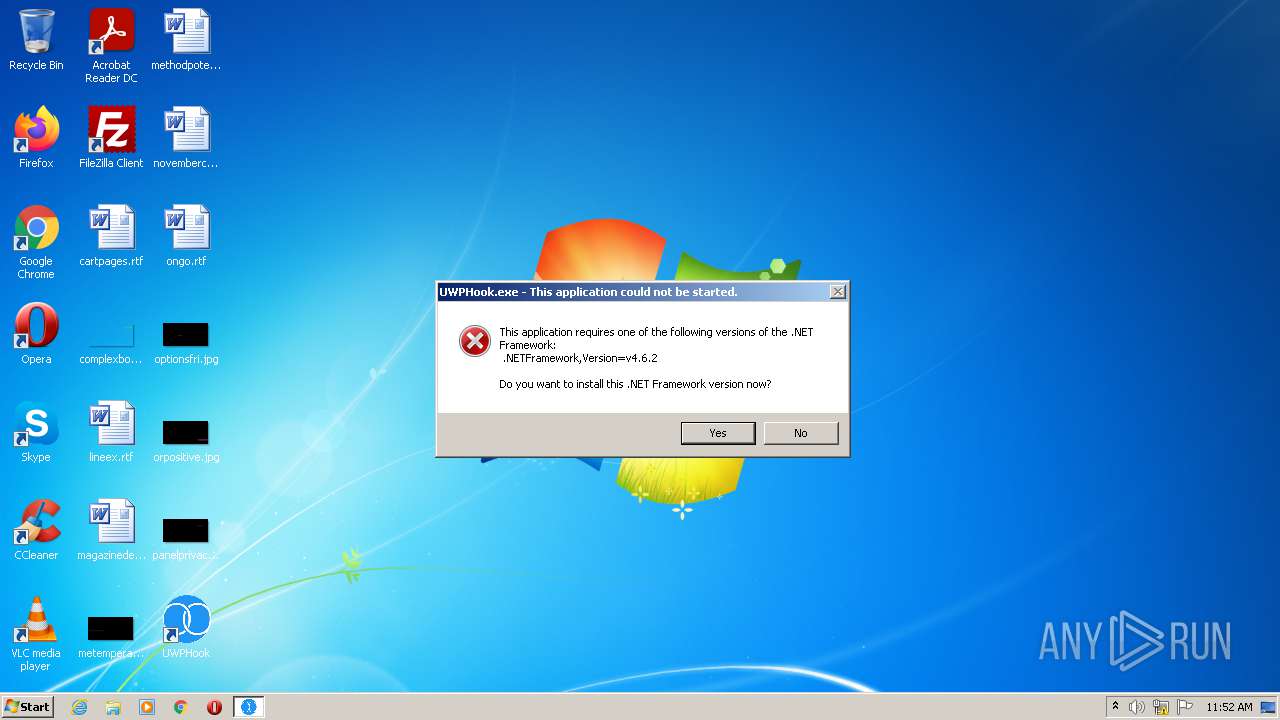
| File name: | UWPHook.exe |
| Full analysis: | https://app.any.run/tasks/ab199958-5d88-4796-9b10-a60c65448066 |
| Verdict: | Malicious activity |
| Analysis date: | November 21, 2021, 11:52:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 495FD640D2E6233EBF22B03CB6744A12 |
| SHA1: | 97ACECA2B2DFBB60285527371B6E1A16FC71B23F |
| SHA256: | 621BD85A78F4F9FDEBDAC6044AFD16982A20785D35F87541A1B7226512A92FFB |
| SSDEEP: | 98304:r9X43cbnlmzL8vVET2SStVCbAihHISb1+5Jick:rB0NXdT2RtojI751k |
MALICIOUS
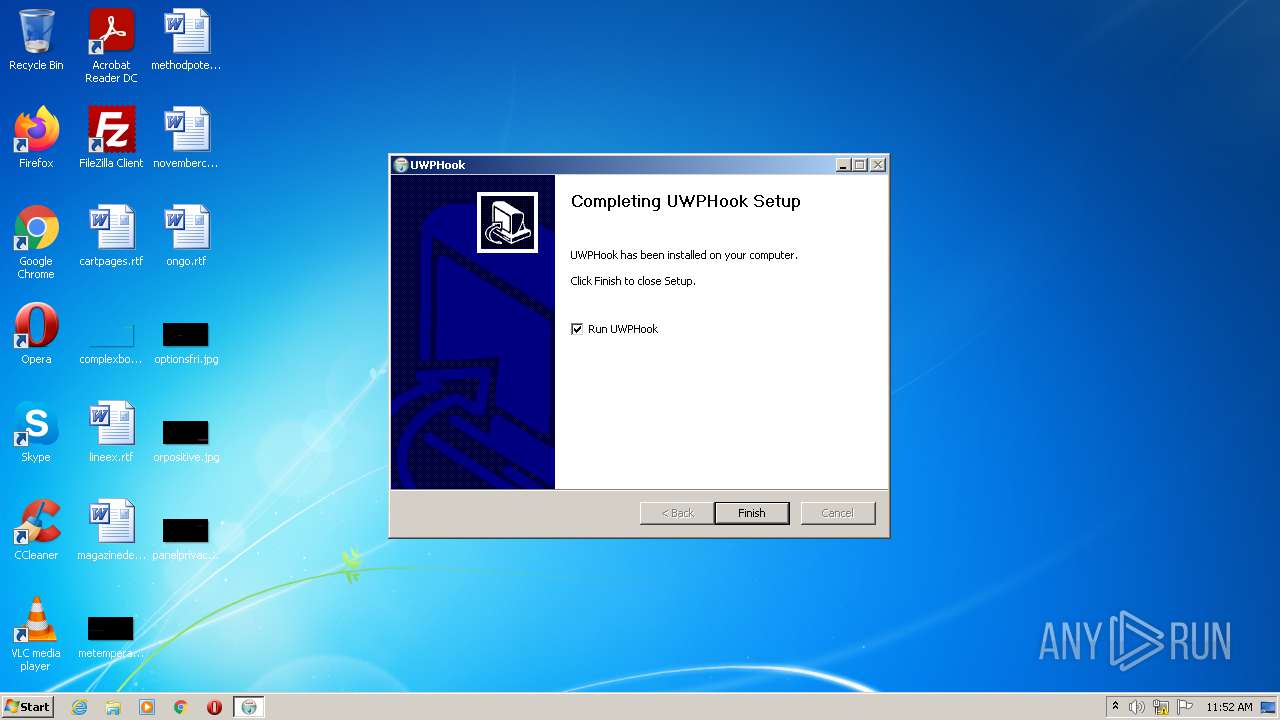
Loads dropped or rewritten executable
- UWPHook.exe (PID: 3648)
Drops executable file immediately after starts
- UWPHook.exe (PID: 3648)
Application was dropped or rewritten from another process
- UWPHook.exe (PID: 3052)
- UWPHook.exe (PID: 4064)
SUSPICIOUS
Reads the computer name
- UWPHook.exe (PID: 3648)
Checks supported languages
- UWPHook.exe (PID: 3648)
- UWPHook.exe (PID: 3052)
- UWPHook.exe (PID: 4064)
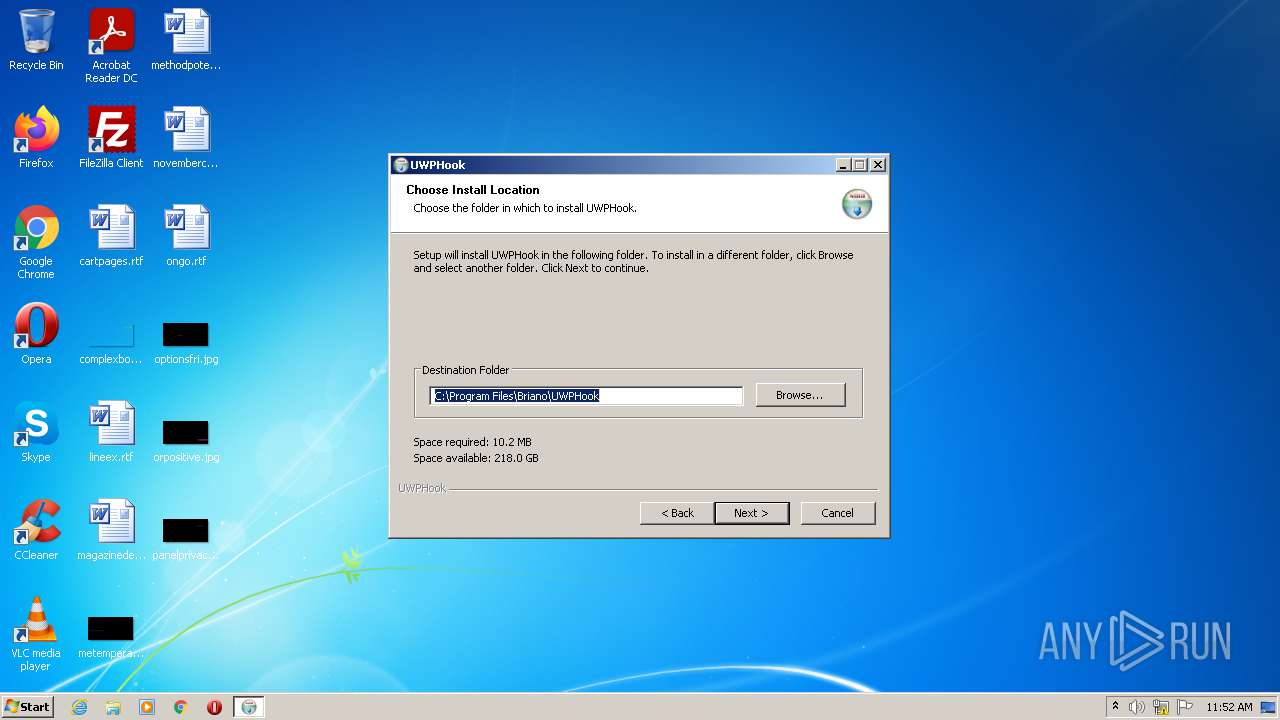
Creates a directory in Program Files
- UWPHook.exe (PID: 3648)
Executable content was dropped or overwritten
- UWPHook.exe (PID: 3648)
Creates files in the program directory
- UWPHook.exe (PID: 3648)
Creates files in the user directory
- UWPHook.exe (PID: 3648)
Drops a file that was compiled in debug mode
- UWPHook.exe (PID: 3648)
Drops a file with a compile date too recent
- UWPHook.exe (PID: 3648)
Creates a software uninstall entry
- UWPHook.exe (PID: 3648)
INFO
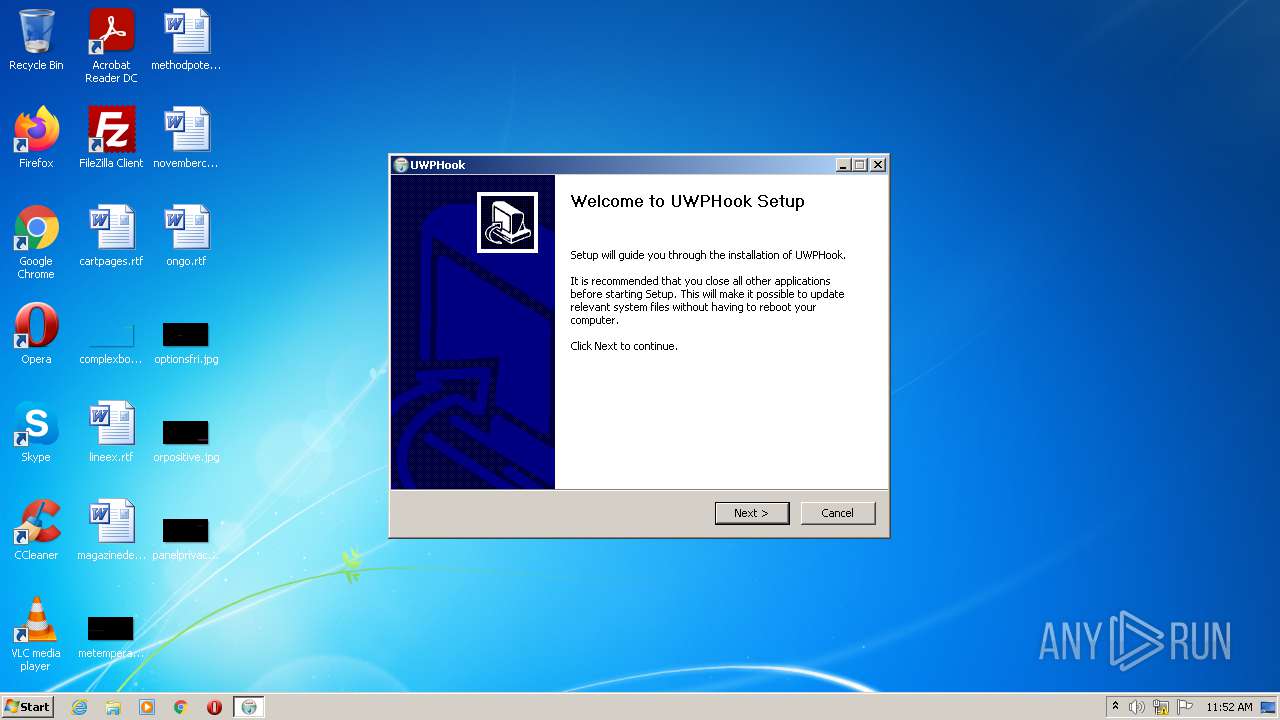
Manual execution by user
- UWPHook.exe (PID: 4064)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:08:01 04:44:50+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26112 |
| InitializedDataSize: | 162816 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x3348 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.10.0.0 |
| ProductVersionNumber: | 2.10.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Briano |
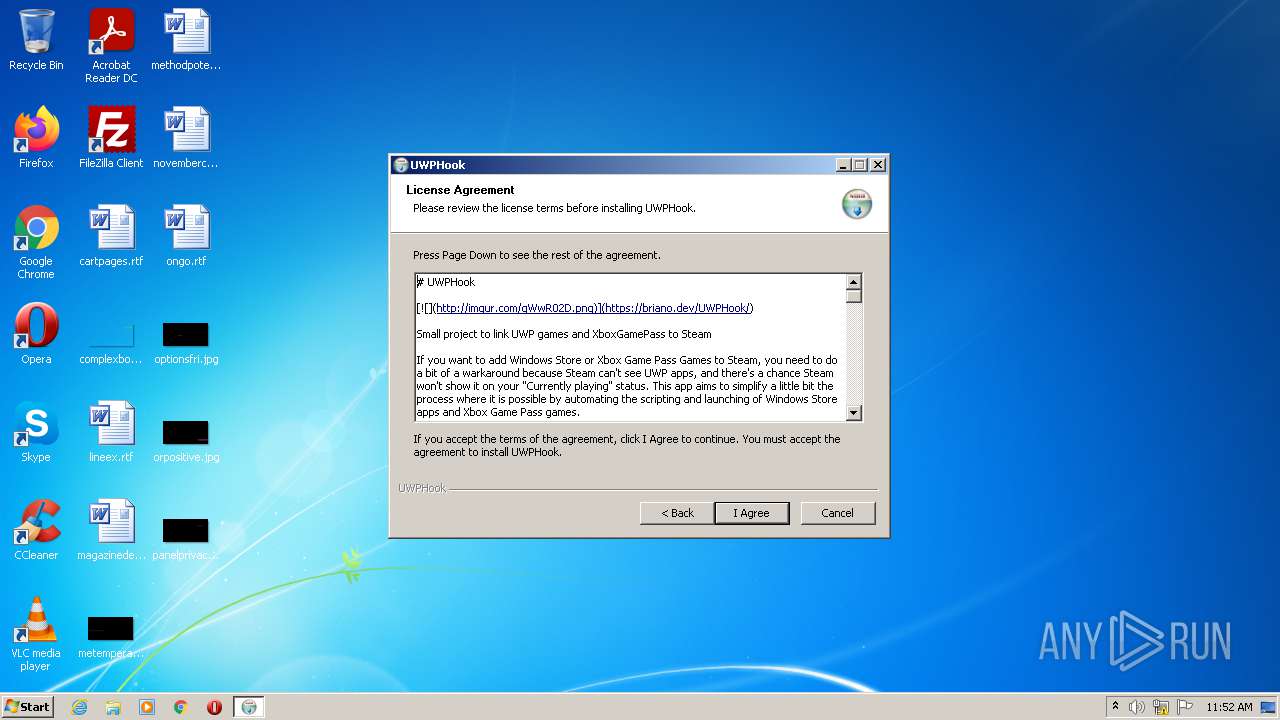
| FileDescription: | The easy way to add UWP and XGP games to Steam |
| FileVersion: | 2.10.00.00 |
| LegalCopyright: | Briano � 2020 2021 |
| ProductName: | UWPHook |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 01-Aug-2020 02:44:50 |
| Detected languages: |
|
| CompanyName: | Briano |
| FileDescription: | The easy way to add UWP and XGP games to Steam |
| FileVersion: | 2.10.00.00 |
| LegalCopyright: | Briano � 2020 2021 |
| ProductName: | UWPHook |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000C8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 01-Aug-2020 02:44:50 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006457 | 0x00006600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.43499 |
.rdata | 0x00008000 | 0x00001380 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.261 |
.data | 0x0000A000 | 0x00025538 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.13373 |
.ndata | 0x00030000 | 0x0000A000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0003A000 | 0x000046B0 | 0x00004800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.83392 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.2901 | 1072 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.9993 | 3752 | UNKNOWN | English - United States | RT_ICON |
3 | 6.24459 | 2216 | UNKNOWN | English - United States | RT_ICON |
4 | 5.01502 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 6.16057 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 3.34146 | 744 | UNKNOWN | English - United States | RT_ICON |
7 | 3.04232 | 296 | UNKNOWN | English - United States | RT_ICON |
102 | 2.71813 | 180 | UNKNOWN | English - United States | RT_DIALOG |
103 | 2.6691 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
41
Monitored processes
4
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
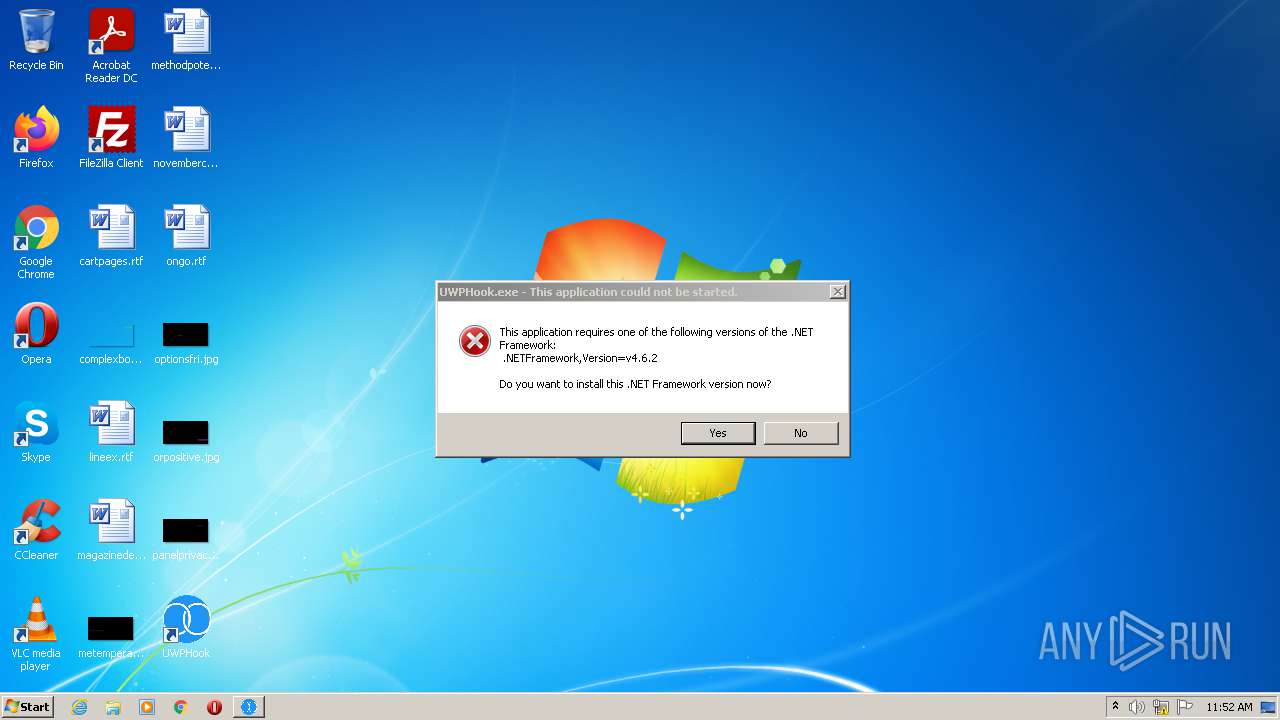
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3052 | "C:\Program Files\Briano\UWPHook\UWPHook.exe" | C:\Program Files\Briano\UWPHook\UWPHook.exe | — | UWPHook.exe | |||||||||||
User: admin Company: Briano Integrity Level: HIGH Description: UWPHook Exit code: 2148734720 Version: 2.10.0.0 Modules
| |||||||||||||||
| 3292 | "C:\Users\admin\AppData\Local\Temp\UWPHook.exe" | C:\Users\admin\AppData\Local\Temp\UWPHook.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Briano Integrity Level: MEDIUM Description: The easy way to add UWP and XGP games to Steam Exit code: 3221226540 Version: 2.10.00.00 Modules
| |||||||||||||||
| 3648 | "C:\Users\admin\AppData\Local\Temp\UWPHook.exe" | C:\Users\admin\AppData\Local\Temp\UWPHook.exe | Explorer.EXE | ||||||||||||
User: admin Company: Briano Integrity Level: HIGH Description: The easy way to add UWP and XGP games to Steam Exit code: 0 Version: 2.10.00.00 Modules
| |||||||||||||||
| 4064 | "C:\Program Files\Briano\UWPHook\UWPHook.exe" | C:\Program Files\Briano\UWPHook\UWPHook.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Briano Integrity Level: MEDIUM Description: UWPHook Exit code: 2148734720 Version: 2.10.0.0 Modules
| |||||||||||||||
Total events
777
Read events
769
Write events
8
Delete events
0
Modification events
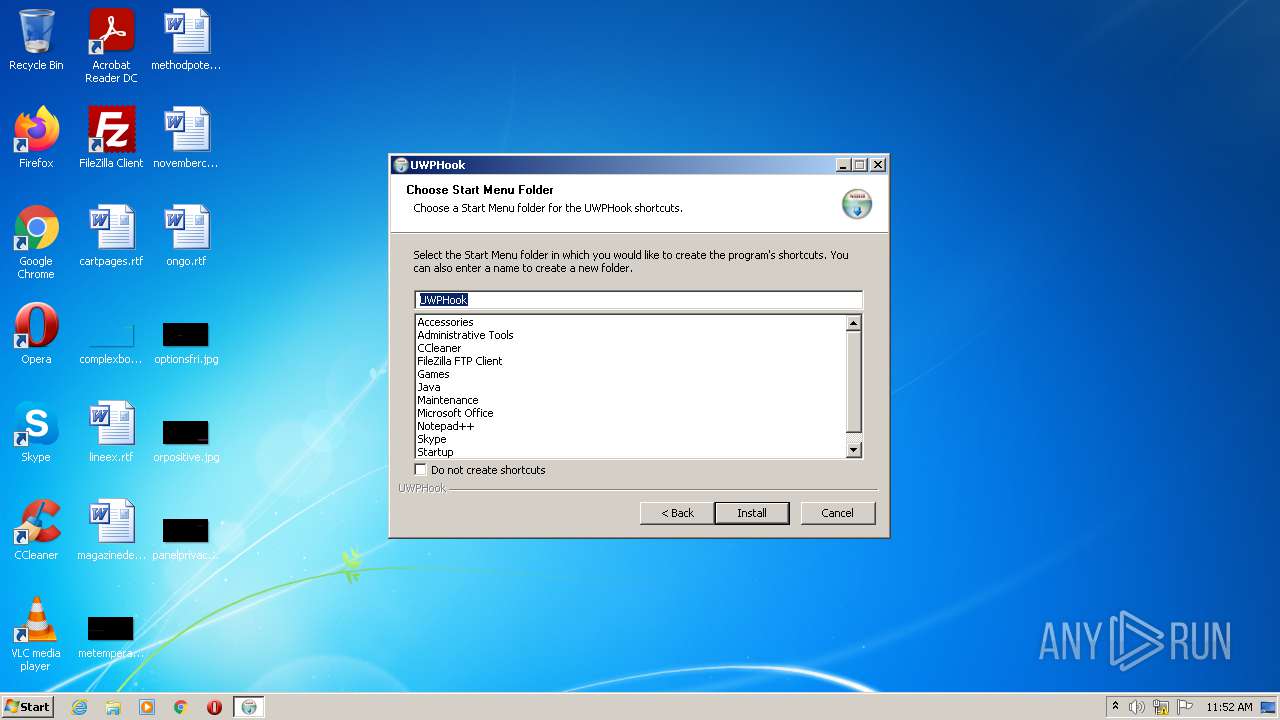
| (PID) Process: | (3648) UWPHook.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\UWPHook |
| Operation: | write | Name: | Start Menu Folder |
Value: UWPHook | |||
| (PID) Process: | (3648) UWPHook.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\App Paths\UWPHook.exe |
| Operation: | write | Name: | (default) |
Value: C:\Program Files\Briano\UWPHook\UWPHook.exe | |||
| (PID) Process: | (3648) UWPHook.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\UWPHook |
| Operation: | write | Name: | DisplayName |
Value: UWPHook | |||
| (PID) Process: | (3648) UWPHook.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\UWPHook |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files\Briano\UWPHook\uninstall.exe | |||
| (PID) Process: | (3648) UWPHook.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\UWPHook |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\Briano\UWPHook\UWPHook.exe | |||
| (PID) Process: | (3648) UWPHook.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\UWPHook |
| Operation: | write | Name: | DisplayVersion |
Value: 2.10.00.00 | |||
| (PID) Process: | (3648) UWPHook.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\UWPHook |
| Operation: | write | Name: | Publisher |
Value: Briano | |||
| (PID) Process: | (3648) UWPHook.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\UWPHook |
| Operation: | write | Name: | URLInfoAbout |
Value: https://briano.dev | |||
Executable files
14
Suspicious files
0
Text files
4
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3648 | UWPHook.exe | C:\Program Files\Briano\UWPHook\MaterialDesignColors.dll | executable | |
MD5:2225A7AF996769188C2ED7CC035E88DA | SHA256:93101E1979A769BFFD591E8BE5FA42A8E3D87AA1B59E58A7D1A40D2711C1B028 | |||
| 3648 | UWPHook.exe | C:\Users\admin\AppData\Local\Temp\nse10C1.tmp\modern-wizard.bmp | image | |
MD5:CBE40FD2B1EC96DAEDC65DA172D90022 | SHA256:3AD2DC318056D0A2024AF1804EA741146CFC18CC404649A44610CBF8B2056CF2 | |||
| 3648 | UWPHook.exe | C:\Users\admin\AppData\Local\Temp\nse10C1.tmp\InstallOptions.dll | executable | |
MD5:5F35212D7E90EE622B10BE39B09BD270 | SHA256:31944B93E44301974D9C6F810D2DA792E34A53DCACD619A08CB0385AC59E513D | |||
| 3648 | UWPHook.exe | C:\Program Files\Briano\UWPHook\VDFParser.dll | executable | |
MD5:— | SHA256:— | |||
| 3648 | UWPHook.exe | C:\Program Files\Briano\UWPHook\uninstall.exe | executable | |
MD5:— | SHA256:— | |||
| 3648 | UWPHook.exe | C:\Program Files\Briano\UWPHook\SharpSteam.dll | executable | |
MD5:— | SHA256:— | |||
| 3648 | UWPHook.exe | C:\Program Files\Briano\UWPHook\UWPHook.exe.config | xml | |
MD5:— | SHA256:— | |||
| 3648 | UWPHook.exe | C:\Program Files\Briano\UWPHook\UWPHook.exe | executable | |
MD5:— | SHA256:— | |||
| 3648 | UWPHook.exe | C:\Program Files\Briano\UWPHook\MaterialDesignThemes.Wpf.dll | executable | |
MD5:CB3252EF55CEB9CDCAB715999E25516C | SHA256:26DAD78DA7BFB24D2046F3AA86F6FE779844FB3681BAAEECA08404F4AB9FDBF0 | |||
| 3648 | UWPHook.exe | C:\Program Files\Briano\UWPHook\System.Net.Http.Formatting.dll | executable | |
MD5:B676D5E9828D6010339743F236F54EC4 | SHA256:7B58ADC6E23B24CD6615B35E848A002BDA053A26D48F9DDAFACFC8098E97C49C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report