| File name: | 62a986c16cdede724c9742f1c825f9e1f0ae5cbbe023dff477f3d6bf0b9e6966.exe |
| Full analysis: | https://app.any.run/tasks/ebc4c639-536c-4a1f-ab0e-8bff1bf911ee |
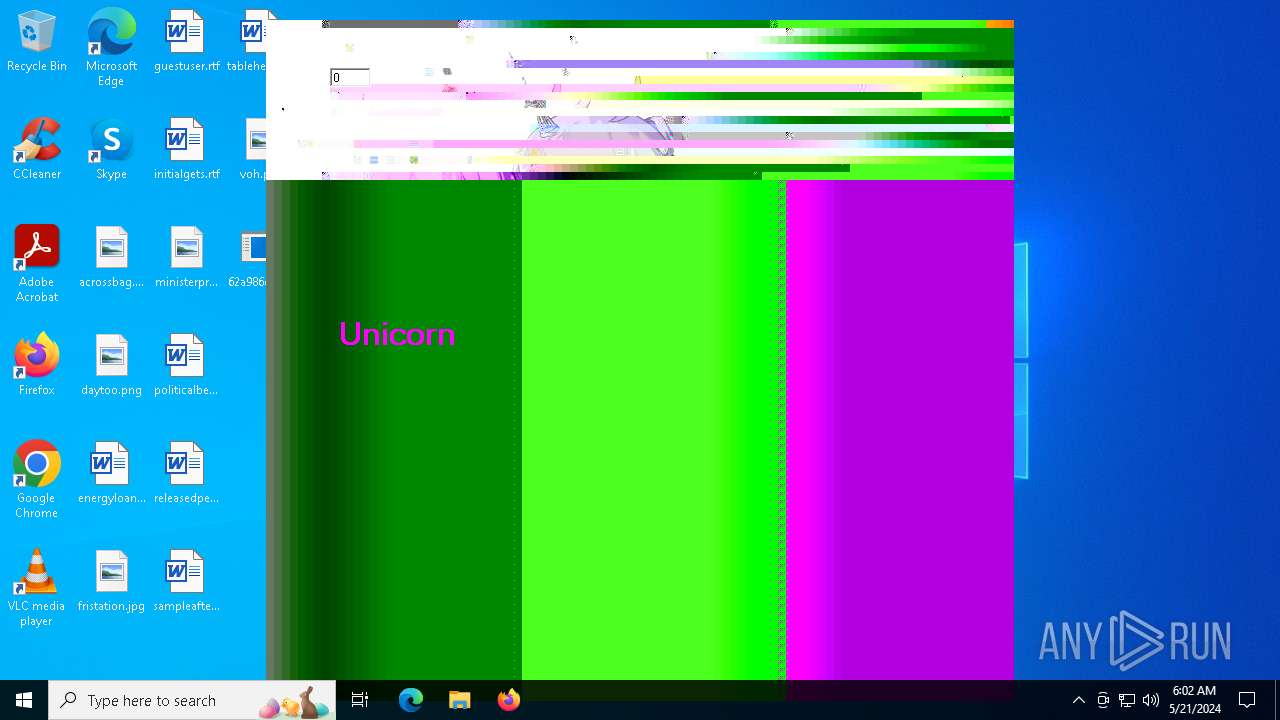
| Verdict: | Malicious activity |
| Analysis date: | May 21, 2024, 06:02:26 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 28ED94A3E2B3A882AAE78DFEBD5808D0 |
| SHA1: | D3C5CA8A33B6209D187A72ADB4A5EF198DE3DC40 |
| SHA256: | 62A986C16CDEDE724C9742F1C825F9E1F0AE5CBBE023DFF477F3D6BF0B9E6966 |
| SSDEEP: | 3072:0KrWbjftvDtqVjpg2kvNW2486RGSD9dsfpfu4+woLc8uIMY:0KrWbjf1D4SVv08y5Sfpfu4+woLc8uI |
MALICIOUS
Drops the executable file immediately after the start
- 62a986c16cdede724c9742f1c825f9e1f0ae5cbbe023dff477f3d6bf0b9e6966.exe (PID: 6480)
- powershell.exe (PID: 6272)
- Unicorn-48311.exe (PID: 6600)
- Unicorn-62431.exe (PID: 6576)
- Unicorn-44974.exe (PID: 6620)
- Unicorn-24679.exe (PID: 6644)
- Unicorn-29509.exe (PID: 6668)
- Unicorn-3822.exe (PID: 6860)
- Unicorn-16437.exe (PID: 6880)
- Unicorn-61575.exe (PID: 6904)
- Unicorn-61575.exe (PID: 6912)
- Unicorn-49375.exe (PID: 6660)
- Unicorn-59581.exe (PID: 6692)
- Unicorn-45727.exe (PID: 7160)
- Unicorn-17309.exe (PID: 6056)
- Unicorn-39287.exe (PID: 6100)
- Unicorn-57853.exe (PID: 3712)
- Unicorn-39479.exe (PID: 1412)
- Unicorn-56007.exe (PID: 1608)
- Unicorn-56007.exe (PID: 5196)
- Unicorn-56007.exe (PID: 4724)
- Unicorn-61575.exe (PID: 6896)
- Unicorn-2317.exe (PID: 4704)
- Unicorn-47277.exe (PID: 6920)
- Unicorn-13252.exe (PID: 1720)
- Unicorn-31607.exe (PID: 380)
- Unicorn-36437.exe (PID: 4108)
- Unicorn-47943.exe (PID: 5032)
- Unicorn-33644.exe (PID: 72)
- Unicorn-28653.exe (PID: 4852)
- Unicorn-23823.exe (PID: 5092)
- Unicorn-32951.exe (PID: 1100)
- Unicorn-37781.exe (PID: 1016)
- Unicorn-41695.exe (PID: 6216)
- Unicorn-58031.exe (PID: 4260)
- Unicorn-58031.exe (PID: 1228)
- Unicorn-56007.exe (PID: 4012)
- Unicorn-15847.exe (PID: 5944)
- Unicorn-15847.exe (PID: 2116)
- Unicorn-56007.exe (PID: 1272)
- Unicorn-32183.exe (PID: 6464)
- Unicorn-32183.exe (PID: 6456)
- Unicorn-32183.exe (PID: 6472)
- Unicorn-32183.exe (PID: 6448)
- Unicorn-37013.exe (PID: 6428)
- Unicorn-2124.exe (PID: 6280)
- Unicorn-47949.exe (PID: 6400)
- Unicorn-12317.exe (PID: 6296)
- Unicorn-2124.exe (PID: 6276)
- Unicorn-58046.exe (PID: 6960)
- Unicorn-21917.exe (PID: 372)
- Unicorn-12109.exe (PID: 6952)
- Unicorn-44310.exe (PID: 2736)
- Unicorn-24311.exe (PID: 6820)
- Unicorn-4253.exe (PID: 6828)
- Unicorn-39687.exe (PID: 5656)
- Unicorn-40071.exe (PID: 4480)
- Unicorn-15182.exe (PID: 4524)
- Unicorn-24015.exe (PID: 6376)
- Unicorn-12037.exe (PID: 5612)
- Unicorn-23351.exe (PID: 7044)
- Unicorn-23351.exe (PID: 7036)
- Unicorn-15182.exe (PID: 5752)
- Unicorn-28181.exe (PID: 7100)
- Unicorn-41917.exe (PID: 7068)
- Unicorn-11845.exe (PID: 7128)
- Unicorn-31991.exe (PID: 308)
- Unicorn-48254.exe (PID: 428)
- Unicorn-50351.exe (PID: 3872)
- Unicorn-309.exe (PID: 7176)
- Unicorn-32863.exe (PID: 3784)
- Unicorn-4829.exe (PID: 5528)
- Unicorn-43645.exe (PID: 7196)
- Unicorn-24415.exe (PID: 7232)
- Unicorn-57663.exe (PID: 7252)
- Unicorn-5125.exe (PID: 7288)
- Unicorn-500.exe (PID: 1964)
- Unicorn-16055.exe (PID: 7216)
- Unicorn-53942.exe (PID: 7308)
- Unicorn-54134.exe (PID: 7272)
- Unicorn-56319.exe (PID: 7328)
- Unicorn-12525.exe (PID: 7368)
- Unicorn-4357.exe (PID: 7380)
- Unicorn-58815.exe (PID: 7408)
- Unicorn-50647.exe (PID: 7444)
- Unicorn-50455.exe (PID: 7540)
- Unicorn-58815.exe (PID: 7416)
- Unicorn-1830.exe (PID: 7584)
- Unicorn-58623.exe (PID: 7468)
- Unicorn-22997.exe (PID: 7648)
- Unicorn-36733.exe (PID: 7656)
- Unicorn-9422.exe (PID: 7500)
- Unicorn-1830.exe (PID: 7580)
- Unicorn-18167.exe (PID: 7628)
- Unicorn-12317.exe (PID: 6284)
- Unicorn-22805.exe (PID: 7764)
- Unicorn-20204.exe (PID: 7736)
- Unicorn-50455.exe (PID: 7548)
- Unicorn-22805.exe (PID: 7780)
- Unicorn-60085.exe (PID: 7804)
- Unicorn-49614.exe (PID: 7884)
- Unicorn-41446.exe (PID: 7892)
- Unicorn-55478.exe (PID: 7704)
- Unicorn-22805.exe (PID: 7772)
- Unicorn-24413.exe (PID: 7876)
- Unicorn-2716.exe (PID: 7836)
- Unicorn-35581.exe (PID: 7908)
- Unicorn-7989.exe (PID: 780)
- Unicorn-48325.exe (PID: 6756)
- Unicorn-32183.exe (PID: 6444)
- Unicorn-65453.exe (PID: 7844)
- Unicorn-16052.exe (PID: 6012)
- Unicorn-37013.exe (PID: 6404)
- Unicorn-2317.exe (PID: 1944)
- Unicorn-20663.exe (PID: 7964)
- Unicorn-30484.exe (PID: 8016)
- Unicorn-17709.exe (PID: 8000)
- Unicorn-54103.exe (PID: 7980)
- Unicorn-28447.exe (PID: 8024)
- Unicorn-6749.exe (PID: 4428)
- Unicorn-17133.exe (PID: 8056)
- Unicorn-44591.exe (PID: 8048)
- Unicorn-26631.exe (PID: 8152)
- Unicorn-34799.exe (PID: 8176)
- Unicorn-53143.exe (PID: 8100)
- Unicorn-52878.exe (PID: 8084)
- Unicorn-34799.exe (PID: 8168)
- Unicorn-53143.exe (PID: 8092)
- Unicorn-59687.exe (PID: 8236)
- Unicorn-34607.exe (PID: 8224)
- Unicorn-64518.exe (PID: 8328)
- Unicorn-51519.exe (PID: 8272)
- Unicorn-27015.exe (PID: 8304)
- Unicorn-51519.exe (PID: 8264)
- Unicorn-31653.exe (PID: 8252)
- Unicorn-55006.exe (PID: 8392)
- Unicorn-52405.exe (PID: 8368)
- Unicorn-404.exe (PID: 8400)
- Unicorn-8373.exe (PID: 8448)
- Unicorn-55006.exe (PID: 8384)
- Unicorn-3588.exe (PID: 8484)
- Unicorn-39053.exe (PID: 8468)
- Unicorn-61277.exe (PID: 8436)
- Unicorn-6189.exe (PID: 8524)
- Unicorn-11446.exe (PID: 8548)
- Unicorn-44311.exe (PID: 8572)
- Unicorn-1093.exe (PID: 8512)
- Unicorn-43735.exe (PID: 8608)
- Unicorn-35567.exe (PID: 8616)
- Unicorn-40589.exe (PID: 8720)
- Unicorn-26173.exe (PID: 8776)
- Unicorn-20772.exe (PID: 8756)
- Unicorn-11062.exe (PID: 8740)
- Unicorn-54134.exe (PID: 8848)
- Unicorn-50455.exe (PID: 7532)
- Unicorn-30590.exe (PID: 8900)
- Unicorn-12317.exe (PID: 6268)
- Unicorn-46815.exe (PID: 9024)
- Unicorn-54599.exe (PID: 9000)
- Unicorn-21735.exe (PID: 8984)
- Unicorn-21159.exe (PID: 9040)
- Unicorn-29327.exe (PID: 9060)
- Unicorn-22909.exe (PID: 8196)
- Unicorn-63942.exe (PID: 6148)
- Unicorn-13374.exe (PID: 9080)
- Unicorn-20317.exe (PID: 9148)
- Unicorn-50581.exe (PID: 9164)
- Unicorn-33860.exe (PID: 9184)
- Unicorn-57597.exe (PID: 9208)
- Unicorn-22887.exe (PID: 9236)
- Unicorn-58055.exe (PID: 9420)
- Unicorn-28869.exe (PID: 9504)
- Unicorn-56903.exe (PID: 9492)
- Unicorn-61926.exe (PID: 9532)
- Unicorn-8086.exe (PID: 9548)
- Unicorn-39117.exe (PID: 7096)
- Unicorn-10486.exe (PID: 8280)
- Unicorn-5886.exe (PID: 9588)
- Unicorn-1934.exe (PID: 8132)
- Unicorn-34349.exe (PID: 9096)
- Unicorn-34349.exe (PID: 9104)
- Unicorn-332.exe (PID: 9604)
- Unicorn-30775.exe (PID: 9620)
- Unicorn-21455.exe (PID: 9700)
- Unicorn-62679.exe (PID: 9652)
- Unicorn-33004.exe (PID: 9636)
- Unicorn-62679.exe (PID: 9656)
- Unicorn-62679.exe (PID: 9668)
- Unicorn-42287.exe (PID: 7560)
- Unicorn-58623.exe (PID: 7476)
- Unicorn-18693.exe (PID: 9792)
- Unicorn-37983.exe (PID: 9716)
- Unicorn-13862.exe (PID: 9732)
- Unicorn-22031.exe (PID: 9764)
- Unicorn-30007.exe (PID: 9860)
- Unicorn-22031.exe (PID: 9748)
- Unicorn-22031.exe (PID: 9756)
- Unicorn-13670.exe (PID: 9828)
- Unicorn-38559.exe (PID: 9800)
- Unicorn-23543.exe (PID: 6508)
- Unicorn-53286.exe (PID: 9880)
- Unicorn-56815.exe (PID: 9896)
- Unicorn-40287.exe (PID: 9932)
- Unicorn-32503.exe (PID: 9956)
- Unicorn-61646.exe (PID: 9996)
- Unicorn-32503.exe (PID: 9948)
- Unicorn-32311.exe (PID: 10016)
- Unicorn-65175.exe (PID: 10032)
- Unicorn-44350.exe (PID: 10096)
- Unicorn-57007.exe (PID: 10052)
- Unicorn-19845.exe (PID: 10088)
- Unicorn-56047.exe (PID: 10136)
- Unicorn-39711.exe (PID: 10104)
- Unicorn-14822.exe (PID: 10168)
- Unicorn-19845.exe (PID: 10080)
- Unicorn-64215.exe (PID: 10124)
- Unicorn-15206.exe (PID: 9300)
- Unicorn-52710.exe (PID: 9312)
- Unicorn-17436.exe (PID: 10232)
- Unicorn-36373.exe (PID: 10256)
- Unicorn-64334.exe (PID: 9316)
- Unicorn-27332.exe (PID: 10376)
- Unicorn-62990.exe (PID: 10276)
- Unicorn-20229.exe (PID: 10248)
- Unicorn-44734.exe (PID: 9280)
- Unicorn-27332.exe (PID: 10372)
- Unicorn-8580.exe (PID: 10532)
- Unicorn-52902.exe (PID: 10216)
- Unicorn-55206.exe (PID: 10436)
- Unicorn-1101.exe (PID: 10516)
- Unicorn-19740.exe (PID: 10476)
- Unicorn-24916.exe (PID: 10552)
- Unicorn-32117.exe (PID: 10648)
- Unicorn-8117.exe (PID: 10600)
- Unicorn-33774.exe (PID: 10452)
- Unicorn-19740.exe (PID: 10484)
- Unicorn-24454.exe (PID: 10608)
- Unicorn-2252.exe (PID: 10592)
- Unicorn-20229.exe (PID: 6492)
- Unicorn-65519.exe (PID: 10584)
- Unicorn-34119.exe (PID: 7508)
SUSPICIOUS
Executable content was dropped or overwritten
- Unicorn-48311.exe (PID: 6600)
- Unicorn-44974.exe (PID: 6620)
- 62a986c16cdede724c9742f1c825f9e1f0ae5cbbe023dff477f3d6bf0b9e6966.exe (PID: 6480)
- Unicorn-24679.exe (PID: 6644)
- Unicorn-29509.exe (PID: 6668)
- Unicorn-3822.exe (PID: 6860)
- Unicorn-16437.exe (PID: 6880)
- Unicorn-61575.exe (PID: 6912)
- Unicorn-59581.exe (PID: 6692)
- Unicorn-49375.exe (PID: 6660)
- Unicorn-62431.exe (PID: 6576)
- Unicorn-45727.exe (PID: 7160)
- Unicorn-17309.exe (PID: 6056)
- Unicorn-39287.exe (PID: 6100)
