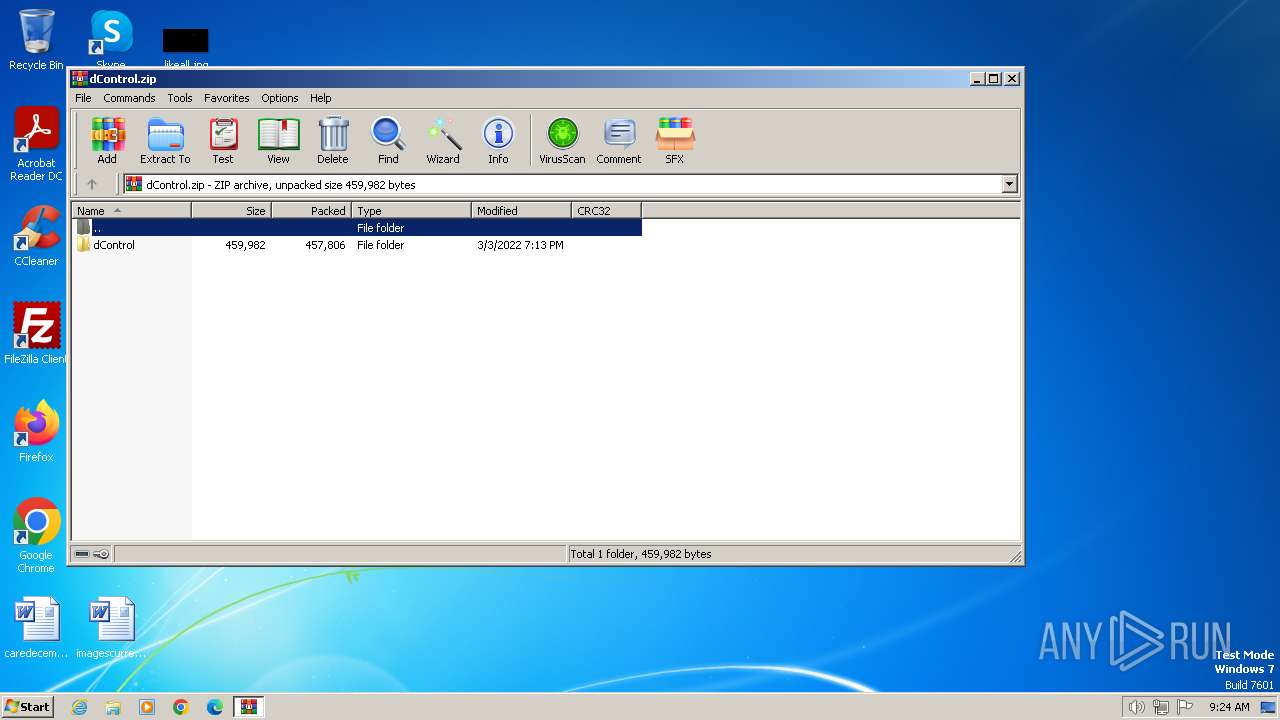
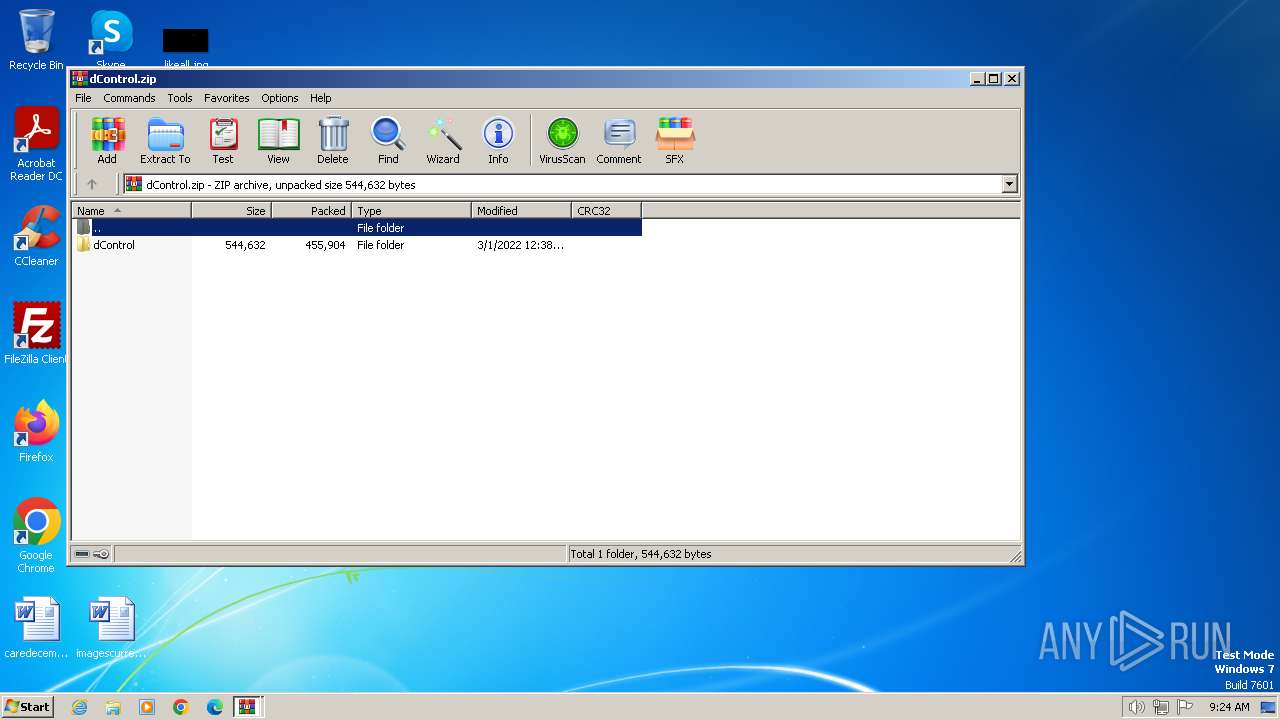
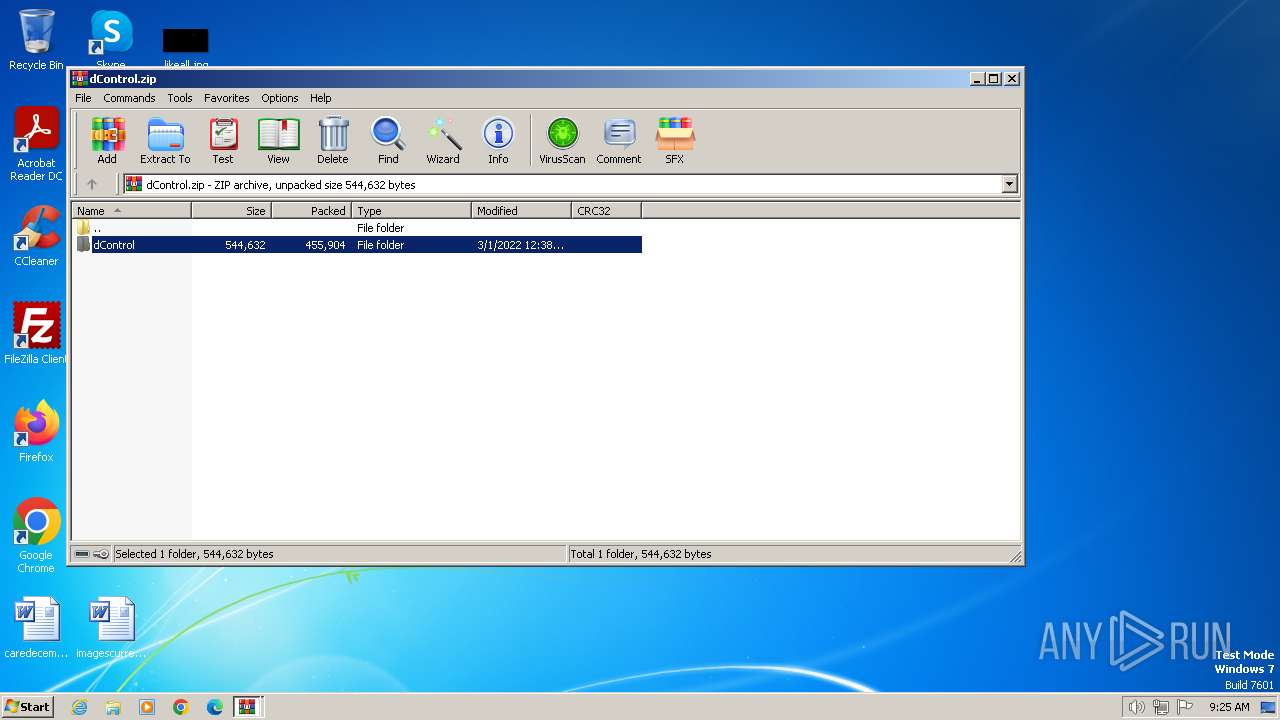
| File name: | dControl.zip |
| Full analysis: | https://app.any.run/tasks/e07bd726-e2a7-4712-ad9f-c83d6fb34bf7 |
| Verdict: | Malicious activity |
| Analysis date: | February 13, 2024, 09:24:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract, compression method=store |
| MD5: | 8E76231C388809BBF874E872848314DE |
| SHA1: | 8BE76AB62DBE10DF5EB2264487ACD12146F63DA7 |
| SHA256: | 62442FD70BDE2BF31B677447CB4216DAEEEFF48FCC0AAC4495CABC30092A5533 |
| SSDEEP: | 24576:gQ2PERuEn6TuYoVzbK3nxDgrNhv+331ZLvW:gQ2cRuE6TuYoVzbK3nxkrNhv+331ZLvW |
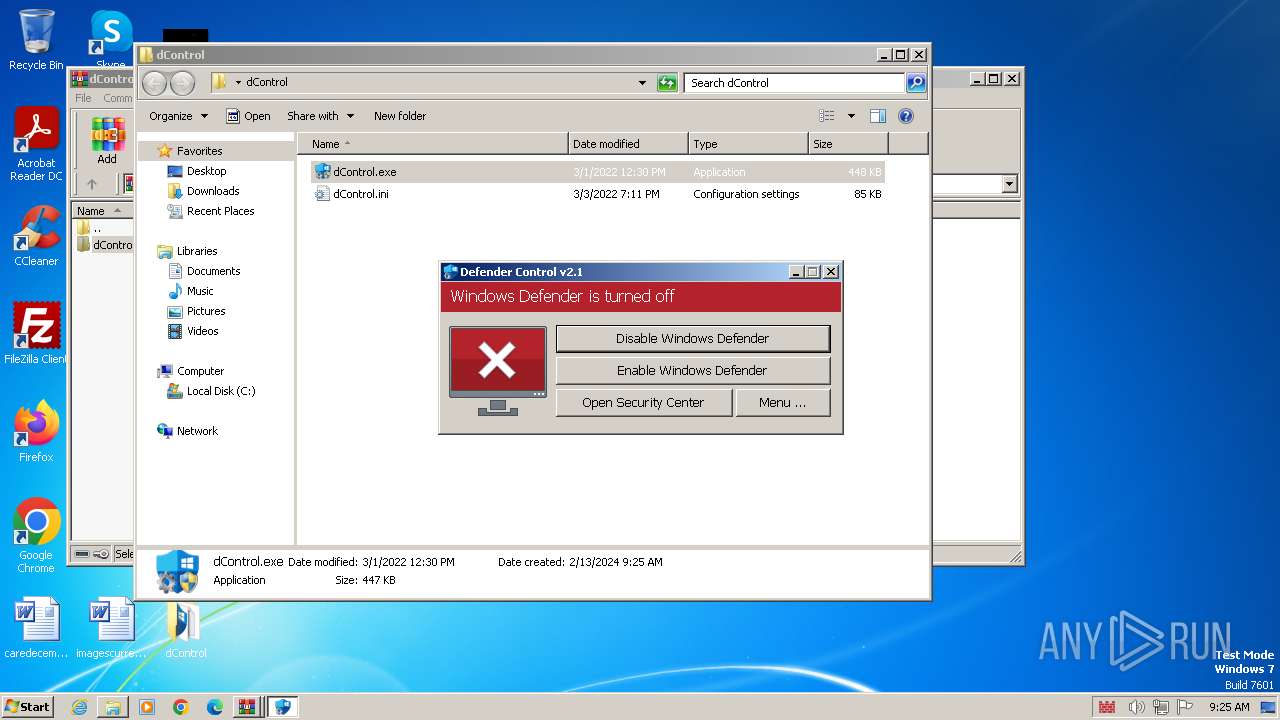
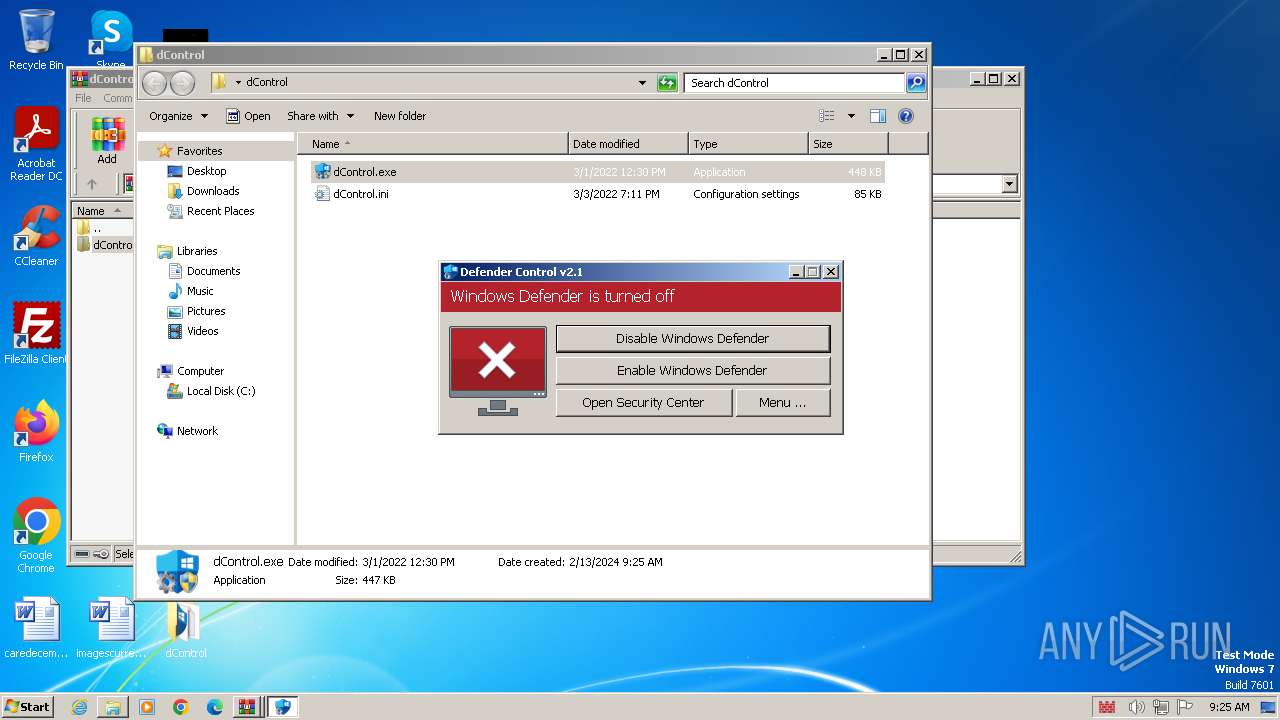
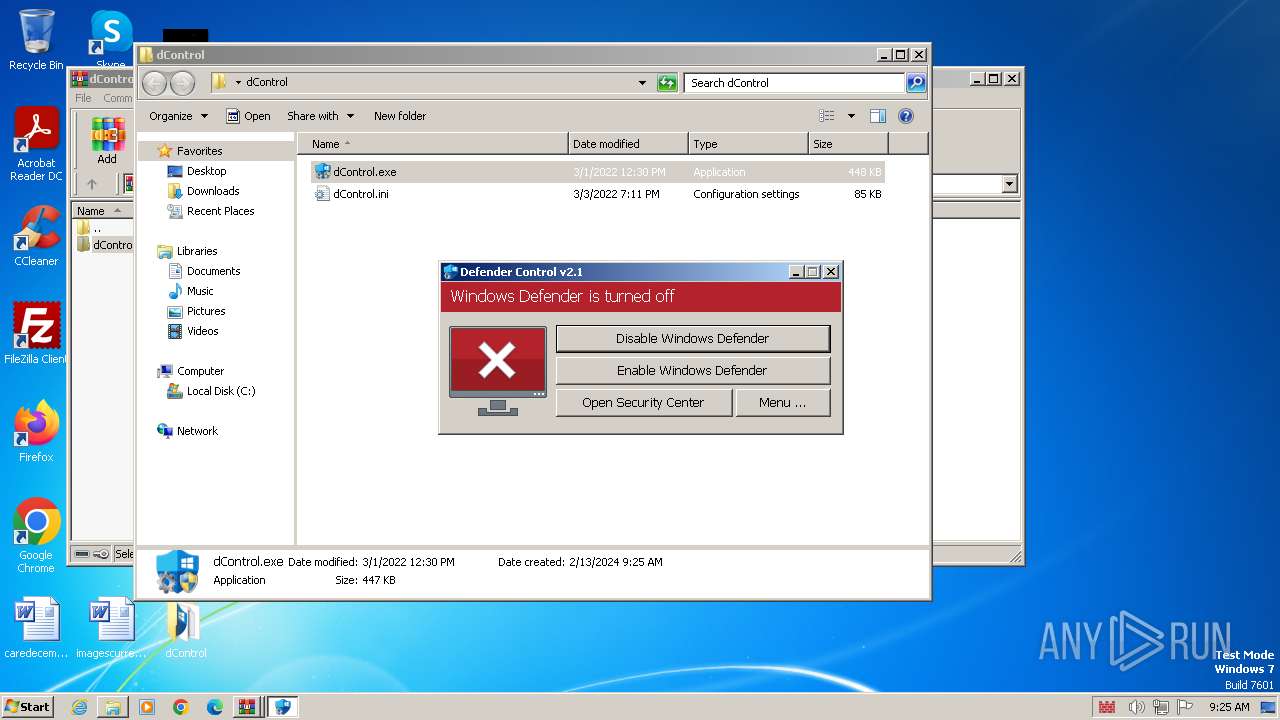
MALICIOUS
Disables Windows Defender
- dControl.exe (PID: 4000)
Creates or modifies Windows services
- dControl.exe (PID: 4000)
SUSPICIOUS
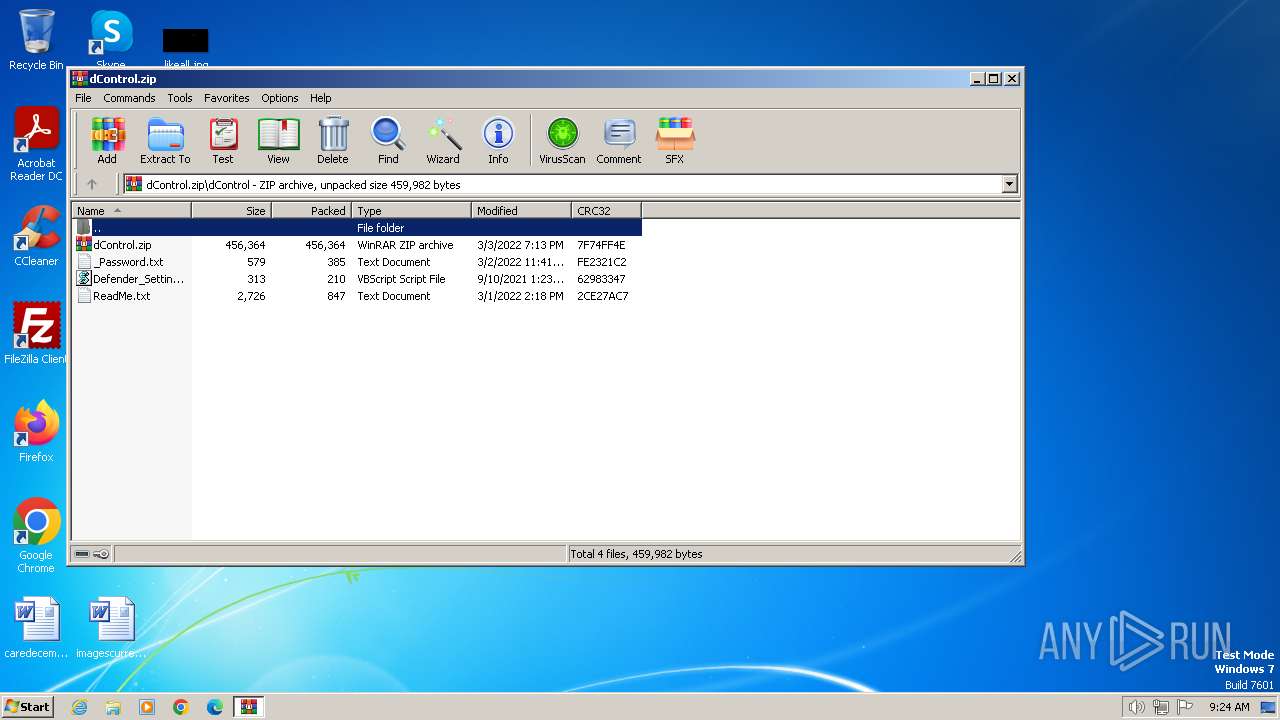
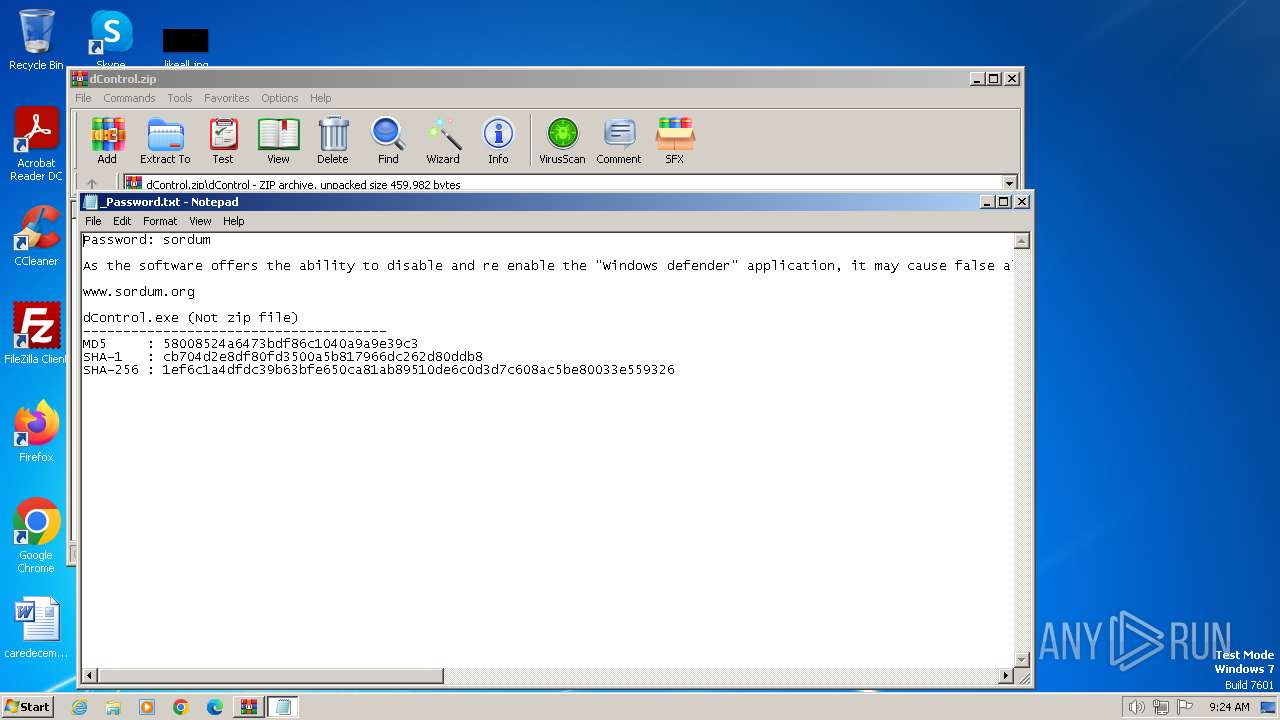
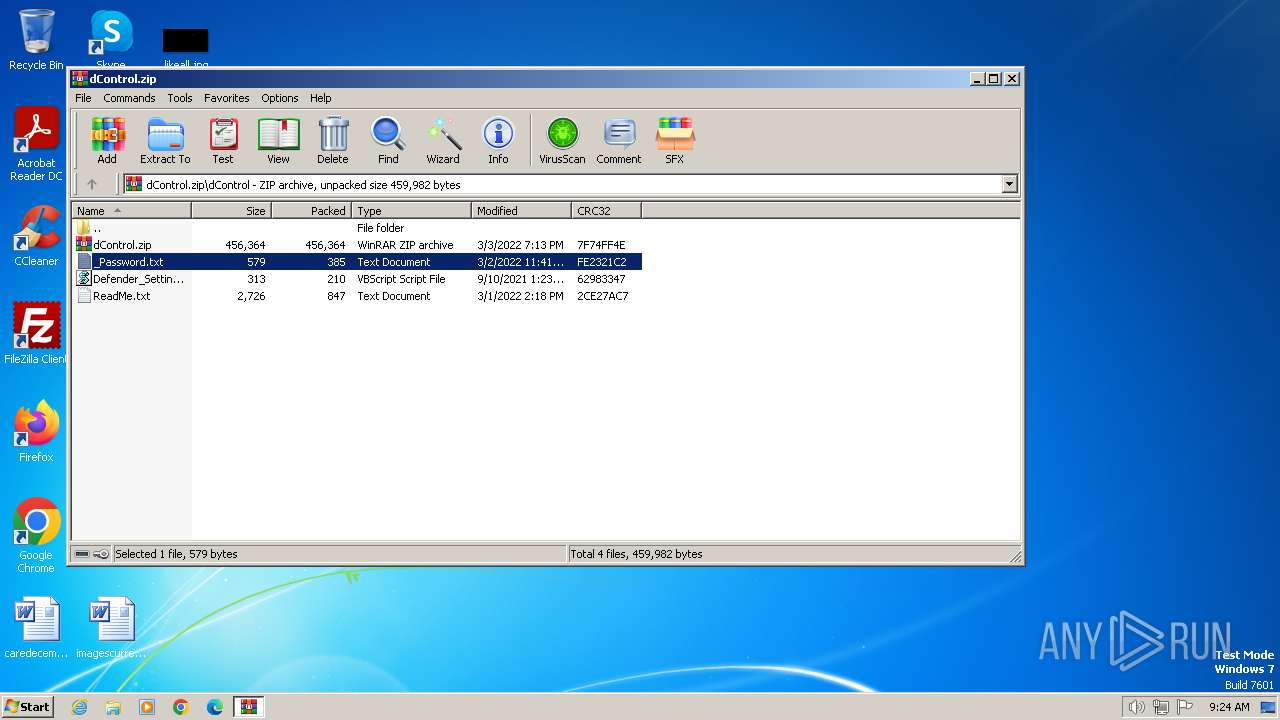
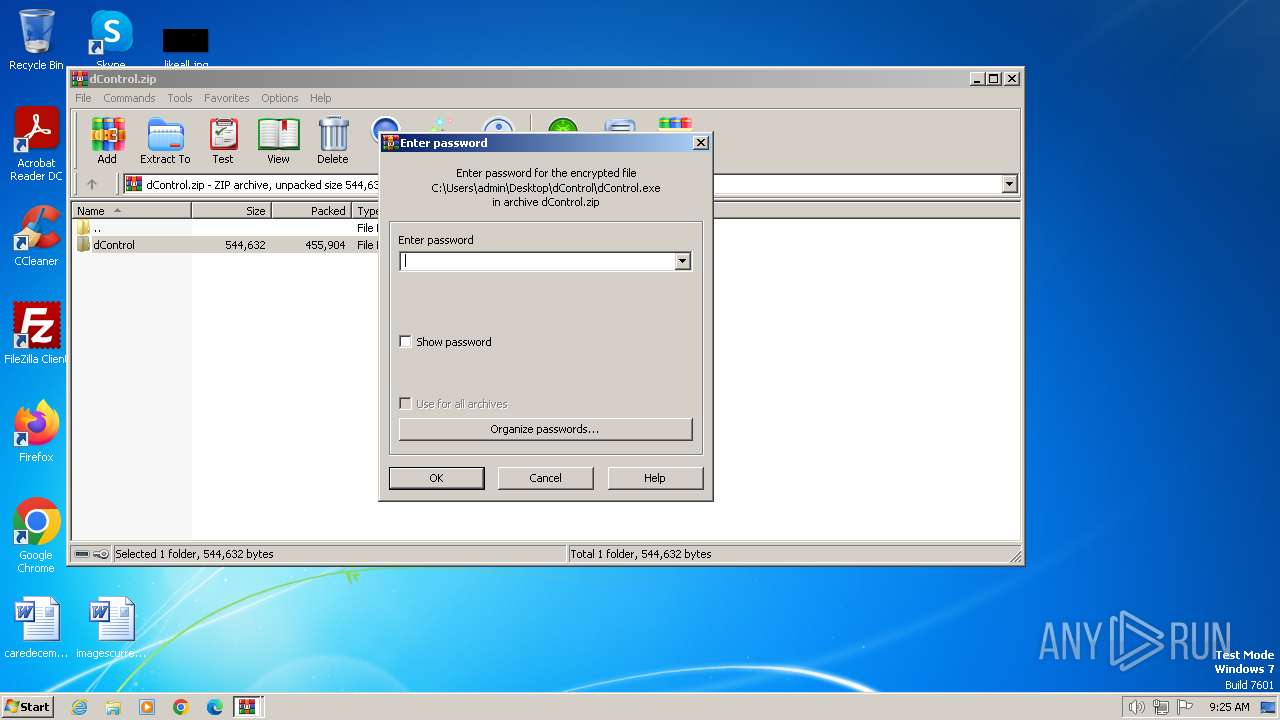
Start notepad (likely ransomware note)
- WinRAR.exe (PID: 3288)
Application launched itself
- WinRAR.exe (PID: 3288)
- dControl.exe (PID: 2124)
- dControl.exe (PID: 1696)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 3288)
INFO
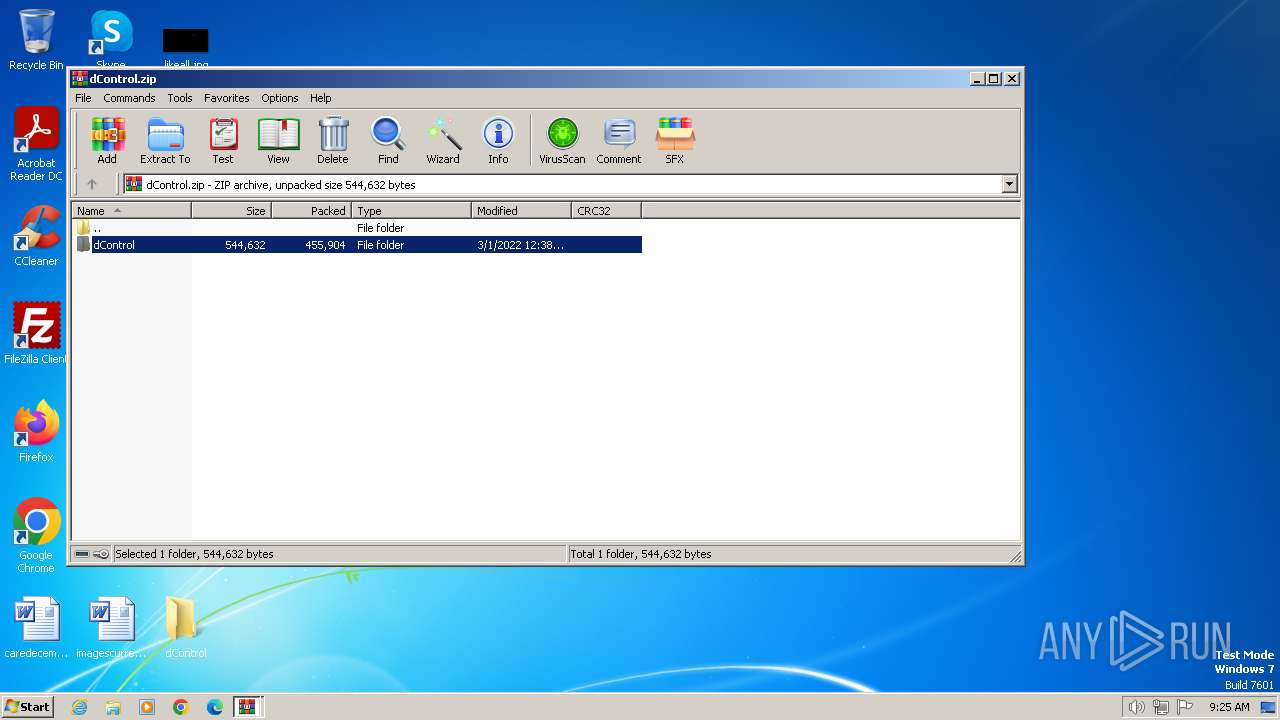
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3348)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3348)
Reads mouse settings
- dControl.exe (PID: 2124)
- dControl.exe (PID: 1696)
- dControl.exe (PID: 4000)
Manual execution by a user
- dControl.exe (PID: 2124)
- dControl.exe (PID: 3944)
- wmpnscfg.exe (PID: 956)
Checks supported languages
- dControl.exe (PID: 2124)
- dControl.exe (PID: 1696)
- dControl.exe (PID: 4000)
- wmpnscfg.exe (PID: 956)
Reads the computer name
- dControl.exe (PID: 2124)
- dControl.exe (PID: 1696)
- dControl.exe (PID: 4000)
- wmpnscfg.exe (PID: 956)
Create files in a temporary directory
- dControl.exe (PID: 2124)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2022:03:03 22:13:40 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | dControl/ |
Total processes
51
Monitored processes
8
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 956 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
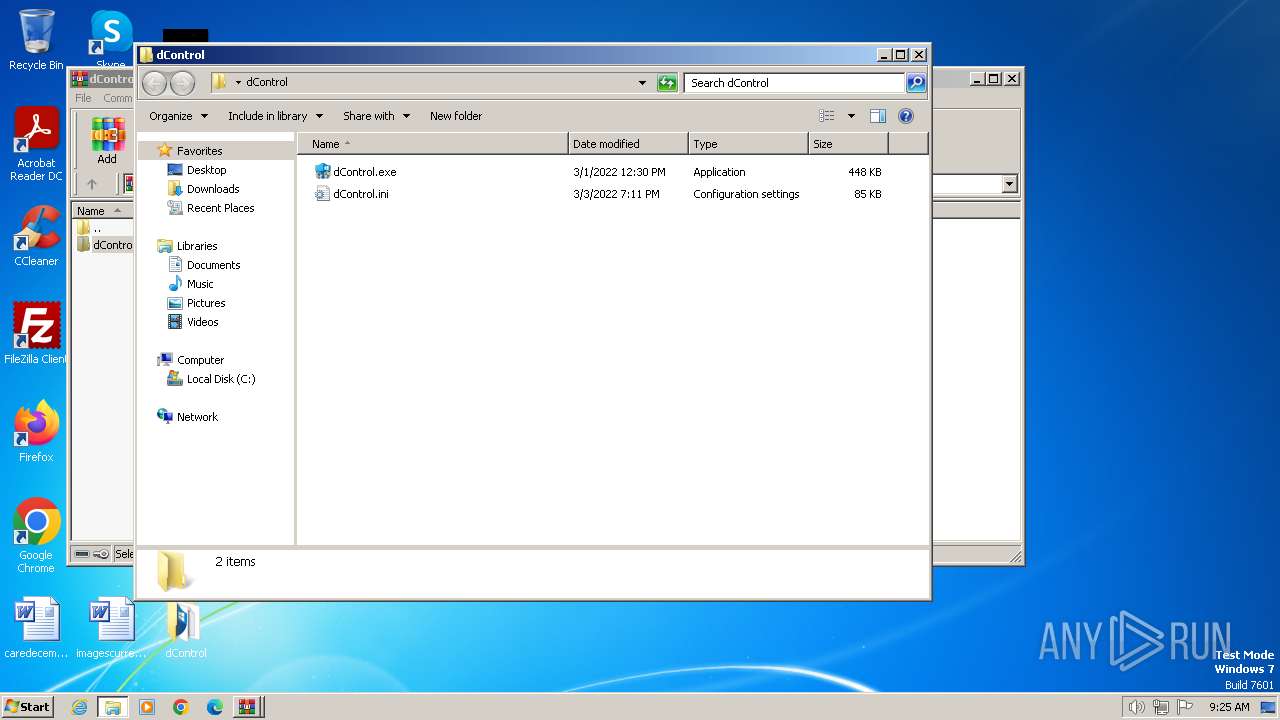
| 1696 | C:\Users\admin\Desktop\dControl\dControl.exe | C:\Users\admin\Desktop\dControl\dControl.exe | dControl.exe | ||||||||||||
User: SYSTEM Company: www.sordum.org Integrity Level: SYSTEM Description: dControl v2.1 Exit code: 0 Version: 2.1.0.0 Modules
| |||||||||||||||
| 2124 | "C:\Users\admin\Desktop\dControl\dControl.exe" | C:\Users\admin\Desktop\dControl\dControl.exe | explorer.exe | ||||||||||||
User: admin Company: www.sordum.org Integrity Level: HIGH Description: dControl v2.1 Exit code: 0 Version: 2.1.0.0 Modules
| |||||||||||||||
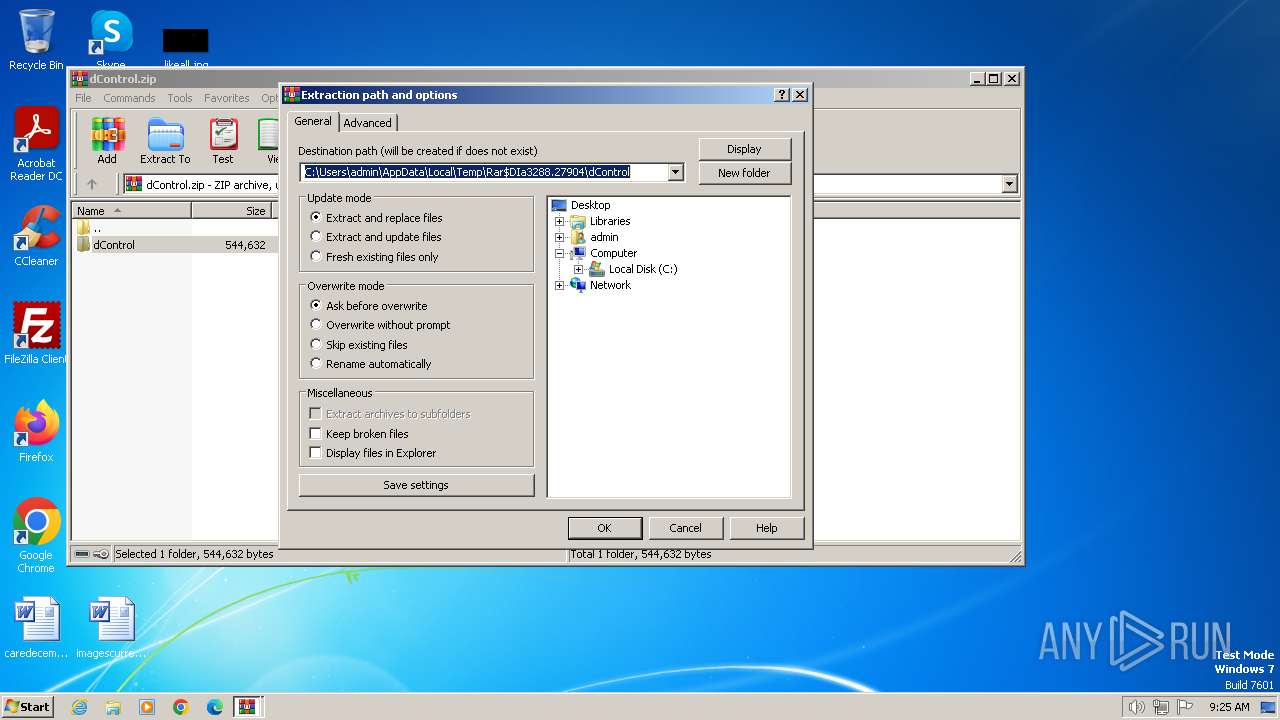
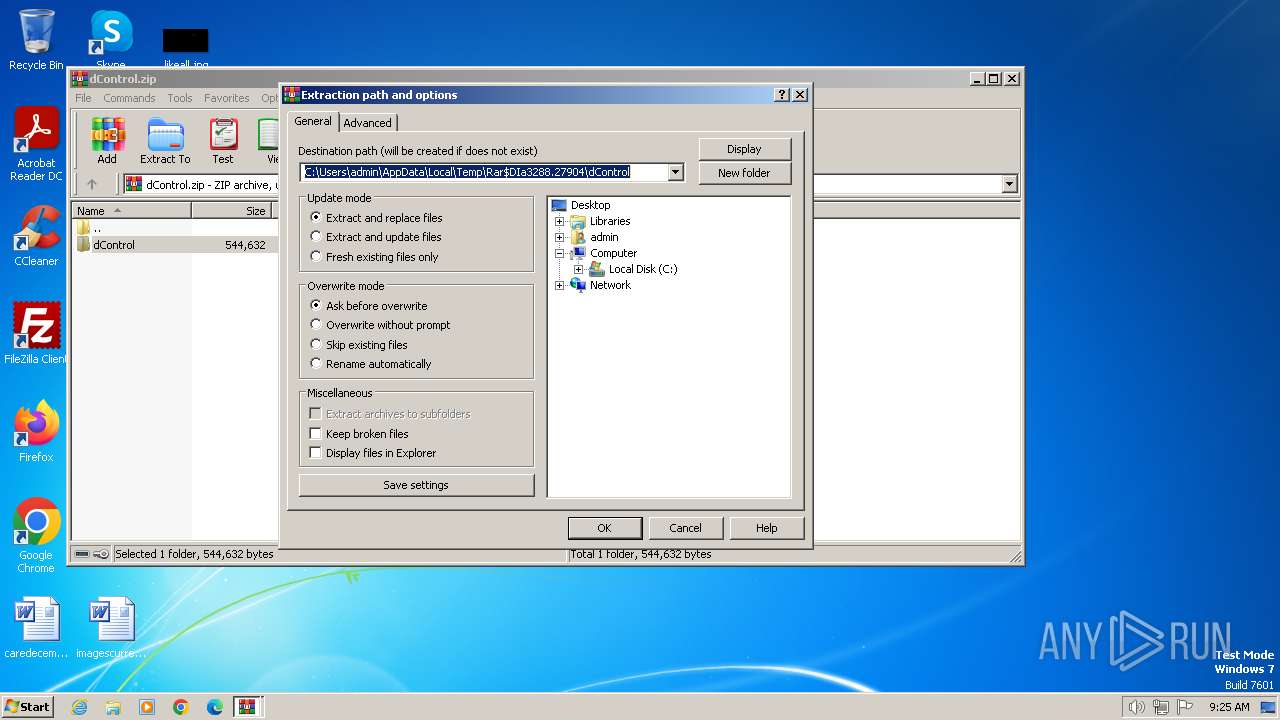
| 3288 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\dControl.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3348 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Rar$DIa3288.27904\dControl.zip | C:\Program Files\WinRAR\WinRAR.exe | WinRAR.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3652 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\Rar$DIa3288.27452\_Password.txt | C:\Windows\System32\notepad.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3944 | "C:\Users\admin\Desktop\dControl\dControl.exe" | C:\Users\admin\Desktop\dControl\dControl.exe | — | explorer.exe | |||||||||||
User: admin Company: www.sordum.org Integrity Level: MEDIUM Description: dControl v2.1 Exit code: 3221226540 Version: 2.1.0.0 Modules
| |||||||||||||||
| 4000 | "C:\Users\admin\Desktop\dControl\dControl.exe" /TI | C:\Users\admin\Desktop\dControl\dControl.exe | — | dControl.exe | |||||||||||
User: SYSTEM Company: www.sordum.org Integrity Level: SYSTEM Description: dControl v2.1 Exit code: 0 Version: 2.1.0.0 Modules
| |||||||||||||||
Total events
7 792
Read events
7 689
Write events
90
Delete events
13
Modification events
| (PID) Process: | (3288) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3288) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3288) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3288) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (3288) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3288) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (3288) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\dControl.zip | |||
| (PID) Process: | (3288) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3288) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3288) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
1
Suspicious files
11
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1696 | dControl.exe | C:\Windows\TEMP\aut8142.tmp | binary | |
MD5:EFE44D9F6E4426A05E39F99AD407D3E7 | SHA256:5EA3B26C6B1B71EDAEF17CE365D50BE963AE9F4CB79B39EC723FE6E9E4054366 | |||
| 2124 | dControl.exe | C:\Users\admin\AppData\Local\Temp\2m1p2w4j.tmp | text | |
MD5:E00DCC76E4DCD90994587375125DE04B | SHA256:C8709F5A8B971D136E2273D66E65449791CA8EBA1F47DD767733EA52EE635447 | |||
| 3348 | WinRAR.exe | C:\Users\admin\Desktop\dControl\dControl.ini | text | |
MD5:1CC7481A289469296E23BD7A21973ED1 | SHA256:FAEE071E4D32DB7266FAEDAD091F6745DF5524BEA45578B06A17C89D148223D8 | |||
| 3348 | WinRAR.exe | C:\Users\admin\Desktop\dControl\dControl.exe | executable | |
MD5:58008524A6473BDF86C1040A9A9E39C3 | SHA256:1EF6C1A4DFDC39B63BFE650CA81AB89510DE6C0D3D7C608AC5BE80033E559326 | |||
| 1696 | dControl.exe | C:\Windows\TEMP\1m6p9w6j.tmp | text | |
MD5:E00DCC76E4DCD90994587375125DE04B | SHA256:C8709F5A8B971D136E2273D66E65449791CA8EBA1F47DD767733EA52EE635447 | |||
| 2124 | dControl.exe | C:\Users\admin\AppData\Local\Temp\aut8047.tmp | binary | |
MD5:9D5A0EF18CC4BB492930582064C5330F | SHA256:8F5BBCC572BC62FEB13A669F856D21886A61888FD6288AFD066272A27EA79BB3 | |||
| 2124 | dControl.exe | C:\Users\admin\AppData\Local\Temp\aut8058.tmp | binary | |
MD5:ECFFD3E81C5F2E3C62BCDC122442B5F2 | SHA256:9874AB363B07DCC7E9CD6022A380A64102C1814343642295239A9F120CB941C5 | |||
| 1696 | dControl.exe | C:\Windows\TEMP\aut8131.tmp | binary | |
MD5:9D5A0EF18CC4BB492930582064C5330F | SHA256:8F5BBCC572BC62FEB13A669F856D21886A61888FD6288AFD066272A27EA79BB3 | |||
| 4000 | dControl.exe | C:\Windows\System32\GroupPolicy\Machine\Registry.pol | binary | |
MD5:D15A332CBA4FC6D5062F42728CF751B4 | SHA256:9C064D5E80AB78FF046430CB6A6CA1B32266AF43500313CC13AD092534EE4A6F | |||
| 4000 | dControl.exe | C:\Windows\TEMP\aut820D.tmp | binary | |
MD5:EFE44D9F6E4426A05E39F99AD407D3E7 | SHA256:5EA3B26C6B1B71EDAEF17CE365D50BE963AE9F4CB79B39EC723FE6E9E4054366 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
10
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |