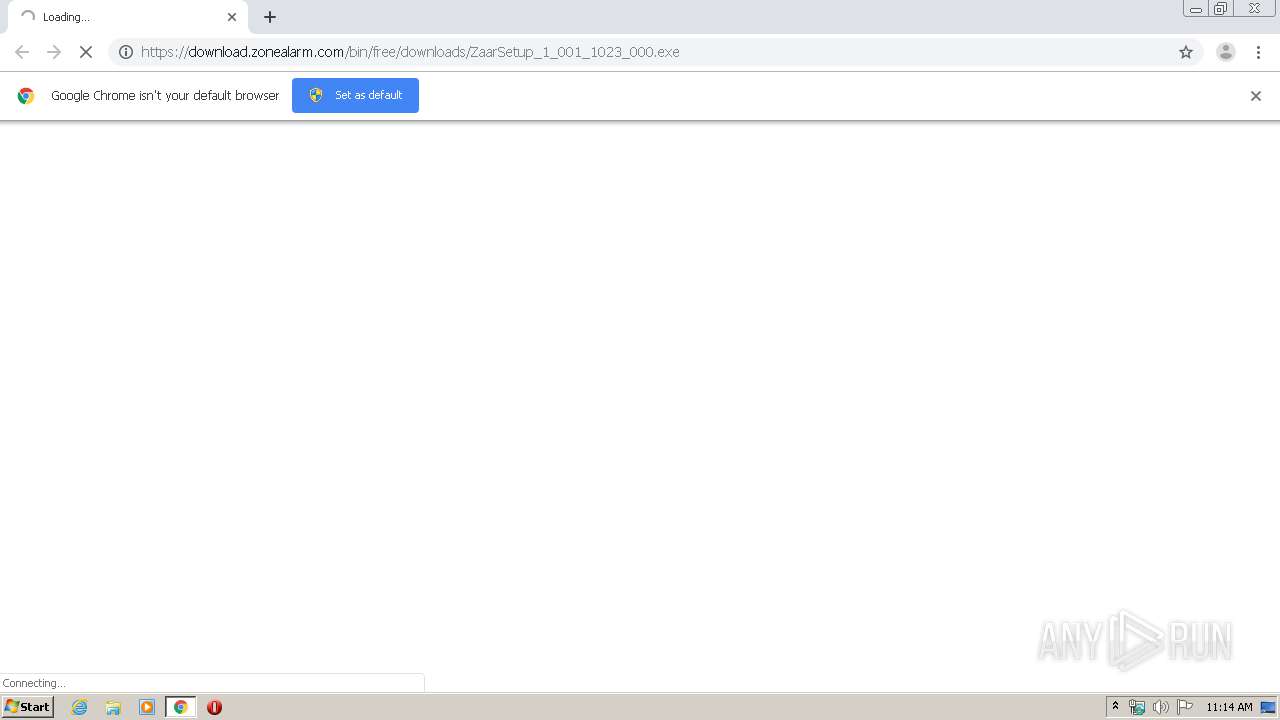
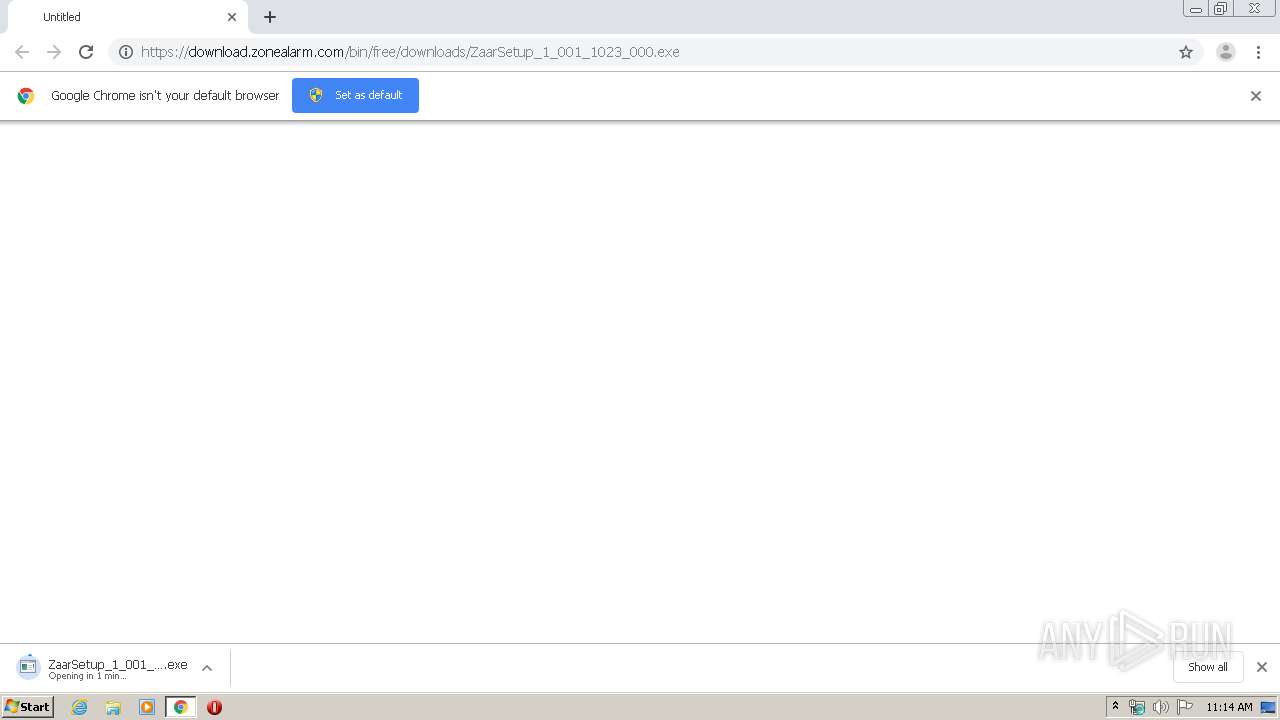
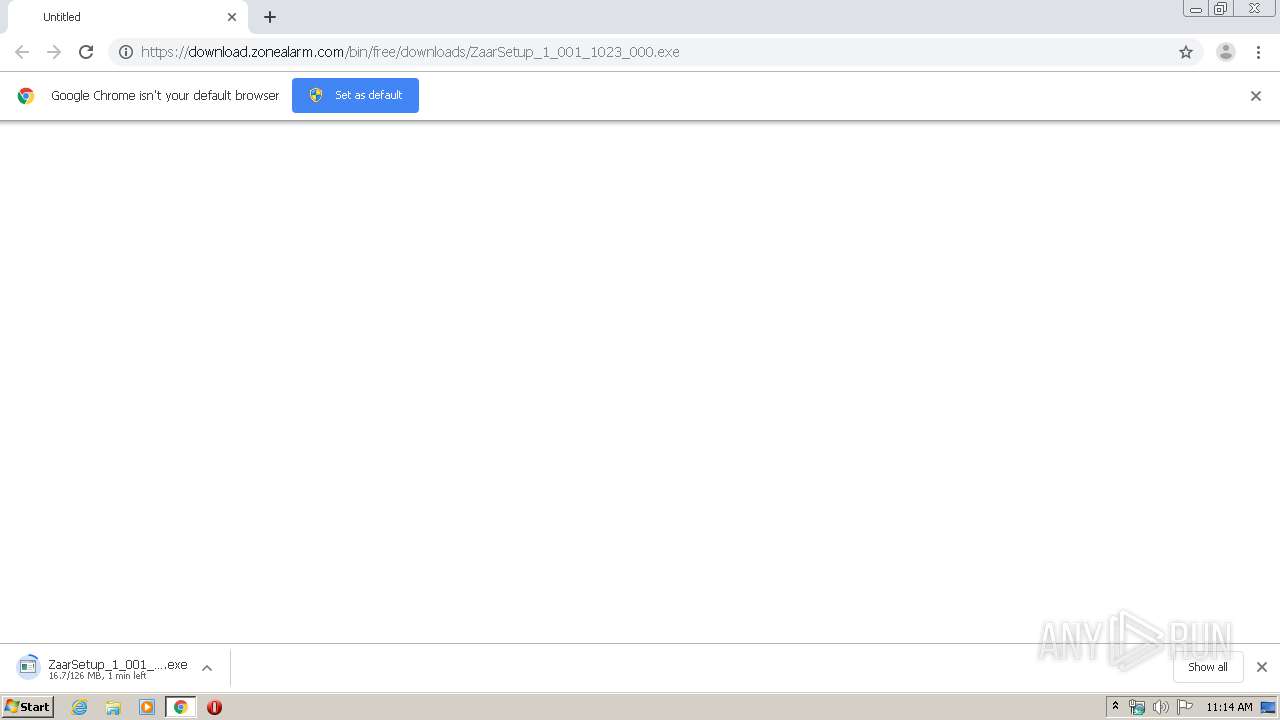
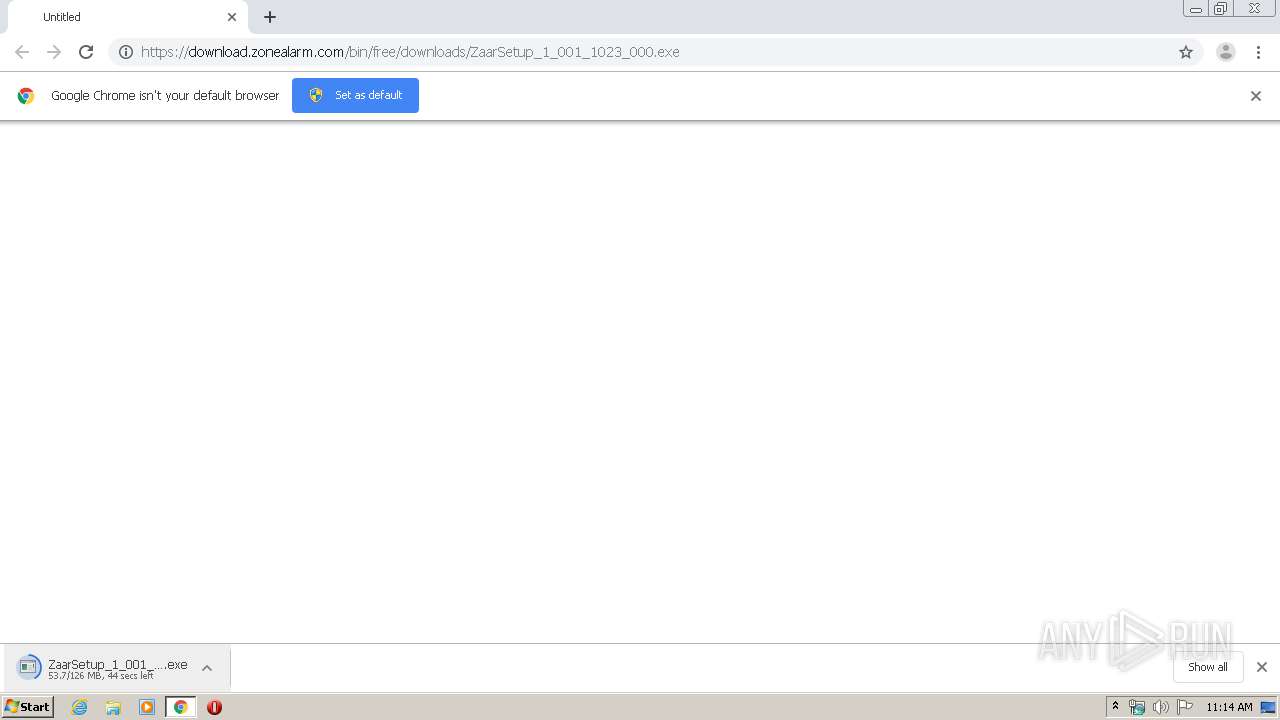
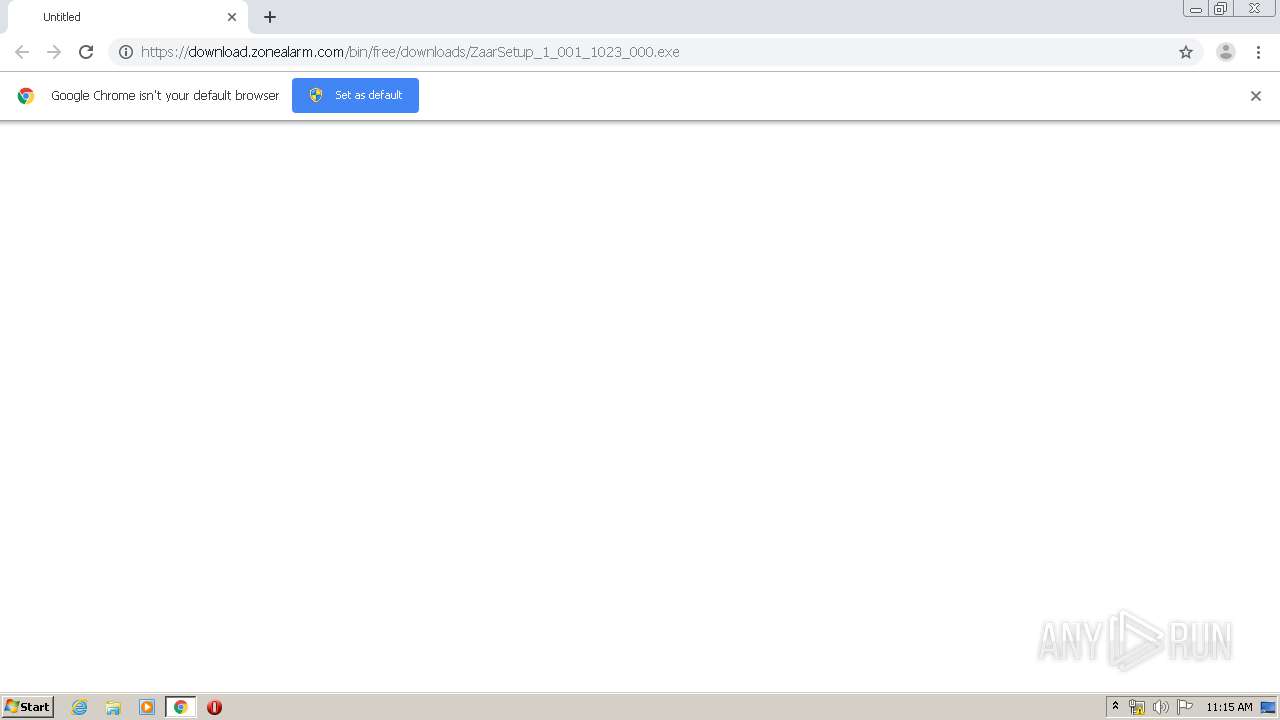
| URL: | https://download.zonealarm.com/bin/free/downloads/ZaarSetup_1_001_1023_000.exe |
| Full analysis: | https://app.any.run/tasks/a74ebc6f-032d-4f3a-8dd3-9607368ec8e7 |
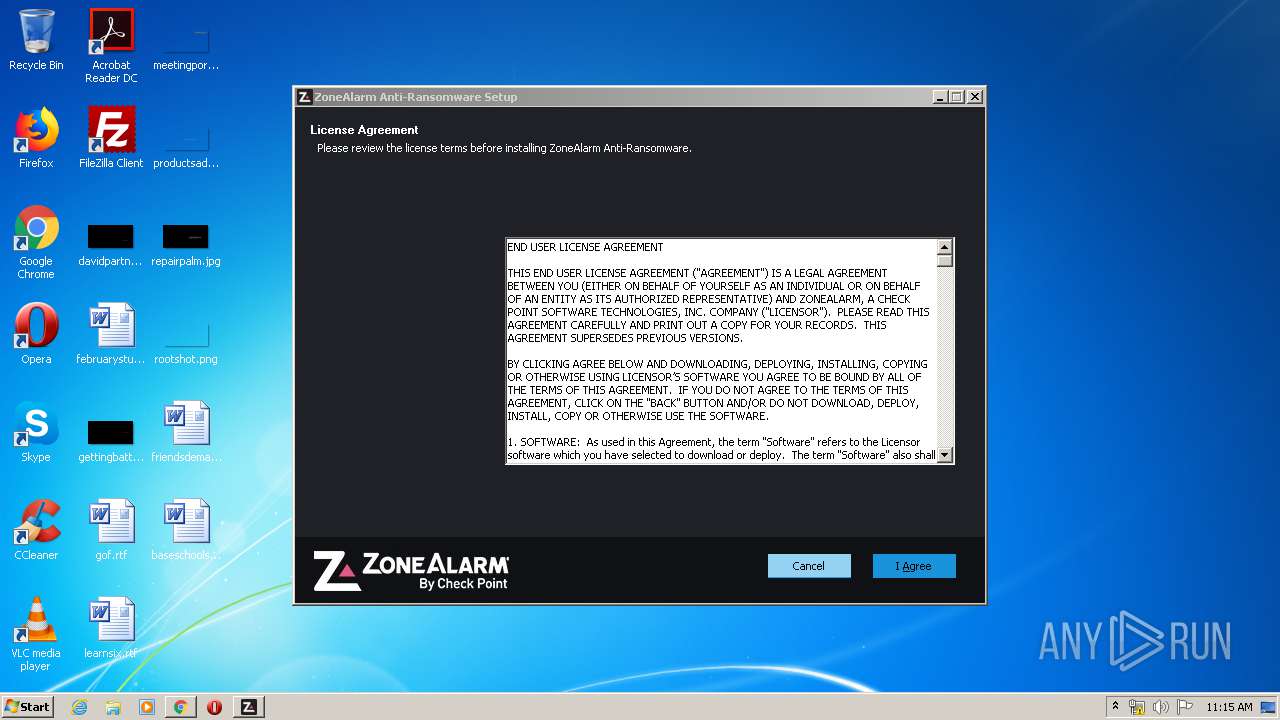
| Verdict: | Malicious activity |
| Analysis date: | March 01, 2020, 11:13:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 361F6A1B9F409549F53E6312B2BEBC4E |
| SHA1: | 039C696219CEE429B2FFFF391CA25D3A9852C2AE |
| SHA256: | 61EC33FBDB2E9CDC4B235BD9A7D56DBD59147A9550EA694D26809BF84B1AB4B4 |
| SSDEEP: | 3:N8SEli0EKYLGGqNF6KM+yXdXRn:2SKdEKmG19MtVRn |
MALICIOUS
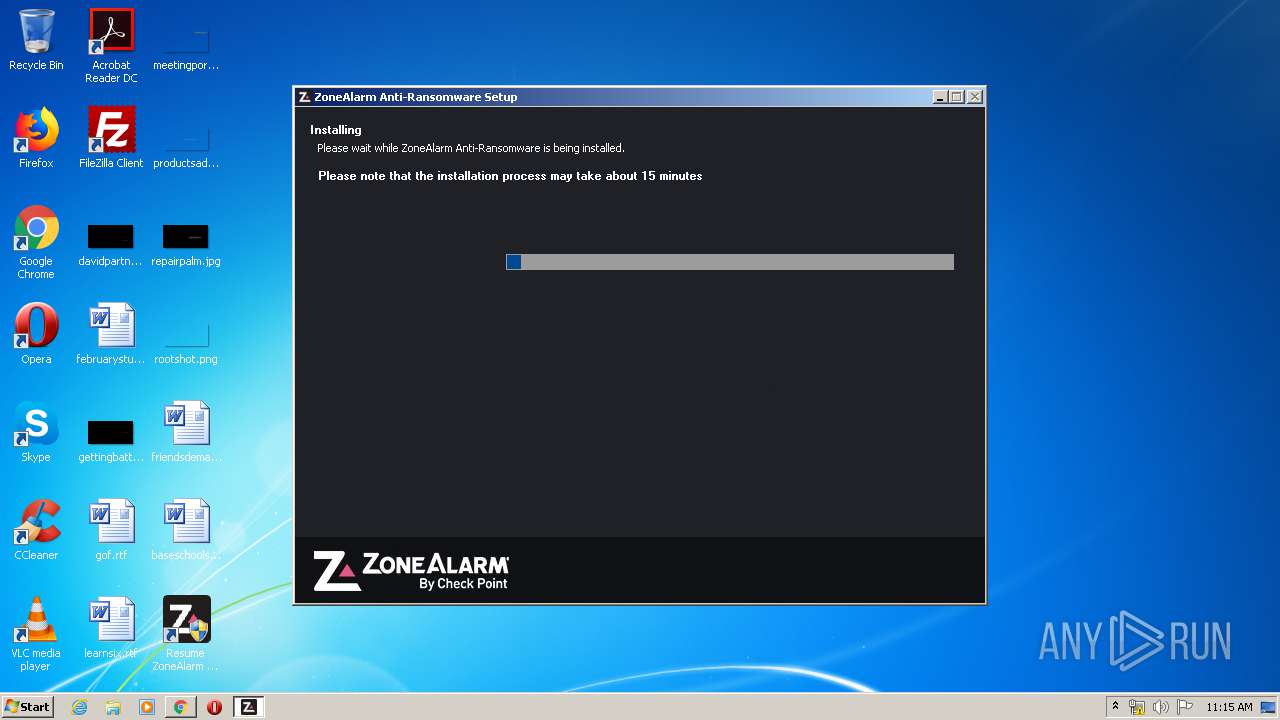
Application was dropped or rewritten from another process
- ZaarSetup_1_001_1023_000.exe (PID: 2656)
- ZaarSetup_1_001_1023_000.exe (PID: 2992)
- nsA5EA.tmp (PID: 3568)
- dltel.exe (PID: 1684)
- nsDBB3.tmp (PID: 3316)
- nsA762.tmp (PID: 2052)
- nsBC72.tmp (PID: 2340)
- nsF7A8.tmp (PID: 3024)
- VC10 Runtimes x86.exe (PID: 3648)
- Setup.exe (PID: 3040)
- VC11 Runtimes x86.exe (PID: 872)
- VC11 Runtimes x86.exe (PID: 3632)
- VC12 Runtimes x64.exe (PID: 1928)
- mpsyschk.exe (PID: 1440)
- VC12 Runtimes x64.exe (PID: 580)
Loads dropped or rewritten executable
- ZaarSetup_1_001_1023_000.exe (PID: 2656)
- Setup.exe (PID: 3040)
- VC11 Runtimes x86.exe (PID: 3632)
- VC12 Runtimes x64.exe (PID: 580)
Changes the autorun value in the registry
- VC11 Runtimes x86.exe (PID: 872)
Changes settings of System certificates
- VC11 Runtimes x86.exe (PID: 872)
- dltel.exe (PID: 1684)
SUSPICIOUS
Executable content was dropped or overwritten
- ZaarSetup_1_001_1023_000.exe (PID: 2656)
- chrome.exe (PID: 3096)
- VC10 Runtimes x86.exe (PID: 3648)
- VC11 Runtimes x86.exe (PID: 3632)
- VC11 Runtimes x86.exe (PID: 872)
- msiexec.exe (PID: 3060)
- VC12 Runtimes x64.exe (PID: 580)
- wusa.exe (PID: 3588)
Creates files in the program directory
- cmd.exe (PID: 2828)
- ZaarSetup_1_001_1023_000.exe (PID: 2656)
- Setup.exe (PID: 3040)
- VC11 Runtimes x86.exe (PID: 3632)
- VC11 Runtimes x86.exe (PID: 872)
- VC12 Runtimes x64.exe (PID: 580)
- wusa.exe (PID: 3588)
Starts application with an unusual extension
- ZaarSetup_1_001_1023_000.exe (PID: 2656)
Reads Environment values
- reg.exe (PID: 3744)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 2828)
Starts CMD.EXE for commands execution
- nsA5EA.tmp (PID: 3568)
Starts SC.EXE for service management
- nsA762.tmp (PID: 2052)
- nsDBB3.tmp (PID: 3316)
- nsF7A8.tmp (PID: 3024)
Reads Windows owner or organization settings
- reg.exe (PID: 3744)
Application launched itself
- VC11 Runtimes x86.exe (PID: 872)
Searches for installed software
- VC11 Runtimes x86.exe (PID: 3632)
- VC11 Runtimes x86.exe (PID: 872)
- VC12 Runtimes x64.exe (PID: 580)
Executed as Windows Service
- vssvc.exe (PID: 2860)
Creates a software uninstall entry
- VC11 Runtimes x86.exe (PID: 872)
Adds / modifies Windows certificates
- VC11 Runtimes x86.exe (PID: 872)
- dltel.exe (PID: 1684)
Creates files in the Windows directory
- msiexec.exe (PID: 3060)
- wusa.exe (PID: 3588)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3096)
Reads Internet Cache Settings
- ZaarSetup_1_001_1023_000.exe (PID: 2656)
INFO
Reads the hosts file
- chrome.exe (PID: 3096)
- chrome.exe (PID: 2752)
Reads Internet Cache Settings
- chrome.exe (PID: 3096)
Application launched itself
- chrome.exe (PID: 3096)
Reads settings of System Certificates
- dltel.exe (PID: 1684)
- chrome.exe (PID: 2752)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2860)
Creates a software uninstall entry
- msiexec.exe (PID: 3060)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
99
Monitored processes
49
Malicious processes
6
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 340 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,8207175108809653409,16631101827843906530,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5587653030506889759 --mojo-platform-channel-handle=4460 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,8207175108809653409,16631101827843906530,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4097675869003392413 --mojo-platform-channel-handle=3828 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 548 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,8207175108809653409,16631101827843906530,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11648530055443309701 --mojo-platform-channel-handle=4448 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 580 | "C:\Users\admin\AppData\Local\Temp\nsnA56C.tmp\VC12 Runtimes x64.exe" /q /norestart /l "C:\ProgramData\CheckPoint\Zaar\Logs\installer\VC12 Runtimes x64.log" -burn.unelevated BurnPipe.{45E36C56-906C-4F91-86CB-BB87C796D8B4} {BD095417-1E81-43FE-AD4D-A412711CFEA5} 1928 | C:\Users\admin\AppData\Local\Temp\nsnA56C.tmp\VC12 Runtimes x64.exe | VC12 Runtimes x64.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2013 Redistributable (x64) - 12.0.30501 Exit code: 1 Version: 12.0.30501.0 Modules
| |||||||||||||||
| 676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1016,8207175108809653409,16631101827843906530,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=914548347364425342 --mojo-platform-channel-handle=3580 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 872 | "C:\Users\admin\AppData\Local\Temp\nsnA56C.tmp\VC11 Runtimes x86.exe" /q /norestart /l "C:\ProgramData\CheckPoint\Zaar\Logs\installer\VC11 Runtimes x86.log" | C:\Users\admin\AppData\Local\Temp\nsnA56C.tmp\VC11 Runtimes x86.exe | ZaarSetup_1_001_1023_000.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Visual C++ 2012 Redistributable (x86) - 11.0.61030 Exit code: 0 Version: 11.0.61030.0 Modules
| |||||||||||||||
| 1092 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,8207175108809653409,16631101827843906530,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3190780827408219529 --mojo-platform-channel-handle=3976 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1440 | "C:\Windows\SoftwareDistribution\Download\Install\mpsyschk.exe" | C:\Windows\SoftwareDistribution\Download\Install\mpsyschk.exe | — | wuauclt.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1016,8207175108809653409,16631101827843906530,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=5444575908759735061 --mojo-platform-channel-handle=1032 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1584 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,8207175108809653409,16631101827843906530,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7177014662113463607 --mojo-platform-channel-handle=4840 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
4 156
Read events
2 247
Write events
1 880
Delete events
29
Modification events
| (PID) Process: | (3096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3380) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3096-13227534842606750 |
Value: 259 | |||
| (PID) Process: | (3096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (3096) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
60
Suspicious files
25
Text files
380
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E5B98FA-C18.pma | — | |
MD5:— | SHA256:— | |||
| 3096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\3dcb3547-ffc6-4b06-8ab4-5905c8e10825.tmp | — | |
MD5:— | SHA256:— | |||
| 3096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFa66c20.TMP | text | |
MD5:— | SHA256:— | |||
| 3096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFa66c2f.TMP | text | |
MD5:— | SHA256:— | |||
| 3096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFa66c20.TMP | text | |
MD5:— | SHA256:— | |||
| 3096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa66e52.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
21
DNS requests
16
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2752 | chrome.exe | GET | 200 | 173.194.150.236:80 | http://r6---sn-2gb7sn7s.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=195.181.166.91&mm=28&mn=sn-2gb7sn7s&ms=nvh&mt=1583061373&mv=m&mvi=5&pl=24&shardbypass=yes | US | crx | 862 Kb | whitelisted |
872 | VC11 Runtimes x86.exe | GET | 200 | 2.16.186.120:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | unknown | der | 781 b | whitelisted |
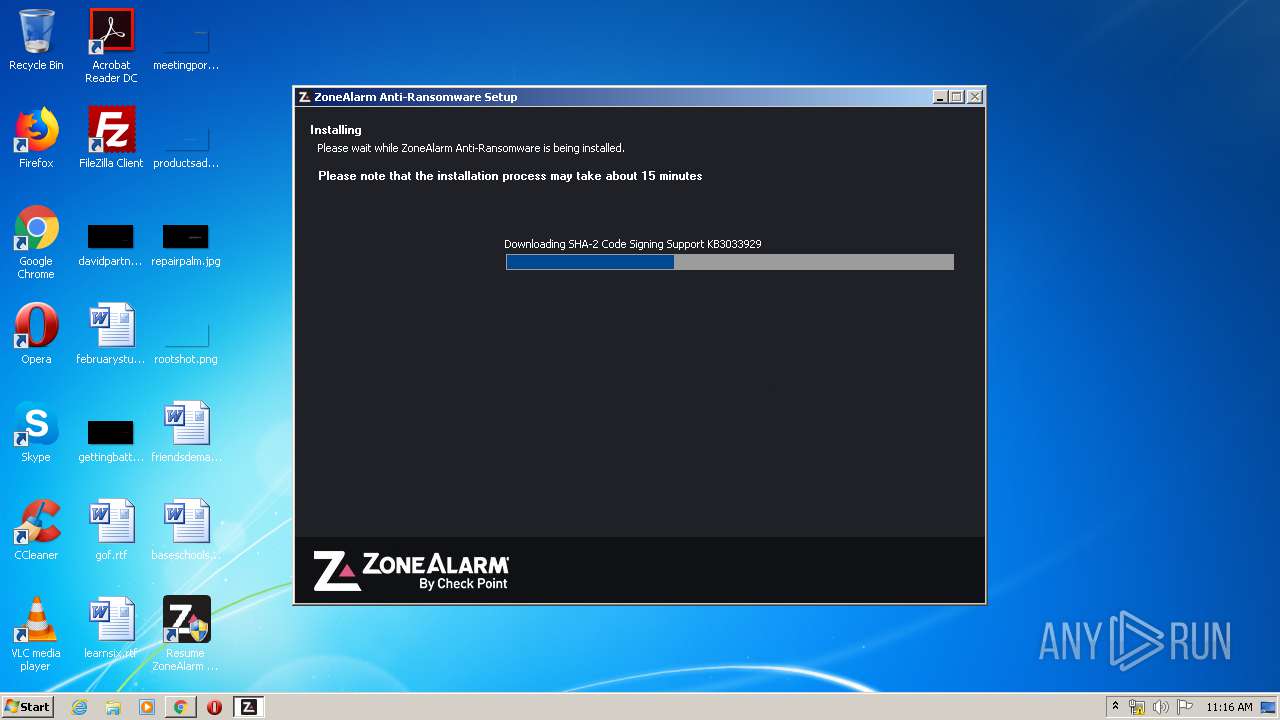
2656 | ZaarSetup_1_001_1023_000.exe | GET | 200 | 2.19.41.37:80 | http://download.zonealarm.com/bin/free/downloads/zaar/Windows6.1-KB3033929-x86.msu | unknown | compressed | 26.4 Mb | suspicious |
872 | VC11 Runtimes x86.exe | GET | 200 | 2.16.186.120:80 | http://crl.microsoft.com/pki/crl/products/MicrosoftTimeStampPCA.crl | unknown | der | 550 b | whitelisted |
2752 | chrome.exe | GET | 302 | 172.217.22.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 510 b | whitelisted |
872 | VC11 Runtimes x86.exe | GET | 200 | 2.16.186.120:80 | http://crl.microsoft.com/pki/crl/products/MicCodSigPCA_08-31-2010.crl | unknown | der | 555 b | whitelisted |
2752 | chrome.exe | GET | 302 | 172.217.22.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 515 b | whitelisted |
2752 | chrome.exe | GET | 200 | 173.194.150.231:80 | http://r1---sn-2gb7sn7s.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=195.181.166.91&mm=28&mn=sn-2gb7sn7s&ms=nvh&mt=1583061373&mv=m&mvi=0&pl=24&shardbypass=yes | US | crx | 293 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2752 | chrome.exe | 172.217.22.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2752 | chrome.exe | 2.19.41.37:443 | download.zonealarm.com | Akamai International B.V. | — | suspicious |
2752 | chrome.exe | 172.217.22.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
2752 | chrome.exe | 172.217.21.228:443 | www.google.com | Google Inc. | US | whitelisted |
2752 | chrome.exe | 172.217.18.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2752 | chrome.exe | 172.217.23.142:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
1684 | dltel.exe | 209.87.211.157:443 | gwevents.checkpoint.com | Check Point Software Technologies, Inc. | US | unknown |
2752 | chrome.exe | 172.217.18.14:443 | clients1.google.com | Google Inc. | US | whitelisted |
872 | VC11 Runtimes x86.exe | 2.16.186.120:80 | crl.microsoft.com | Akamai International B.V. | — | whitelisted |
— | — | 2.19.41.37:80 | download.zonealarm.com | Akamai International B.V. | — | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download.zonealarm.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
gwevents.checkpoint.com |
| unknown |
clients1.google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2656 | ZaarSetup_1_001_1023_000.exe | Potentially Bad Traffic | ET USER_AGENTS Observed Suspicious UA (NSIS_Inetc (Mozilla)) |
2656 | ZaarSetup_1_001_1023_000.exe | Misc activity | SUSPICIOUS [PTsecurity] HTTP header - Sometimes used by hostile installer |
Process | Message |
|---|---|
ZaarSetup_1_001_1023_000.exe | [ZAARINST] Created new mutex: 000001CC (error: 0) |
dltel.exe | Finished telemetry for type=211124
|
ZaarSetup_1_001_1023_000.exe | [INSTHELP] CreateAllAccessDirectory: C:\ProgramData\CheckPoint\Zaar\Data
|
ZaarSetup_1_001_1023_000.exe | [INSTHELP] CreateAllAccessDirectory: C:\ProgramData\CheckPoint\Zaar\Logs
|
ZaarSetup_1_001_1023_000.exe | [INSTHELP] CreateAllAccessDirectory: C:\ProgramData\CheckPoint\Zaar\Logs\installer
|
ZaarSetup_1_001_1023_000.exe | [ZAARINST] Closing mutex handle: 000001CC, result=1 |
ZaarSetup_1_001_1023_000.exe | [INSTHELP] CreateAllAccessDirectory: C:\ProgramData\CheckPoint\ICM
|
ZaarSetup_1_001_1023_000.exe | [ZAARINST] Created new mutex: 000001EC (error: 0) |
Setup.exe | A StopBlock was hit or a System Requirement was not met. |
wusa.exe | InstallWorker.00931: Start of search
|