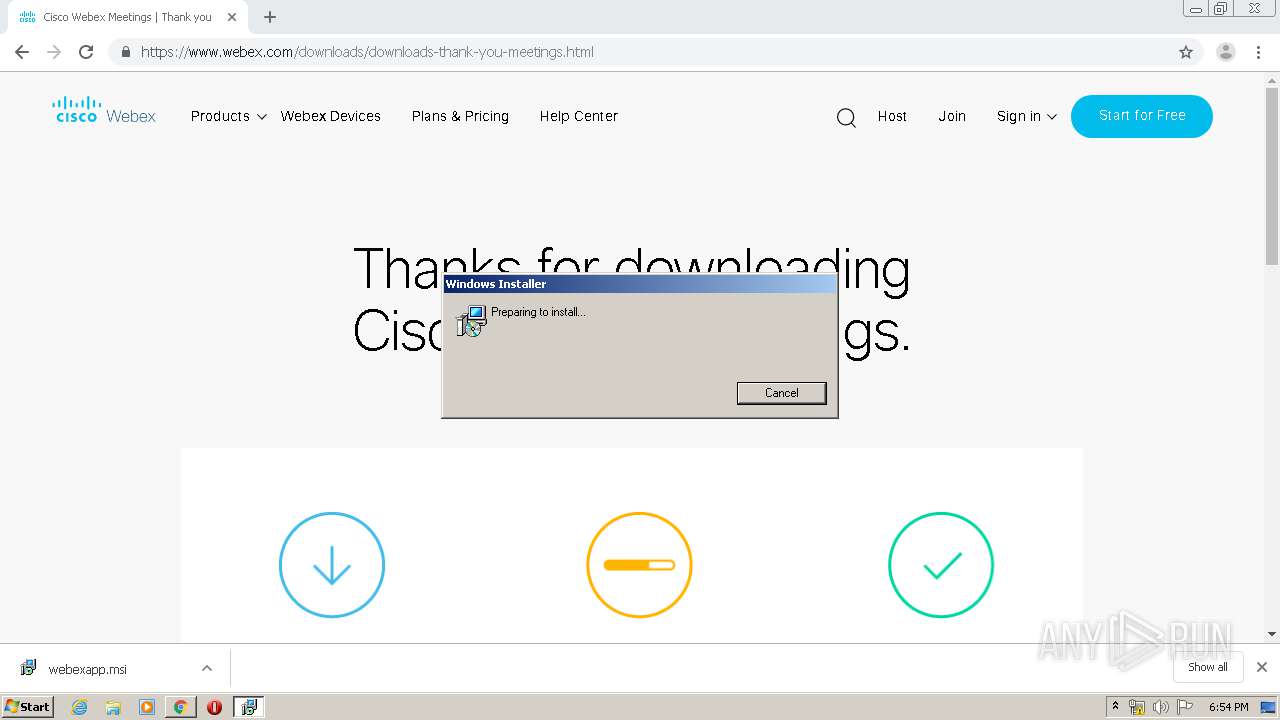
Starts Microsoft Installer
- chrome.exe (PID: 3144)
Executed as Windows Service
- vssvc.exe (PID: 2484)
Executable content was dropped or overwritten
- msiexec.exe (PID: 2792)
- WbxDLInst.exe (PID: 3500)
- spoolsv.exe (PID: 1188)
- msiexec.exe (PID: 2900)
- MsiExec.exe (PID: 2160)
Creates COM task schedule object
- msiexec.exe (PID: 2900)
Removes files from Windows directory
- WbxDLDrv.exe (PID: 4076)
- spoolsv.exe (PID: 1188)
Modifies the open verb of a shell class
- CiscoWebExStart.exe (PID: 3048)
- MsiExec.exe (PID: 2160)
- webex.exe (PID: 780)
Creates files in the program directory
- WbxDLInst.exe (PID: 3500)
- CiscoWebExStart.exe (PID: 3048)
- ptWbxONI.exe (PID: 3956)
Creates files in the Windows directory
- spoolsv.exe (PID: 1188)
- WbxDLDrv.exe (PID: 4076)
INFO
Application launched itself
- chrome.exe (PID: 3144)
- msiexec.exe (PID: 2900)
Reads the hosts file
- chrome.exe (PID: 2724)
- chrome.exe (PID: 3144)
Reads settings of System Certificates
- chrome.exe (PID: 3144)
- chrome.exe (PID: 2724)
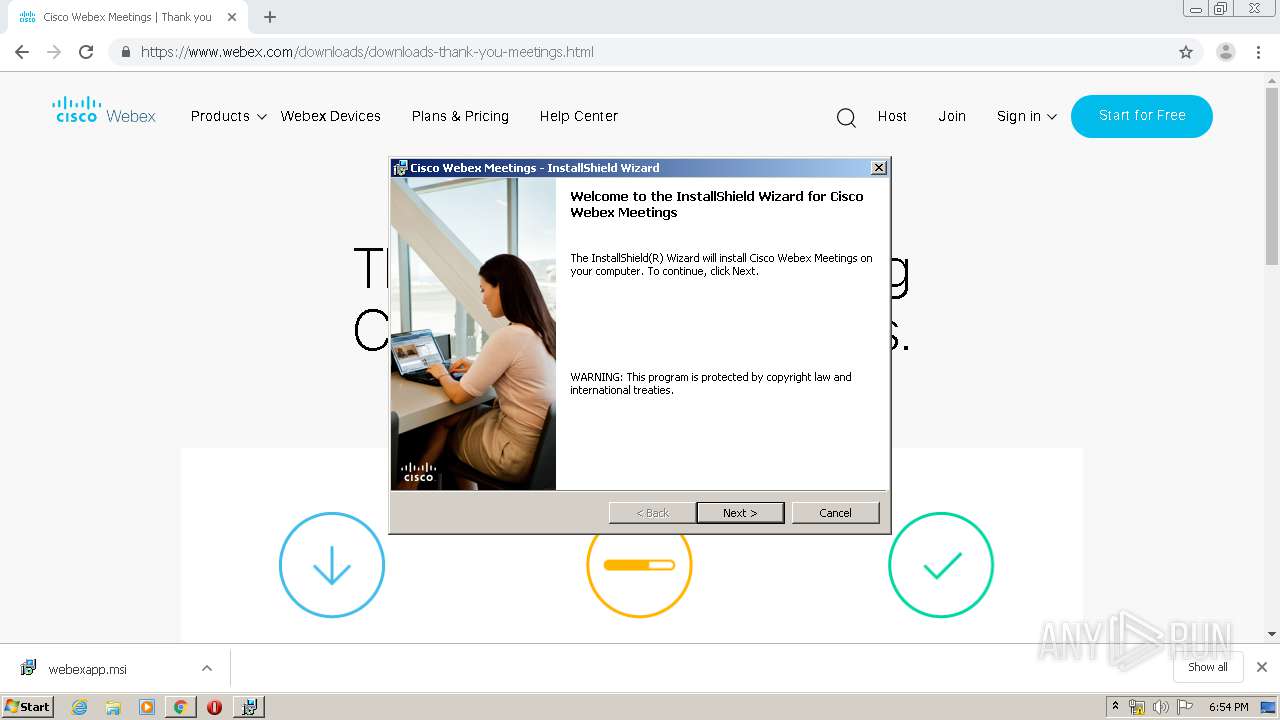
Searches for installed software
- msiexec.exe (PID: 2900)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2160)
- MsiExec.exe (PID: 2812)
- MsiExec.exe (PID: 3024)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2484)
Reads Internet Cache Settings
- chrome.exe (PID: 3144)
Dropped object may contain Bitcoin addresses
- msiexec.exe (PID: 2900)
Creates a software uninstall entry
- msiexec.exe (PID: 2900)
Creates files in the program directory
- msiexec.exe (PID: 2900)
- MsiExec.exe (PID: 2160)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
84
Monitored processes
47
Malicious processes
8
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 780 | webex.exe /registerall | C:\Program Files\Webex\webex.exe | MsiExec.exe | ||||||||||||
User: SYSTEM Company: Cisco Webex LLC Integrity Level: SYSTEM Description: Cisco Webex Meeting Exit code: 1 Version: 10050,1,2020,0131 Modules
| |||||||||||||||
| 1092 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,8089408637081907420,4871026662220011763,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3778034261683678059 --mojo-platform-channel-handle=4732 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,8089408637081907420,4871026662220011763,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4536225120925577248 --mojo-platform-channel-handle=5208 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,8089408637081907420,4871026662220011763,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10486215320815425220 --mojo-platform-channel-handle=1064 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1188 | C:\Windows\System32\spoolsv.exe | C:\Windows\System32\spoolsv.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Spooler SubSystem App Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1516 | "C:\PROGRA~1\Webex\Webex\APPLIC~1\ptsrv.exe" /RegServer | C:\PROGRA~1\Webex\Webex\APPLIC~1\ptsrv.exe | MsiExec.exe | ||||||||||||
User: SYSTEM Company: Cisco WebEx LLC Integrity Level: SYSTEM Description: Cisco Webex Meetings App Service Exit code: 0 Version: 4001,0,1912,1600 Modules
| |||||||||||||||
| 1520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,8089408637081907420,4871026662220011763,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12003943736338558075 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3728 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,8089408637081907420,4871026662220011763,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6285912149065815337 --mojo-platform-channel-handle=3248 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2160 | C:\Windows\system32\MsiExec.exe -Embedding DC03AA5391D1DCA71CD91AADAB03F4A0 M Global\MSI0000 | C:\Windows\system32\MsiExec.exe | msiexec.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2312 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,8089408637081907420,4871026662220011763,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17210737395157895354 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3780 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 853
Read events
1 758
Write events
1 050
Delete events
45
Modification events
| (PID) Process: | (3144) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3144) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3144) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3144) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3144) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2960) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3144-13225488799999125 |
Value: 259 | |||
| (PID) Process: | (3144) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3144) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3144) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (3144) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
382
Suspicious files
167
Text files
251
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E3C60A0-C48.pma | — | |
MD5:— | SHA256:— | |||
| 3144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\1e184de8-0a11-4f93-9954-bb497ab73b71.tmp | — | |
MD5:— | SHA256:— | |||
| 3144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFa66d87.TMP | text | |
MD5:— | SHA256:— | |||
| 3144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFa66d87.TMP | text | |
MD5:— | SHA256:— | |||
| 3144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3144 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa67017.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
108
DNS requests
64
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2724 | chrome.exe | GET | 302 | 172.217.21.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 517 b | whitelisted |
2724 | chrome.exe | GET | 302 | 172.217.21.238:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 522 b | whitelisted |
2724 | chrome.exe | GET | 200 | 159.148.69.143:80 | http://r4---sn-a5uoxu-gpme.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=159.148.186.246&mm=28&mn=sn-a5uoxu-gpme&ms=nvh&mt=1581014796&mv=u&mvi=3&pl=24&shardbypass=yes | LV | crx | 293 Kb | whitelisted |
2724 | chrome.exe | GET | 200 | 159.148.69.142:80 | http://r3---sn-a5uoxu-gpme.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=159.148.186.246&mm=28&mn=sn-a5uoxu-gpme&ms=nvh&mt=1581014796&mv=u&mvi=2&pl=24&shardbypass=yes | LV | crx | 862 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2724 | chrome.exe | 35.181.91.36:443 | smetrics.webex.com | — | CA | suspicious |
2724 | chrome.exe | 172.217.21.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2724 | chrome.exe | 104.109.56.133:443 | www.webex.com | Akamai International B.V. | NL | whitelisted |
2724 | chrome.exe | 172.217.18.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
2724 | chrome.exe | 13.35.254.213:443 | cdn.amplitude.com | — | US | suspicious |
2724 | chrome.exe | 13.35.253.61:443 | cdn.appdynamics.com | — | US | malicious |
2724 | chrome.exe | 147.75.32.13:443 | static.hotjar.com | Packet Host, Inc. | US | unknown |
2724 | chrome.exe | 143.204.214.113:443 | intljs.rmtag.com | — | US | malicious |
2724 | chrome.exe | 104.109.77.38:443 | tags.tiqcdn.com | Akamai International B.V. | NL | whitelisted |
2724 | chrome.exe | 23.210.248.45:443 | assets.adobedtm.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.webex.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
cdn.appdynamics.com |
| whitelisted |
cdn.amplitude.com |
| whitelisted |
static.hotjar.com |
| whitelisted |
assets.adobedtm.com |
| whitelisted |
intljs.rmtag.com |
| whitelisted |
tags.tiqcdn.com |
| whitelisted |
vars.hotjar.com |
| shared |
Threats
Process | Message |
|---|---|
MsiExec.exe | ~WEBEXLOGInitialize
|
MsiExec.exe | WEBEXLOGInitialize
|
MsiExec.exe | WEBEXLOGInitialize
|
MsiExec.exe | CSCvf70643 UninitWBXTRACER: g_pfnWBXTRACEA=0x00000000, g_pfnWbxTraceResident=0x00000000,g_pfnWbxTraceResident=0x00000000, g_hWbxTracer=0x00000000
|
MsiExec.exe | CSCvf70643 InitWBXTRACER: g_pfnWBXTRACEA=0x00000000, g_pfnWbxTraceResident=0x00000000, g_pfnWbxTraceDllResident=0x00000000,g_hWbxTracer=0x00000000, szInstancePath=C:\Users\admin\AppData\Local\Temp\MSI5431.tmp
|
MsiExec.exe | CSCvf70643 UninitWBXTRACER: g_pfnWBXTRACEA=0x00000000, g_pfnWbxTraceResident=0x00000000,g_pfnWbxTraceResident=0x00000000, g_hWbxTracer=0x00000000
|
MsiExec.exe | ~WEBEXLOGInitialize
|
MsiExec.exe | WEBEXLOGInitialize
|
MsiExec.exe | WEBEXLOGInitialize
|
MsiExec.exe | WEBEXLOGInitialize
|