- Unicorn-57853.exe (PID: 3712)
- Unicorn-39479.exe (PID: 1412)
- Unicorn-56007.exe (PID: 1608)
- Unicorn-56007.exe (PID: 5196)
- Unicorn-56007.exe (PID: 4724)
- Unicorn-61575.exe (PID: 6896)
- Unicorn-2317.exe (PID: 4704)
- Unicorn-47277.exe (PID: 6920)
- Unicorn-13252.exe (PID: 1720)
- Unicorn-31607.exe (PID: 380)
- Unicorn-61575.exe (PID: 6904)
- Unicorn-36437.exe (PID: 4108)
- Unicorn-23823.exe (PID: 5092)
- Unicorn-47943.exe (PID: 5032)
- Unicorn-33644.exe (PID: 72)
- Unicorn-28653.exe (PID: 4852)
- Unicorn-32951.exe (PID: 1100)
- Unicorn-41695.exe (PID: 6216)
- Unicorn-58031.exe (PID: 4260)
- Unicorn-58031.exe (PID: 1228)
- Unicorn-37781.exe (PID: 1016)
- Unicorn-56007.exe (PID: 4012)
- Unicorn-15847.exe (PID: 5944)
- Unicorn-15847.exe (PID: 2116)
- Unicorn-56007.exe (PID: 1272)
- Unicorn-32183.exe (PID: 6456)
- Unicorn-32183.exe (PID: 6472)
- Unicorn-32183.exe (PID: 6448)
- Unicorn-32183.exe (PID: 6464)
- Unicorn-37013.exe (PID: 6428)
- Unicorn-2124.exe (PID: 6280)
- Unicorn-12317.exe (PID: 6296)
- Unicorn-47949.exe (PID: 6400)
- Unicorn-2124.exe (PID: 6276)
- Unicorn-21917.exe (PID: 372)
- Unicorn-58046.exe (PID: 6960)
- Unicorn-44310.exe (PID: 2736)
- Unicorn-12109.exe (PID: 6952)
- Unicorn-24311.exe (PID: 6820)
- Unicorn-4253.exe (PID: 6828)
- Unicorn-500.exe (PID: 1964)
- Unicorn-40071.exe (PID: 4480)
- Unicorn-12037.exe (PID: 5612)
- Unicorn-39687.exe (PID: 5656)
- Unicorn-15182.exe (PID: 4524)
- Unicorn-24015.exe (PID: 6376)
- Unicorn-23351.exe (PID: 7044)
- Unicorn-23351.exe (PID: 7036)
- Unicorn-15182.exe (PID: 5752)
- Unicorn-41917.exe (PID: 7068)
- Unicorn-28181.exe (PID: 7100)
- Unicorn-11845.exe (PID: 7128)
- Unicorn-31991.exe (PID: 308)
- Unicorn-48254.exe (PID: 428)
- Unicorn-4829.exe (PID: 5528)
- Unicorn-50351.exe (PID: 3872)
- Unicorn-32863.exe (PID: 3784)
- Unicorn-309.exe (PID: 7176)
- Unicorn-16055.exe (PID: 7216)
- Unicorn-43645.exe (PID: 7196)
- Unicorn-24415.exe (PID: 7232)
- Unicorn-5125.exe (PID: 7288)
- Unicorn-57663.exe (PID: 7252)
- Unicorn-53942.exe (PID: 7308)
- Unicorn-54134.exe (PID: 7272)
- Unicorn-56319.exe (PID: 7328)
- Unicorn-12525.exe (PID: 7368)
- Unicorn-4357.exe (PID: 7380)
- Unicorn-58815.exe (PID: 7416)
- Unicorn-58815.exe (PID: 7408)
- Unicorn-50455.exe (PID: 7540)
- Unicorn-50647.exe (PID: 7444)
- Unicorn-1830.exe (PID: 7584)
- Unicorn-58623.exe (PID: 7468)
- Unicorn-22997.exe (PID: 7648)
- Unicorn-36733.exe (PID: 7656)
- Unicorn-12317.exe (PID: 6284)
- Unicorn-9422.exe (PID: 7500)
- Unicorn-1830.exe (PID: 7580)
- Unicorn-18167.exe (PID: 7628)
- Unicorn-22805.exe (PID: 7780)
- Unicorn-22805.exe (PID: 7764)
- Unicorn-50455.exe (PID: 7548)
- Unicorn-20204.exe (PID: 7736)
- Unicorn-60085.exe (PID: 7804)
- Unicorn-49614.exe (PID: 7884)
- Unicorn-41446.exe (PID: 7892)
- Unicorn-55478.exe (PID: 7704)
- Unicorn-24413.exe (PID: 7876)
- Unicorn-22805.exe (PID: 7772)
- Unicorn-2716.exe (PID: 7836)
- Unicorn-35581.exe (PID: 7908)
- Unicorn-7989.exe (PID: 780)
- Unicorn-48325.exe (PID: 6756)
- Unicorn-65453.exe (PID: 7844)
- Unicorn-32183.exe (PID: 6444)
- Unicorn-2317.exe (PID: 1944)
- Unicorn-37013.exe (PID: 6404)
- Unicorn-16052.exe (PID: 6012)
- Unicorn-20663.exe (PID: 7964)
- Unicorn-30484.exe (PID: 8016)
- Unicorn-17709.exe (PID: 8000)
- Unicorn-54103.exe (PID: 7980)
- Unicorn-28447.exe (PID: 8024)
- Unicorn-17133.exe (PID: 8056)
- Unicorn-6749.exe (PID: 4428)
- Unicorn-44591.exe (PID: 8048)
- Unicorn-26631.exe (PID: 8152)
- Unicorn-34799.exe (PID: 8176)
- Unicorn-53143.exe (PID: 8100)
- Unicorn-52878.exe (PID: 8084)
- Unicorn-34799.exe (PID: 8168)
- Unicorn-53143.exe (PID: 8092)
- Unicorn-64518.exe (PID: 8328)
- Unicorn-51519.exe (PID: 8272)
- Unicorn-34607.exe (PID: 8224)
- Unicorn-59687.exe (PID: 8236)
- Unicorn-27015.exe (PID: 8304)
- Unicorn-51519.exe (PID: 8264)
- Unicorn-31653.exe (PID: 8252)
- Unicorn-55006.exe (PID: 8392)
- Unicorn-52405.exe (PID: 8368)
- Unicorn-404.exe (PID: 8400)
- Unicorn-55006.exe (PID: 8384)
- Unicorn-3588.exe (PID: 8484)
- Unicorn-39053.exe (PID: 8468)
- Unicorn-61277.exe (PID: 8436)
- Unicorn-8373.exe (PID: 8448)
- Unicorn-1093.exe (PID: 8512)
- Unicorn-6189.exe (PID: 8524)
- Unicorn-11446.exe (PID: 8548)
- Unicorn-43735.exe (PID: 8608)
- Unicorn-40589.exe (PID: 8720)
- Unicorn-44311.exe (PID: 8572)
- Unicorn-35567.exe (PID: 8616)
- Unicorn-11062.exe (PID: 8740)
- Unicorn-20772.exe (PID: 8756)
- Unicorn-26173.exe (PID: 8776)
- Unicorn-54134.exe (PID: 8848)
- Unicorn-50455.exe (PID: 7532)
- Unicorn-30590.exe (PID: 8900)
- Unicorn-12317.exe (PID: 6268)
- Unicorn-54599.exe (PID: 9000)
- Unicorn-21735.exe (PID: 8984)
- Unicorn-46815.exe (PID: 9024)
- Unicorn-21159.exe (PID: 9040)
- Unicorn-29327.exe (PID: 9060)
- Unicorn-22909.exe (PID: 8196)
- Unicorn-63942.exe (PID: 6148)
- Unicorn-13374.exe (PID: 9080)
- Unicorn-20317.exe (PID: 9148)
- Unicorn-50581.exe (PID: 9164)
- Unicorn-33860.exe (PID: 9184)
- Unicorn-57597.exe (PID: 9208)
- Unicorn-22887.exe (PID: 9236)
- Unicorn-58055.exe (PID: 9420)
- Unicorn-28869.exe (PID: 9504)
- Unicorn-56903.exe (PID: 9492)
- Unicorn-61926.exe (PID: 9532)
- Unicorn-8086.exe (PID: 9548)
- Unicorn-39117.exe (PID: 7096)
- Unicorn-5886.exe (PID: 9588)
- Unicorn-1934.exe (PID: 8132)
- Unicorn-10486.exe (PID: 8280)
- Unicorn-34349.exe (PID: 9104)
- Unicorn-34349.exe (PID: 9096)
- Unicorn-332.exe (PID: 9604)
- Unicorn-30775.exe (PID: 9620)
- Unicorn-21455.exe (PID: 9700)
- Unicorn-33004.exe (PID: 9636)
- Unicorn-62679.exe (PID: 9656)
- Unicorn-62679.exe (PID: 9668)
- Unicorn-42287.exe (PID: 7560)
- Unicorn-58623.exe (PID: 7476)
- Unicorn-62679.exe (PID: 9652)
- Unicorn-18693.exe (PID: 9792)
- Unicorn-37983.exe (PID: 9716)
- Unicorn-13862.exe (PID: 9732)
- Unicorn-30007.exe (PID: 9860)
- Unicorn-22031.exe (PID: 9764)
- Unicorn-22031.exe (PID: 9748)
- Unicorn-13670.exe (PID: 9828)
- Unicorn-22031.exe (PID: 9756)
- Unicorn-38559.exe (PID: 9800)
- Unicorn-23543.exe (PID: 6508)
- Unicorn-53286.exe (PID: 9880)
- Unicorn-56815.exe (PID: 9896)
- Unicorn-40287.exe (PID: 9932)
- Unicorn-32503.exe (PID: 9956)
- Unicorn-61646.exe (PID: 9996)
- Unicorn-32503.exe (PID: 9948)
- Unicorn-32311.exe (PID: 10016)
- Unicorn-65175.exe (PID: 10032)
- Unicorn-44350.exe (PID: 10096)
- Unicorn-57007.exe (PID: 10052)
- Unicorn-19845.exe (PID: 10088)
- Unicorn-56047.exe (PID: 10136)
- Unicorn-14822.exe (PID: 10168)
- Unicorn-64215.exe (PID: 10124)
- Unicorn-39711.exe (PID: 10104)
- Unicorn-19845.exe (PID: 10080)
- Unicorn-15206.exe (PID: 9300)
- Unicorn-52710.exe (PID: 9312)
- Unicorn-17436.exe (PID: 10232)
- Unicorn-36373.exe (PID: 10256)
- Unicorn-27332.exe (PID: 10376)
- Unicorn-52902.exe (PID: 10216)
- Unicorn-62990.exe (PID: 10276)
- Unicorn-20229.exe (PID: 10248)
- Unicorn-27332.exe (PID: 10372)
- Unicorn-44734.exe (PID: 9280)
- Unicorn-8580.exe (PID: 10532)
- Unicorn-64334.exe (PID: 9316)
- Unicorn-19740.exe (PID: 10484)
- Unicorn-1101.exe (PID: 10516)
- Unicorn-32117.exe (PID: 10648)
- Unicorn-19740.exe (PID: 10476)
- Unicorn-24916.exe (PID: 10552)
- Unicorn-8117.exe (PID: 10600)
- Unicorn-33774.exe (PID: 10452)
- Unicorn-55206.exe (PID: 10436)
- Unicorn-24454.exe (PID: 10608)
- Unicorn-2252.exe (PID: 10592)
- Unicorn-20229.exe (PID: 6492)
- Unicorn-34119.exe (PID: 7508)
- Unicorn-65519.exe (PID: 10584)
Starts itself from another location
- Unicorn-48311.exe (PID: 6600)
- Unicorn-62431.exe (PID: 6576)
- 62a986c16cdede724c9742f1c825f9e1f0ae5cbbe023dff477f3d6bf0b9e6966.exe (PID: 6480)
- Unicorn-44974.exe (PID: 6620)
- Unicorn-24679.exe (PID: 6644)
- Unicorn-49375.exe (PID: 6660)
- Unicorn-3822.exe (PID: 6860)
- Unicorn-16437.exe (PID: 6880)
- Unicorn-61575.exe (PID: 6904)
- Unicorn-61575.exe (PID: 6912)
- Unicorn-61575.exe (PID: 6896)
- Unicorn-58046.exe (PID: 6960)
- Unicorn-29509.exe (PID: 6668)
- Unicorn-45727.exe (PID: 7160)
- Unicorn-17309.exe (PID: 6056)
- Unicorn-39287.exe (PID: 6100)
- Unicorn-57853.exe (PID: 3712)
- Unicorn-39479.exe (PID: 1412)
- Unicorn-56007.exe (PID: 5196)
- Unicorn-56007.exe (PID: 4012)
- Unicorn-56007.exe (PID: 1272)
- Unicorn-56007.exe (PID: 4724)
- Unicorn-56007.exe (PID: 1608)
- Unicorn-13252.exe (PID: 1720)
- Unicorn-21917.exe (PID: 372)
- Unicorn-2317.exe (PID: 1944)
- Unicorn-2317.exe (PID: 4704)
- Unicorn-47277.exe (PID: 6920)
- Unicorn-31607.exe (PID: 380)
- Unicorn-12109.exe (PID: 6952)
- Unicorn-36437.exe (PID: 4108)
- Unicorn-47943.exe (PID: 5032)
- Unicorn-33644.exe (PID: 72)
- Unicorn-23823.exe (PID: 5092)
- Unicorn-28653.exe (PID: 4852)
- Unicorn-48254.exe (PID: 428)
- Unicorn-31991.exe (PID: 308)
- Unicorn-37781.exe (PID: 1016)
- Unicorn-59581.exe (PID: 6692)
- Unicorn-41695.exe (PID: 6216)
- Unicorn-58031.exe (PID: 4260)
- Unicorn-58031.exe (PID: 1228)
- Unicorn-15847.exe (PID: 5944)
- Unicorn-32183.exe (PID: 6456)
- Unicorn-12317.exe (PID: 6268)
- Unicorn-12317.exe (PID: 6284)
- Unicorn-37013.exe (PID: 6428)
- Unicorn-2124.exe (PID: 6280)
- Unicorn-37013.exe (PID: 6404)
- Unicorn-47949.exe (PID: 6400)
- Unicorn-32183.exe (PID: 6444)
- Unicorn-48325.exe (PID: 6756)
- Unicorn-44310.exe (PID: 2736)
- Unicorn-16052.exe (PID: 6012)
- Unicorn-24311.exe (PID: 6820)
- Unicorn-4253.exe (PID: 6828)
- Unicorn-23543.exe (PID: 6508)
- Unicorn-39687.exe (PID: 5656)
- Unicorn-500.exe (PID: 1964)
- Unicorn-40071.exe (PID: 4480)
- Unicorn-23351.exe (PID: 7044)
- Unicorn-6749.exe (PID: 4428)
- Unicorn-15182.exe (PID: 4524)
- Unicorn-32183.exe (PID: 6448)
- Unicorn-24015.exe (PID: 6376)
- Unicorn-12037.exe (PID: 5612)
- Unicorn-23351.exe (PID: 7036)
- Unicorn-11845.exe (PID: 7128)
- Unicorn-41917.exe (PID: 7068)
- Unicorn-4829.exe (PID: 5528)
- Unicorn-50351.exe (PID: 3872)
- Unicorn-309.exe (PID: 7176)
- Unicorn-32951.exe (PID: 1100)
- Unicorn-43645.exe (PID: 7196)
- Unicorn-57663.exe (PID: 7252)
- Unicorn-24415.exe (PID: 7232)
- Unicorn-5125.exe (PID: 7288)
- Unicorn-16055.exe (PID: 7216)
- Unicorn-53942.exe (PID: 7308)
- Unicorn-54134.exe (PID: 7272)
- Unicorn-56319.exe (PID: 7328)
- Unicorn-15847.exe (PID: 2116)
- Unicorn-58815.exe (PID: 7416)
- Unicorn-58815.exe (PID: 7408)
- Unicorn-58623.exe (PID: 7476)
- Unicorn-50647.exe (PID: 7444)
- Unicorn-1830.exe (PID: 7584)
- Unicorn-58623.exe (PID: 7468)
- Unicorn-22997.exe (PID: 7648)
- Unicorn-36733.exe (PID: 7656)
- Unicorn-18167.exe (PID: 7628)
- Unicorn-9422.exe (PID: 7500)
- Unicorn-1830.exe (PID: 7580)
- Unicorn-32183.exe (PID: 6464)
- Unicorn-22805.exe (PID: 7764)
- Unicorn-20204.exe (PID: 7736)
- Unicorn-22805.exe (PID: 7780)
- Unicorn-60085.exe (PID: 7804)
- Unicorn-41446.exe (PID: 7892)
- Unicorn-55478.exe (PID: 7704)
- Unicorn-32183.exe (PID: 6472)
- Unicorn-24413.exe (PID: 7876)
- Unicorn-65453.exe (PID: 7844)
- Unicorn-2124.exe (PID: 6276)
- Unicorn-12317.exe (PID: 6296)
- Unicorn-35581.exe (PID: 7908)
- Unicorn-20663.exe (PID: 7964)
- Unicorn-54103.exe (PID: 7980)
- Unicorn-17709.exe (PID: 8000)
- Unicorn-15182.exe (PID: 5752)
- Unicorn-17133.exe (PID: 8056)
- Unicorn-39117.exe (PID: 7096)
- Unicorn-44591.exe (PID: 8048)
- Unicorn-52878.exe (PID: 8084)
- Unicorn-26631.exe (PID: 8152)
- Unicorn-53143.exe (PID: 8100)
- Unicorn-34799.exe (PID: 8168)
- Unicorn-1934.exe (PID: 8132)
- Unicorn-53143.exe (PID: 8092)
- Unicorn-34799.exe (PID: 8176)
- Unicorn-59687.exe (PID: 8236)
- Unicorn-32863.exe (PID: 3784)
- Unicorn-34607.exe (PID: 8224)
- Unicorn-64518.exe (PID: 8328)
- Unicorn-22909.exe (PID: 8196)
- Unicorn-63942.exe (PID: 6148)
- Unicorn-31653.exe (PID: 8252)
- Unicorn-27015.exe (PID: 8304)
- Unicorn-51519.exe (PID: 8264)
- Unicorn-55006.exe (PID: 8392)
- Unicorn-52405.exe (PID: 8368)
- Unicorn-404.exe (PID: 8400)
- Unicorn-8373.exe (PID: 8448)
- Unicorn-3588.exe (PID: 8484)
- Unicorn-55006.exe (PID: 8384)
- Unicorn-39053.exe (PID: 8468)
- Unicorn-61277.exe (PID: 8436)
- Unicorn-1093.exe (PID: 8512)
- Unicorn-6189.exe (PID: 8524)
- Unicorn-11446.exe (PID: 8548)
- Unicorn-44311.exe (PID: 8572)
- Unicorn-43735.exe (PID: 8608)
- Unicorn-40589.exe (PID: 8720)
- Unicorn-35567.exe (PID: 8616)
- Unicorn-20772.exe (PID: 8756)
- Unicorn-11062.exe (PID: 8740)
- Unicorn-4357.exe (PID: 7380)
- Unicorn-54134.exe (PID: 8848)
- Unicorn-50455.exe (PID: 7540)
- Unicorn-50455.exe (PID: 7548)
- Unicorn-30590.exe (PID: 8900)
- Unicorn-6469.exe (PID: 7728)
- Unicorn-49614.exe (PID: 7884)
- Unicorn-2716.exe (PID: 7836)
- Unicorn-7989.exe (PID: 780)
- Unicorn-28447.exe (PID: 8024)
- Unicorn-22805.exe (PID: 7772)
- Unicorn-30484.exe (PID: 8016)
- Unicorn-54599.exe (PID: 9000)
- Unicorn-21735.exe (PID: 8984)
- Unicorn-29327.exe (PID: 9060)
- Unicorn-10486.exe (PID: 8280)
- Unicorn-51519.exe (PID: 8272)
- Unicorn-13374.exe (PID: 9080)
- Unicorn-28181.exe (PID: 7100)
- Unicorn-20317.exe (PID: 9148)
- Unicorn-50581.exe (PID: 9164)
- Unicorn-33860.exe (PID: 9184)
- Unicorn-26173.exe (PID: 8776)
- Unicorn-57597.exe (PID: 9208)
- Unicorn-22887.exe (PID: 9236)
- Unicorn-12525.exe (PID: 7368)
- Unicorn-34119.exe (PID: 7508)
- Unicorn-42287.exe (PID: 7560)
- Unicorn-50455.exe (PID: 7532)
- Unicorn-58055.exe (PID: 9420)
- Unicorn-56903.exe (PID: 9492)
- Unicorn-28869.exe (PID: 9504)
- Unicorn-61926.exe (PID: 9532)
- Unicorn-8086.exe (PID: 9548)
- Unicorn-46815.exe (PID: 9024)
- Unicorn-21159.exe (PID: 9040)
- Unicorn-5886.exe (PID: 9588)
- Unicorn-34349.exe (PID: 9096)
- Unicorn-34349.exe (PID: 9104)
- Unicorn-332.exe (PID: 9604)
- Unicorn-30775.exe (PID: 9620)
- Unicorn-62679.exe (PID: 9652)
- Unicorn-62679.exe (PID: 9668)
- Unicorn-37983.exe (PID: 9716)
- Unicorn-18693.exe (PID: 9792)
- Unicorn-22031.exe (PID: 9764)
- Unicorn-13862.exe (PID: 9732)
- Unicorn-30007.exe (PID: 9860)
- Unicorn-13670.exe (PID: 9828)
- Unicorn-22031.exe (PID: 9748)
- Unicorn-38559.exe (PID: 9800)
- Unicorn-22031.exe (PID: 9756)
- Unicorn-53286.exe (PID: 9880)
- Unicorn-40287.exe (PID: 9932)
- Unicorn-61646.exe (PID: 9996)
- Unicorn-32311.exe (PID: 10016)
- Unicorn-65175.exe (PID: 10032)
- Unicorn-33004.exe (PID: 9636)
- Unicorn-62679.exe (PID: 9656)
- Unicorn-44350.exe (PID: 10096)
- Unicorn-21455.exe (PID: 9700)
- Unicorn-19845.exe (PID: 10088)
- Unicorn-56047.exe (PID: 10136)
- Unicorn-14822.exe (PID: 10168)
- Unicorn-39711.exe (PID: 10104)
- Unicorn-64215.exe (PID: 10124)
- Unicorn-19845.exe (PID: 10080)
- Unicorn-15206.exe (PID: 9300)
- Unicorn-52710.exe (PID: 9312)
- Unicorn-56815.exe (PID: 9896)
- Unicorn-17436.exe (PID: 10232)
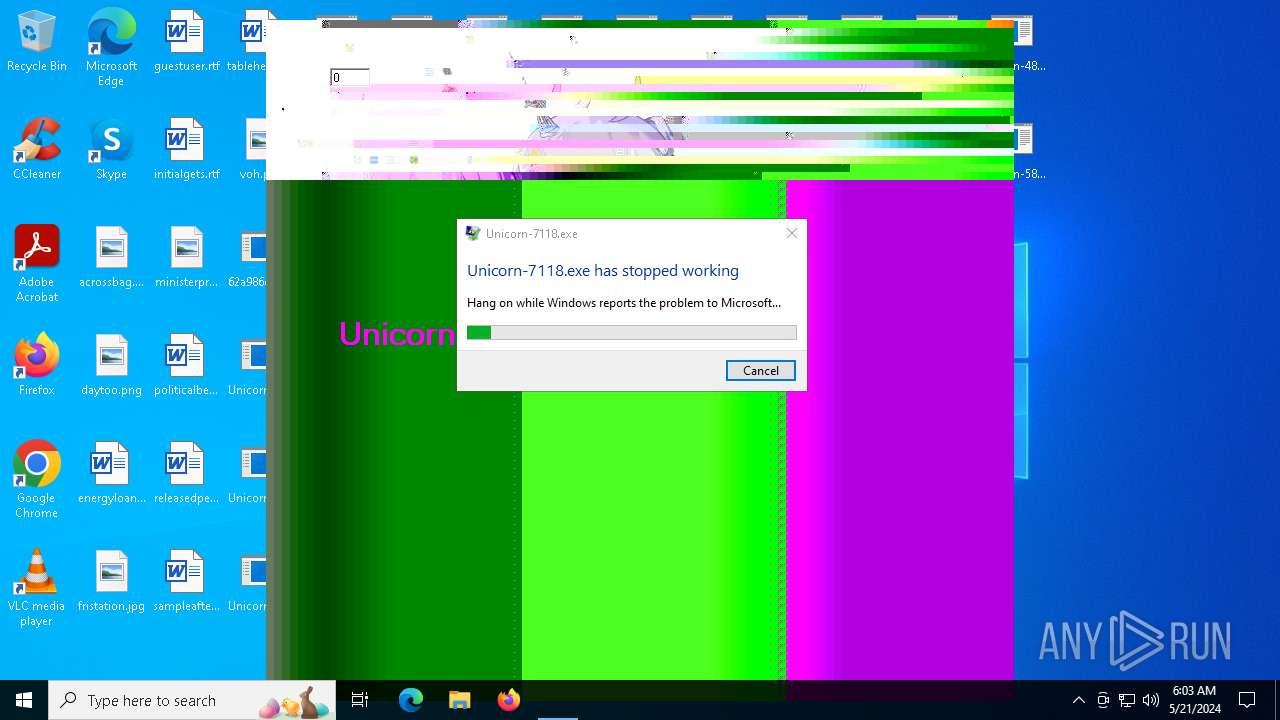
Executes application which crashes
- Unicorn-7118.exe (PID: 7348)
- Unicorn-24335.exe (PID: 9980)
INFO
Checks supported languages
- 62a986c16cdede724c9742f1c825f9e1f0ae5cbbe023dff477f3d6bf0b9e6966.exe (PID: 6480)
- Unicorn-44974.exe (PID: 6620)
- Unicorn-24679.exe (PID: 6644)
- Unicorn-62431.exe (PID: 6576)
- Unicorn-29509.exe (PID: 6668)
- Unicorn-49375.exe (PID: 6660)
- Unicorn-59581.exe (PID: 6692)
- Unicorn-3822.exe (PID: 6860)
- Unicorn-16437.exe (PID: 6880)
- Unicorn-61575.exe (PID: 6896)
- Unicorn-47277.exe (PID: 6920)
- Unicorn-12109.exe (PID: 6952)
- Unicorn-61575.exe (PID: 6912)
- Unicorn-61575.exe (PID: 6904)
- Unicorn-58046.exe (PID: 6960)
- Unicorn-45727.exe (PID: 7160)
- Unicorn-39287.exe (PID: 6100)
- Unicorn-57853.exe (PID: 3712)
- Unicorn-17309.exe (PID: 6056)
- Unicorn-39479.exe (PID: 1412)
- Unicorn-56007.exe (PID: 1272)
- Unicorn-56007.exe (PID: 1608)
- Unicorn-56007.exe (PID: 4012)
- Unicorn-56007.exe (PID: 4724)
- Unicorn-44310.exe (PID: 2736)
- Unicorn-21917.exe (PID: 372)
- Unicorn-2317.exe (PID: 4704)
- Unicorn-16052.exe (PID: 6012)
- Unicorn-13252.exe (PID: 1720)
- Unicorn-2317.exe (PID: 1944)
- Unicorn-56007.exe (PID: 5196)
- Unicorn-48311.exe (PID: 6600)
- Unicorn-31607.exe (PID: 380)
- Unicorn-33644.exe (PID: 72)
- Unicorn-47943.exe (PID: 5032)
- Unicorn-36437.exe (PID: 4108)
- Unicorn-31991.exe (PID: 308)
- Unicorn-23823.exe (PID: 5092)
- Unicorn-32951.exe (PID: 1100)
- Unicorn-48254.exe (PID: 428)
- Unicorn-28653.exe (PID: 4852)
- Unicorn-37781.exe (PID: 1016)
- Unicorn-58031.exe (PID: 1228)
- Unicorn-58031.exe (PID: 4260)
- Unicorn-15847.exe (PID: 2116)
- Unicorn-41695.exe (PID: 6216)
- Unicorn-15847.exe (PID: 5944)
- Unicorn-24015.exe (PID: 6376)
- Unicorn-12317.exe (PID: 6284)
- Unicorn-12317.exe (PID: 6296)
- Unicorn-32183.exe (PID: 6464)
- Unicorn-32183.exe (PID: 6456)
- Unicorn-32183.exe (PID: 6444)
- Unicorn-32183.exe (PID: 6472)
- Unicorn-32183.exe (PID: 6448)
- Unicorn-37013.exe (PID: 6404)
- Unicorn-37013.exe (PID: 6428)
- Unicorn-47949.exe (PID: 6400)
- Unicorn-2124.exe (PID: 6276)
- Unicorn-2124.exe (PID: 6280)
- Unicorn-7989.exe (PID: 780)
- Unicorn-48325.exe (PID: 6756)
- Unicorn-4253.exe (PID: 6828)
- Unicorn-24311.exe (PID: 6820)
- Unicorn-12317.exe (PID: 6268)
- Unicorn-500.exe (PID: 1964)
- Unicorn-23543.exe (PID: 6508)
- Unicorn-40071.exe (PID: 4480)
- Unicorn-12037.exe (PID: 5612)
- Unicorn-39687.exe (PID: 5656)
- Unicorn-6749.exe (PID: 4428)
- Unicorn-23351.exe (PID: 7044)
- Unicorn-23351.exe (PID: 7036)
- Unicorn-15182.exe (PID: 4524)
- Unicorn-15182.exe (PID: 5752)
- Unicorn-11845.exe (PID: 7128)
- Unicorn-28181.exe (PID: 7100)
- Unicorn-41917.exe (PID: 7068)
- Unicorn-39117.exe (PID: 7096)
- Unicorn-50351.exe (PID: 3872)
- Unicorn-4829.exe (PID: 5528)
- Unicorn-32863.exe (PID: 3784)
- Unicorn-309.exe (PID: 7176)
- Unicorn-24415.exe (PID: 7232)
- Unicorn-16055.exe (PID: 7216)
- Unicorn-54134.exe (PID: 7272)
- Unicorn-57663.exe (PID: 7252)
- Unicorn-43645.exe (PID: 7196)
- Unicorn-53942.exe (PID: 7308)
- Unicorn-56319.exe (PID: 7328)
- Unicorn-7118.exe (PID: 7348)
- Unicorn-4357.exe (PID: 7380)
- Unicorn-12525.exe (PID: 7368)
- Unicorn-5125.exe (PID: 7288)
- Unicorn-58815.exe (PID: 7408)
- Unicorn-58623.exe (PID: 7468)
- Unicorn-58815.exe (PID: 7416)
- Unicorn-50647.exe (PID: 7444)
- Unicorn-58623.exe (PID: 7476)
- Unicorn-34119.exe (PID: 7508)
- Unicorn-9422.exe (PID: 7500)
- Unicorn-50455.exe (PID: 7540)
- Unicorn-50455.exe (PID: 7532)
- Unicorn-1830.exe (PID: 7580)
- Unicorn-1830.exe (PID: 7584)
- Unicorn-36733.exe (PID: 7656)
- Unicorn-22997.exe (PID: 7648)
- Unicorn-55478.exe (PID: 7704)
- Unicorn-42287.exe (PID: 7560)
- Unicorn-50455.exe (PID: 7548)
- Unicorn-18167.exe (PID: 7628)
- Unicorn-22805.exe (PID: 7772)
- Unicorn-6469.exe (PID: 7728)
- Unicorn-60085.exe (PID: 7804)
- Unicorn-20204.exe (PID: 7736)
- Unicorn-22805.exe (PID: 7764)
- Unicorn-22805.exe (PID: 7780)
- Unicorn-65453.exe (PID: 7844)
- Unicorn-2716.exe (PID: 7836)
- Unicorn-49614.exe (PID: 7884)
- Unicorn-24413.exe (PID: 7876)
- Unicorn-35581.exe (PID: 7908)
- Unicorn-20663.exe (PID: 7964)
- Unicorn-17709.exe (PID: 8000)
- Unicorn-41446.exe (PID: 7892)
- Unicorn-33311.exe (PID: 7900)
- Unicorn-54103.exe (PID: 7980)
- Unicorn-30484.exe (PID: 8016)
- Unicorn-17133.exe (PID: 8056)
- Unicorn-1934.exe (PID: 8132)
- Unicorn-52878.exe (PID: 8084)
- Unicorn-53143.exe (PID: 8092)
- Unicorn-53143.exe (PID: 8100)
- Unicorn-28447.exe (PID: 8024)
- Unicorn-44591.exe (PID: 8048)
- Unicorn-26631.exe (PID: 8152)
- Unicorn-34799.exe (PID: 8168)
- Unicorn-34799.exe (PID: 8176)
- Unicorn-63942.exe (PID: 6148)
- Unicorn-22909.exe (PID: 8196)
- Unicorn-34607.exe (PID: 8224)
- Unicorn-59687.exe (PID: 8236)
- Unicorn-31653.exe (PID: 8252)
- Unicorn-10486.exe (PID: 8280)
- Unicorn-51519.exe (PID: 8272)
- Unicorn-51519.exe (PID: 8264)
- Unicorn-64518.exe (PID: 8328)
- Unicorn-52405.exe (PID: 8368)
- Unicorn-55006.exe (PID: 8384)
- Unicorn-404.exe (PID: 8400)
- Unicorn-61277.exe (PID: 8436)
- Unicorn-8373.exe (PID: 8448)
- Unicorn-39053.exe (PID: 8468)
- Unicorn-3588.exe (PID: 8484)
- Unicorn-6189.exe (PID: 8524)
- Unicorn-1093.exe (PID: 8512)
- Unicorn-27015.exe (PID: 8304)
- Unicorn-55006.exe (PID: 8392)
- Unicorn-44311.exe (PID: 8572)
- Unicorn-11446.exe (PID: 8548)
- Unicorn-53749.exe (PID: 8624)
- Unicorn-43735.exe (PID: 8608)
- Unicorn-35567.exe (PID: 8616)
- Unicorn-11062.exe (PID: 8740)
- Unicorn-40589.exe (PID: 8720)
- Unicorn-20772.exe (PID: 8756)
- Unicorn-26173.exe (PID: 8776)
- Unicorn-54134.exe (PID: 8848)
- Unicorn-30590.exe (PID: 8900)
- Unicorn-21735.exe (PID: 8984)
- Unicorn-54599.exe (PID: 9000)
- Unicorn-46815.exe (PID: 9024)
- Unicorn-21159.exe (PID: 9040)
- Unicorn-29327.exe (PID: 9060)
- Unicorn-13374.exe (PID: 9080)
- Unicorn-34349.exe (PID: 9104)
- Unicorn-34349.exe (PID: 9096)
- Unicorn-33860.exe (PID: 9184)
- Unicorn-50581.exe (PID: 9164)
- Unicorn-20317.exe (PID: 9148)
- Unicorn-57597.exe (PID: 9208)
- Unicorn-22887.exe (PID: 9236)
- Unicorn-58055.exe (PID: 9420)
- Unicorn-28869.exe (PID: 9504)
- Unicorn-56903.exe (PID: 9492)
- Unicorn-61926.exe (PID: 9532)
- Unicorn-5886.exe (PID: 9588)
- Unicorn-332.exe (PID: 9604)
- Unicorn-33004.exe (PID: 9636)
- Unicorn-62679.exe (PID: 9668)
- Unicorn-62679.exe (PID: 9656)
- Unicorn-8086.exe (PID: 9548)
- Unicorn-30775.exe (PID: 9620)
- Unicorn-37983.exe (PID: 9716)
- Unicorn-13862.exe (PID: 9732)
- Unicorn-62679.exe (PID: 9652)
- Unicorn-21455.exe (PID: 9700)
- Unicorn-22031.exe (PID: 9764)
- Unicorn-22031.exe (PID: 9748)
- Unicorn-13670.exe (PID: 9828)
- Unicorn-30007.exe (PID: 9860)
- Unicorn-22031.exe (PID: 9756)
- Unicorn-18693.exe (PID: 9792)
- Unicorn-38559.exe (PID: 9800)
- Unicorn-56815.exe (PID: 9896)
- Unicorn-7422.exe (PID: 9912)
- Unicorn-40287.exe (PID: 9932)
- Unicorn-32503.exe (PID: 9948)
- Unicorn-53286.exe (PID: 9880)
- Unicorn-24335.exe (PID: 9980)
- Unicorn-61646.exe (PID: 9996)
- Unicorn-57007.exe (PID: 10052)
- Unicorn-32311.exe (PID: 10016)
- Unicorn-65175.exe (PID: 10032)
- Unicorn-32503.exe (PID: 9956)
- Unicorn-19845.exe (PID: 10088)
- Unicorn-19845.exe (PID: 10080)
- Unicorn-64215.exe (PID: 10124)
- Unicorn-44350.exe (PID: 10096)
- Unicorn-39711.exe (PID: 10104)
- Unicorn-56047.exe (PID: 10136)
- Unicorn-52902.exe (PID: 10216)
- Unicorn-17436.exe (PID: 10232)
- Unicorn-36373.exe (PID: 10256)
- Unicorn-20229.exe (PID: 6492)
- Unicorn-20229.exe (PID: 10248)
- Unicorn-62990.exe (PID: 10276)
- Unicorn-15206.exe (PID: 9300)
- Unicorn-64334.exe (PID: 9316)
- Unicorn-14822.exe (PID: 10168)
- Unicorn-52710.exe (PID: 9312)
- Unicorn-27332.exe (PID: 10376)
- Unicorn-33774.exe (PID: 10452)
- Unicorn-55206.exe (PID: 10436)
- Unicorn-19740.exe (PID: 10476)
- Unicorn-24916.exe (PID: 10552)
- Unicorn-19740.exe (PID: 10484)
- Unicorn-1101.exe (PID: 10516)
- Unicorn-8580.exe (PID: 10532)
- Unicorn-65519.exe (PID: 10584)
- Unicorn-44734.exe (PID: 9280)
- Unicorn-27332.exe (PID: 10372)
- Unicorn-24454.exe (PID: 10608)
- Unicorn-39637.exe (PID: 10760)
- Unicorn-58927.exe (PID: 10740)
- Unicorn-8117.exe (PID: 10600)
- Unicorn-2252.exe (PID: 10592)
- Unicorn-32117.exe (PID: 10648)
- Unicorn-32799.exe (PID: 10788)
- Unicorn-16655.exe (PID: 10808)
- Unicorn-15502.exe (PID: 10828)
- Unicorn-15887.exe (PID: 10864)
- Unicorn-20525.exe (PID: 10884)
- Unicorn-3508.exe (PID: 10904)
- Unicorn-42046.exe (PID: 10920)
- Unicorn-22445.exe (PID: 10928)
- Unicorn-20036.exe (PID: 10968)
- Unicorn-6301.exe (PID: 10960)
- Unicorn-38205.exe (PID: 11004)
- Unicorn-5149.exe (PID: 11060)
- Unicorn-38013.exe (PID: 11080)
- Unicorn-38013.exe (PID: 11088)
- Unicorn-14085.exe (PID: 11152)
- Unicorn-14085.exe (PID: 11160)
- Unicorn-49141.exe (PID: 10996)
- Unicorn-38205.exe (PID: 11008)
- Unicorn-46182.exe (PID: 11044)
- Unicorn-19460.exe (PID: 11120)
- Unicorn-27820.exe (PID: 11136)
- Unicorn-52325.exe (PID: 11184)
- Unicorn-38589.exe (PID: 11200)
- Unicorn-33951.exe (PID: 11176)
- Unicorn-11100.exe (PID: 11236)
- Unicorn-38589.exe (PID: 11192)
- Unicorn-46566.exe (PID: 11220)
- Unicorn-50095.exe (PID: 11292)
- Unicorn-46077.exe (PID: 11332)
- Unicorn-51942.exe (PID: 11316)
- Unicorn-26741.exe (PID: 11324)
- Unicorn-52326.exe (PID: 11388)
- Unicorn-52359.exe (PID: 11396)
- Unicorn-11366.exe (PID: 11404)
- Unicorn-54629.exe (PID: 11376)
- Unicorn-19535.exe (PID: 11464)
- Unicorn-2238.exe (PID: 11524)
- Unicorn-49997.exe (PID: 11364)
- Unicorn-20612.exe (PID: 11516)
- Unicorn-35103.exe (PID: 11580)
- Unicorn-26743.exe (PID: 11540)
- Unicorn-35103.exe (PID: 11572)
- Unicorn-23789.exe (PID: 11628)
- Unicorn-26551.exe (PID: 11608)
- Unicorn-17812.exe (PID: 11532)
- Unicorn-37407.exe (PID: 11656)
- Unicorn-37407.exe (PID: 11664)
- Unicorn-20687.exe (PID: 11708)
- Unicorn-20687.exe (PID: 11716)
- Unicorn-28855.exe (PID: 11692)
- Unicorn-20687.exe (PID: 11700)
- Unicorn-53286.exe (PID: 11732)
- Unicorn-45383.exe (PID: 11724)
- Unicorn-41853.exe (PID: 11744)
- Unicorn-33685.exe (PID: 11756)
- Unicorn-61719.exe (PID: 11780)
- Unicorn-4926.exe (PID: 11812)
- Unicorn-31660.exe (PID: 11856)
- Unicorn-19149.exe (PID: 11920)
- Unicorn-54821.exe (PID: 11948)
- Unicorn-19919.exe (PID: 11940)
- Unicorn-60951.exe (PID: 11972)
- Unicorn-12134.exe (PID: 12000)
- Unicorn-37791.exe (PID: 11872)
- Unicorn-49446.exe (PID: 11900)
- Unicorn-26655.exe (PID: 12036)
- Unicorn-1766.exe (PID: 12052)
- Unicorn-10510.exe (PID: 12092)
- Unicorn-50397.exe (PID: 12020)
- Unicorn-42799.exe (PID: 12072)
- Unicorn-43375.exe (PID: 12112)
- Unicorn-9358.exe (PID: 12136)
- Unicorn-25695.exe (PID: 12152)
- Unicorn-19948.exe (PID: 12172)
- Unicorn-34247.exe (PID: 12180)
- Unicorn-60671.exe (PID: 12224)
- Unicorn-43957.exe (PID: 12280)
- Unicorn-4956.exe (PID: 6544)
- Unicorn-52119.exe (PID: 3732)
- Unicorn-62207.exe (PID: 5712)
- Unicorn-54039.exe (PID: 2088)
- Unicorn-3613.exe (PID: 12260)
- Unicorn-42149.exe (PID: 12368)
- Unicorn-52046.exe (PID: 12424)
- Unicorn-43878.exe (PID: 12444)
- Unicorn-11205.exe (PID: 12464)
- Unicorn-23287.exe (PID: 12492)
- Unicorn-52430.exe (PID: 12512)
- Unicorn-39623.exe (PID: 12536)
- Unicorn-32532.exe (PID: 12556)
- Unicorn-17645.exe (PID: 12400)
- Unicorn-38663.exe (PID: 12592)
- Unicorn-38590.exe (PID: 12648)
- Unicorn-32724.exe (PID: 12640)
- Unicorn-59358.exe (PID: 12908)
- Unicorn-64157.exe (PID: 12964)
- Unicorn-52918.exe (PID: 12720)
- Unicorn-12269.exe (PID: 12768)
- Unicorn-40717.exe (PID: 12816)
- Unicorn-65309.exe (PID: 12924)
- Unicorn-51574.exe (PID: 12932)
- Unicorn-17749.exe (PID: 12984)
- Unicorn-48869.exe (PID: 12608)
- Unicorn-38855.exe (PID: 12696)
- Unicorn-42637.exe (PID: 13008)
- Unicorn-14957.exe (PID: 13052)
- Unicorn-36389.exe (PID: 13044)
- Unicorn-52918.exe (PID: 13204)
- Unicorn-28029.exe (PID: 13080)
- Unicorn-19861.exe (PID: 13096)
- Unicorn-36773.exe (PID: 13104)
- Unicorn-19861.exe (PID: 13088)
- Unicorn-12269.exe (PID: 13132)
- Unicorn-44750.exe (PID: 13164)
- Unicorn-42149.exe (PID: 13232)
- Unicorn-52918.exe (PID: 13196)
- Unicorn-61086.exe (PID: 13184)
- Unicorn-28413.exe (PID: 13240)
- Unicorn-37734.exe (PID: 13028)
- Unicorn-44174.exe (PID: 636)
- Unicorn-52150.exe (PID: 13336)
- Unicorn-52150.exe (PID: 13344)
- Unicorn-3141.exe (PID: 13356)
- Unicorn-51661.exe (PID: 13400)
- Unicorn-13421.exe (PID: 13424)
- Unicorn-29757.exe (PID: 13440)
- Unicorn-62238.exe (PID: 13468)
- Unicorn-35621.exe (PID: 13276)
- Unicorn-8132.exe (PID: 13296)
- Unicorn-19093.exe (PID: 2288)
- Unicorn-35813.exe (PID: 1176)
- Unicorn-47703.exe (PID: 13316)
- Unicorn-35133.exe (PID: 13508)
- Unicorn-35133.exe (PID: 13492)
- Unicorn-58869.exe (PID: 13620)
- Unicorn-21397.exe (PID: 13516)
- Unicorn-62814.exe (PID: 13524)
- Unicorn-36965.exe (PID: 13628)
- Unicorn-50701.exe (PID: 13668)
- Unicorn-50701.exe (PID: 13644)
