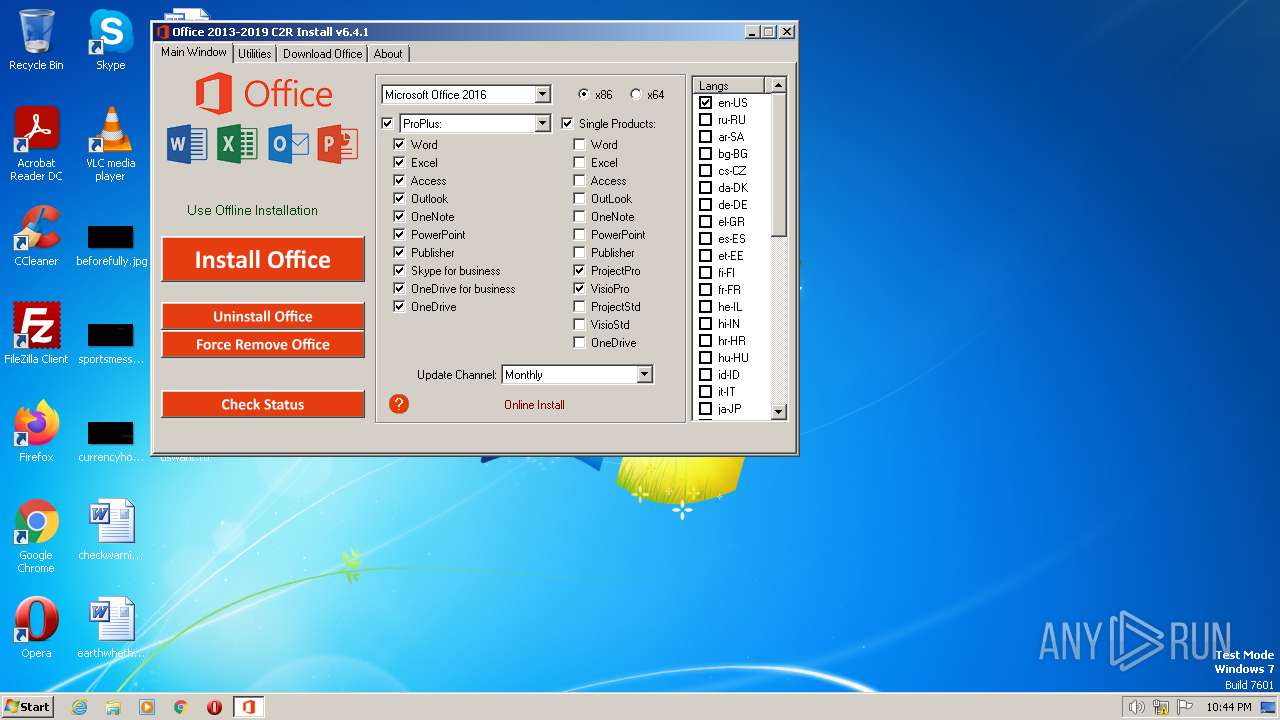
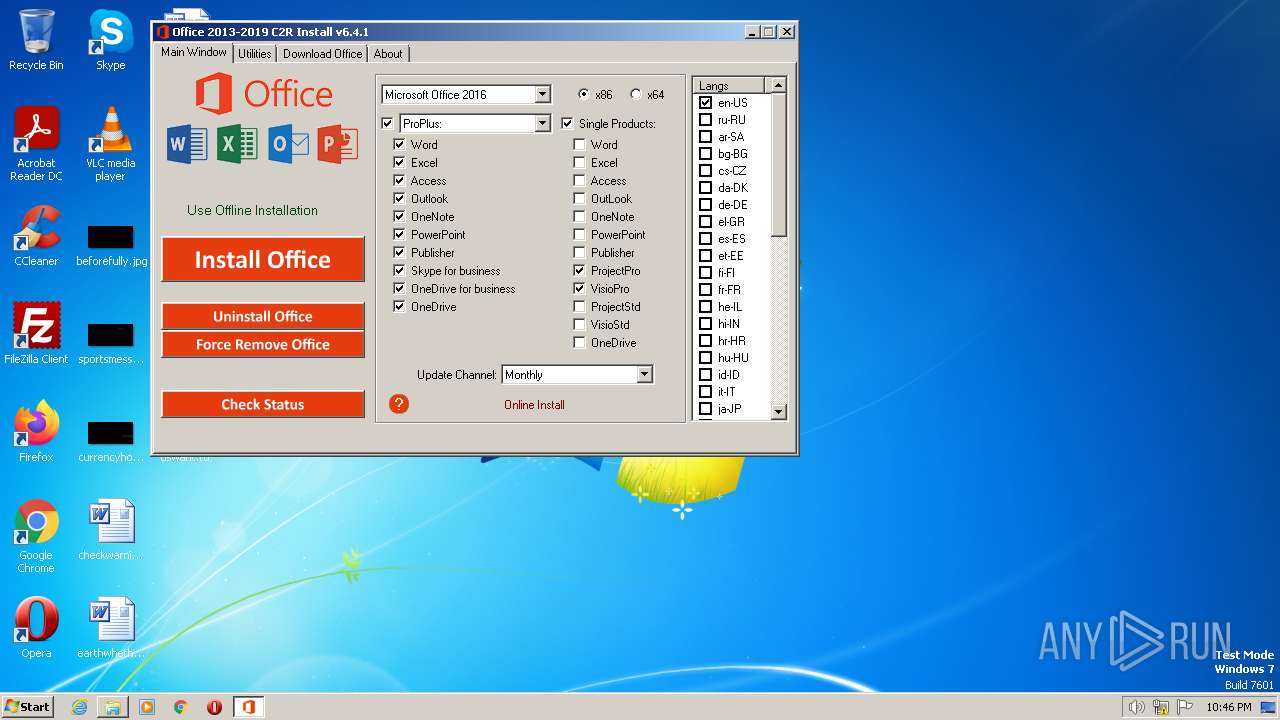
| File name: | OInstall.exe |
| Full analysis: | https://app.any.run/tasks/dd81253e-a112-4000-a49f-cb95e2c32881 |
| Verdict: | Malicious activity |
| Analysis date: | June 03, 2023, 21:44:47 |
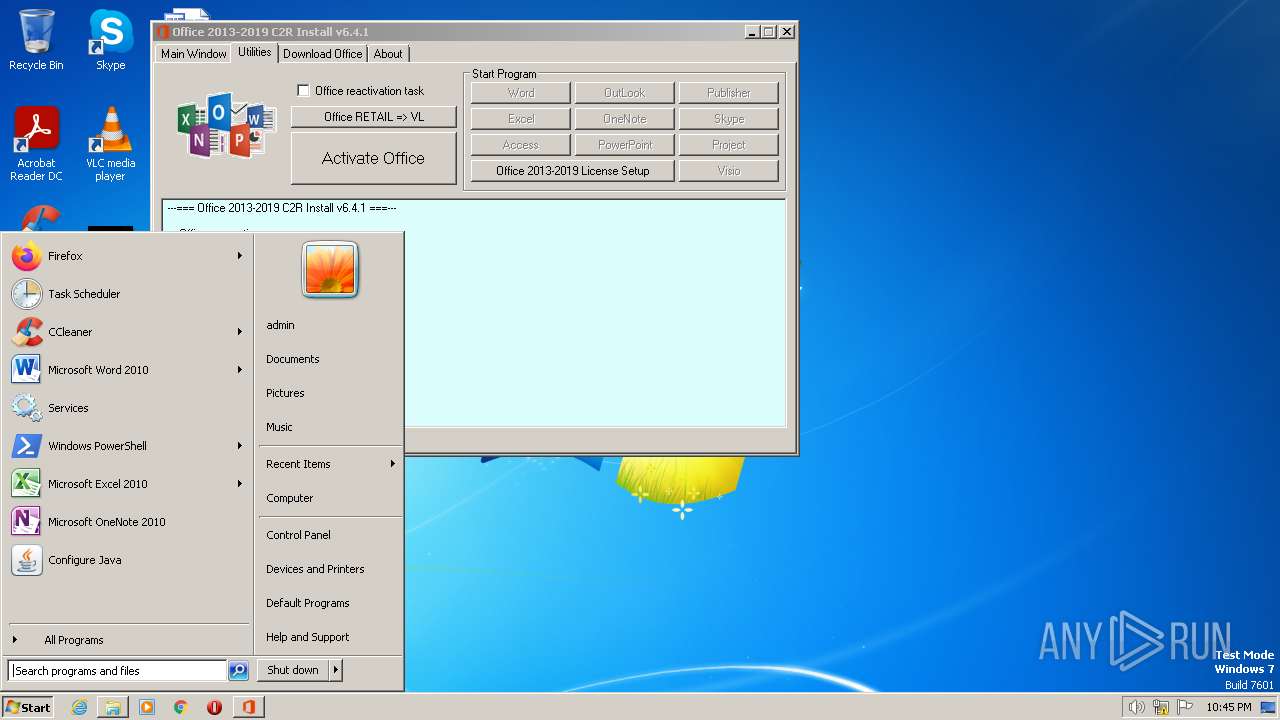
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | B99FAC79315B274F536A73E57DD10649 |
| SHA1: | 5B479138D2D7CF8EAEA1713D5E1B06758A8808E5 |
| SHA256: | 623344AA7C04D12756D890223DF826D6D7637FAE951407C29692CA40F6857B20 |
| SSDEEP: | 196608:/VrCEhhtHnNQoeXEXpTaCDnp2OU/vp0BWjmJJnwEYrbZu59mmrS3xUMxUgd3PJMu:9+YttbeXep2CDp2x/vqJnMZu59pr4OgT |
MALICIOUS
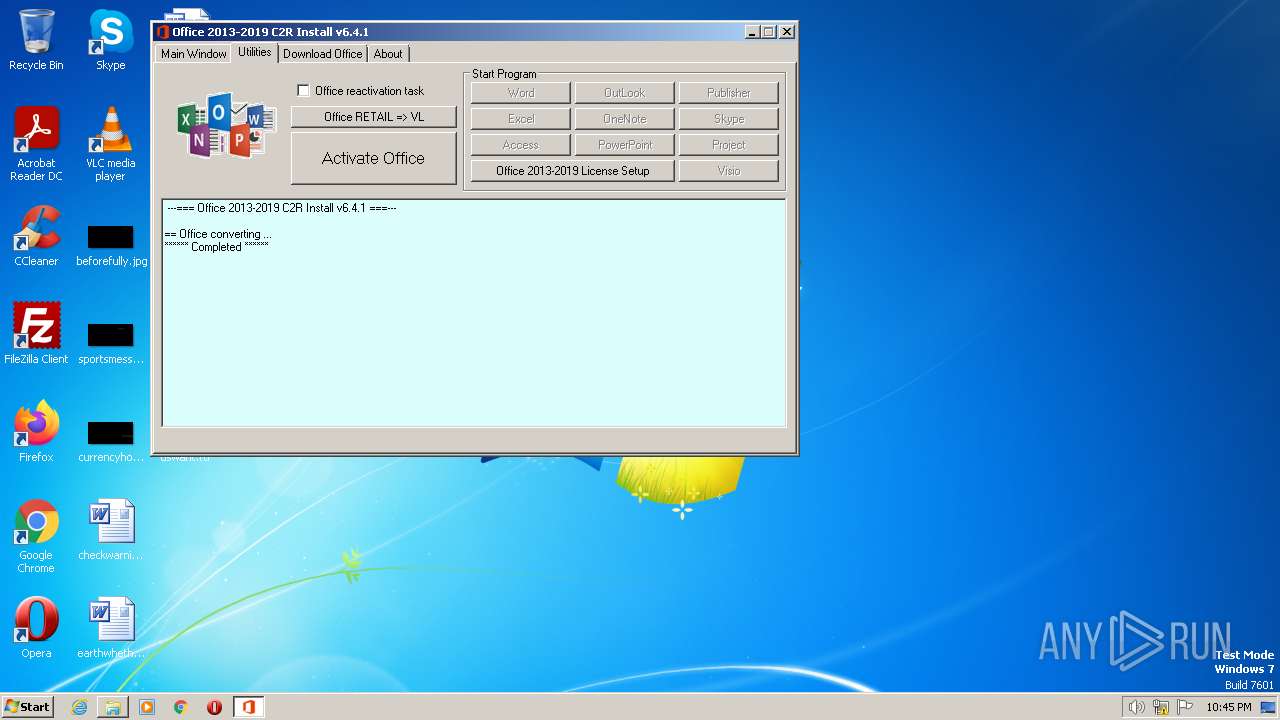
Application was dropped or rewritten from another process
- files.dat (PID: 3092)
- kmss.dat (PID: 1992)
- KMSS.exe (PID: 2780)
- setup.exe (PID: 292)
- OfficeClickToRun.exe (PID: 1960)
- OfficeClickToRun.exe (PID: 3952)
- OfficeC2RClient.exe (PID: 1932)
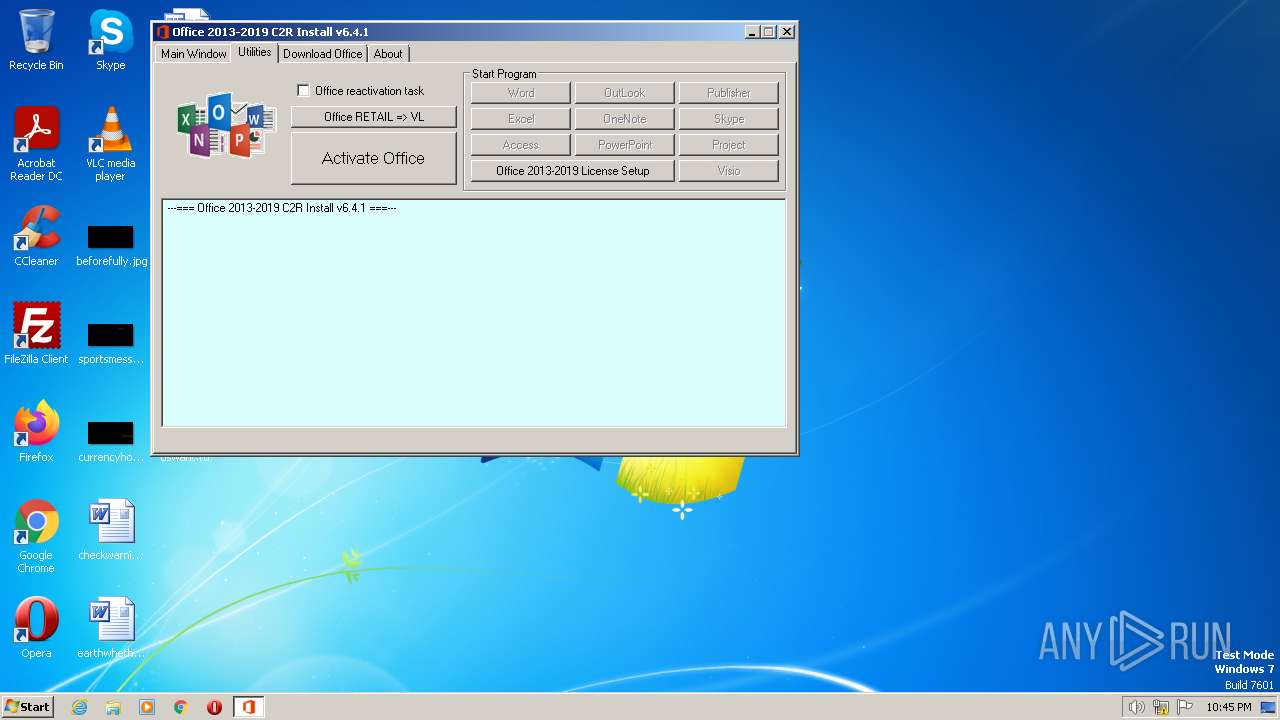
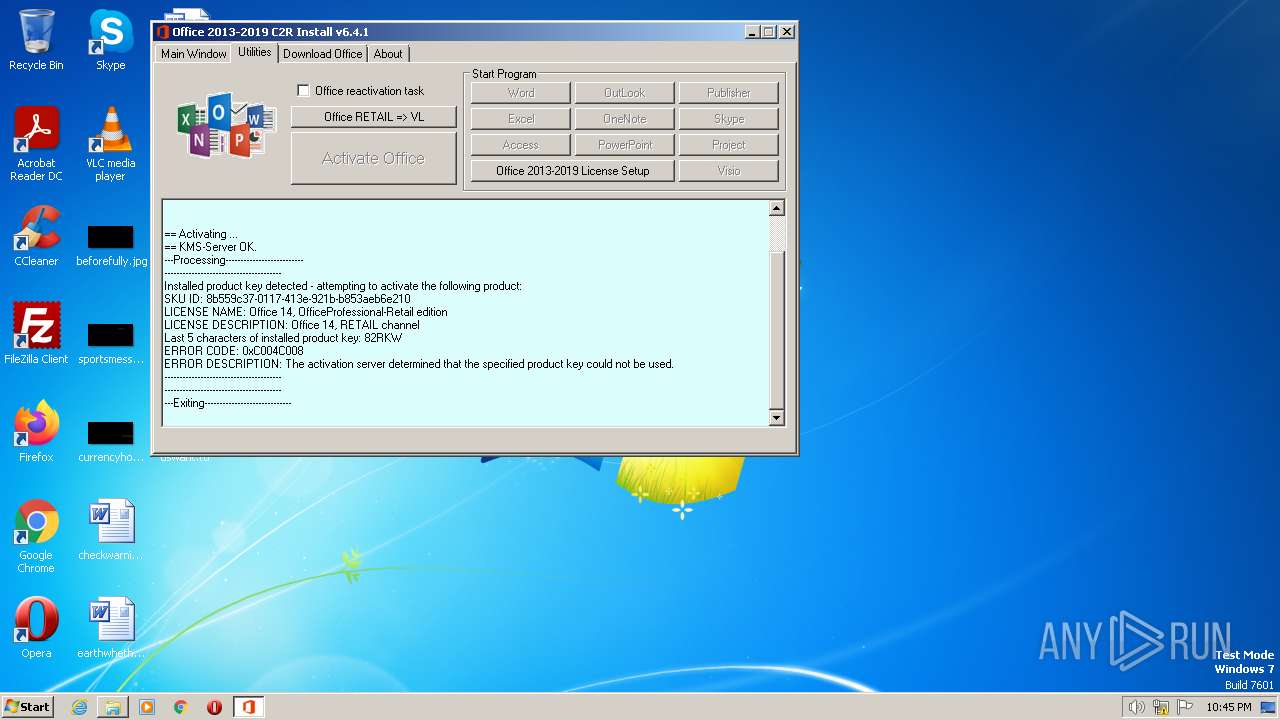
Starts NET.EXE for service management
- cmd.exe (PID: 3388)
- net.exe (PID: 3916)
Run PowerShell with an invisible window
- powershell.exe (PID: 3980)
Loads dropped or rewritten executable
- OfficeClickToRun.exe (PID: 1960)
- OfficeClickToRun.exe (PID: 3952)
- OfficeC2RClient.exe (PID: 1932)
Creates a writable file the system directory
- OfficeClickToRun.exe (PID: 3952)
SUSPICIOUS
Executable content was dropped or overwritten
- OInstall.exe (PID: 2452)
- files.dat (PID: 3092)
- kmss.dat (PID: 1992)
- setup.exe (PID: 292)
- OfficeClickToRun.exe (PID: 3952)
Reads the Internet Settings
- cscript.exe (PID: 3456)
- cscript.exe (PID: 1232)
- setup.exe (PID: 292)
- powershell.exe (PID: 3980)
- OfficeClickToRun.exe (PID: 1960)
- OfficeC2RClient.exe (PID: 1932)
Starts CMD.EXE for commands execution
- OInstall.exe (PID: 2452)
Starts application with an unusual extension
- cmd.exe (PID: 2712)
- cmd.exe (PID: 528)
The process executes VB scripts
- cmd.exe (PID: 2324)
- cmd.exe (PID: 2232)
- cmd.exe (PID: 3808)
- cmd.exe (PID: 4088)
- cmd.exe (PID: 3056)
Drops a system driver (possible attempt to evade defenses)
- kmss.dat (PID: 1992)
Uses TASKKILL.EXE to kill process
- OInstall.exe (PID: 2452)
- cmd.exe (PID: 3128)
Uses NETSH.EXE to add a firewall rule or allowed programs
- cmd.exe (PID: 2692)
Uses NETSH.EXE to delete a firewall rule or allowed programs
- cmd.exe (PID: 2720)
- cmd.exe (PID: 3472)
Adds/modifies Windows certificates
- cmd.exe (PID: 2212)
The process hide an interactive prompt from the user
- setup.exe (PID: 292)
Using PowerShell to operate with local accounts
- powershell.exe (PID: 3980)
Reads security settings of Internet Explorer
- setup.exe (PID: 292)
Searches for installed software
- setup.exe (PID: 292)
Starts POWERSHELL.EXE for commands execution
- setup.exe (PID: 292)
The process bypasses the loading of PowerShell profile settings
- setup.exe (PID: 292)
Reads settings of System Certificates
- OfficeClickToRun.exe (PID: 1960)
- setup.exe (PID: 292)
Executes as Windows Service
- OfficeClickToRun.exe (PID: 3952)
Checks Windows Trust Settings
- OfficeClickToRun.exe (PID: 3952)
- setup.exe (PID: 292)
INFO
Checks supported languages
- OInstall.exe (PID: 2452)
- files.dat (PID: 3092)
- kmss.dat (PID: 1992)
- KMSS.exe (PID: 2780)
- setup.exe (PID: 292)
- OfficeClickToRun.exe (PID: 1960)
- OfficeClickToRun.exe (PID: 3952)
- OfficeC2RClient.exe (PID: 1932)
Reads the computer name
- OInstall.exe (PID: 2452)
- KMSS.exe (PID: 2780)
- setup.exe (PID: 292)
- OfficeClickToRun.exe (PID: 1960)
- OfficeClickToRun.exe (PID: 3952)
- OfficeC2RClient.exe (PID: 1932)
The process checks LSA protection
- OInstall.exe (PID: 2452)
- cscript.exe (PID: 3456)
- netsh.exe (PID: 1852)
- taskkill.exe (PID: 2368)
- netsh.exe (PID: 3960)
- taskkill.exe (PID: 2476)
- KMSS.exe (PID: 2780)
- taskkill.exe (PID: 2096)
- cscript.exe (PID: 1480)
- cscript.exe (PID: 2752)
- cscript.exe (PID: 672)
- taskkill.exe (PID: 1036)
- cscript.exe (PID: 1232)
- netsh.exe (PID: 2832)
- setup.exe (PID: 292)
- OfficeClickToRun.exe (PID: 3952)
- OfficeC2RClient.exe (PID: 1932)
- OfficeClickToRun.exe (PID: 1960)
Create files in a temporary directory
- files.dat (PID: 3092)
- OInstall.exe (PID: 2452)
- kmss.dat (PID: 1992)
- setup.exe (PID: 292)
- powershell.exe (PID: 3980)
- OfficeClickToRun.exe (PID: 1960)
- OfficeC2RClient.exe (PID: 1932)
The executable file from the user directory is run by the CMD process
- files.dat (PID: 3092)
- kmss.dat (PID: 1992)
- setup.exe (PID: 292)
Reads security settings of Internet Explorer
- cscript.exe (PID: 3456)
- cscript.exe (PID: 1480)
- cscript.exe (PID: 2752)
- cscript.exe (PID: 672)
- cscript.exe (PID: 1232)
Reads Environment values
- OInstall.exe (PID: 2452)
- OfficeClickToRun.exe (PID: 3952)
- OfficeClickToRun.exe (PID: 1960)
- OfficeC2RClient.exe (PID: 1932)
Reads the machine GUID from the registry
- KMSS.exe (PID: 2780)
- setup.exe (PID: 292)
- OfficeClickToRun.exe (PID: 1960)
- OfficeClickToRun.exe (PID: 3952)
- OfficeC2RClient.exe (PID: 1932)
Reads Microsoft Office registry keys
- setup.exe (PID: 292)
- OfficeClickToRun.exe (PID: 1960)
- OfficeClickToRun.exe (PID: 3952)
- OfficeC2RClient.exe (PID: 1932)
Checks proxy server information
- setup.exe (PID: 292)
- OfficeClickToRun.exe (PID: 1960)
- OfficeC2RClient.exe (PID: 1932)
Process checks computer location settings
- setup.exe (PID: 292)
- OfficeClickToRun.exe (PID: 1960)
- OfficeClickToRun.exe (PID: 3952)
- OfficeC2RClient.exe (PID: 1932)
Creates files or folders in the user directory
- setup.exe (PID: 292)
- OfficeClickToRun.exe (PID: 1960)
- OfficeC2RClient.exe (PID: 1932)
Creates files in the program directory
- setup.exe (PID: 292)
- OfficeClickToRun.exe (PID: 3952)
Manual execution by a user
- OfficeC2RClient.exe (PID: 1932)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (76) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.6) |
| .exe | | | Generic Win/DOS Executable (5.6) |
| .exe | | | DOS Executable Generic (5.6) |
EXIF
EXE
| FileDescription: | Office 2013-2016 C2R Install |
|---|---|
| ProductName: | Office 2013-2016 C2R Install |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Unknown |
| FileOS: | Unknown (0) |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 6.4.1.0 |
| FileVersionNumber: | 6.4.1.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x113a5c0 |
| UninitializedDataSize: | 8470528 |
| InitializedDataSize: | 86016 |
| CodeSize: | 9592832 |
| LinkerVersion: | 2.5 |
| PEType: | PE32 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| TimeStamp: | 2018:08:01 04:34:53+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Aug-2018 04:34:53 |
| Detected languages: |
|
| ProductName: | Office 2013-2016 C2R Install |
| FileDescription: | Office 2013-2016 C2R Install |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 01-Aug-2018 04:34:53 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x00814000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x00815000 | 0x00926000 | 0x00925800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.88053 |
.rsrc | 0x0113B000 | 0x00015000 | 0x00015000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.94971 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.8674 | 874 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 1.96082 | 9640 | UNKNOWN | English - United States | RT_ICON |
3 | 2.20562 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 2.87138 | 1128 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.DLL |
COMCTL32.DLL |
GDI32.DLL |
ICMP.DLL |
IMAGEHLP.DLL |
IPHLPAPI.DLL |
KERNEL32.DLL |
MSI.DLL |
MSVCRT.dll |
NETAPI32.DLL |
Total processes
101
Monitored processes
38
Malicious processes
8
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | C:\Users\admin\AppData\Local\Temp\files\Setup.exe /configure Configure.xml | C:\Users\admin\AppData\Local\Temp\files\setup.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Office Exit code: 0 Version: 16.0.10321.33602 Modules
| |||||||||||||||
| 528 | "C:\Windows\System32\cmd.exe" /D /c kmss.dat -y -pkmsauto | C:\Windows\System32\cmd.exe | — | OInstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 672 | cscript.exe "C:\Program Files\Microsoft Office\Office14\OSPP.VBS" //NoLogo /setprt:1688 | C:\Windows\System32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1036 | "taskkill.exe" /t /f /IM KMSS.exe | C:\Windows\System32\taskkill.exe | — | OInstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1232 | cscript.exe "C:\Program Files\Microsoft Office\Office14\OSPP.VBS" //NoLogo /act | C:\Windows\System32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1480 | cscript.exe "C:\Program Files\Microsoft Office\Office14\OSPP.VBS" //NoLogo /remhst | C:\Windows\System32\cscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Console Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1788 | "C:\Users\admin\AppData\Local\Temp\OInstall.exe" | C:\Users\admin\AppData\Local\Temp\OInstall.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Office 2013-2016 C2R Install Exit code: 3221226540 Modules
| |||||||||||||||
| 1852 | Netsh.exe Advfirewall Firewall delete rule name=0pen_Port_KMS protocol=TCP | C:\Windows\System32\netsh.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1932 | "C:\Program Files\Common Files\Microsoft Shared\ClickToRun\OfficeC2RClient.exe" /progressandlaunch AppTargets="root\office16\excel.exe|root\office16\powerpnt.exe|root\office16\winword.exe" ManualUpgrade=False ScenarioToTrack="Scenario:{FB9843BB-0D8A-4347-A227-C759C3FC9103}@INSTALL" | C:\Program Files\Common Files\Microsoft Shared\ClickToRun\OfficeC2RClient.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Office Click-to-Run Client Exit code: 0 Version: 16.0.12527.22286 Modules
| |||||||||||||||
| 1960 | deliverymechanism=492350f6-3a01-4f97-b9c0-c7c6ddf67d60 platform=x86 productreleaseid=none forcecentcheck= culture=en-us defaultplatform=False storeid= lcid=1033 b= totalclientcabsize=21067269 productstoadd=ProplusRetail.16_en-us_x-none scenariosubtype=ODT scenario=unknown updatesenabled.16=True acceptalleulas.16=True cdnbaseurl.16=http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60 version.16=16.0.12527.22286 mediatype.16=CDN proplusretail.excludedapps.16=access,publisher,groove,lync,onenote,outlook,onedrive baseurl.16=http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60 sourcetype.16=CDN flt.downloadappvcab=unknown flt.useclientcabmanager=unknown flt.useexptransportinplacepl=unknown flt.useaddons=unknown flt.useofficehelperaddon=unknown flt.useonedriveclientaddon=unknown | C:\Program Files\Common Files\Microsoft Shared\ClickToRun\OfficeClickToRun.exe | setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Office Click-to-Run (SxS) Exit code: 0 Version: 16.0.12527.22286 Modules
| |||||||||||||||
Total events
38 898
Read events
38 570
Write events
327
Delete events
1
Modification events
| (PID) Process: | (2452) OInstall.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\MediaResources\DirectSound\Speaker Configuration |
| Operation: | write | Name: | Speaker Configuration |
Value: 4 | |||
| (PID) Process: | (3456) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3456) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3456) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3456) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1852) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3960) netsh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1232) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1232) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1232) cscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
Executable files
208
Suspicious files
56
Text files
37
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3092 | files.dat | C:\Users\admin\AppData\Local\Temp\files\x64\cleanospp.exe | executable | |
MD5:162AB955CB2F002A73C1530AA796477F | SHA256:5CE462E5F34065FC878362BA58617FAB28C22D631B9D836DDDCF43FB1AD4DE6E | |||
| 3092 | files.dat | C:\Users\admin\AppData\Local\Temp\files\x64\msvcr100.dll | executable | |
MD5:DF3CA8D16BDED6A54977B30E66864D33 | SHA256:1D1A1AE540BA132F998D60D3622F0297B6E86AE399332C3B47462D7C0F560A36 | |||
| 3092 | files.dat | C:\Users\admin\AppData\Local\Temp\files\Configure.xml | text | |
MD5:AC6BE84084E31DBB0E08D188B6C86EC8 | SHA256:1879F7DE537C2AA70292C61EBEF9C6477D36E25B2E6A639E318B159E0A22B0FC | |||
| 3092 | files.dat | C:\Users\admin\AppData\Local\Temp\files\x86\msvcr100.dll | executable | |
MD5:BF38660A9125935658CFA3E53FDC7D65 | SHA256:60C06E0FA4449314DA3A0A87C1A9D9577DF99226F943637E06F61188E5862EFA | |||
| 1992 | kmss.dat | C:\Users\admin\AppData\Local\Temp\files\bin\x64WDV\FakeClient.exe | executable | |
MD5:6241A145A6BC3511E7690DCF107CEFD8 | SHA256:2218293E4442DEB06E398AA0357AEF54DF377B95E46B6ED79B48B65B666C9405 | |||
| 1992 | kmss.dat | C:\Users\admin\AppData\Local\Temp\files\bin\KMSS.exe | executable | |
MD5:6361F25EDE0442F2E0AD3BCD33C331C8 | SHA256:592835F805DA0D9A24A5D91A0F77AD9988853DA34A97B50E75E77C72573EDEAC | |||
| 1992 | kmss.dat | C:\Users\admin\AppData\Local\Temp\files\bin\x86WDV\WinDivert32.sys | executable | |
MD5:ECAB976E5B0434685524BA6D534301A5 | SHA256:BD27499533E42D64BCAB52A018ADD1E361DE02F04C4B1D16852CB643BF4C5755 | |||
| 2452 | OInstall.exe | C:\Users\admin\AppData\Local\Temp\files\files.dat | executable | |
MD5:BB81E763AB0E673B3C1AF2FEA2586A9A | SHA256:4D45C64B244C8F997358635C3B5CB9A65743FAC473D65C455D3BA8A25E50D5F9 | |||
| 1992 | kmss.dat | C:\Users\admin\AppData\Local\Temp\files\bin\x86WDV\FakeClient.exe | executable | |
MD5:0520D5EABEB550C6BB24357A961B230A | SHA256:6ACAA70493133170451F82F6228EF0C96A44243E69935B4516023C935DCFB810 | |||
| 292 | setup.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
49
TCP/UDP connections
40
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
292 | setup.exe | HEAD | 200 | 67.27.234.124:80 | http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v32_16.0.12527.22286.cab | US | — | — | whitelisted |
2400 | WmiPrvSE.exe | POST | 302 | 104.102.40.139:80 | http://go.microsoft.com/fwlink/?LinkID=120751 | DE | — | — | whitelisted |
2400 | WmiPrvSE.exe | POST | 302 | 104.102.40.139:80 | http://go.microsoft.com/fwlink/?LinkID=120752 | DE | — | — | whitelisted |
292 | setup.exe | HEAD | 200 | 67.27.234.124:80 | http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v32_16.0.12527.22286.cab | US | — | — | whitelisted |
852 | svchost.exe | HEAD | 200 | 67.27.234.124:80 | http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/16.0.12527.22286/s321033.cab | US | — | — | whitelisted |
3952 | OfficeClickToRun.exe | HEAD | 200 | 67.27.234.124:80 | http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/16.0.12527.22286/s321033.cab | US | — | — | whitelisted |
2400 | WmiPrvSE.exe | POST | 302 | 104.102.40.139:80 | http://go.microsoft.com/fwlink/?LinkID=120750 | DE | — | — | whitelisted |
292 | setup.exe | GET | 200 | 67.27.234.124:80 | http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/16.0.12527.22286/i321033.cab | US | compressed | 9.71 Kb | whitelisted |
292 | setup.exe | HEAD | 200 | 67.27.234.124:80 | http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/16.0.12527.22286/i320.cab | US | compressed | 9.71 Kb | whitelisted |
292 | setup.exe | GET | 200 | 67.27.234.124:80 | http://officecdn.microsoft.com/pr/492350f6-3a01-4f97-b9c0-c7c6ddf67d60/Office/Data/v32_16.0.12527.22286.cab | US | compressed | 10.5 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1076 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3712 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2400 | WmiPrvSE.exe | 104.102.40.139:80 | go.microsoft.com | AKAMAI-AS | DE | malicious |
292 | setup.exe | 13.107.5.88:443 | client-office365-tas.msedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
292 | setup.exe | 67.27.234.124:80 | officecdn.microsoft.com | LEVEL3 | US | unknown |
292 | setup.exe | 209.197.3.8:80 | ctldl.windowsupdate.com | STACKPATH-CDN | US | whitelisted |
292 | setup.exe | 95.101.54.122:80 | crl.microsoft.com | Akamai International B.V. | DE | suspicious |
1376 | svchost.exe | 51.132.193.104:443 | vortex-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | suspicious |
1376 | svchost.exe | 52.168.112.66:443 | vortex-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
go.microsoft.com |
| whitelisted |
activation.sls.microsoft.com |
| whitelisted |
config.edge.skype.com |
| malicious |
mrodevicemgr.officeapps.live.com |
| whitelisted |
client-office365-tas.msedge.net |
| whitelisted |
officecdn.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
vortex-win.data.microsoft.com |
| whitelisted |