| File name: | bill4759.doc |
| Full analysis: | https://app.any.run/tasks/72ddf59e-9256-4a8f-900d-c226a20f123e |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2019, 12:38:42 |
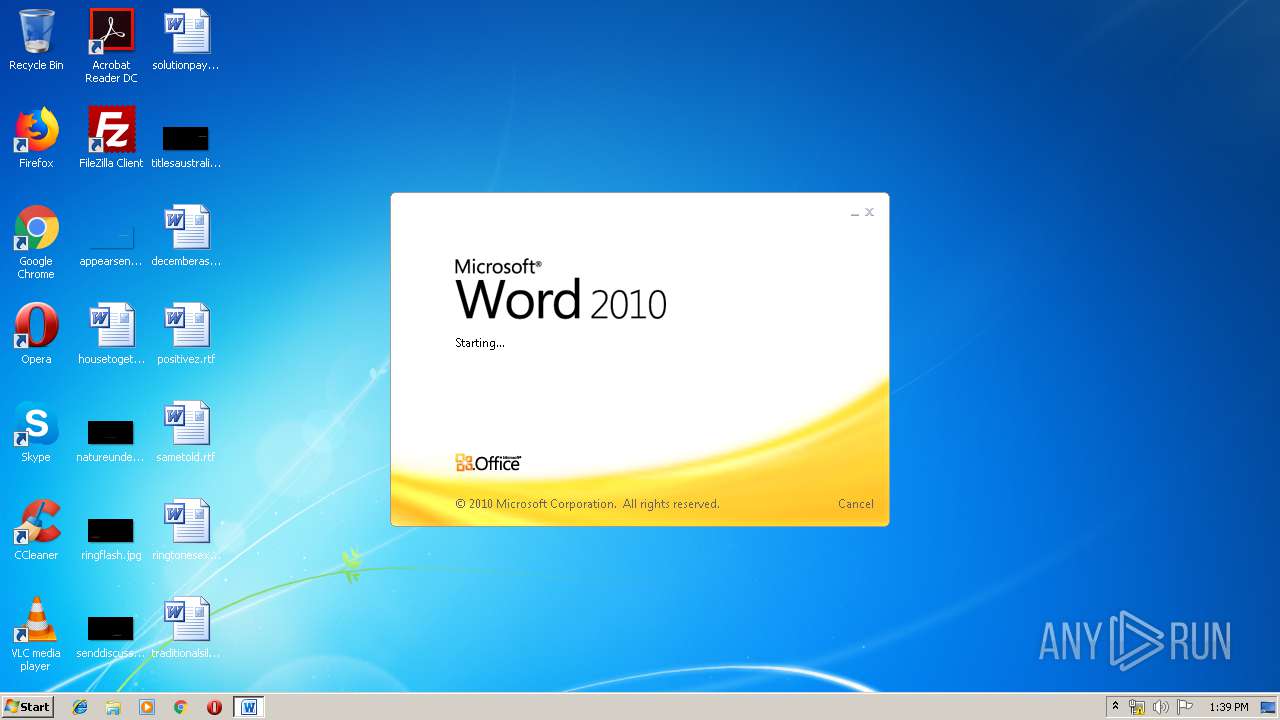
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Author: Bob Brown, Template: Normal.dotm, Last Saved By: Bob Brown, Revision Number: 8, Name of Creating Application: Microsoft Office Word, Total Editing Time: 05:00, Create Time/Date: Thu May 16 10:32:00 2019, Last Saved Time/Date: Thu May 16 10:58:00 2019, Number of Pages: 1, Number of Words: 0, Number of Characters: 1, Security: 0 |
| MD5: | C459B5D54552D99A4658C680DBF61DCC |
| SHA1: | CC29DB93DC649F7AF9E9D2E4BB6F35382278B943 |
| SHA256: | 62AE80DC45B409A7A609EEAB1228C661B9303FCB1D8B8090907C9241B1FE1F57 |
| SSDEEP: | 3072:IQSzo2azvHOWAFum2UIUiN1r+F1+nls1v/kvy:IBzo2AvPA92UIUeznls1v9 |
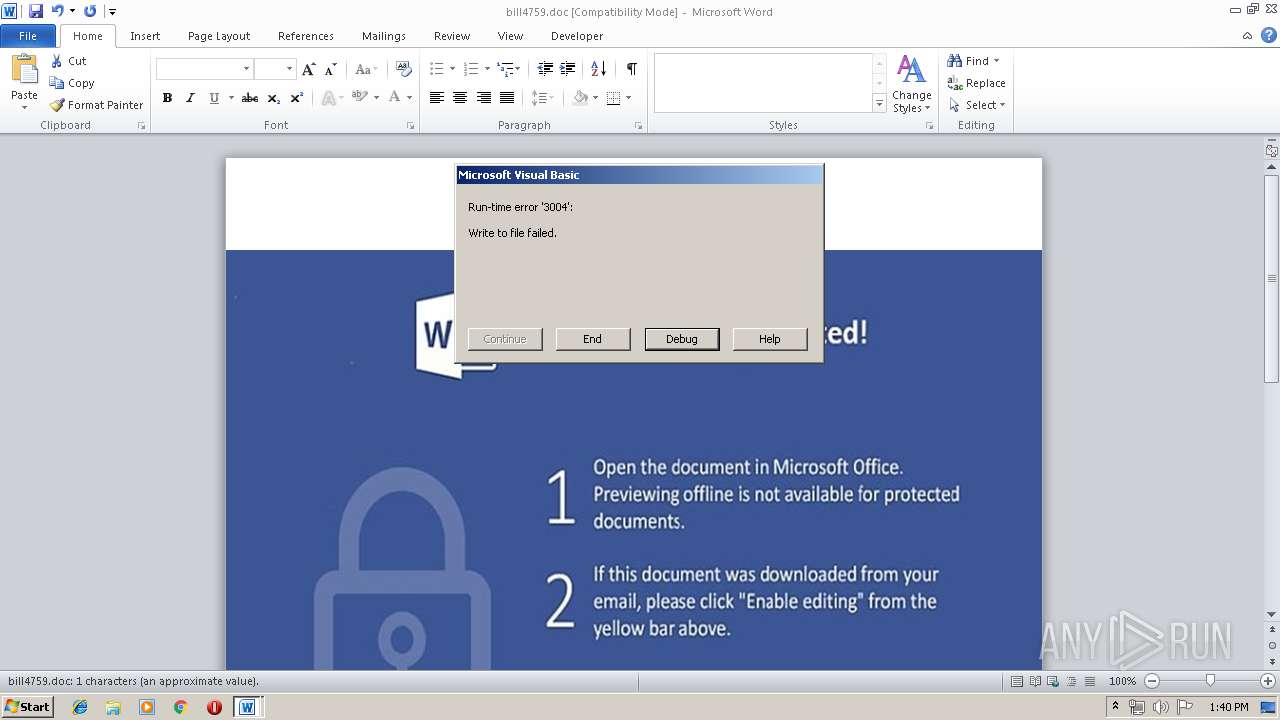
MALICIOUS
Executable content was dropped or overwritten
- WINWORD.EXE (PID: 3336)
Loads dropped or rewritten executable
- WINWORD.EXE (PID: 3336)
- wprgxyeqd79.exe (PID: 2684)
- svchost.exe (PID: 4056)
- rher.exe (PID: 2724)
- WerFault.exe (PID: 2644)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3336)
Application was dropped or rewritten from another process
- wprgxyeqd79.exe (PID: 2684)
- rher.exe (PID: 2724)
SUSPICIOUS
Reads Internet Cache Settings
- WINWORD.EXE (PID: 3336)
Executable content was dropped or overwritten
- wprgxyeqd79.exe (PID: 2684)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3336)
Creates files in the user directory
- WINWORD.EXE (PID: 3336)
Dropped object may contain Bitcoin addresses
- WINWORD.EXE (PID: 3336)
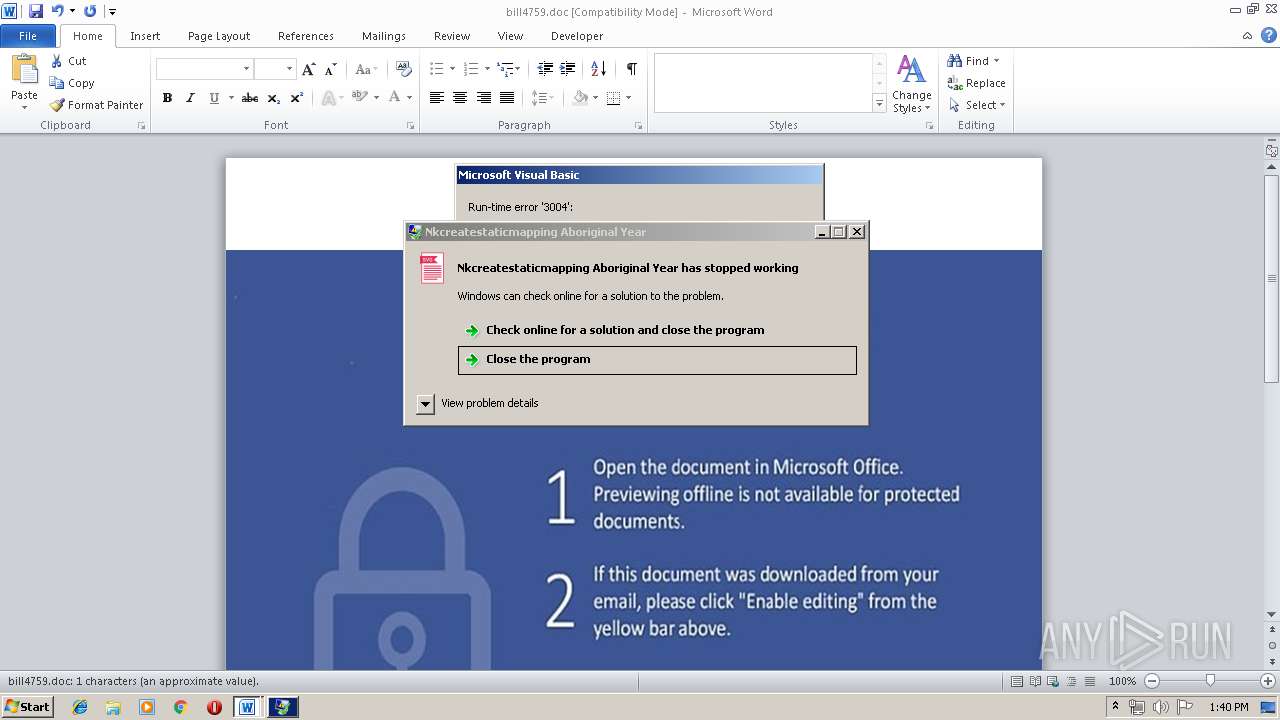
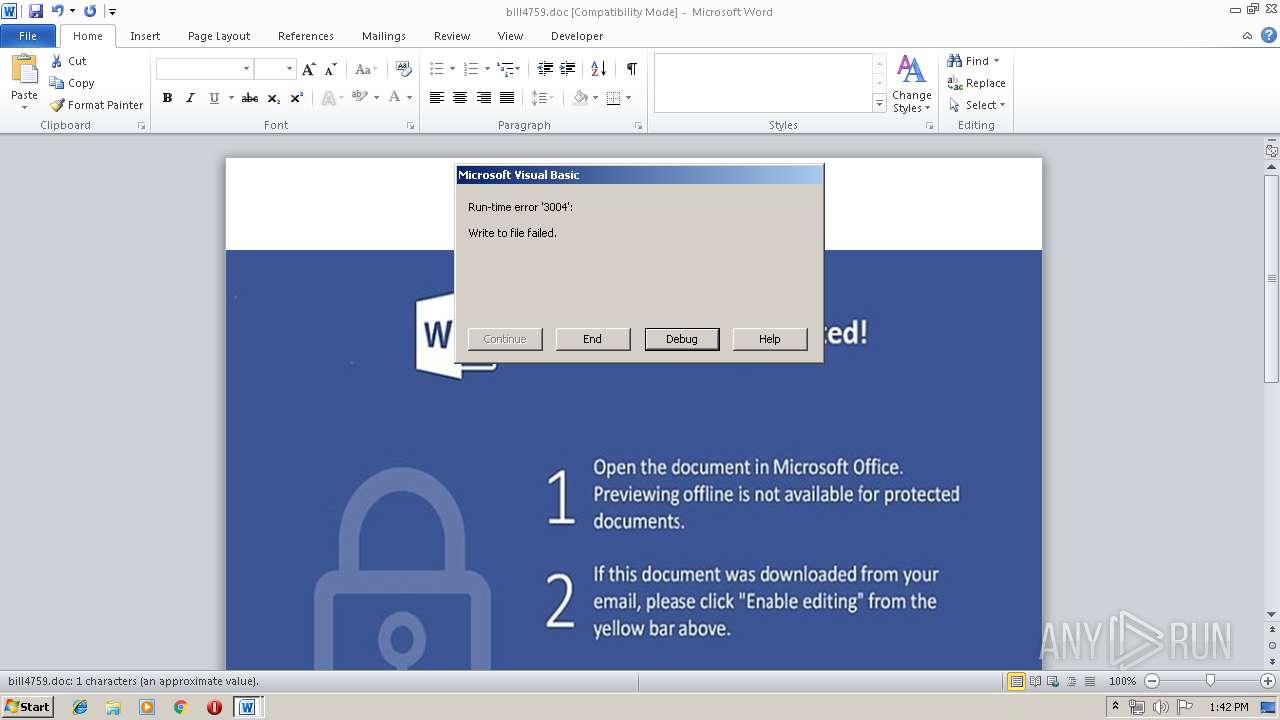
Application was crashed
- rher.exe (PID: 2724)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (80) |
|---|
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | Bob Brown |
| Keywords: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | Bob Brown |
| RevisionNumber: | 8 |
| Software: | Microsoft Office Word |
| TotalEditTime: | 5.0 minutes |
| CreateDate: | 2019:05:16 09:32:00 |
| ModifyDate: | 2019:05:16 09:58:00 |
| Pages: | 1 |
| Words: | - |
| Characters: | 1 |
| Security: | None |
| CodePage: | Unicode (UTF-8) |
| Company: | Microsoft |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 1 |
| AppVersion: | 14 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | - |
| CompObjUserType: | - |
Total processes
37
Monitored processes
5
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2644 | C:\Windows\system32\WerFault.exe -u -p 2724 -s 712 | C:\Windows\system32\WerFault.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2684 | C:\Users\Public\wprgxyeqd79.exe | C:\Users\Public\wprgxyeqd79.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Miranda IM Integrity Level: MEDIUM Description: Tile Textheight Clipbook Mostly Wading Exit code: 0 Version: 8.7.56.236 Modules
| |||||||||||||||
| 2724 | C:\Users\Public\rher.exe | C:\Users\Public\rher.exe | WINWORD.EXE | ||||||||||||
User: admin Company: x264 project Integrity Level: MEDIUM Description: Nkcreatestaticmapping Aboriginal Year Exit code: 3221225477 Version: 5.7.3.790 Modules
| |||||||||||||||
| 3336 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\bill4759.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 4056 | C:\Windows\System32\svchost.exe -k WerSvcGroup | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 135
Read events
793
Write events
337
Delete events
5
Modification events
| (PID) Process: | (3336) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | j9? |
Value: 6A393F00080D0000010000000000000000000000 | |||
| (PID) Process: | (3336) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3336) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3336) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1320419358 | |||
| (PID) Process: | (3336) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1320419472 | |||
| (PID) Process: | (3336) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1320419473 | |||
| (PID) Process: | (3336) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 080D000054970403090FD50100000000 | |||
| (PID) Process: | (3336) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | ?;? |
Value: 3F3B3F00080D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3336) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | ?;? |
Value: 3F3B3F00080D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3336) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
5
Suspicious files
1
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3336 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRED6A.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3336 | WINWORD.EXE | C:\Users\Public\wprgxyeqd79.exe | executable | |
MD5:— | SHA256:— | |||
| 2684 | wprgxyeqd79.exe | C:\Users\admin\AppData\Local\Temp\1D86.tmp | executable | |
MD5:— | SHA256:— | |||
| 3336 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$ll4759.doc | pgc | |
MD5:— | SHA256:— | |||
| 3336 | WINWORD.EXE | C:\Users\Public\rher.exe | executable | |
MD5:— | SHA256:— | |||
| 3336 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3336 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\pasmmm[1].exe | executable | |
MD5:— | SHA256:— | |||
| 2644 | WerFault.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WER\ReportArchive\AppCrash_rher.exe_379ab0e06c94173b5e3bfd67e28d4ef6f46c3531_0a40bdff\Report.wer | binary | |
MD5:— | SHA256:— | |||
| 3336 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\ananas[1].exe | executable | |
MD5:— | SHA256:— | |||
| 2644 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\rher.exe.2724.dmp | dmp | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
9
DNS requests
3
Threats
18
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2724 | rher.exe | GET | — | 185.96.180.164:80 | http://185.96.180.164/tor/server/fp/4109314e35c8e4084ae2bc1711562d380077b1f0 | DK | — | — | suspicious |
2724 | rher.exe | GET | — | 162.247.74.216:80 | http://162.247.74.216/tor/server/fp/7f849e3b86dd0df2c4d0e31108228ec7c714191b | US | — | — | suspicious |
2724 | rher.exe | GET | — | 104.218.63.76:80 | http://104.218.63.76/tor/server/fp/484f666c491bcde22b45e0e19d1cea5acc5a9611 | CA | — | — | suspicious |
2724 | rher.exe | GET | — | 66.111.2.131:9030 | http://66.111.2.131:9030/tor/status-vote/current/consensus | US | — | — | suspicious |
2724 | rher.exe | GET | — | 199.249.230.108:80 | http://199.249.230.108/tor/server/fp/592031cfdba17dd46e1e365e6c60ad1f81655033 | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3336 | WINWORD.EXE | 47.245.58.124:443 | kentona.su | — | US | suspicious |
2724 | rher.exe | 54.243.147.226:443 | api.ipify.org | Amazon.com, Inc. | US | malicious |
2724 | rher.exe | 185.96.180.164:80 | — | BornFiber Service Provider ApS | DK | suspicious |
2724 | rher.exe | 162.247.74.216:80 | — | The Calyx Institute | US | suspicious |
2724 | rher.exe | 129.6.15.28:13 | time-a.nist.gov | National Bureau of Standards | US | unknown |
2724 | rher.exe | 104.218.63.76:80 | — | Tech Futures Interactive Inc. | CA | suspicious |
2724 | rher.exe | 37.123.132.154:443 | — | Bahnhof Internet AB | NO | suspicious |
2724 | rher.exe | 66.111.2.131:9030 | — | The New York Internet Company | US | suspicious |
2724 | rher.exe | 199.249.230.108:80 | — | Quintex Alliance Consulting | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
kentona.su |
| malicious |
api.ipify.org |
| shared |
time-a.nist.gov |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1056 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
2724 | rher.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 550 |
2724 | rher.exe | Misc activity | SUSPICIOUS [PTsecurity] ipify.org External IP Check |
2724 | rher.exe | Misc activity | SUSPICIOUS [PTsecurity] ipify.org External IP Check |
2724 | rher.exe | Misc Attack | ET TOR Known Tor Exit Node Traffic group 12 |
2724 | rher.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 13 |
2724 | rher.exe | Potential Corporate Privacy Violation | ET P2P Tor Get Server Request |
2724 | rher.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 452 |
2724 | rher.exe | Misc Attack | ET TOR Known Tor Exit Node Traffic group 2 |
2724 | rher.exe | Misc Attack | ET TOR Known Tor Relay/Router (Not Exit) Node Traffic group 2 |
1 ETPRO signatures available at the full report