| File name: | MagicMRS.exe |
| Full analysis: | https://app.any.run/tasks/d8f05c5a-4b53-4a78-b582-9916c5fff042 |
| Verdict: | Malicious activity |
| Analysis date: | September 09, 2020, 00:46:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 7777A83BBCCD037370FB874A6A28E355 |
| SHA1: | 4B036B3861F2D67CBBF0E0CE9A052184BE4C0CCC |
| SHA256: | 62208DD29A044E457B07EFBABB03E73A52356A15359D3A109811969D13CB131D |
| SSDEEP: | 196608:MNvCltG8l6SXeyfncbOQRBwiCeNilDo4/KVK+dD7L:EvCXiueyRYxCeNilDo4S79L |
MALICIOUS
Changes internet zones settings
- MagicMRS.exe (PID: 2664)
Loads dropped or rewritten executable
- MagicMRS.exe (PID: 2664)
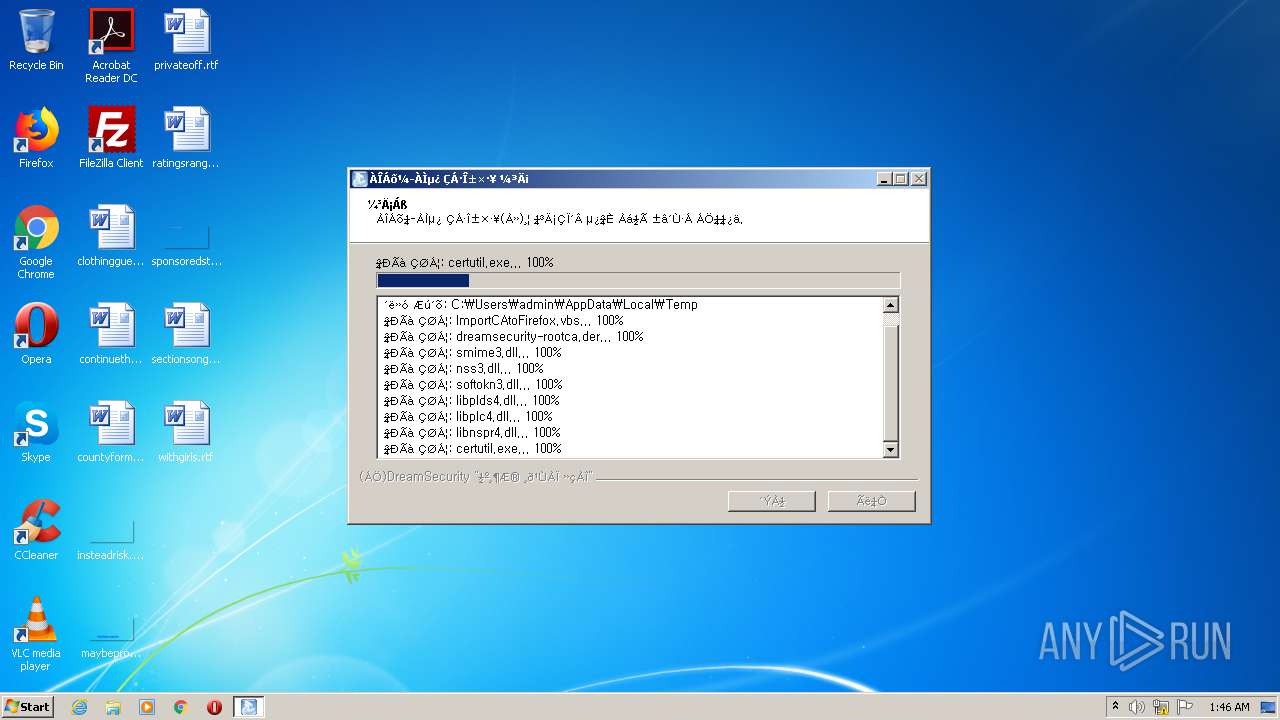
- certutil.exe (PID: 2252)
- regsvr32.exe (PID: 1592)
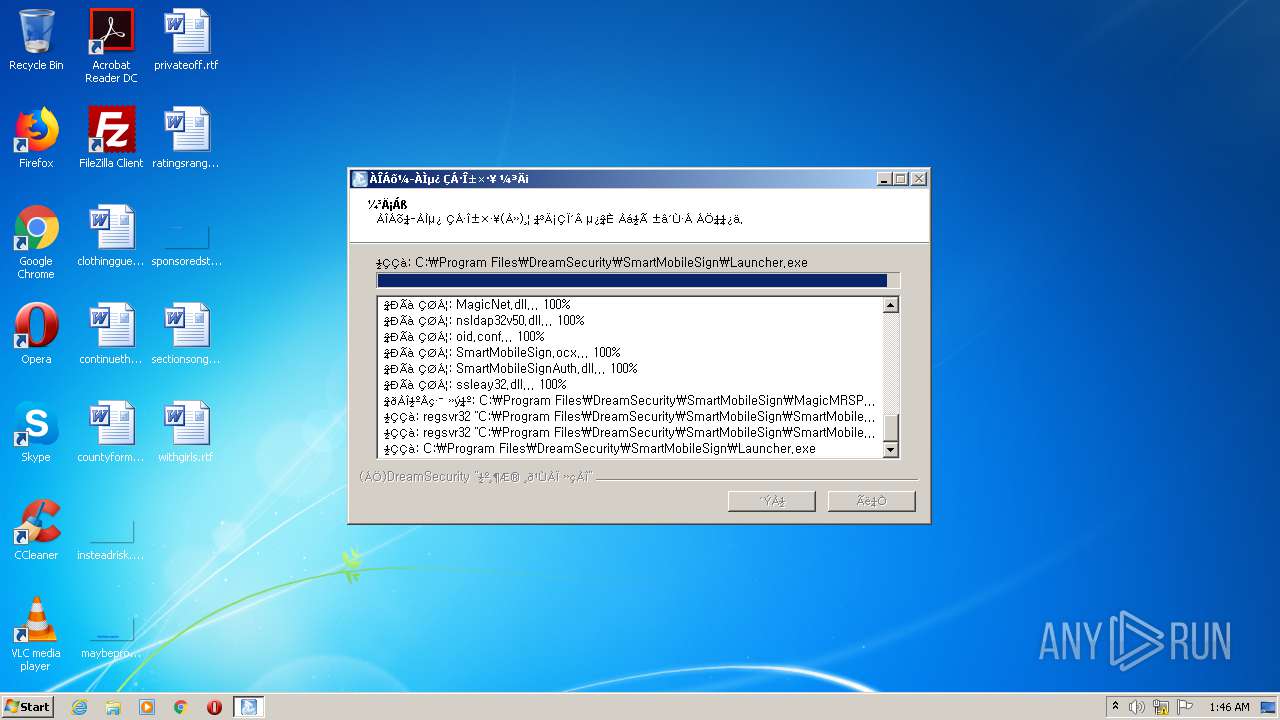
- Launcher.exe (PID: 3072)
- regsvr32.exe (PID: 2336)
Application was dropped or rewritten from another process
- certutil.exe (PID: 2252)
- Launcher.exe (PID: 3072)
Actions looks like stealing of personal data
- certutil.exe (PID: 2252)
Changes settings of System certificates
- certmgr.exe (PID: 2696)
Registers / Runs the DLL via REGSVR32.EXE
- MagicMRS.exe (PID: 2664)
Changes the autorun value in the registry
- MagicMRS.exe (PID: 2664)
SUSPICIOUS
Starts CMD.EXE for commands execution
- MagicMRS.exe (PID: 2664)
Executable content was dropped or overwritten
- MagicMRS.exe (PID: 2664)
Executes scripts
- cmd.exe (PID: 2584)
Creates files in the user directory
- certutil.exe (PID: 2252)
Starts application with an unusual extension
- MagicMRS.exe (PID: 2664)
Creates files in the program directory
- MagicMRS.exe (PID: 2664)
Creates a software uninstall entry
- MagicMRS.exe (PID: 2664)
Creates COM task schedule object
- regsvr32.exe (PID: 2336)
INFO
Dropped object may contain Bitcoin addresses
- MagicMRS.exe (PID: 2664)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:08:01 02:34:02+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25600 |
| InitializedDataSize: | 162816 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x31f1 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Aug-2017 00:34:02 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 01-Aug-2017 00:34:02 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006254 | 0x00006400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.43386 |
.rdata | 0x00008000 | 0x00001354 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.23627 |
.data | 0x0000A000 | 0x00025518 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.04463 |
.ndata | 0x00030000 | 0x0000B000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0003B000 | 0x00001638 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.88989 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.2901 | 1072 | UNKNOWN | English - United States | RT_MANIFEST |
103 | 1.91924 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.62016 | 492 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.86295 | 228 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.92694 | 218 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
52
Monitored processes
10
Malicious processes
3
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 868 | "C:\Users\admin\AppData\Local\Temp\nsa1509.tmp\ns1B34.tmp" "C:\Users\admin\AppData\Local\Temp\certmgr.exe" -add dreamsecurity-rootca.der -c -s -r localMachine Root | C:\Users\admin\AppData\Local\Temp\nsa1509.tmp\ns1B34.tmp | — | MagicMRS.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 888 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\ImportCAtoFirefox.vbs" | C:\Windows\System32\WScript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1592 | regsvr32 "C:\Program Files\DreamSecurity\SmartMobileSign\SmartMobileSign.ocx" /S | C:\Windows\system32\regsvr32.exe | — | MagicMRS.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2252 | "C:\Users\admin\AppData\Local\Temp\certutil.exe" -A -n "Dreamsecurity ROOT CA" -i "dreamsecurity-rootca.der" -t "CT,c,C" -d "C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default" | C:\Users\admin\AppData\Local\Temp\certutil.exe | WScript.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2336 | regsvr32 "C:\Program Files\DreamSecurity\SmartMobileSign\SmartMobileSignAuth.dll" /S | C:\Windows\system32\regsvr32.exe | — | MagicMRS.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2584 | "C:\Windows\System32\cmd.exe" /C ImportCAtoFirefox.vbs | C:\Windows\System32\cmd.exe | — | MagicMRS.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2664 | "C:\Users\admin\AppData\Local\Temp\MagicMRS.exe" | C:\Users\admin\AppData\Local\Temp\MagicMRS.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2696 | "C:\Users\admin\AppData\Local\Temp\certmgr.exe" -add dreamsecurity-rootca.der -c -s -r localMachine Root | C:\Users\admin\AppData\Local\Temp\certmgr.exe | — | ns1B34.tmp | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3072 | "C:\Program Files\DreamSecurity\SmartMobileSign\Launcher.exe" | C:\Program Files\DreamSecurity\SmartMobileSign\Launcher.exe | — | MagicMRS.exe | |||||||||||
User: admin Company: DreamSecurity Integrity Level: HIGH Description: 멀티브라우저를 지원하는 인증서복사 Exit code: 0 Version: 1.0.0.3 Modules
| |||||||||||||||
| 3140 | "C:\Users\admin\AppData\Local\Temp\MagicMRS.exe" | C:\Users\admin\AppData\Local\Temp\MagicMRS.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
Total events
1 215
Read events
1 108
Write events
107
Delete events
0
Modification events
| (PID) Process: | (2664) MagicMRS.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones\2 |
| Operation: | write | Name: | 1406 |
Value: 0 | |||
| (PID) Process: | (2664) MagicMRS.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones\2 |
| Operation: | write | Name: | 1607 |
Value: 0 | |||
| (PID) Process: | (2664) MagicMRS.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones\2 |
| Operation: | write | Name: | CurrentLevel |
Value: 0 | |||
| (PID) Process: | (2664) MagicMRS.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones\3 |
| Operation: | write | Name: | 1406 |
Value: 0 | |||
| (PID) Process: | (2664) MagicMRS.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones\3 |
| Operation: | write | Name: | 1607 |
Value: 0 | |||
| (PID) Process: | (2664) MagicMRS.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones\3 |
| Operation: | write | Name: | CurrentLevel |
Value: 0 | |||
| (PID) Process: | (2664) MagicMRS.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2664) MagicMRS.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2584) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2584) cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
25
Suspicious files
3
Text files
7
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2664 | MagicMRS.exe | C:\Users\admin\AppData\Local\Temp\certmgr.exe | — | |
MD5:— | SHA256:— | |||
| 2664 | MagicMRS.exe | C:\Users\admin\AppData\Local\Temp\nsa1509.tmp\ns1B34.tmp | — | |
MD5:— | SHA256:— | |||
| 2252 | certutil.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\key3.db | binary | |
MD5:— | SHA256:— | |||
| 2664 | MagicMRS.exe | C:\Users\admin\AppData\Local\Temp\softokn3.dll | executable | |
MD5:4410D05CC6B0DED09A5526F4A17D1F54 | SHA256:E6454987A148F825305D3BAC056430AA235956BB09B0970B61FDE3F6AE99F9C0 | |||
| 2252 | certutil.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cert8.db | binary | |
MD5:9C69C6CEDD5EE764D496971B28C5A24A | SHA256:E47EACA8AB3788C9AA18412FB0B65D7CA91EC38AE4A8E7A217F67FCB4C86541F | |||
| 2664 | MagicMRS.exe | C:\Users\admin\AppData\Local\Temp\nsa1509.tmp\NsisUtil.dll | executable | |
MD5:59541B9DA3C09F318A58BEF52C9FF131 | SHA256:74A542EF3BBE0673453286DFEB335C1D7BDE4E601C932A3D0D04C85EB098BB47 | |||
| 2664 | MagicMRS.exe | C:\Users\admin\AppData\Local\Temp\smime3.dll | executable | |
MD5:3FF29C1154E061A138E93E9539A4EE7C | SHA256:03C250A0FE3E2E686EDB0F2C017DB17F60A690AB98E8C3CEFA8E620EA964E6C6 | |||
| 2664 | MagicMRS.exe | C:\Users\admin\AppData\Local\Temp\libnspr4.dll | executable | |
MD5:7957E822B5E67AFE2CB64E1FBFC923DB | SHA256:480C54ABD5C555520EE38069D9233B1C2739286471376A56EE66BD756A37FDE2 | |||
| 2664 | MagicMRS.exe | C:\Users\admin\AppData\Local\Temp\nss3.dll | executable | |
MD5:EDCA3446CA38FC3615FE59DCE8B23001 | SHA256:B75FDF34A37F2474B47D3AA043B42B19F8F47AD4E6390F9C3C99FDB1E0918BF5 | |||
| 2664 | MagicMRS.exe | C:\Users\admin\AppData\Local\Temp\certutil.exe | executable | |
MD5:ED17F7213E399B1AF6E8665FF054B703 | SHA256:728AF6F9477B9EF2897DCB912BD02D93BFFB24D435081EC29DB172498B226C43 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report