| File name: | BluetraitAgent381.msi |
| Full analysis: | https://app.any.run/tasks/66a67ccf-36bc-46d8-bff1-cb8305b94501 |
| Verdict: | Malicious activity |
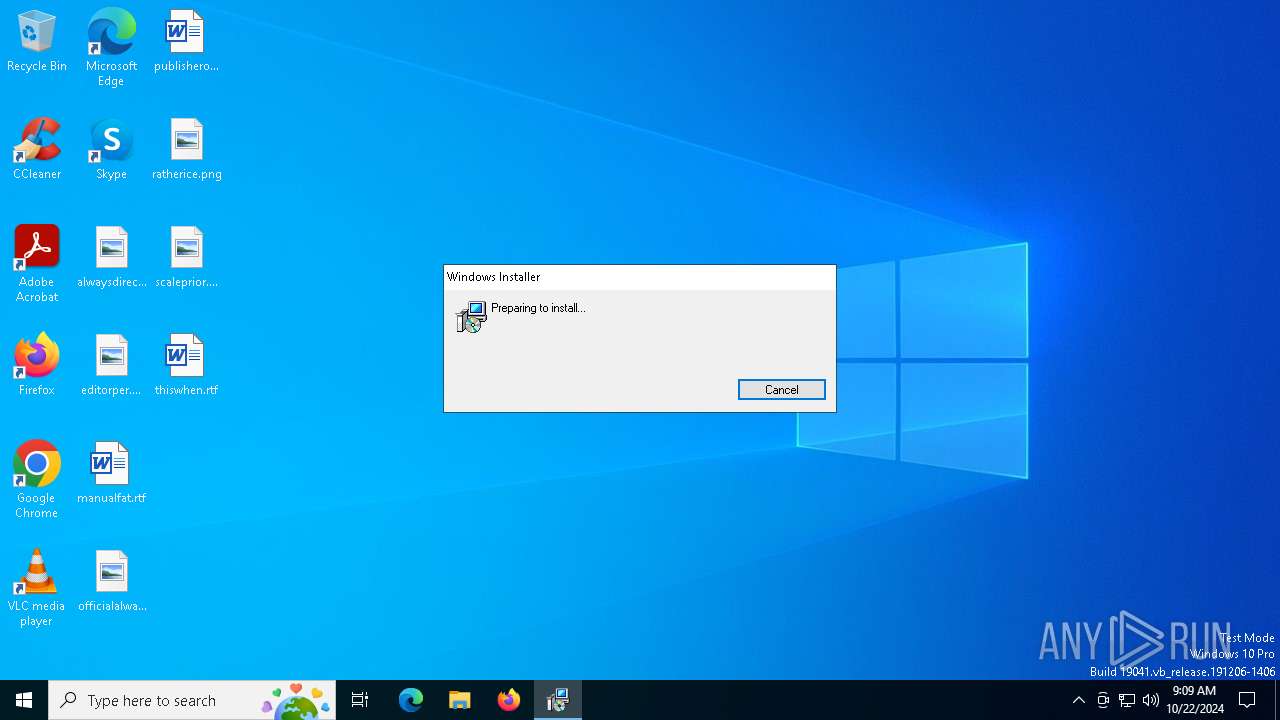
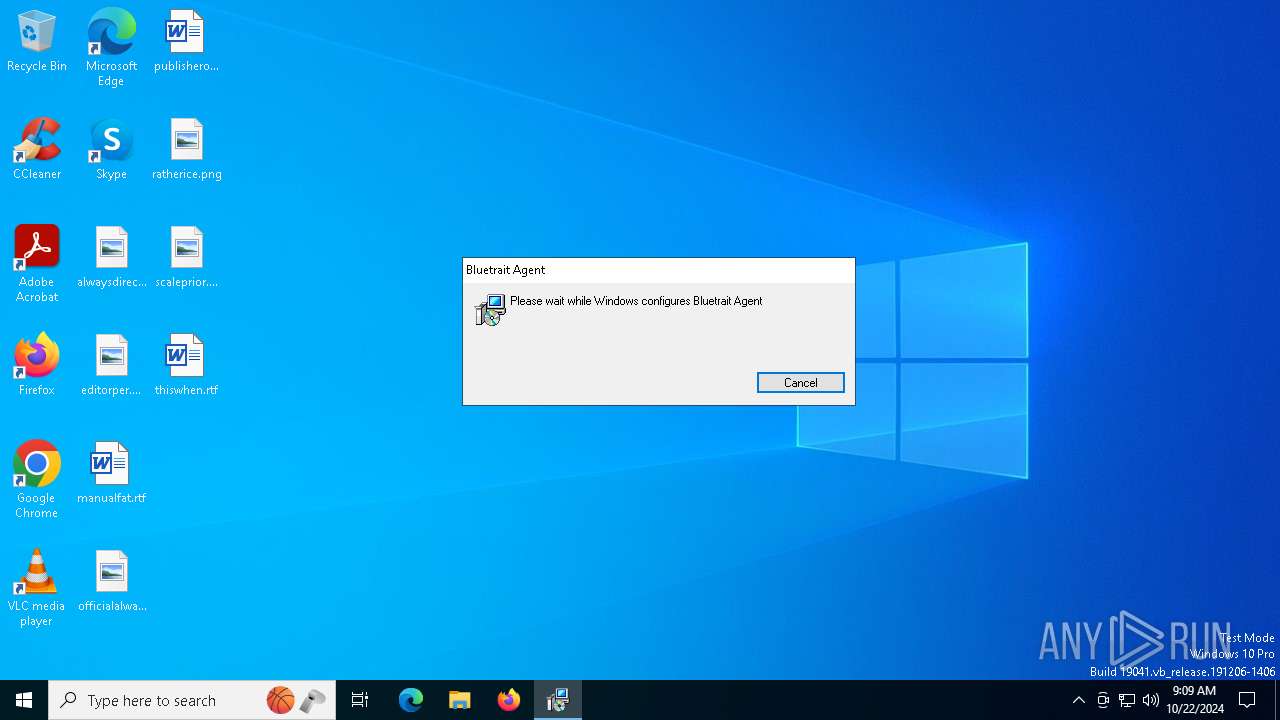
| Analysis date: | October 22, 2024, 09:09:11 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, MSI Installer, Code page: 1252, Title: Installation Database, Subject: Bluetrait Agent, Author: Dalegroup Pty Ltd, Keywords: Installer, Comments: This installer database contains the logic and data required to install Bluetrait Agent., Template: Intel;1033, Revision Number: {BCFAFD79-BEB0-48F6-A358-DB0915FB06C8}, Create Time/Date: Thu Oct 17 17:19:30 2024, Last Saved Time/Date: Thu Oct 17 17:19:30 2024, Number of Pages: 200, Number of Words: 2, Name of Creating Application: Windows Installer XML Toolset (3.11.2.4516), Security: 2 |
| MD5: | 03259B8571BBD157354D1CD6E2771E34 |
| SHA1: | 93BE79F79651BFA55B6EB0082153D455157C08F6 |
| SHA256: | 62446E7258B20B64C058AE723B5F38B82F0B6214C5E8B9F015BF971BE061EEB0 |
| SSDEEP: | 98304:BXqSlxGf1BYOp/BS0E30q173bpS+CKLujmlSUOx6AW4p1Z3fmqRPfPAA2rNPcFYc:caenF9zW |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 3828)
- Bluetrait MSP Agent.exe (PID: 7076)
- WmiApSrv.exe (PID: 4556)
- level.exe (PID: 5604)
- WmiApSrv.exe (PID: 7004)
Hides errors and continues executing the command without stopping
- powershell.exe (PID: 4700)
Executable content was dropped or overwritten
- Bluetrait MSP Agent.exe (PID: 7076)
- install_windows.exe (PID: 3912)
- level-windows-amd64.exe (PID: 2088)
Deletes scheduled task without confirmation
- schtasks.exe (PID: 1028)
Starts POWERSHELL.EXE for commands execution
- install_windows.exe (PID: 3912)
- level.exe (PID: 5604)
- winpty-agent.exe (PID: 2088)
Starts SC.EXE for service management
- level.exe (PID: 5604)
- level-windows-amd64.exe (PID: 2088)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- cmd.exe (PID: 6216)
Uses NETSH.EXE to add a firewall rule or allowed programs
- cmd.exe (PID: 3700)
Starts CMD.EXE for commands execution
- level-windows-amd64.exe (PID: 2088)
INFO
Manages system restore points
- SrTasks.exe (PID: 6408)
An automatically generated document
- msiexec.exe (PID: 6368)
Executable content was dropped or overwritten
- msiexec.exe (PID: 5196)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
| Subject: | Bluetrait Agent |
| Author: | Dalegroup Pty Ltd |
| Keywords: | Installer |
| Comments: | This installer database contains the logic and data required to install Bluetrait Agent. |
| Template: | Intel;1033 |
| RevisionNumber: | {BCFAFD79-BEB0-48F6-A358-DB0915FB06C8} |
| CreateDate: | 2024:10:17 17:19:30 |
| ModifyDate: | 2024:10:17 17:19:30 |
| Pages: | 200 |
| Words: | 2 |
| Software: | Windows Installer XML Toolset (3.11.2.4516) |
| Security: | Read-only recommended |
Total processes
190
Monitored processes
53
Malicious processes
2
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 300 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe |
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
| 540 | powershell -Command "Get-WmiObject win32_operatingsystem | Select-Object -Expand osarchitecture" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | install_windows.exe |
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
| 612 | netsh advfirewall firewall delete rule name=\"Level Agent\" dir=in | C:\Windows\System32\netsh.exe | — | cmd.exe |
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Network Command Shell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
| 1028 | schtasks /Delete /F /TN "Level\Level Watchdog" | C:\Windows\System32\schtasks.exe | — | level-windows-amd64.exe |
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Task Scheduler Configuration Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
| 1336 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | osqueryi.exe |
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
| 1376 | "C:\Program Files\Level\osqueryi.exe" -S --verbose --alarm_timeout 10 --disable_carver --disable_enrollment --disable_extensions --disable_reenrollment --disable_watchdog --disable_caching --disable_database --disable_events --disable_hash_cache --ephemeral --config_path "C:\Program Files\Level\osquery_config.conf" --json " SELECT type, hardware_model, serial, disk_size FROM disk_info " | C:\Program Files\Level\osqueryi.exe | — | level.exe |
User: SYSTEM Company: Osquery Foundation Integrity Level: SYSTEM Description: osquery daemon and shell Exit code: 0 Version: 5.9.1.0 | ||||
| 2056 | C:\windows\system32\sc.exe failureflag Level 1 | C:\Windows\System32\sc.exe | — | level.exe |
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
| 2088 | C:\WINDOWS\TEMP\level-windows-amd64.exe /action install /key W8NnBRE2fRfLJgb21PkPDMMc | C:\Windows\Temp\level-windows-amd64.exe | install_windows.exe | |
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 | ||||
| 2088 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | osqueryi.exe |
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | ||||
| 2088 | "C:\Program Files\Level\winpty-agent.exe" \\.\pipe\winpty-control-5604-1-1db24627e51ceb0-31a1631cbcf84a4c5186da0e5df1c369 0 1 40 40 | C:\Program Files\Level\winpty-agent.exe | — | level.exe |
User: SYSTEM Integrity Level: SYSTEM | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
30
Suspicious files
47
Text files
28
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5196 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 6368 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_93702E680A5530C052C8D2BA33A2225F | der | |
MD5:C58609BF40685CB5C34DAB4979C2E0D0 | SHA256:FD8AC52BCC75885BA10ED1F25FD03B63A00C2BBCA34F606A62E01C35396D7DAE | |||
| 6368 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B2FAF7692FD9FFBD64EDE317E42334BA_93702E680A5530C052C8D2BA33A2225F | binary | |
MD5:B6E614F1E0D58BE9AF6270A36EC7F586 | SHA256:4A65584AA82B7B4380456314120DA15DA44BD85C8B8E89C3941A23EE75DEAB10 | |||
| 6368 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\18E6B4A57A6BC7EC9B861CDF2D6D0D02_C3B142D2C5374581DC2FDFFDEDBDEDDB | der | |
MD5:9DC8D530072E5640974D0DCCD1CC0275 | SHA256:50EC44E88EC292BCB1480B28CC773F0BDCDEBC9A78138578B213E8CC3C43CC8D | |||
| 5196 | msiexec.exe | C:\Windows\Installer\MSI3609.tmp | executable | |
MD5:A3AE5D86ECF38DB9427359EA37A5F646 | SHA256:C8D190D5BE1EFD2D52F72A72AE9DFA3940AB3FACEB626405959349654FE18B74 | |||
| 5196 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{b38830e7-1a68-402d-8398-869d1e8e25e3}_OnDiskSnapshotProp | binary | |
MD5:A012566DC5CA9828C84C6A1A9514891E | SHA256:B988BC83AA280F046CE4B774312C8DE773E396CDF830F3EED7778188F6AC05F3 | |||
| 5196 | msiexec.exe | C:\Windows\Installer\MSI35D9.tmp | binary | |
MD5:96616559ABAF0B576AD14924A4FCB5BE | SHA256:071B20424B76145178E46776DFE5CF56EC9C298B60D5DDBB34C66240779293B9 | |||
| 5196 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:A012566DC5CA9828C84C6A1A9514891E | SHA256:B988BC83AA280F046CE4B774312C8DE773E396CDF830F3EED7778188F6AC05F3 | |||
| 5196 | msiexec.exe | C:\Program Files (x86)\Bluetrait Agent\Bluetrait MSP Agent.exe | executable | |
MD5:0BF209E4007D441249AE049C623F6544 | SHA256:53313CD27BEFC363C5D49FF70DE54EF0DACE6E6470B9B53875F40B67980EA263 | |||
| 5196 | msiexec.exe | C:\Windows\Installer\930f7.msi | executable | |
MD5:7EE67DEBCAA7A2B2088E395FA878C3CC | SHA256:A409E2BF0B5C7C7507E4DBA46E6BBF0D1A01A75BDA68A81067D11C9DABEA42B9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
159
DNS requests
38
Threats
252
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 973 b | whitelisted |
— | — | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 1.01 Kb | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 973 b | whitelisted |
— | — | GET | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEEj8k7RgVZSNNqfJionWlBY%3D | US | binary | 1.42 Kb | whitelisted |
— | — | GET | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQVD%2BnGf79Hpedv3mhy6uKMVZkPCQQUDyrLIIcouOxvSK4rVKYpqhekzQwCEHJ8a%2B5Vb7xQ27FZY20Vhh4%3D | US | binary | 637 b | whitelisted |
— | — | GET | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSdE3gf41WAic8Uh9lF92%2BIJqh5qwQUMuuSmv81lkgvKEBCcCA2kVwXheYCEGIdbQxSAZ47kHkVIIkhHAo%3D | US | binary | 765 b | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 312 b | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | NL | binary | 408 b | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
4020 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 172.64.149.23:80 | ocsp.comodoca.com | CLOUDFLARENET | US | whitelisted |
— | — | 2.23.209.135:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
— | — | 40.126.31.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO Level.io Download Agent Domain in DNS Lookup (downloads .level .io) |
— | — | Misc activity | ET INFO Level.io Agent Update Domain in DNS Lookup (builds .level .io) |
— | — | Misc activity | ET INFO Level.io Check Connectivity Status in DNS Lookup (online .level .io) |
— | — | Misc activity | ET INFO Level.io Agent Domain in DNS Lookup (agents .level .io) |
— | — | Misc activity | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
— | — | Misc activity | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
— | — | Misc activity | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
— | — | Misc activity | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
— | — | Misc activity | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |
— | — | Misc activity | ET INFO Session Traversal Utilities for NAT (STUN Binding Request On Non-Standard High Port) |