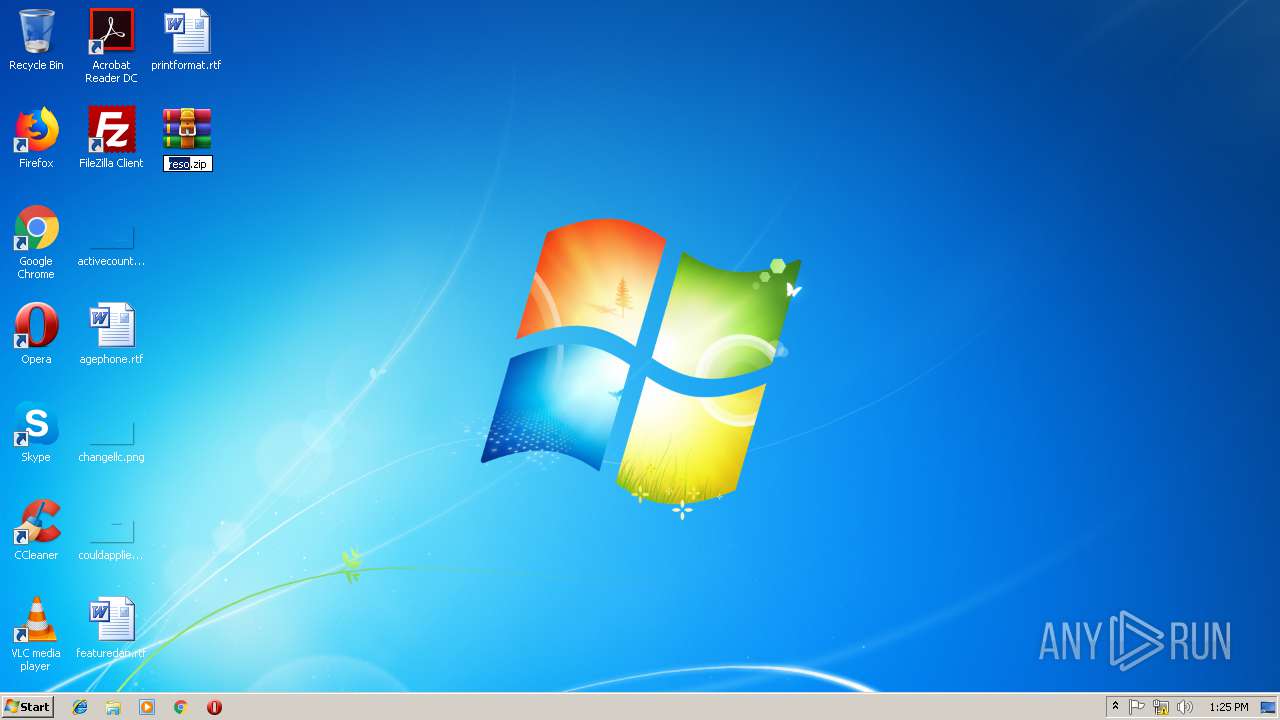
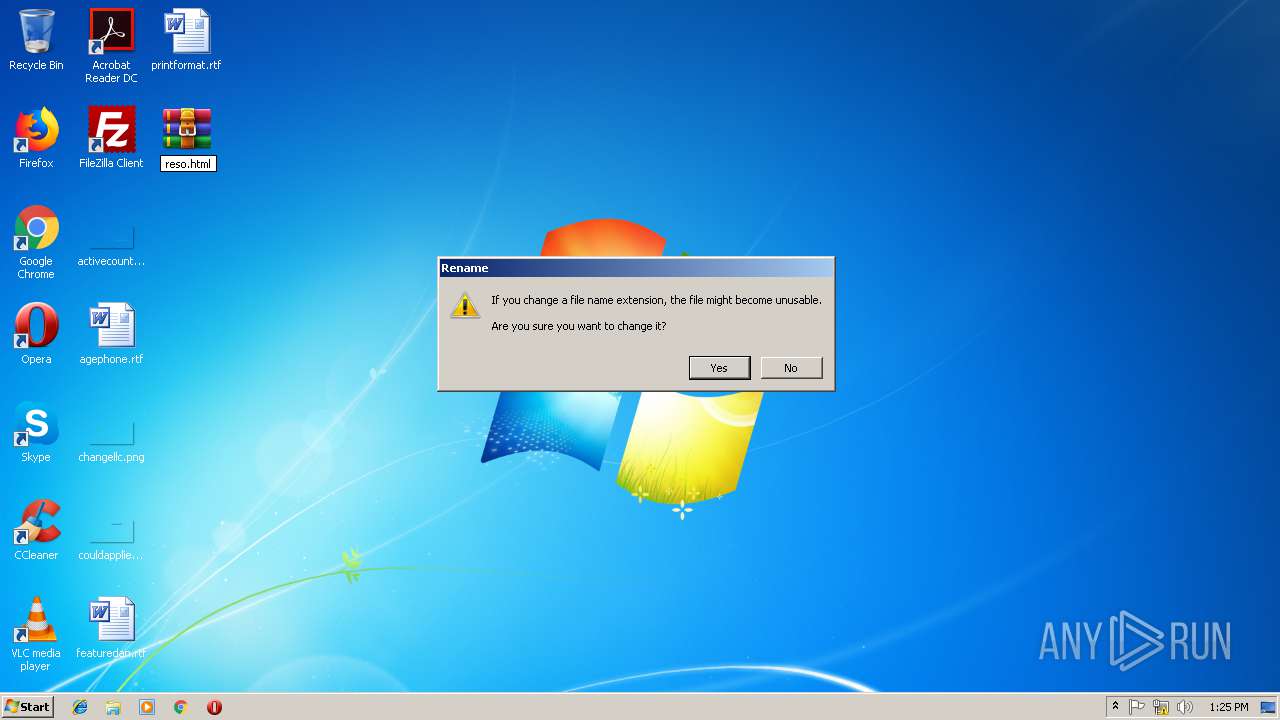
| File name: | http://colortheglobe.com/wp-content/themes/twentyseventeen/inc/reso.zip |
| Full analysis: | https://app.any.run/tasks/e97ba444-0ae8-41af-a62e-743588609c35 |
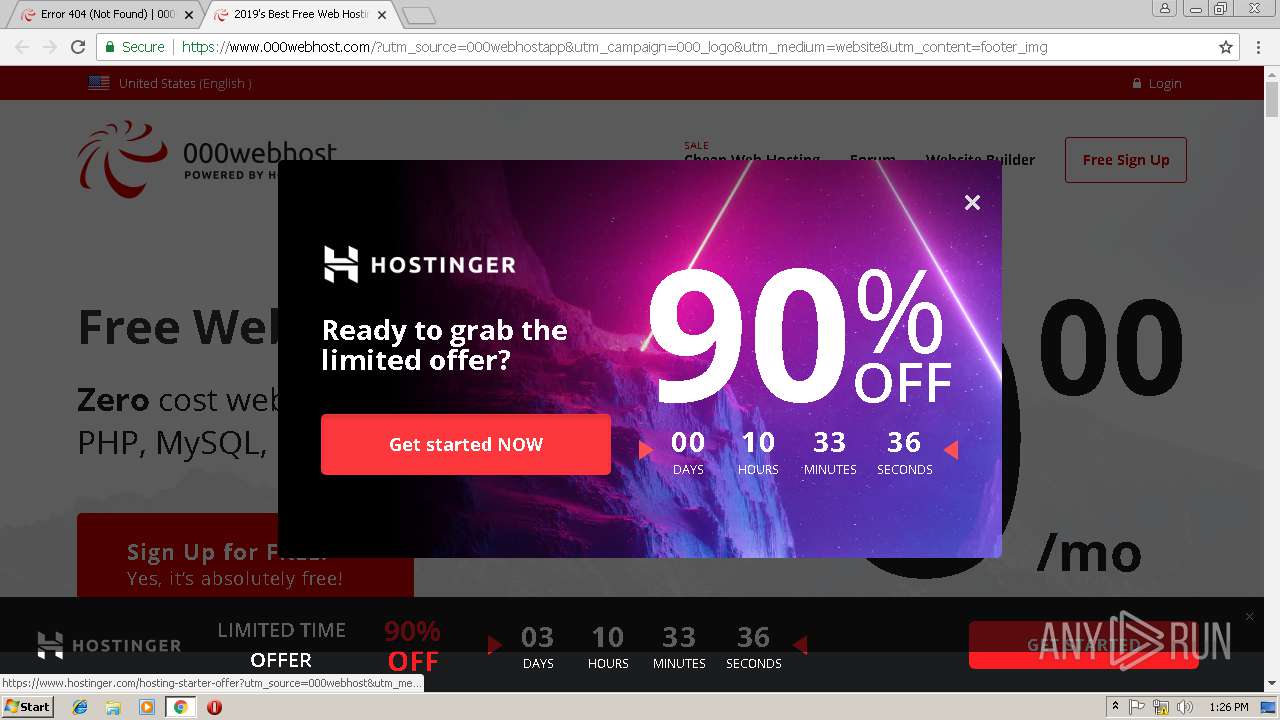
| Verdict: | Malicious activity |
| Analysis date: | March 14, 2019, 13:23:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines |
| MD5: | 065210D384B8F5988DCC2EE1D7D3BD29 |
| SHA1: | 85FA82967A505472C8271BA51F9C4E8BFF07BFD5 |
| SHA256: | 627C2FD168C193D82811B4247102557DA92730DEF9B89CF66F8B2B050BD2B6E5 |
| SSDEEP: | 384:zP+ProMuvAVIgtsP8frhFgmayYU+/oe9b4LdIyoo:zP+53VzsP8fkmayYU+/oe9b4LdIyoo |
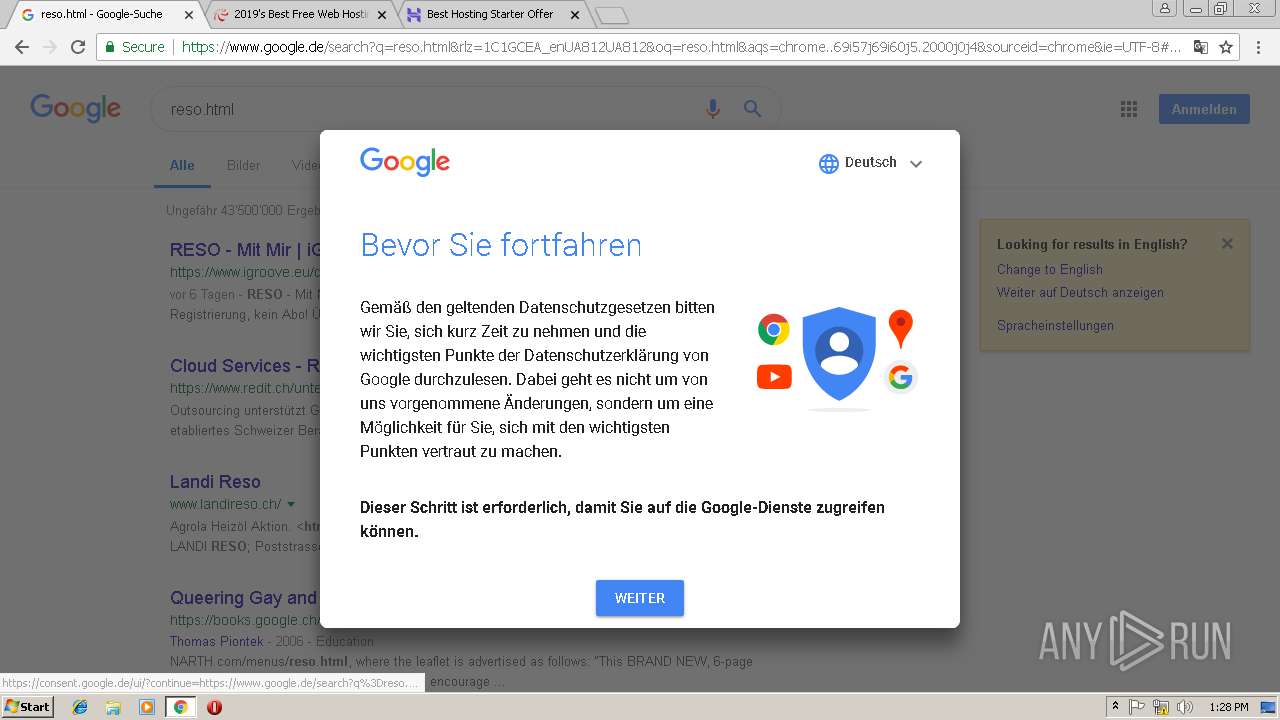
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
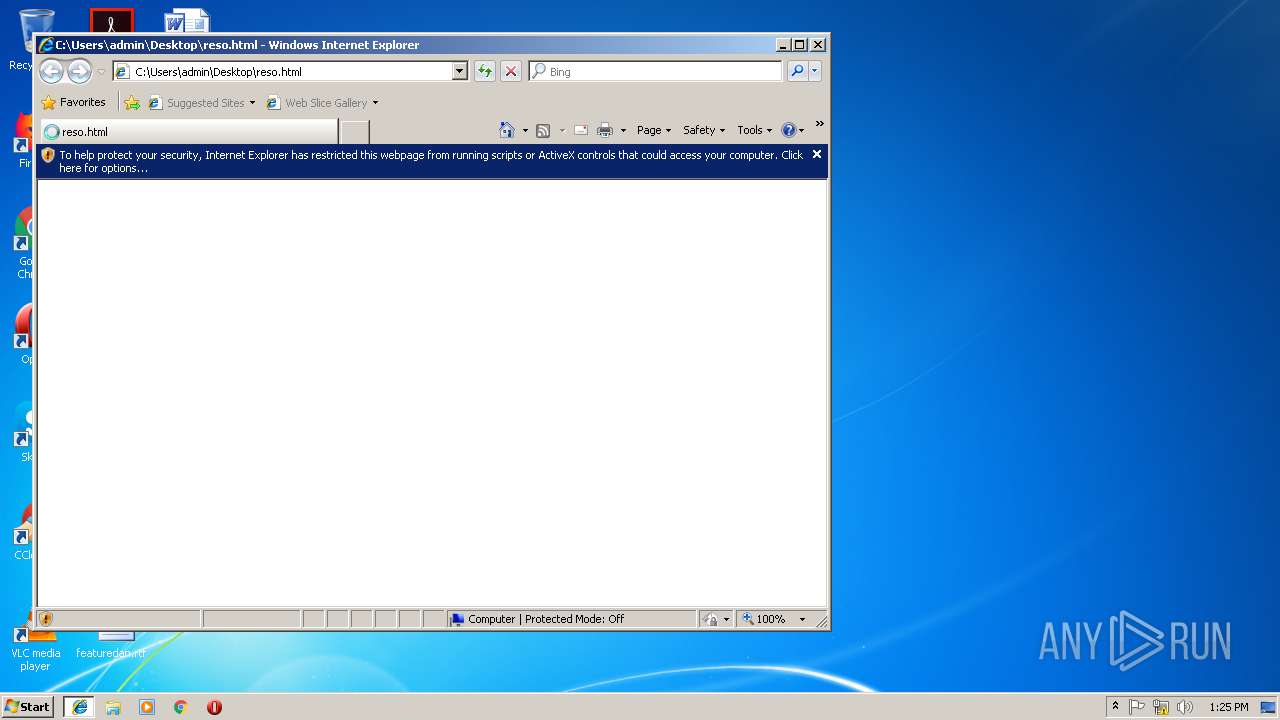
Reads internet explorer settings
- iexplore.exe (PID: 2440)
Reads settings of System Certificates
- iexplore.exe (PID: 2440)
- chrome.exe (PID: 1488)
Changes internet zones settings