- Unicorn-50701.exe (PID: 13660)
- Unicorn-50701.exe (PID: 13676)
- Unicorn-50701.exe (PID: 13652)
- Unicorn-56566.exe (PID: 13684)
- Unicorn-47901.exe (PID: 13692)
- Unicorn-35133.exe (PID: 13500)
- Unicorn-48782.exe (PID: 13856)
- Unicorn-46277.exe (PID: 13904)
- Unicorn-40614.exe (PID: 13888)
- Unicorn-46077.exe (PID: 13932)
- Unicorn-31948.exe (PID: 13896)
- Unicorn-13405.exe (PID: 13980)
- Unicorn-46661.exe (PID: 14128)
- Unicorn-25660.exe (PID: 14120)
- Unicorn-39023.exe (PID: 14152)
- Unicorn-55326.exe (PID: 14112)
- Unicorn-61766.exe (PID: 14296)
- Unicorn-58013.exe (PID: 14316)
- Unicorn-50701.exe (PID: 13636)
- Unicorn-7941.exe (PID: 13792)
- Unicorn-42917.exe (PID: 13848)
- Unicorn-46661.exe (PID: 14104)
- Unicorn-52830.exe (PID: 14344)
- Unicorn-38797.exe (PID: 14396)
- Unicorn-30245.exe (PID: 14360)
- Unicorn-36005.exe (PID: 14432)
- Unicorn-27836.exe (PID: 14440)
- Unicorn-26876.exe (PID: 14496)
- Unicorn-45814.exe (PID: 14468)
- Unicorn-24382.exe (PID: 14512)
- Unicorn-16100.exe (PID: 14572)
- Unicorn-16100.exe (PID: 14560)
- Unicorn-25340.exe (PID: 14332)
- Unicorn-29180.exe (PID: 14648)
- Unicorn-27143.exe (PID: 14640)
- Unicorn-35046.exe (PID: 14656)
- Unicorn-4676.exe (PID: 14856)
- Unicorn-35311.exe (PID: 14696)
- Unicorn-29564.exe (PID: 14752)
- Unicorn-29564.exe (PID: 14760)
- Unicorn-10229.exe (PID: 14780)
- Unicorn-29564.exe (PID: 14768)
- Unicorn-29564.exe (PID: 14792)
- Unicorn-18900.exe (PID: 14580)
- Unicorn-60007.exe (PID: 14864)
- Unicorn-50614.exe (PID: 14916)
- Unicorn-20244.exe (PID: 14948)
- Unicorn-52725.exe (PID: 14996)
- Unicorn-28412.exe (PID: 14988)
- Unicorn-34278.exe (PID: 14964)
- Unicorn-14677.exe (PID: 14980)
- Unicorn-34278.exe (PID: 14972)
- Unicorn-4676.exe (PID: 14848)
- Unicorn-18901.exe (PID: 14900)
- Unicorn-44749.exe (PID: 14924)
- Unicorn-42693.exe (PID: 15120)
- Unicorn-17828.exe (PID: 15084)
- Unicorn-26494.exe (PID: 15076)
- Unicorn-18358.exe (PID: 15068)
- Unicorn-31397.exe (PID: 15048)
- Unicorn-15628.exe (PID: 15148)
- Unicorn-24294.exe (PID: 15140)
- Unicorn-35276.exe (PID: 15180)
- Unicorn-37173.exe (PID: 15192)
- Unicorn-24559.exe (PID: 15204)
- Unicorn-65207.exe (PID: 15240)
- Unicorn-62446.exe (PID: 15256)
- Unicorn-56846.exe (PID: 15264)
- Unicorn-54278.exe (PID: 15272)
- Unicorn-54278.exe (PID: 15280)
- Unicorn-16509.exe (PID: 15288)
- Unicorn-28621.exe (PID: 15416)
- Unicorn-44958.exe (PID: 15456)
- Unicorn-30733.exe (PID: 15512)
- Unicorn-20453.exe (PID: 15424)
- Unicorn-6884.exe (PID: 15504)
- Unicorn-29389.exe (PID: 15304)
- Unicorn-62446.exe (PID: 15296)
- Unicorn-9492.exe (PID: 13248)
- Unicorn-44958.exe (PID: 15448)
- Unicorn-9684.exe (PID: 15440)
- Unicorn-49566.exe (PID: 15700)
- Unicorn-44958.exe (PID: 15476)
- Unicorn-17661.exe (PID: 15596)
- Unicorn-58693.exe (PID: 15464)
- Unicorn-14397.exe (PID: 15620)
- Unicorn-3436.exe (PID: 15636)
- Unicorn-29965.exe (PID: 15692)
- Unicorn-34223.exe (PID: 15664)
- Unicorn-29965.exe (PID: 15708)
- Unicorn-28621.exe (PID: 15408)
- Unicorn-44958.exe (PID: 15472)
- Unicorn-29773.exe (PID: 15792)
- Unicorn-48606.exe (PID: 15876)
- Unicorn-32269.exe (PID: 15864)
- Unicorn-46494.exe (PID: 15840)
- Unicorn-48990.exe (PID: 15924)
- Unicorn-32269.exe (PID: 15856)
- Unicorn-35150.exe (PID: 15996)
- Unicorn-32077.exe (PID: 15904)
- Unicorn-10069.exe (PID: 15972)
- Unicorn-57158.exe (PID: 15944)
- Unicorn-64174.exe (PID: 15964)
- Unicorn-39861.exe (PID: 16012)
- Unicorn-26292.exe (PID: 16024)
- Unicorn-49831.exe (PID: 15740)
- Unicorn-49831.exe (PID: 15748)
- Unicorn-49831.exe (PID: 15768)
- Unicorn-41085.exe (PID: 15812)
- Unicorn-3702.exe (PID: 16092)
- Unicorn-3245.exe (PID: 16112)
- Unicorn-33421.exe (PID: 16132)
- Unicorn-57926.exe (PID: 16152)
- Unicorn-12254.exe (PID: 16184)
- Unicorn-8725.exe (PID: 16176)
- Unicorn-28589.exe (PID: 16044)
- Unicorn-31396.exe (PID: 16068)
- Unicorn-36021.exe (PID: 16312)
- Unicorn-9478.exe (PID: 16352)
- Unicorn-35829.exe (PID: 16368)
- Unicorn-52549.exe (PID: 16440)
- Unicorn-38325.exe (PID: 16476)
- Unicorn-52549.exe (PID: 16448)
- Unicorn-3733.exe (PID: 16596)
- Unicorn-57454.exe (PID: 16496)
- Unicorn-21988.exe (PID: 16516)
- Unicorn-49094.exe (PID: 16536)
- Unicorn-60910.exe (PID: 16572)
- Unicorn-49670.exe (PID: 16588)
- Unicorn-1892.exe (PID: 16672)
- Unicorn-20260.exe (PID: 16236)
- Unicorn-10054.exe (PID: 16244)
- Unicorn-10557.exe (PID: 16660)
- Unicorn-4388.exe (PID: 16764)
- Unicorn-56581.exe (PID: 16820)
- Unicorn-37631.exe (PID: 16788)
- Unicorn-25060.exe (PID: 16896)
- Unicorn-31116.exe (PID: 16864)
- Unicorn-30926.exe (PID: 16888)
- Unicorn-55814.exe (PID: 16976)
- Unicorn-25444.exe (PID: 16992)
- Unicorn-8916.exe (PID: 17036)
- Unicorn-62525.exe (PID: 17072)
- Unicorn-64662.exe (PID: 16688)
- Unicorn-2468.exe (PID: 16716)
- Unicorn-54549.exe (PID: 17128)
- Unicorn-8148.exe (PID: 17216)
- Unicorn-55053.exe (PID: 17320)
- Unicorn-55053.exe (PID: 17336)
- Unicorn-63413.exe (PID: 17248)
- Unicorn-63413.exe (PID: 17232)
- Unicorn-63413.exe (PID: 17240)
- Unicorn-14212.exe (PID: 17256)
- Unicorn-63221.exe (PID: 17312)
- Unicorn-19885.exe (PID: 17360)
- Unicorn-55053.exe (PID: 17324)
- Unicorn-14020.exe (PID: 17344)
- Unicorn-14020.exe (PID: 17348)
- Unicorn-36798.exe (PID: 16936)
- Unicorn-5276.exe (PID: 17424)
- Unicorn-57349.exe (PID: 17136)
- Unicorn-40549.exe (PID: 17480)
- Unicorn-29780.exe (PID: 17500)
- Unicorn-62646.exe (PID: 17700)
- Unicorn-29780.exe (PID: 17520)
- Unicorn-60726.exe (PID: 17588)
- Unicorn-38525.exe (PID: 17620)
- Unicorn-62646.exe (PID: 17708)
- Unicorn-5468.exe (PID: 17644)
- Unicorn-21996.exe (PID: 17668)
- Unicorn-62646.exe (PID: 17692)
- Unicorn-7580.exe (PID: 17724)
- Unicorn-32276.exe (PID: 17760)
- Unicorn-48805.exe (PID: 17856)
- Unicorn-29972.exe (PID: 17436)
- Unicorn-54285.exe (PID: 17472)
- Unicorn-29780.exe (PID: 17508)
- Unicorn-54670.exe (PID: 17896)
- Unicorn-54670.exe (PID: 17872)
- Unicorn-45037.exe (PID: 18076)
- Unicorn-54670.exe (PID: 17912)
- Unicorn-29469.exe (PID: 17904)
- Unicorn-37836.exe (PID: 17932)
- Unicorn-54670.exe (PID: 17864)
- Unicorn-54670.exe (PID: 17888)
- Unicorn-46502.exe (PID: 17920)
- Unicorn-22071.exe (PID: 17948)
- Unicorn-28516.exe (PID: 18052)
- Unicorn-62103.exe (PID: 18092)
- Unicorn-45037.exe (PID: 18068)
- Unicorn-54670.exe (PID: 17880)
- Unicorn-21262.exe (PID: 18148)
- Unicorn-53493.exe (PID: 18220)
- Unicorn-58828.exe (PID: 18212)
- Unicorn-63294.exe (PID: 18200)
- Unicorn-39175.exe (PID: 18324)
- Unicorn-25335.exe (PID: 6616)
- Unicorn-16709.exe (PID: 5004)
- Unicorn-7581.exe (PID: 6628)
- Unicorn-58893.exe (PID: 9816)
- Unicorn-61573.exe (PID: 18084)
- Unicorn-4701.exe (PID: 18100)
- Unicorn-14292.exe (PID: 18184)
- Unicorn-63294.exe (PID: 18192)
- Unicorn-43133.exe (PID: 9928)
- Unicorn-16428.exe (PID: 10176)
- Unicorn-30846.exe (PID: 10388)
- Unicorn-8260.exe (PID: 6656)
- Unicorn-45533.exe (PID: 10560)
- Unicorn-13549.exe (PID: 18448)
- Unicorn-46990.exe (PID: 6684)
- Unicorn-53886.exe (PID: 18440)
- Unicorn-53886.exe (PID: 10664)
- Unicorn-10285.exe (PID: 18480)
- Unicorn-13052.exe (PID: 18508)
- Unicorn-21717.exe (PID: 18496)
- Unicorn-18453.exe (PID: 18536)
- Unicorn-7566.exe (PID: 18556)
- Unicorn-31806.exe (PID: 18592)
- Unicorn-31806.exe (PID: 18608)
- Unicorn-14773.exe (PID: 18672)
- Unicorn-65054.exe (PID: 18680)
- Unicorn-23903.exe (PID: 18712)
- Unicorn-64557.exe (PID: 18724)
- Unicorn-15548.exe (PID: 18760)
- Unicorn-53622.exe (PID: 18732)
- Unicorn-24214.exe (PID: 18768)
- Unicorn-31806.exe (PID: 18580)
- Unicorn-23670.exe (PID: 18572)
- Unicorn-31806.exe (PID: 18600)
- Unicorn-39974.exe (PID: 18652)
- Unicorn-40550.exe (PID: 18808)
- Unicorn-15356.exe (PID: 18816)
- Unicorn-15356.exe (PID: 18836)
- Unicorn-24022.exe (PID: 18852)
- Unicorn-18156.exe (PID: 18864)
- Unicorn-24022.exe (PID: 18848)
- Unicorn-58740.exe (PID: 18944)
- Unicorn-14204.exe (PID: 18984)
- Unicorn-17004.exe (PID: 18952)
- Unicorn-63206.exe (PID: 18960)
- Unicorn-54758.exe (PID: 19016)
- Unicorn-24676.exe (PID: 19092)
- Unicorn-48981.exe (PID: 19084)
- Unicorn-13741.exe (PID: 19112)
- Unicorn-13741.exe (PID: 19108)
- Unicorn-52557.exe (PID: 19216)
- Unicorn-60533.exe (PID: 19296)
- Unicorn-32844.exe (PID: 19180)
- Unicorn-50287.exe (PID: 19224)
- Unicorn-17079.exe (PID: 19236)
- Unicorn-60533.exe (PID: 19304)
- Unicorn-49102.exe (PID: 19400)
- Unicorn-2396.exe (PID: 10816)
- Unicorn-39181.exe (PID: 19100)
- Unicorn-19308.exe (PID: 19124)
- Unicorn-35645.exe (PID: 19188)
- Unicorn-2396.exe (PID: 10772)
- Unicorn-18924.exe (PID: 4656)
- Unicorn-18924.exe (PID: 4416)
- Unicorn-24790.exe (PID: 2308)
- Unicorn-24790.exe (PID: 5228)
- Unicorn-18924.exe (PID: 19276)
- Unicorn-32460.exe (PID: 4020)
- Unicorn-18924.exe (PID: 5504)
- Unicorn-35261.exe (PID: 3940)
- Unicorn-45541.exe (PID: 19560)
- Unicorn-18349.exe (PID: 19568)
- Unicorn-10068.exe (PID: 19648)
- Unicorn-54604.exe (PID: 19656)
- Unicorn-65126.exe (PID: 4708)
- Unicorn-18924.exe (PID: 4348)
- Unicorn-12868.exe (PID: 19640)
- Unicorn-41781.exe (PID: 19800)
- Unicorn-47374.exe (PID: 19728)
- Unicorn-55542.exe (PID: 19744)
- Unicorn-52749.exe (PID: 19776)
- Unicorn-59223.exe (PID: 19808)
- Unicorn-12100.exe (PID: 19836)
- Unicorn-20460.exe (PID: 19848)
- Unicorn-20460.exe (PID: 19856)
- Unicorn-20460.exe (PID: 19864)
- Unicorn-42957.exe (PID: 19904)
- Unicorn-29396.exe (PID: 19664)
- Unicorn-31997.exe (PID: 19696)
- Unicorn-26236.exe (PID: 19988)
- Unicorn-23436.exe (PID: 19996)
- Unicorn-15076.exe (PID: 20020)
- Unicorn-14877.exe (PID: 20048)
- Unicorn-50199.exe (PID: 20084)
- Unicorn-9590.exe (PID: 20104)
- Unicorn-59101.exe (PID: 19936)
- Unicorn-18644.exe (PID: 19968)
- Unicorn-17876.exe (PID: 20036)
- Unicorn-8557.exe (PID: 20152)
- Unicorn-23933.exe (PID: 20368)
- Unicorn-19412.exe (PID: 20336)
- Unicorn-16228.exe (PID: 20188)
- Unicorn-35365.exe (PID: 20200)
- Unicorn-33062.exe (PID: 20212)
- Unicorn-2884.exe (PID: 20280)
- Unicorn-5677.exe (PID: 20324)
- Unicorn-10093.exe (PID: 20460)
- Unicorn-43534.exe (PID: 20376)
- Unicorn-34982.exe (PID: 6996)
- Unicorn-42958.exe (PID: 6868)
- Unicorn-23357.exe (PID: 20476)
- Unicorn-61598.exe (PID: 6968)
- Unicorn-14892.exe (PID: 11244)
- Unicorn-20757.exe (PID: 7008)
- Unicorn-13653.exe (PID: 20172)
- Unicorn-15276.exe (PID: 11604)
- Unicorn-12476.exe (PID: 368)
- Unicorn-27468.exe (PID: 1680)
- Unicorn-52927.exe (PID: 5444)
- Unicorn-10933.exe (PID: 3408)
- Unicorn-60710.exe (PID: 2328)
- Unicorn-3918.exe (PID: 532)
- Unicorn-47966.exe (PID: 3628)
- Unicorn-50342.exe (PID: 2932)
- Unicorn-31036.exe (PID: 5064)
- Unicorn-45149.exe (PID: 2364)
- Unicorn-55349.exe (PID: 1808)
- Unicorn-2029.exe (PID: 3116)
- Unicorn-9429.exe (PID: 3696)
- Unicorn-35159.exe (PID: 4584)
- Unicorn-34967.exe (PID: 12100)
- Unicorn-43909.exe (PID: 3740)
- Unicorn-27380.exe (PID: 4912)
- Unicorn-36046.exe (PID: 3868)
- Unicorn-52574.exe (PID: 3700)
- Unicorn-28070.exe (PID: 1120)
- Unicorn-26221.exe (PID: 3528)
- Unicorn-59662.exe (PID: 2800)
- Unicorn-19325.exe (PID: 4920)
- Unicorn-35351.exe (PID: 4844)
- Unicorn-21245.exe (PID: 4668)
- Unicorn-4525.exe (PID: 4240)
- Unicorn-53726.exe (PID: 5800)
- Unicorn-53726.exe (PID: 3608)
- Unicorn-51687.exe (PID: 1512)
- Unicorn-4525.exe (PID: 4152)
- Unicorn-53726.exe (PID: 6088)
- Unicorn-4525.exe (PID: 5332)
- Unicorn-14420.exe (PID: 712)
- Unicorn-12309.exe (PID: 12012)
- Unicorn-20940.exe (PID: 5080)
- Unicorn-20477.exe (PID: 12584)
- Unicorn-28454.exe (PID: 896)
- Unicorn-28454.exe (PID: 1676)
- Unicorn-19788.exe (PID: 4216)
- Unicorn-28454.exe (PID: 4996)
- Unicorn-29030.exe (PID: 2072)
- Unicorn-4028.exe (PID: 2524)
- Unicorn-45558.exe (PID: 3680)
- Unicorn-4525.exe (PID: 5240)
- Unicorn-4525.exe (PID: 5812)
- Unicorn-4220.exe (PID: 5008)
- Unicorn-14116.exe (PID: 20496)
- Unicorn-37006.exe (PID: 20488)
- Unicorn-22782.exe (PID: 20516)
- Unicorn-14116.exe (PID: 20524)
- Unicorn-30452.exe (PID: 20548)
- Unicorn-30950.exe (PID: 20604)
- Unicorn-23047.exe (PID: 20624)
- Unicorn-64079.exe (PID: 20724)
- Unicorn-29684.exe (PID: 20760)
- Unicorn-47743.exe (PID: 20704)
- Unicorn-6710.exe (PID: 20696)
- Unicorn-29684.exe (PID: 20768)
- Unicorn-29684.exe (PID: 20784)
- Unicorn-29684.exe (PID: 20792)
- Unicorn-29684.exe (PID: 20776)
- Unicorn-31023.exe (PID: 20680)
- Unicorn-45829.exe (PID: 20840)
- Unicorn-30215.exe (PID: 20808)
- Unicorn-38350.exe (PID: 20800)
- Unicorn-14110.exe (PID: 20920)
- Unicorn-10389.exe (PID: 20928)
- Unicorn-45829.exe (PID: 20816)
- Unicorn-29293.exe (PID: 20832)
- Unicorn-31372.exe (PID: 21016)
- Unicorn-52903.exe (PID: 21000)
- Unicorn-52903.exe (PID: 21024)
- Unicorn-31372.exe (PID: 21032)
- Unicorn-30045.exe (PID: 21072)
- Unicorn-35837.exe (PID: 21064)
- Unicorn-38807.exe (PID: 21084)
- Unicorn-21509.exe (PID: 20952)
- Unicorn-22087.exe (PID: 20944)
- Unicorn-38423.exe (PID: 20968)
- Unicorn-52373.exe (PID: 21008)
- Unicorn-35645.exe (PID: 21152)
- Unicorn-52711.exe (PID: 21172)
- Unicorn-44543.exe (PID: 21192)
- Unicorn-13181.exe (PID: 21436)
- Unicorn-59118.exe (PID: 21452)
- Unicorn-61309.exe (PID: 21416)
- Unicorn-4516.exe (PID: 21444)
- Unicorn-22964.exe (PID: 3104)
- Unicorn-48158.exe (PID: 21492)
- Unicorn-31630.exe (PID: 6204)
- Unicorn-22004.exe (PID: 4916)
- Unicorn-25845.exe (PID: 21164)
- Unicorn-42973.exe (PID: 21320)
- Unicorn-63759.exe (PID: 6412)
- Unicorn-43253.exe (PID: 13124)
- Unicorn-54214.exe (PID: 11652)
- Unicorn-36172.exe (PID: 13568)
- Unicorn-32668.exe (PID: 6832)
- Unicorn-21812.exe (PID: 6384)
- Unicorn-30478.exe (PID: 6536)
- Unicorn-55054.exe (PID: 6408)
- Unicorn-63229.exe (PID: 6424)
- Unicorn-63759.exe (PID: 6540)
- Unicorn-35085.exe (PID: 6812)
- Unicorn-15749.exe (PID: 6784)
- Unicorn-32284.exe (PID: 13176)
- Unicorn-57173.exe (PID: 2384)
- Unicorn-57703.exe (PID: 4312)
- Unicorn-57173.exe (PID: 6836)
- Unicorn-57173.exe (PID: 4944)
- Unicorn-57173.exe (PID: 13748)
- Unicorn-41215.exe (PID: 7120)
- Unicorn-62766.exe (PID: 7072)
- Unicorn-65334.exe (PID: 7052)
- Unicorn-19132.exe (PID: 13952)
- Unicorn-40182.exe (PID: 21576)
- Unicorn-21812.exe (PID: 4988)
- Unicorn-14981.exe (PID: 21592)
- Unicorn-31516.exe (PID: 21584)
- Unicorn-7926.exe (PID: 21660)
- Unicorn-32668.exe (PID: 5556)
- Unicorn-43694.exe (PID: 21708)
- Unicorn-64566.exe (PID: 21724)
- Unicorn-56213.exe (PID: 7172)
- Unicorn-48045.exe (PID: 7204)
- Unicorn-31516.exe (PID: 21568)
- Unicorn-4525.exe (PID: 4800)
- Unicorn-65334.exe (PID: 4196)
- Unicorn-14981.exe (PID: 21604)
- Unicorn-46597.exe (PID: 21668)
- Unicorn-16061.exe (PID: 21676)
- Unicorn-32645.exe (PID: 21748)
- Unicorn-212.exe (PID: 21764)
- Unicorn-63479.exe (PID: 21772)
- Unicorn-41053.exe (PID: 21780)
- Unicorn-38174.exe (PID: 21916)
- Unicorn-53934.exe (PID: 21884)
- Unicorn-28733.exe (PID: 21868)
- Unicorn-53934.exe (PID: 21876)
- Unicorn-38174.exe (PID: 21908)
- Unicorn-55351.exe (PID: 21844)
- Unicorn-24268.exe (PID: 21860)
- Unicorn-38174.exe (PID: 21924)
- Unicorn-12973.exe (PID: 21940)
- Unicorn-37484.exe (PID: 22020)
- Unicorn-46607.exe (PID: 22036)
- Unicorn-6461.exe (PID: 22140)
- Unicorn-6461.exe (PID: 22132)
- Unicorn-22300.exe (PID: 22100)
- Unicorn-30966.exe (PID: 22092)
- Unicorn-18573.exe (PID: 21932)
- Unicorn-6461.exe (PID: 22228)
- Unicorn-63333.exe (PID: 22172)
- Unicorn-6461.exe (PID: 22148)
- Unicorn-31044.exe (PID: 22188)
- Unicorn-6461.exe (PID: 22124)
- Unicorn-24215.exe (PID: 22200)
- Unicorn-39710.exe (PID: 22180)
- Unicorn-17125.exe (PID: 22356)
- Unicorn-63806.exe (PID: 22372)
- Unicorn-43741.exe (PID: 22364)
- Unicorn-11068.exe (PID: 22428)
- Unicorn-41438.exe (PID: 22384)
- Unicorn-16237.exe (PID: 22400)
- Unicorn-63863.exe (PID: 22116)
- Unicorn-5765.exe (PID: 22108)
- Unicorn-6461.exe (PID: 22164)
- Unicorn-6461.exe (PID: 22156)
- Unicorn-40862.exe (PID: 8864)
- Unicorn-11644.exe (PID: 22436)
- Unicorn-40862.exe (PID: 22512)
- Unicorn-8381.exe (PID: 22520)
- Unicorn-40862.exe (PID: 7228)
- Unicorn-7997.exe (PID: 7496)
- Unicorn-57846.exe (PID: 22452)
- Unicorn-17509.exe (PID: 22444)
- Unicorn-40862.exe (PID: 9020)
- Unicorn-52804.exe (PID: 22408)
- Unicorn-17509.exe (PID: 22464)
- Unicorn-51022.exe (PID: 7720)
- Unicorn-6269.exe (PID: 7868)
- Unicorn-13116.exe (PID: 15040)
- Unicorn-26548.exe (PID: 7404)
- Unicorn-23556.exe (PID: 7456)
- Unicorn-32798.exe (PID: 8044)
- Unicorn-7597.exe (PID: 8080)
- Unicorn-2014.exe (PID: 8068)
- Unicorn-8838.exe (PID: 7600)
- Unicorn-51022.exe (PID: 7640)
- Unicorn-10685.exe (PID: 7664)
- Unicorn-2517.exe (PID: 7748)
- Unicorn-1590.exe (PID: 7820)
- Unicorn-56037.exe (PID: 8376)
- Unicorn-58837.exe (PID: 8408)
- Unicorn-33836.exe (PID: 8668)
- Unicorn-36637.exe (PID: 8580)
- Unicorn-33836.exe (PID: 8684)
- Unicorn-7790.exe (PID: 8688)
- Unicorn-57189.exe (PID: 16192)
- Unicorn-125.exe (PID: 8120)
- Unicorn-57302.exe (PID: 8220)
- Unicorn-10404.exe (PID: 8208)
- Unicorn-49405.exe (PID: 22548)
- Unicorn-32869.exe (PID: 22556)
- Unicorn-18453.exe (PID: 22588)
- Unicorn-24053.exe (PID: 22596)
- Unicorn-16919.exe (PID: 22652)
- Unicorn-3230.exe (PID: 22668)
- Unicorn-35678.exe (PID: 22660)
- Unicorn-49597.exe (PID: 16380)
- Unicorn-58262.exe (PID: 8856)
- Unicorn-701.exe (PID: 22540)
- Unicorn-58070.exe (PID: 22580)
- Unicorn-1349.exe (PID: 22684)
- Unicorn-12590.exe (PID: 22860)
- Unicorn-31837.exe (PID: 22748)
- Unicorn-10630.exe (PID: 22756)
- Unicorn-45381.exe (PID: 22768)
- Unicorn-9908.exe (PID: 22792)
- Unicorn-33565.exe (PID: 22824)
- Unicorn-9061.exe (PID: 22816)
- Unicorn-18222.exe (PID: 22708)
- Unicorn-3078.exe (PID: 22720)
- Unicorn-45647.exe (PID: 22884)
- Unicorn-36140.exe (PID: 22916)
- Unicorn-44687.exe (PID: 22896)
- Unicorn-19605.exe (PID: 22908)
- Unicorn-4038.exe (PID: 22996)
- Unicorn-3468.exe (PID: 22940)
- Unicorn-33172.exe (PID: 23012)
- Unicorn-16637.exe (PID: 23020)
- Unicorn-10198.exe (PID: 23044)
- Unicorn-41871.exe (PID: 23132)
- Unicorn-17174.exe (PID: 23068)
- Unicorn-2414.exe (PID: 23092)
- Unicorn-30405.exe (PID: 23124)
- Unicorn-41917.exe (PID: 23184)
- Unicorn-30981.exe (PID: 23192)
- Unicorn-52389.exe (PID: 23320)
