| File name: | dropshot.exe.mal |
| Full analysis: | https://app.any.run/tasks/f27ad106-dded-4daa-8cc3-47a2975de5fb |
| Verdict: | Malicious activity |
| Analysis date: | January 17, 2020, 20:25:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 0CCC9EC82F1D44C243329014B82D3125 |
| SHA1: | 279FF728023EEAA1715403EC823801BF3493F5CA |
| SHA256: | 62AABCE7A5741A9270CDDAC49CD1D715305C1D0505E620BBEAEC6FF9B6FD0260 |
| SSDEEP: | 3072:v9EkH5M0x4Xaql2IGBDDwvUGNeHWBX5+PNzndF/wYLRsIa7SPwa2PbU5:hM0qtV7LfYzdFIYLRLjwlU5 |
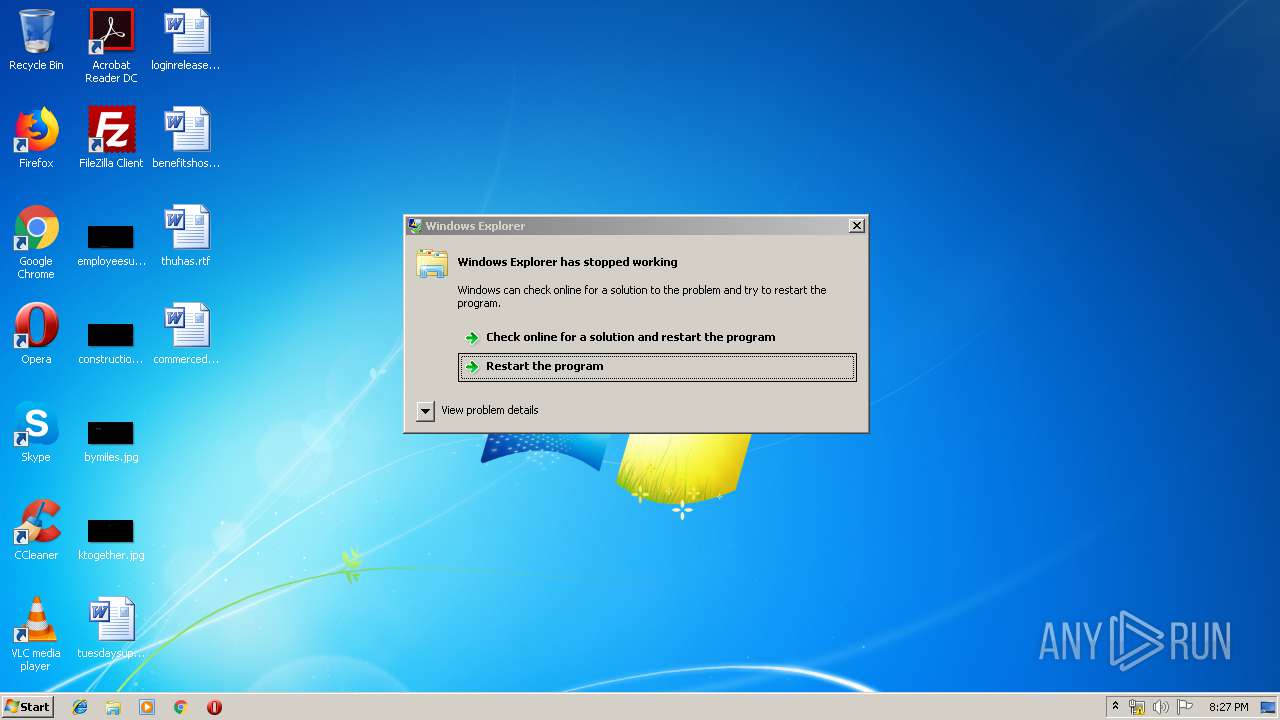
MALICIOUS
Low-level write access rights to disk partition
- iexplore.exe (PID: 1024)
Writes to a start menu file
- iexplore.exe (PID: 1024)
Modifies files in Chrome extension folder
- iexplore.exe (PID: 1024)
SUSPICIOUS
Uses WMIC.EXE to create a new process
- cmd.exe (PID: 2084)
Starts Internet Explorer
- dropshot.exe.mal.exe (PID: 964)
Starts CMD.EXE for commands execution
- dropshot.exe.mal.exe (PID: 964)
Executed via WMI
- Wscript.exe (PID: 3748)
Low-level read access rights to disk partition
- iexplore.exe (PID: 1024)
Removes files from Windows directory
- iexplore.exe (PID: 1024)
INFO
Writes to a desktop.ini file (may be used to cloak folders)
- iexplore.exe (PID: 1024)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1999:02:08 07:15:47+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 71680 |
| InitializedDataSize: | 122368 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x8adb |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 08-Feb-1999 06:15:47 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 08-Feb-1999 06:15:47 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000117A7 | 0x00011800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.41644 |
.rdata | 0x00013000 | 0x0000745A | 0x00007600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.0832 |
.data | 0x0001B000 | 0x00002C38 | 0x00002200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.2848 |
.rsrc | 0x0001E000 | 0x000131DC | 0x00013200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.86196 |
.reloc | 0x00032000 | 0x000012DC | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.47994 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.89623 | 392 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 5.7839 | 2216 | Latin 1 / Western European | Farsi - Iran | RT_ICON |
3 | 2.22232 | 1384 | Latin 1 / Western European | Farsi - Iran | RT_ICON |
101 | 7.99319 | 69632 | Latin 1 / Western European | UNKNOWN | UNKNOWN |
102 | 1.88851 | 19 | Latin 1 / Western European | UNKNOWN | UNKNOWN |
103 | 2.54942 | 48 | Latin 1 / Western European | Farsi - Iran | RT_GROUP_ICON |
110 | 0.591673 | 28 | Latin 1 / Western European | Farsi - Iran | UNKNOWN |
1040 | 2.43186 | 100 | Latin 1 / Western European | Farsi - Iran | RT_DIALOG |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.dll |
USER32.dll |
Total processes
45
Monitored processes
6
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 640 | "C:\Users\admin\AppData\Local\Temp\dropshot.exe.mal.exe" | C:\Users\admin\AppData\Local\Temp\dropshot.exe.mal.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 964 | "C:\Users\admin\AppData\Local\Temp\dropshot.exe.mal.exe" | C:\Users\admin\AppData\Local\Temp\dropshot.exe.mal.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 2 Modules
| |||||||||||||||
| 1024 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | dropshot.exe.mal.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2084 | cmd /c WMIC Process Call Create "C:\Windows\System32\Wscript.exe //NOLOGO C:\Users\admin\AppData\Local\Temp\C-Dlt-C-Org-T.vbs" | C:\Windows\system32\cmd.exe | — | dropshot.exe.mal.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2720 | WMIC Process Call Create "C:\Windows\System32\Wscript.exe //NOLOGO C:\Users\admin\AppData\Local\Temp\C-Dlt-C-Org-T.vbs" | C:\Windows\System32\Wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3748 | C:\Windows\System32\Wscript.exe //NOLOGO C:\Users\admin\AppData\Local\Temp\C-Dlt-C-Org-T.vbs | C:\Windows\System32\Wscript.exe | — | wmiprvse.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
Total events
39
Read events
39
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
85
Text files
1
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1024 | iexplore.exe | C: | — | |
MD5:— | SHA256:— | |||
| 1024 | iexplore.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-1000\desktop.ini | — | |
MD5:— | SHA256:— | |||
| 1024 | iexplore.exe | C:\$Recycle.Bin\S-1-5-21-1302019708-1500728564-335382590-500\desktop.ini | — | |
MD5:— | SHA256:— | |||
| 1024 | iexplore.exe | C:\autoexec.bat | — | |
MD5:— | SHA256:— | |||
| 1024 | iexplore.exe | C:\config.sys | — | |
MD5:— | SHA256:— | |||
| 1024 | iexplore.exe | C:\MSOCache\All Users\{90140000-0015-0407-0000-0000000FF1CE}-C\AccessMUI.msi | — | |
MD5:— | SHA256:— | |||
| 1024 | iexplore.exe | C:\MSOCache\All Users\{90140000-0015-0407-0000-0000000FF1CE}-C\AccessMUI.xml | — | |
MD5:— | SHA256:— | |||
| 1024 | iexplore.exe | C:\MSOCache\All Users\{90140000-0015-0407-0000-0000000FF1CE}-C\AccLR.cab | — | |
MD5:— | SHA256:— | |||
| 1024 | iexplore.exe | C:\MSOCache\All Users\{90140000-0015-0407-0000-0000000FF1CE}-C\branding.xml | — | |
MD5:— | SHA256:— | |||
| 1024 | iexplore.exe | C:\MSOCache\All Users\{90140000-0015-0407-0000-0000000FF1CE}-C\Setup.xml | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report