- iexplore.exe (PID: 1736)
Application launched itself
- chrome.exe (PID: 1488)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
EXIF
HTML
| viewport: | width=device-width,initial-scale=1.0,minimum-scale=1.0,maximum-scale=1.0,user-scalable=no |
|---|---|
| HandheldFriendly: | |
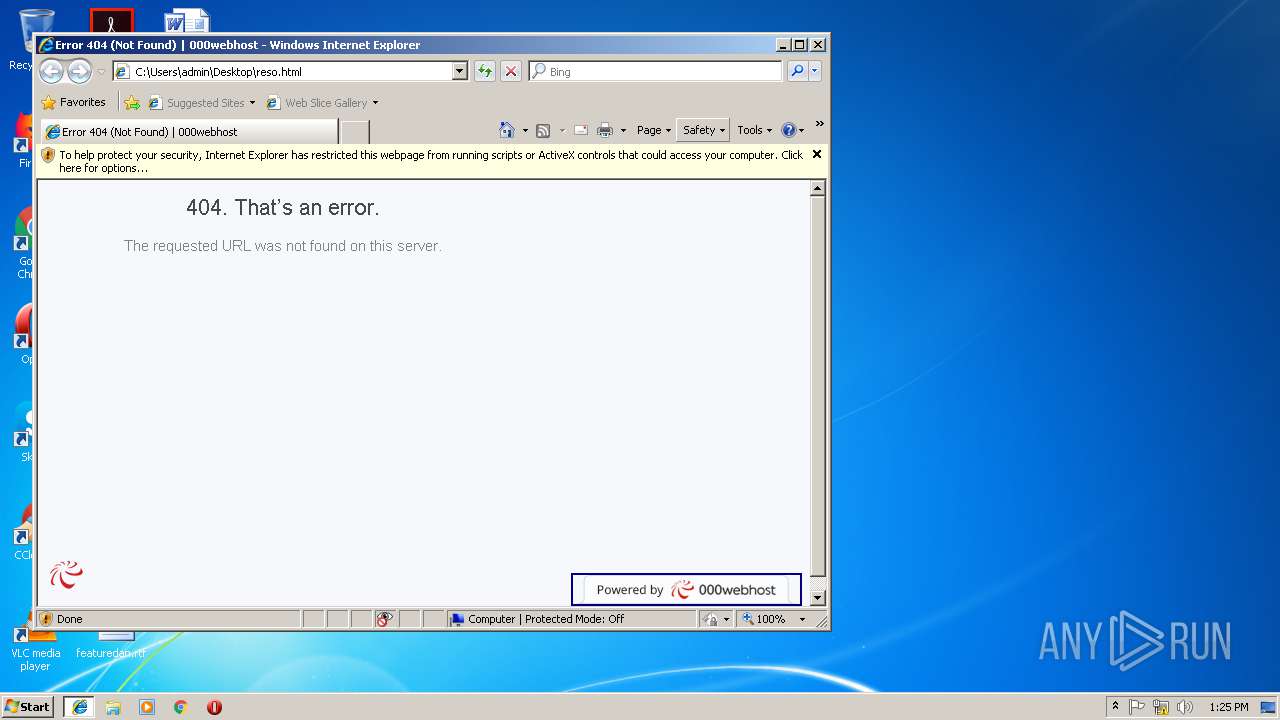
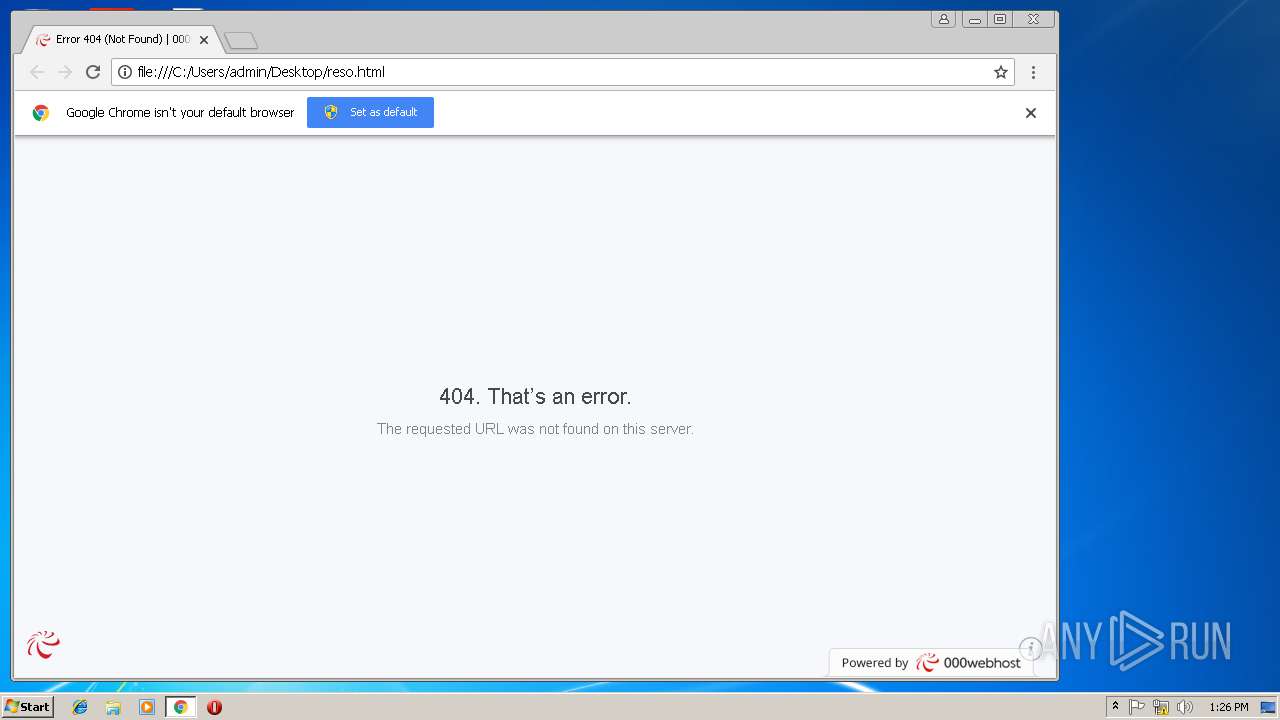
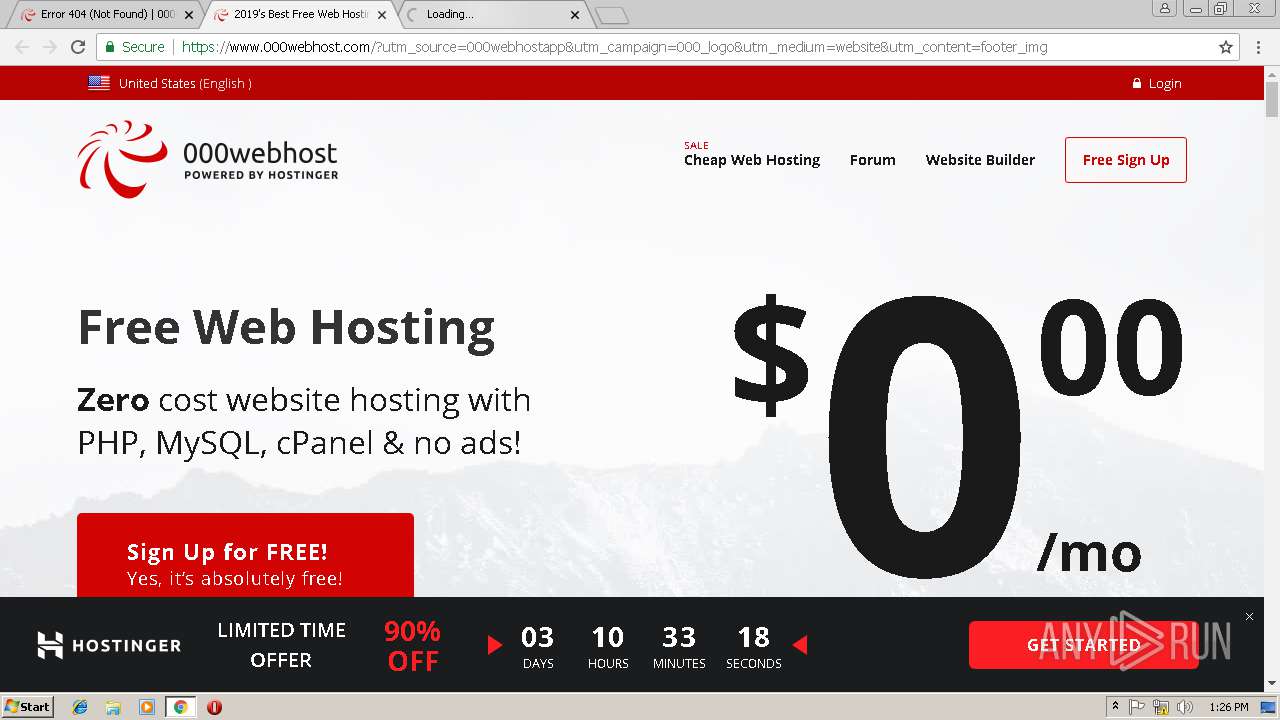
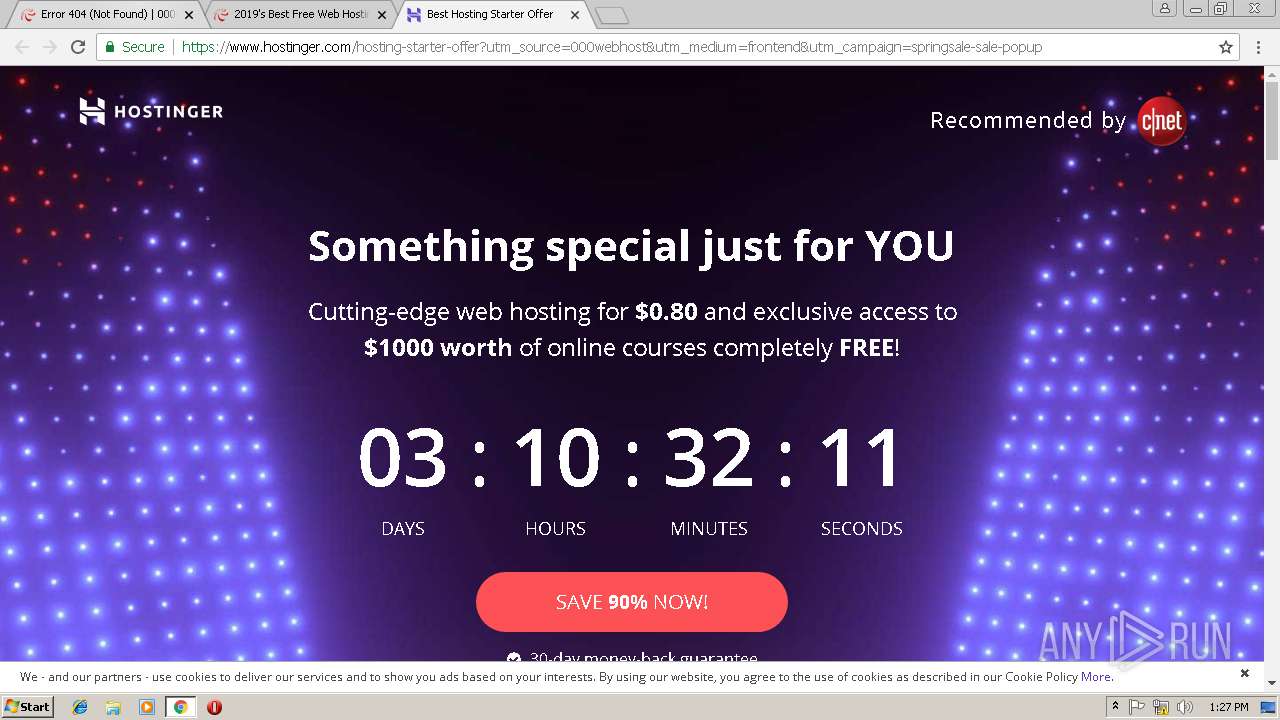
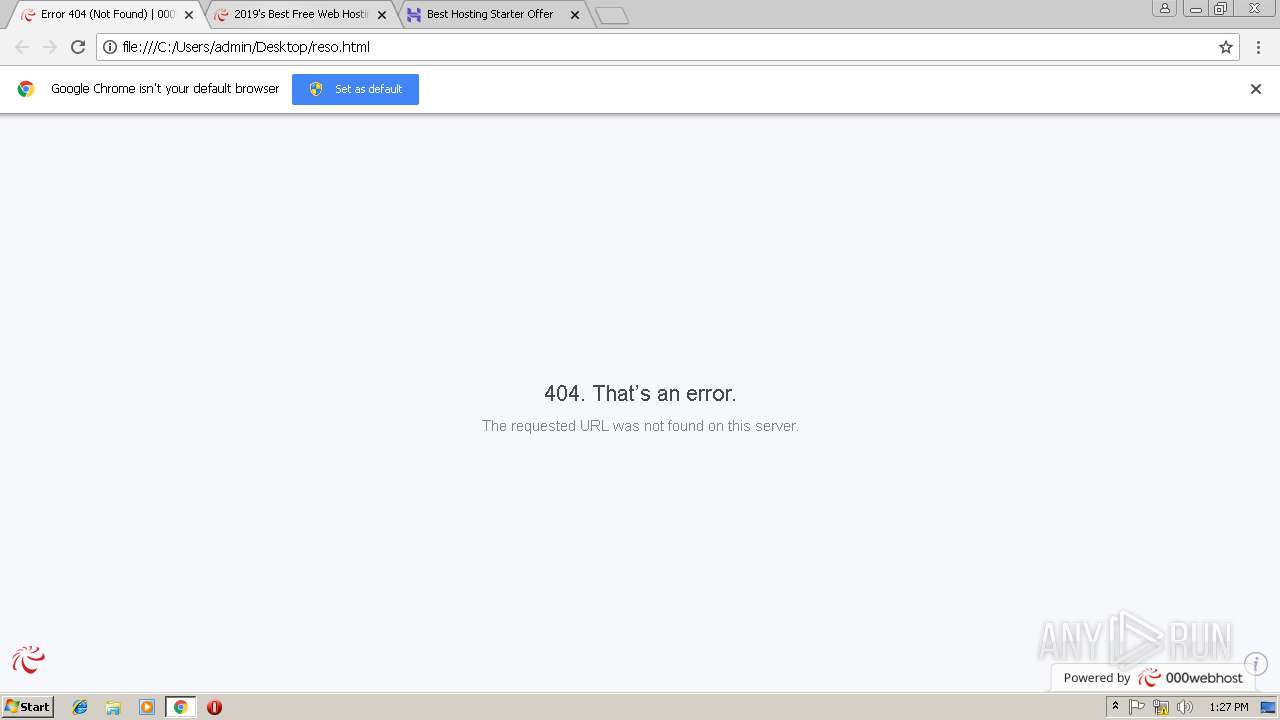
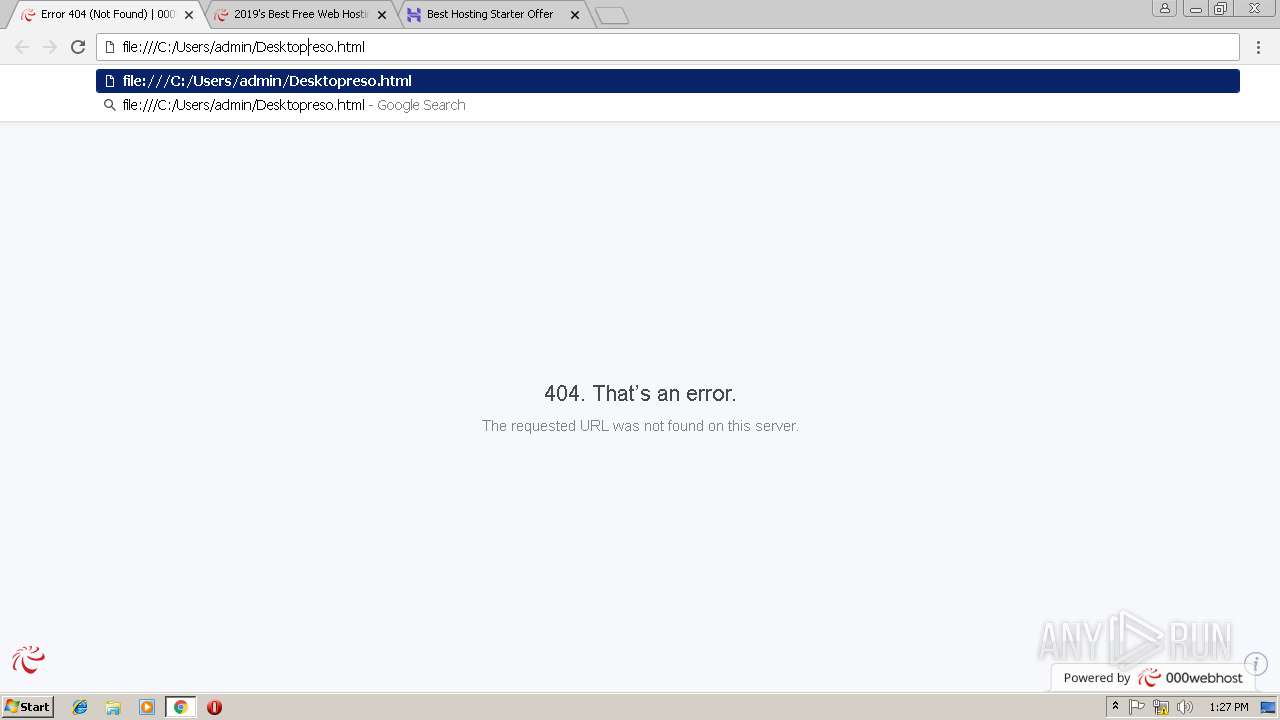
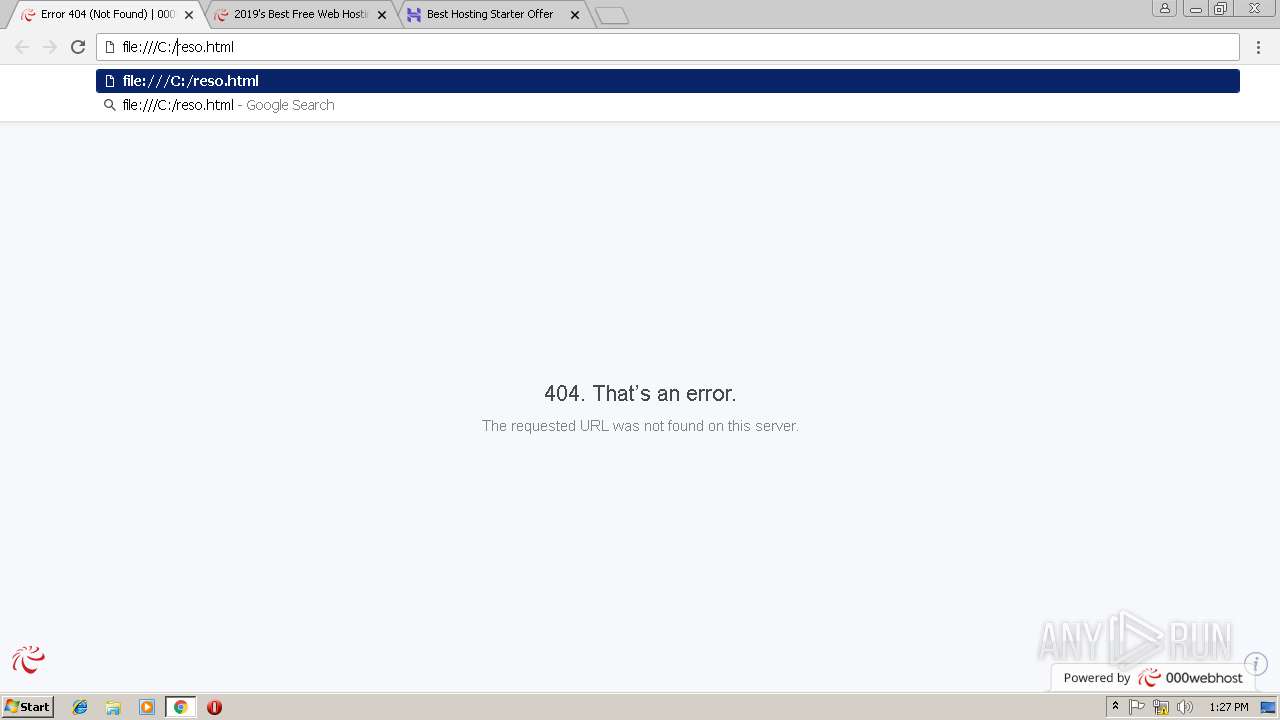
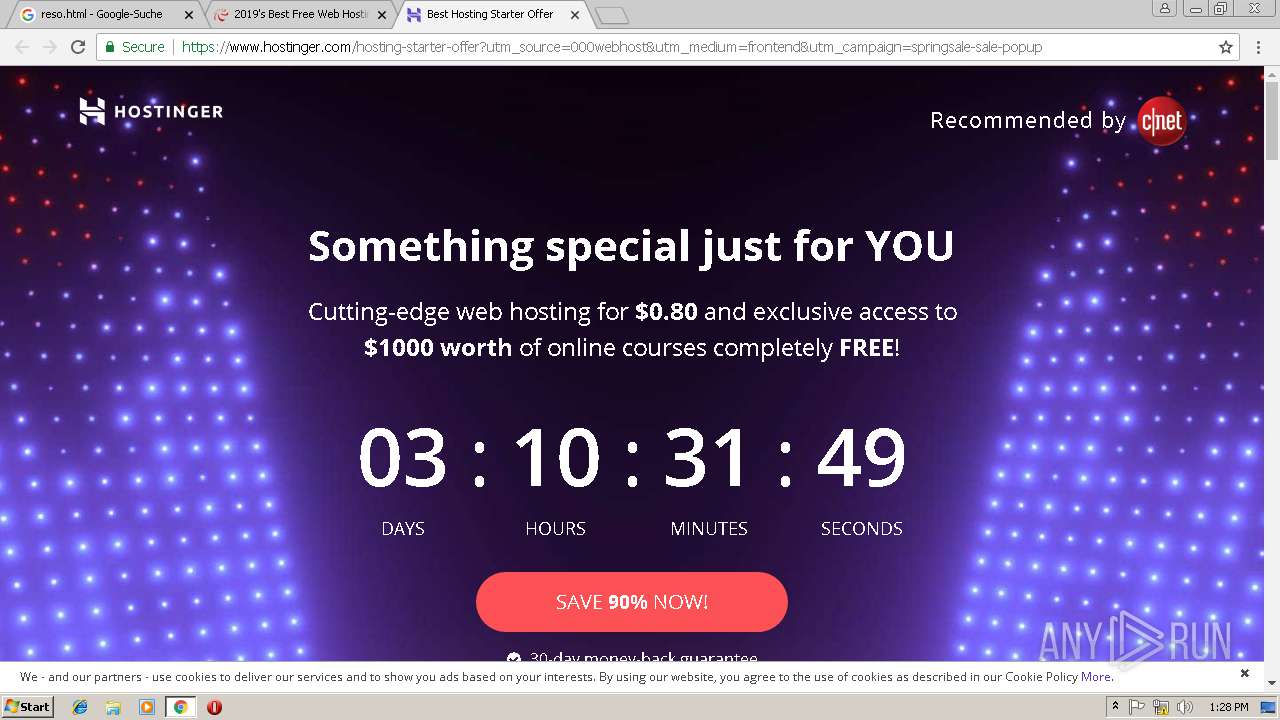
| Title: | Error 404 (Not Found) | 000webhost |
Total processes
50
Monitored processes
17
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=860,14132593805774996108,16649584940360337039,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=252E1D03321C9B36C5A351F482BBA696 --mojo-platform-channel-handle=960 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
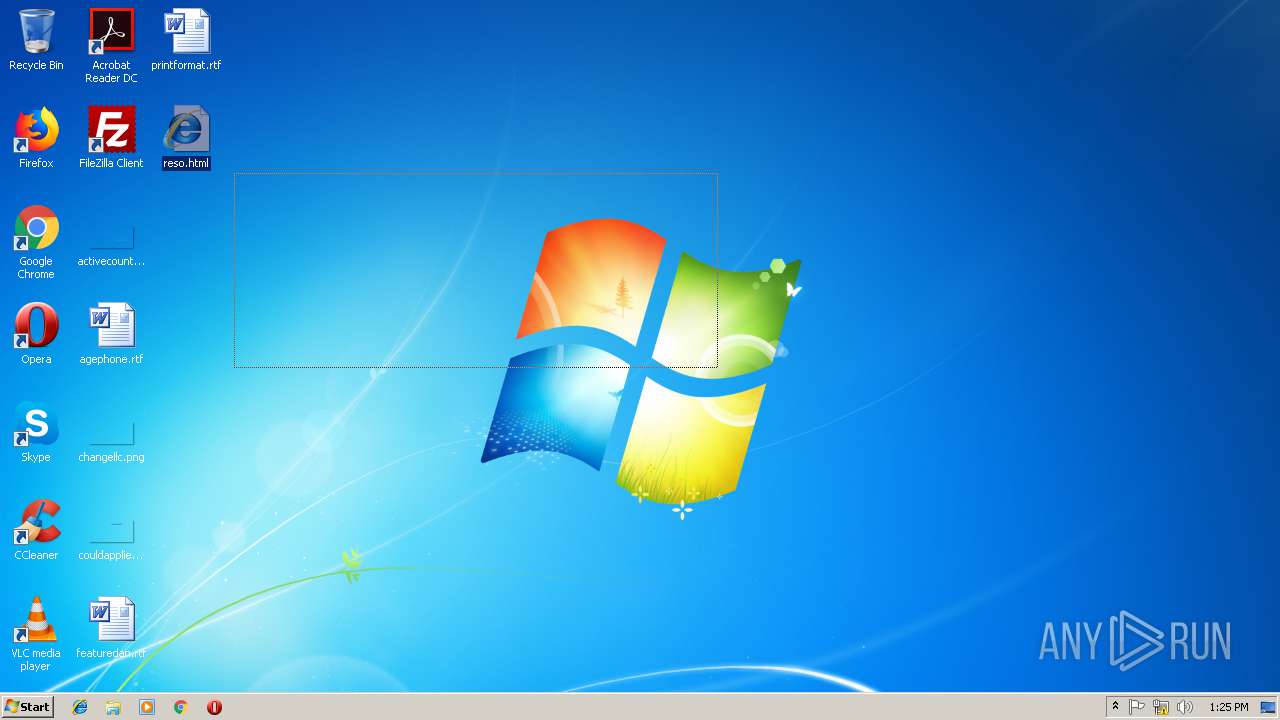
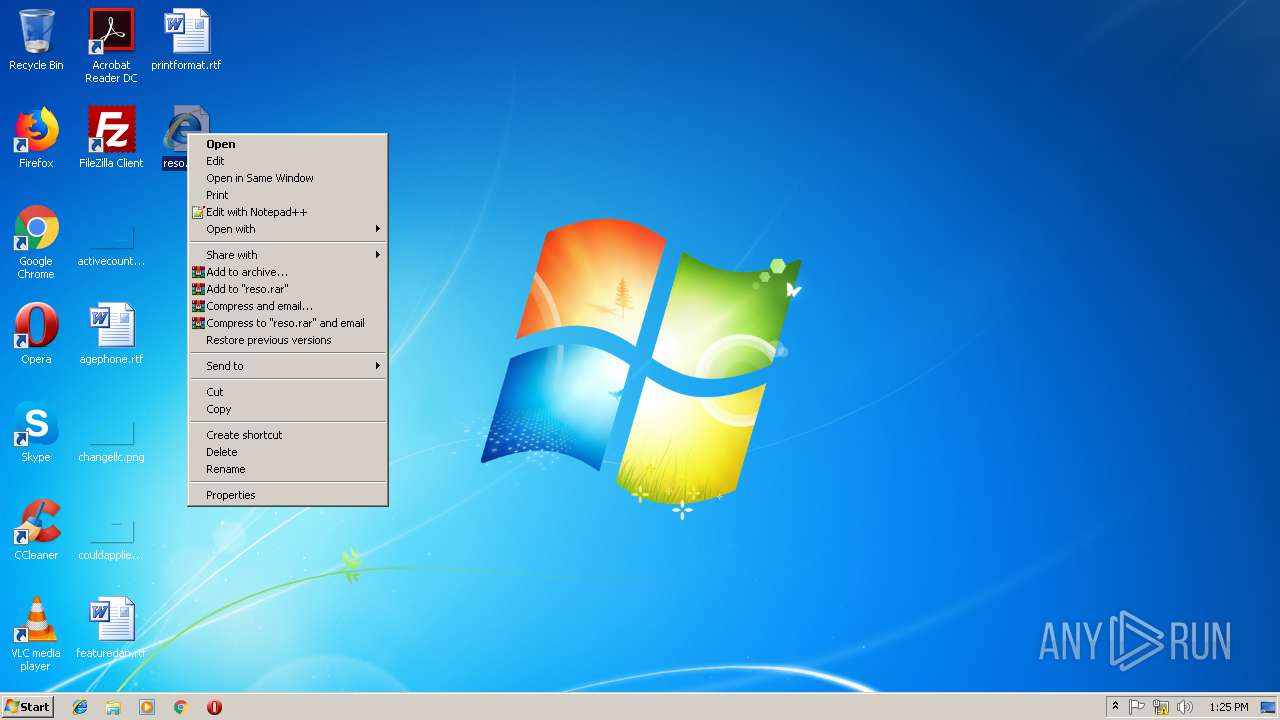
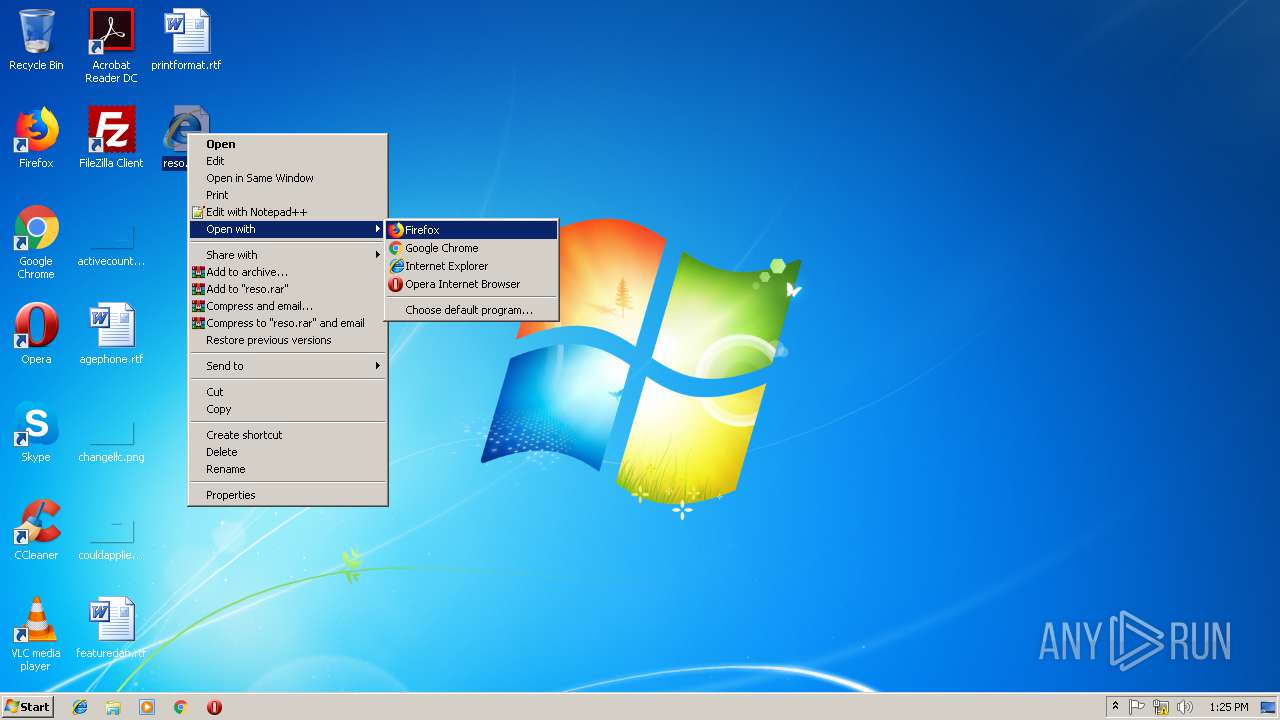
| 1488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" -- "C:\Users\admin\Desktop\reso.html" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1736 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\Desktop\reso.html | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=860,14132593805774996108,16649584940360337039,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=08A98D03D1BA9CD575956F0DD37D1685 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=08A98D03D1BA9CD575956F0DD37D1685 --renderer-client-id=8 --mojo-platform-channel-handle=1028 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2412 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6f8a00b0,0x6f8a00c0,0x6f8a00cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2440 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1736 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
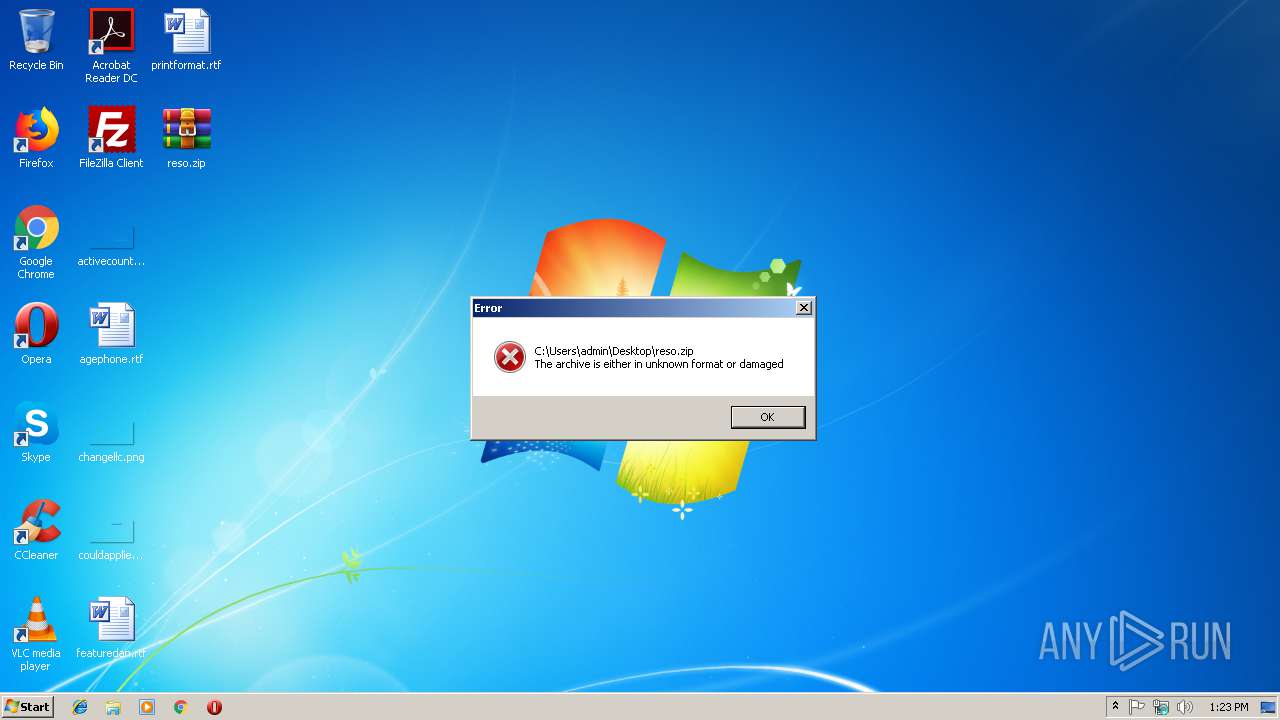
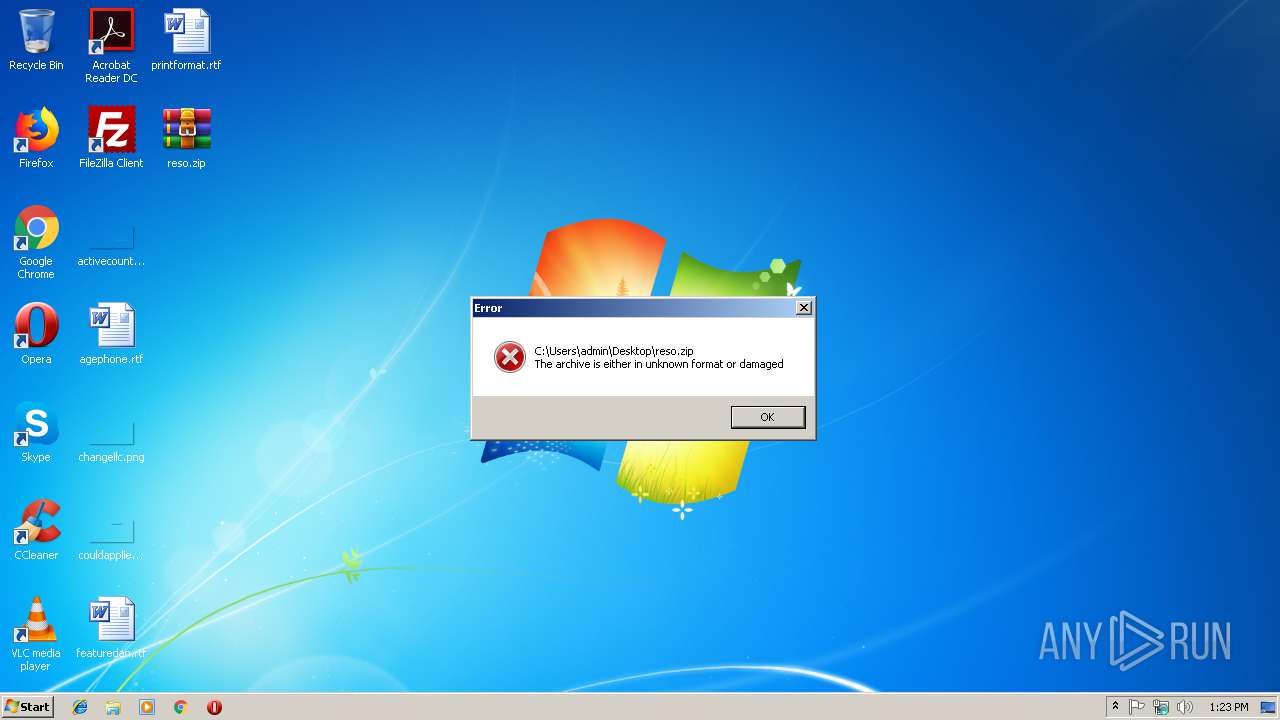
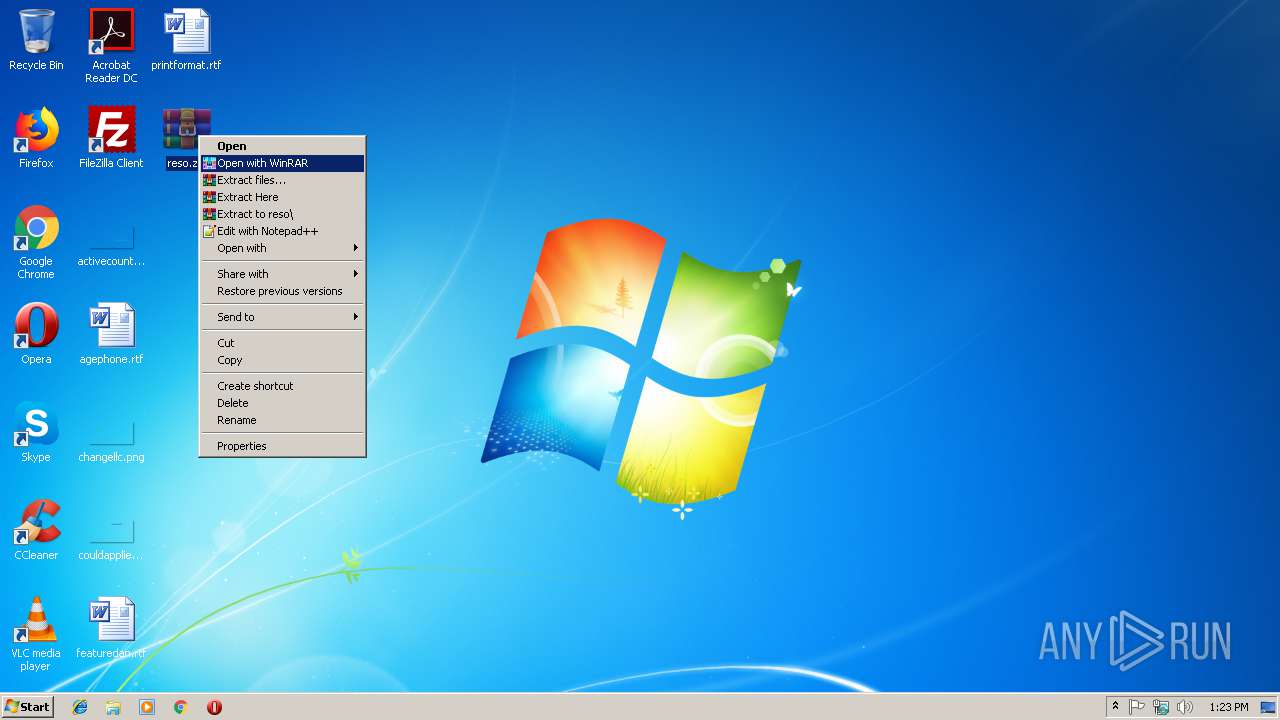
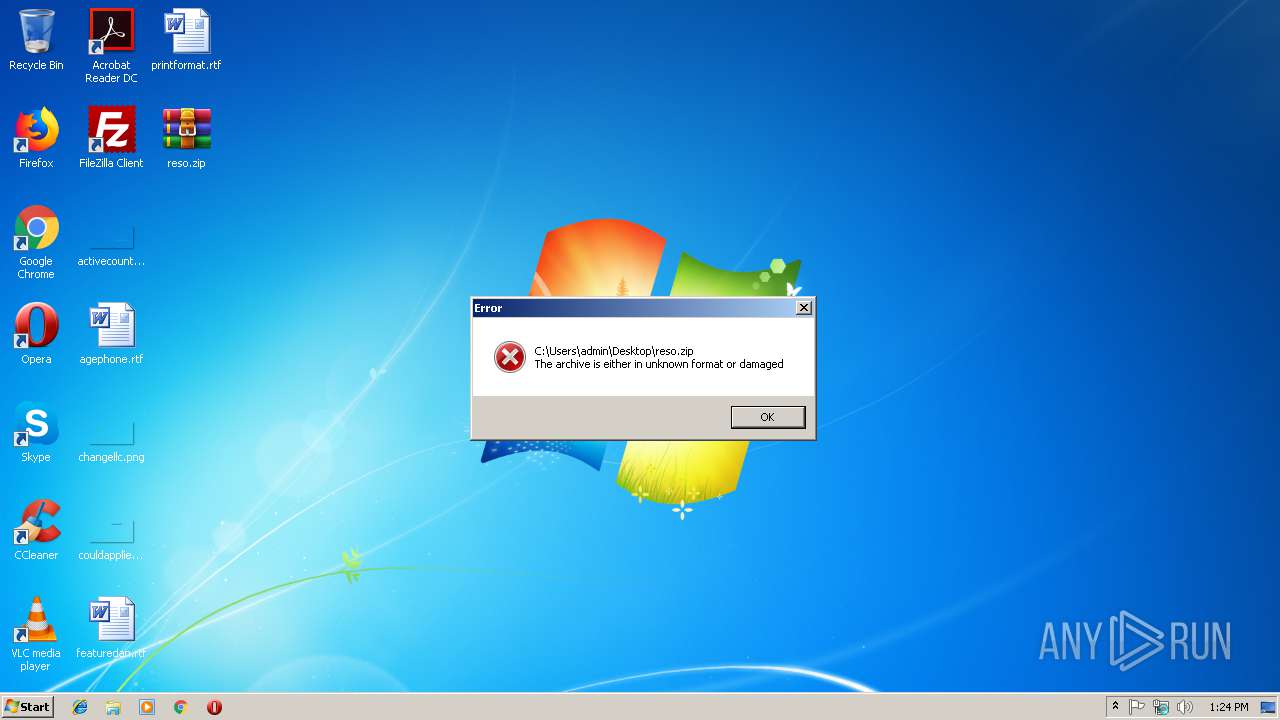
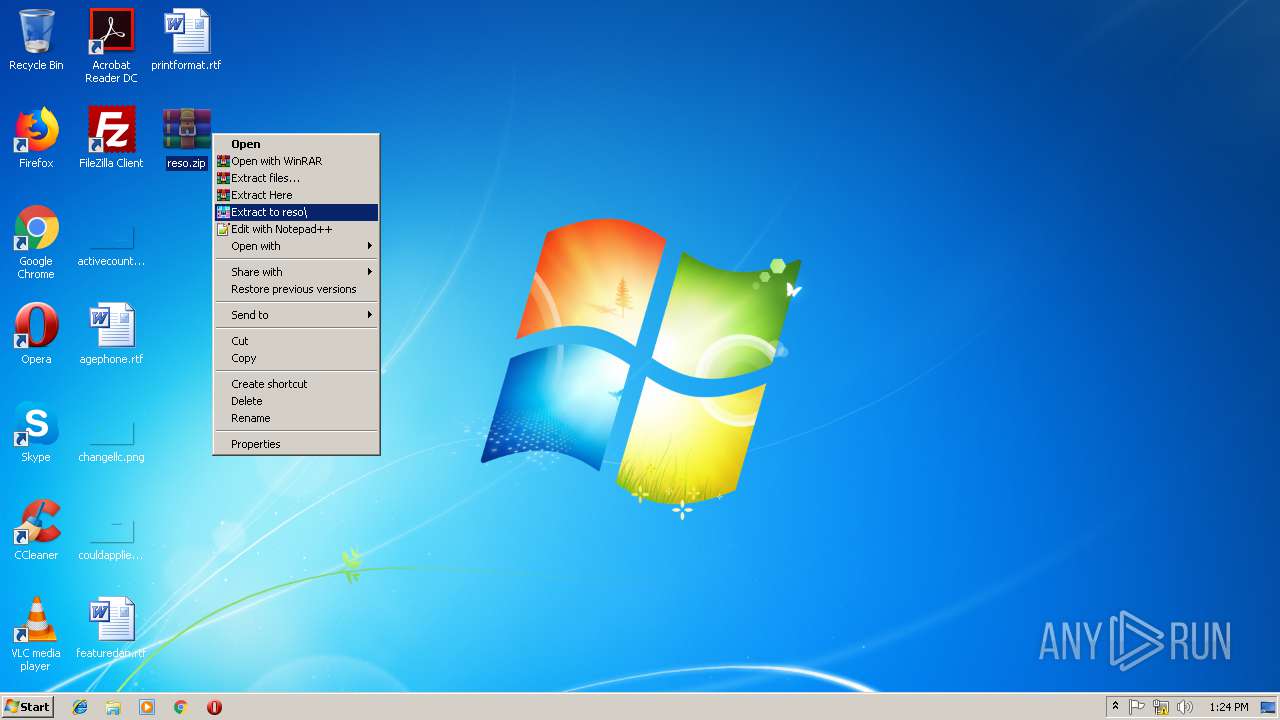
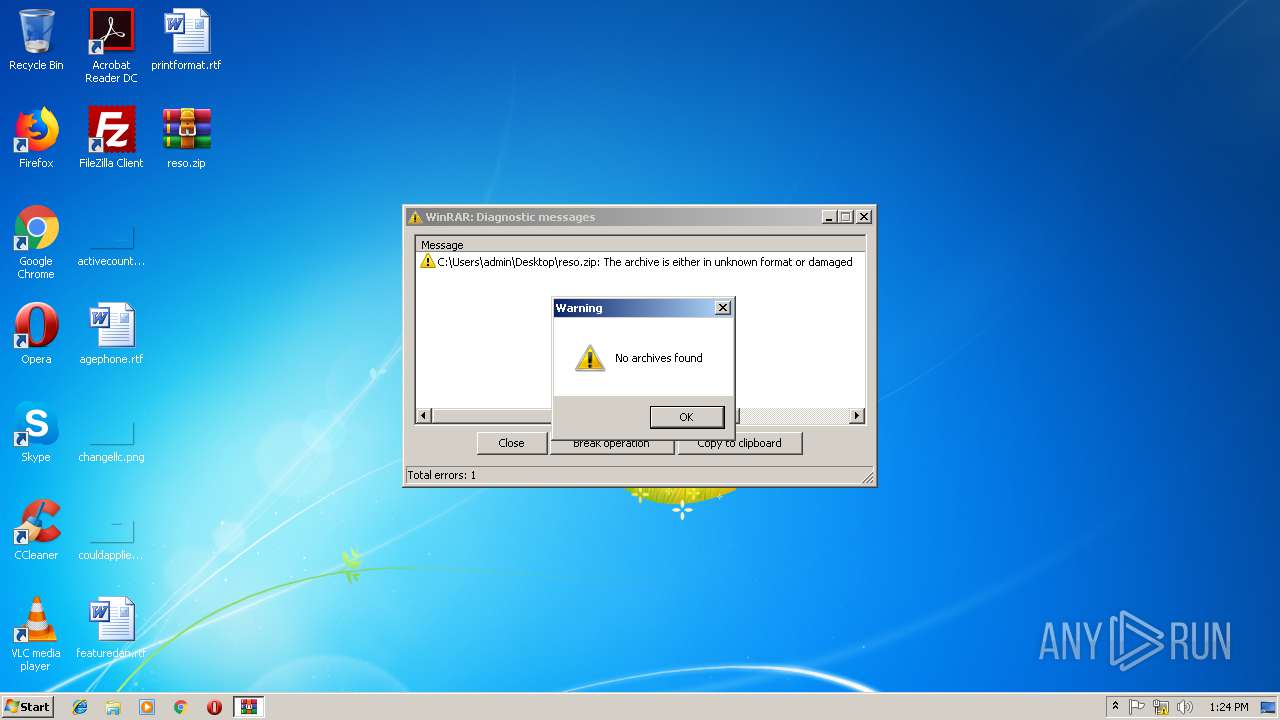
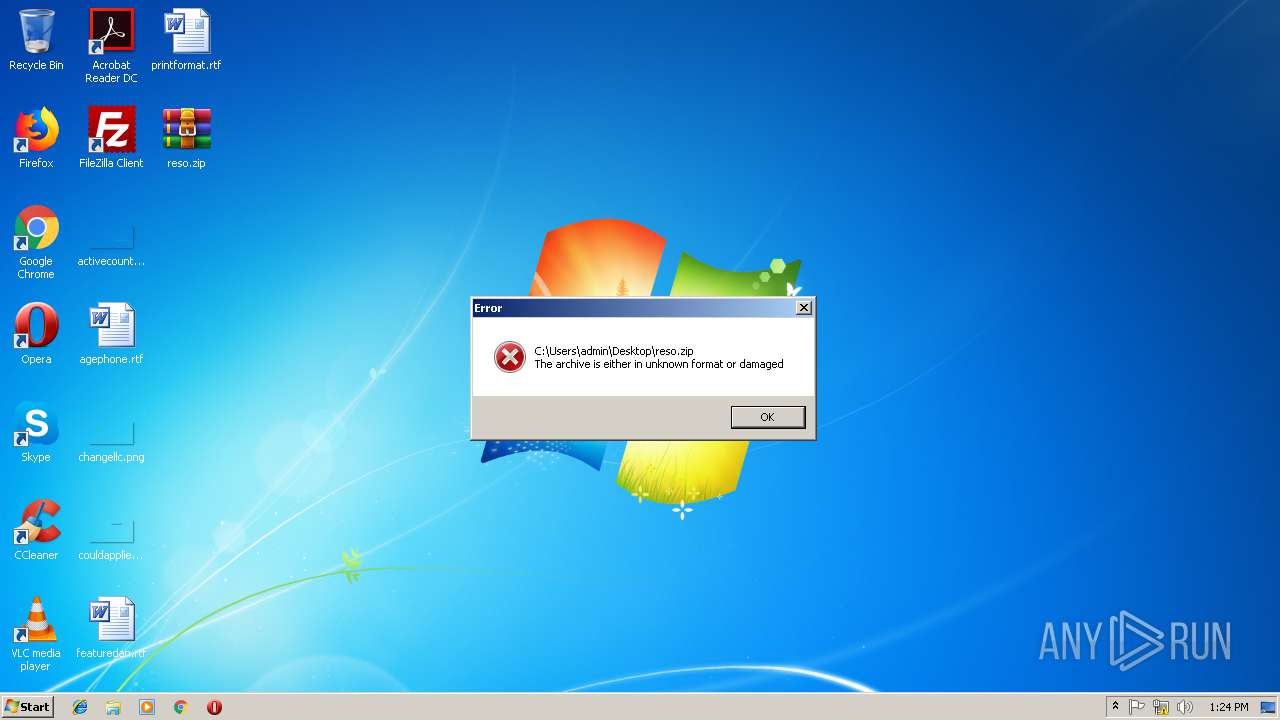
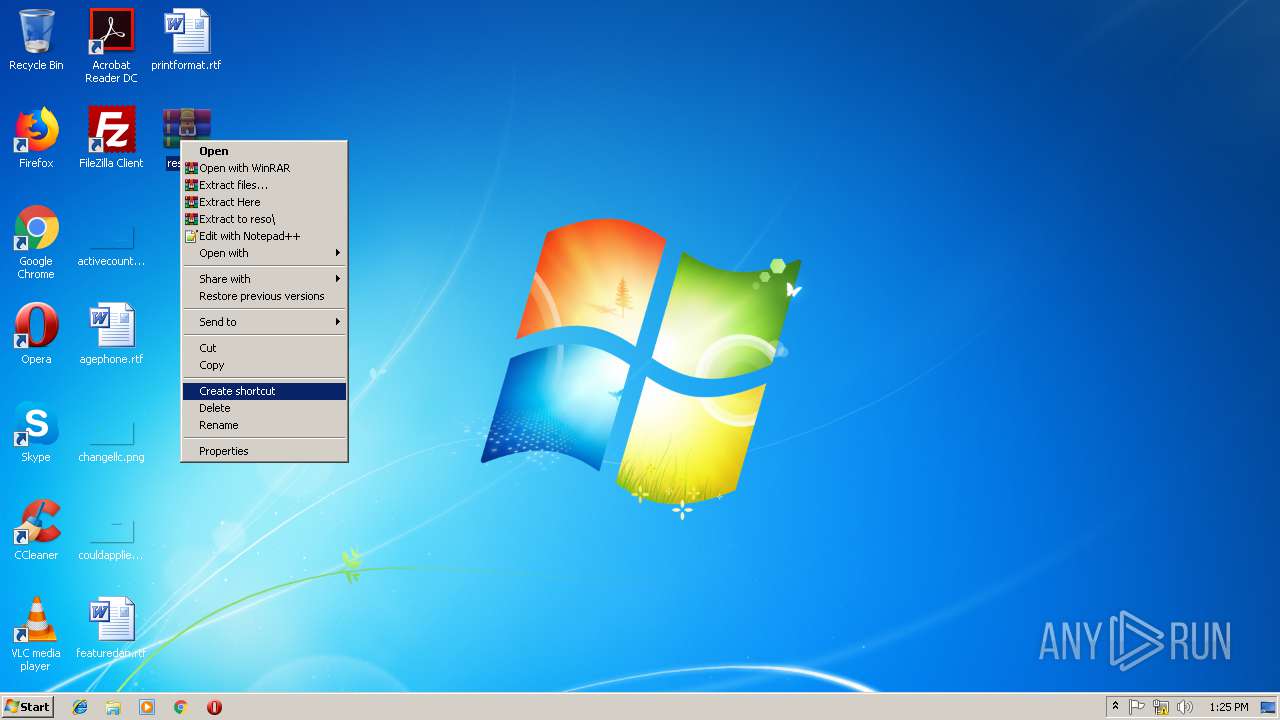
| 2892 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\reso.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 1 Version: 5.60.0 Modules
| |||||||||||||||
| 3076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=860,14132593805774996108,16649584940360337039,131072 --enable-features=PasswordImport --service-pipe-token=62166AA52740B5A1E4FC915C7EA22A32 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=62166AA52740B5A1E4FC915C7EA22A32 --renderer-client-id=4 --mojo-platform-channel-handle=1896 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3096 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\reso.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 1 Version: 5.60.0 Modules
| |||||||||||||||
| 3232 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=860,14132593805774996108,16649584940360337039,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9652A7256806062DD46567416B1E33D2 --mojo-platform-channel-handle=524 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
2 190
Read events
2 023
Write events
163
Delete events
4
Modification events
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\Desktop | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General\Toolbar\Layout |
| Operation: | write | Name: | Band56_0 |
Value: 38000000730100000402000000000000D4D0C800000000000000000000000000300102000000000039000000B40200000000000001000000 | |||
| (PID) Process: | (2892) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General\Toolbar\Layout |
| Operation: | write | Name: | Band56_1 |
Value: 38000000730100000500000000000000D4D0C8000000000000000000000000003201010000000000160000002A0000000000000002000000 | |||
Executable files
0
Suspicious files
43
Text files
108
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1736 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 1736 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 1736 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF609B097631D17A03.TMP | — | |
MD5:— | SHA256:— | |||
| 1736 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF235EC174B8191869.TMP | — | |
MD5:— | SHA256:— | |||
| 1736 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFC6780841DF0A621A.TMP | — | |
MD5:— | SHA256:— | |||
| 1736 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{A4B898D0-465C-11E9-AA93-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 1736 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF9B8CBA039ABE4A19.TMP | — | |
MD5:— | SHA256:— | |||
| 1736 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{A4B898CF-465C-11E9-AA93-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 1488 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e96107d9-437d-4e54-9c02-3e4a0d7679ed.tmp | — | |
MD5:— | SHA256:— | |||
| 1488 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
61
DNS requests
52
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
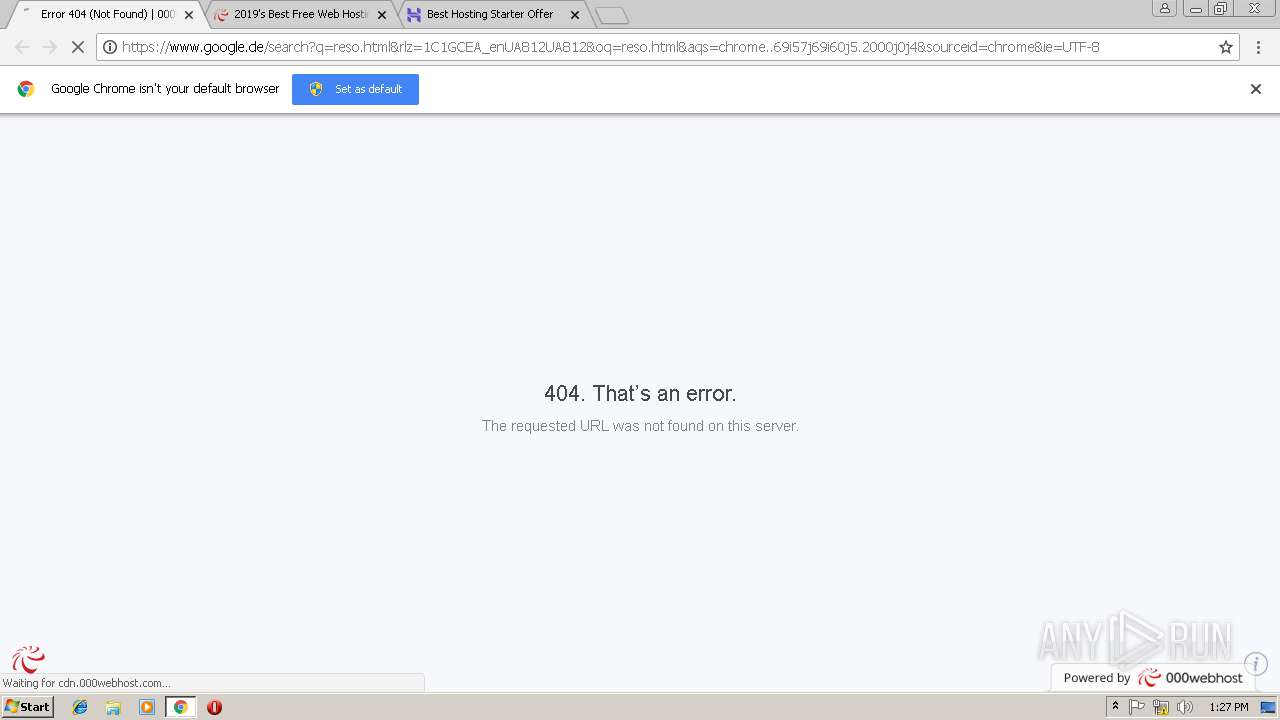
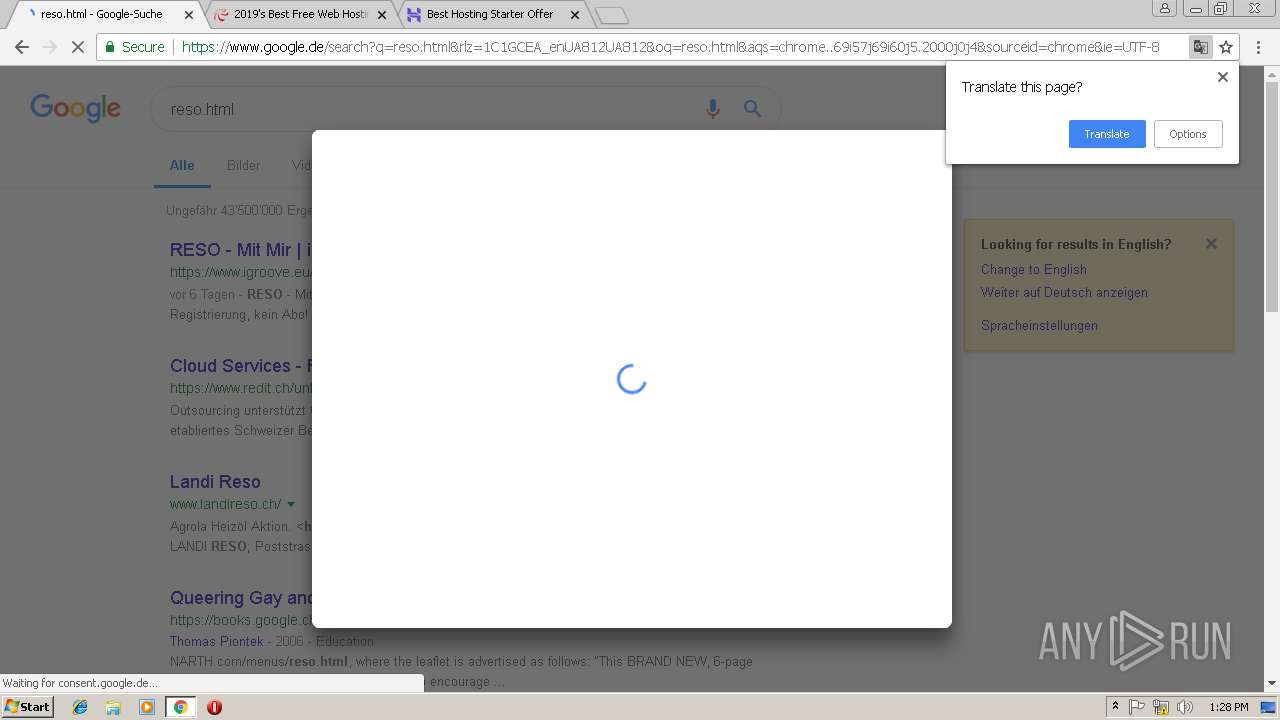
1488 | chrome.exe | GET | 204 | 216.58.208.35:80 | http://www.gstatic.com/generate_204 | US | — | — | whitelisted |
1488 | chrome.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.2 Kb | whitelisted |
1736 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
1488 | chrome.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/DF3C24F9BFD666761B268073FE06D1CC8D4F82A4.crt | US | der | 914 b | whitelisted |
1488 | chrome.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/47BEABC922EAE80E78783462A79F45C254FDE68B.crt | US | der | 969 b | whitelisted |
1488 | chrome.exe | GET | 200 | 13.35.254.34:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1488 | chrome.exe | 93.184.221.240:80 | www.download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1488 | chrome.exe | 172.217.18.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1488 | chrome.exe | 172.217.22.10:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
1488 | chrome.exe | 172.217.21.228:443 | www.google.com | Google Inc. | US | whitelisted |
1488 | chrome.exe | 172.217.18.174:443 | apis.google.com | Google Inc. | US | whitelisted |
1488 | chrome.exe | 104.27.175.49:443 | instant.page | Cloudflare Inc | US | shared |
1488 | chrome.exe | 31.13.90.6:443 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
1488 | chrome.exe | 216.58.205.232:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
1736 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
1488 | chrome.exe | 216.58.208.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
cdn.000webhost.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
accounts.google.com |
| shared |
a.optnmstr.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
api.optmnstr.com |
| unknown |
www.download.windowsupdate.com |
| whitelisted |
www.000webhost.com |
| shared |