- Unicorn-52389.exe (PID: 23344)
- Unicorn-52389.exe (PID: 23368)
- Unicorn-35853.exe (PID: 23336)
- Unicorn-52389.exe (PID: 23384)
- Unicorn-3188.exe (PID: 23400)
- Unicorn-3188.exe (PID: 23392)
- Unicorn-19903.exe (PID: 23376)
- Unicorn-52389.exe (PID: 23352)
- Unicorn-10965.exe (PID: 23512)
- Unicorn-10965.exe (PID: 23520)
- Unicorn-37012.exe (PID: 8992)
- Unicorn-59789.exe (PID: 22928)
- Unicorn-37012.exe (PID: 9008)
- Unicorn-20477.exe (PID: 9032)
- Unicorn-36813.exe (PID: 17384)
- Unicorn-53349.exe (PID: 9092)
- Unicorn-52389.exe (PID: 23328)
- Unicorn-52389.exe (PID: 23360)
- Unicorn-37012.exe (PID: 9124)
- Unicorn-34821.exe (PID: 23596)
- Unicorn-26461.exe (PID: 9248)
- Unicorn-20861.exe (PID: 23556)
- Unicorn-20861.exe (PID: 23564)
- Unicorn-20861.exe (PID: 23572)
- Unicorn-61702.exe (PID: 23680)
- Unicorn-12700.exe (PID: 23728)
- Unicorn-57236.exe (PID: 23736)
- Unicorn-26269.exe (PID: 23744)
- Unicorn-61702.exe (PID: 23764)
- Unicorn-54263.exe (PID: 23816)
- Unicorn-61702.exe (PID: 23780)
- Unicorn-42797.exe (PID: 23800)
- Unicorn-26269.exe (PID: 23752)
- Unicorn-56533.exe (PID: 23808)
- Unicorn-45678.exe (PID: 9056)
- Unicorn-37396.exe (PID: 5244)
- Unicorn-37396.exe (PID: 9192)
- Unicorn-37396.exe (PID: 17536)
- Unicorn-61702.exe (PID: 23772)
- Unicorn-29029.exe (PID: 23832)
- Unicorn-61702.exe (PID: 23704)
- Unicorn-19238.exe (PID: 24056)
- Unicorn-61702.exe (PID: 23688)
- Unicorn-1765.exe (PID: 23712)
- Unicorn-50006.exe (PID: 23956)
- Unicorn-4102.exe (PID: 23936)
- Unicorn-42773.exe (PID: 24036)
- Unicorn-52574.exe (PID: 24028)
- Unicorn-31021.exe (PID: 24048)
- Unicorn-32156.exe (PID: 24108)
- Unicorn-6884.exe (PID: 24068)
- Unicorn-16949.exe (PID: 24100)
- Unicorn-28415.exe (PID: 24132)
- Unicorn-6884.exe (PID: 24120)
- Unicorn-53687.exe (PID: 24216)
- Unicorn-32156.exe (PID: 24200)
- Unicorn-42773.exe (PID: 23944)
- Unicorn-42797.exe (PID: 23856)
- Unicorn-57301.exe (PID: 24388)
- Unicorn-27117.exe (PID: 24420)
- Unicorn-39437.exe (PID: 24492)
- Unicorn-3765.exe (PID: 24524)
- Unicorn-14046.exe (PID: 24564)
- Unicorn-53357.exe (PID: 24572)
- Unicorn-29037.exe (PID: 24444)
- Unicorn-20300.exe (PID: 24500)
- Unicorn-20300.exe (PID: 24508)
Reads the computer name
- 62a986c16cdede724c9742f1c825f9e1f0ae5cbbe023dff477f3d6bf0b9e6966.exe (PID: 6480)
- Unicorn-62431.exe (PID: 6576)
- Unicorn-49375.exe (PID: 6660)
- Unicorn-24679.exe (PID: 6644)
- Unicorn-29509.exe (PID: 6668)
- Unicorn-59581.exe (PID: 6692)
- Unicorn-3822.exe (PID: 6860)
- Unicorn-16437.exe (PID: 6880)
- Unicorn-61575.exe (PID: 6912)
- Unicorn-12109.exe (PID: 6952)
- Unicorn-61575.exe (PID: 6904)
- Unicorn-61575.exe (PID: 6896)
- Unicorn-58046.exe (PID: 6960)
- Unicorn-45727.exe (PID: 7160)
- Unicorn-17309.exe (PID: 6056)
- Unicorn-47277.exe (PID: 6920)
- Unicorn-57853.exe (PID: 3712)
- Unicorn-39287.exe (PID: 6100)
- Unicorn-56007.exe (PID: 5196)
- Unicorn-39479.exe (PID: 1412)
- Unicorn-2317.exe (PID: 1944)
- Unicorn-56007.exe (PID: 4012)
- Unicorn-56007.exe (PID: 1272)
- Unicorn-21917.exe (PID: 372)
- Unicorn-16052.exe (PID: 6012)
- Unicorn-44310.exe (PID: 2736)
- Unicorn-48311.exe (PID: 6600)
- Unicorn-44974.exe (PID: 6620)
- Unicorn-56007.exe (PID: 1608)
- Unicorn-56007.exe (PID: 4724)
- Unicorn-13252.exe (PID: 1720)
- Unicorn-2317.exe (PID: 4704)
- Unicorn-31607.exe (PID: 380)
- Unicorn-36437.exe (PID: 4108)
- Unicorn-48254.exe (PID: 428)
- Unicorn-47943.exe (PID: 5032)
- Unicorn-33644.exe (PID: 72)
- Unicorn-23823.exe (PID: 5092)
- Unicorn-31991.exe (PID: 308)
- Unicorn-28653.exe (PID: 4852)
- Unicorn-32951.exe (PID: 1100)
- Unicorn-37781.exe (PID: 1016)
- Unicorn-58031.exe (PID: 1228)
- Unicorn-41695.exe (PID: 6216)
- Unicorn-58031.exe (PID: 4260)
- Unicorn-15847.exe (PID: 5944)
- Unicorn-15847.exe (PID: 2116)
- Unicorn-12317.exe (PID: 6284)
- Unicorn-32183.exe (PID: 6464)
- Unicorn-48325.exe (PID: 6756)
- Unicorn-24015.exe (PID: 6376)
- Unicorn-47949.exe (PID: 6400)
- Unicorn-32183.exe (PID: 6448)
- Unicorn-32183.exe (PID: 6444)
- Unicorn-7989.exe (PID: 780)
- Unicorn-37013.exe (PID: 6428)
- Unicorn-37013.exe (PID: 6404)
- Unicorn-2124.exe (PID: 6280)
- Unicorn-12317.exe (PID: 6296)
- Unicorn-2124.exe (PID: 6276)
- Unicorn-32183.exe (PID: 6456)
- Unicorn-32183.exe (PID: 6472)
- Unicorn-12317.exe (PID: 6268)
- Unicorn-24311.exe (PID: 6820)
- Unicorn-4253.exe (PID: 6828)
- Unicorn-39687.exe (PID: 5656)
- Unicorn-500.exe (PID: 1964)
- Unicorn-23543.exe (PID: 6508)
- Unicorn-40071.exe (PID: 4480)
- Unicorn-12037.exe (PID: 5612)
- Unicorn-23351.exe (PID: 7044)
- Unicorn-15182.exe (PID: 4524)
- Unicorn-6749.exe (PID: 4428)
- Unicorn-28181.exe (PID: 7100)
- Unicorn-11845.exe (PID: 7128)
- Unicorn-23351.exe (PID: 7036)
- Unicorn-39117.exe (PID: 7096)
- Unicorn-41917.exe (PID: 7068)
- Unicorn-15182.exe (PID: 5752)
- Unicorn-4829.exe (PID: 5528)
- Unicorn-50351.exe (PID: 3872)
- Unicorn-309.exe (PID: 7176)
- Unicorn-32863.exe (PID: 3784)
- Unicorn-43645.exe (PID: 7196)
- Unicorn-5125.exe (PID: 7288)
- Unicorn-56319.exe (PID: 7328)
- Unicorn-16055.exe (PID: 7216)
- Unicorn-24415.exe (PID: 7232)
- Unicorn-54134.exe (PID: 7272)
- Unicorn-53942.exe (PID: 7308)
- Unicorn-12525.exe (PID: 7368)
- Unicorn-7118.exe (PID: 7348)
- Unicorn-4357.exe (PID: 7380)
- Unicorn-57663.exe (PID: 7252)
- Unicorn-58815.exe (PID: 7416)
- Unicorn-58815.exe (PID: 7408)
- Unicorn-50455.exe (PID: 7540)
- Unicorn-34119.exe (PID: 7508)
- Unicorn-58623.exe (PID: 7476)
- Unicorn-50455.exe (PID: 7532)
- Unicorn-1830.exe (PID: 7584)
- Unicorn-58623.exe (PID: 7468)
- Unicorn-22997.exe (PID: 7648)
- Unicorn-50647.exe (PID: 7444)
- Unicorn-1830.exe (PID: 7580)
- Unicorn-22805.exe (PID: 7780)
- Unicorn-6469.exe (PID: 7728)
- Unicorn-22805.exe (PID: 7764)
- Unicorn-50455.exe (PID: 7548)
- Unicorn-20204.exe (PID: 7736)
- Unicorn-55478.exe (PID: 7704)
- Unicorn-60085.exe (PID: 7804)
- Unicorn-49614.exe (PID: 7884)
- Unicorn-41446.exe (PID: 7892)
- Unicorn-22805.exe (PID: 7772)
- Unicorn-36733.exe (PID: 7656)
- Unicorn-42287.exe (PID: 7560)
- Unicorn-18167.exe (PID: 7628)
- Unicorn-9422.exe (PID: 7500)
- Unicorn-35581.exe (PID: 7908)
- Unicorn-2716.exe (PID: 7836)
- Unicorn-65453.exe (PID: 7844)
- Unicorn-24413.exe (PID: 7876)
- Unicorn-20663.exe (PID: 7964)
- Unicorn-54103.exe (PID: 7980)
- Unicorn-17709.exe (PID: 8000)
- Unicorn-30484.exe (PID: 8016)
- Unicorn-28447.exe (PID: 8024)
- Unicorn-17133.exe (PID: 8056)
- Unicorn-44591.exe (PID: 8048)
- Unicorn-53143.exe (PID: 8100)
- Unicorn-34799.exe (PID: 8168)
- Unicorn-52878.exe (PID: 8084)
- Unicorn-26631.exe (PID: 8152)
- Unicorn-1934.exe (PID: 8132)
- Unicorn-34799.exe (PID: 8176)
- Unicorn-53143.exe (PID: 8092)
- Unicorn-22909.exe (PID: 8196)
- Unicorn-51519.exe (PID: 8272)
- Unicorn-64518.exe (PID: 8328)
- Unicorn-63942.exe (PID: 6148)
- Unicorn-59687.exe (PID: 8236)
- Unicorn-10486.exe (PID: 8280)
- Unicorn-34607.exe (PID: 8224)
- Unicorn-51519.exe (PID: 8264)
- Unicorn-55006.exe (PID: 8392)
- Unicorn-52405.exe (PID: 8368)
- Unicorn-404.exe (PID: 8400)
- Unicorn-8373.exe (PID: 8448)
- Unicorn-55006.exe (PID: 8384)
- Unicorn-3588.exe (PID: 8484)
- Unicorn-31653.exe (PID: 8252)
- Unicorn-27015.exe (PID: 8304)
- Unicorn-39053.exe (PID: 8468)
- Unicorn-61277.exe (PID: 8436)
- Unicorn-1093.exe (PID: 8512)
- Unicorn-6189.exe (PID: 8524)
- Unicorn-11446.exe (PID: 8548)
- Unicorn-44311.exe (PID: 8572)
- Unicorn-35567.exe (PID: 8616)
- Unicorn-40589.exe (PID: 8720)
- Unicorn-43735.exe (PID: 8608)
- Unicorn-53749.exe (PID: 8624)
- Unicorn-11062.exe (PID: 8740)
- Unicorn-20772.exe (PID: 8756)
- Unicorn-26173.exe (PID: 8776)
- Unicorn-54134.exe (PID: 8848)
- Unicorn-30590.exe (PID: 8900)
- Unicorn-54599.exe (PID: 9000)
- Unicorn-21735.exe (PID: 8984)
- Unicorn-46815.exe (PID: 9024)
- Unicorn-21159.exe (PID: 9040)
- Unicorn-29327.exe (PID: 9060)
- Unicorn-34349.exe (PID: 9104)
- Unicorn-13374.exe (PID: 9080)
- Unicorn-34349.exe (PID: 9096)
- Unicorn-20317.exe (PID: 9148)
- Unicorn-50581.exe (PID: 9164)
- Unicorn-33860.exe (PID: 9184)
- Unicorn-57597.exe (PID: 9208)
- Unicorn-22887.exe (PID: 9236)
- Unicorn-56903.exe (PID: 9492)
- Unicorn-58055.exe (PID: 9420)
- Unicorn-28869.exe (PID: 9504)
- Unicorn-8086.exe (PID: 9548)
- Unicorn-61926.exe (PID: 9532)
- Unicorn-5886.exe (PID: 9588)
- Unicorn-332.exe (PID: 9604)
- Unicorn-30775.exe (PID: 9620)
- Unicorn-21455.exe (PID: 9700)
- Unicorn-62679.exe (PID: 9656)
- Unicorn-33004.exe (PID: 9636)
- Unicorn-62679.exe (PID: 9668)
- Unicorn-62679.exe (PID: 9652)
- Unicorn-18693.exe (PID: 9792)
- Unicorn-22031.exe (PID: 9764)
- Unicorn-37983.exe (PID: 9716)
- Unicorn-30007.exe (PID: 9860)
- Unicorn-13862.exe (PID: 9732)
- Unicorn-13670.exe (PID: 9828)
- Unicorn-22031.exe (PID: 9748)
- Unicorn-22031.exe (PID: 9756)
- Unicorn-38559.exe (PID: 9800)
- Unicorn-53286.exe (PID: 9880)
- Unicorn-7422.exe (PID: 9912)
- Unicorn-40287.exe (PID: 9932)
- Unicorn-32503.exe (PID: 9956)
- Unicorn-24335.exe (PID: 9980)
- Unicorn-56815.exe (PID: 9896)
- Unicorn-61646.exe (PID: 9996)
- Unicorn-32503.exe (PID: 9948)
- Unicorn-32311.exe (PID: 10016)
- Unicorn-65175.exe (PID: 10032)
- Unicorn-44350.exe (PID: 10096)
- Unicorn-57007.exe (PID: 10052)
- Unicorn-14822.exe (PID: 10168)
- Unicorn-19845.exe (PID: 10088)
- Unicorn-19845.exe (PID: 10080)
- Unicorn-64215.exe (PID: 10124)
- Unicorn-56047.exe (PID: 10136)
- Unicorn-39711.exe (PID: 10104)
- Unicorn-15206.exe (PID: 9300)
- Unicorn-52710.exe (PID: 9312)
- Unicorn-17436.exe (PID: 10232)
- Unicorn-52902.exe (PID: 10216)
- Unicorn-20229.exe (PID: 6492)
- Unicorn-36373.exe (PID: 10256)
- Unicorn-64334.exe (PID: 9316)
- Unicorn-62990.exe (PID: 10276)
- Unicorn-27332.exe (PID: 10376)
- Unicorn-20229.exe (PID: 10248)
- Unicorn-44734.exe (PID: 9280)
- Unicorn-27332.exe (PID: 10372)
- Unicorn-8580.exe (PID: 10532)
- Unicorn-33774.exe (PID: 10452)
- Unicorn-19740.exe (PID: 10484)
- Unicorn-55206.exe (PID: 10436)
- Unicorn-24454.exe (PID: 10608)
- Unicorn-1101.exe (PID: 10516)
- Unicorn-24916.exe (PID: 10552)
- Unicorn-19740.exe (PID: 10476)
- Unicorn-32117.exe (PID: 10648)
- Unicorn-8117.exe (PID: 10600)
- Unicorn-2252.exe (PID: 10592)
- Unicorn-65519.exe (PID: 10584)
Checks proxy server information
- WerFault.exe (PID: 9360)
Reads the software policy settings
- WerFault.exe (PID: 9360)
Creates files or folders in the user directory
- WerFault.exe (PID: 9360)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:04:26 10:28:09+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 176128 |
| InitializedDataSize: | 8192 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x13b0 |
| OSVersion: | 4 |
| ImageVersion: | 1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| CompanyName: | aaaa |
| ProductName: | Kawa噩i-Unicorn |
| FileVersion: | 1 |
| ProductVersion: | 1 |
| InternalName: | Kawaii-Unicorn |
| OriginalFileName: | Kawaii-Unicorn.exe |
Total processes
1 184
Monitored processes
1 066
Malicious processes
215
Suspicious processes
24
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 72 | C:\Users\admin\Desktop\Unicorn-33644.exe | C:\Users\admin\Desktop\Unicorn-33644.exe | Unicorn-24679.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 308 | C:\Users\admin\Desktop\Unicorn-31991.exe | C:\Users\admin\Desktop\Unicorn-31991.exe | Unicorn-39287.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 368 | C:\Users\admin\Desktop\Unicorn-12476.exe | C:\Users\admin\Desktop\Unicorn-12476.exe | — | Unicorn-58031.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 372 | C:\Users\admin\Desktop\Unicorn-21917.exe | C:\Users\admin\Desktop\Unicorn-21917.exe | Unicorn-62431.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 380 | C:\Users\admin\Desktop\Unicorn-31607.exe | C:\Users\admin\Desktop\Unicorn-31607.exe | Unicorn-45727.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 428 | C:\Users\admin\Desktop\Unicorn-48254.exe | C:\Users\admin\Desktop\Unicorn-48254.exe | Unicorn-48311.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 532 | C:\Users\admin\Desktop\Unicorn-3918.exe | C:\Users\admin\Desktop\Unicorn-3918.exe | — | Unicorn-21455.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 636 | C:\Users\admin\Desktop\Unicorn-44174.exe | C:\Users\admin\Desktop\Unicorn-44174.exe | — | Unicorn-22805.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 712 | C:\Users\admin\Desktop\Unicorn-14420.exe | C:\Users\admin\Desktop\Unicorn-14420.exe | — | Unicorn-30590.exe | |||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 780 | C:\Users\admin\Desktop\Unicorn-7989.exe | C:\Users\admin\Desktop\Unicorn-7989.exe | Unicorn-44974.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
Total events
77 826
Read events
77 760
Write events
57
Delete events
9
Modification events
| (PID) Process: | (6272) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6272) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6272) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6272) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (9360) WerFault.exe | Key: | \REGISTRY\A\{e99e70ad-5b4c-56eb-32f7-1639a0048b11}\Root\InventoryApplicationFile |
| Operation: | write | Name: | WritePermissionsCheck |
Value: 1 | |||
| (PID) Process: | (9360) WerFault.exe | Key: | \REGISTRY\A\{e99e70ad-5b4c-56eb-32f7-1639a0048b11}\Root\InventoryApplicationFile\PermissionsCheckTestKey |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (9360) WerFault.exe | Key: | \REGISTRY\A\{e99e70ad-5b4c-56eb-32f7-1639a0048b11}\Root\InventoryApplicationFile\unicorn-7118.exe|d0d9a0149e2f69b1 |
| Operation: | write | Name: | ProgramId |
Value: 00067724019ef2e244068aa5bb58d90b8b140000ffff | |||
| (PID) Process: | (9360) WerFault.exe | Key: | \REGISTRY\A\{e99e70ad-5b4c-56eb-32f7-1639a0048b11}\Root\InventoryApplicationFile\unicorn-7118.exe|d0d9a0149e2f69b1 |
| Operation: | write | Name: | FileId |
Value: 0000664c04ec0376580249f4c55bae2203b86a6ff05c | |||
| (PID) Process: | (9360) WerFault.exe | Key: | \REGISTRY\A\{e99e70ad-5b4c-56eb-32f7-1639a0048b11}\Root\InventoryApplicationFile\unicorn-7118.exe|d0d9a0149e2f69b1 |
| Operation: | write | Name: | LowerCaseLongPath |
Value: c:\users\admin\desktop\unicorn-7118.exe | |||
| (PID) Process: | (9360) WerFault.exe | Key: | \REGISTRY\A\{e99e70ad-5b4c-56eb-32f7-1639a0048b11}\Root\InventoryApplicationFile\unicorn-7118.exe|d0d9a0149e2f69b1 |
| Operation: | write | Name: | LongPathHash |
Value: unicorn-7118.exe|d0d9a0149e2f69b1 | |||
Executable files
1 229
Suspicious files
7
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6272 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\ETEWE2QA25SGBDXB2VJ3.temp | — | |
MD5:— | SHA256:— | |||
| 6600 | Unicorn-48311.exe | C:\Users\admin\Desktop\Unicorn-24679.exe | executable | |
MD5:FFA8A84569FBA77D0439DFB0C78C5500 | SHA256:E18EB3E11F0923347315B109FBE72C584D2853E58309F017CAE084FB0F98A43A | |||
| 6620 | Unicorn-44974.exe | C:\Users\admin\Desktop\Unicorn-49375.exe | executable | |
MD5:EA3A16EEEB1D34EFAE79E9AC5DDE607D | SHA256:67B4FB7894DED1FA2D55CFDBABF60E222CCF512CC63EC79E949C77ACAF2D982F | |||
| 6600 | Unicorn-48311.exe | C:\Users\admin\Desktop\Unicorn-16437.exe | executable | |
MD5:E1AC4B6097E3660D7952ECE960719CBC | SHA256:C8138F6F8DBFA1E8FE53B3FB1AF46D95B96677D6FF52112724967D8A6B5C02F1 | |||
| 6272 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_2xkr4sq0.kgt.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6576 | Unicorn-62431.exe | C:\Users\admin\Desktop\Unicorn-29509.exe | executable | |
MD5:6D7DB654F8A888E1EB9D376102C88C8B | SHA256:4DE087516C658483A1DF92BE1F0BE4607505C8DDB7DA9013CD612CF191AD8649 | |||
| 6480 | 62a986c16cdede724c9742f1c825f9e1f0ae5cbbe023dff477f3d6bf0b9e6966.exe | C:\Users\admin\Desktop\Unicorn-62431.exe | executable | |
MD5:0813FDA2D9435BC9C1A66F4833EE5951 | SHA256:5BA8F0E4DB436A38A4D30655911F118992DC9A4E9E1F3AF99D7BBFE29BE1BA3D | |||
| 6272 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF113843.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 6272 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_zhiarybs.4ew.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 6644 | Unicorn-24679.exe | C:\Users\admin\Desktop\Unicorn-3822.exe | executable | |
MD5:FAE8F51FF54CB30446769795D1D4F8C3 | SHA256:92E0BBBC598F1AB5BD85CBA3F3BA1E73A53D20A350D29E2C36941B5DA275A9D0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
23
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4428 | RUXIMICS.exe | GET | — | 184.51.127.17:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
5504 | svchost.exe | GET | 200 | 184.51.127.17:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
5140 | MoUsoCoreWorker.exe | GET | 200 | 184.51.127.17:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
5504 | svchost.exe | GET | 200 | 2.17.245.133:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
5140 | MoUsoCoreWorker.exe | GET | 200 | 2.17.245.133:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
4428 | RUXIMICS.exe | GET | 200 | 2.17.245.133:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
— | — | POST | 200 | 20.42.73.31:443 | https://self.events.data.microsoft.com/OneCollector/1.0/ | unknown | binary | 9 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5504 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4428 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5140 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4428 | RUXIMICS.exe | 184.51.127.17:80 | crl.microsoft.com | Akamai International B.V. | IT | unknown |
4364 | svchost.exe | 239.255.255.250:1900 | — | — | — | unknown |
5504 | svchost.exe | 184.51.127.17:80 | crl.microsoft.com | Akamai International B.V. | IT | unknown |
5140 | MoUsoCoreWorker.exe | 184.51.127.17:80 | crl.microsoft.com | Akamai International B.V. | IT | unknown |
5504 | svchost.exe | 2.17.245.133:80 | www.microsoft.com | Akamai International B.V. | NL | unknown |
5140 | MoUsoCoreWorker.exe | 2.17.245.133:80 | www.microsoft.com | Akamai International B.V. | NL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
watson.events.data.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |