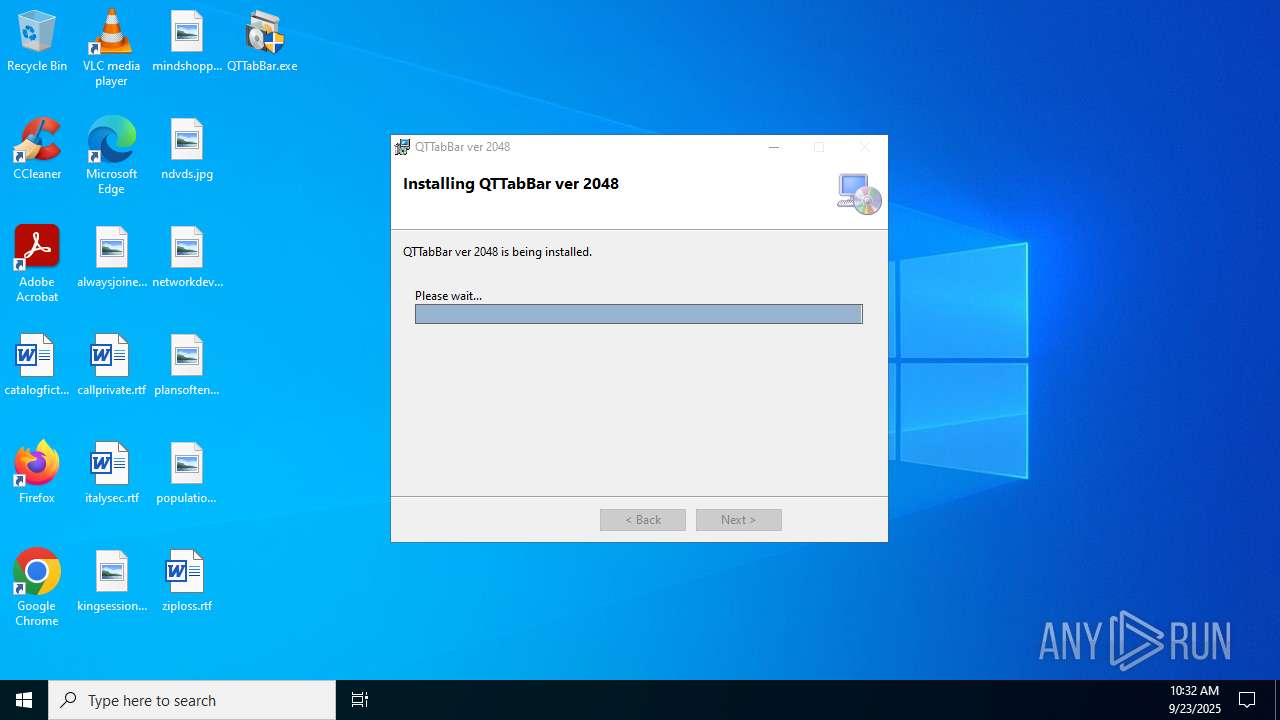
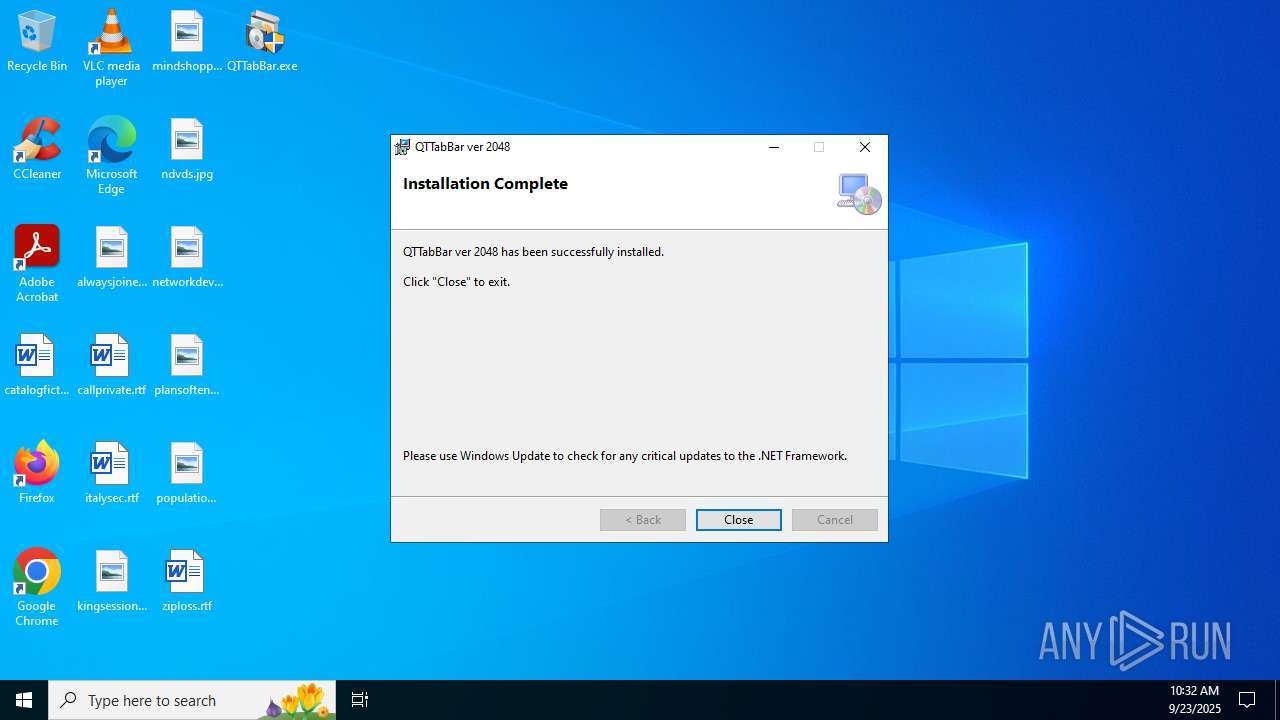
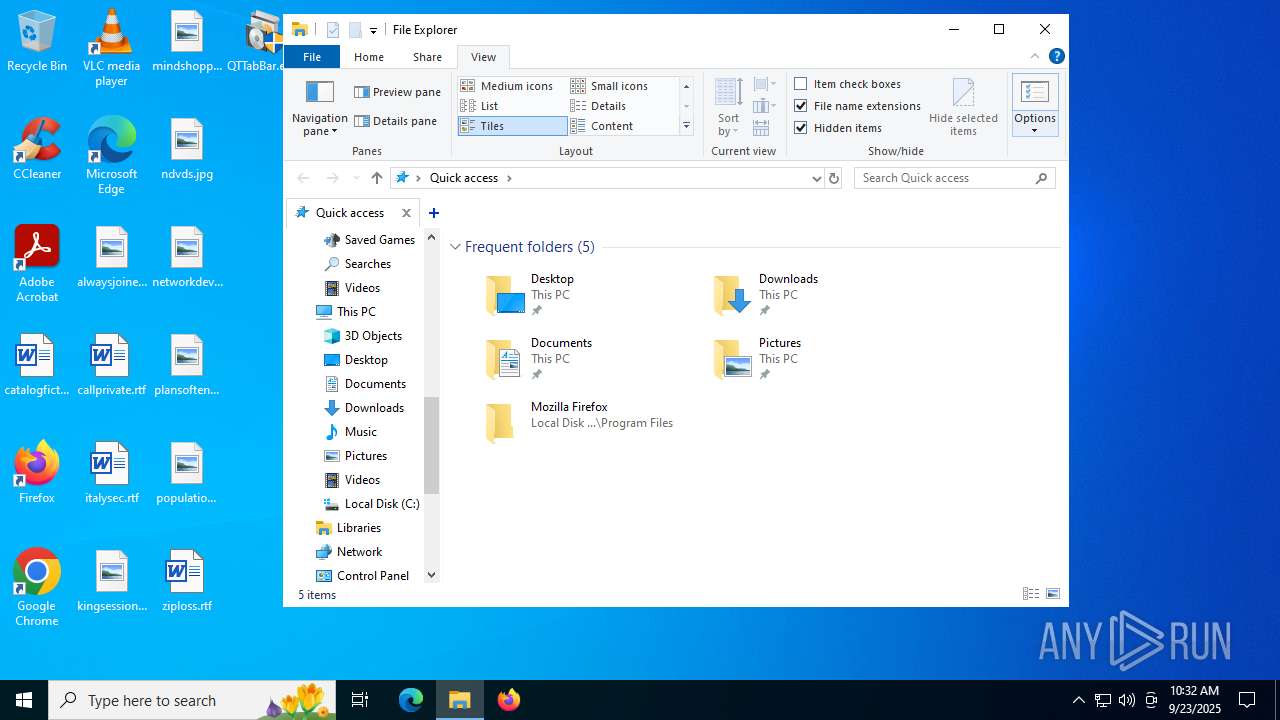
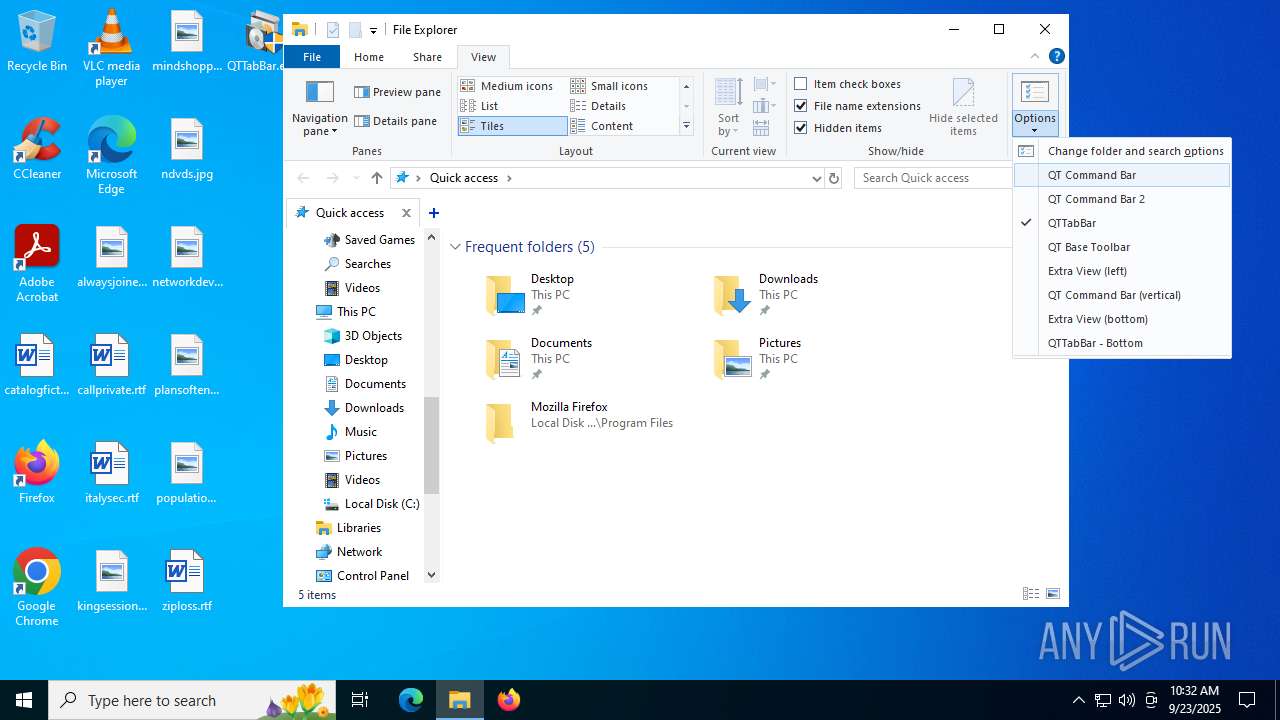
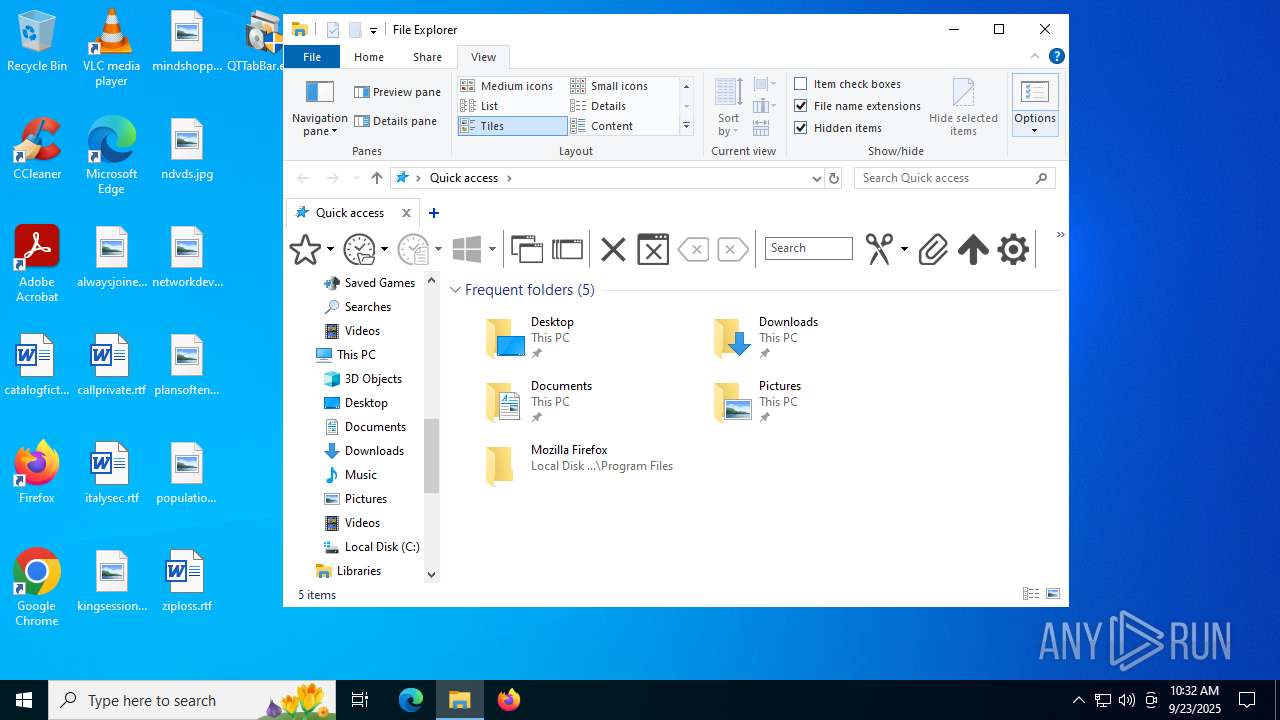
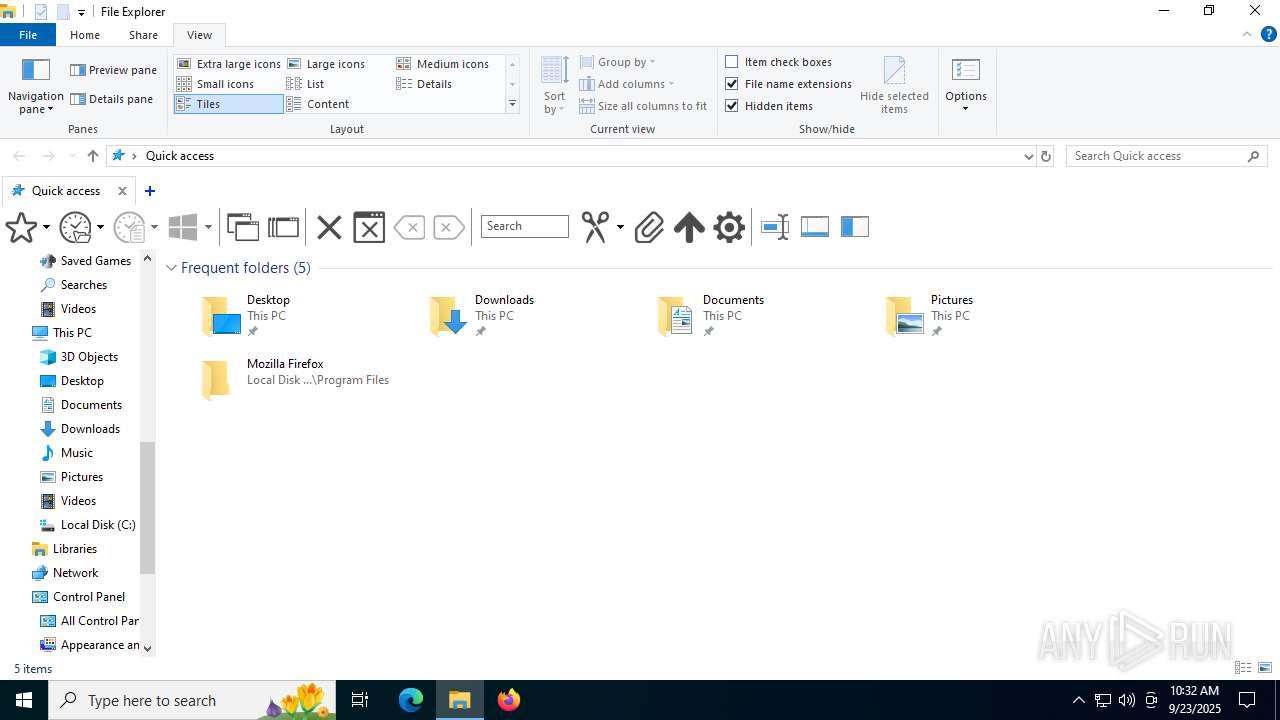
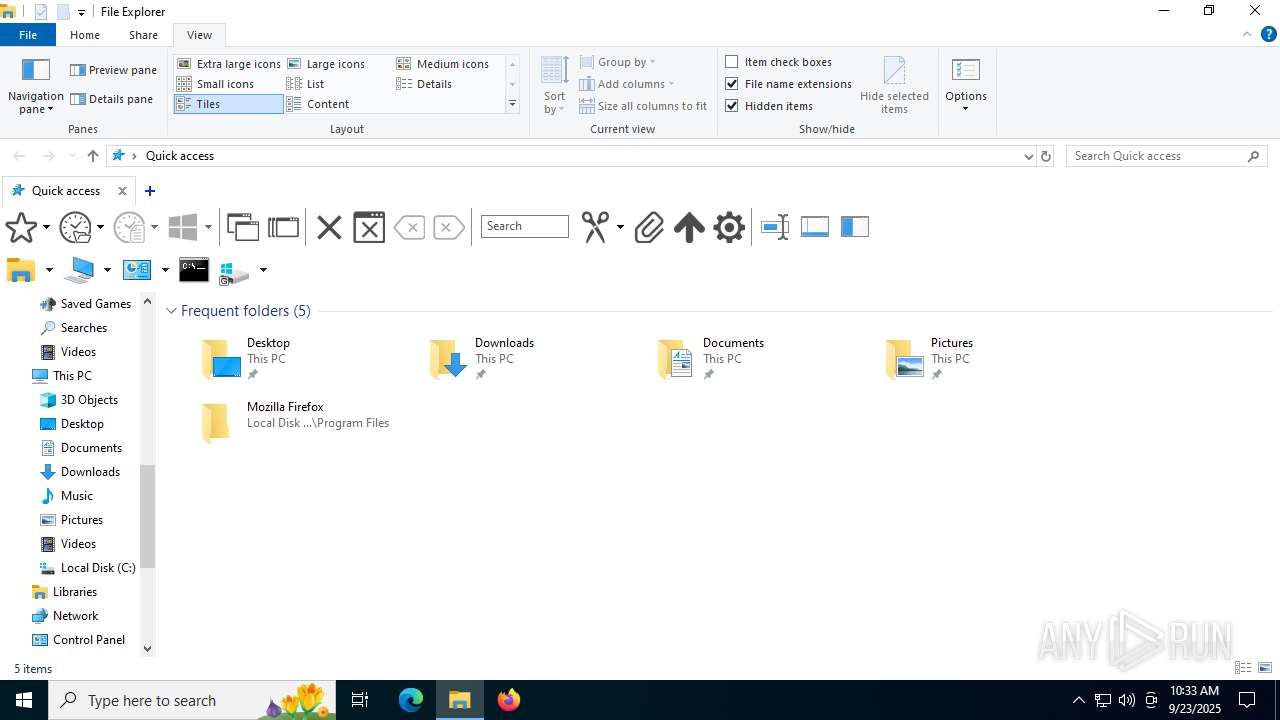
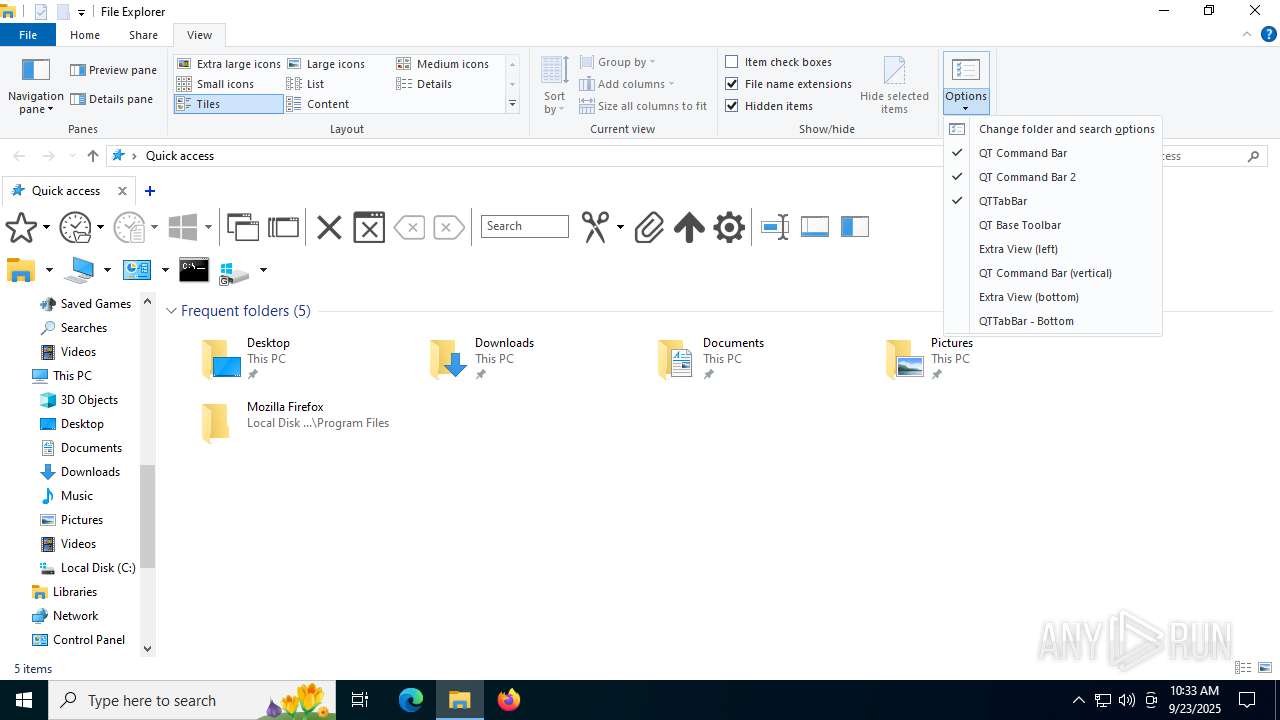
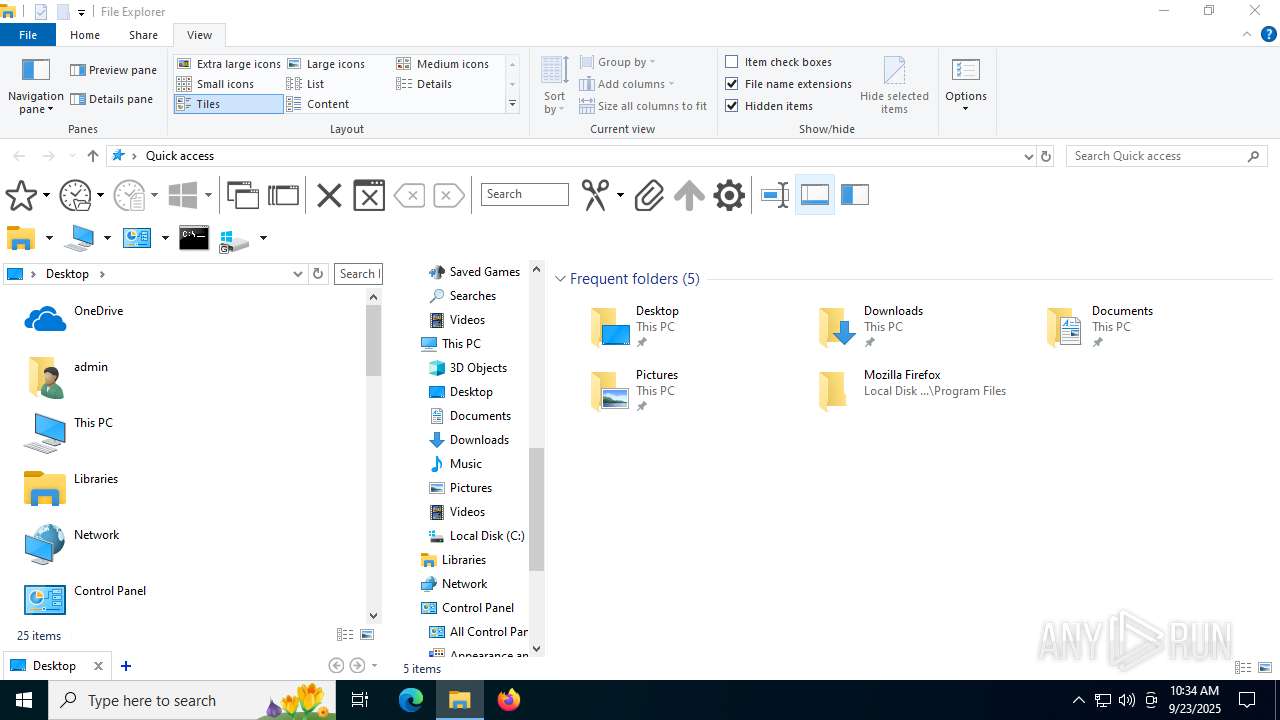
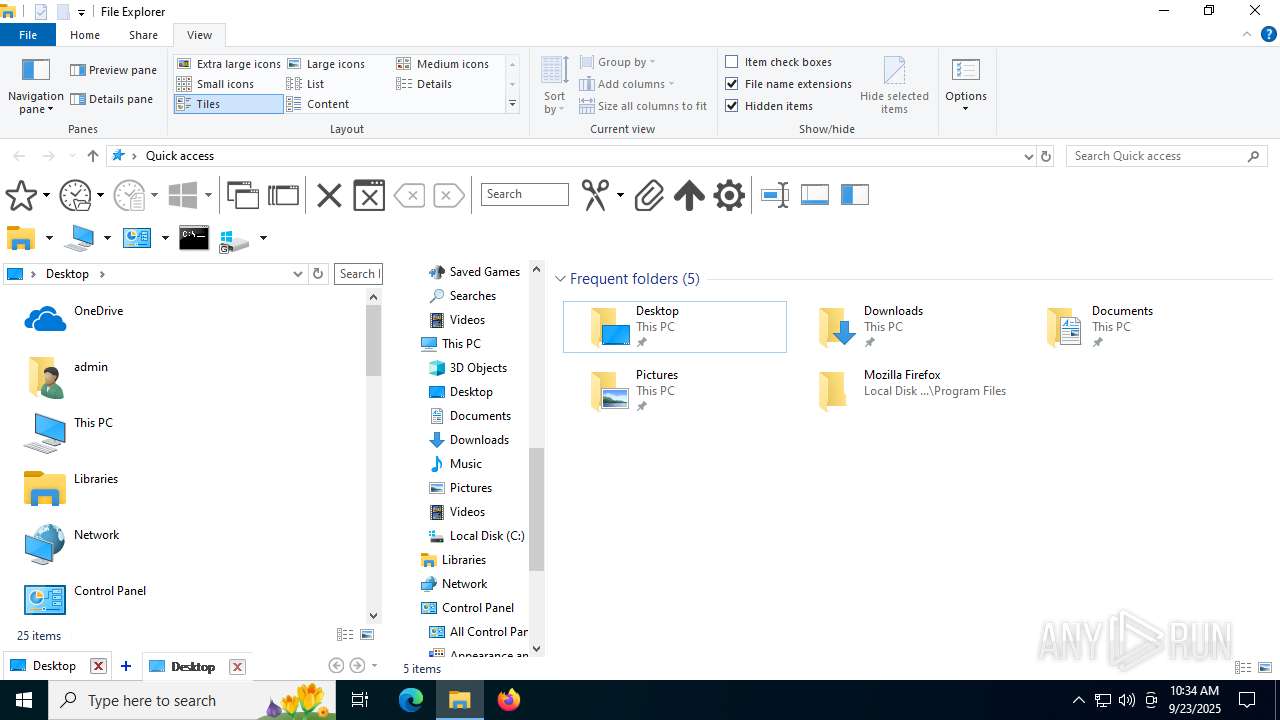
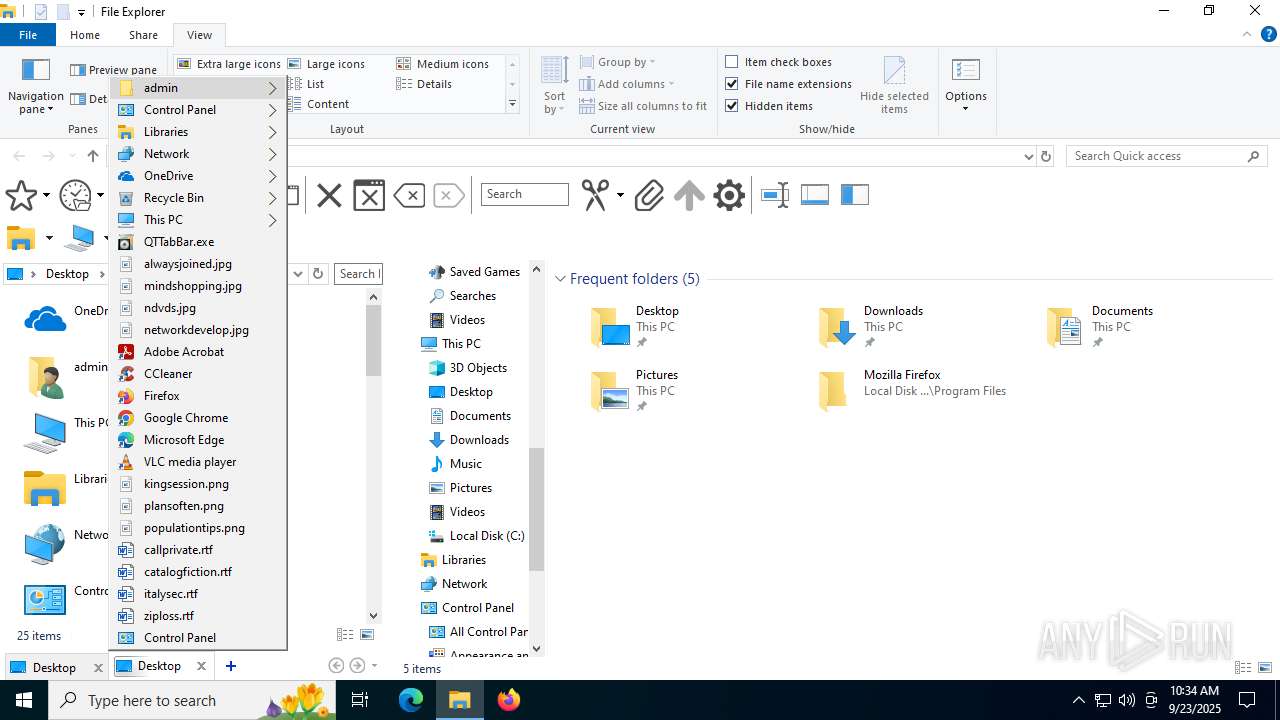
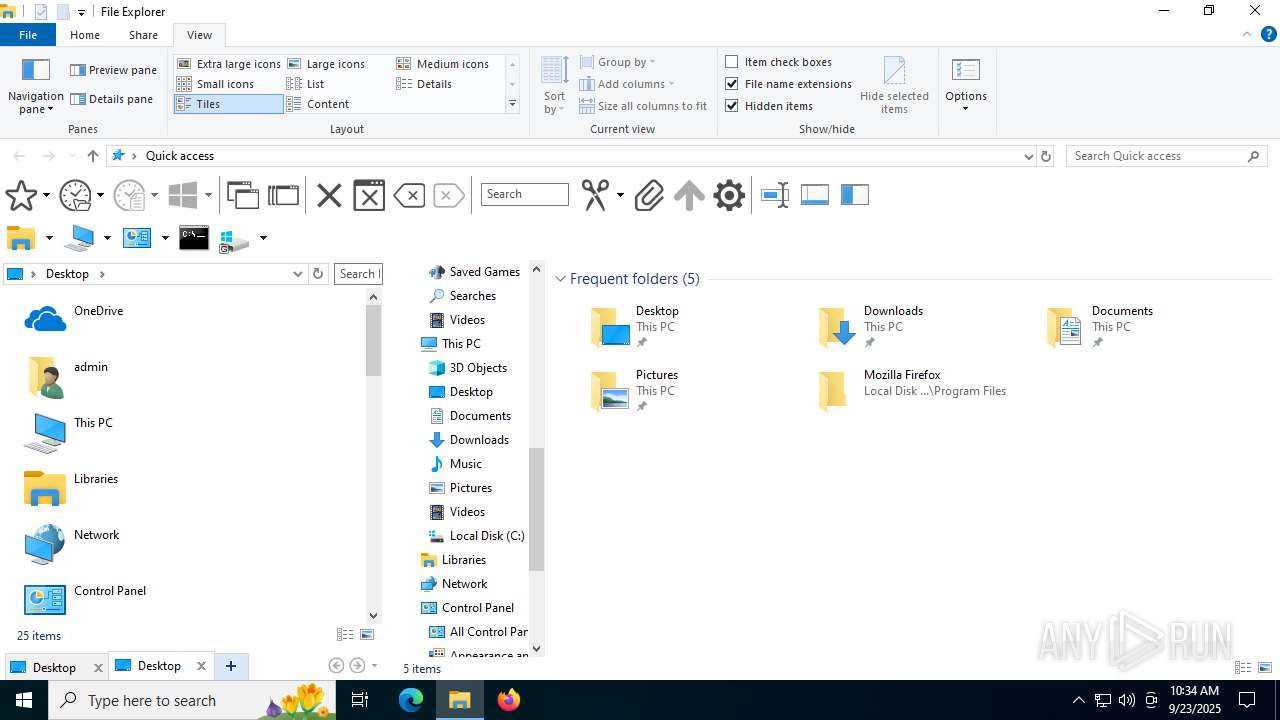
| File name: | QTTabBar.exe |
| Full analysis: | https://app.any.run/tasks/8b513d76-2f9b-457f-b22b-5529f211e0ce |
| Verdict: | Malicious activity |
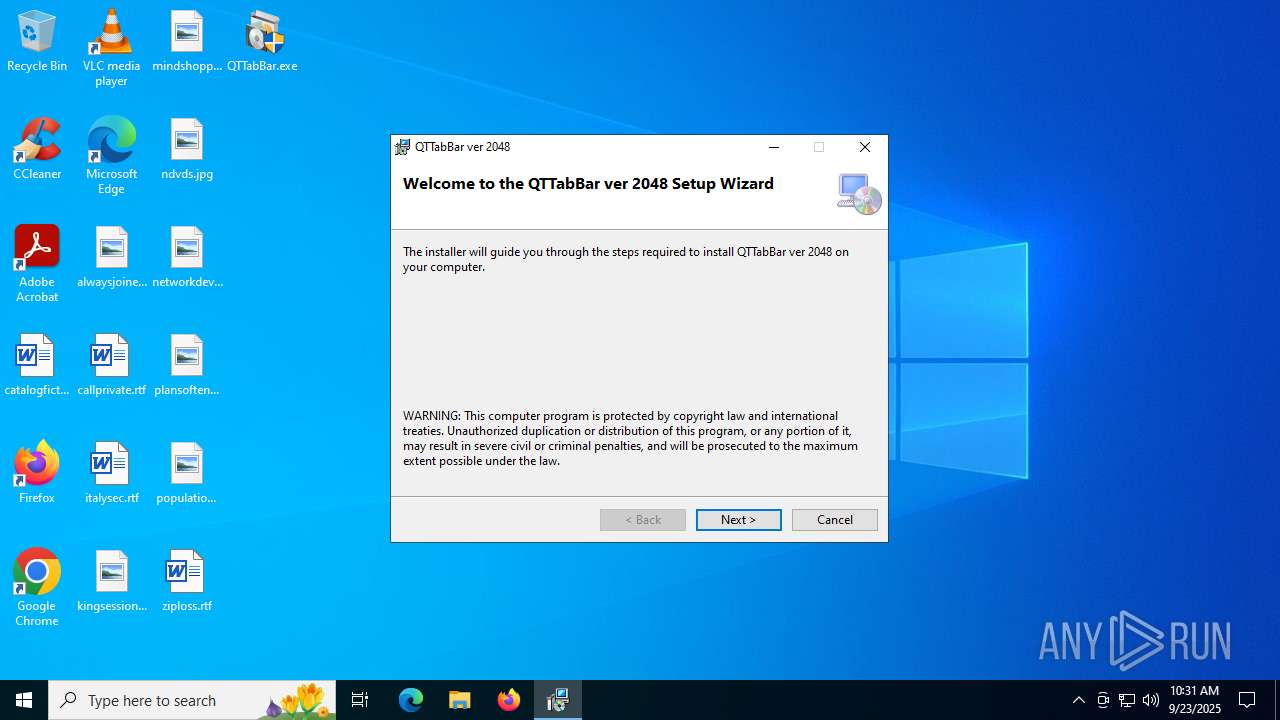
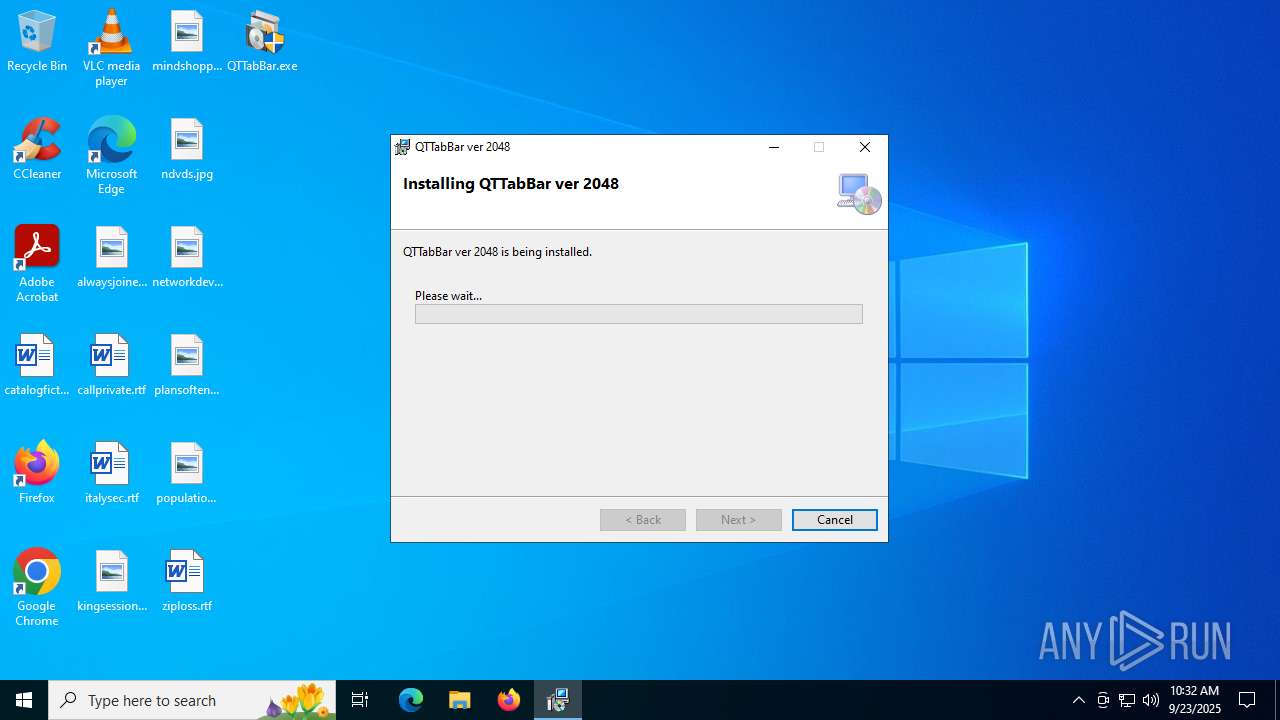
| Analysis date: | September 23, 2025, 10:31:46 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows, 3 sections |
| MD5: | 1A4782A50C18736761528BC51678EEFC |
| SHA1: | FEF48925960E8A59CB08B98480ACEF768CB9D195 |
| SHA256: | 6201B32BAE395974CADFC9059AED718313D2879560C2F6F11B73824CFD60BA47 |
| SSDEEP: | 98304:u0el1e+DEreL40FOczKDZj1jxTHrNRtCaVdrG7009gTlwEpEc5PYKbn9YWtsrIAN:sUjA8A |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- QTTabBar.exe (PID: 1644)
- SetupHelper.exe (PID: 5684)
- mscorsvw.exe (PID: 4060)
- mscorsvw.exe (PID: 4188)
Reads security settings of Internet Explorer
- QTTabBar.exe (PID: 1644)
- RegAsm.exe (PID: 2580)
- StartMenuExperienceHost.exe (PID: 5244)
Reads the date of Windows installation
- QTTabBar.exe (PID: 1644)
- StartMenuExperienceHost.exe (PID: 5244)
- SearchApp.exe (PID: 4788)
Executes as Windows Service
- VSSVC.exe (PID: 6304)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 4684)
Process drops legitimate windows executable
- msiexec.exe (PID: 4684)
Creates/Modifies COM task schedule object
- RegAsm.exe (PID: 2580)
INFO
Reads the machine GUID from the registry
- QTTabBar.exe (PID: 1644)
- msiexec.exe (PID: 4684)
- RegAsm.exe (PID: 2580)
- mscorsvw.exe (PID: 6404)
- ngen.exe (PID: 4512)
- mscorsvw.exe (PID: 6368)
- mscorsvw.exe (PID: 4060)
- ngen.exe (PID: 4580)
- mscorsvw.exe (PID: 4188)
- SearchApp.exe (PID: 4788)
Checks supported languages
- QTTabBar.exe (PID: 1644)
- msiexec.exe (PID: 4684)
- msiexec.exe (PID: 5468)
- msiexec.exe (PID: 1180)
- SetupHelper.exe (PID: 5684)
- RegAsm.exe (PID: 2580)
- ngen.exe (PID: 4512)
- ngen.exe (PID: 4580)
- mscorsvw.exe (PID: 6404)
- mscorsvw.exe (PID: 4060)
- mscorsvw.exe (PID: 6368)
- mscorsvw.exe (PID: 4188)
- StartMenuExperienceHost.exe (PID: 5244)
- TextInputHost.exe (PID: 6060)
- SearchApp.exe (PID: 4788)
Create files in a temporary directory
- QTTabBar.exe (PID: 1644)
- msiexec.exe (PID: 5468)
- msiexec.exe (PID: 1180)
- msiexec.exe (PID: 4684)
Reads the computer name
- QTTabBar.exe (PID: 1644)
- msiexec.exe (PID: 4684)
- msiexec.exe (PID: 5468)
- msiexec.exe (PID: 1180)
- SetupHelper.exe (PID: 5684)
- RegAsm.exe (PID: 2580)
- ngen.exe (PID: 4580)
- ngen.exe (PID: 4512)
- mscorsvw.exe (PID: 6404)
- mscorsvw.exe (PID: 6368)
- mscorsvw.exe (PID: 4188)
- mscorsvw.exe (PID: 4060)
- TextInputHost.exe (PID: 6060)
- SearchApp.exe (PID: 4788)
- StartMenuExperienceHost.exe (PID: 5244)
Process checks computer location settings
- QTTabBar.exe (PID: 1644)
- StartMenuExperienceHost.exe (PID: 5244)
- SearchApp.exe (PID: 4788)
The sample compiled with english language support
- msiexec.exe (PID: 4072)
- msiexec.exe (PID: 4684)
Executable content was dropped or overwritten
- msiexec.exe (PID: 4072)
- msiexec.exe (PID: 4684)
Manages system restore points
- SrTasks.exe (PID: 2604)
Creates a software uninstall entry
- msiexec.exe (PID: 4684)
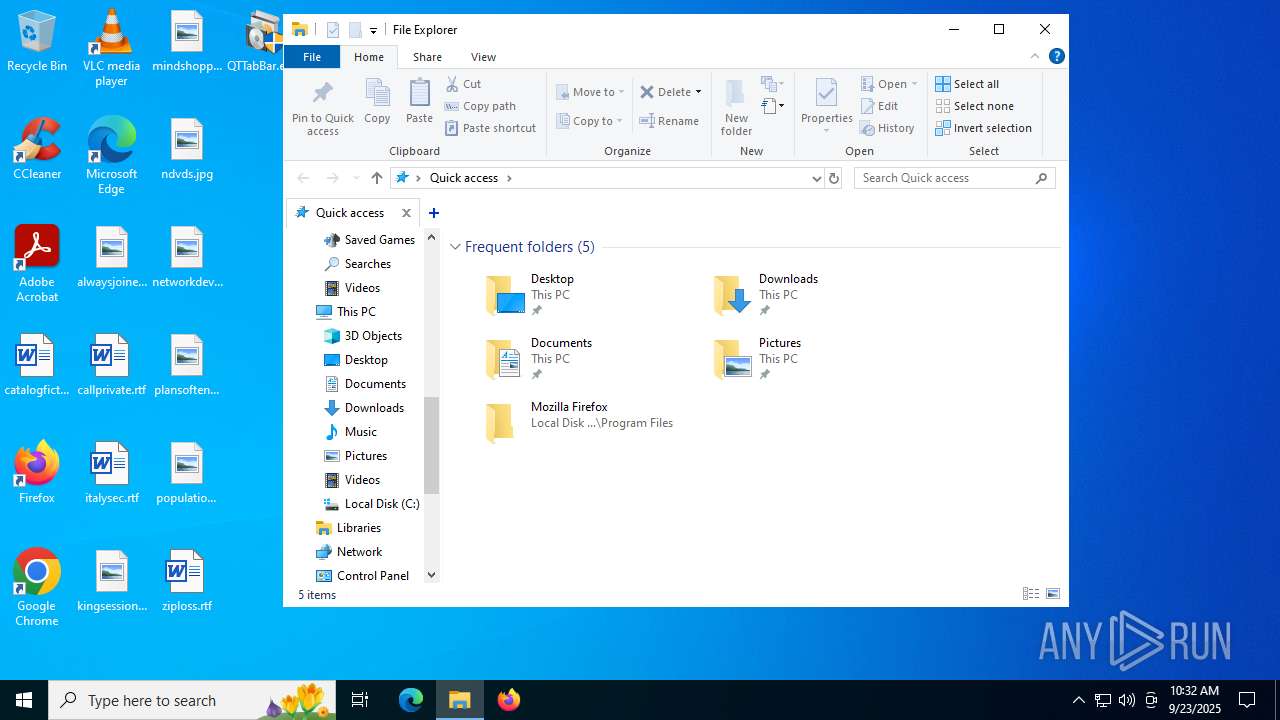
Creates files or folders in the user directory
- msiexec.exe (PID: 4684)
Creates files in the program directory
- SetupHelper.exe (PID: 5684)
Checks proxy server information
- SearchApp.exe (PID: 4788)
- slui.exe (PID: 7828)
Reads the software policy settings
- SearchApp.exe (PID: 4788)
- slui.exe (PID: 7828)
Reads Environment values
- SearchApp.exe (PID: 4788)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:09:19 05:42:40+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32 |
| LinkerVersion: | 48 |
| CodeSize: | 4184064 |
| InitializedDataSize: | 48640 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3ff7da |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | QTTabBar msi launcher |
| CompanyName: | Quizo |
| FileDescription: | QTTabBar Installer |
| FileVersion: | 1.0.0.0 |
| InternalName: | QTTabBar.exe |
| LegalCopyright: | Copyright Quizo © 2021 |
| LegalTrademarks: | - |
| OriginalFileName: | QTTabBar.exe |
| ProductName: | QTTabBar |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
174
Monitored processes
26
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 856 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | RegAsm.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1180 | C:\Windows\syswow64\MsiExec.exe -Embedding 39F3BB6C5FFDAC16EC01BDE6C0EC1FF4 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1508 | "C:\Users\admin\Desktop\QTTabBar.exe" | C:\Users\admin\Desktop\QTTabBar.exe | — | explorer.exe | |||||||||||
User: admin Company: Quizo Integrity Level: MEDIUM Description: QTTabBar Installer Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1644 | "C:\Users\admin\Desktop\QTTabBar.exe" | C:\Users\admin\Desktop\QTTabBar.exe | explorer.exe | ||||||||||||
User: admin Company: Quizo Integrity Level: HIGH Description: QTTabBar Installer Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1864 | C:\WINDOWS\winsxs\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe -Embedding | C:\Windows\WinSxS\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Modules Installer Worker Exit code: 0 Version: 10.0.19041.3989 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2580 | "C:\Windows\Microsoft.NET\Framework64\v4.0.30319\RegAsm.exe" "C:\ProgramData\Quizo\QTTabBar.dll" /verbose | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\RegAsm.exe | — | SetupHelper.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 2604 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3888 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | ngen.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4060 | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\mscorsvw.exe -StartupEvent 2a0 -InterruptEvent 0 -NGENProcess 284 -Pipe 29c -Comment "NGen Worker Process" | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\mscorsvw.exe | ngen.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: .NET Runtime Optimization Service Exit code: 0 Version: 4.8.9093.0 built by: NET481REL1LAST_C Modules
| |||||||||||||||
| 4072 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\QTTabBar_40alzm5v.5fx\QTTabBar Setup.msi" REINSTALL=ALL REINSTALLMODE=vamus | C:\Windows\System32\msiexec.exe | QTTabBar.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
28 644
Read events
27 993
Write events
625
Delete events
26
Modification events
| (PID) Process: | (4684) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000C659754B752CDC014C120000CC1B0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4684) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 480000000000000036BD774B752CDC014C120000CC1B0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4684) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 480000000000000062B9964B752CDC014C120000CC1B0000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4684) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 480000000000000062B9964B752CDC014C120000CC1B0000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4684) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 480000000000000062B9964B752CDC014C120000CC1B0000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4684) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4800000000000000C3809B4B752CDC014C120000CC1B0000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4684) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (6304) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\11000001 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6304) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\11000001 |
| Operation: | write | Name: | Element |
Value: 0000000000000000000000000000000006000000000000004800000000000000715E5C2FA985EB1190A89A9B763584210000000000000000745E5C2FA985EB1190A89A9B7635842100000000000000000000000000000000 | |||
| (PID) Process: | (6304) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\12000002 |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
35
Suspicious files
68
Text files
137
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4684 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 4684 | msiexec.exe | C:\Windows\Installer\MSI19B8.tmp | executable | |
MD5:9945F10135A4C7214FA5605C21E5DE9B | SHA256:9F3B0F3AF4BFA061736935BAB1D50ED2581358DDC9A9C0DB22564ACED1A1807C | |||
| 5468 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\CFGCDAB.tmp | xml | |
MD5:2BE48F533744EFA173A2EDE37EA8031E | SHA256:02375FA63B79648ED6BB419C08F78BA9032EE22BA7170250E24427F47FDDFA4E | |||
| 4684 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{c64b87f1-f62d-4867-93a8-87ee41bbd2a5}_OnDiskSnapshotProp | binary | |
MD5:5653EB7D1A421866B9F899218F9032C9 | SHA256:D19450618123383D76093E2BA77CE1C505EDF80E79A24BD19EC3161F0D1F4D24 | |||
| 4684 | msiexec.exe | C:\Windows\Installer\inprogressinstallinfo.ipi | binary | |
MD5:95B04B3E744D87291B8C21682241A2C4 | SHA256:77A8E407436914DE8E7C5A7A6B50C901002300EE1B212910885B436514CE61D8 | |||
| 4684 | msiexec.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:5653EB7D1A421866B9F899218F9032C9 | SHA256:D19450618123383D76093E2BA77CE1C505EDF80E79A24BD19EC3161F0D1F4D24 | |||
| 4072 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSICDBC.tmp | executable | |
MD5:9945F10135A4C7214FA5605C21E5DE9B | SHA256:9F3B0F3AF4BFA061736935BAB1D50ED2581358DDC9A9C0DB22564ACED1A1807C | |||
| 4684 | msiexec.exe | C:\Windows\Installer\1918fc.msi | executable | |
MD5:D4657E4D3A2D1117C5BC97C4393FE75A | SHA256:4C313671BCC34AD60AF66E0E890DAB95AE2E6D8BB16785087EA0836506631909 | |||
| 4684 | msiexec.exe | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\ngen.log | text | |
MD5:77AE1EC4A96723D89A69CF65AE938DFB | SHA256:D58310BA10FE6307979F3AFF2035E20D571A8E49CC73D51D07CD5D71999465DD | |||
| 1180 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\CFG1A45.tmp | xml | |
MD5:2BE48F533744EFA173A2EDE37EA8031E | SHA256:02375FA63B79648ED6BB419C08F78BA9032EE22BA7170250E24427F47FDDFA4E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
41
DNS requests
25
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.216.77.37:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6936 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6724 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6724 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6724 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.37:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
6724 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
6724 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | unknown | — | — | whitelisted |
6724 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5460 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 23.216.77.37:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4832 | svchost.exe | 23.35.238.131:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |