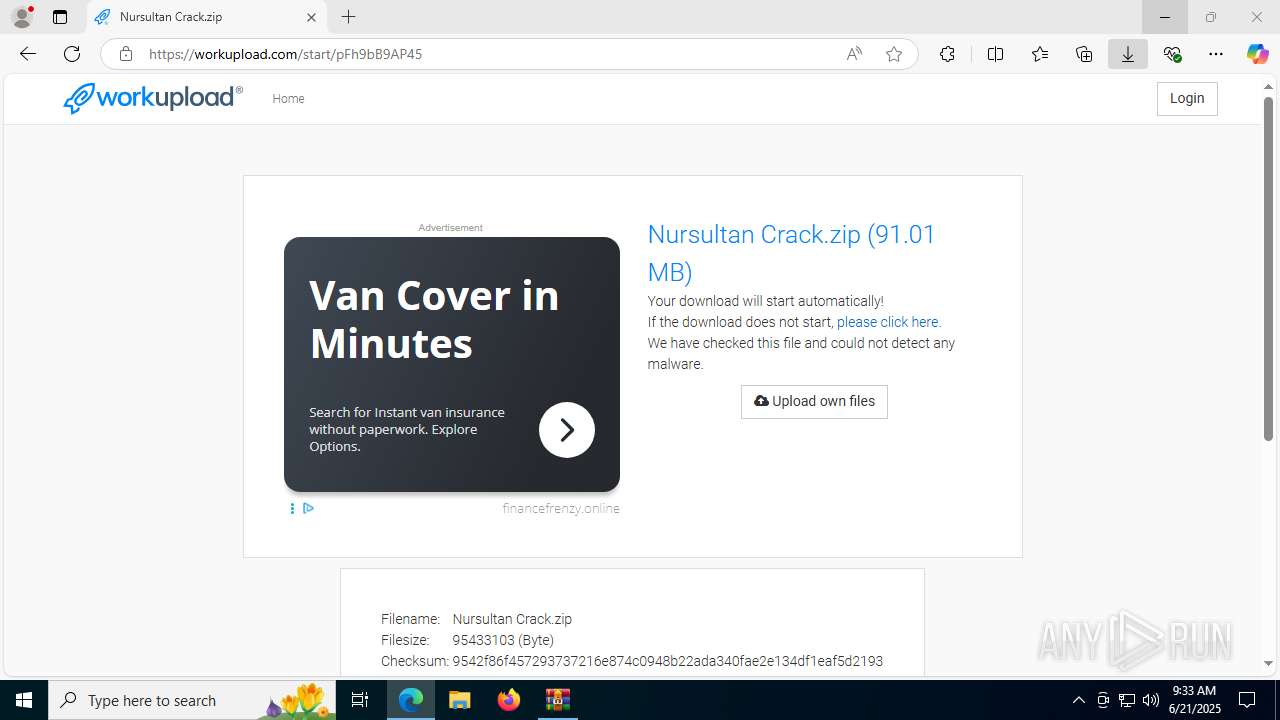
| URL: | https://workupload.com/file/pFh9bB9AP45 |
| Full analysis: | https://app.any.run/tasks/0091b773-a247-4a7e-bec3-259b6661602f |
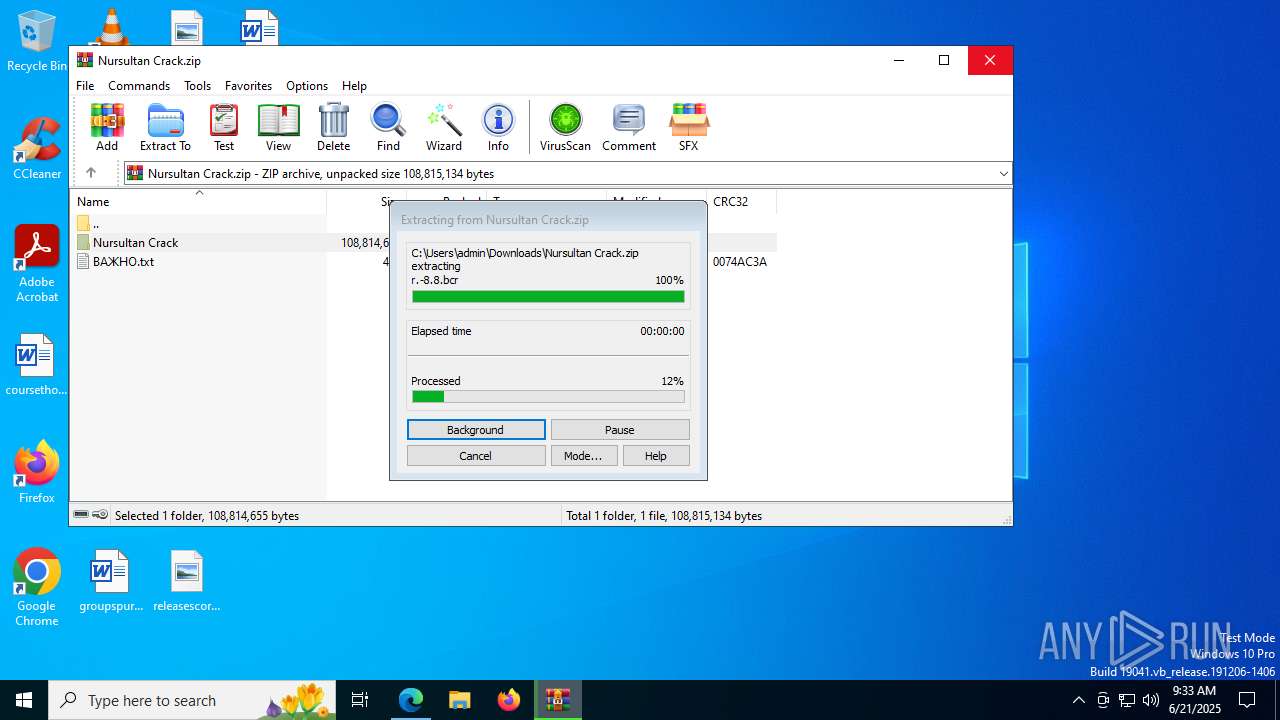
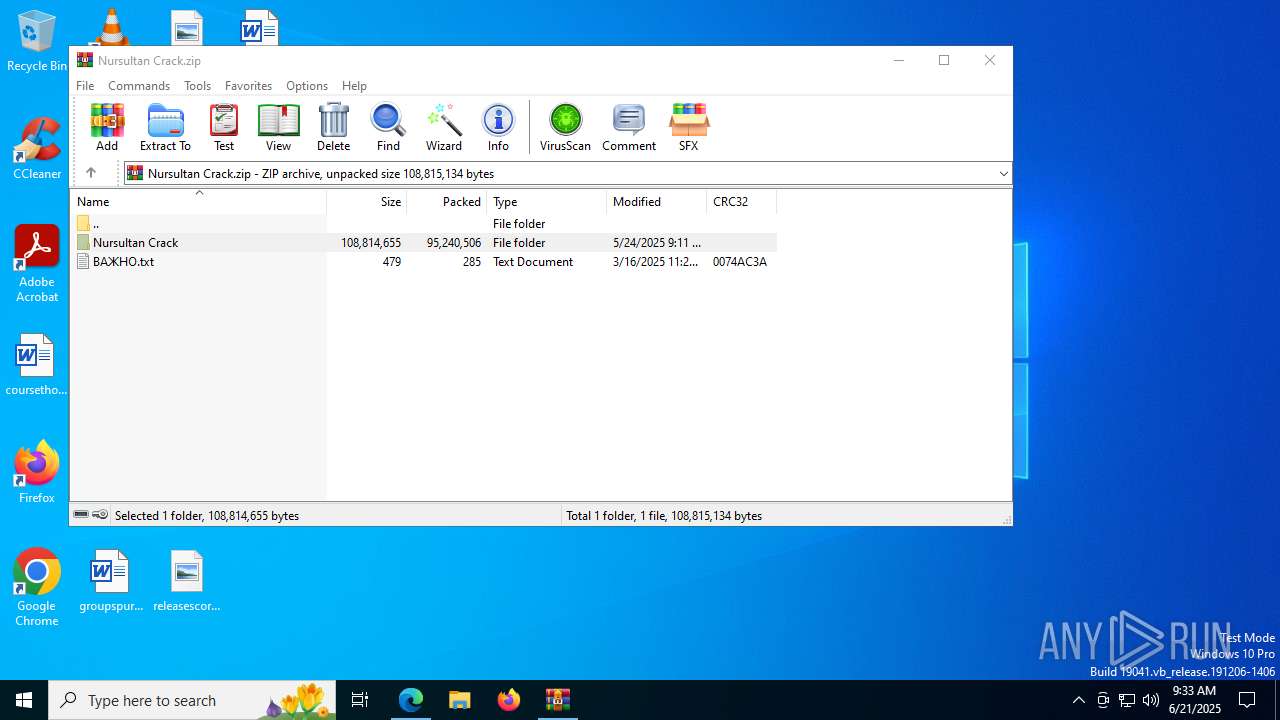
| Verdict: | Malicious activity |
| Analysis date: | June 21, 2025, 09:32:44 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 27792274E8EED7D9418BFBE7E73FC118 |
| SHA1: | 98E1BD771D2625DEAE5D444ECB3E7750C4DD7646 |
| SHA256: | 628AC5FAB08B8795C1D1CB666C33114DC31E94D8D4B1CCD6EB8AC8909403FFB6 |
| SSDEEP: | 3:N8bXOrZXDcHV0:2itz/ |
MALICIOUS
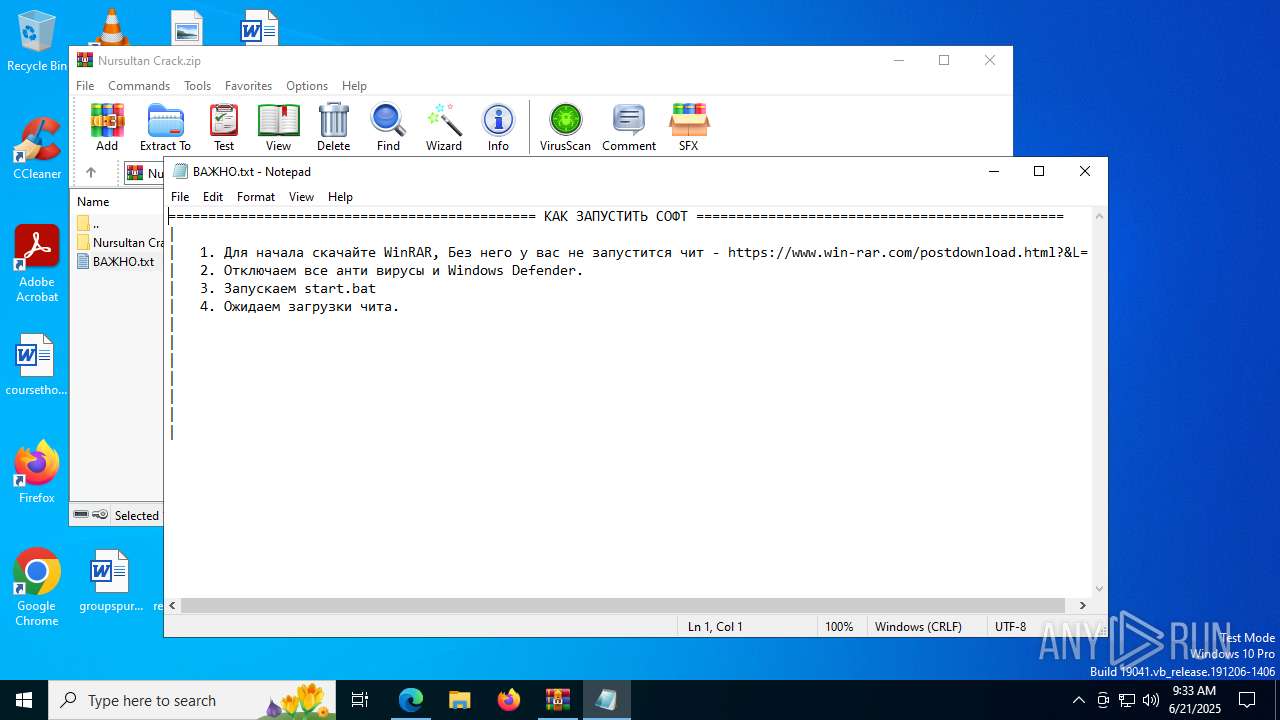
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 2520)
- cmd.exe (PID: 7852)
Bypass execution policy to execute commands
- powershell.exe (PID: 7220)
- powershell.exe (PID: 7152)
- powershell.exe (PID: 2764)
- powershell.exe (PID: 4708)
- powershell.exe (PID: 3944)
- powershell.exe (PID: 5124)
- powershell.exe (PID: 4824)
Changes Windows Defender settings
- cmd.exe (PID: 7852)
Adds path to the Windows Defender exclusion list
- cmd.exe (PID: 7852)
Script downloads file (POWERSHELL)
- powershell.exe (PID: 7908)
SUSPICIOUS
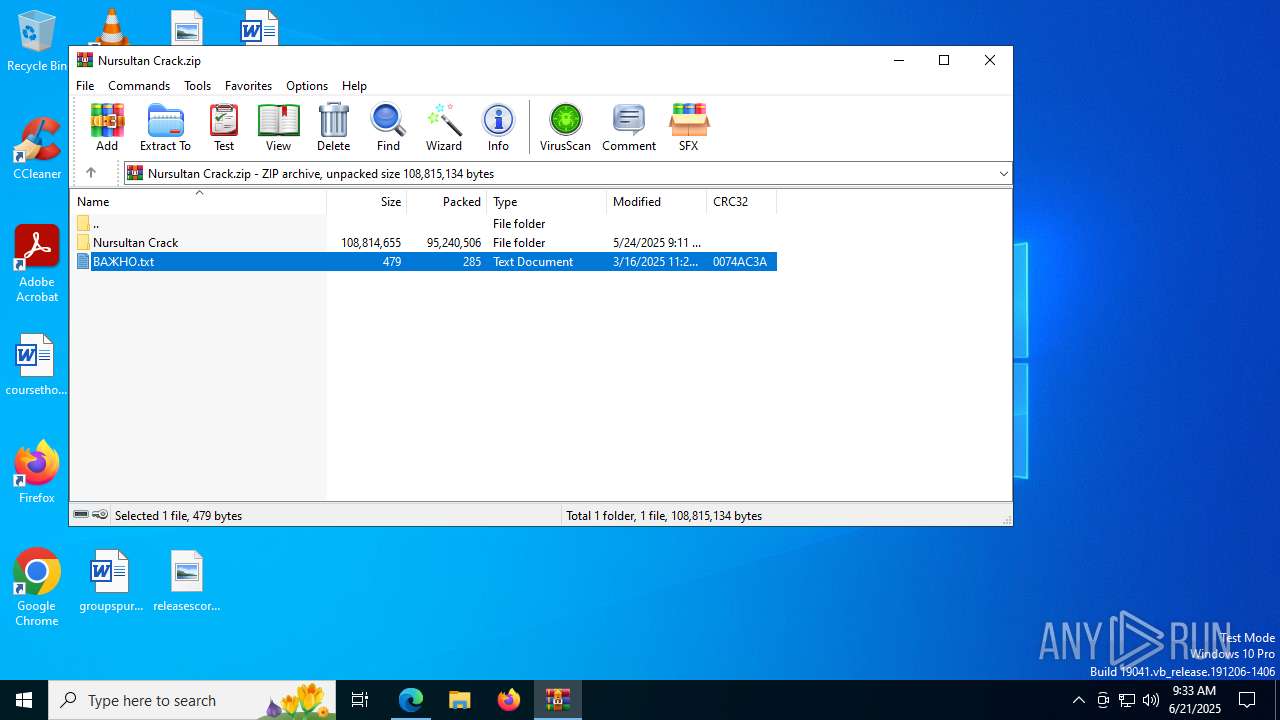
Start notepad (likely ransomware note)
- WinRAR.exe (PID: 7652)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 7652)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 2520)
- cmd.exe (PID: 7852)
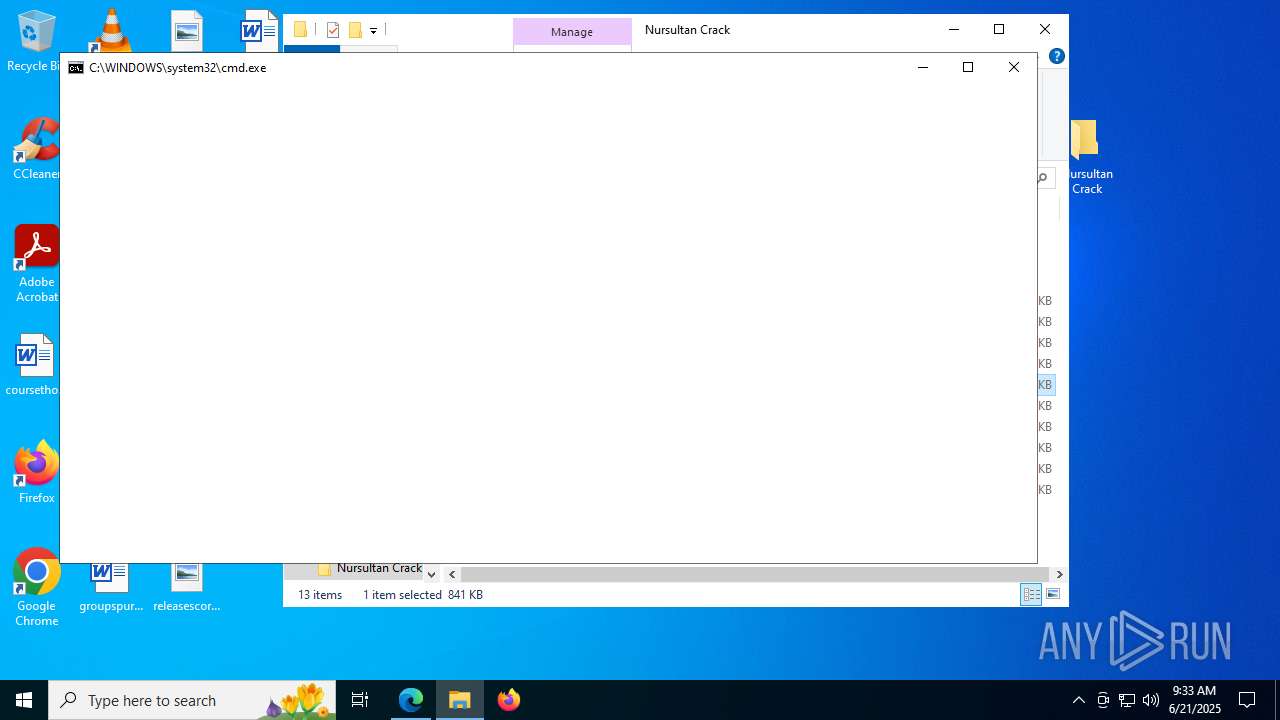
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2520)
- powershell.exe (PID: 6348)
- cmd.exe (PID: 7852)
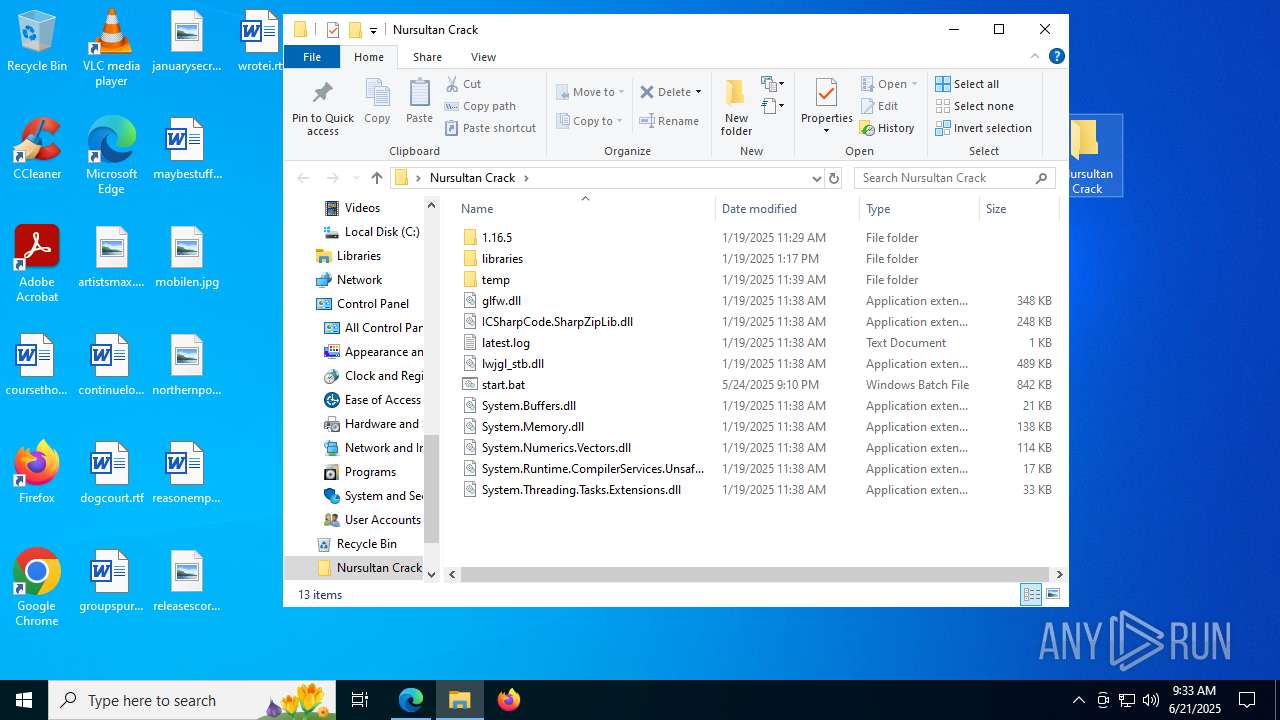
Process drops legitimate windows executable
- WinRAR.exe (PID: 7652)
Application launched itself
- cmd.exe (PID: 2520)
- cmd.exe (PID: 7852)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 6212)
- cmd.exe (PID: 2212)
- cmd.exe (PID: 3608)
- cmd.exe (PID: 1700)
- cmd.exe (PID: 7692)
- cmd.exe (PID: 5896)
- cmd.exe (PID: 7716)
Starts application with an unusual extension
- cmd.exe (PID: 2520)
- cmd.exe (PID: 7852)
Uses RUNDLL32.EXE to load library
- cmd.exe (PID: 2520)
- cmd.exe (PID: 7852)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 2520)
- cmd.exe (PID: 7852)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2520)
- cmd.exe (PID: 7852)
Lists computer manufacturer and model
- cmd.exe (PID: 2520)
- cmd.exe (PID: 7852)
The process hides Powershell's copyright startup banner
- cmd.exe (PID: 2520)
- cmd.exe (PID: 7852)
Starts NET.EXE to display or manage information about active sessions
- cmd.exe (PID: 2520)
- net.exe (PID: 4888)
- cmd.exe (PID: 7852)
- net.exe (PID: 7608)
Starts process via Powershell
- powershell.exe (PID: 6348)
Executing commands from a ".bat" file
- powershell.exe (PID: 6348)
Hides errors and continues executing the command without stopping
- powershell.exe (PID: 2764)
- powershell.exe (PID: 4312)
- powershell.exe (PID: 4824)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 7852)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 7852)
Executes script without checking the security policy
- powershell.exe (PID: 8072)
- powershell.exe (PID: 2536)
- powershell.exe (PID: 4576)
- powershell.exe (PID: 7988)
- powershell.exe (PID: 6200)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 7852)
Probably download files using WebClient
- cmd.exe (PID: 7852)
INFO
Reads the computer name
- identity_helper.exe (PID: 7792)
Reads Environment values
- identity_helper.exe (PID: 7792)
Reads Microsoft Office registry keys
- WinRAR.exe (PID: 7652)
- msedge.exe (PID: 4500)
Application launched itself
- msedge.exe (PID: 4500)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7652)
Reads security settings of Internet Explorer
- notepad.exe (PID: 7916)
- WMIC.exe (PID: 3392)
- WMIC.exe (PID: 7924)
- WMIC.exe (PID: 7920)
- WMIC.exe (PID: 7632)
- WMIC.exe (PID: 8044)
- WMIC.exe (PID: 7100)
- WMIC.exe (PID: 1700)
Checks supported languages
- identity_helper.exe (PID: 7792)
- chcp.com (PID: 2764)
- chcp.com (PID: 7896)
Manual execution by a user
- cmd.exe (PID: 2520)
The sample compiled with english language support
- WinRAR.exe (PID: 7652)
Changes the display of characters in the console
- cmd.exe (PID: 2520)
- cmd.exe (PID: 7852)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 4312)
Checks proxy server information
- powershell.exe (PID: 7908)
- slui.exe (PID: 7788)
Reads the software policy settings
- slui.exe (PID: 7788)
Disables trace logs
- powershell.exe (PID: 7908)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
253
Monitored processes
112
Malicious processes
3
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 424 | doskey ICACLS=SC | C:\Windows\System32\doskey.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Keyboard History Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 640 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3692,i,11014316806960099559,14191235615749024386,262144 --variations-seed-version --mojo-platform-channel-handle=3708 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 728 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=7764,i,11014316806960099559,14191235615749024386,262144 --variations-seed-version --mojo-platform-channel-handle=7724 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1700 | C:\WINDOWS\system32\cmd.exe /c wmic computersystem get manufacturer /value | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1700 | wmic computersystem get manufacturer /value | C:\Windows\System32\wbem\WMIC.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: WMI Commandline Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2212 | C:\WINDOWS\system32\cmd.exe /c wmic computersystem get manufacturer /value | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
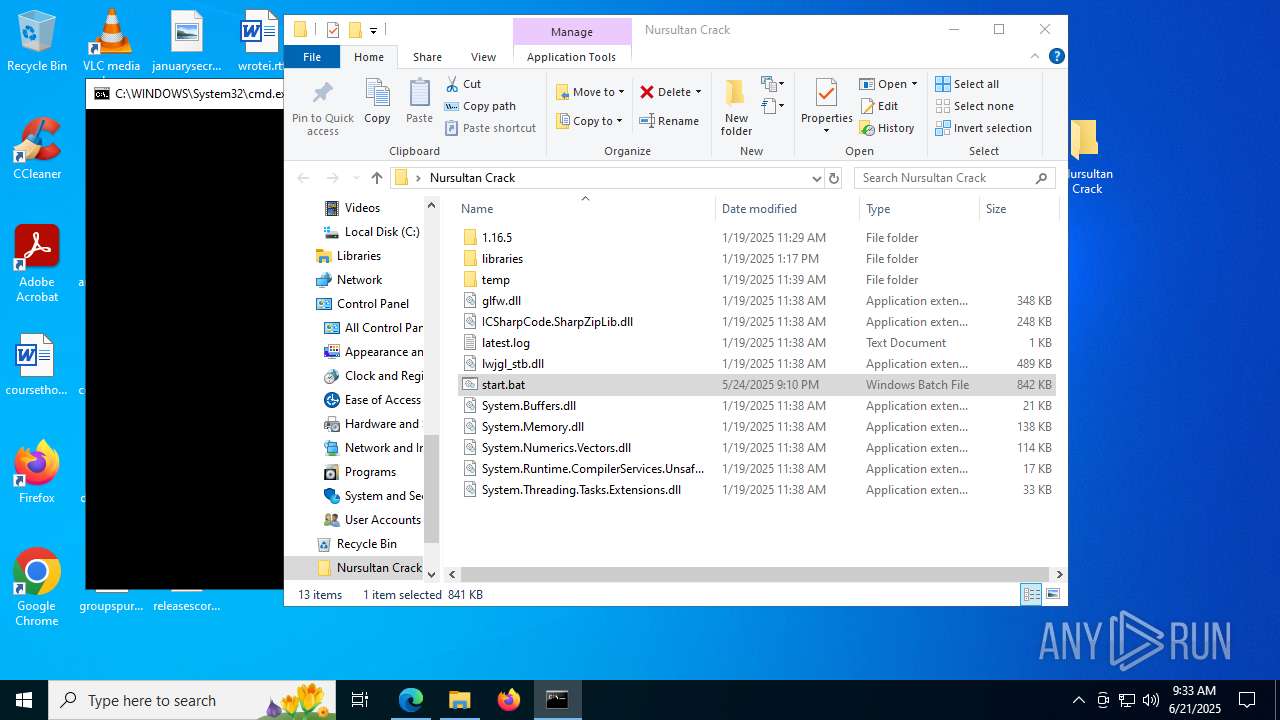
| 2212 | findstr /i "echo" "C:\Users\admin\Desktop\Nursultan Crack\start.bat" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
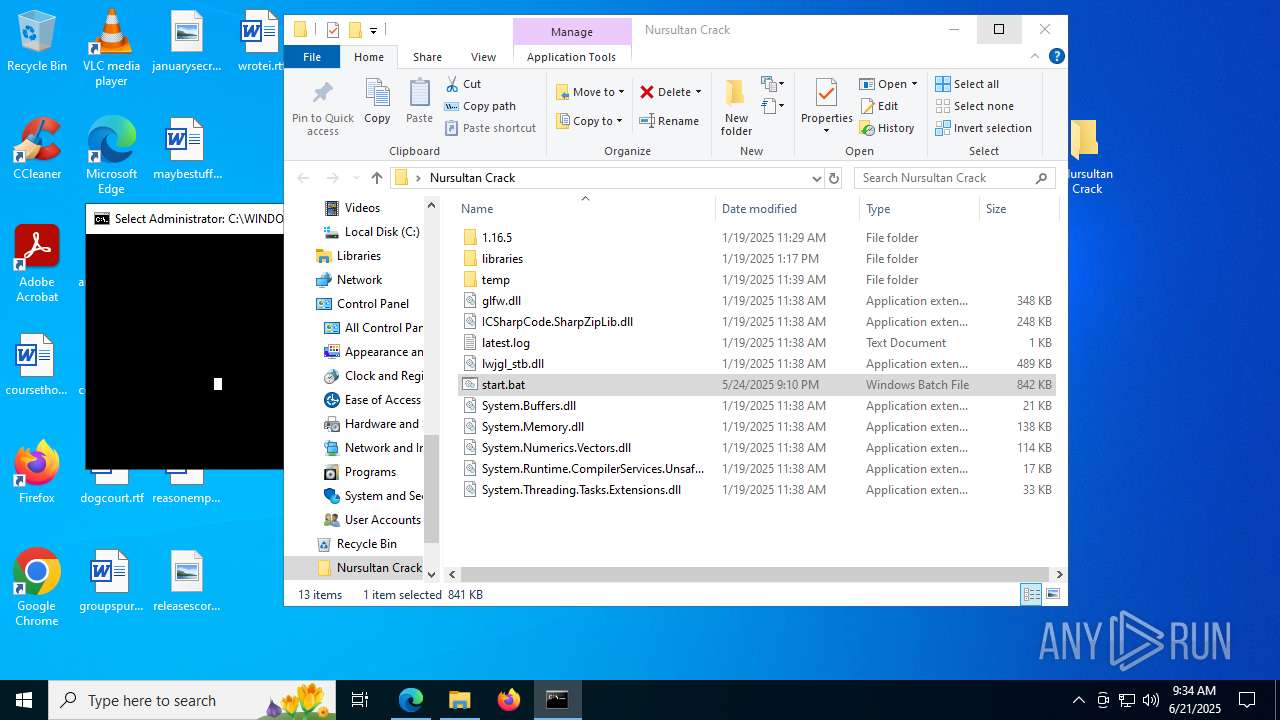
| 2520 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\Desktop\Nursultan Crack\start.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2536 | powershell.exe -nop -c "Write-Host -NoNewLine $null" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2620 | rundll32 | C:\Windows\System32\rundll32.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
79 449
Read events
79 400
Write events
49
Delete events
0
Modification events
| (PID) Process: | (4500) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4500) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4500) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (4500) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (4500) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4500) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4500) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 597D16F2A7962F00 | |||
| (PID) Process: | (4500) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\263054 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {A4295C0B-DE65-447B-8544-A3C68A24ACA3} | |||
| (PID) Process: | (4500) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\263054 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {4613528B-FD0A-4409-BCBA-99A2DCF12366} | |||
| (PID) Process: | (4500) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\263054 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {D8704C00-82E0-437B-A4FD-9B6D804C7289} | |||
Executable files
45
Suspicious files
685
Text files
113
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4500 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF176263.TMP | — | |
MD5:— | SHA256:— | |||
| 4500 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4500 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF176273.TMP | — | |
MD5:— | SHA256:— | |||
| 4500 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF176273.TMP | — | |
MD5:— | SHA256:— | |||
| 4500 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4500 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF176273.TMP | — | |
MD5:— | SHA256:— | |||
| 4500 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF176273.TMP | — | |
MD5:— | SHA256:— | |||
| 4500 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4500 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4500 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
166
DNS requests
115
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3148 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1751066851&P2=404&P3=2&P4=PsCzt%2breW7ZUxvz%2fOO2cjaay%2bb%2fM%2bOpQ%2b3RdGg465GyrdJVuPJ8lLs8dl5f6bSS%2f9p8IXFjTkm%2bdS5VdiCescQ%3d%3d | unknown | — | — | whitelisted |
3148 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9244b52a-55cc-41a2-b7c4-7f4983d8753c?P1=1751066854&P2=404&P3=2&P4=CCtMR%2fuxhMHaXLPsP0ZvrNBTDd0EpeF%2f7jRzkQ4dYfinYXMsIF%2fuy54h%2fQgn%2fog%2bTtqWAxrLXNKYo61CiRouTw%3d%3d | unknown | — | — | whitelisted |
3148 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1751066852&P2=404&P3=2&P4=Um44CYFLJfv5bl0jXgiddGi1%2b%2brRbCOSXE%2b4jbm743MFZ3e%2fBx2KtMakhi3FGQAi4jIlausF5M4wzvDIW45E5Q%3d%3d | unknown | — | — | whitelisted |
3976 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:AnxO15bYePD-6KbMuSx8FINb5SYY7wEUB5xFu0gH1Qo&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
7020 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.55.104.172:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2220 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
3148 | svchost.exe | GET | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/4c4fdee0-d69c-42b7-bf5c-3ec046e9dfc9?P1=1751066852&P2=404&P3=2&P4=Um44CYFLJfv5bl0jXgiddGi1%2b%2brRbCOSXE%2b4jbm743MFZ3e%2fBx2KtMakhi3FGQAi4jIlausF5M4wzvDIW45E5Q%3d%3d | unknown | — | — | whitelisted |
3148 | svchost.exe | GET | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9244b52a-55cc-41a2-b7c4-7f4983d8753c?P1=1751066854&P2=404&P3=2&P4=CCtMR%2fuxhMHaXLPsP0ZvrNBTDd0EpeF%2f7jRzkQ4dYfinYXMsIF%2fuy54h%2fQgn%2fog%2bTtqWAxrLXNKYo61CiRouTw%3d%3d | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 23.209.209.135:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3800 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3976 | msedge.exe | 193.111.198.62:443 | workupload.com | myLoc managed IT AG | DE | whitelisted |
3976 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3976 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3976 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3976 | msedge.exe | 2.23.227.199:443 | copilot.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
workupload.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
fundingchoicesmessages.google.com |
| whitelisted |
googleads.g.doubleclick.net |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |