| File name: | SAB.3.0.bat |
| Full analysis: | https://app.any.run/tasks/4db15f59-f882-459e-9541-ec223bed3472 |
| Verdict: | Malicious activity |
| Analysis date: | June 21, 2025, 02:33:19 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/x-msdos-batch |
| File info: | DOS batch file, ASCII text, with CRLF line terminators |
| MD5: | 874B14B6495A76CC4B91FADF34B87A59 |
| SHA1: | 385D50E81FFC9F56BB3E36BCE0142EF95F07787C |
| SHA256: | 62AF07DAF768B591B1FCF4B0A03610E009954D9F4AD97201E0C9DA33B29B93E5 |
| SSDEEP: | 48:yutJjHmKCljukmtp6bDohSz+zcEPAEAiHin:TtNcQKbSzcEYEs |
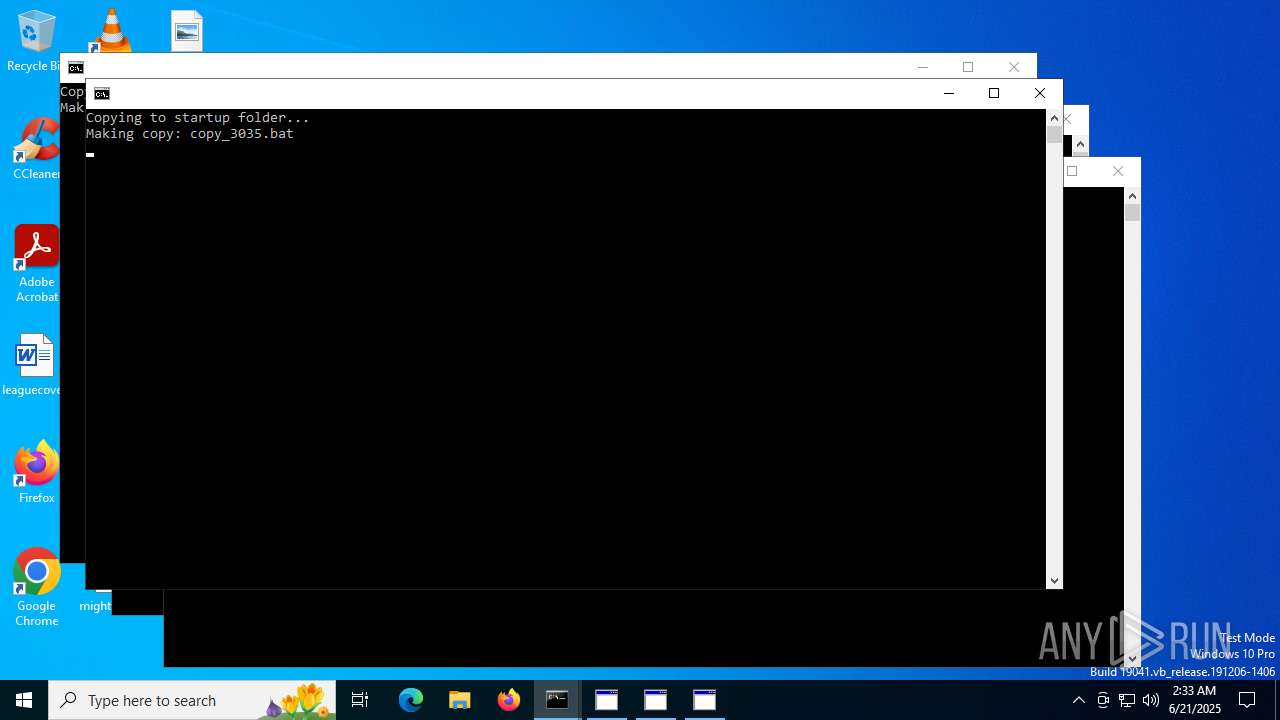
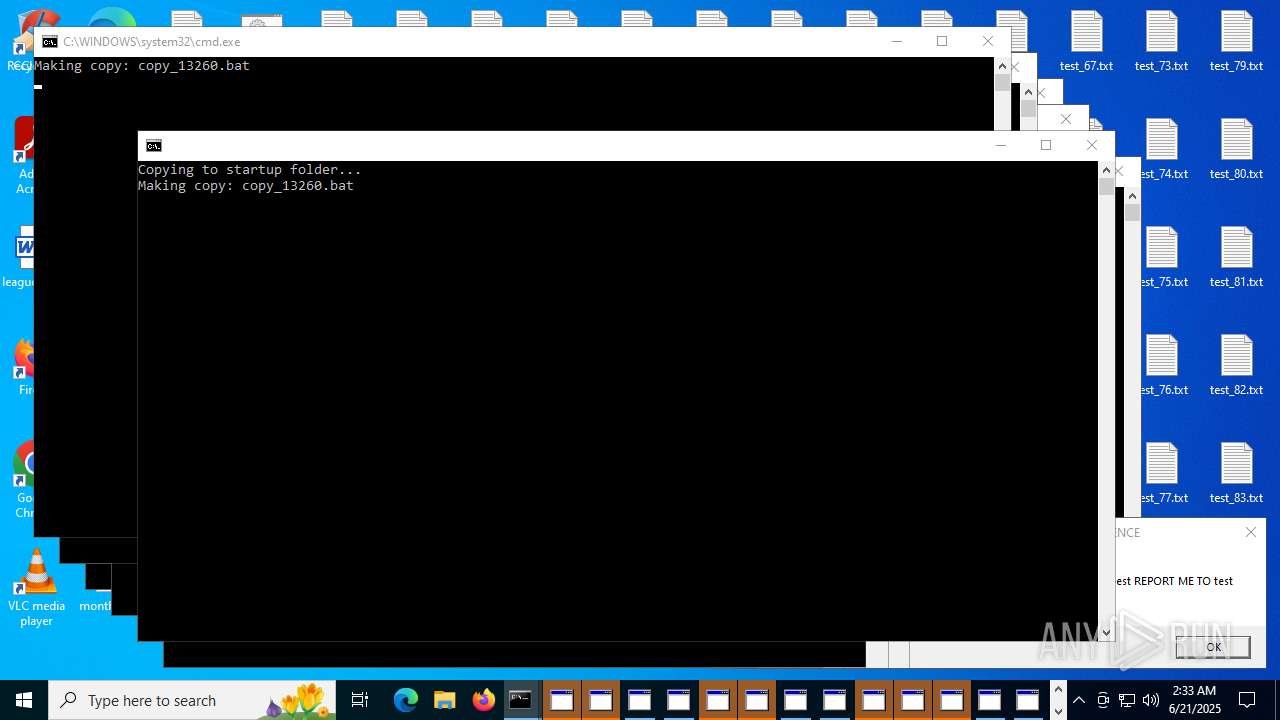
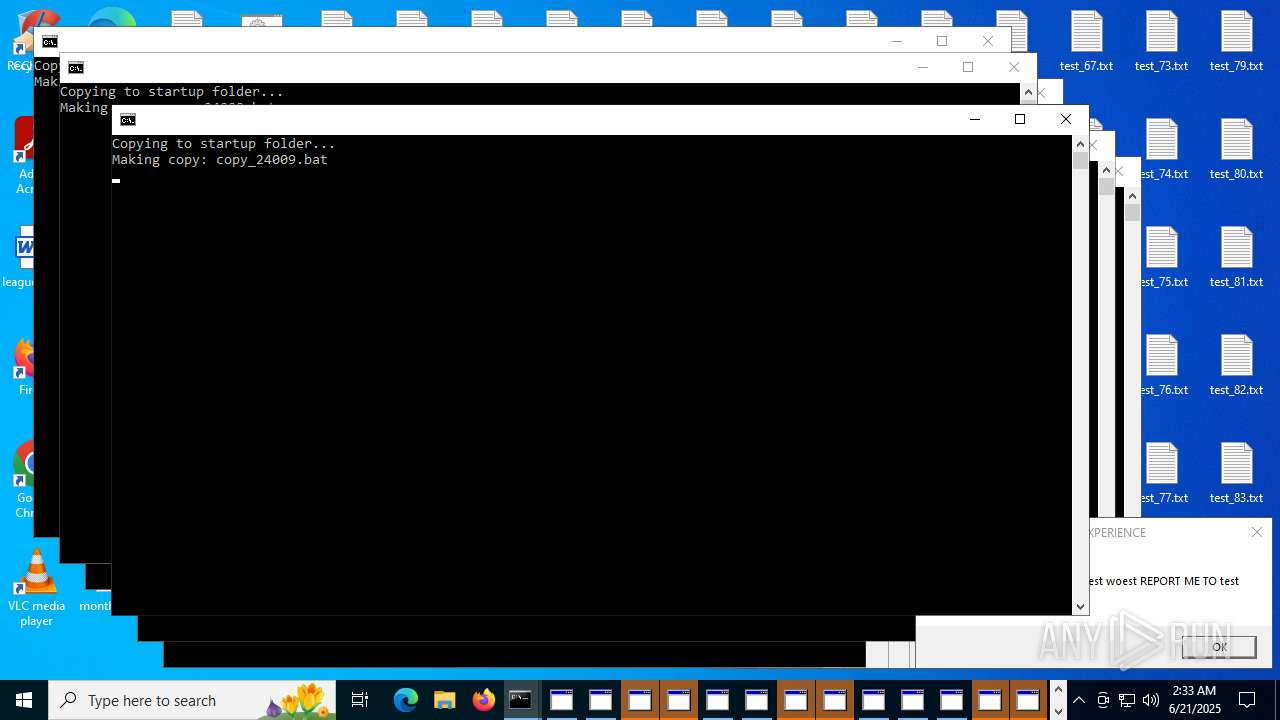
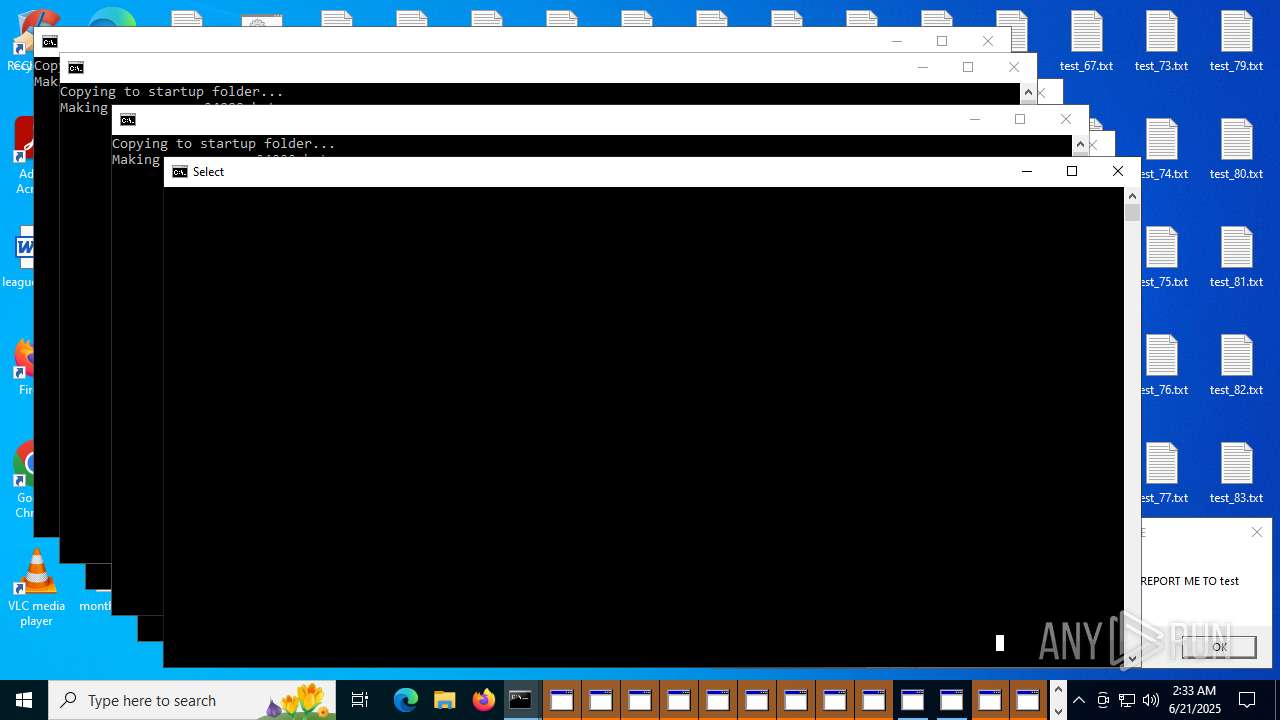
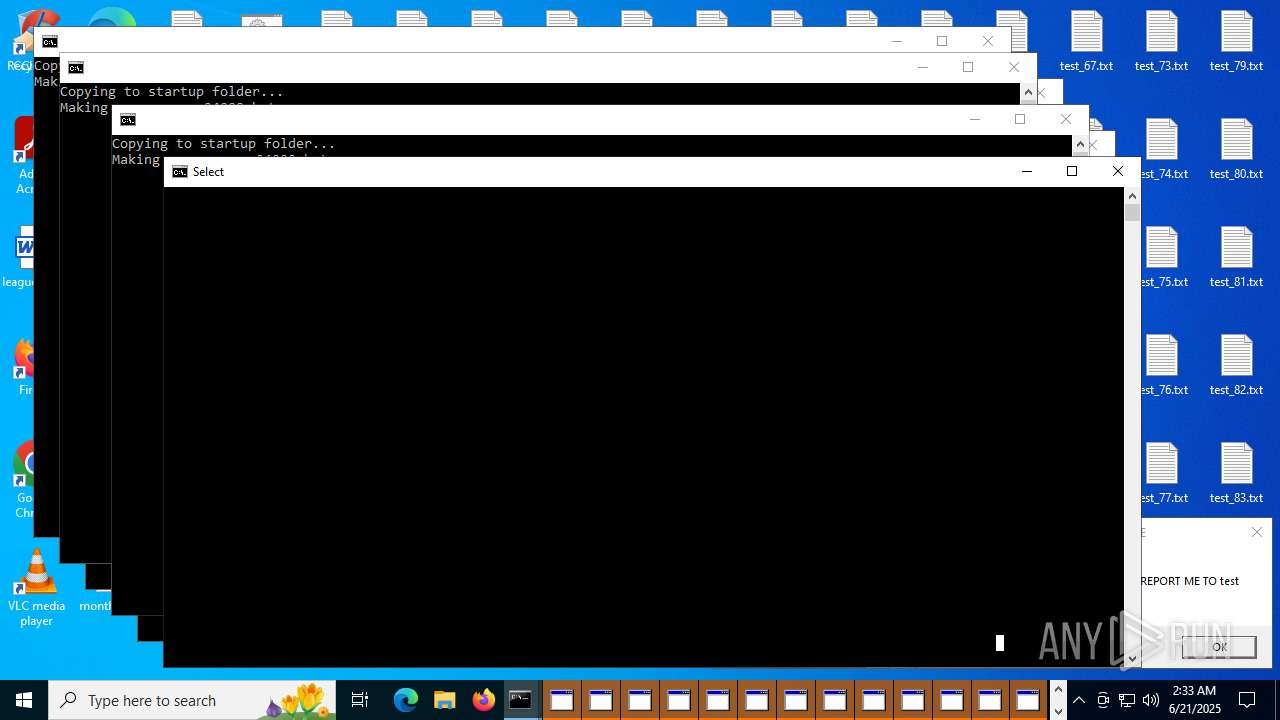
MALICIOUS
Create files in the Startup directory
- cmd.exe (PID: 6852)
SUSPICIOUS
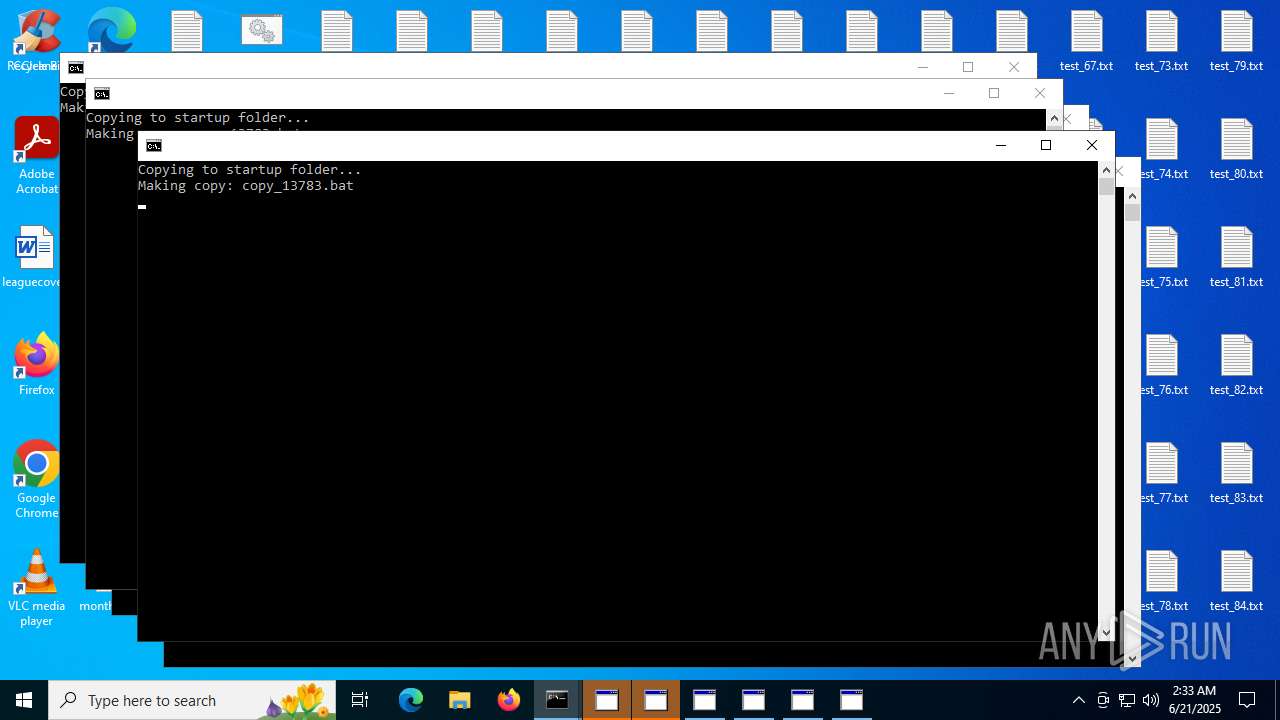
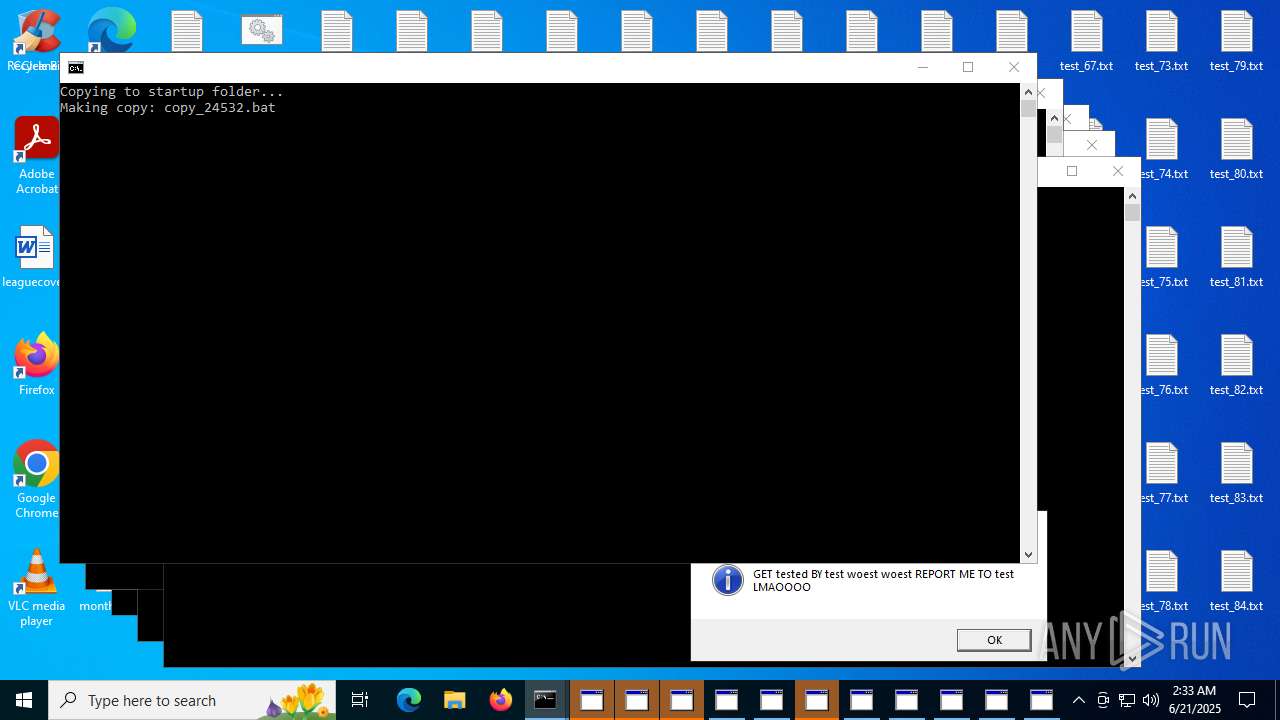
Executing commands from a ".bat" file
- cmd.exe (PID: 6852)
- cmd.exe (PID: 1496)
- cmd.exe (PID: 4832)
- cmd.exe (PID: 3768)
- cmd.exe (PID: 6532)
- cmd.exe (PID: 3724)
- cmd.exe (PID: 1212)
- cmd.exe (PID: 6236)
- cmd.exe (PID: 7216)
- cmd.exe (PID: 7348)
- cmd.exe (PID: 7480)
- cmd.exe (PID: 2288)
- cmd.exe (PID: 7600)
- cmd.exe (PID: 7720)
- cmd.exe (PID: 7840)
- cmd.exe (PID: 7944)
- cmd.exe (PID: 8032)
- cmd.exe (PID: 8212)
- cmd.exe (PID: 8092)
- cmd.exe (PID: 7616)
- cmd.exe (PID: 8664)
- cmd.exe (PID: 8472)
- cmd.exe (PID: 8320)
- cmd.exe (PID: 8848)
- cmd.exe (PID: 8980)
- cmd.exe (PID: 8744)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 6852)
- cmd.exe (PID: 1496)
- cmd.exe (PID: 4832)
- cmd.exe (PID: 3768)
- cmd.exe (PID: 6532)
- cmd.exe (PID: 6236)
- cmd.exe (PID: 1212)
- cmd.exe (PID: 3724)
- cmd.exe (PID: 2288)
- cmd.exe (PID: 7216)
- cmd.exe (PID: 7348)
- cmd.exe (PID: 7480)
- cmd.exe (PID: 7600)
- cmd.exe (PID: 7720)
- cmd.exe (PID: 7840)
- cmd.exe (PID: 7944)
- cmd.exe (PID: 8092)
- cmd.exe (PID: 7616)
- cmd.exe (PID: 8032)
- cmd.exe (PID: 8212)
- cmd.exe (PID: 8664)
- cmd.exe (PID: 8472)
- cmd.exe (PID: 8320)
- cmd.exe (PID: 8848)
- cmd.exe (PID: 8980)
- cmd.exe (PID: 8744)
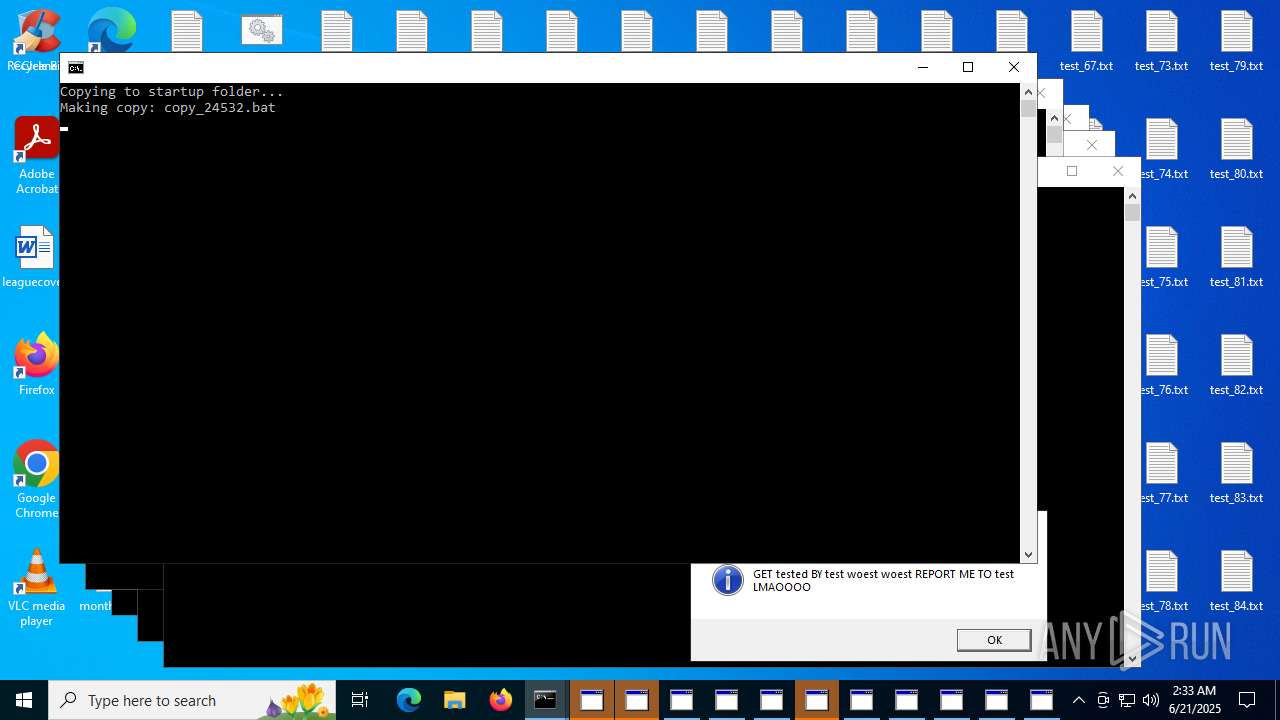
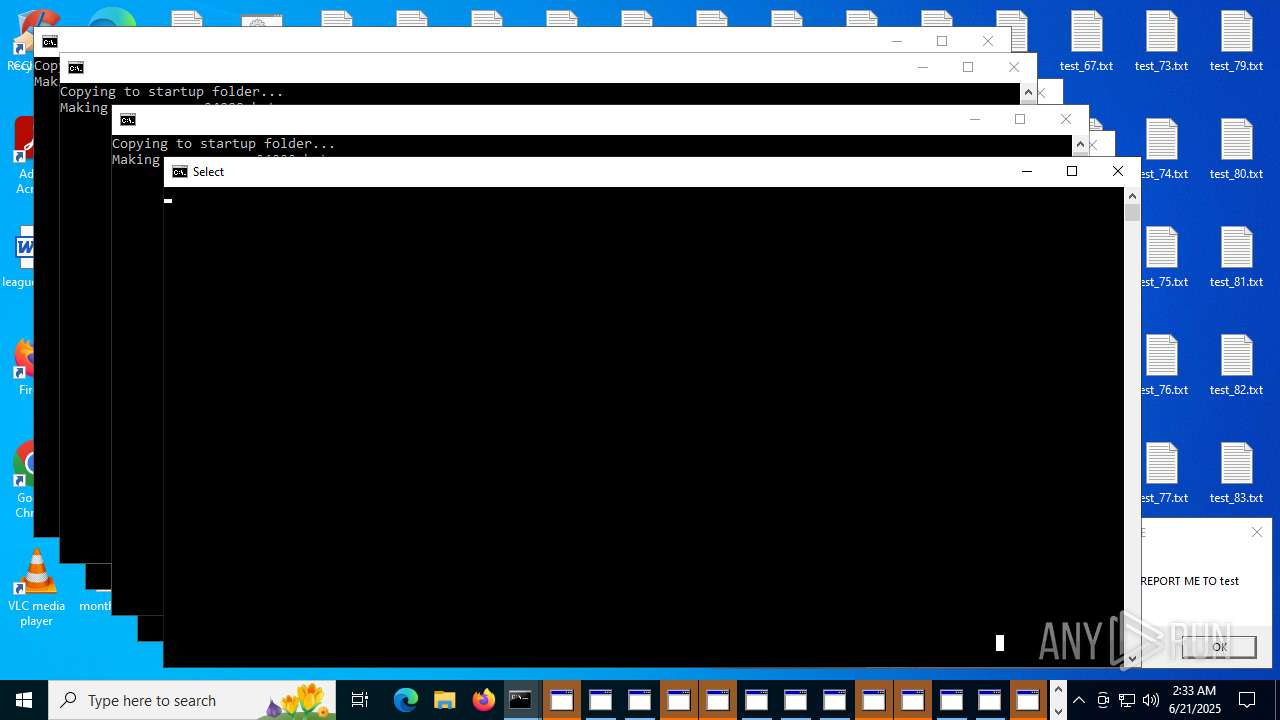
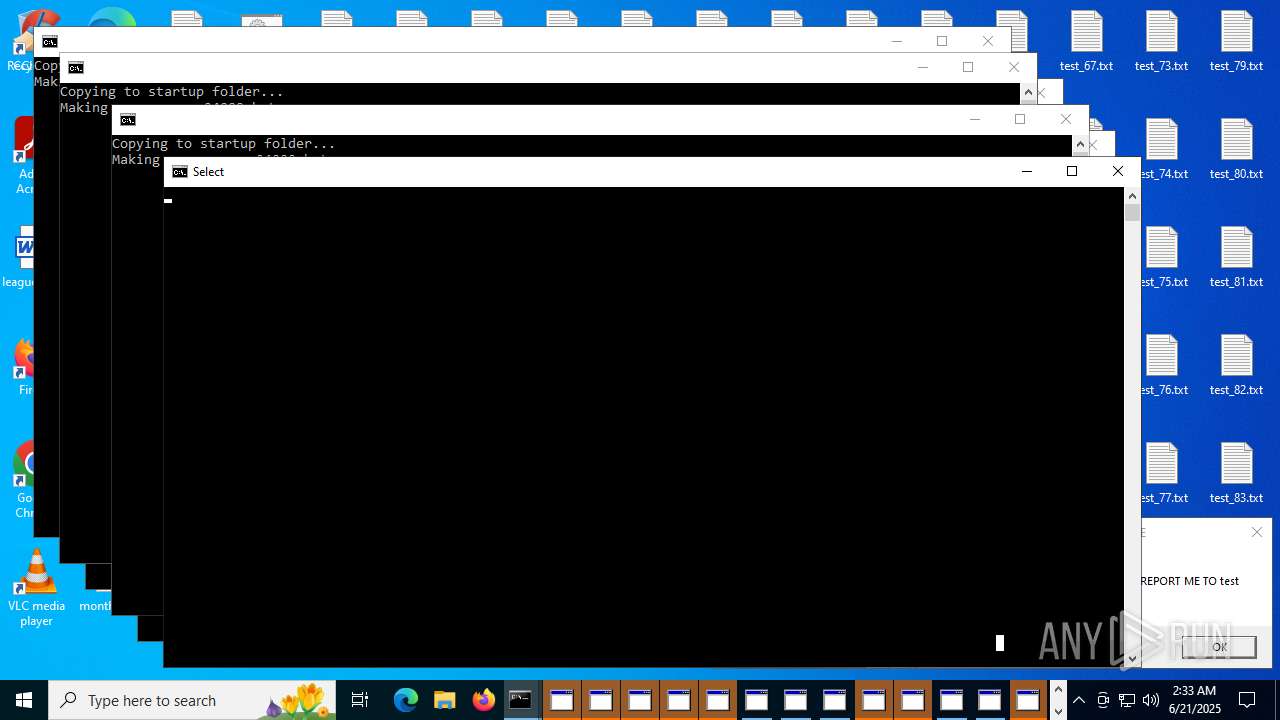
Executes JavaScript directly as a command
- cmd.exe (PID: 6852)
- cmd.exe (PID: 1496)
- cmd.exe (PID: 4832)
- cmd.exe (PID: 3768)
- cmd.exe (PID: 6532)
- cmd.exe (PID: 3724)
- cmd.exe (PID: 1212)
- cmd.exe (PID: 6236)
- cmd.exe (PID: 2288)
- cmd.exe (PID: 7216)
- cmd.exe (PID: 7348)
- cmd.exe (PID: 7480)
- cmd.exe (PID: 7600)
- cmd.exe (PID: 7840)
- cmd.exe (PID: 7720)
- cmd.exe (PID: 7944)
- cmd.exe (PID: 8092)
- cmd.exe (PID: 7616)
- cmd.exe (PID: 8032)
- cmd.exe (PID: 8212)
- cmd.exe (PID: 8472)
- cmd.exe (PID: 8320)
- cmd.exe (PID: 8744)
- cmd.exe (PID: 8848)
- cmd.exe (PID: 8980)
- cmd.exe (PID: 8664)
Application launched itself
- cmd.exe (PID: 6852)
- cmd.exe (PID: 1496)
- cmd.exe (PID: 4832)
- cmd.exe (PID: 3768)
- cmd.exe (PID: 6532)
- cmd.exe (PID: 3724)
- cmd.exe (PID: 1212)
- cmd.exe (PID: 6236)
- cmd.exe (PID: 2288)
- cmd.exe (PID: 7216)
- cmd.exe (PID: 7348)
- cmd.exe (PID: 7480)
- cmd.exe (PID: 7600)
- cmd.exe (PID: 7720)
- cmd.exe (PID: 7840)
- cmd.exe (PID: 7944)
- cmd.exe (PID: 8092)
- cmd.exe (PID: 7616)
- cmd.exe (PID: 8032)
- cmd.exe (PID: 8212)
- cmd.exe (PID: 8472)
- cmd.exe (PID: 8320)
- cmd.exe (PID: 8848)
- cmd.exe (PID: 8980)
- cmd.exe (PID: 8664)
- cmd.exe (PID: 8744)
INFO
Launching a file from the Startup directory
- cmd.exe (PID: 6852)
Reads Internet Explorer settings
- mshta.exe (PID: 3388)
- mshta.exe (PID: 6612)
- mshta.exe (PID: 4236)
- mshta.exe (PID: 2124)
- mshta.exe (PID: 2188)
- mshta.exe (PID: 2380)
- mshta.exe (PID: 7172)
- mshta.exe (PID: 7364)
- mshta.exe (PID: 7456)
- mshta.exe (PID: 7580)
- mshta.exe (PID: 2276)
- mshta.exe (PID: 7704)
- mshta.exe (PID: 7936)
- mshta.exe (PID: 7820)
- mshta.exe (PID: 4320)
- mshta.exe (PID: 1812)
- mshta.exe (PID: 6260)
- mshta.exe (PID: 8076)
- mshta.exe (PID: 8304)
- mshta.exe (PID: 8532)
- mshta.exe (PID: 8524)
- mshta.exe (PID: 9188)
- mshta.exe (PID: 8960)
- mshta.exe (PID: 9076)
- mshta.exe (PID: 8724)
- mshta.exe (PID: 8836)
Manual execution by a user
- cmd.exe (PID: 8372)
Application launched itself
- msedge.exe (PID: 6336)
Checks supported languages
- identity_helper.exe (PID: 5248)
Reads the computer name
- identity_helper.exe (PID: 5248)
Reads Environment values
- identity_helper.exe (PID: 5248)
Checks proxy server information
- slui.exe (PID: 10808)
Reads the software policy settings
- slui.exe (PID: 10808)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
253
Monitored processes
117
Malicious processes
25
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 304 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6680,i,4234966029937990593,1239853618109419270,262144 --variations-seed-version --mojo-platform-channel-handle=7824 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1212 | C:\WINDOWS\system32\cmd.exe /K "copy_3035.bat" 600000 | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1496 | C:\WINDOWS\system32\cmd.exe /K "copy_3035.bat" 100000 | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1520 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1812 | mshta "javascript:var sh=new ActiveXObject('WScript.Shell'); sh.Popup('GET tested BY test woest woest REPORT ME TO test LMAOOOO', 0, 'SORRY FOR AFFECTING USER EXPERIENCE', 64);close();" | C:\Windows\System32\mshta.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2124 | mshta "javascript:var sh=new ActiveXObject('WScript.Shell'); sh.Popup('GET tested BY test woest woest REPORT ME TO test LMAOOOO', 0, 'SORRY FOR AFFECTING USER EXPERIENCE', 64);close();" | C:\Windows\System32\mshta.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2188 | mshta "javascript:var sh=new ActiveXObject('WScript.Shell'); sh.Popup('GET tested BY test woest woest REPORT ME TO test LMAOOOO', 0, 'SORRY FOR AFFECTING USER EXPERIENCE', 64);close();" | C:\Windows\System32\mshta.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2232 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2276 | mshta "javascript:var sh=new ActiveXObject('WScript.Shell'); sh.Popup('GET tested BY test woest woest REPORT ME TO test LMAOOOO', 0, 'SORRY FOR AFFECTING USER EXPERIENCE', 64);close();" | C:\Windows\System32\mshta.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2288 | C:\WINDOWS\system32\cmd.exe /K "copy_13783.bat" 800000 | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
16 824
Read events
16 777
Write events
47
Delete events
0
Modification events
| (PID) Process: | (9188) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (9188) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (9188) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (8980) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (8980) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (8980) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (8848) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (8848) cmd.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (9076) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (9076) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
Executable files
7
Suspicious files
369
Text files
152
Unknown types
0
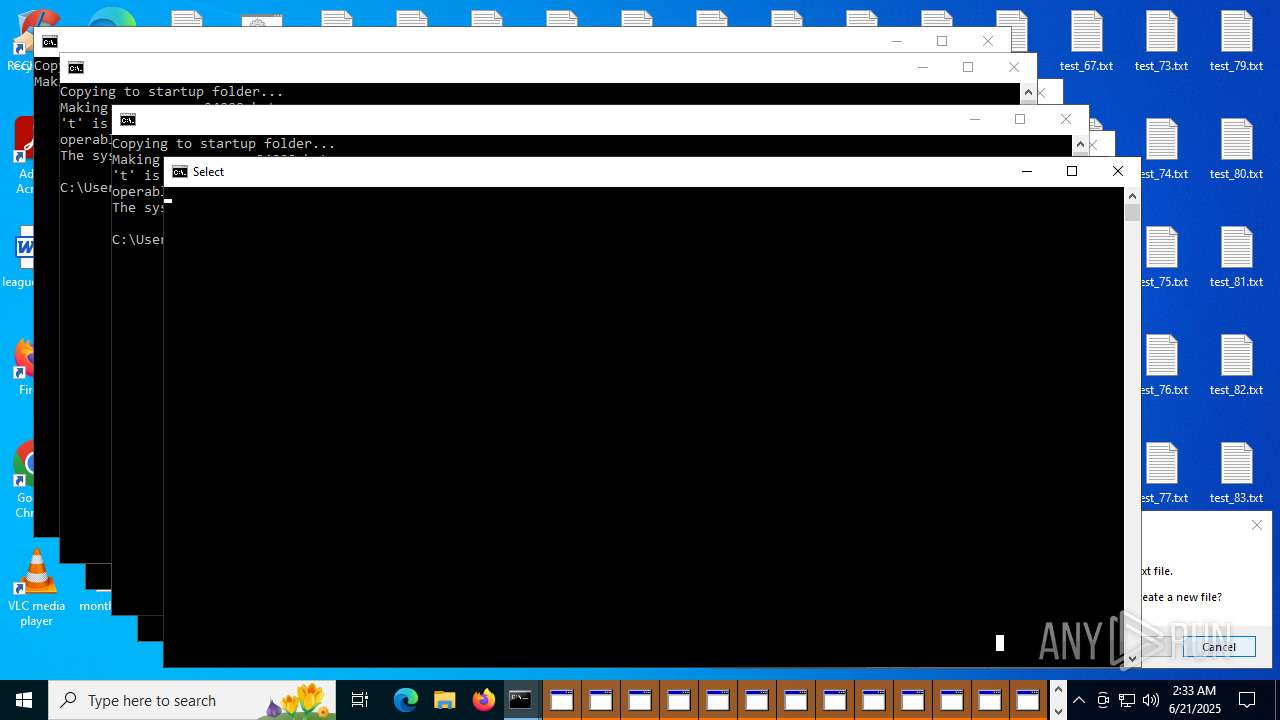
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6852 | cmd.exe | C:\Users\admin\Desktop\copy_3035.bat | text | |
MD5:874B14B6495A76CC4B91FADF34B87A59 | SHA256:62AF07DAF768B591B1FCF4B0A03610E009954D9F4AD97201E0C9DA33B29B93E5 | |||
| 6852 | cmd.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\MyAutoStart.bat | text | |
MD5:874B14B6495A76CC4B91FADF34B87A59 | SHA256:62AF07DAF768B591B1FCF4B0A03610E009954D9F4AD97201E0C9DA33B29B93E5 | |||
| 6852 | cmd.exe | C:\Users\admin\Desktop\test_4.txt | text | |
MD5:81051BCC2CF1BEDF378224B0A93E2877 | SHA256:7EB70257593DA06F682A3DDDA54A9D260D4FC514F645237F5CA74B08F8DA61A6 | |||
| 6852 | cmd.exe | C:\Users\admin\Desktop\test_2.txt | text | |
MD5:81051BCC2CF1BEDF378224B0A93E2877 | SHA256:7EB70257593DA06F682A3DDDA54A9D260D4FC514F645237F5CA74B08F8DA61A6 | |||
| 6852 | cmd.exe | C:\Users\admin\Desktop\test_1.txt | text | |
MD5:81051BCC2CF1BEDF378224B0A93E2877 | SHA256:7EB70257593DA06F682A3DDDA54A9D260D4FC514F645237F5CA74B08F8DA61A6 | |||
| 6852 | cmd.exe | C:\Users\admin\Desktop\test_5.txt | text | |
MD5:81051BCC2CF1BEDF378224B0A93E2877 | SHA256:7EB70257593DA06F682A3DDDA54A9D260D4FC514F645237F5CA74B08F8DA61A6 | |||
| 6852 | cmd.exe | C:\Users\admin\Desktop\test_9.txt | text | |
MD5:81051BCC2CF1BEDF378224B0A93E2877 | SHA256:7EB70257593DA06F682A3DDDA54A9D260D4FC514F645237F5CA74B08F8DA61A6 | |||
| 6852 | cmd.exe | C:\Users\admin\Desktop\test_16.txt | text | |
MD5:81051BCC2CF1BEDF378224B0A93E2877 | SHA256:7EB70257593DA06F682A3DDDA54A9D260D4FC514F645237F5CA74B08F8DA61A6 | |||
| 6852 | cmd.exe | C:\Users\admin\Desktop\test_13.txt | text | |
MD5:81051BCC2CF1BEDF378224B0A93E2877 | SHA256:7EB70257593DA06F682A3DDDA54A9D260D4FC514F645237F5CA74B08F8DA61A6 | |||
| 6852 | cmd.exe | C:\Users\admin\Desktop\test_14.txt | text | |
MD5:81051BCC2CF1BEDF378224B0A93E2877 | SHA256:7EB70257593DA06F682A3DDDA54A9D260D4FC514F645237F5CA74B08F8DA61A6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
359
TCP/UDP connections
199
DNS requests
116
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 2.20.118.102:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.20.118.102:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
3732 | RUXIMICS.exe | GET | 304 | 2.20.118.102:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 200 | 20.190.160.4:443 | https://login.live.com/RST2.srf | unknown | xml | 10.2 Kb | whitelisted |
— | — | POST | 200 | 20.190.160.14:443 | https://login.live.com/RST2.srf | unknown | xml | 11.0 Kb | whitelisted |
— | — | GET | 200 | 142.250.181.238:443 | https://www.youtube.com/watch?v=WCKUuI22cY4 | unknown | html | 943 Kb | whitelisted |
— | — | GET | 200 | 92.123.104.53:443 | https://copilot.microsoft.com/c/api/user/eligibility | unknown | binary | 25 b | whitelisted |
— | — | GET | 200 | 92.123.104.32:443 | https://www.bing.com/bloomfilterfiles/ExpandedDomainsFilterGlobal.json | unknown | binary | 655 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3732 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 2.20.118.102:80 | www.microsoft.com | RCS & RDS | RO | whitelisted |
1268 | svchost.exe | 2.20.118.102:80 | www.microsoft.com | RCS & RDS | RO | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
www.youtube.com |
| whitelisted |