| File name: | webex (1).exe |
| Full analysis: | https://app.any.run/tasks/281542b4-9de2-4911-b629-bcf152e9ada5 |
| Verdict: | Malicious activity |
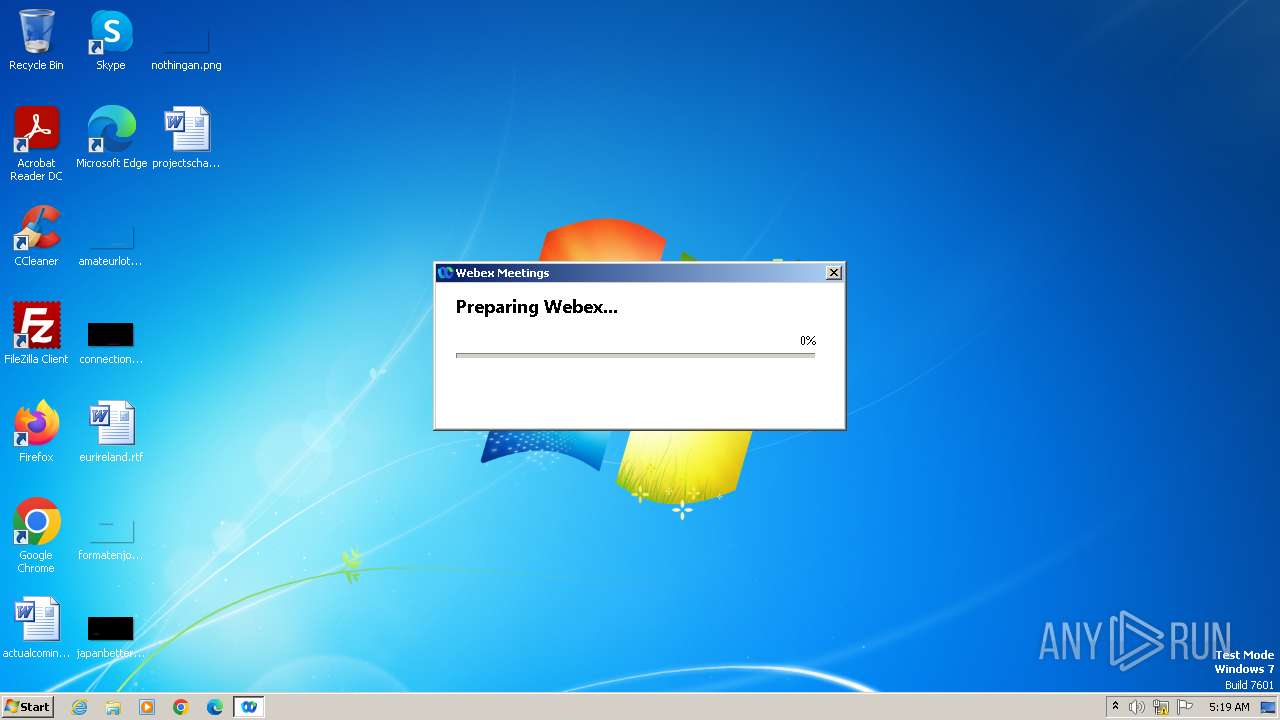
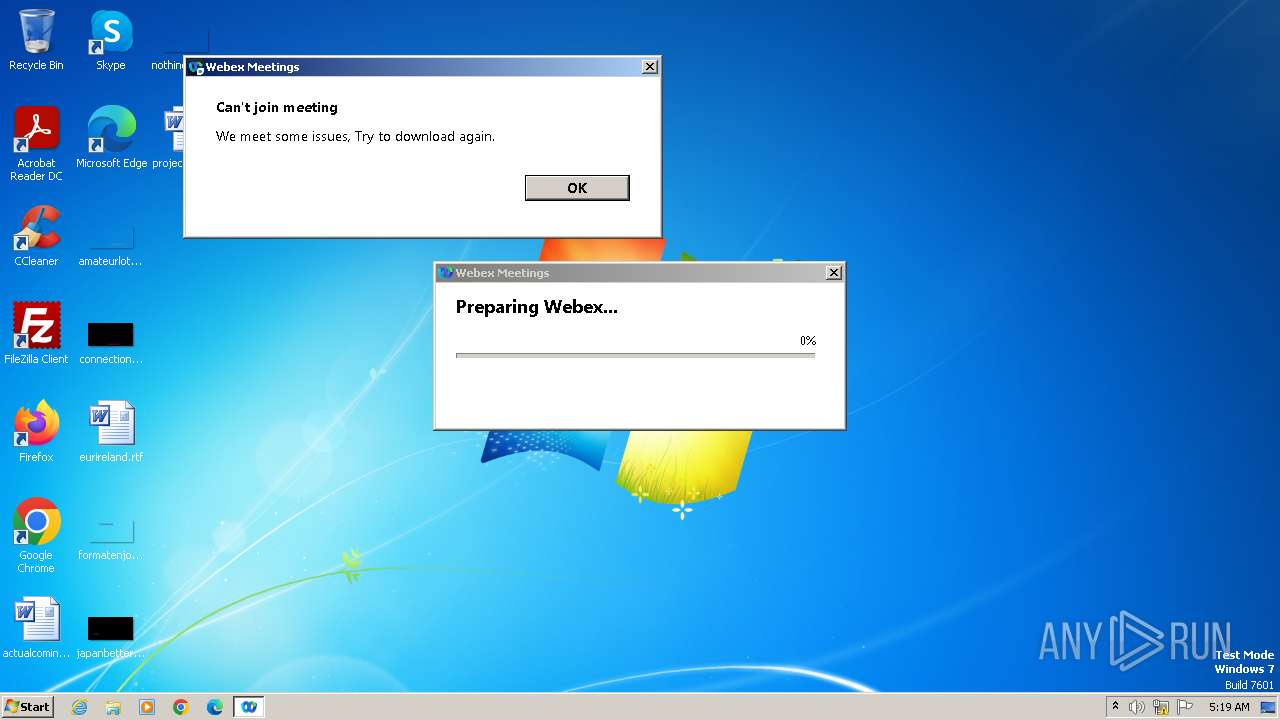
| Analysis date: | November 18, 2023, 05:19:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B749218878399A03955EE6BCE9147993 |
| SHA1: | B9E4773B263AAF3C99373CD8BBB1658DA0B62E2F |
| SHA256: | 6267E1F536CDE94E5657DD74C1A07C9A2D78EC434F95EE5EC20AED5BAB429DE8 |
| SSDEEP: | 12288:beSHl8p5O8XwE5RkDmYanznVzRnVzh0Fja:beSHl8poAwiumVrS2 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads settings of System Certificates
- webex (1).exe (PID: 3428)
Reads security settings of Internet Explorer
- webex (1).exe (PID: 3428)
Checks Windows Trust Settings
- webex (1).exe (PID: 3428)
Reads the Internet Settings
- webex (1).exe (PID: 3428)
INFO
Checks proxy server information
- webex (1).exe (PID: 3428)
Checks supported languages
- webex (1).exe (PID: 3428)
- wmpnscfg.exe (PID: 3468)
Reads the computer name
- webex (1).exe (PID: 3428)
- wmpnscfg.exe (PID: 3468)
Reads the machine GUID from the registry
- webex (1).exe (PID: 3428)
- wmpnscfg.exe (PID: 3468)
Create files in a temporary directory
- webex (1).exe (PID: 3428)
Creates files or folders in the user directory
- webex (1).exe (PID: 3428)
Manual execution by a user
- wmpnscfg.exe (PID: 3468)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:09:26 09:03:18+02:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.28 |
| CodeSize: | 188416 |
| InitializedDataSize: | 294912 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x171b0 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 10043.10.2023.926 |
| ProductVersionNumber: | 10043.10.2023.926 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Cisco Webex LLC |
| FileDescription: | Cisco Webex Meeting |
| FileVersion: | 10043,10,2023,0926 |
| InternalName: | Webex |
| LegalCopyright: | © 2023 Cisco and/or its affiliates. All rights reserved. |
| OriginalFileName: | Webex.exe |
| ProductName: | Cisco Webex Meeting |
| ProductVersion: | 10043,10,2023,0926 |
| GPCVersion: | 3 |
| UrlProtocolVersion: | 1 |
Total processes
36
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3428 | "C:\Users\admin\AppData\Local\Temp\webex (1).exe" | C:\Users\admin\AppData\Local\Temp\webex (1).exe | explorer.exe | ||||||||||||
User: admin Company: Cisco Webex LLC Integrity Level: MEDIUM Description: Cisco Webex Meeting Exit code: 0 Version: 10043,10,2023,0926 Modules
| |||||||||||||||
| 3468 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
4 494
Read events
4 465
Write events
24
Delete events
5
Modification events
| (PID) Process: | (3428) webex (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3428) webex (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000059010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3428) webex (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3428) webex (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3428) webex (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3428) webex (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3428) webex (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3428) webex (1).exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3428) webex (1).exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17A\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3468) wmpnscfg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows Media Player NSS\3.0\Events\{81CD229C-547A-41DD-AD60-BEB17B702C31}\{03BA301B-659E-43B6-BFC3-03A08DE591CE} |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
0
Suspicious files
4
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3428 | webex (1).exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 3428 | webex (1).exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6CFED4E1A8866BE87BE17622BFB4D726_FBADB8F7FD7B56EE191ACF24A8989D94 | binary | |
MD5:6E3DF49EABC73FB66ACF82030EE3E32D | SHA256:41258F4DB52B67E4E33896C4453200AE7A861AB4C7A2FF6A17CBF1D077D95D66 | |||
| 3428 | webex (1).exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\ITK86ZM3.txt | text | |
MD5:2CA7B50A951283572C943627C2311A36 | SHA256:0160D87BE935C80FBD70E36BEB27927B1FB4CA9DB56C89209D65CE4A7B1BC2FD | |||
| 3428 | webex (1).exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:00C8930598719A44B41EB31C8F942567 | SHA256:ADD81C4E1D0742C215A25D9C6F875B4D7255CA12922DD334538E713E61836BE0 | |||
| 3428 | webex (1).exe | C:\Users\admin\AppData\Local\Temp\wbx_tfs_3428_38.txt | text | |
MD5:E9EEA0EFE02A9C53BB9BCA04261663EE | SHA256:F7D97DB0C2E575BCE6B8F7A52FD6724E9D33EAF99DCC0FD42712DE88CFCFDE73 | |||
| 3428 | webex (1).exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6CFED4E1A8866BE87BE17622BFB4D726_FBADB8F7FD7B56EE191ACF24A8989D94 | binary | |
MD5:1394F408108FB460A5AD438BC16E3568 | SHA256:4E661BCB361B9DA01D4064854DD0904FE6477943C0CA327C0E89238D81E2EAB1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
8
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3428 | webex (1).exe | GET | 200 | 192.35.177.23:80 | http://commercial.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTQfEOioPd4%2FtCA3%2FhgDklRXB0FwgQU7UQZwNPwBovupHu%2BQucmVMiONnYCEEABbvsKIFz66%2BGPcdc6u3g%3D | unknown | binary | 1.63 Kb | unknown |
3428 | webex (1).exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?329a857ab7c19b20 | unknown | compressed | 4.66 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3428 | webex (1).exe | 114.29.220.99:443 | mitwpu.webex.com | 13445 | SG | unknown |
3428 | webex (1).exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3428 | webex (1).exe | 192.35.177.23:80 | commercial.ocsp.identrust.com | SLC-IDENT-AS | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
mitwpu.webex.com |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
commercial.ocsp.identrust.com |
| whitelisted |