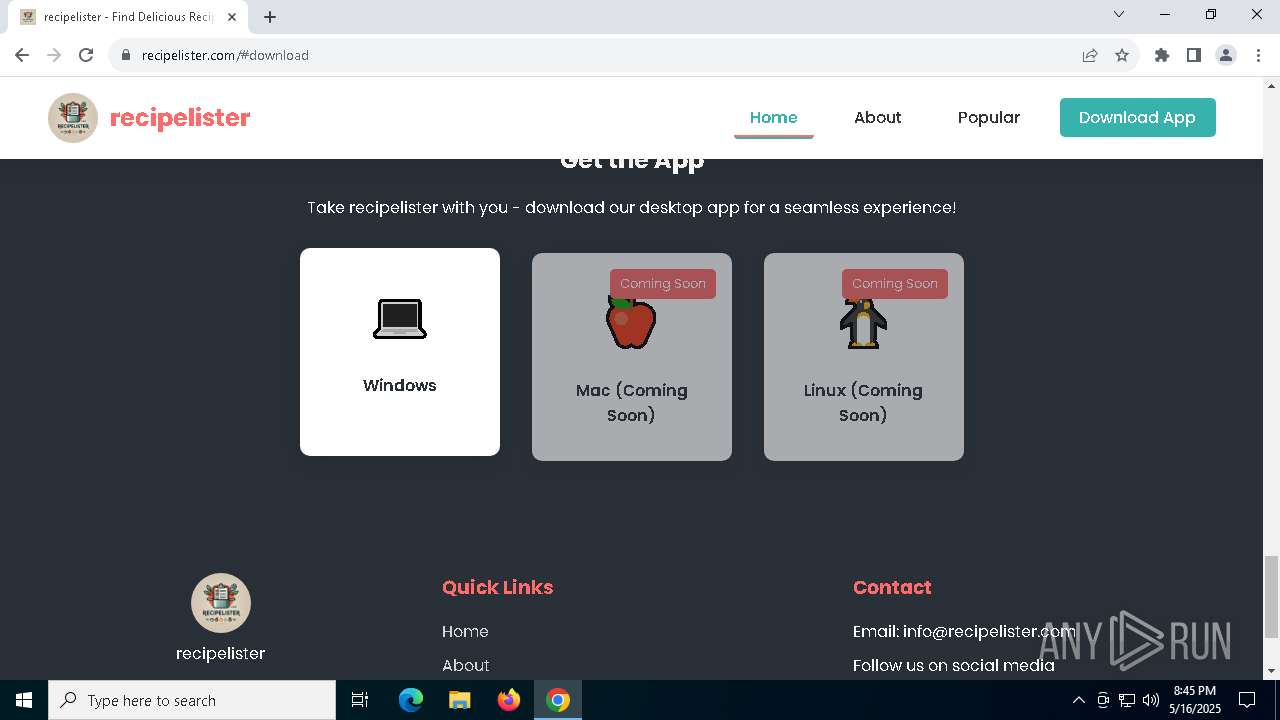
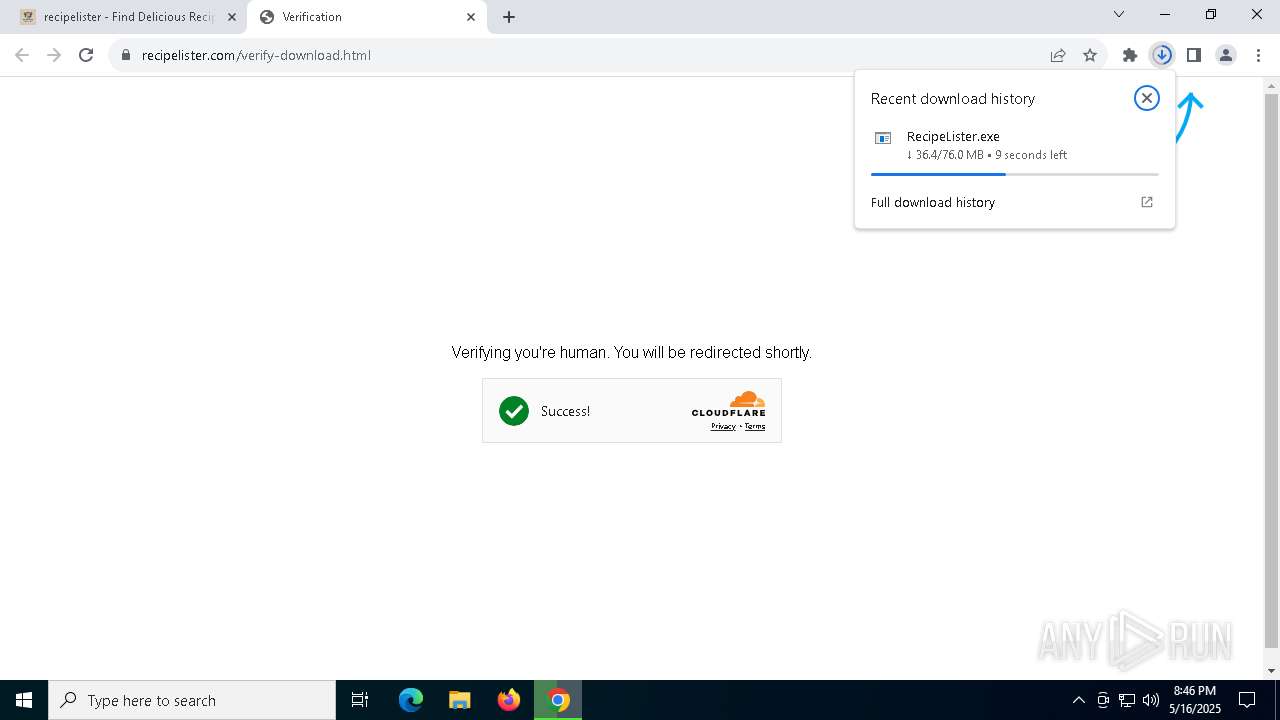
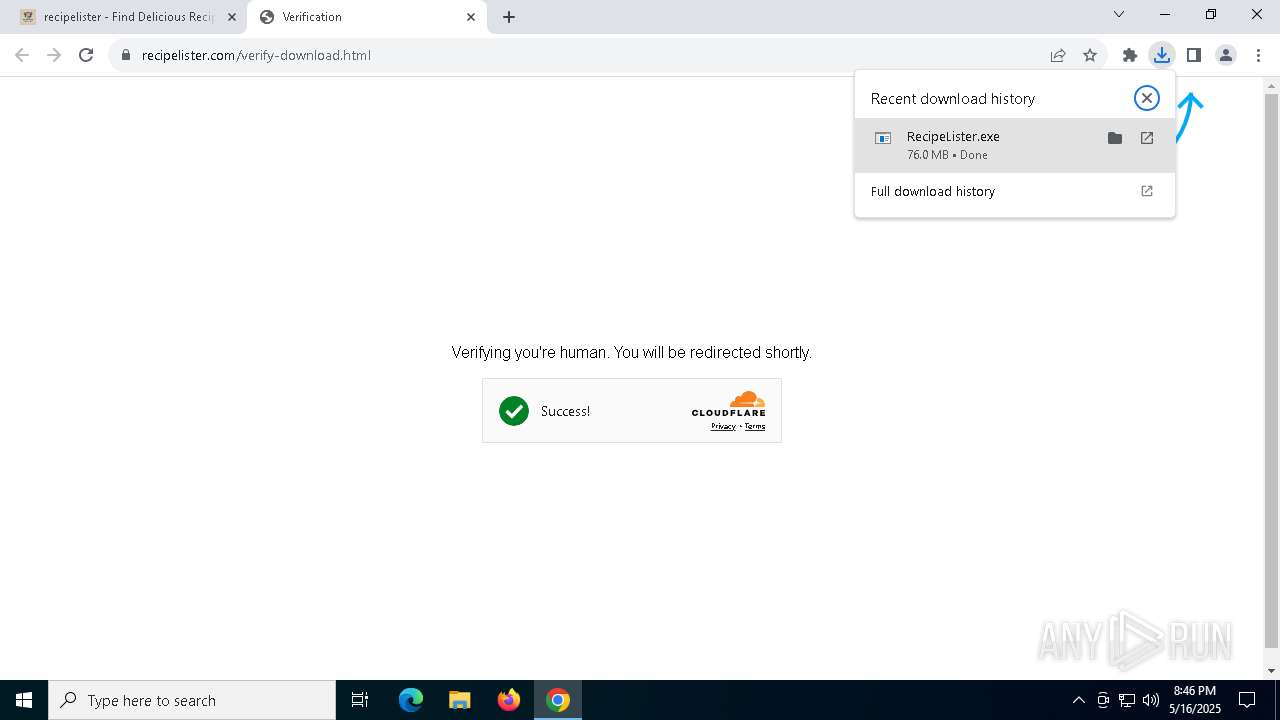
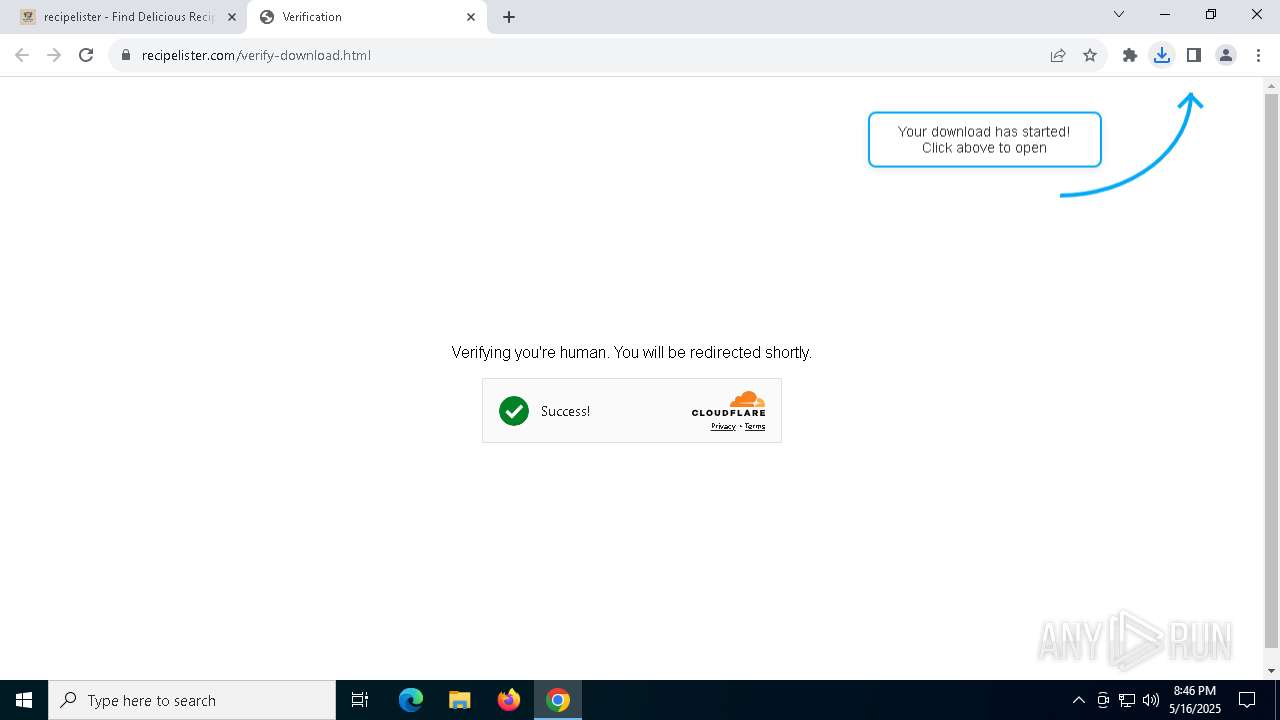
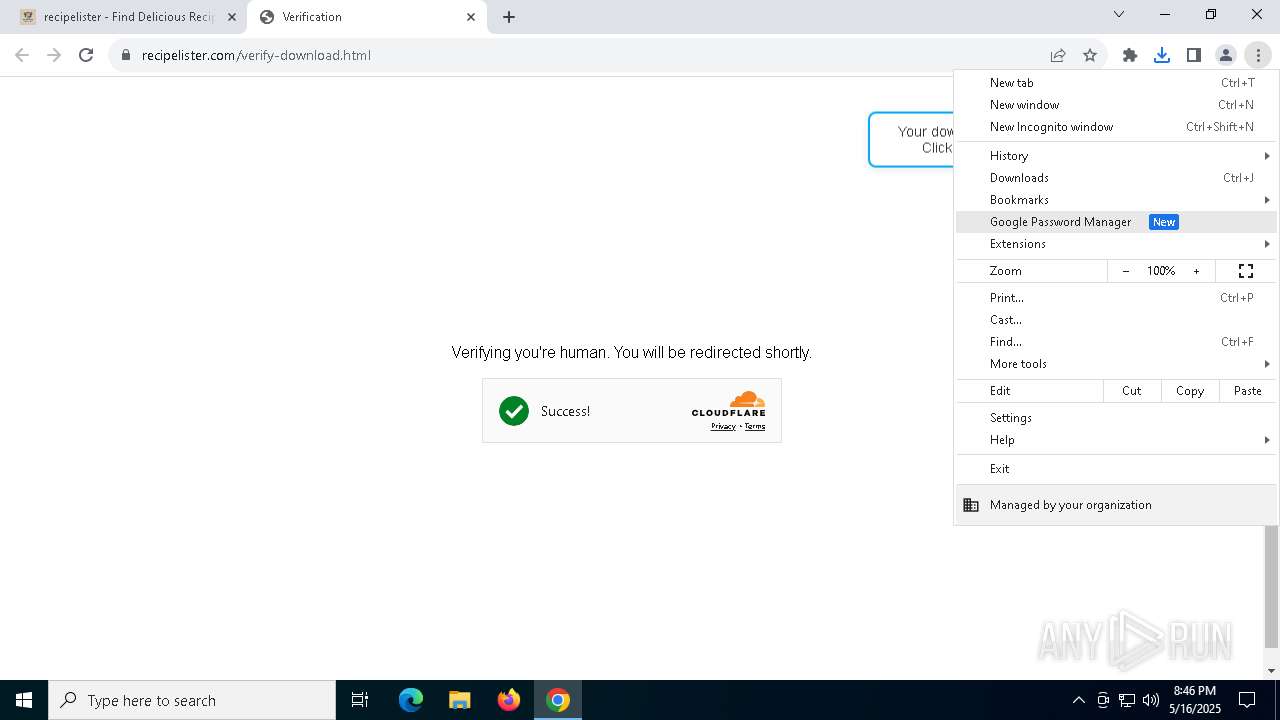
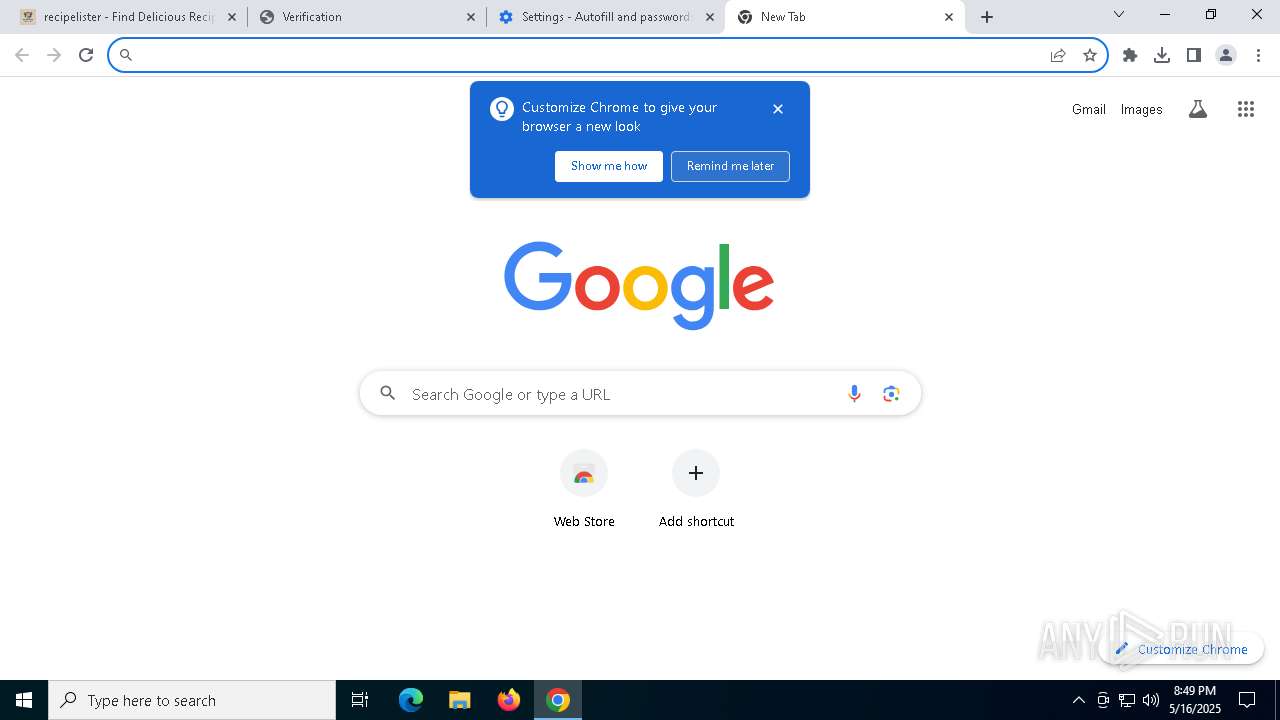
| URL: | recipelister.com |
| Full analysis: | https://app.any.run/tasks/6f1d8f69-f4c7-4040-b111-9330494484f5 |
| Verdict: | Malicious activity |
| Analysis date: | May 16, 2025, 20:45:35 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | F154E393EA8A5A105D972C66FE65DACA |
| SHA1: | D7787F11559B38FDFBF2D45C1EB3ED61EEC7033C |
| SHA256: | 623D191DCED7BF2FED9E5239F77A5D0CFE1766E8EDCF46A1CE86E40B1B702CE7 |
| SSDEEP: | 3:wtHpI:Sm |
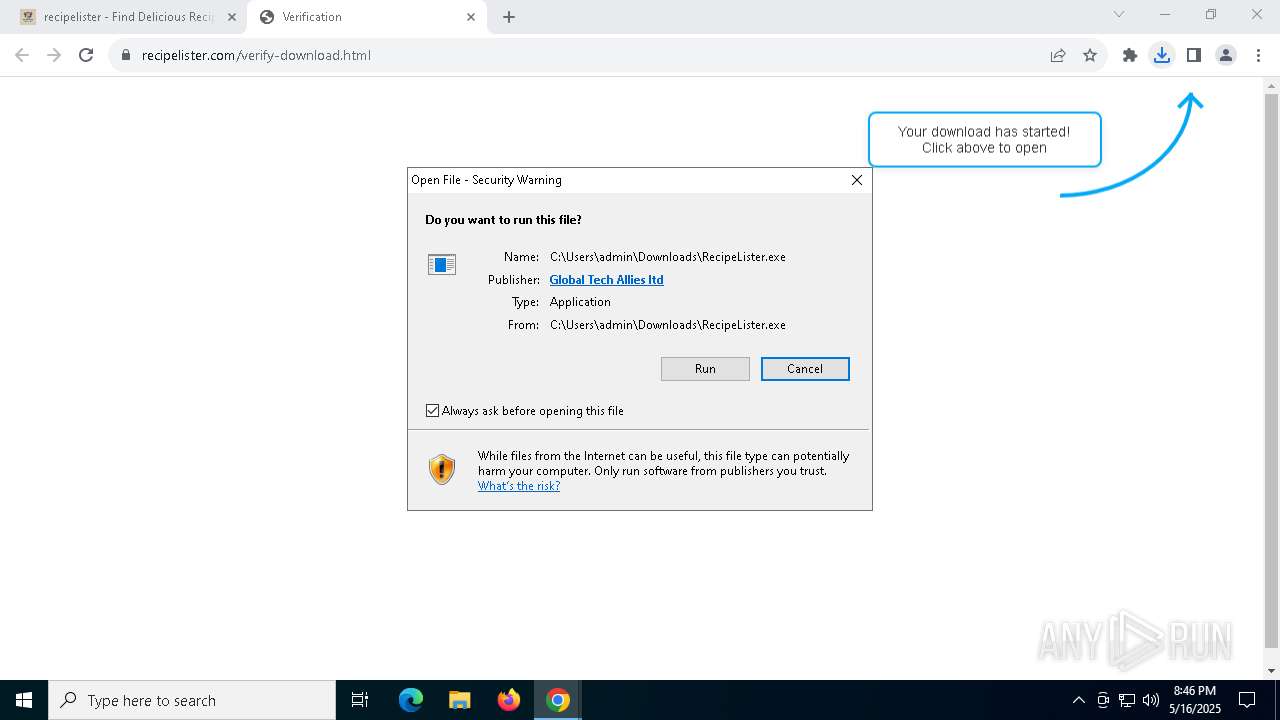
MALICIOUS
Executing a file with an untrusted certificate
- RecipeLister.exe (PID: 4068)
SUSPICIOUS
The process creates files with name similar to system file names
- RecipeLister.exe (PID: 4068)
Malware-specific behavior (creating "System.dll" in Temp)
- RecipeLister.exe (PID: 4068)
Drops 7-zip archiver for unpacking
- RecipeLister.exe (PID: 4068)
Process drops legitimate windows executable
- RecipeLister.exe (PID: 4068)
Executable content was dropped or overwritten
- RecipeLister.exe (PID: 4068)
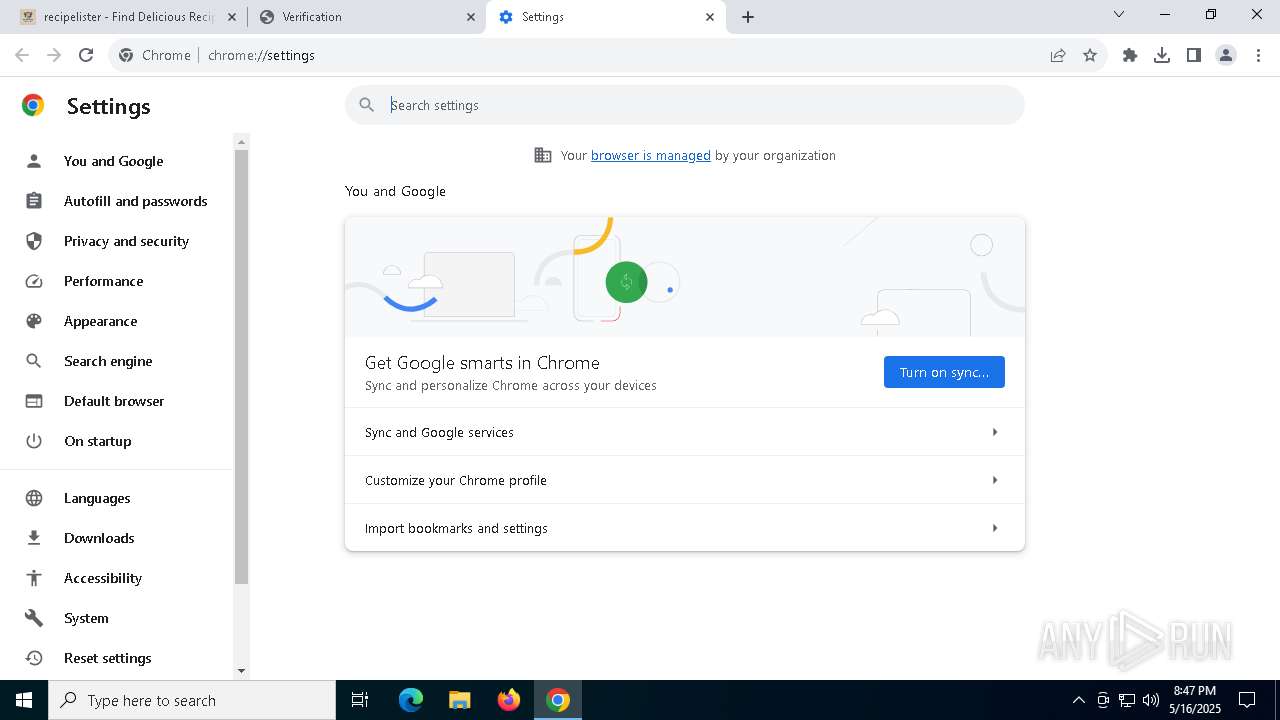
Reads security settings of Internet Explorer
- RecipeLister.exe (PID: 4068)
- Recipe Finder - Recipe Lister.exe (PID: 5164)
Application launched itself
- Recipe Finder - Recipe Lister.exe (PID: 1012)
There is functionality for taking screenshot (YARA)
- RecipeLister.exe (PID: 4068)
- Recipe Finder - Recipe Lister.exe (PID: 6480)
INFO
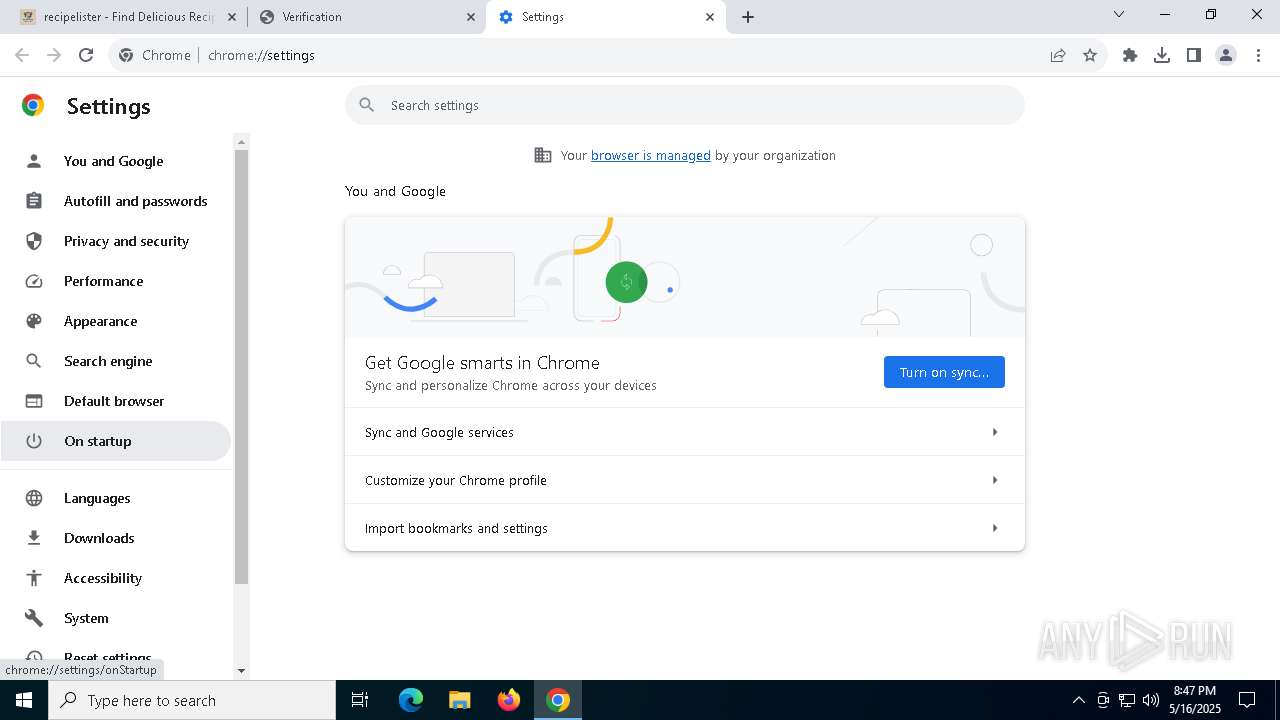
Checks supported languages
- RecipeLister.exe (PID: 4068)
- Recipe Finder - Recipe Lister.exe (PID: 1012)
- Recipe Finder - Recipe Lister.exe (PID: 6480)
- Recipe Finder - Recipe Lister.exe (PID: 5512)
- Recipe Finder - Recipe Lister.exe (PID: 6988)
- Recipe Finder - Recipe Lister.exe (PID: 5164)
Executable content was dropped or overwritten
- chrome.exe (PID: 5972)
Application launched itself
- chrome.exe (PID: 5972)
Reads the computer name
- RecipeLister.exe (PID: 4068)
- Recipe Finder - Recipe Lister.exe (PID: 1012)
- Recipe Finder - Recipe Lister.exe (PID: 5512)
- Recipe Finder - Recipe Lister.exe (PID: 6480)
- Recipe Finder - Recipe Lister.exe (PID: 5164)
Create files in a temporary directory
- RecipeLister.exe (PID: 4068)
- Recipe Finder - Recipe Lister.exe (PID: 1012)
The sample compiled with english language support
- RecipeLister.exe (PID: 4068)
Reads product name
- Recipe Finder - Recipe Lister.exe (PID: 1012)
Reads Environment values
- Recipe Finder - Recipe Lister.exe (PID: 1012)
- Recipe Finder - Recipe Lister.exe (PID: 5164)
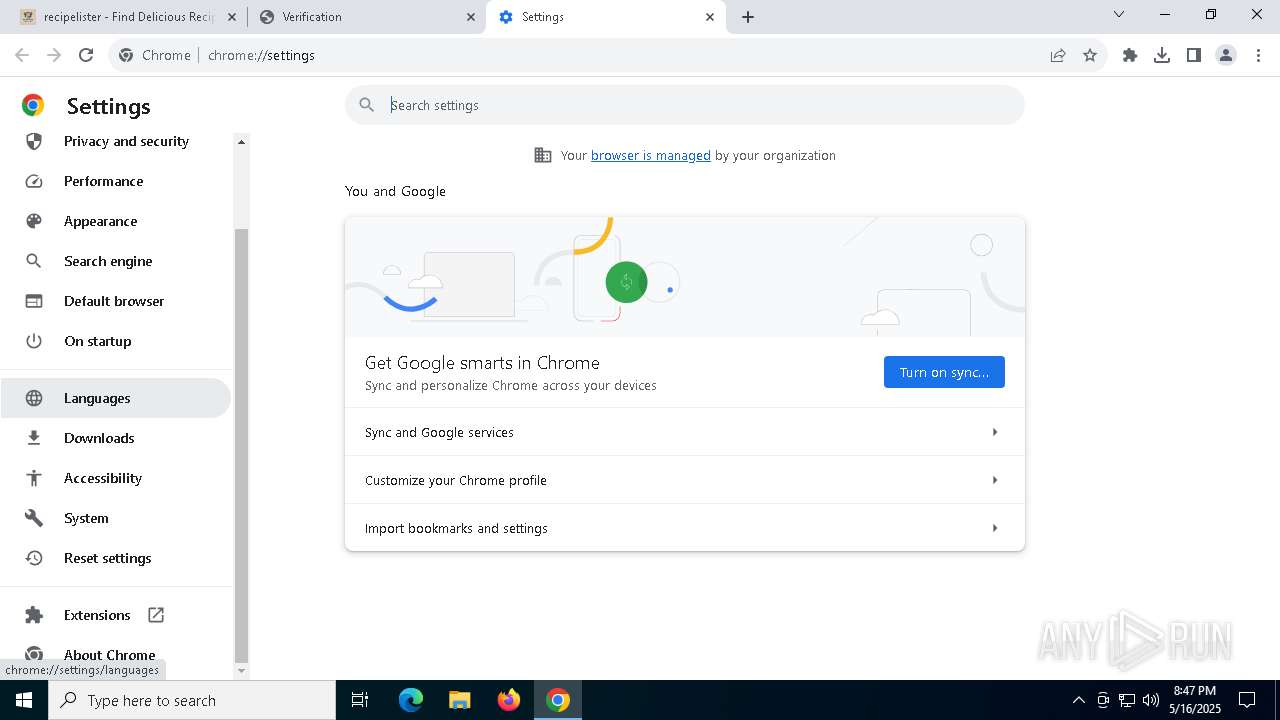
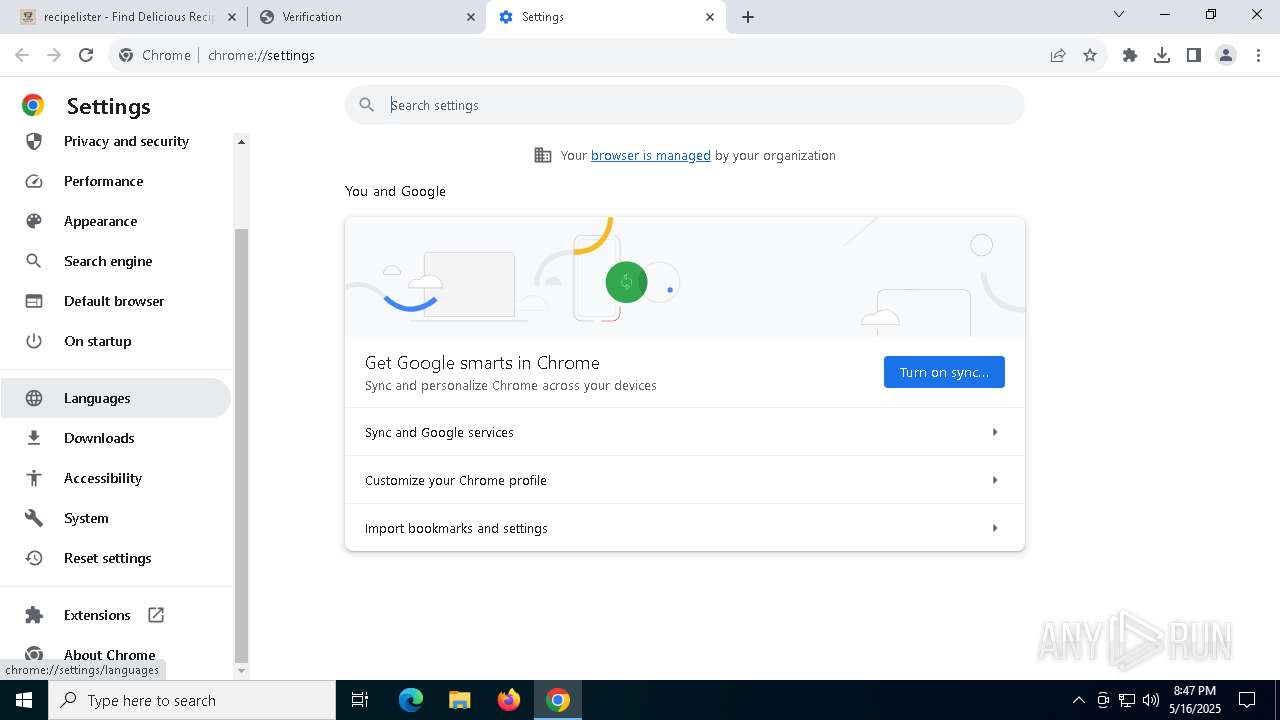
Checks proxy server information
- Recipe Finder - Recipe Lister.exe (PID: 1012)
- slui.exe (PID: 8012)
Node.js compiler has been detected
- Recipe Finder - Recipe Lister.exe (PID: 1012)
- Recipe Finder - Recipe Lister.exe (PID: 6480)
Reads the machine GUID from the registry
- Recipe Finder - Recipe Lister.exe (PID: 1012)
- Recipe Finder - Recipe Lister.exe (PID: 5164)
Creates files or folders in the user directory
- Recipe Finder - Recipe Lister.exe (PID: 5512)
- Recipe Finder - Recipe Lister.exe (PID: 1012)
- Recipe Finder - Recipe Lister.exe (PID: 5164)
Reads the software policy settings
- slui.exe (PID: 7844)
- slui.exe (PID: 8012)
- Recipe Finder - Recipe Lister.exe (PID: 5164)
Process checks computer location settings
- Recipe Finder - Recipe Lister.exe (PID: 6988)
- Recipe Finder - Recipe Lister.exe (PID: 1012)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
176
Monitored processes
40
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=11 --mojo-platform-channel-handle=4848 --field-trial-handle=2032,i,5781374932997332676,3141081599889490793,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 776 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=24 --mojo-platform-channel-handle=6672 --field-trial-handle=2032,i,5781374932997332676,3141081599889490793,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 896 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=4980 --field-trial-handle=2032,i,5781374932997332676,3141081599889490793,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1012 | "C:\Users\admin\AppData\Local\Temp\2w1rXpxZnwDUwuTeNvdD6FUkeI0\Recipe Finder - Recipe Lister.exe" | C:\Users\admin\AppData\Local\Temp\2w1rXpxZnwDUwuTeNvdD6FUkeI0\Recipe Finder - Recipe Lister.exe | — | RecipeLister.exe | |||||||||||
User: admin Company: GitHub, Inc. Integrity Level: MEDIUM Description: Recipe Finder - Recipe Lister Version: 1.0.0 Modules
| |||||||||||||||
| 1280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=22 --mojo-platform-channel-handle=5732 --field-trial-handle=2032,i,5781374932997332676,3141081599889490793,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.ProcessorMetrics --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5512 --field-trial-handle=2032,i,5781374932997332676,3141081599889490793,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
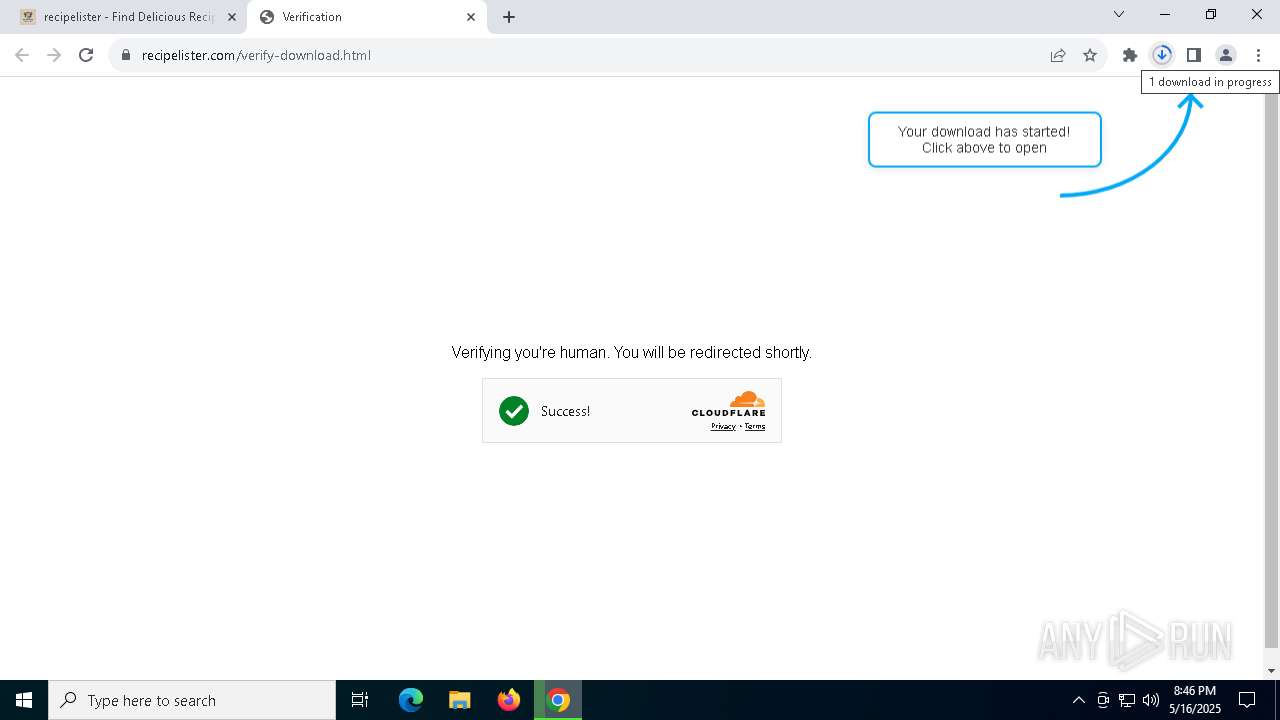
| 4068 | "C:\Users\admin\Downloads\RecipeLister.exe" | C:\Users\admin\Downloads\RecipeLister.exe | chrome.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Recipe finder app powered by recipelister.com Version: 1.0.0 Modules
| |||||||||||||||
| 4108 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=6212 --field-trial-handle=2032,i,5781374932997332676,3141081599889490793,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 4728 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=3472 --field-trial-handle=2032,i,5781374932997332676,3141081599889490793,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 5020 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoABAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=6864 --field-trial-handle=2032,i,5781374932997332676,3141081599889490793,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
17 432
Read events
17 353
Write events
19
Delete events
60
Modification events
| (PID) Process: | (5972) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5972) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5972) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5972) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5972) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (8116) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000ADC71A91A3C6DB01 | |||
| (PID) Process: | (1012) Recipe Finder - Recipe Lister.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Spelling\Dictionaries |
| Operation: | delete value | Name: | en-US |
Value: | |||
| (PID) Process: | (1012) Recipe Finder - Recipe Lister.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Spelling\Dictionaries |
| Operation: | delete value | Name: | en |
Value: | |||
| (PID) Process: | (1012) Recipe Finder - Recipe Lister.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Spelling\Dictionaries |
| Operation: | delete value | Name: | _Global_ |
Value: | |||
| (PID) Process: | (5972) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1I |
Value: 1 | |||
Executable files
26
Suspicious files
428
Text files
217
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF10c1fa.TMP | — | |
MD5:— | SHA256:— | |||
| 5972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF10c1fa.TMP | — | |
MD5:— | SHA256:— | |||
| 5972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF10c1fa.TMP | — | |
MD5:— | SHA256:— | |||
| 5972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF10c1fa.TMP | — | |
MD5:— | SHA256:— | |||
| 5972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF10c1fa.TMP | — | |
MD5:— | SHA256:— | |||
| 5972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5972 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
84
DNS requests
69
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 104.124.11.17:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5972 | chrome.exe | GET | 200 | 108.138.36.22:80 | http://ocsps.ssl.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT4XPMAgX8rbNb10iD9IkFVxGbTWwQUW8pe5d7SgarNqC1kUbbZcpuX5k8CEG7dTyXnMX05gVcxNM%2FB3KA%3D | unknown | — | — | whitelisted |
7900 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7900 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7936 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ktyagi2aeozubwzo2hlk3u6dni_1313/efniojlnjndmcbiieegkicadnoecjjef_1313_all_p4rv2wtycprx24knn2sn7g2ag4.crx3 | unknown | — | — | whitelisted |
5972 | chrome.exe | GET | 200 | 108.138.36.22:80 | http://ocsps.ssl.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBROpre88MpUocDyy2wCPdWKwtQZDwQUAYmUuf60M13w8fqF%2BSRGhKNXaV4CED%2FPMYE3OZi7YghPjS3TGKM%3D | unknown | — | — | whitelisted |
7936 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ktyagi2aeozubwzo2hlk3u6dni_1313/efniojlnjndmcbiieegkicadnoecjjef_1313_all_p4rv2wtycprx24knn2sn7g2ag4.crx3 | unknown | — | — | whitelisted |
7936 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ktyagi2aeozubwzo2hlk3u6dni_1313/efniojlnjndmcbiieegkicadnoecjjef_1313_all_p4rv2wtycprx24knn2sn7g2ag4.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 104.124.11.17:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7316 | chrome.exe | 104.21.11.185:443 | recipelister.com | CLOUDFLARENET | — | unknown |
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
7316 | chrome.exe | 74.125.71.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
7316 | chrome.exe | 142.250.185.106:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
recipelister.com |
| unknown |
accounts.google.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
www.themealdb.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
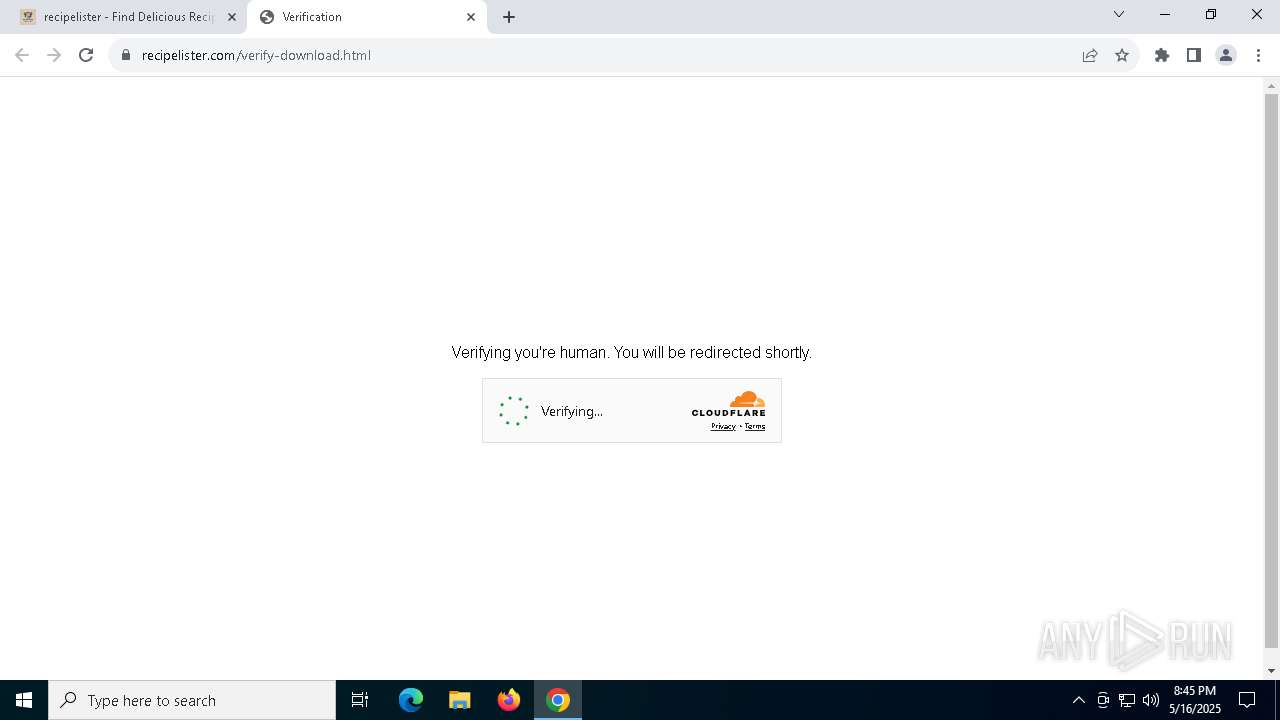
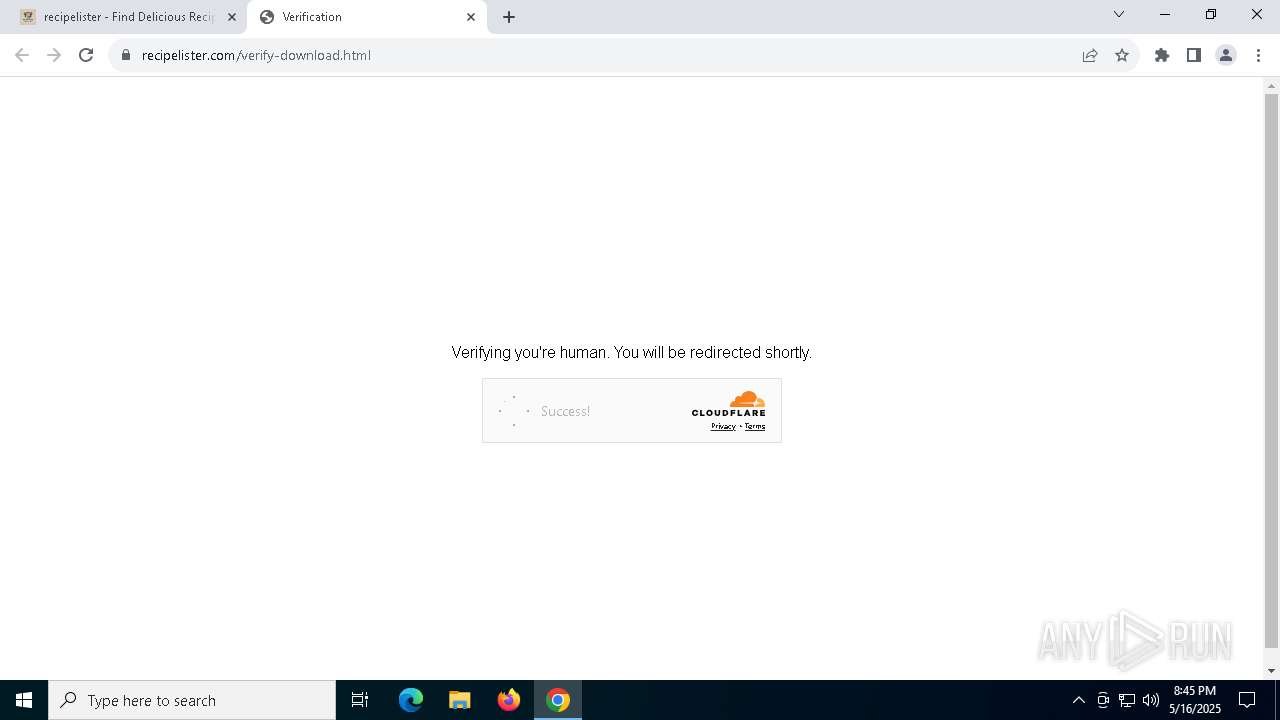
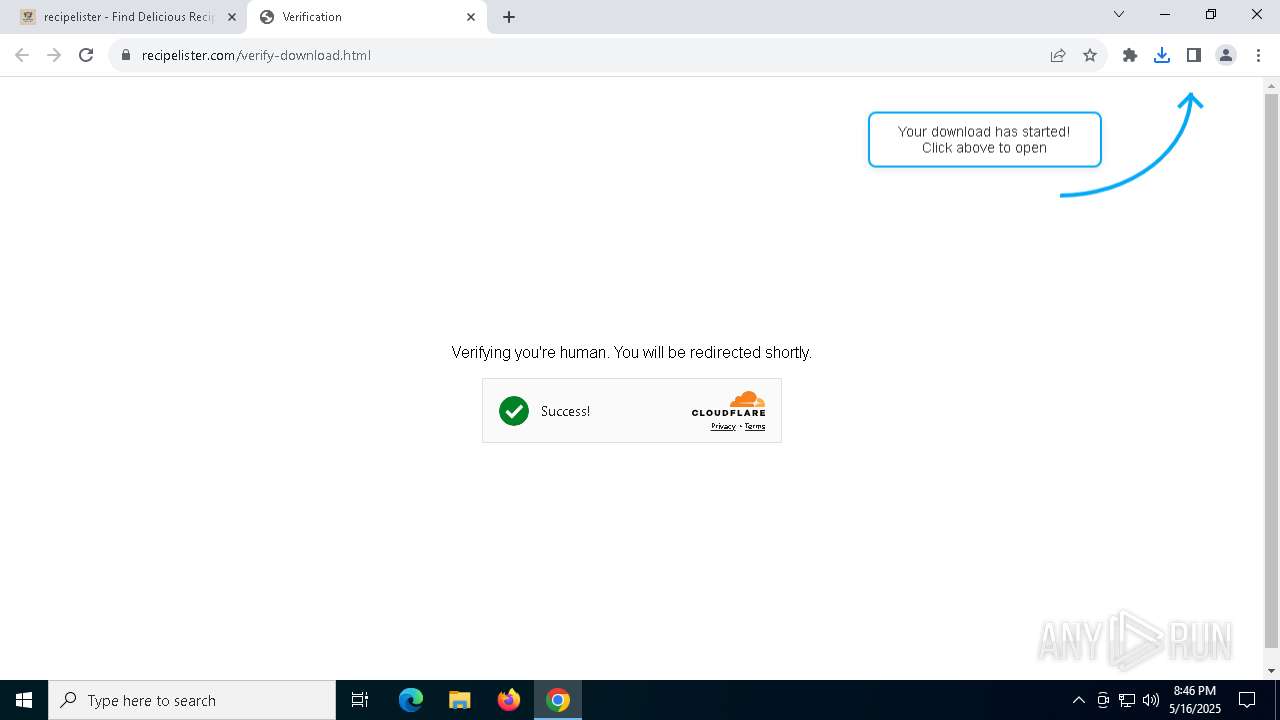
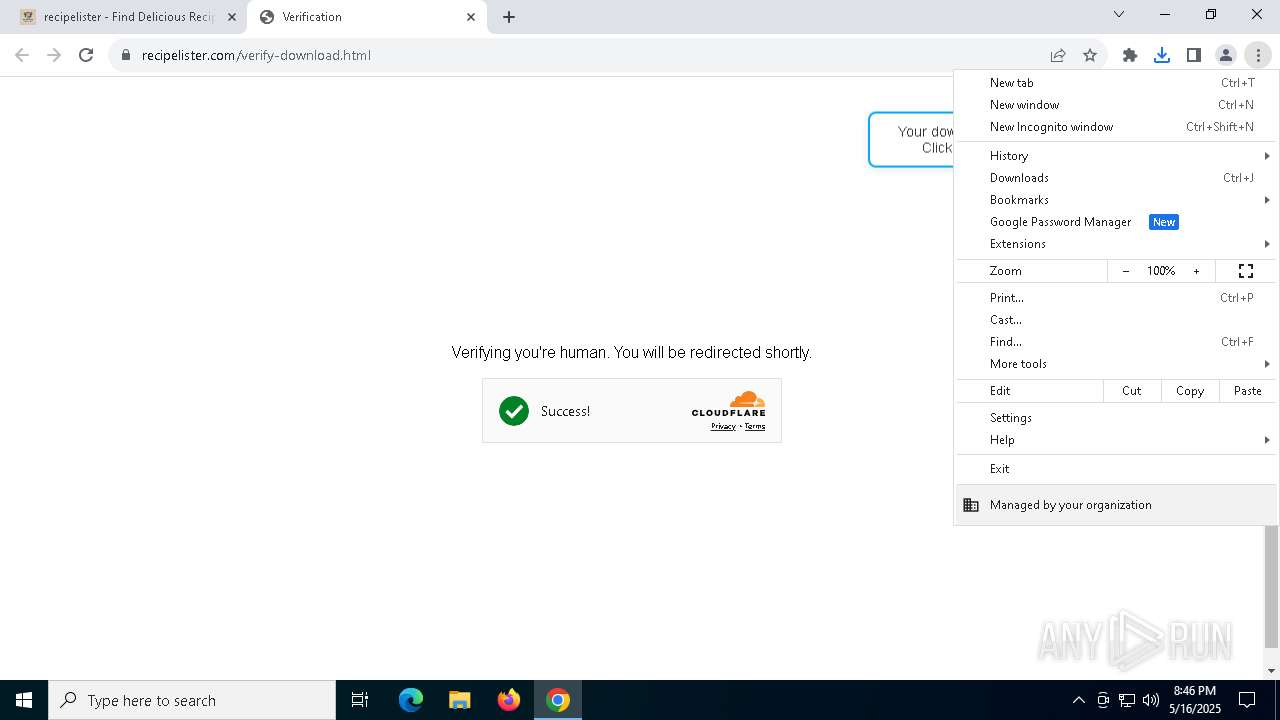
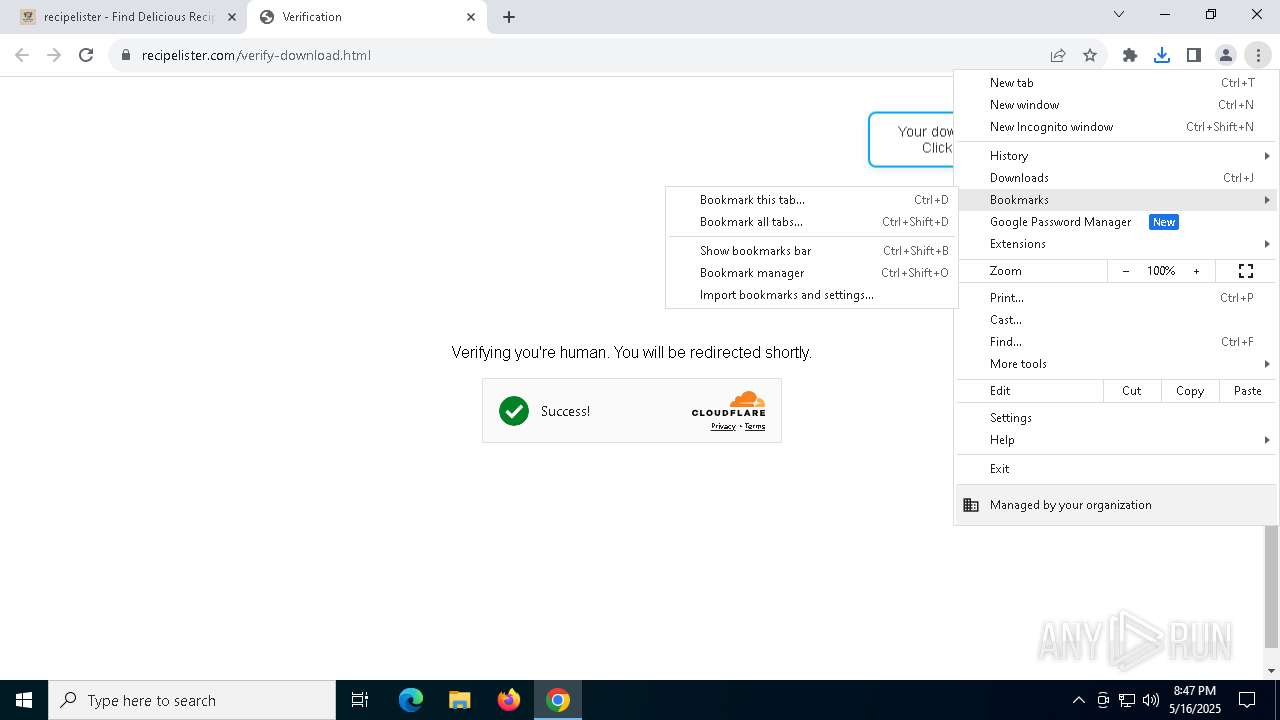
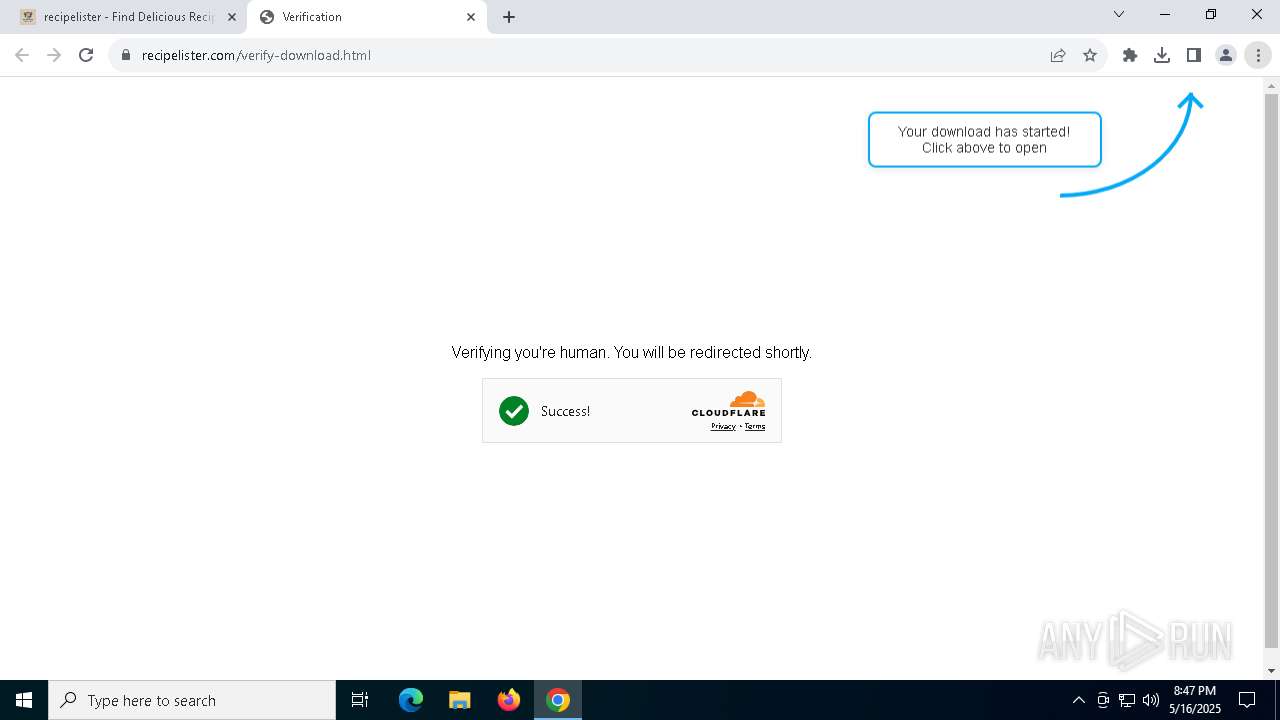
7316 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
7316 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |