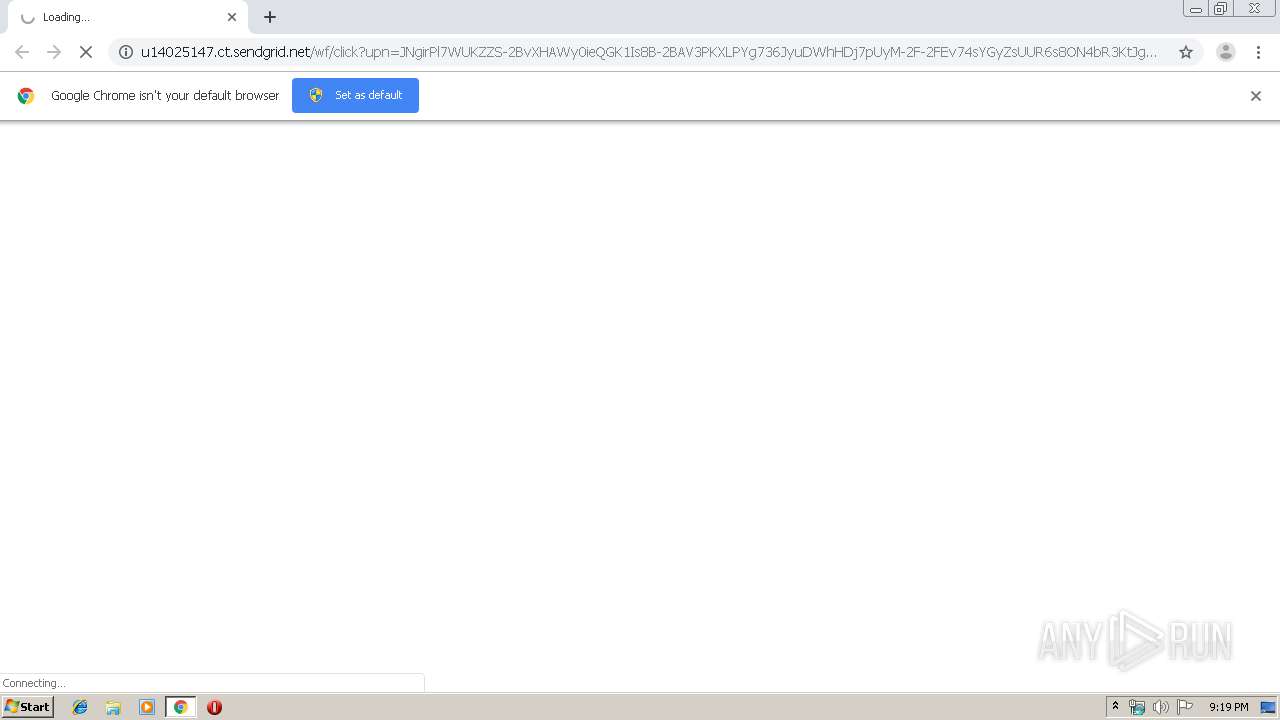
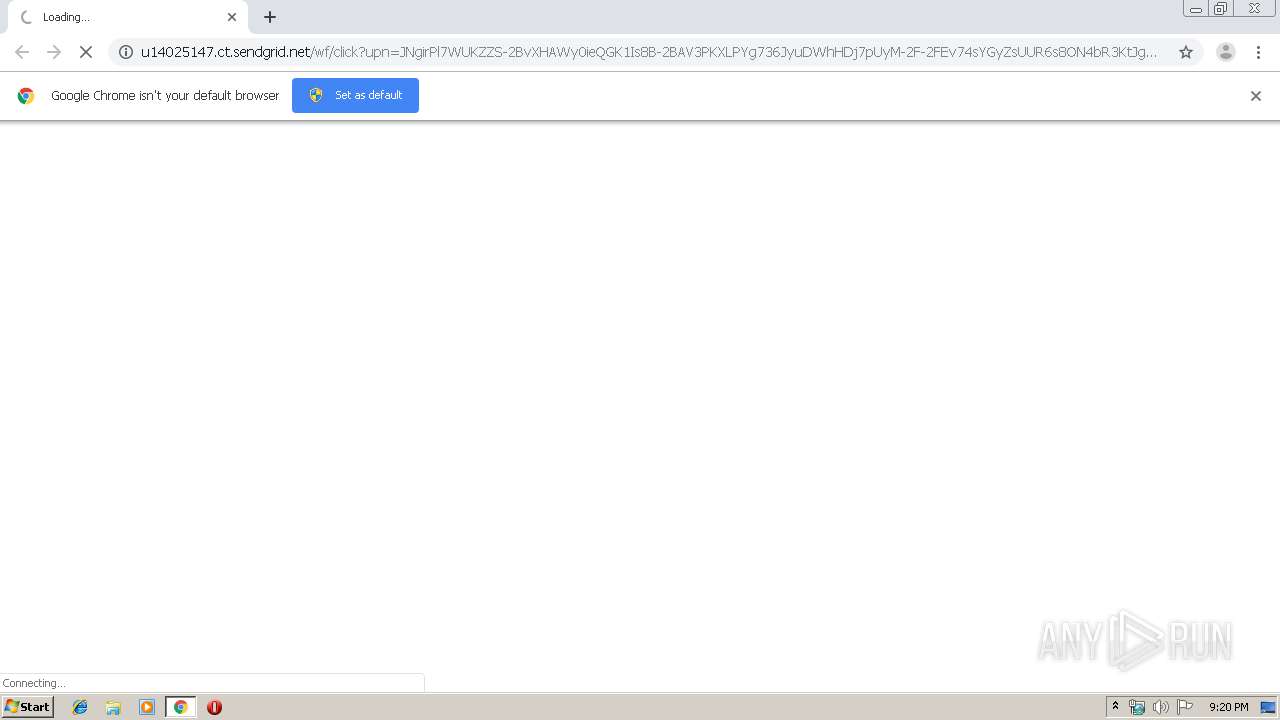
| URL: | http://u14025147.ct.sendgrid.net/wf/click?upn=JNgirPl7WUKZZS-2BvXHAWy0ieQGK1Is8B-2BAV3PKXLPYg736JyuDWhHDj7pUyM-2F-2FEv74sYGyZsUUR6s8ON4bR3KtJgXoCuvHFnV-2ByDeJCjhBxfb3D1Qrw85bsyRRZ-2Bweu9_-2BuyqbAT6LrWvGmCRH8NeQSaiePdTbjBgMBG9v4w7aI2Yt3a91U079vZtc4tpauTfeXxWXOFwasTFovw2BD5HNxqj13DTX6jwpGyPKIdu6bG-2FUy8qkTp-2FxMCfUvByAxm71SWZ1WsrkMN-2Bb7xya4KQ7ZR86zZ8KOpzGbClJOpbblJL888jBWk4FQokC3-2By5Ih9tHAE2T7zvpRvbR29JIMEjkiPf5J0RMkk-2Bl4-2Fq706B5WM4F6vgE2tUkZyWvP3wApiBgspZFnUKAAU0ShYUUuNATIbhkYM44LL4PJvFpuj6D89lDMb8smsBq549AbVmgiQHbEx1UO0HQGikaUnpTkfLJRSFd-2B-2B8rS1KnYK0wlKwLu5rxFh9rRX8CuyPuLJvmeUcT7QhyYusPAx1g94UY5WYK6O0jFez2UGEy3wkcp4Y-2By0Uqv5dTNqj7RisrmtGq7I9JVjZU5NmnU1uQMudsuHGfWCgGKhNt3ybIZvy1oq-2BWCaoYigqRBJmufi7ioQerjcMHg9h7uC06TPC44jYHsgn3igA9obS0gtbZy6ymeHZhAF9JjXG4-2BqmAOKz4RdGicKVppoKISLoIzWklhVwve6K7grvfD8iUqs7X2kSLW-2BXTw-3D |
| Full analysis: | https://app.any.run/tasks/71badddf-3f8c-49ad-a491-e5cd312033b8 |
| Verdict: | Malicious activity |
| Analysis date: | December 02, 2019, 21:19:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 1C91EB50742BA8DA52A769F1AAAEC4F6 |
| SHA1: | 028CD66B87DEEC9BF1EE11CACF96FA59F7F88D10 |
| SHA256: | 625B45C16E582ED3C226640EB43E8E5E92E994D07DBDBBD1FCD7DE21F4E09EBD |
| SSDEEP: | 12:yDSziPx3WtoOJlcf5zDVEiRkKx1hgUkFHZmwWDk158coHtJgBCFhSDh8cpY:QTpU1M5zGkxeUa2Qb8coNGpKca |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 896)
INFO
Reads the hosts file
- chrome.exe (PID: 896)
- chrome.exe (PID: 4048)
Application launched itself
- chrome.exe (PID: 896)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
62
Monitored processes
28
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 460 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,12759159181383890708,13867502939497499811,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7436068988754147655 --mojo-platform-channel-handle=3740 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 896 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://u14025147.ct.sendgrid.net/wf/click?upn=JNgirPl7WUKZZS-2BvXHAWy0ieQGK1Is8B-2BAV3PKXLPYg736JyuDWhHDj7pUyM-2F-2FEv74sYGyZsUUR6s8ON4bR3KtJgXoCuvHFnV-2ByDeJCjhBxfb3D1Qrw85bsyRRZ-2Bweu9_-2BuyqbAT6LrWvGmCRH8NeQSaiePdTbjBgMBG9v4w7aI2Yt3a91U079vZtc4tpauTfeXxWXOFwasTFovw2BD5HNxqj13DTX6jwpGyPKIdu6bG-2FUy8qkTp-2FxMCfUvByAxm71SWZ1WsrkMN-2Bb7xya4KQ7ZR86zZ8KOpzGbClJOpbblJL888jBWk4FQokC3-2By5Ih9tHAE2T7zvpRvbR29JIMEjkiPf5J0RMkk-2Bl4-2Fq706B5WM4F6vgE2tUkZyWvP3wApiBgspZFnUKAAU0ShYUUuNATIbhkYM44LL4PJvFpuj6D89lDMb8smsBq549AbVmgiQHbEx1UO0HQGikaUnpTkfLJRSFd-2B-2B8rS1KnYK0wlKwLu5rxFh9rRX8CuyPuLJvmeUcT7QhyYusPAx1g94UY5WYK6O0jFez2UGEy3wkcp4Y-2By0Uqv5dTNqj7RisrmtGq7I9JVjZU5NmnU1uQMudsuHGfWCgGKhNt3ybIZvy1oq-2BWCaoYigqRBJmufi7ioQerjcMHg9h7uC06TPC44jYHsgn3igA9obS0gtbZy6ymeHZhAF9JjXG4-2BqmAOKz4RdGicKVppoKISLoIzWklhVwve6K7grvfD8iUqs7X2kSLW-2BXTw-3D" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,12759159181383890708,13867502939497499811,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4618325617733449578 --mojo-platform-channel-handle=3040 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1028 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,12759159181383890708,13867502939497499811,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13018628361634237425 --mojo-platform-channel-handle=3540 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1096 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1404 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1600 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,12759159181383890708,13867502939497499811,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6610284771654519721 --mojo-platform-channel-handle=4244 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,12759159181383890708,13867502939497499811,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9645392228999957527 --mojo-platform-channel-handle=1348 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1892 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,12759159181383890708,13867502939497499811,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8335086777228269500 --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3796 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1972 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=992,12759159181383890708,13867502939497499811,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12947508932614939898 --mojo-platform-channel-handle=4040 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2028 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=992,12759159181383890708,13867502939497499811,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4227890484004354380 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2248 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
637
Read events
520
Write events
111
Delete events
6
Modification events
| (PID) Process: | (896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 896-13219795185926875 |
Value: 259 | |||
| (PID) Process: | (896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (896) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 896-13219795185926875 |
Value: 259 | |||
Executable files
0
Suspicious files
10
Text files
284
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | — | |
MD5:— | SHA256:— | |||
| 896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF39c08b.TMP | — | |
MD5:— | SHA256:— | |||
| 896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\49542cf3-f736-49e6-9536-349d1ed0fcb4.tmp | — | |
MD5:— | SHA256:— | |||
| 896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 896 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF39bf62.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
24
DNS requests
15
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4048 | chrome.exe | GET | 302 | 167.89.115.54:80 | http://u14025147.ct.sendgrid.net/wf/click?upn=JNgirPl7WUKZZS-2BvXHAWy0ieQGK1Is8B-2BAV3PKXLPYg736JyuDWhHDj7pUyM-2F-2FEv74sYGyZsUUR6s8ON4bR3KtJgXoCuvHFnV-2ByDeJCjhBxfb3D1Qrw85bsyRRZ-2Bweu9_-2BuyqbAT6LrWvGmCRH8NeQSaiePdTbjBgMBG9v4w7aI2Yt3a91U079vZtc4tpauTfeXxWXOFwasTFovw2BD5HNxqj13DTX6jwpGyPKIdu6bG-2FUy8qkTp-2FxMCfUvByAxm71SWZ1WsrkMN-2Bb7xya4KQ7ZR86zZ8KOpzGbClJOpbblJL888jBWk4FQokC3-2By5Ih9tHAE2T7zvpRvbR29JIMEjkiPf5J0RMkk-2Bl4-2Fq706B5WM4F6vgE2tUkZyWvP3wApiBgspZFnUKAAU0ShYUUuNATIbhkYM44LL4PJvFpuj6D89lDMb8smsBq549AbVmgiQHbEx1UO0HQGikaUnpTkfLJRSFd-2B-2B8rS1KnYK0wlKwLu5rxFh9rRX8CuyPuLJvmeUcT7QhyYusPAx1g94UY5WYK6O0jFez2UGEy3wkcp4Y-2By0Uqv5dTNqj7RisrmtGq7I9JVjZU5NmnU1uQMudsuHGfWCgGKhNt3ybIZvy1oq-2BWCaoYigqRBJmufi7ioQerjcMHg9h7uC06TPC44jYHsgn3igA9obS0gtbZy6ymeHZhAF9JjXG4-2BqmAOKz4RdGicKVppoKISLoIzWklhVwve6K7grvfD8iUqs7X2kSLW-2BXTw-3D | US | — | — | suspicious |
4048 | chrome.exe | GET | 302 | 172.217.23.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 508 b | whitelisted |
4048 | chrome.exe | GET | 302 | 172.217.23.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 513 b | whitelisted |
4048 | chrome.exe | GET | 200 | 173.194.7.89:80 | http://r3---sn-p5qs7n7e.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=85.203.20.94&mm=28&mn=sn-p5qs7n7e&ms=nvh&mt=1575321569&mv=m&mvi=2&pl=25&shardbypass=yes | US | crx | 862 Kb | whitelisted |
4048 | chrome.exe | GET | 200 | 74.125.155.199:80 | http://r1---sn-p5qs7n7z.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=85.203.20.94&mm=28&mn=sn-p5qs7n7z&ms=nvh&mt=1575321569&mv=m&mvi=0&pl=25&shardbypass=yes | US | crx | 293 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4048 | chrome.exe | 172.217.18.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
4048 | chrome.exe | 167.89.115.54:80 | u14025147.ct.sendgrid.net | SendGrid, Inc. | US | suspicious |
4048 | chrome.exe | 172.217.22.100:443 | www.google.com | Google Inc. | US | whitelisted |
4048 | chrome.exe | 172.217.23.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
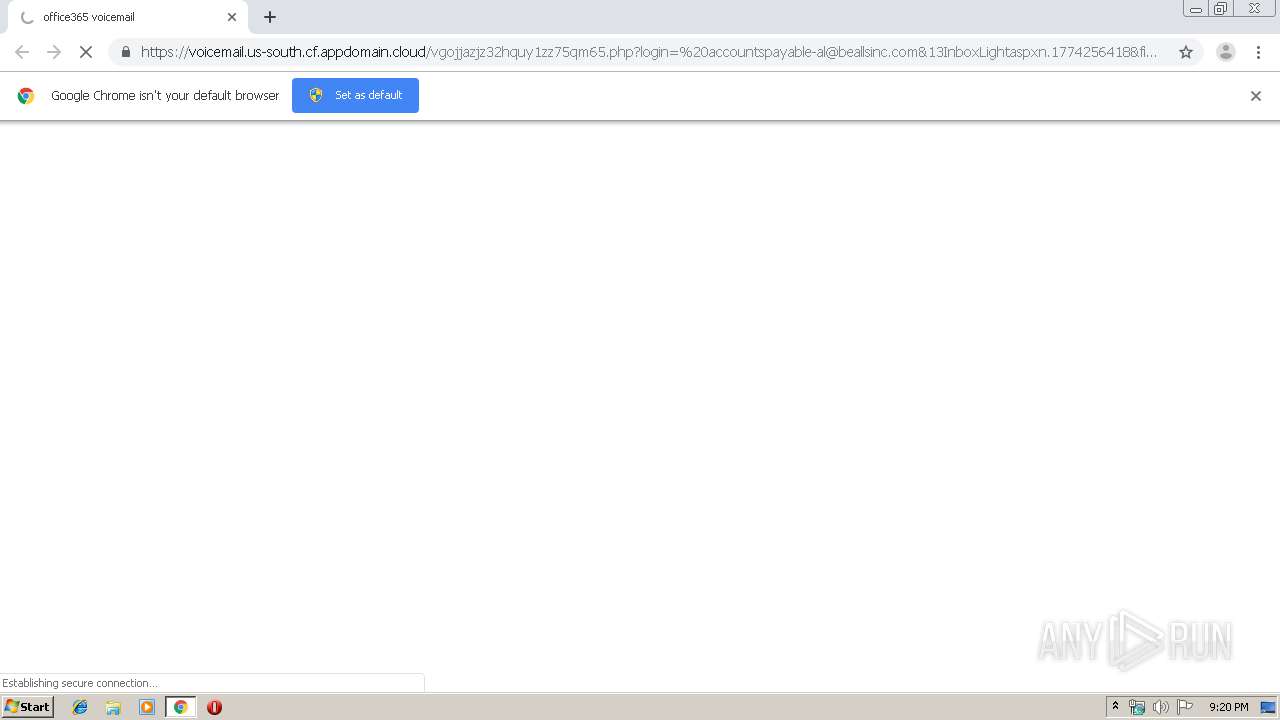
4048 | chrome.exe | 169.46.89.151:443 | voicemail.us-south.cf.appdomain.cloud | SoftLayer Technologies Inc. | US | suspicious |
4048 | chrome.exe | 216.58.210.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
4048 | chrome.exe | 169.62.254.80:443 | voicemail.us-south.cf.appdomain.cloud | — | US | suspicious |
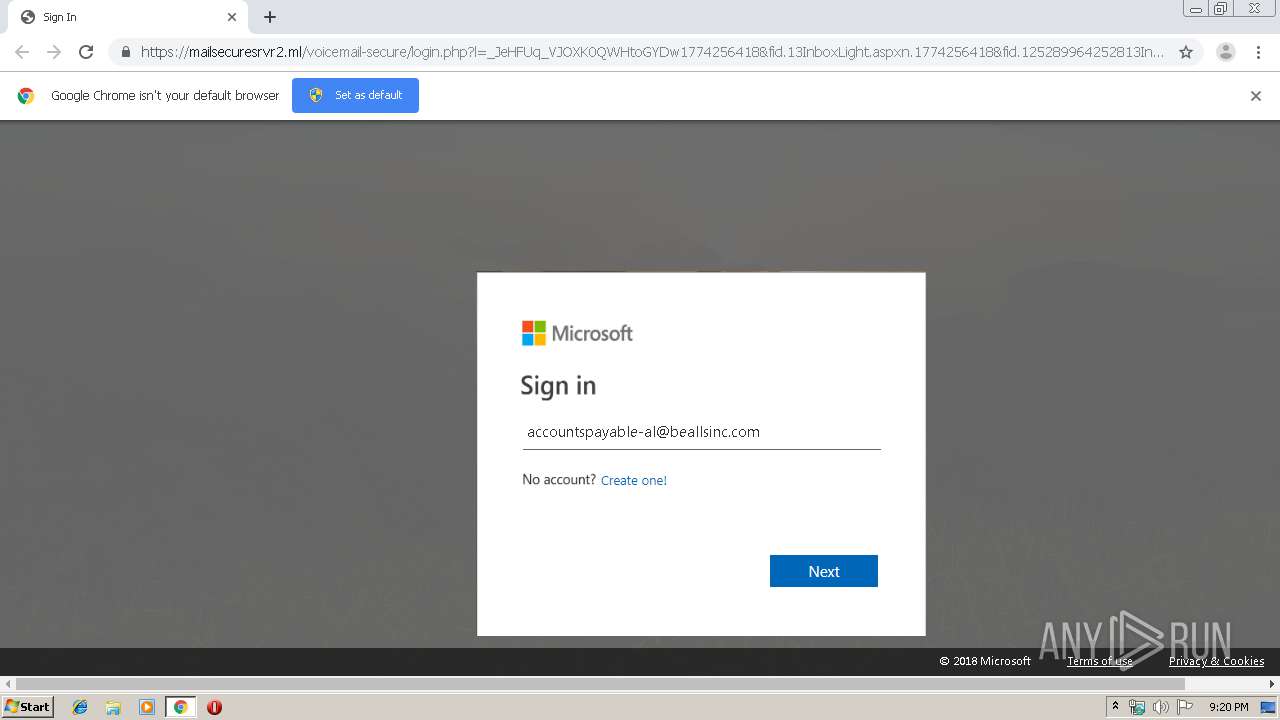
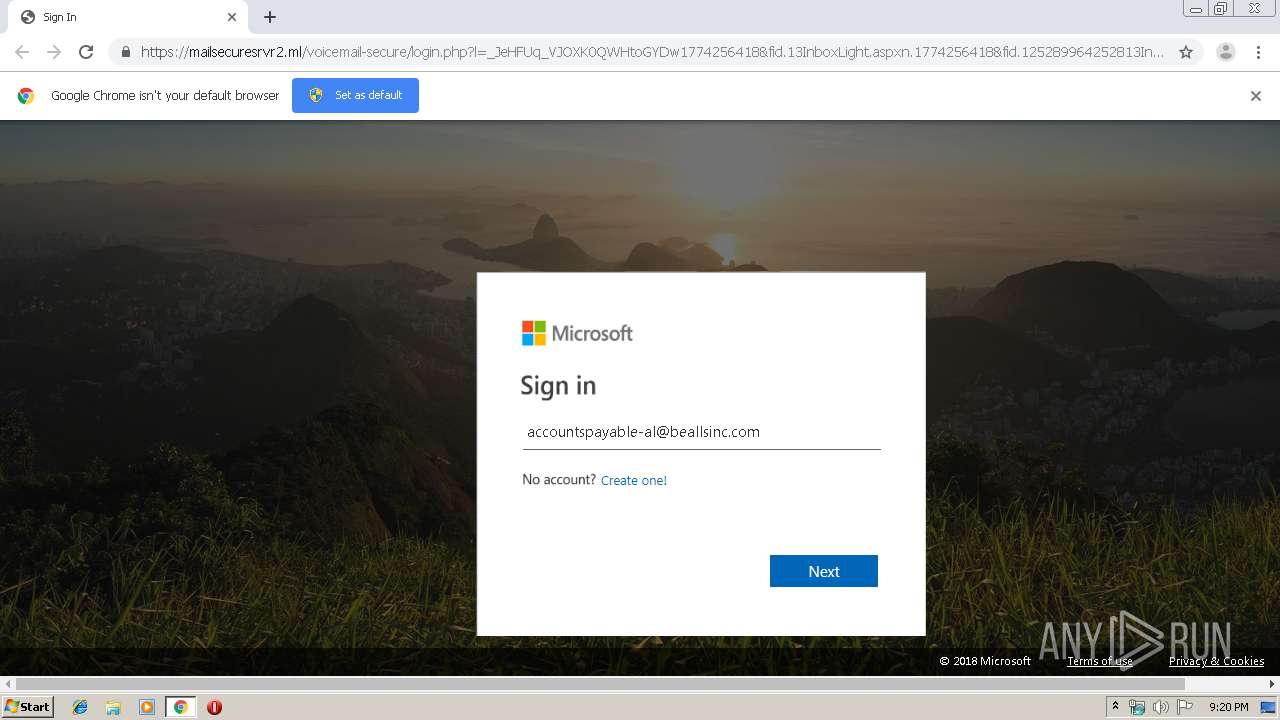
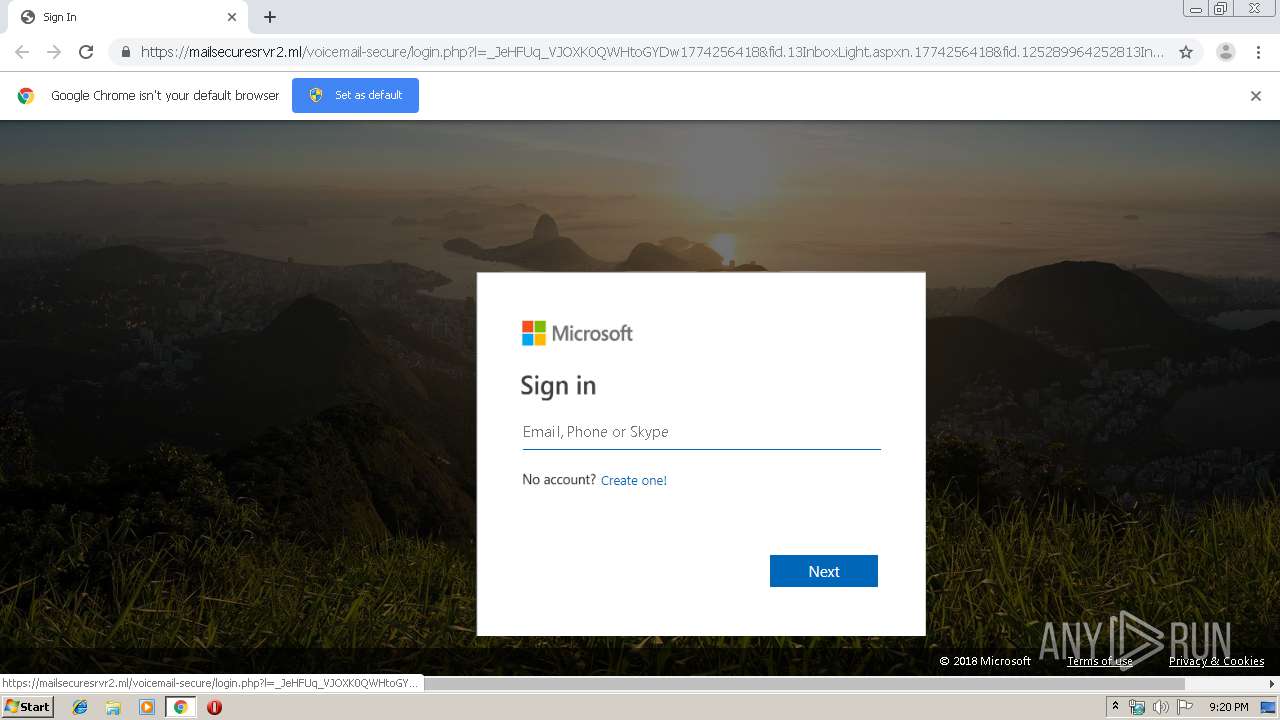
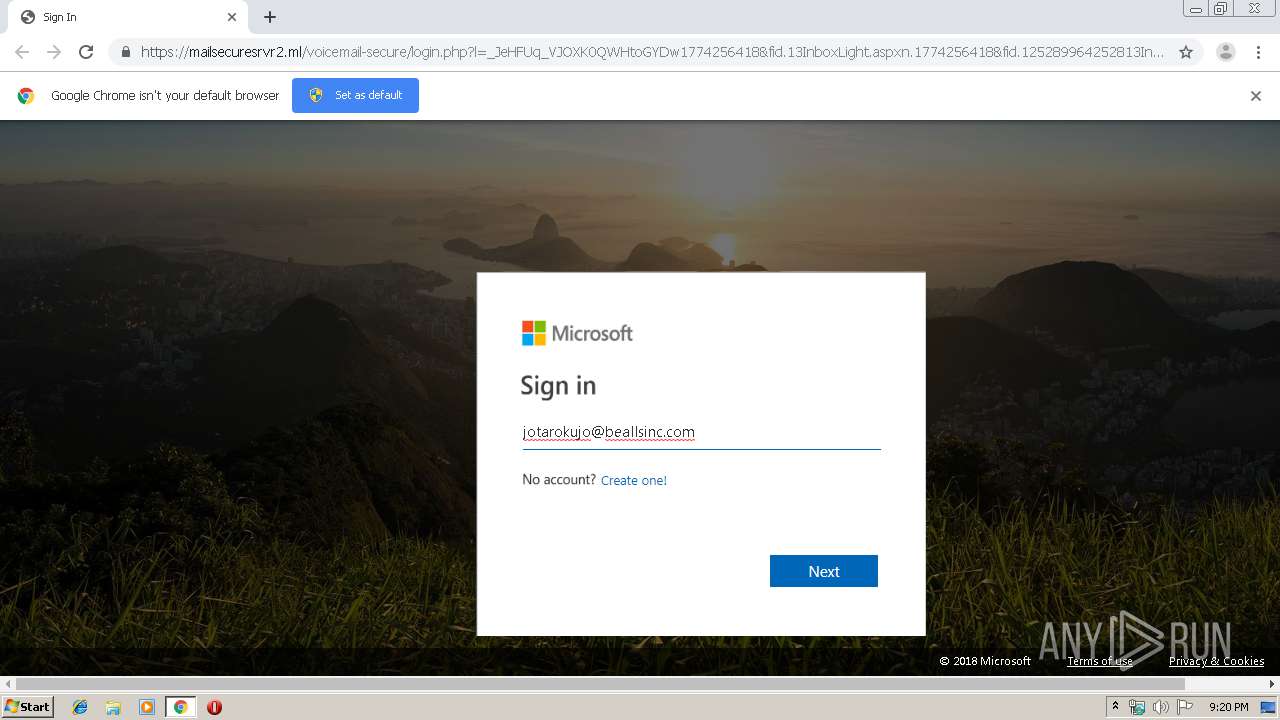
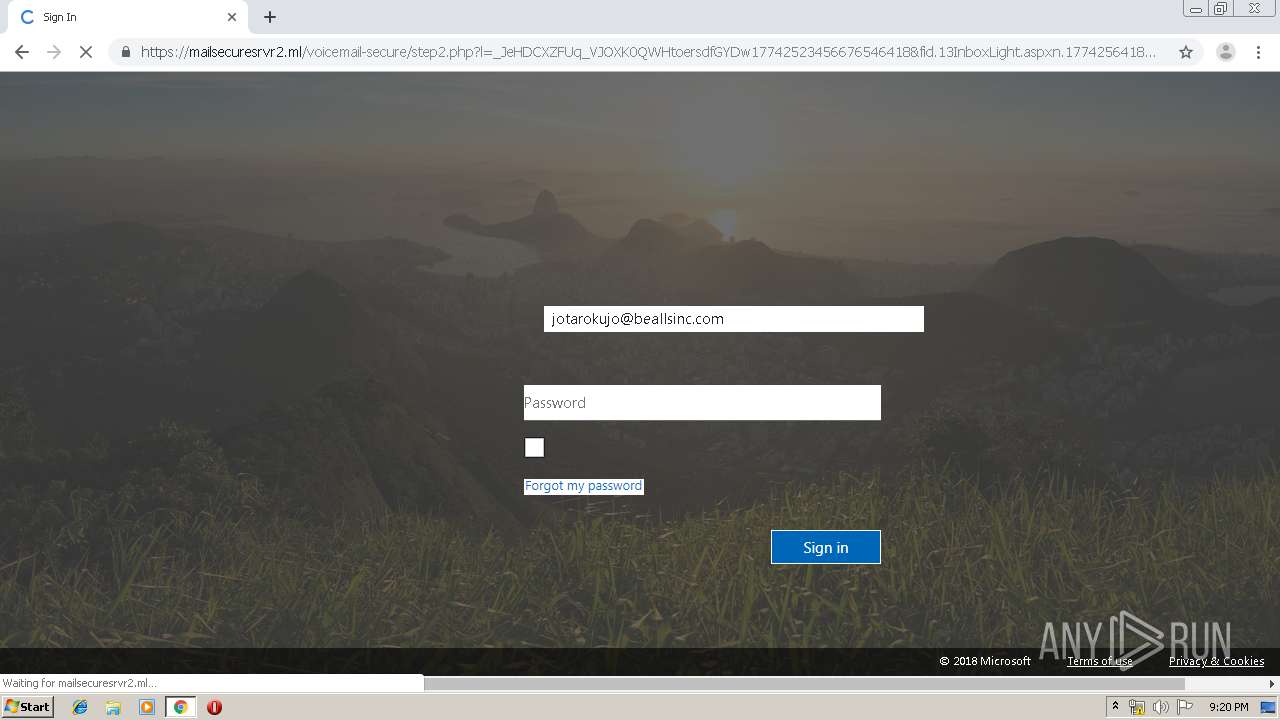
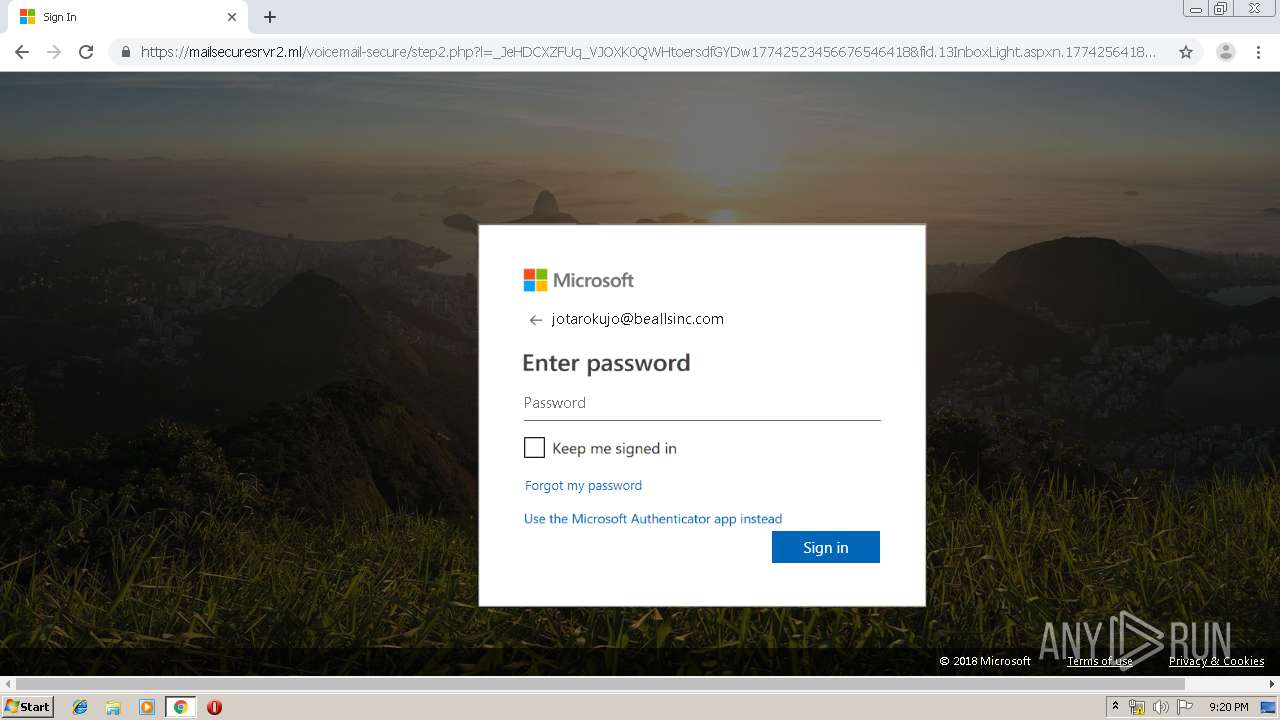
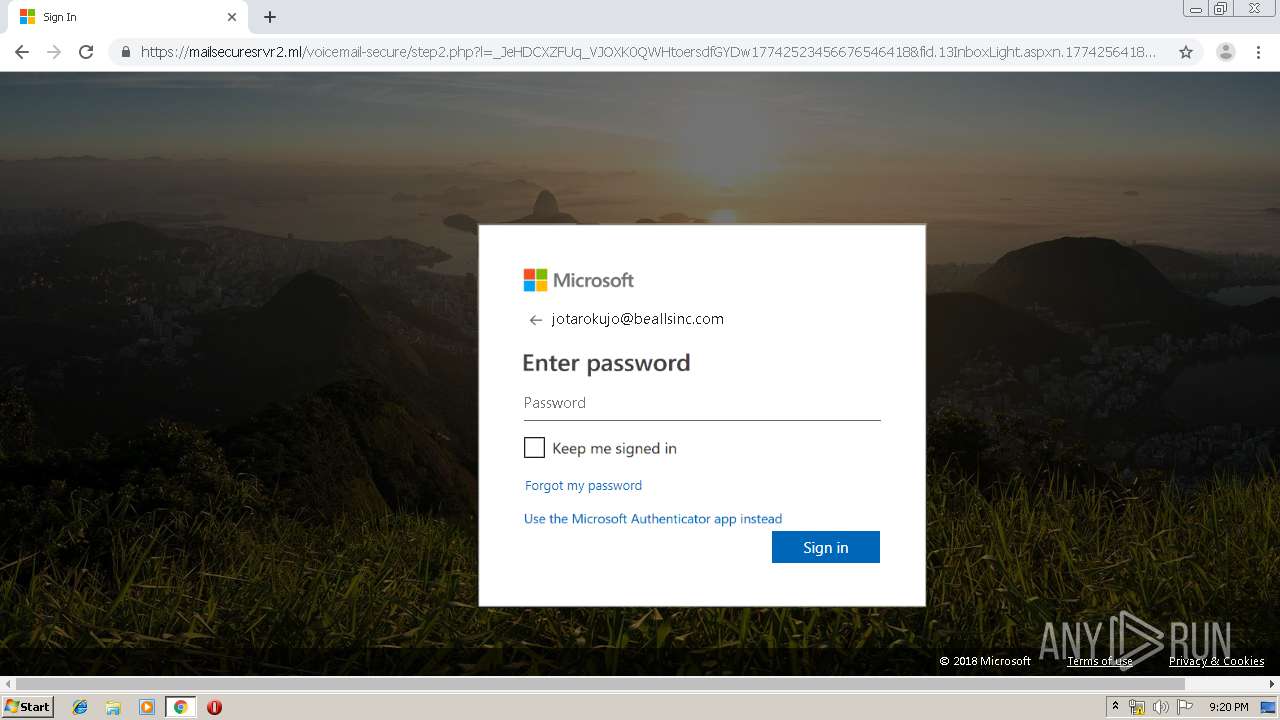
4048 | chrome.exe | 104.18.39.105:443 | mailsecuresrvr2.ml | Cloudflare Inc | US | suspicious |
4048 | chrome.exe | 172.217.21.238:443 | clients1.google.com | Google Inc. | US | whitelisted |
4048 | chrome.exe | 172.217.23.142:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
u14025147.ct.sendgrid.net |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
voicemail.us-south.cf.appdomain.cloud |
| suspicious |
ssl.gstatic.com |
| whitelisted |
mailsecuresrvr2.ml |
| suspicious |
clients1.google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .cloud TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO DNS Query for Suspicious .ml Domain |
4048 | chrome.exe | Potentially Bad Traffic | ET INFO Suspicious Domain (*.ml) in TLS SNI |