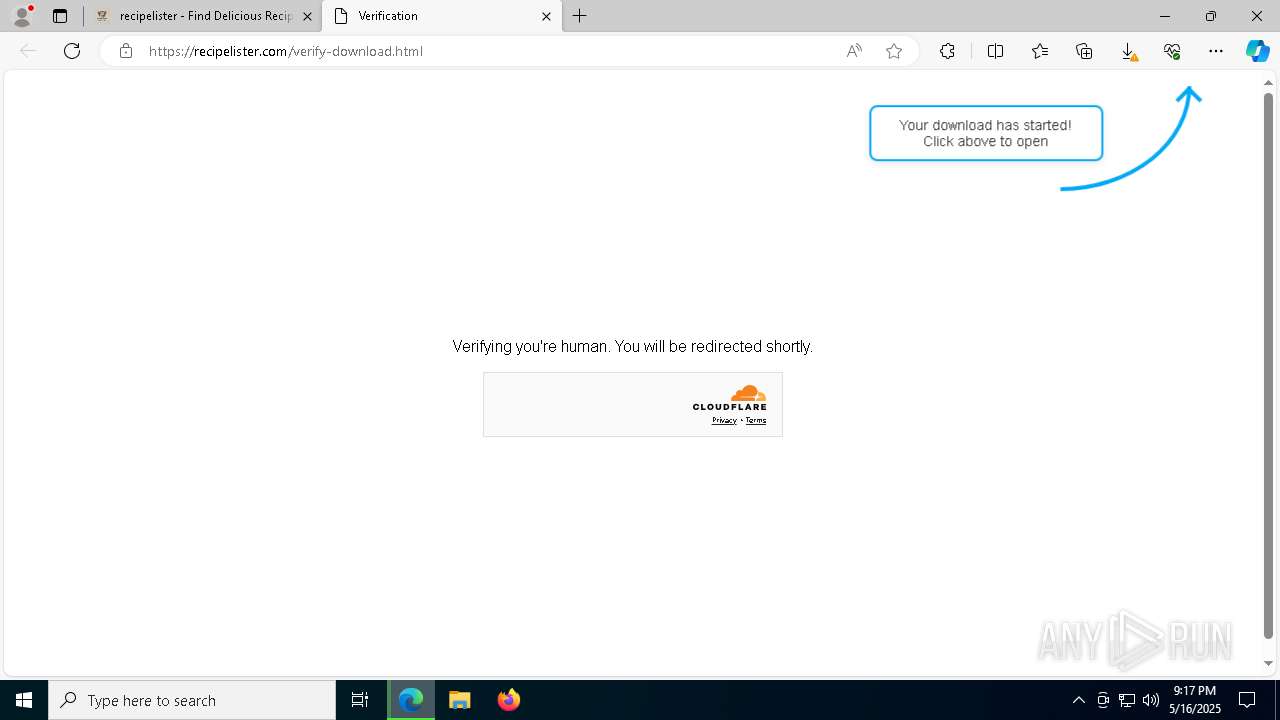
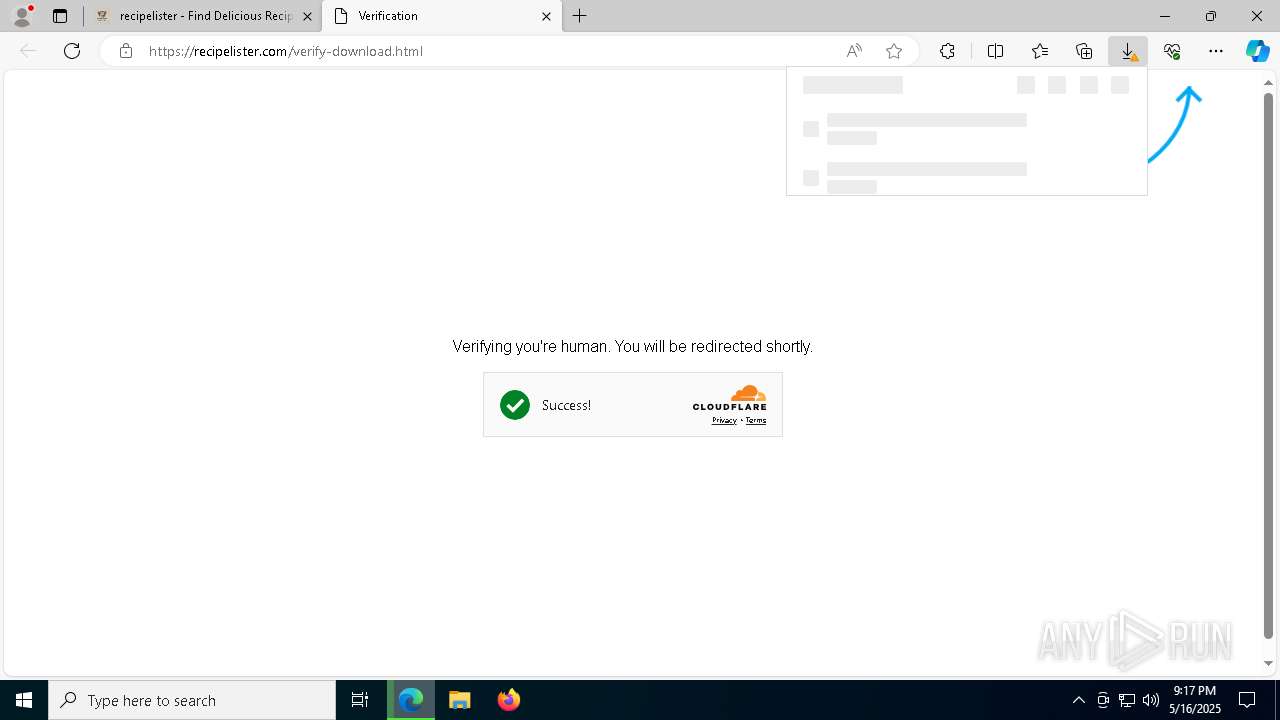
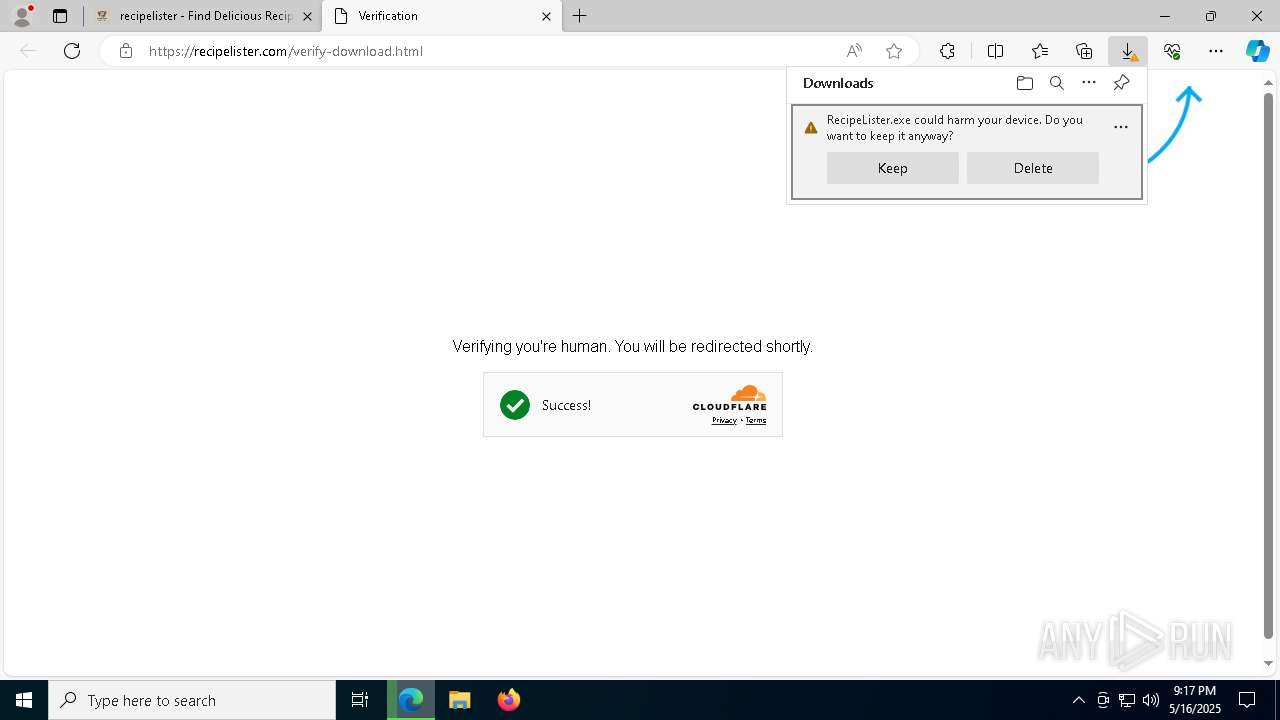
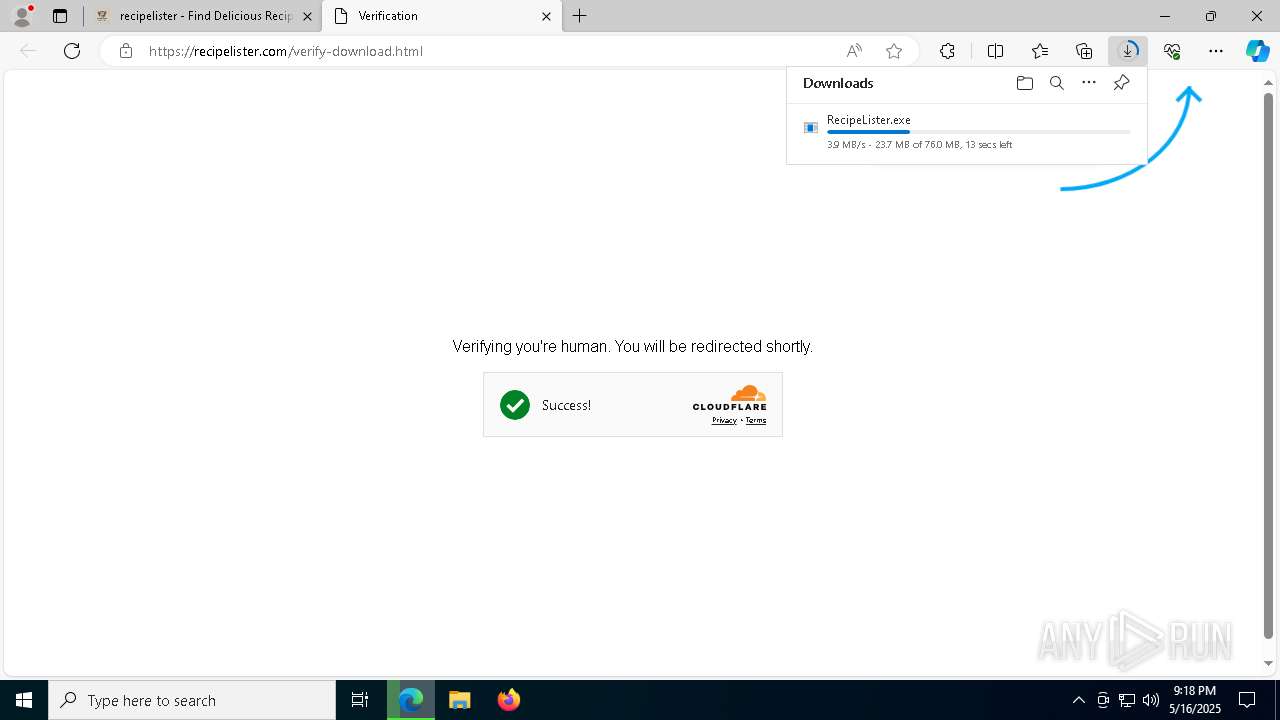
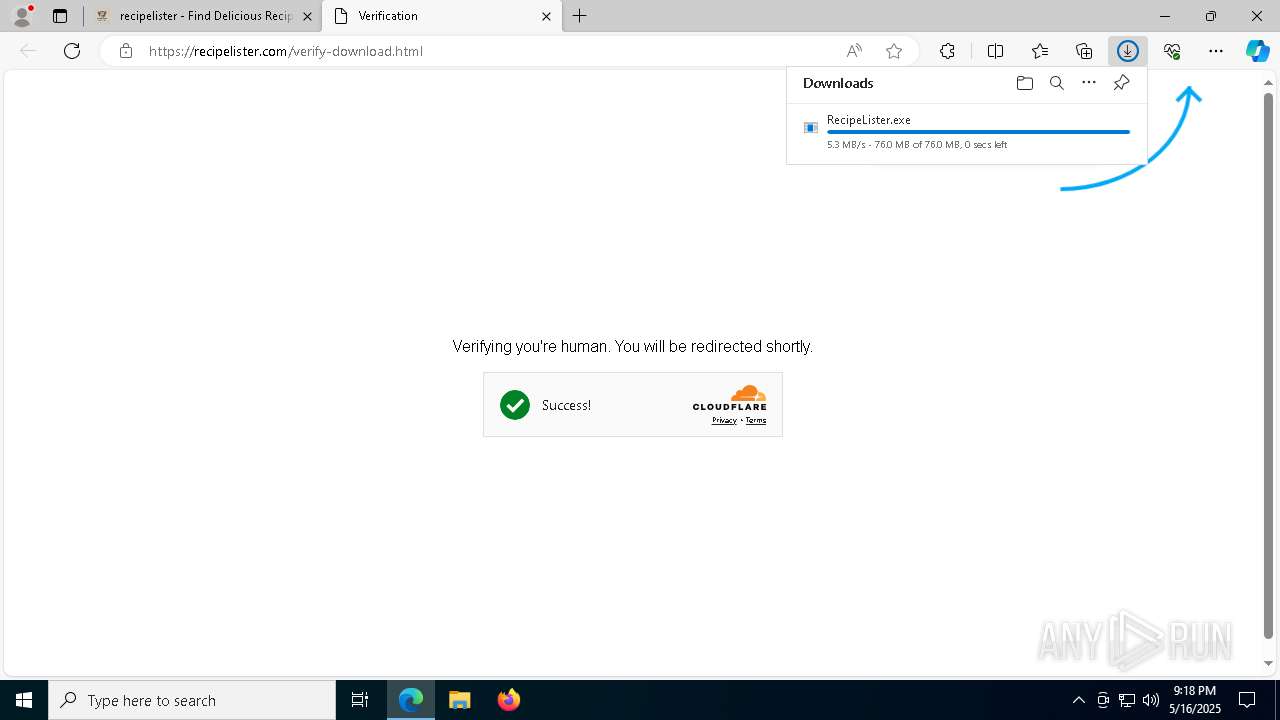
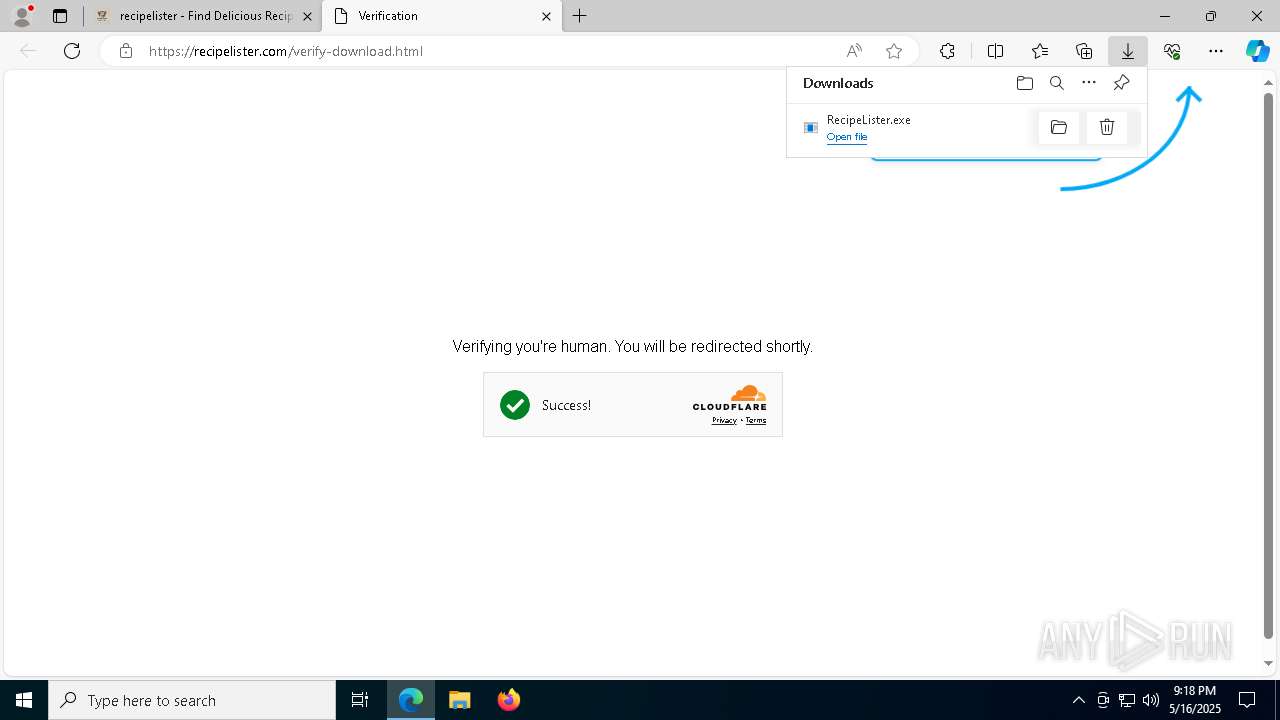
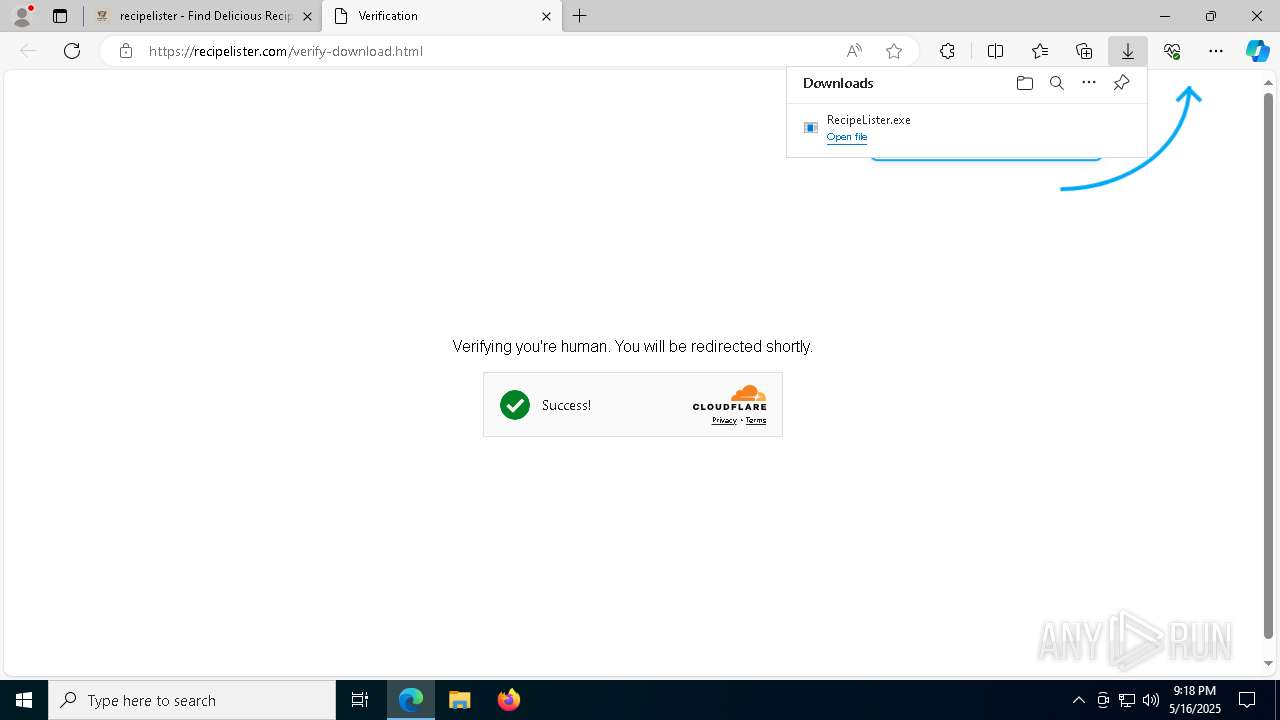
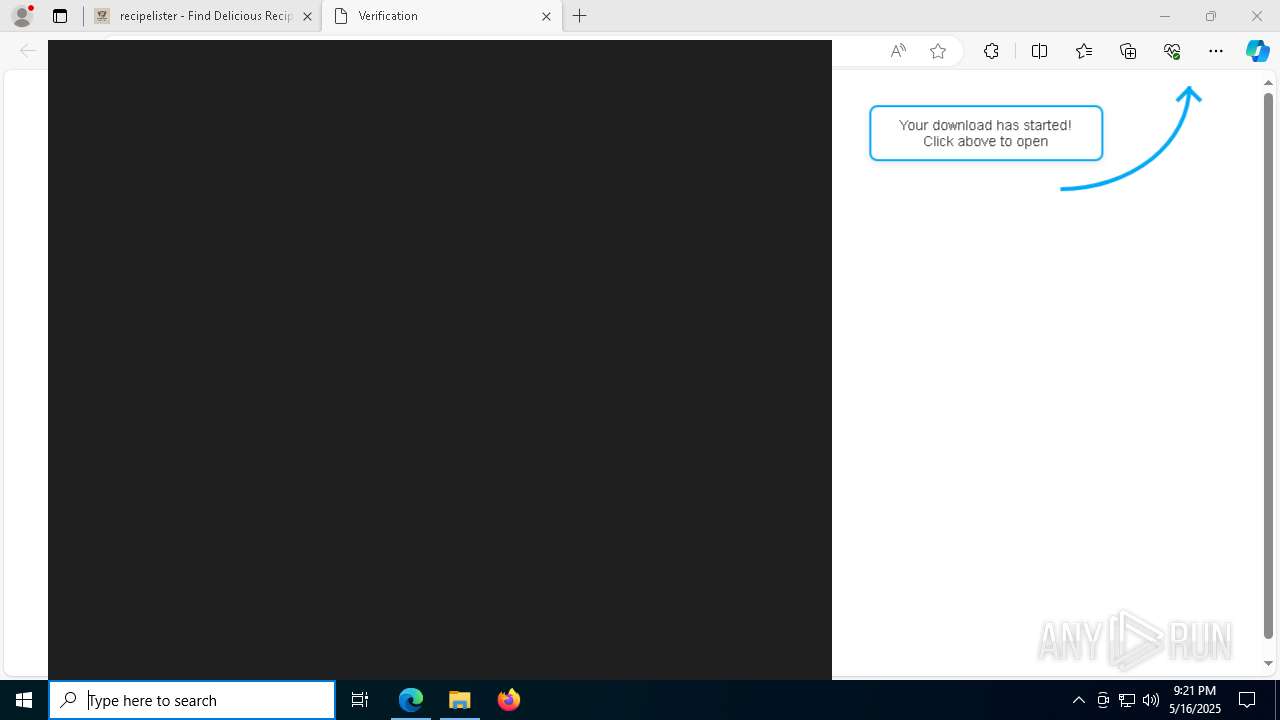
| URL: | recipelister.com |
| Full analysis: | https://app.any.run/tasks/459a8e45-b349-4125-b54a-f0666d9adc1d |
| Verdict: | Malicious activity |
| Analysis date: | May 16, 2025, 21:17:27 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
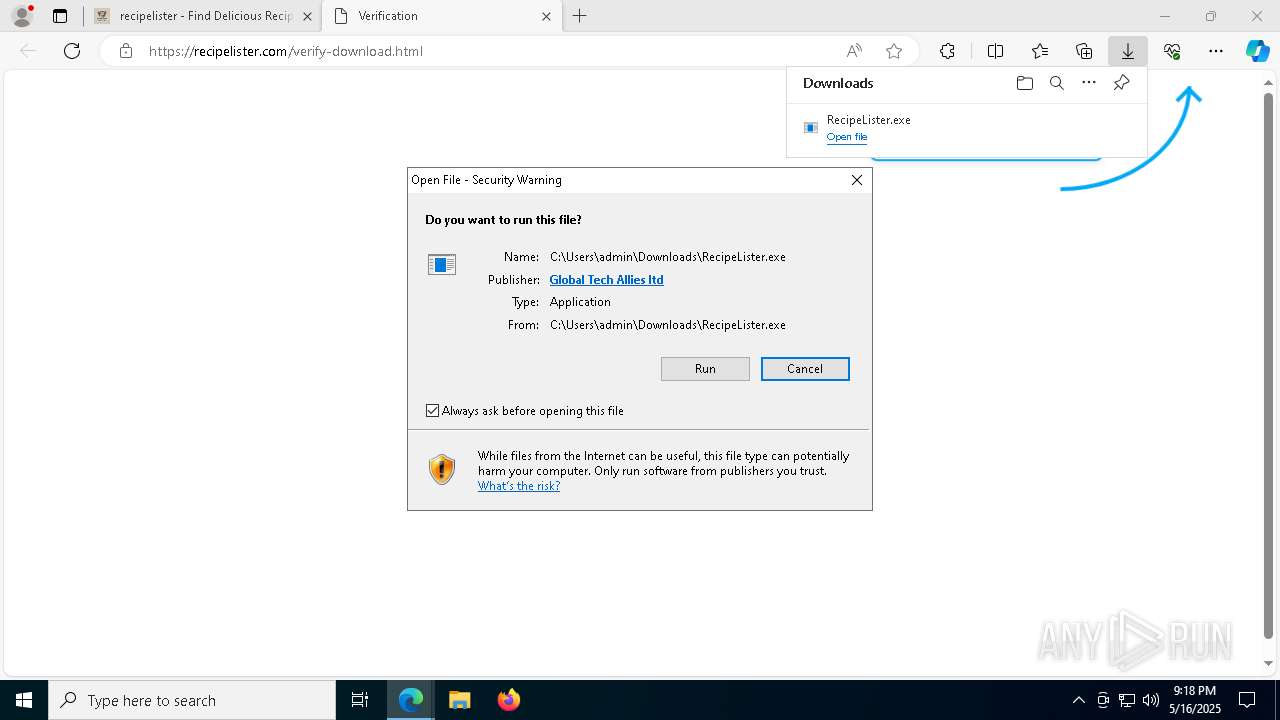
| MD5: | F154E393EA8A5A105D972C66FE65DACA |
| SHA1: | D7787F11559B38FDFBF2D45C1EB3ED61EEC7033C |
| SHA256: | 623D191DCED7BF2FED9E5239F77A5D0CFE1766E8EDCF46A1CE86E40B1B702CE7 |
| SSDEEP: | 3:wtHpI:Sm |
MALICIOUS
Executing a file with an untrusted certificate
- RecipeLister.exe (PID: 3300)
SUSPICIOUS
The process creates files with name similar to system file names
- RecipeLister.exe (PID: 3300)
Executable content was dropped or overwritten
- RecipeLister.exe (PID: 3300)
Malware-specific behavior (creating "System.dll" in Temp)
- RecipeLister.exe (PID: 3300)
Process drops legitimate windows executable
- RecipeLister.exe (PID: 3300)
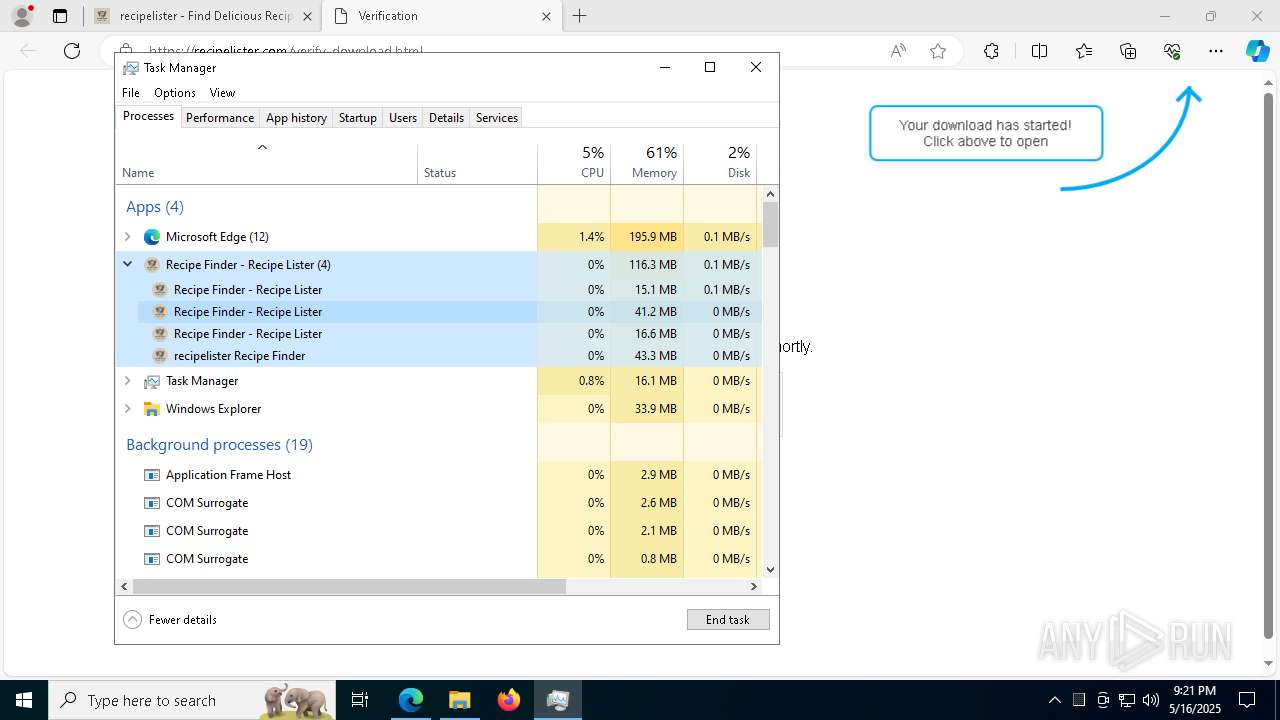
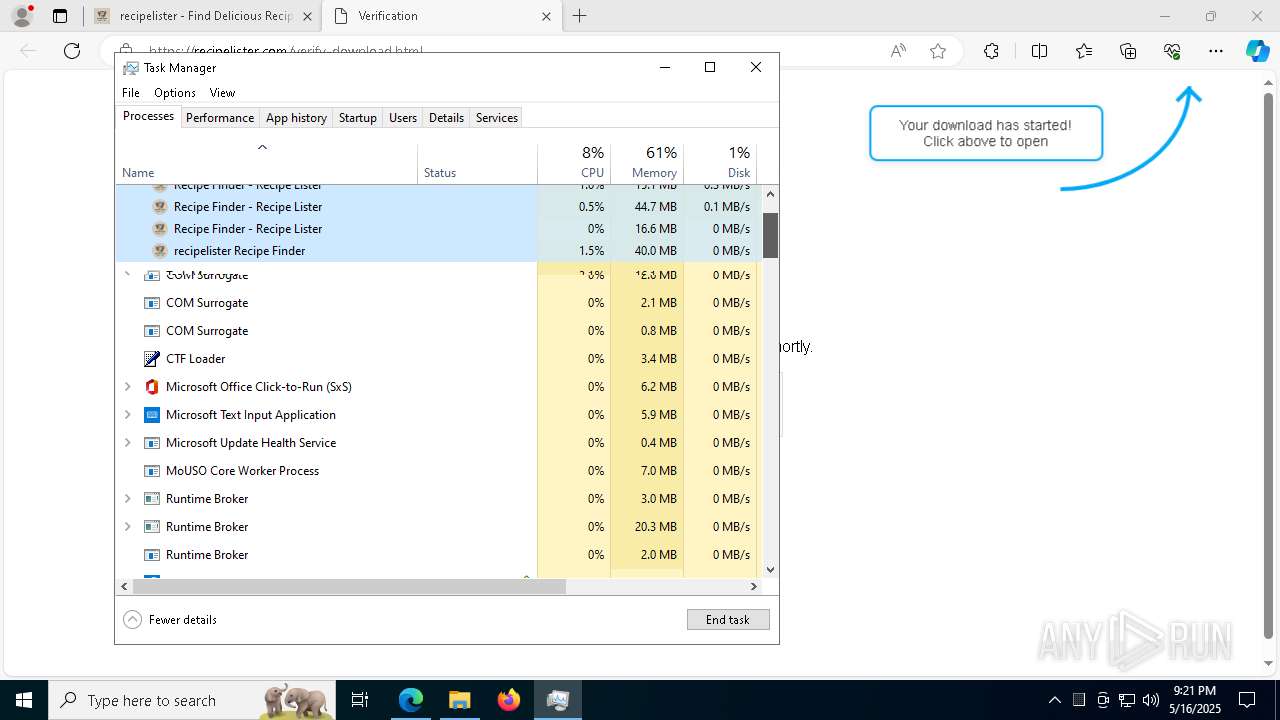
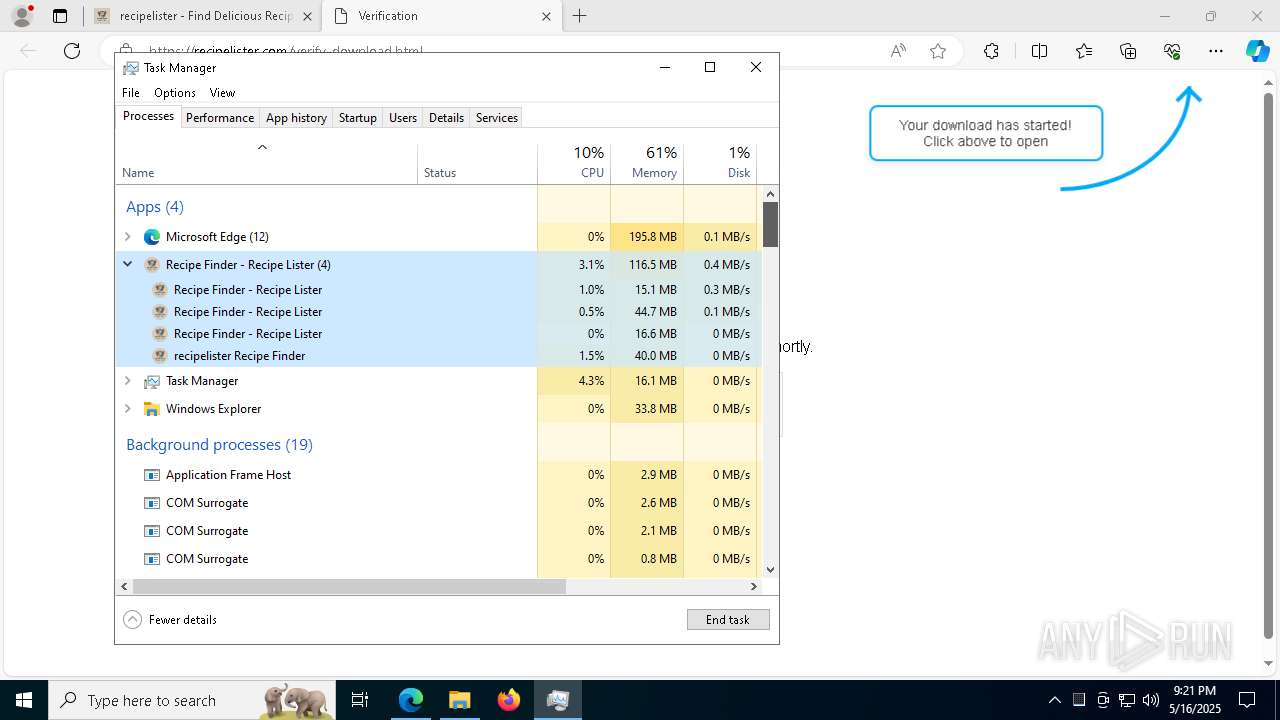
Application launched itself
- Recipe Finder - Recipe Lister.exe (PID: 2984)
There is functionality for taking screenshot (YARA)
- RecipeLister.exe (PID: 3300)
- Recipe Finder - Recipe Lister.exe (PID: 4756)
Reads security settings of Internet Explorer
- Recipe Finder - Recipe Lister.exe (PID: 2984)
- RecipeLister.exe (PID: 3300)
Drops 7-zip archiver for unpacking
- RecipeLister.exe (PID: 3300)
INFO
Checks supported languages
- identity_helper.exe (PID: 1088)
- RecipeLister.exe (PID: 3300)
- Recipe Finder - Recipe Lister.exe (PID: 4756)
- Recipe Finder - Recipe Lister.exe (PID: 6032)
- Recipe Finder - Recipe Lister.exe (PID: 7856)
- Recipe Finder - Recipe Lister.exe (PID: 6436)
- Recipe Finder - Recipe Lister.exe (PID: 2984)
Application launched itself
- msedge.exe (PID: 7436)
- AcroCEF.exe (PID: 6964)
- Acrobat.exe (PID: 5428)
Reads product name
- Recipe Finder - Recipe Lister.exe (PID: 2984)
Reads the computer name
- identity_helper.exe (PID: 1088)
- Recipe Finder - Recipe Lister.exe (PID: 4756)
- Recipe Finder - Recipe Lister.exe (PID: 6032)
- RecipeLister.exe (PID: 3300)
- Recipe Finder - Recipe Lister.exe (PID: 2984)
Reads Environment values
- identity_helper.exe (PID: 1088)
- Recipe Finder - Recipe Lister.exe (PID: 2984)
Executable content was dropped or overwritten
- msedge.exe (PID: 7436)
- msedge.exe (PID: 8852)
Create files in a temporary directory
- RecipeLister.exe (PID: 3300)
- Recipe Finder - Recipe Lister.exe (PID: 2984)
The sample compiled with english language support
- RecipeLister.exe (PID: 3300)
- msedge.exe (PID: 8852)
Creates files or folders in the user directory
- Recipe Finder - Recipe Lister.exe (PID: 2984)
- Recipe Finder - Recipe Lister.exe (PID: 6032)
Process checks computer location settings
- Recipe Finder - Recipe Lister.exe (PID: 2984)
- Recipe Finder - Recipe Lister.exe (PID: 7856)
- Recipe Finder - Recipe Lister.exe (PID: 6436)
Checks proxy server information
- Recipe Finder - Recipe Lister.exe (PID: 2984)
- slui.exe (PID: 1128)
Reads the machine GUID from the registry
- Recipe Finder - Recipe Lister.exe (PID: 2984)
Reads the software policy settings
- slui.exe (PID: 8184)
- slui.exe (PID: 1128)
Node.js compiler has been detected
- Recipe Finder - Recipe Lister.exe (PID: 2984)
- Recipe Finder - Recipe Lister.exe (PID: 4756)
- Recipe Finder - Recipe Lister.exe (PID: 6032)
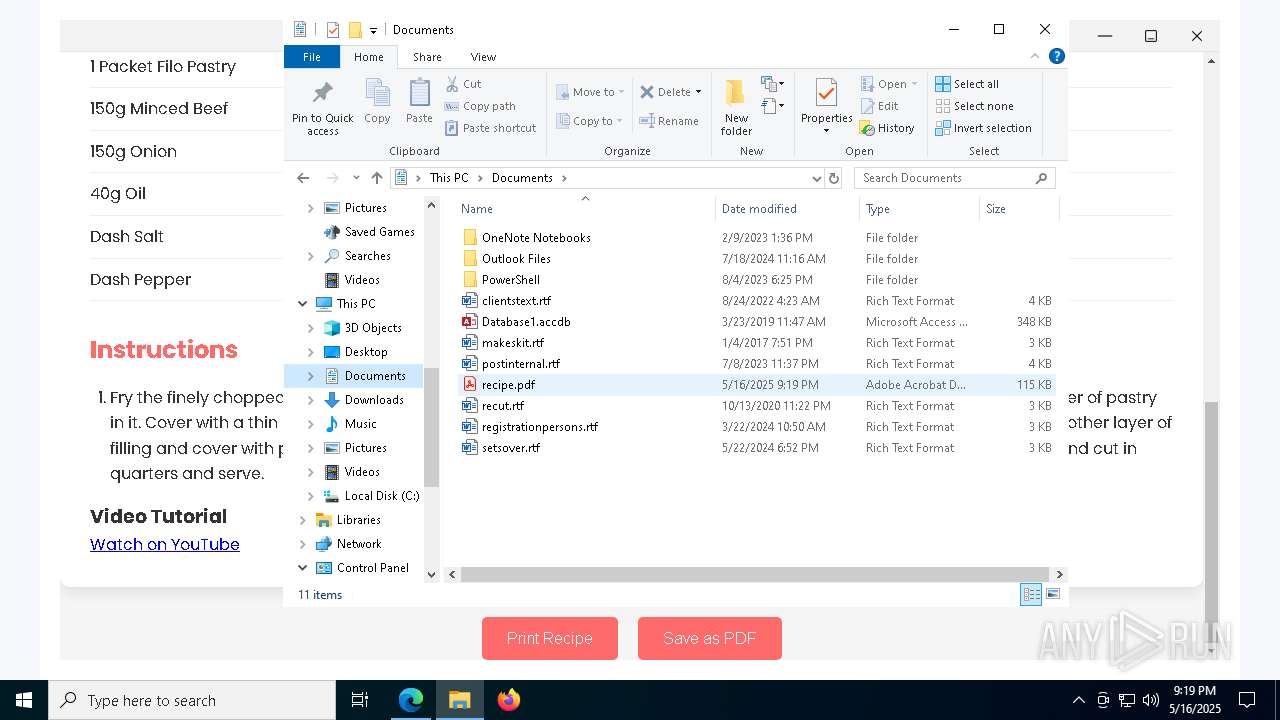
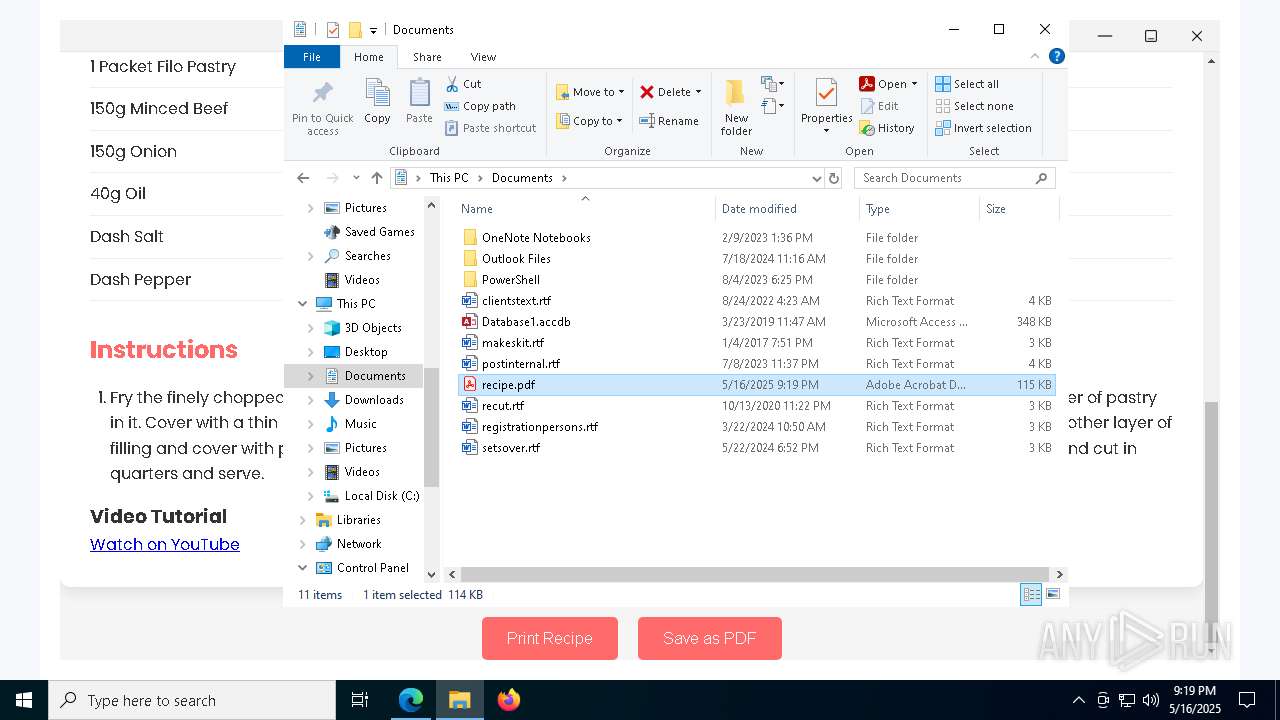
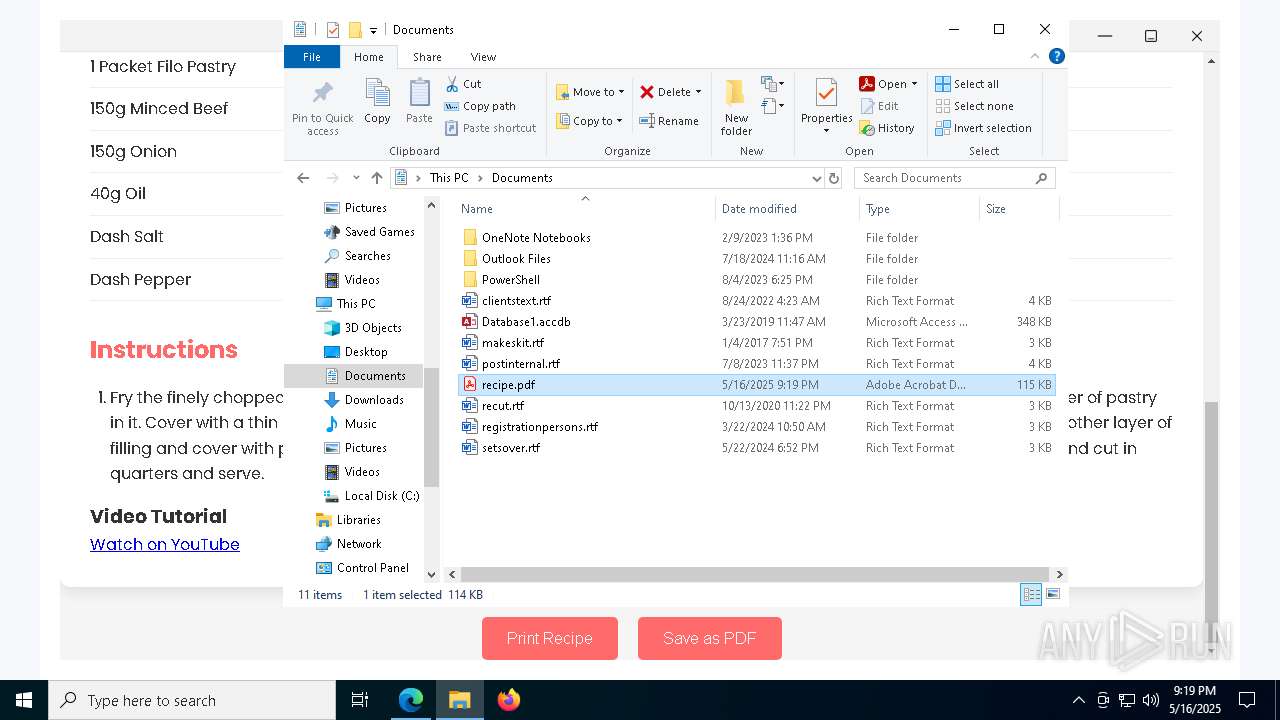
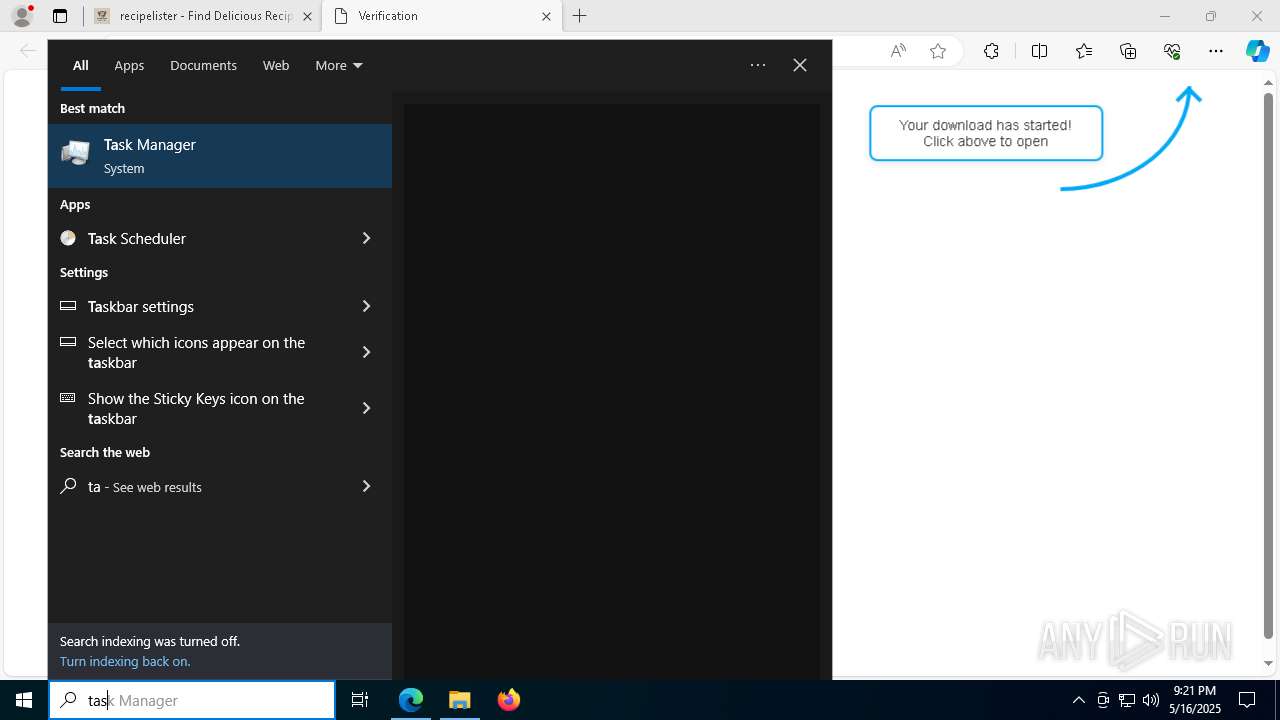
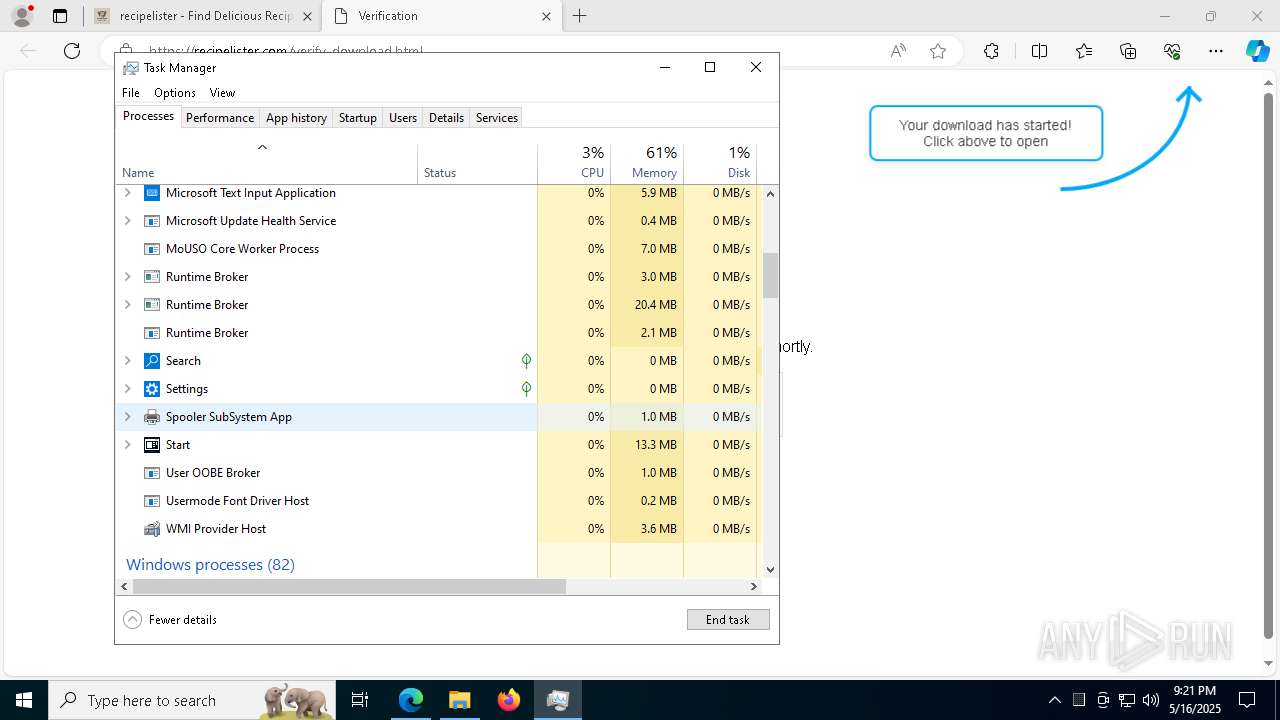
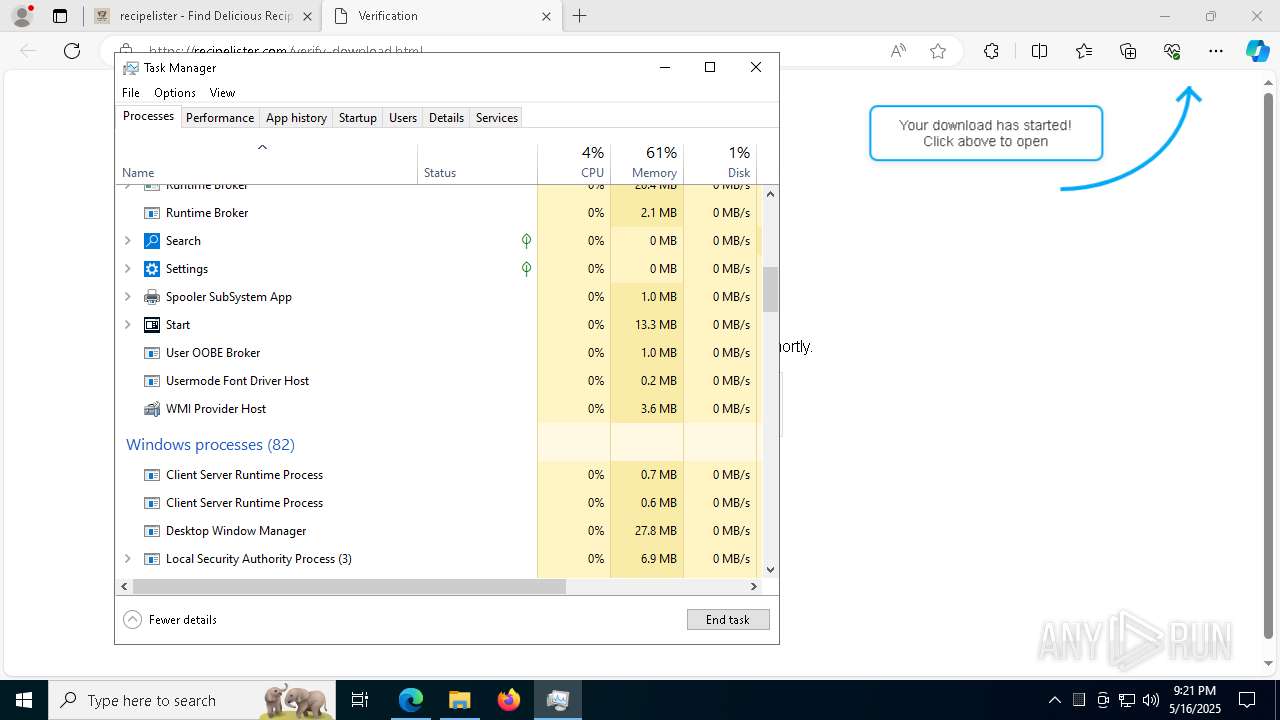
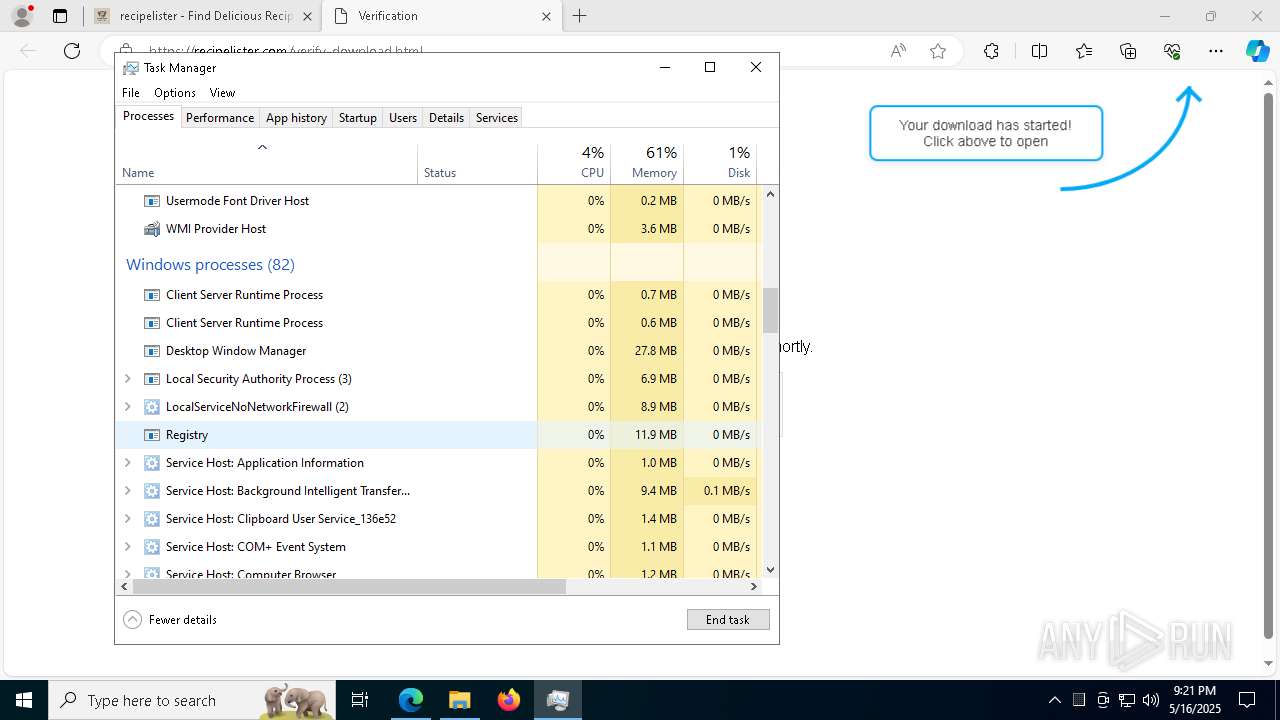
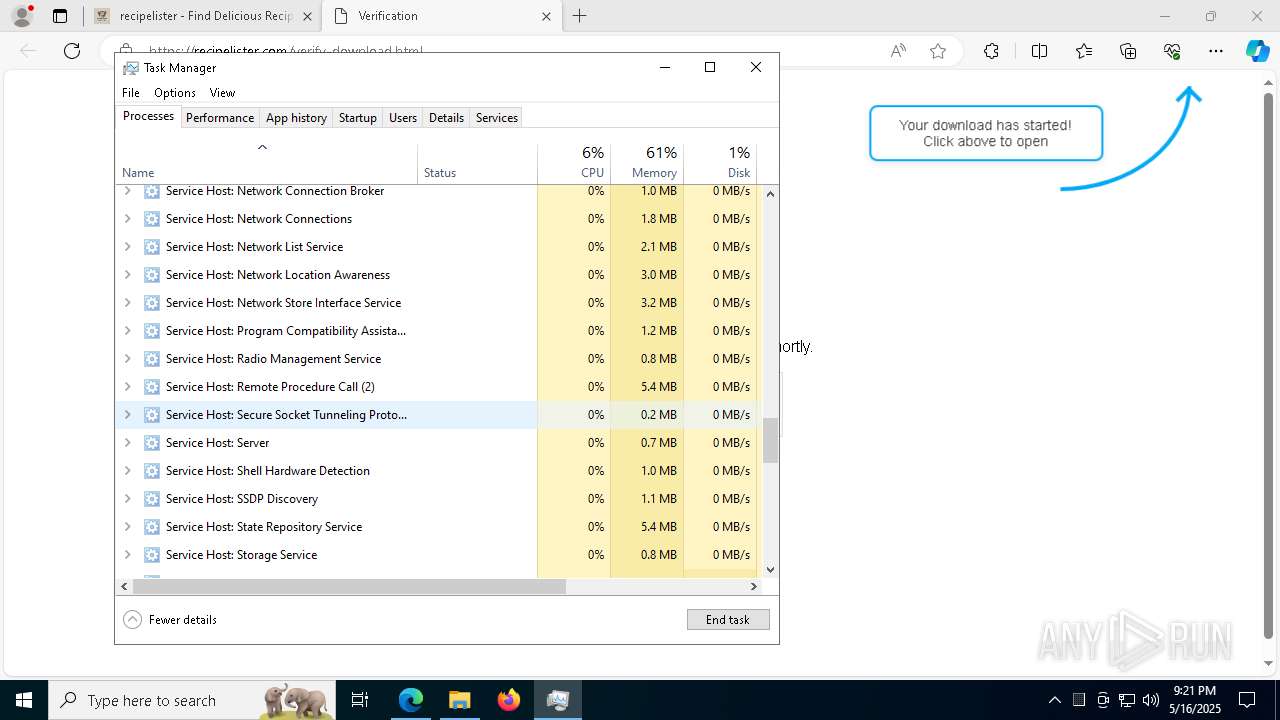
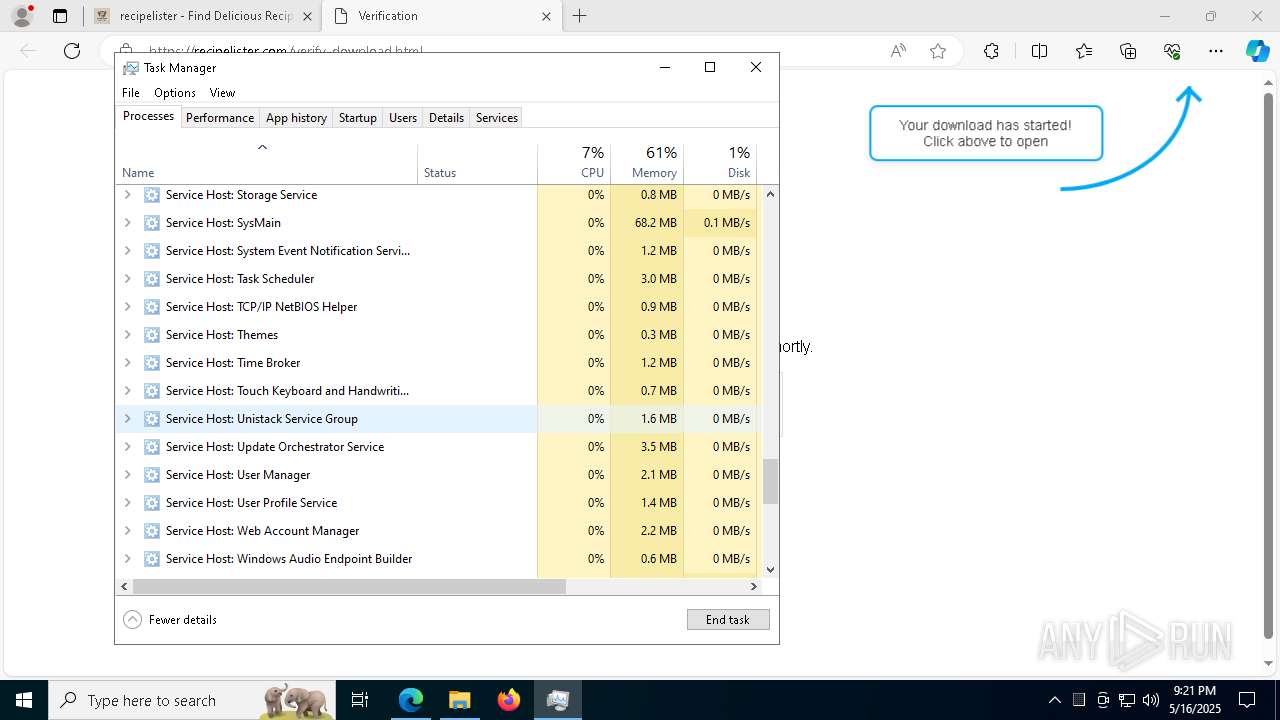
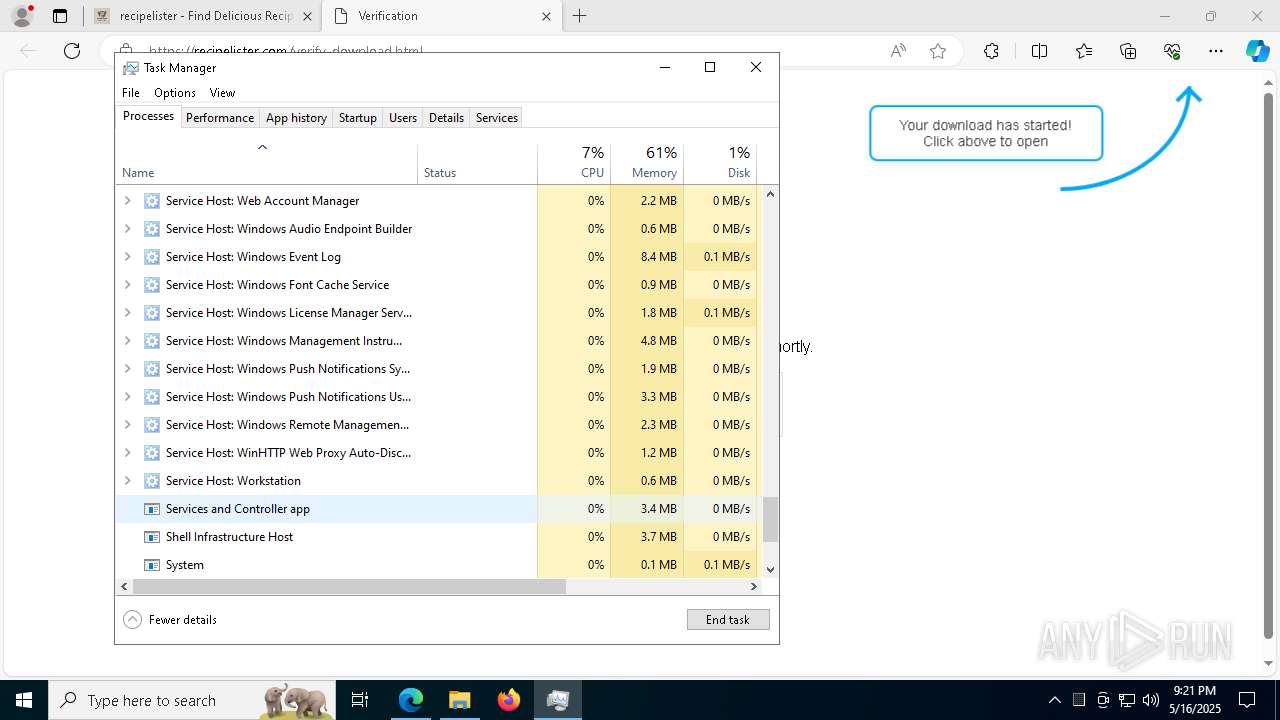
Manual execution by a user
- Acrobat.exe (PID: 5428)
- Taskmgr.exe (PID: 5796)
- Taskmgr.exe (PID: 5780)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
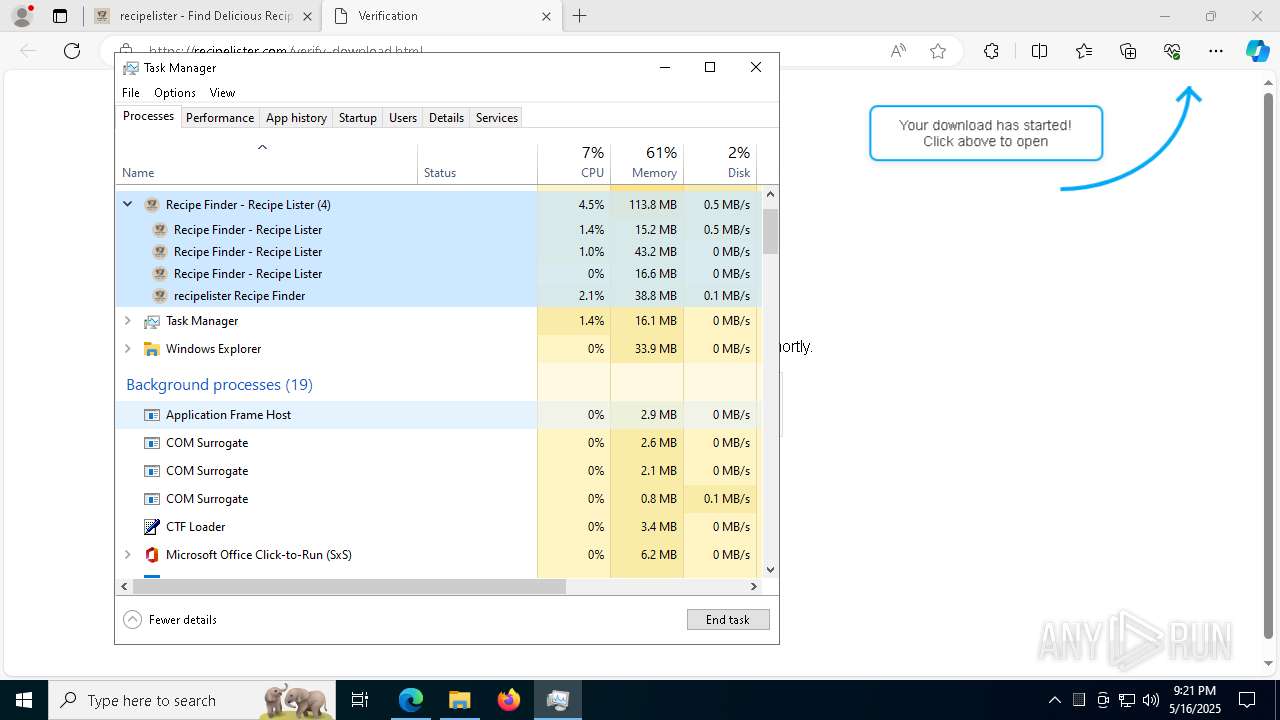
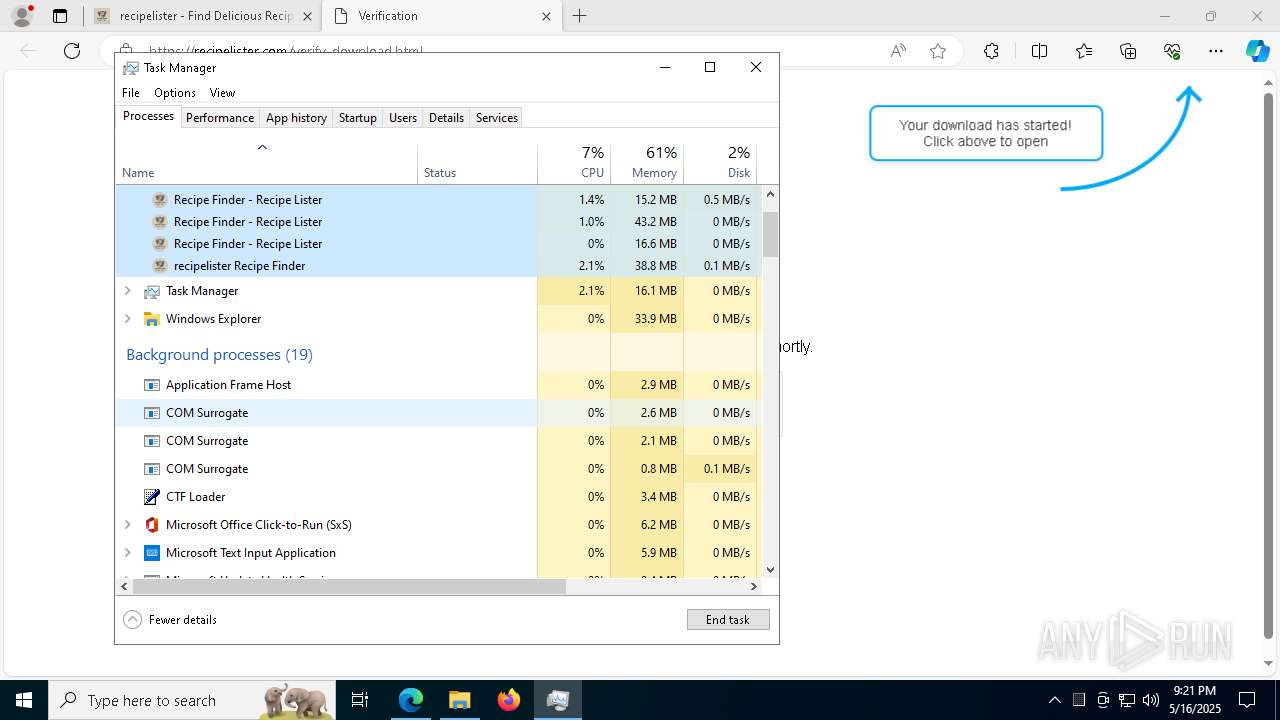
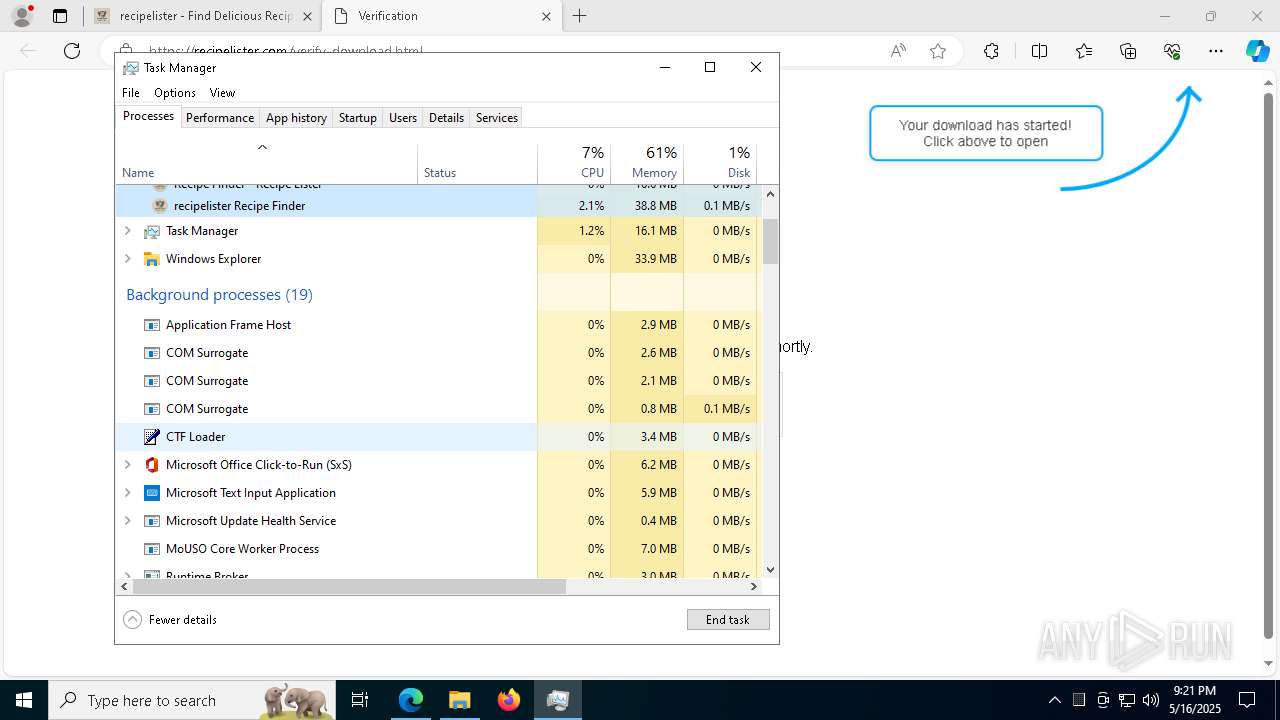
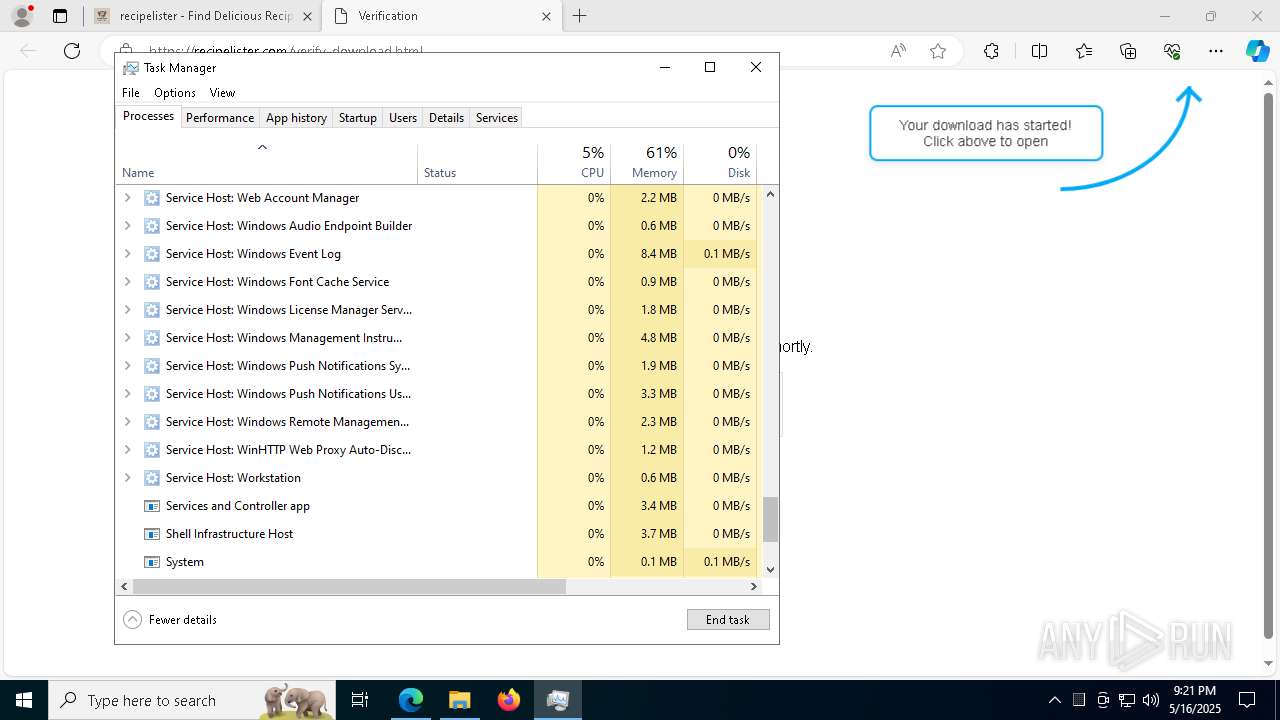
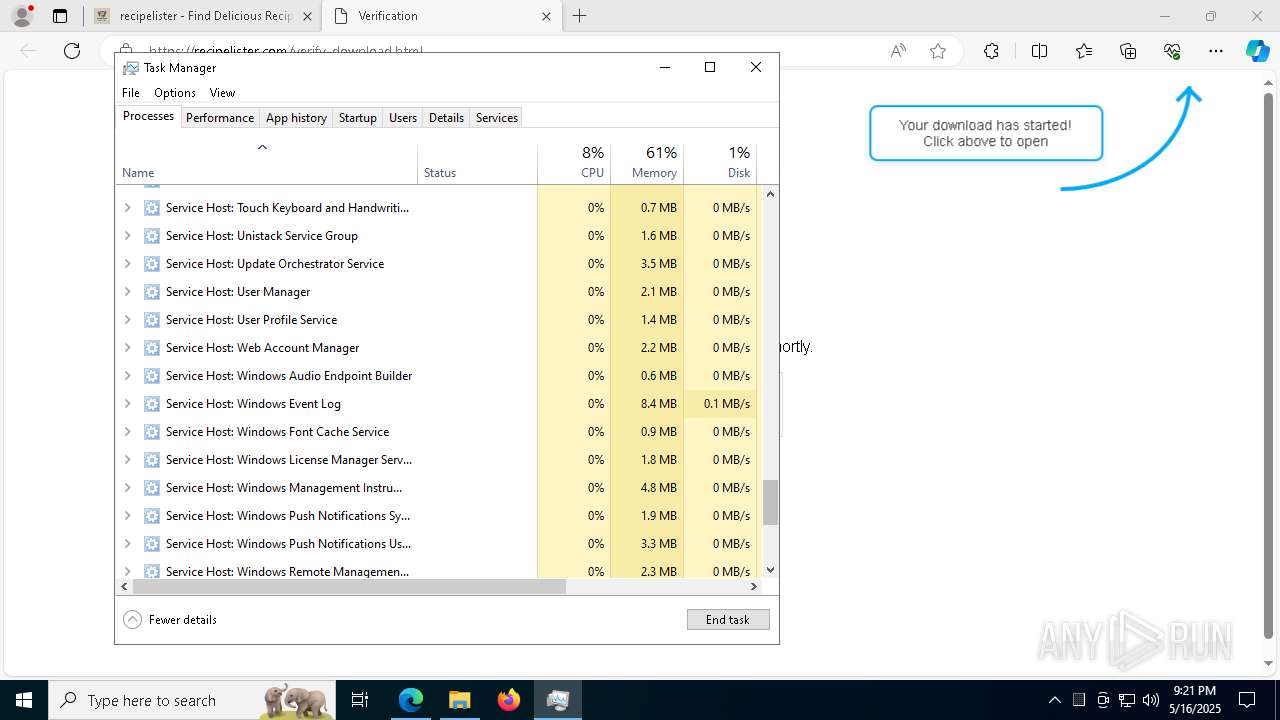
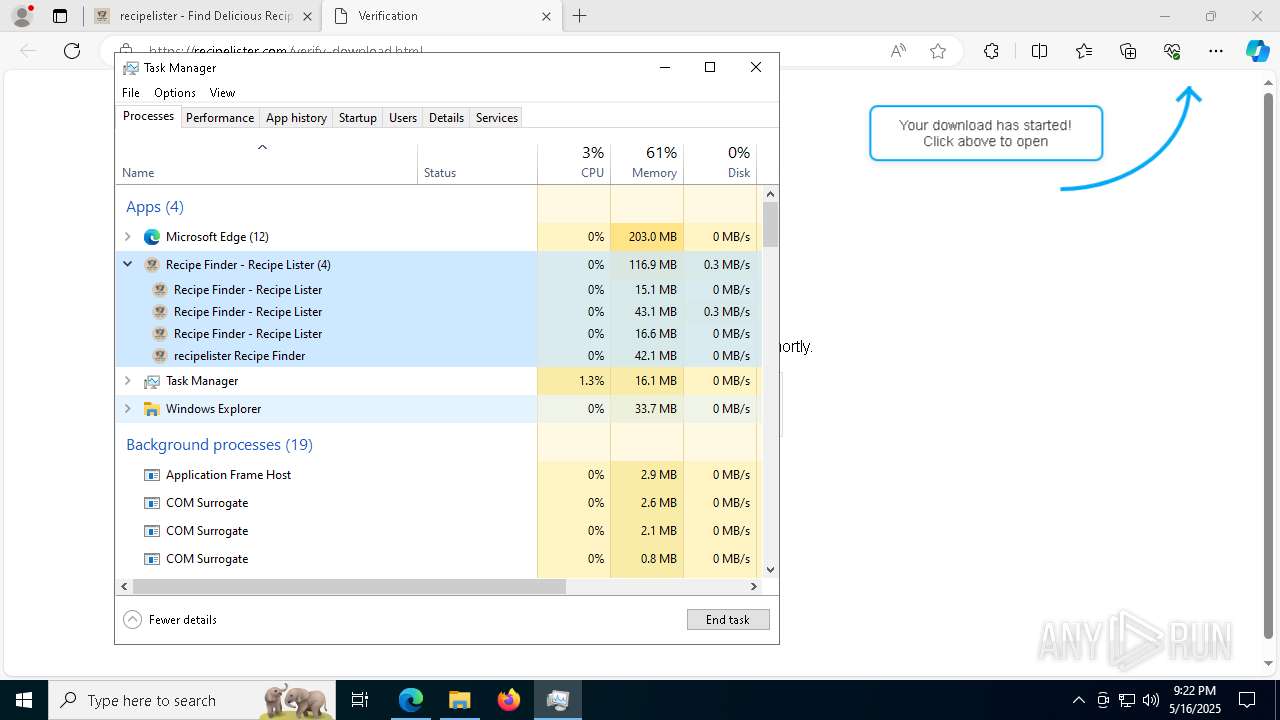
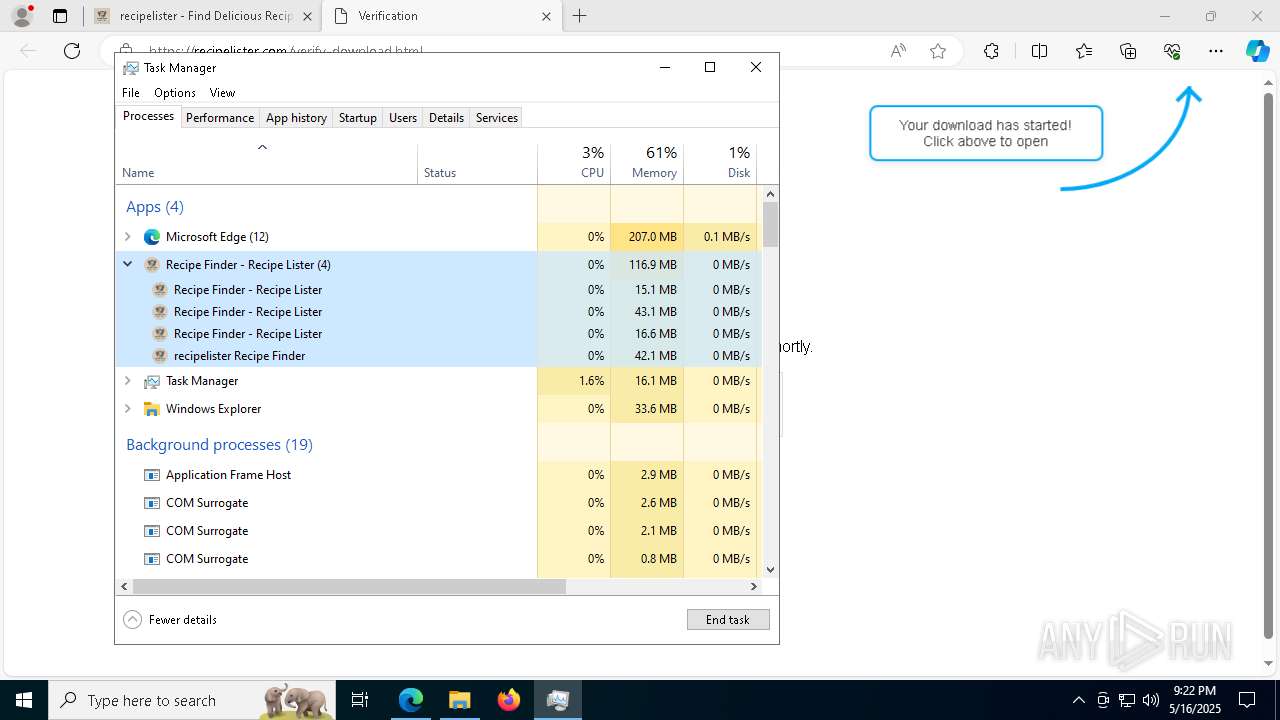
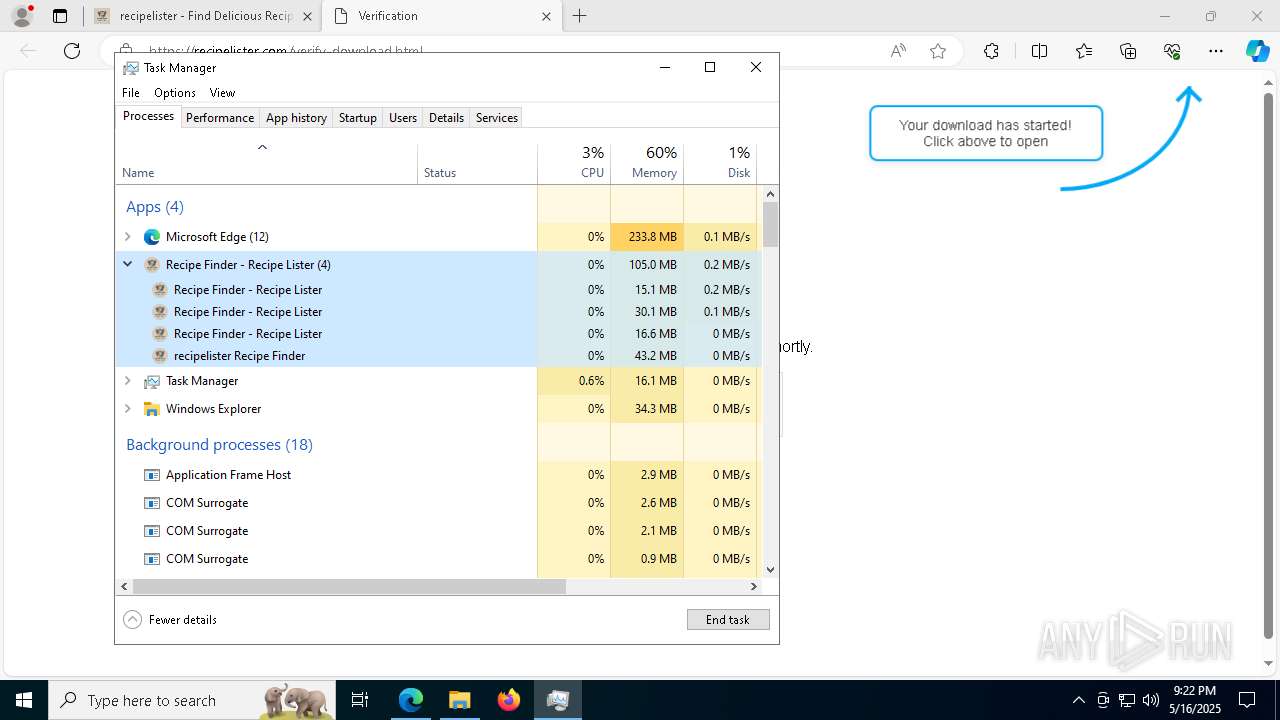
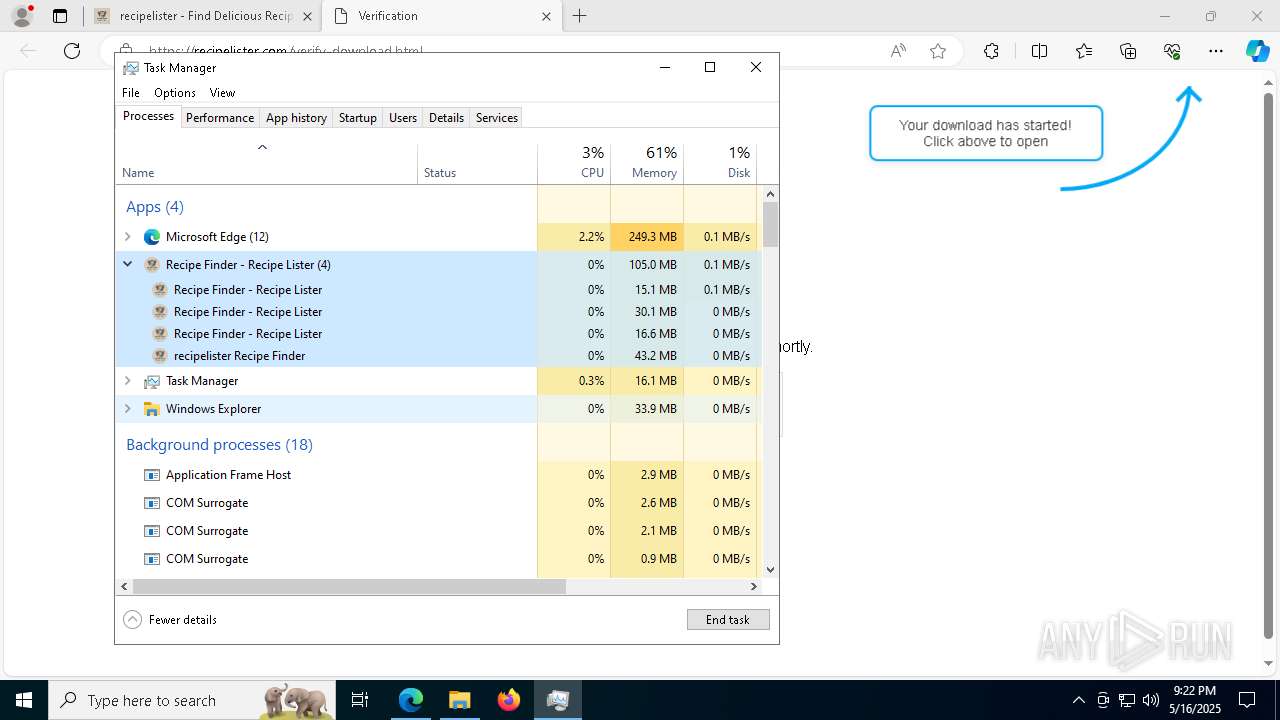
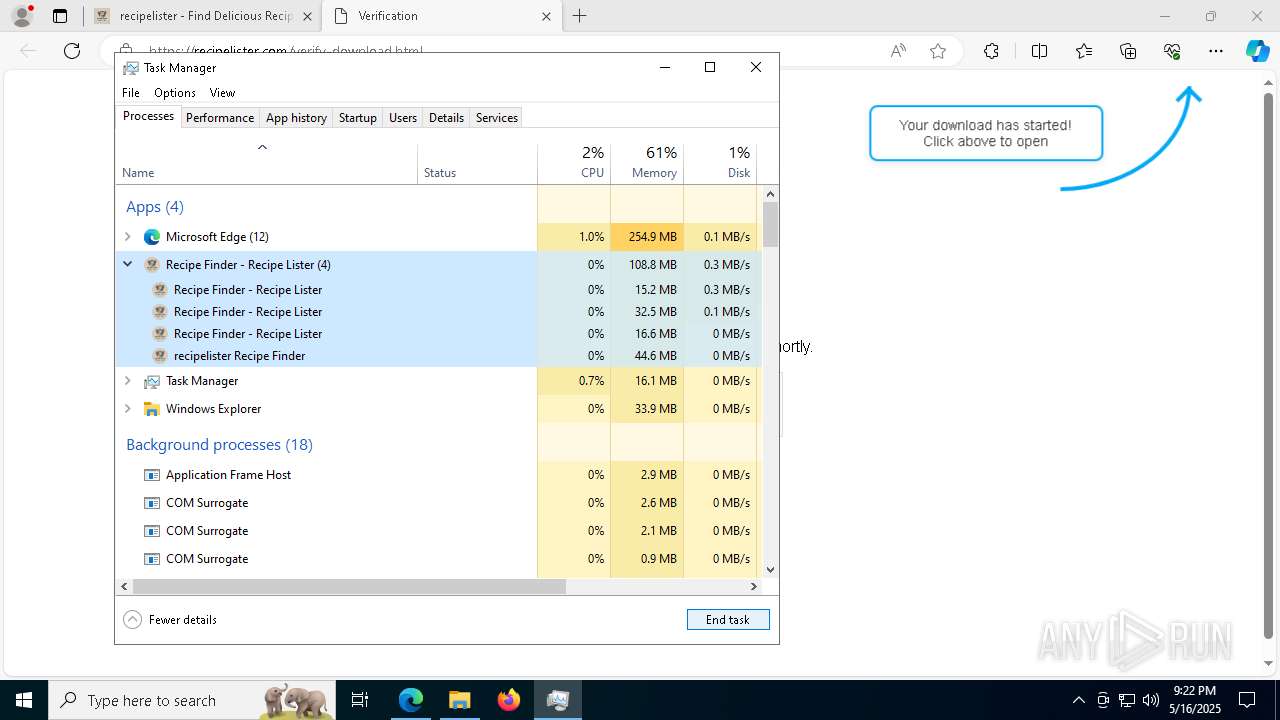
Total processes
218
Monitored processes
79
Malicious processes
1
Suspicious processes
2
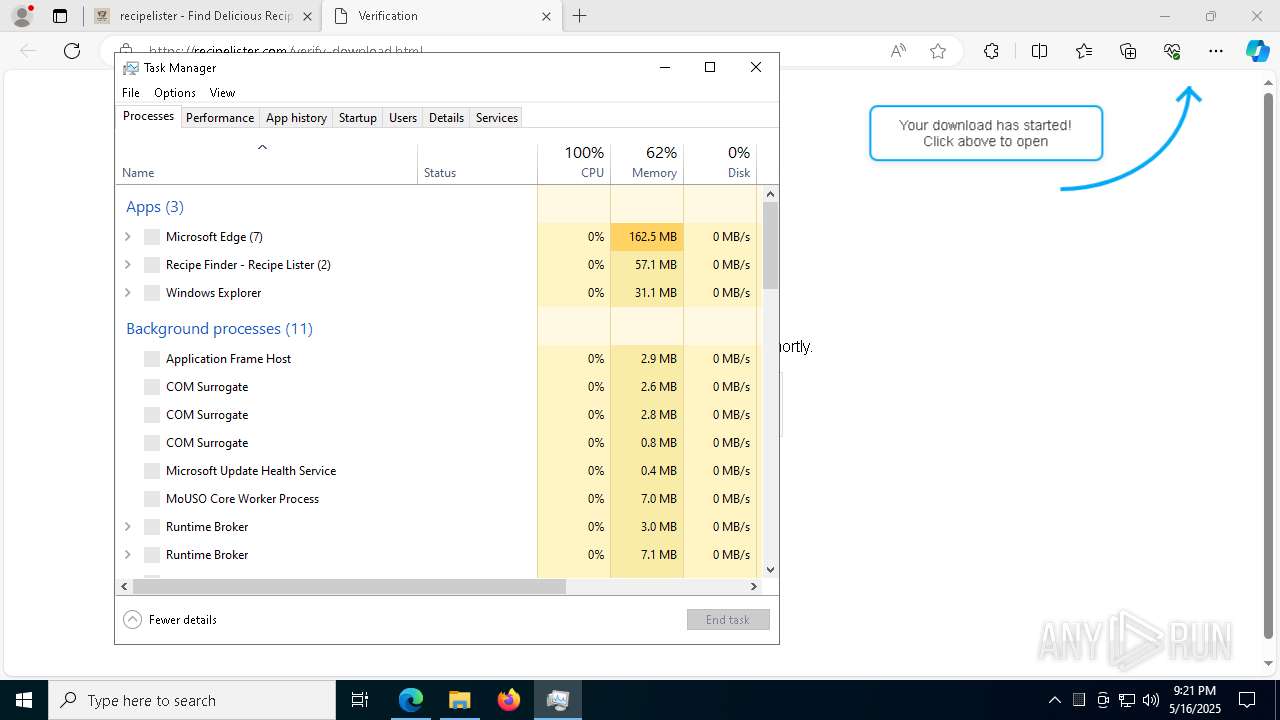
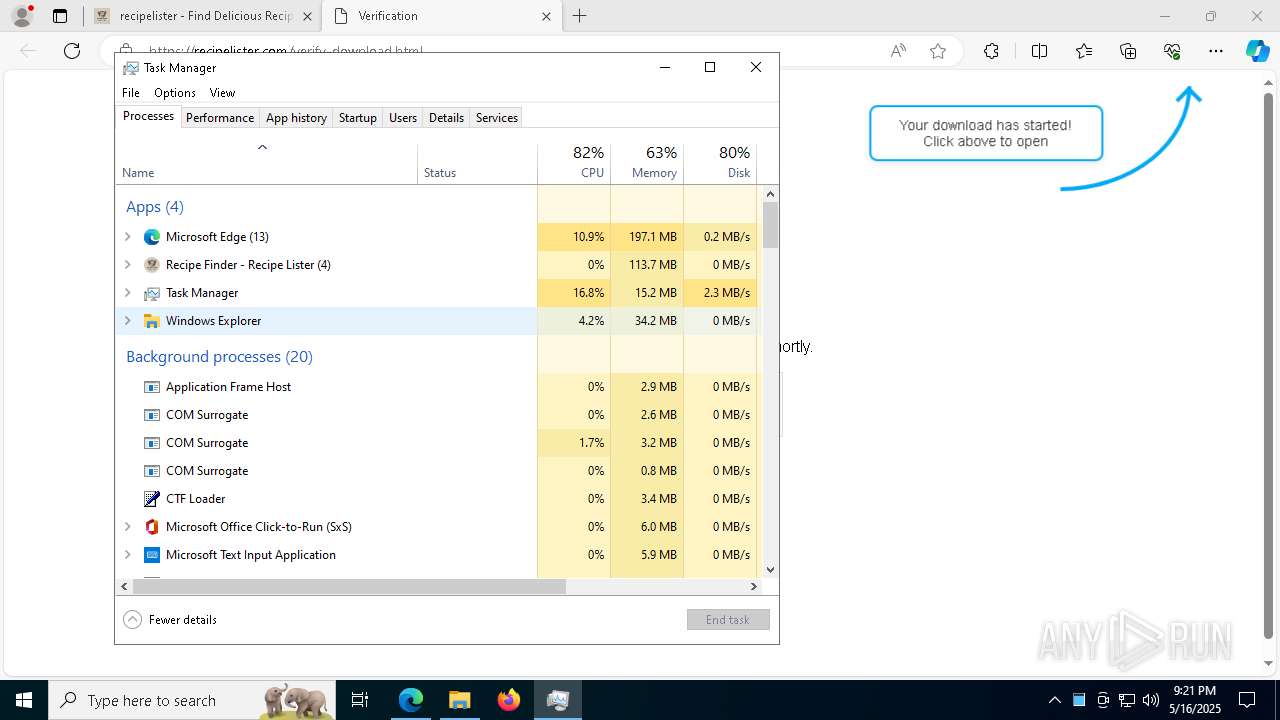
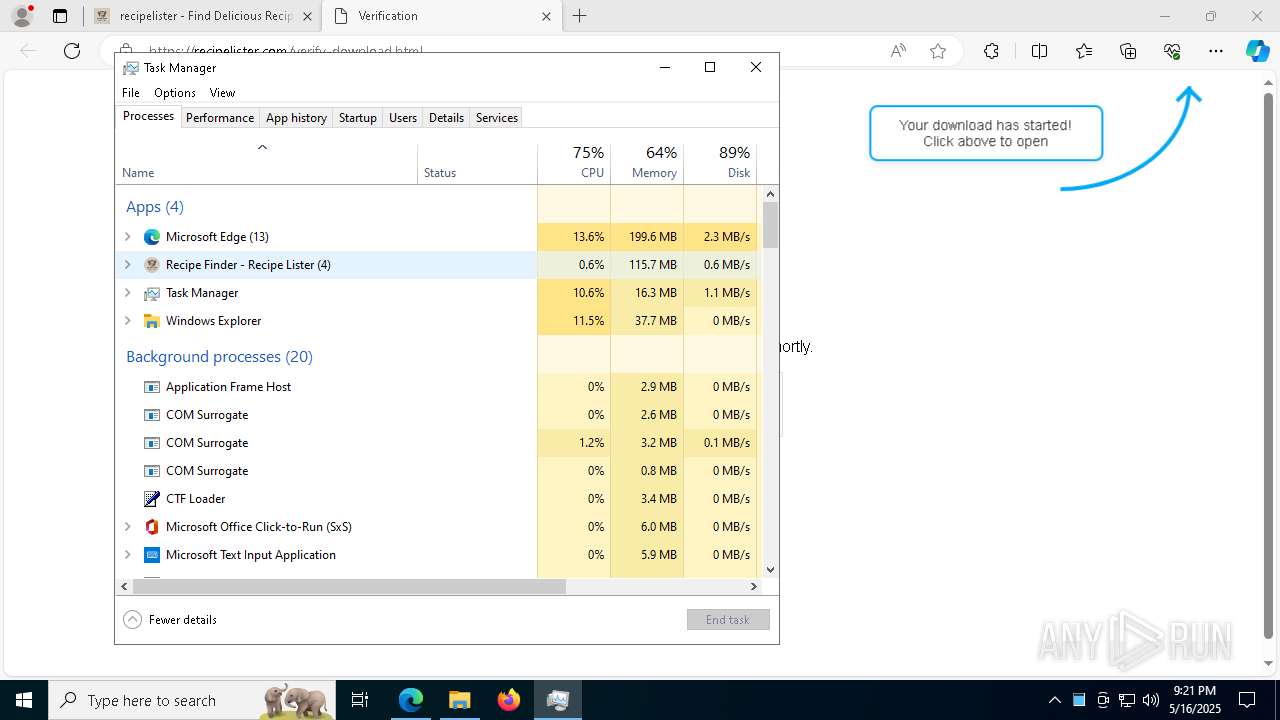
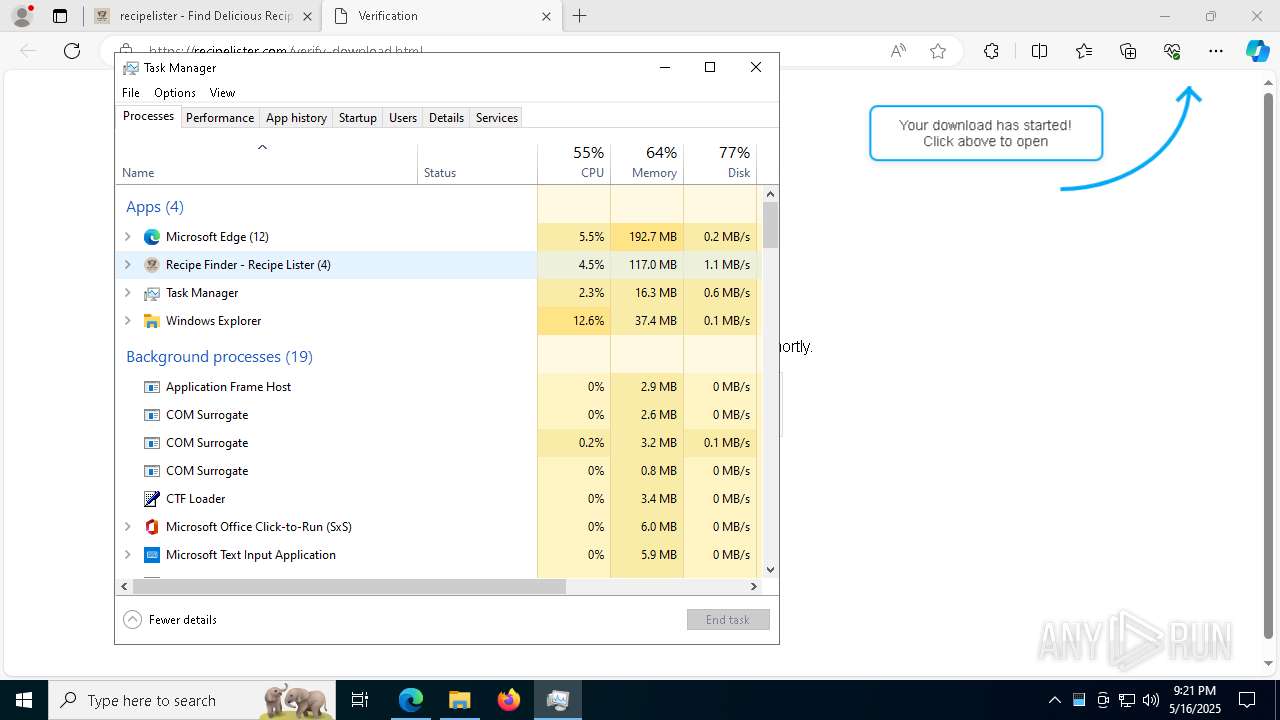
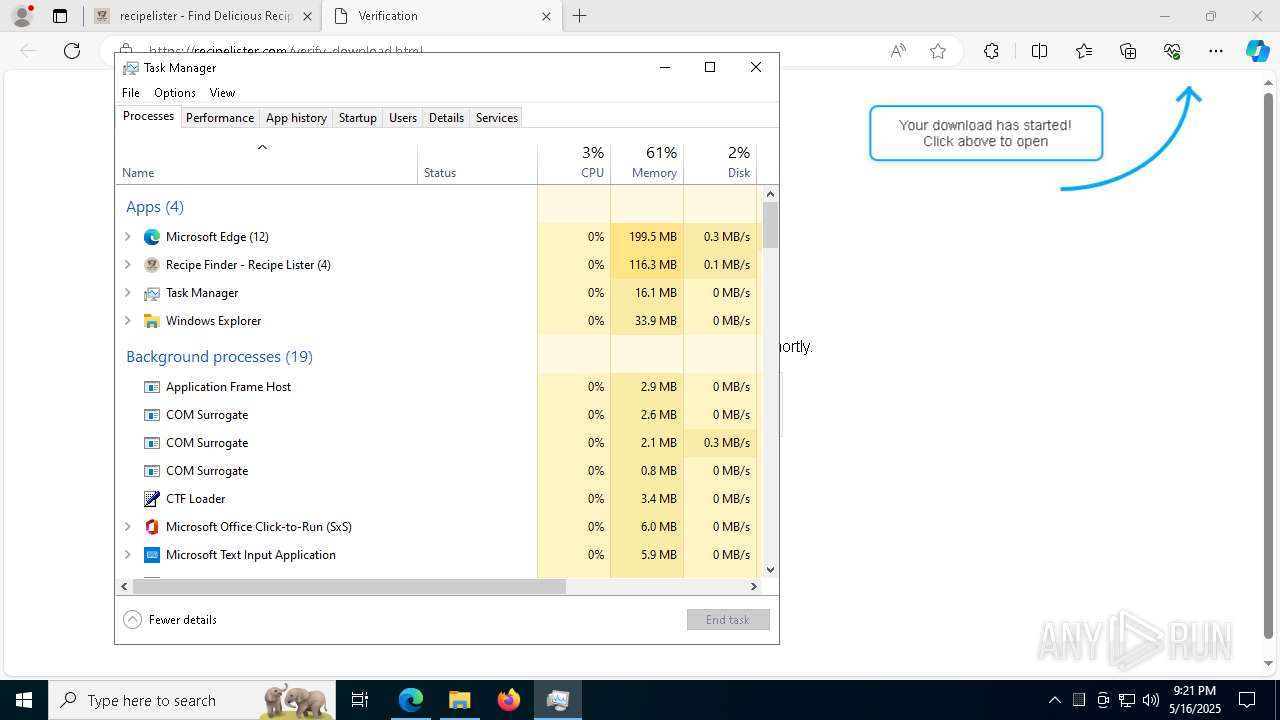
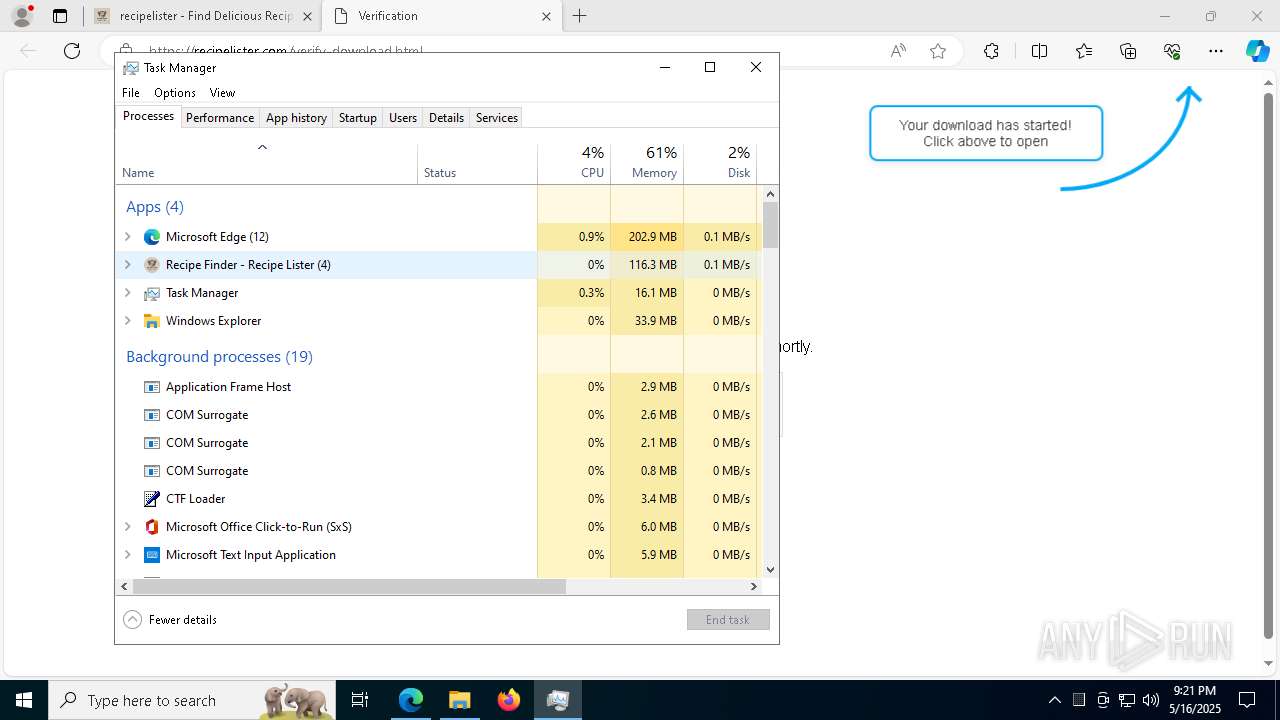
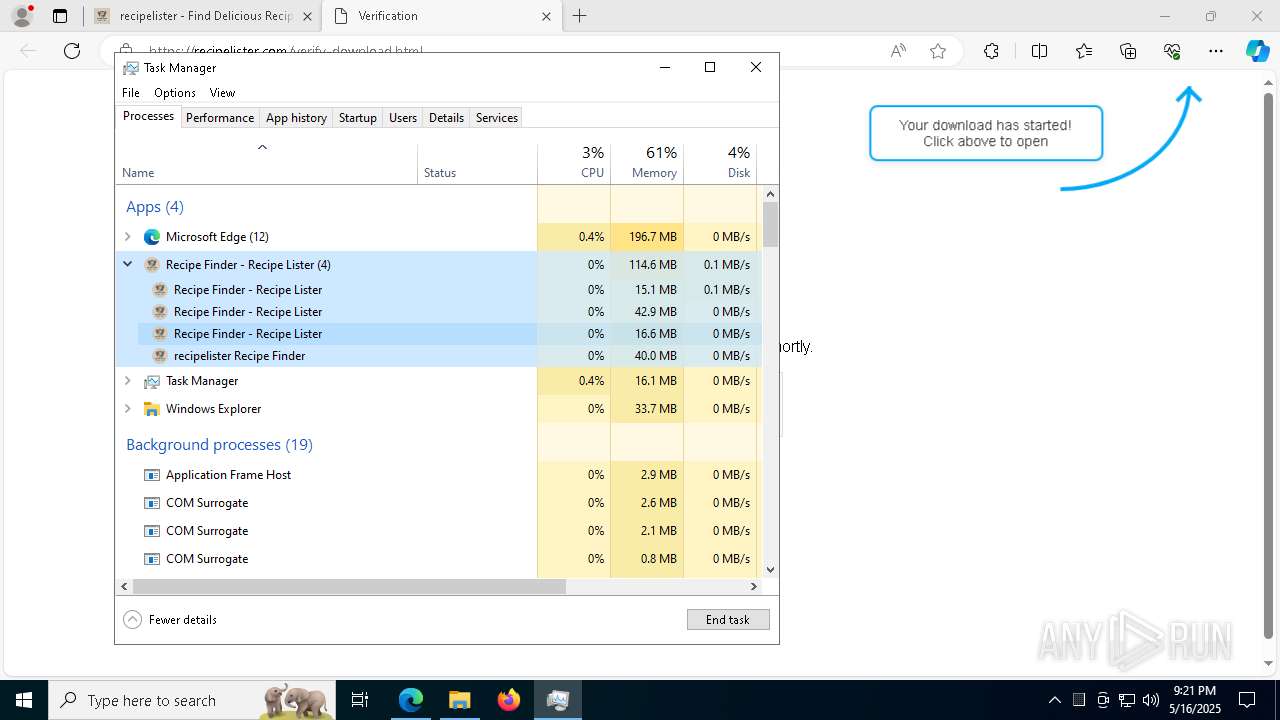
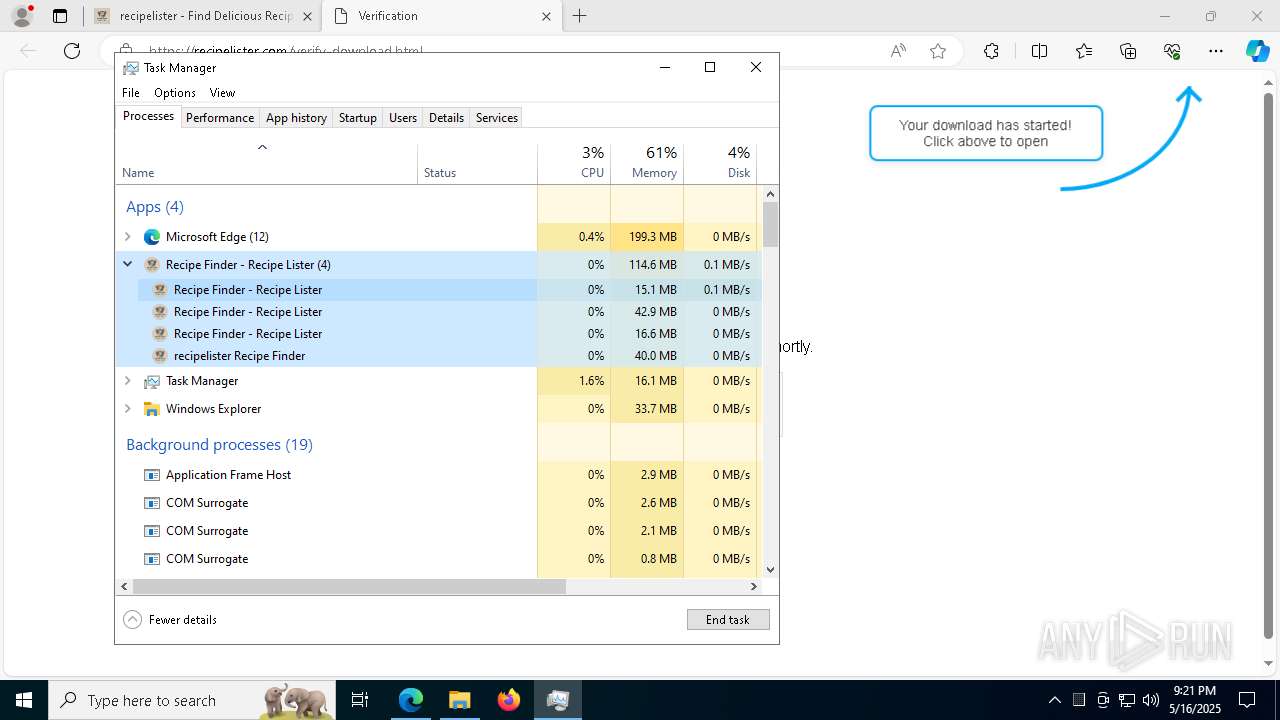
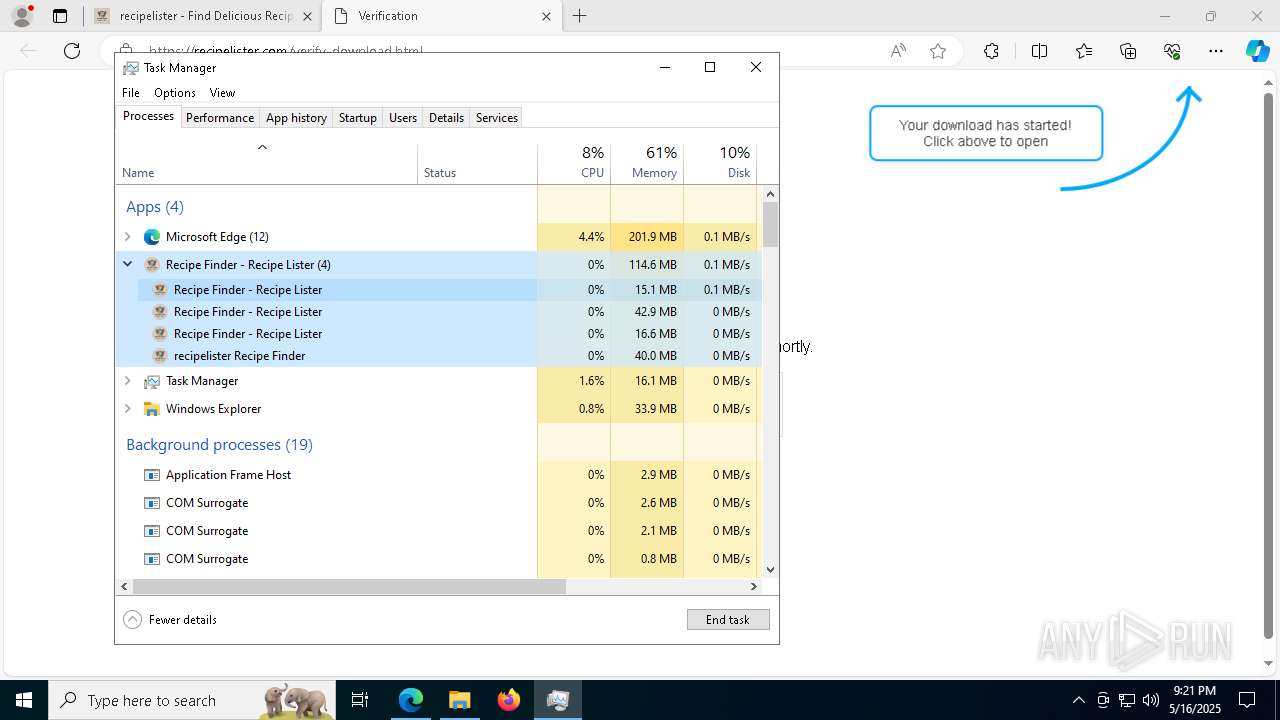
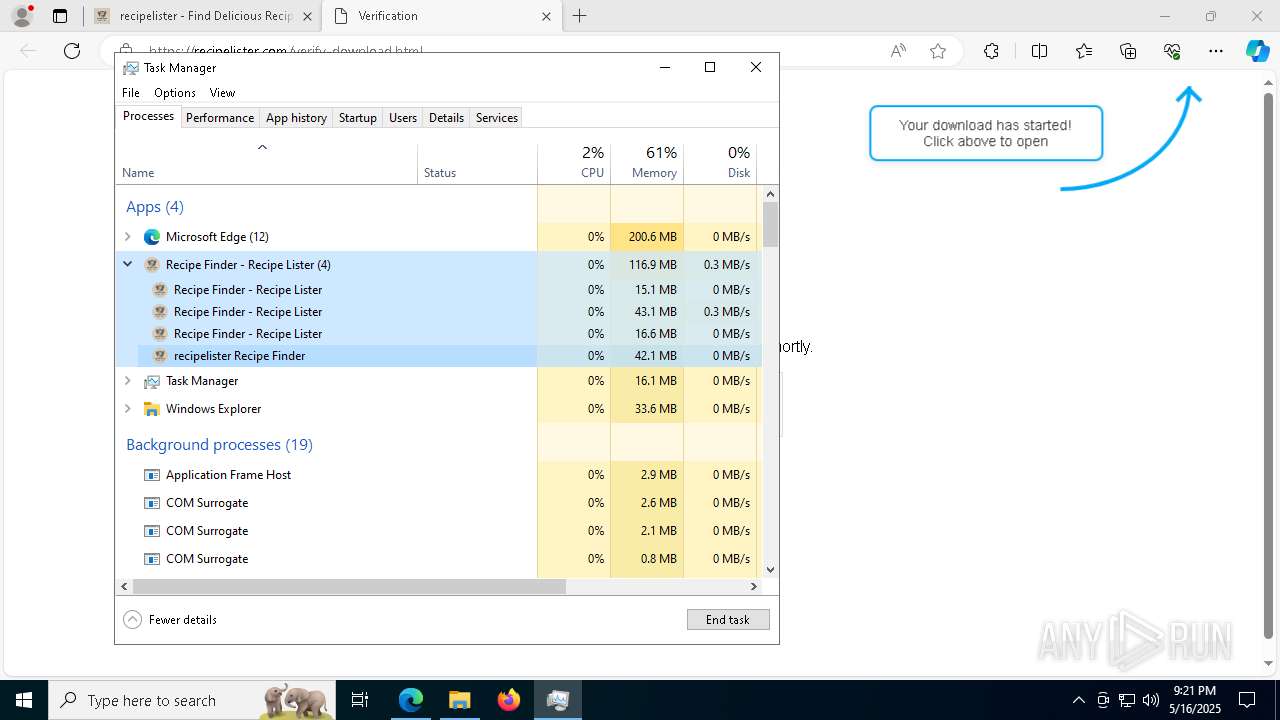
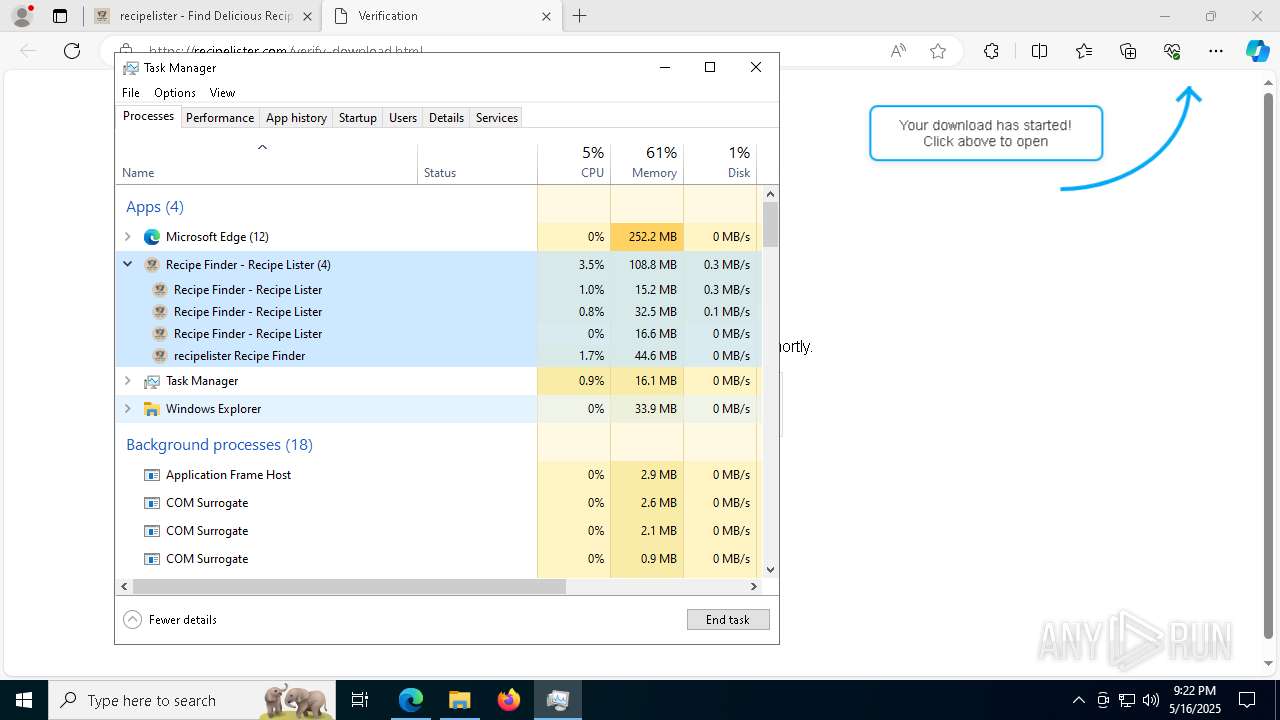
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
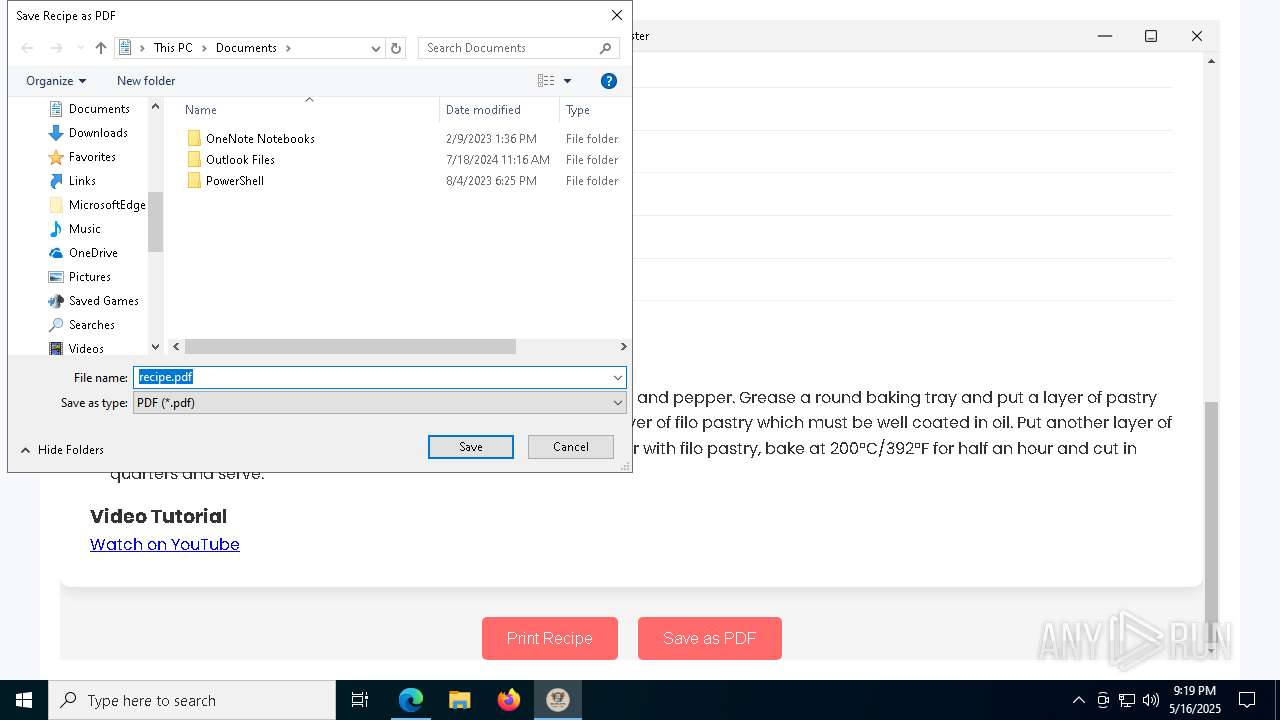
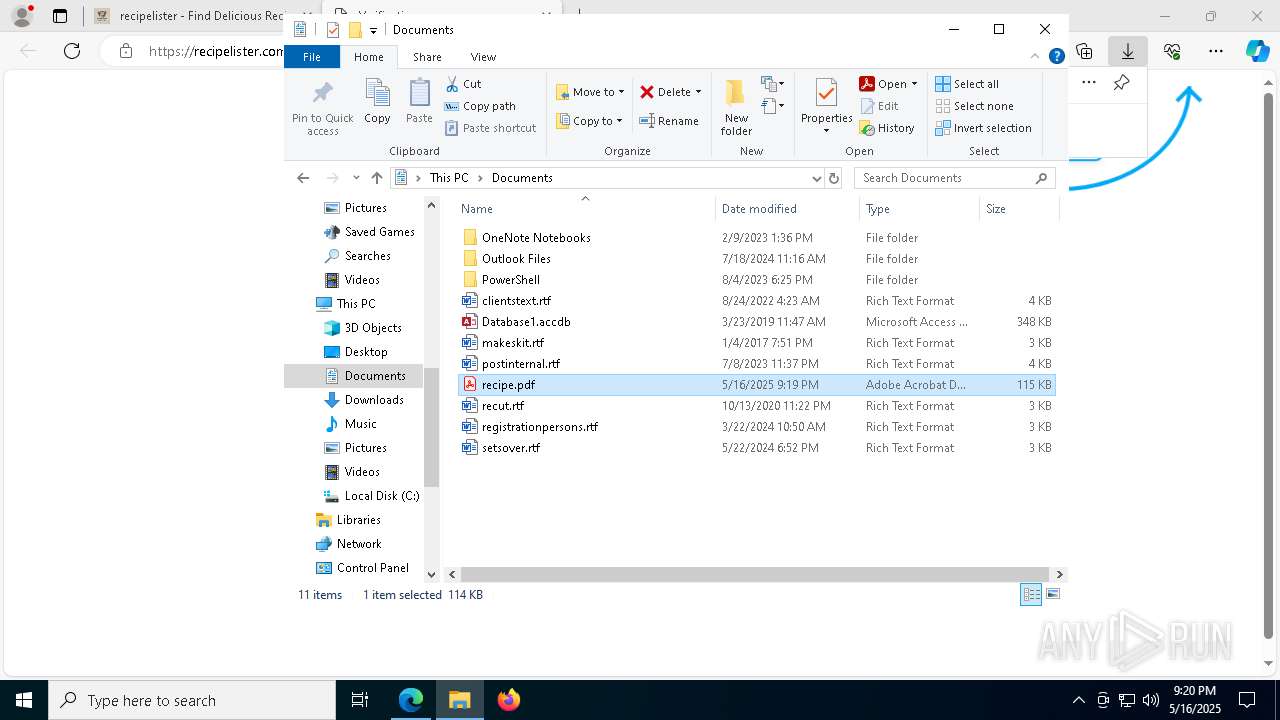
| 644 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.exe" --type=renderer /prefetch:1 "C:\Users\admin\Documents\recipe.pdf" | C:\Program Files\Adobe\Acrobat DC\Acrobat\Acrobat.exe | — | Acrobat.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe Acrobat Exit code: 1 Version: 23.1.20093.0 Modules
| |||||||||||||||
| 780 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --onnx-enabled-for-ee --no-appcompat-clear --mojo-platform-channel-handle=3560 --field-trial-handle=2364,i,66547608635069298,521920814620682804,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 968 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=5764 --field-trial-handle=2364,i,66547608635069298,521920814620682804,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1056 | "C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=utility --log-severity=disable --user-agent-product="ReaderServices/23.1.20093 Chrome/105.0.0.0" --lang=en-US --log-file="C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\debug.log" --mojo-platform-channel-handle=2128 --field-trial-handle=1584,i,8901741176921503114,33950436335772535,131072 --disable-features=BackForwardCache,CalculateNativeWinOcclusion,WinUseBrowserSpellChecker /prefetch:8 | C:\Program Files\Adobe\Acrobat DC\Acrobat\acrocef_1\AcroCEF.exe | — | AcroCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe AcroCEF Exit code: 0 Version: 23.1.20093.0 Modules
| |||||||||||||||
| 1088 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6068 --field-trial-handle=2364,i,66547608635069298,521920814620682804,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1088 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7736 --field-trial-handle=2364,i,66547608635069298,521920814620682804,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1128 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2800 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5784 --field-trial-handle=2364,i,66547608635069298,521920814620682804,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2984 | "C:\Users\admin\AppData\Local\Temp\2w1rXpxZnwDUwuTeNvdD6FUkeI0\Recipe Finder - Recipe Lister.exe" | C:\Users\admin\AppData\Local\Temp\2w1rXpxZnwDUwuTeNvdD6FUkeI0\Recipe Finder - Recipe Lister.exe | — | RecipeLister.exe | |||||||||||
User: admin Company: GitHub, Inc. Integrity Level: MEDIUM Description: Recipe Finder - Recipe Lister Version: 1.0.0 Modules
| |||||||||||||||
| 3272 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) | |||||||||||||||
Total events
29 997
Read events
29 708
Write events
253
Delete events
36
Modification events
| (PID) Process: | (7436) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (7436) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (7436) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (7436) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (7436) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 49E7EA97DD932F00 | |||
| (PID) Process: | (7436) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: ED600A98DD932F00 | |||
| (PID) Process: | (7436) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
| (PID) Process: | (7436) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
| (PID) Process: | (7436) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: CBF84398DD932F00 | |||
| (PID) Process: | (7436) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\Profiles |
| Operation: | write | Name: | EnhancedLinkOpeningDefault |
Value: Default | |||
Executable files
34
Suspicious files
753
Text files
299
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7436 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10ae14.TMP | — | |
MD5:— | SHA256:— | |||
| 7436 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7436 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10ae24.TMP | — | |
MD5:— | SHA256:— | |||
| 7436 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7436 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10ae43.TMP | — | |
MD5:— | SHA256:— | |||
| 7436 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7436 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10ae33.TMP | — | |
MD5:— | SHA256:— | |||
| 7436 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7436 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10ae62.TMP | — | |
MD5:— | SHA256:— | |||
| 7436 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
56
TCP/UDP connections
111
DNS requests
108
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 104.124.11.58:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 104.124.11.58:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7436 | msedge.exe | GET | 200 | 18.173.205.43:80 | http://ocsps.ssl.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT4XPMAgX8rbNb10iD9IkFVxGbTWwQUW8pe5d7SgarNqC1kUbbZcpuX5k8CEG7dTyXnMX05gVcxNM%2FB3KA%3D | unknown | — | — | whitelisted |
6272 | svchost.exe | HEAD | 200 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1747702819&P2=404&P3=2&P4=kvsI1qg%2fvRDoE6252p8%2fVPlXYPgBORj1qwGcCYvdGG1pIKSKNTDlLmkj3JEX3txv784gLDThkfZh9lZmpEPz1g%3d%3d | unknown | — | — | whitelisted |
7436 | msedge.exe | GET | 200 | 18.173.205.43:80 | http://ocsps.ssl.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBROpre88MpUocDyy2wCPdWKwtQZDwQUAYmUuf60M13w8fqF%2BSRGhKNXaV4CED%2FPMYE3OZi7YghPjS3TGKM%3D | unknown | — | — | whitelisted |
6272 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1747702819&P2=404&P3=2&P4=kvsI1qg%2fvRDoE6252p8%2fVPlXYPgBORj1qwGcCYvdGG1pIKSKNTDlLmkj3JEX3txv784gLDThkfZh9lZmpEPz1g%3d%3d | unknown | — | — | whitelisted |
6272 | svchost.exe | GET | 206 | 199.232.214.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9b9f8fb4-8a65-41e4-bda3-5416858f0aeb?P1=1747702819&P2=404&P3=2&P4=kvsI1qg%2fvRDoE6252p8%2fVPlXYPgBORj1qwGcCYvdGG1pIKSKNTDlLmkj3JEX3txv784gLDThkfZh9lZmpEPz1g%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 104.124.11.58:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 104.124.11.58:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7720 | msedge.exe | 172.67.150.5:443 | recipelister.com | — | — | unknown |
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
recipelister.com |
| unknown |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
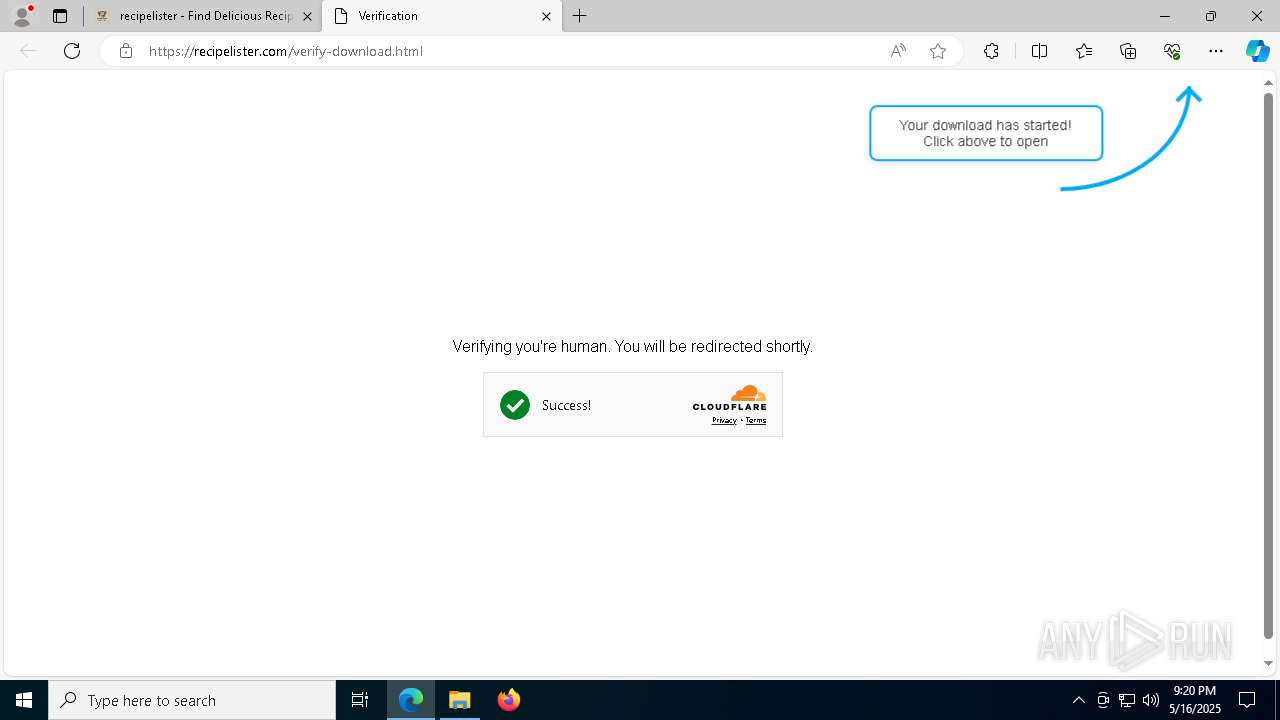
7720 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
7720 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare turnstile CAPTCHA challenge |
6032 | Recipe Finder - Recipe Lister.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |
6032 | Recipe Finder - Recipe Lister.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare Network Error Logging (NEL) |