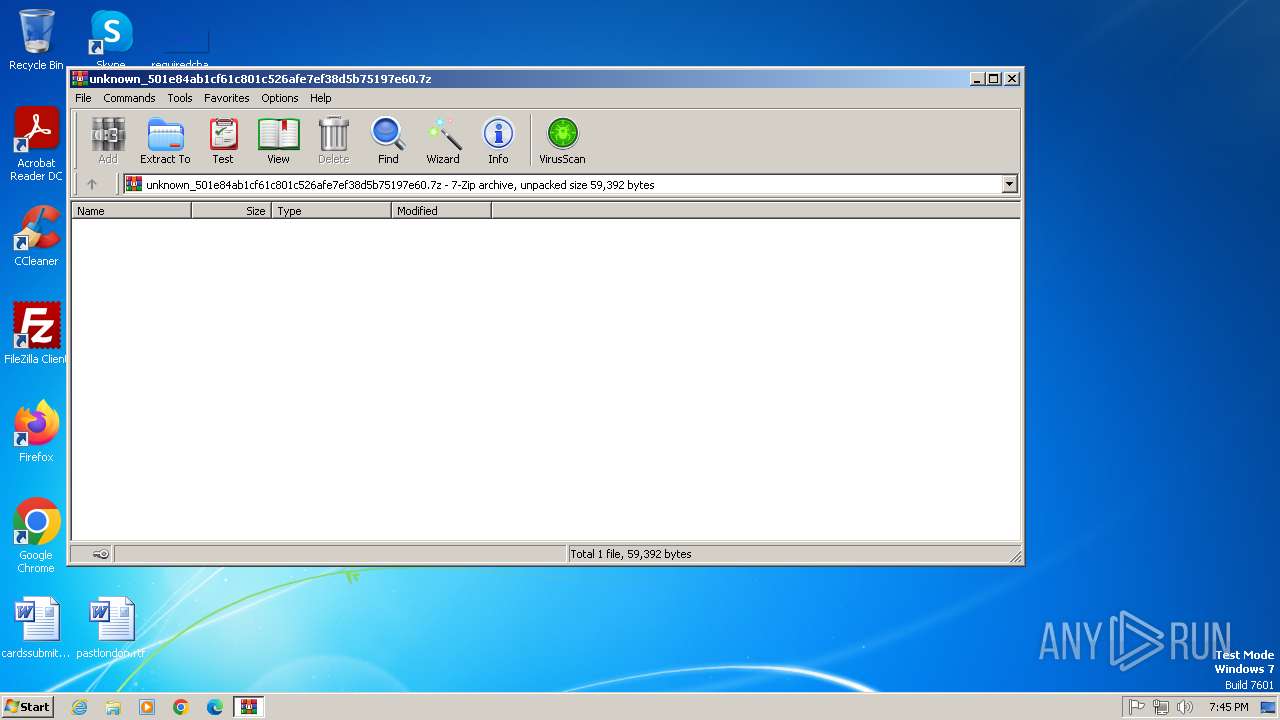
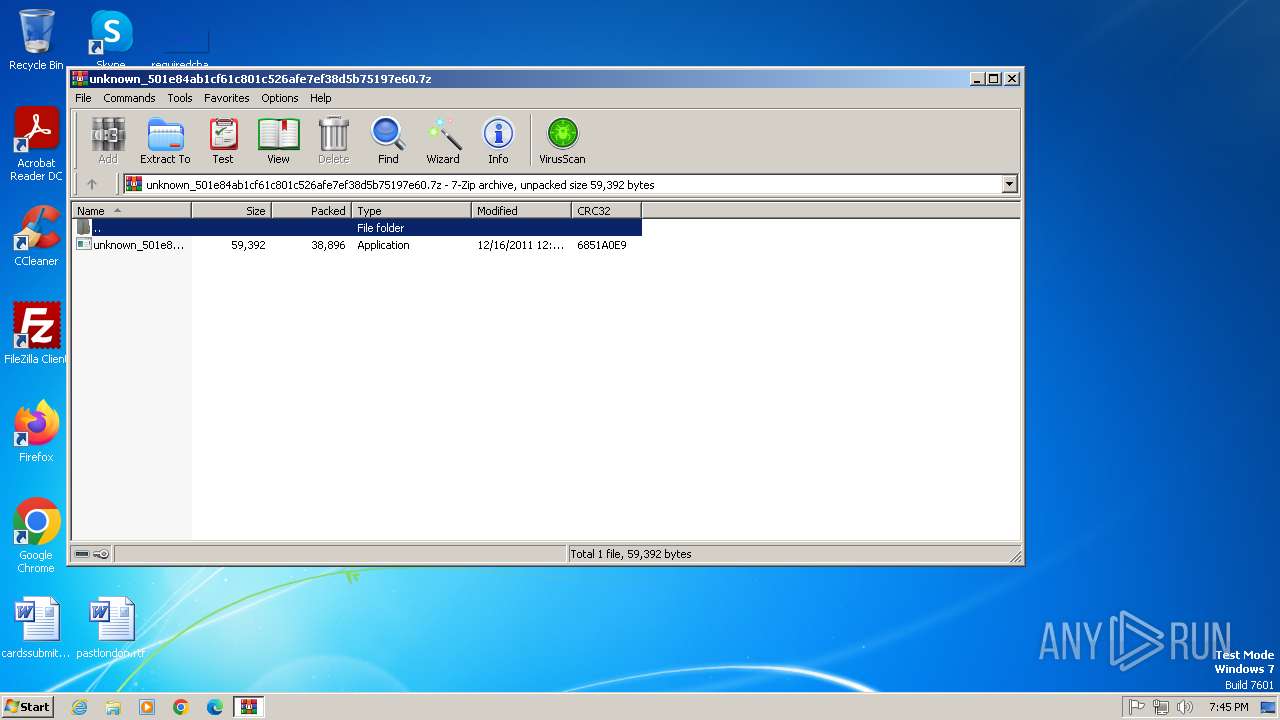
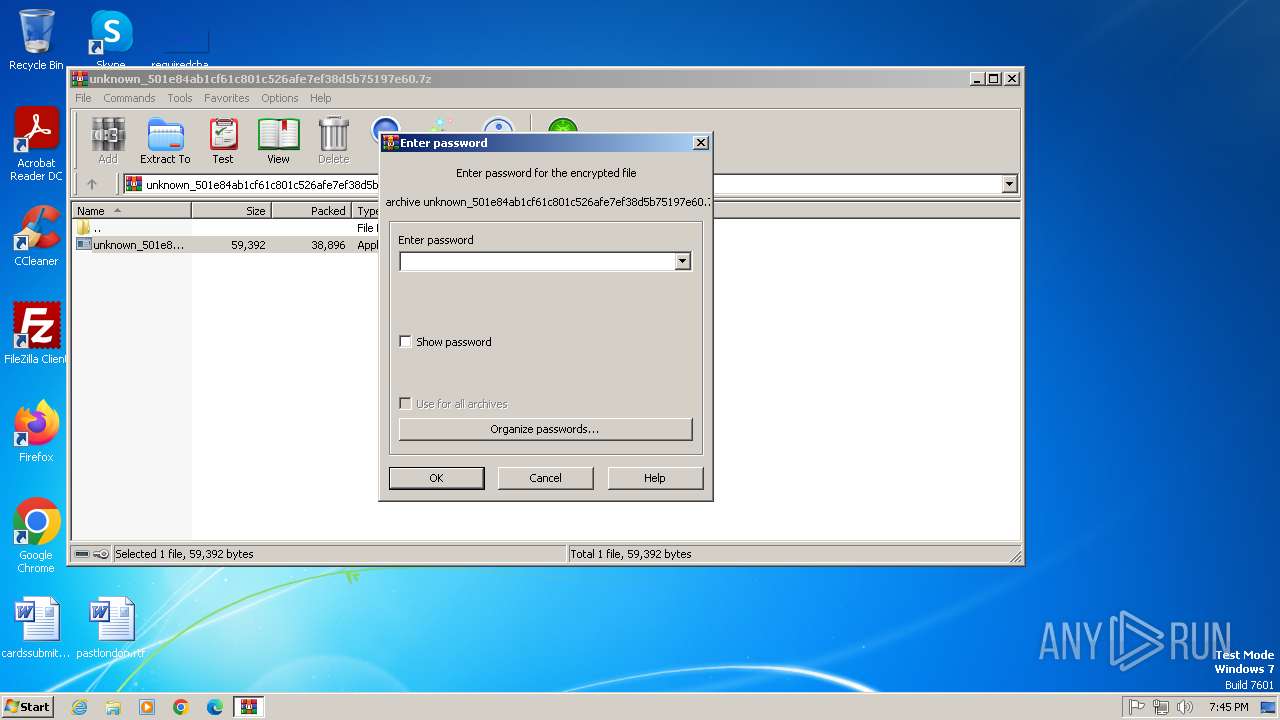
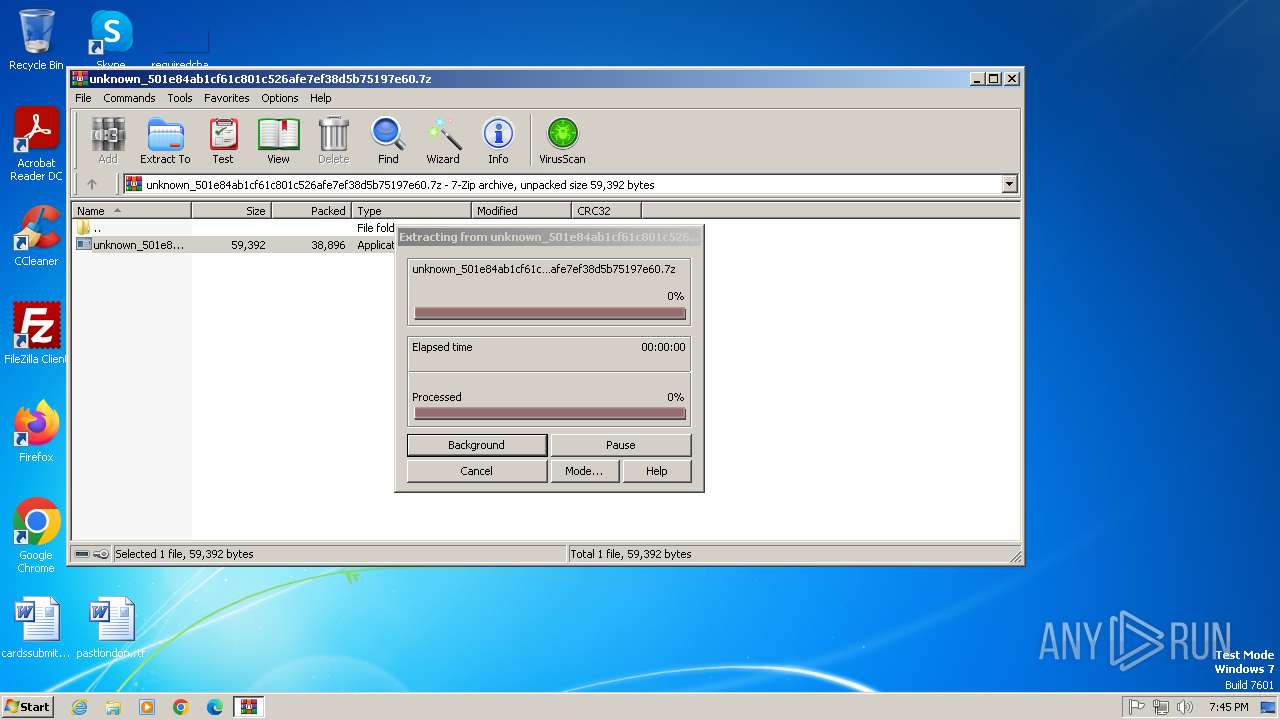
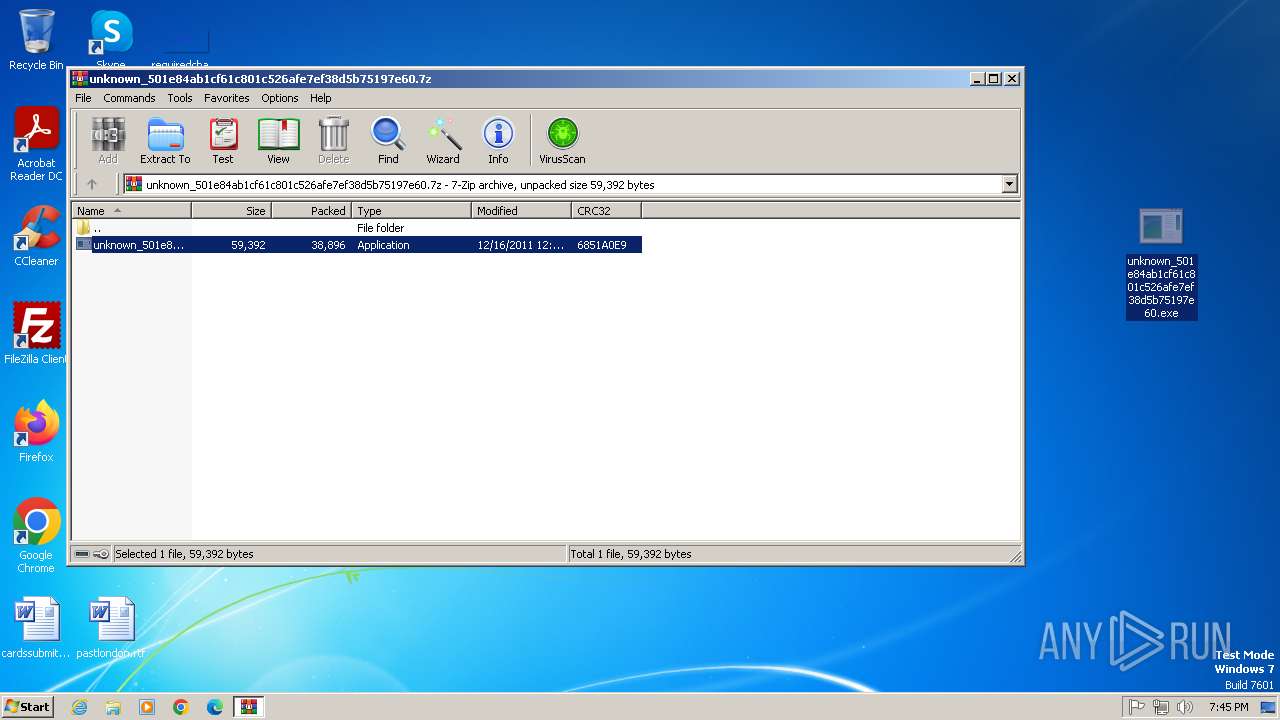
| File name: | unknown_501e84ab1cf61c801c526afe7ef38d5b75197e60.7z |
| Full analysis: | https://app.any.run/tasks/7afb5792-f9b0-4486-8513-f8283f4ced9f |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2025, 18:45:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 0946BEA69D0C371BB140FA3EB3920B4A |
| SHA1: | 8FF2779568BCC1F67FA53558561B268F93476554 |
| SHA256: | 61E9BC5F32AFD17C7B81ABDFB02CCE86437952E097FCCA180E874C1496628D4D |
| SSDEEP: | 768:A001EG+RzkGgRD/OsAaMBWJFBvrvVVedpk+scHN+sGlOic/mDZV0B:A0W2ARD/3L4SFt/ec+scGl3MQC |
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 2448)
Changes the login/logoff helper path in the registry
- svchost.exe (PID: 2732)
Changes image file execution options
- reg.exe (PID: 3312)
- reg.exe (PID: 2936)
- reg.exe (PID: 2952)
- reg.exe (PID: 3136)
- reg.exe (PID: 3748)
- reg.exe (PID: 3144)
Task Manager has been disabled (taskmgr)
- reg.exe (PID: 3000)
Modify registry editing tools (regedit)
- reg.exe (PID: 3088)
SUSPICIOUS
Drops a system driver (possible attempt to evade defenses)
- svchost.exe (PID: 2732)
Executes as Windows Service
- fldkcm.sys (PID: 984)
- VSSVC.exe (PID: 2976)
Uses REG/REGEDIT.EXE to modify registry
- svchost.exe (PID: 2204)
- svchost.exe (PID: 2732)
Executable content was dropped or overwritten
- svchost.exe (PID: 2732)
Potential Corporate Privacy Violation
- svchost.exe (PID: 3780)
Searches for installed software
- svchost.exe (PID: 2732)
- dllhost.exe (PID: 4020)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2448)
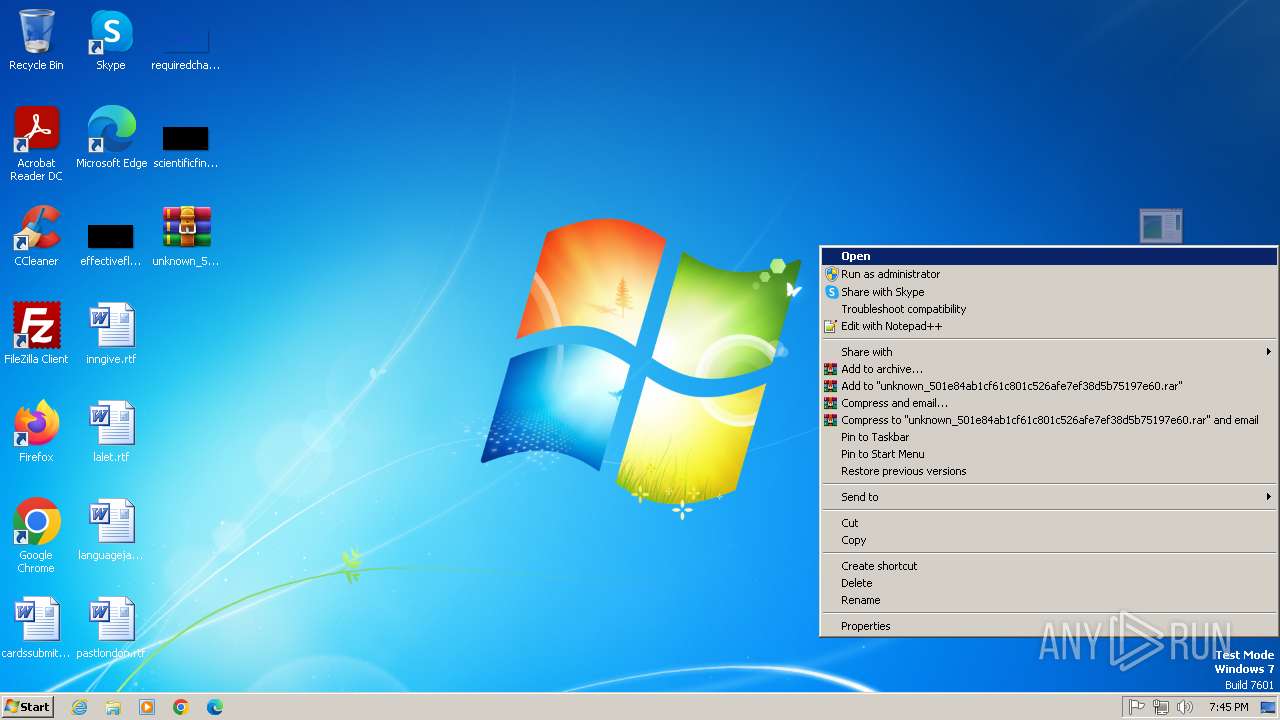
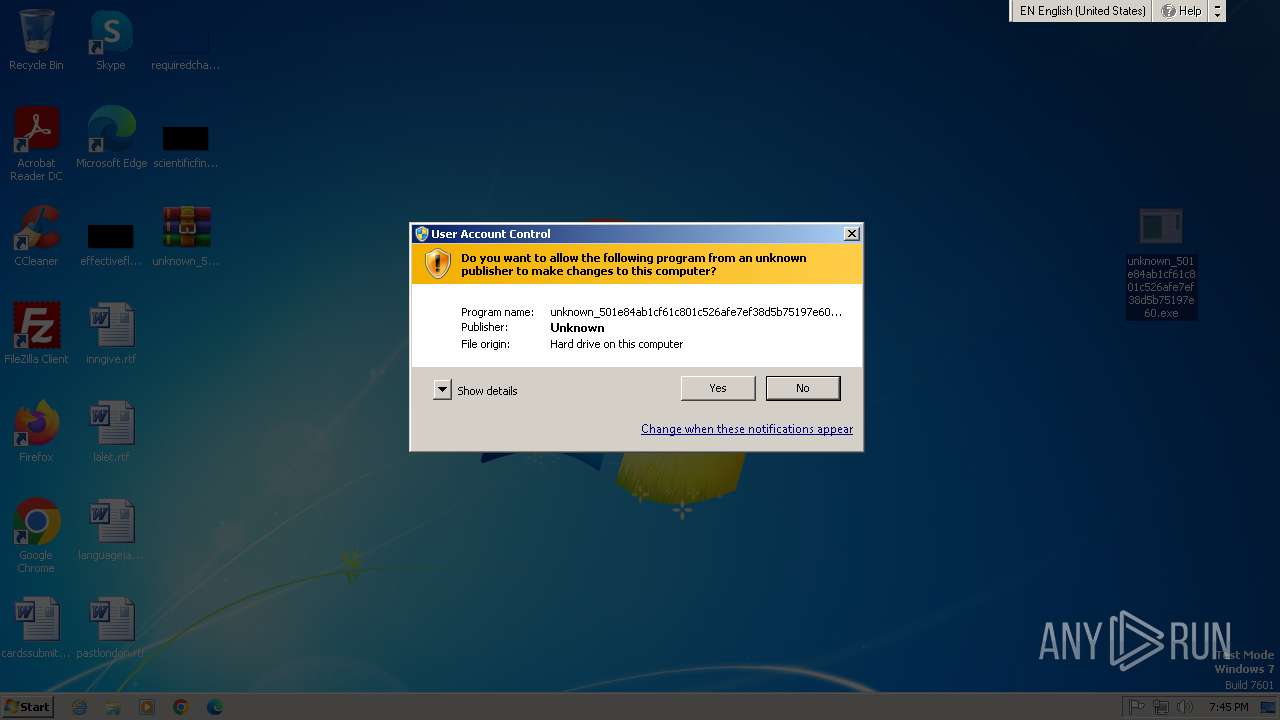
Manual execution by a user
- unknown_501e84ab1cf61c801c526afe7ef38d5b75197e60.exe (PID: 704)
Checks supported languages
- unknown_501e84ab1cf61c801c526afe7ef38d5b75197e60.exe (PID: 704)
- fldkcm.sys (PID: 984)
- eutllvluq.exe (PID: 3732)
Reads the computer name
- fldkcm.sys (PID: 984)
Reads security settings of Internet Explorer
- svchost.exe (PID: 3780)
Create files in a temporary directory
- svchost.exe (PID: 2732)
- svchost.exe (PID: 3780)
Checks proxy server information
- svchost.exe (PID: 3780)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|---|
| ModifyDate: | 2011:12:16 00:25:02+00:00 |
| ArchivedFileName: | unknown_501e84ab1cf61c801c526afe7ef38d5b75197e60.exe |
Total processes
79
Monitored processes
25
Malicious processes
5
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 704 | "C:\Users\admin\Desktop\unknown_501e84ab1cf61c801c526afe7ef38d5b75197e60.exe" | C:\Users\admin\Desktop\unknown_501e84ab1cf61c801c526afe7ef38d5b75197e60.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 872 | reg.exe add "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System" /t REG_DWORD /f /v DisableRegedit /d "1" | C:\Windows\System32\reg.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 984 | C:\Windows\system32\fldkcm.sys | C:\Windows\System32\fldkcm.sys | — | services.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 1092 | svchost.exe | C:\Windows\System32\svchost.exe | — | qhncaoluqspr96635.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1240 | C:\Users\admin\AppData\Local\Temp\qhncaoluqspr96635.exe | C:\Users\admin\AppData\Local\Temp\qhncaoluqspr96635.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 1396 | reg.exe add "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System" /t REG_DWORD /f /v DisableRegistryTools /d "1" | C:\Windows\System32\reg.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2204 | svchost.exe | C:\Windows\System32\svchost.exe | — | fldkcm.sys | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2420 | reg.exe add "HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System" /t REG_DWORD /f /v DisableTaskMgr /d "1" | C:\Windows\System32\reg.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2448 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\unknown_501e84ab1cf61c801c526afe7ef38d5b75197e60.7z | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2464 | reg.exe delete "HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\SafeBoot" /f | C:\Windows\System32\reg.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
5 375
Read events
4 989
Write events
371
Delete events
15
Modification events
| (PID) Process: | (2448) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2448) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2448) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2448) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (2448) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2448) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\unknown_501e84ab1cf61c801c526afe7ef38d5b75197e60.7z | |||
| (PID) Process: | (2448) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2448) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2448) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2448) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
4
Suspicious files
5
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4020 | dllhost.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 4020 | dllhost.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{d4a9a489-202c-4146-bd5c-a2ec2728fb3c}_OnDiskSnapshotProp | binary | |
MD5:5367F6F36016C11F64451C56E2D00B74 | SHA256:94CF6ED985E73358C02CCAD0AA566B50A031AE3A6C0138CAC1FF23FA1BE67D0D | |||
| 4020 | dllhost.exe | C:\System Volume Information\SPP\snapshot-2 | binary | |
MD5:5367F6F36016C11F64451C56E2D00B74 | SHA256:94CF6ED985E73358C02CCAD0AA566B50A031AE3A6C0138CAC1FF23FA1BE67D0D | |||
| 2448 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2448.2639\unknown_501e84ab1cf61c801c526afe7ef38d5b75197e60.exe | executable | |
MD5:7661AF05900B43DE972B08D0AC4C8B05 | SHA256:338281CFA78430E5A7AF8800B51CE9679D26A4610958E22C108955F333E78504 | |||
| 2732 | svchost.exe | C:\Windows\System32\fldkcm.sys | executable | |
MD5:7661AF05900B43DE972B08D0AC4C8B05 | SHA256:338281CFA78430E5A7AF8800B51CE9679D26A4610958E22C108955F333E78504 | |||
| 2732 | svchost.exe | C:\Windows\System32\eutllvluq.exe | executable | |
MD5:7661AF05900B43DE972B08D0AC4C8B05 | SHA256:338281CFA78430E5A7AF8800B51CE9679D26A4610958E22C108955F333E78504 | |||
| 2732 | svchost.exe | C:\Users\admin\AppData\Local\Temp\qhncaoluqspr96635.exe | executable | |
MD5:7661AF05900B43DE972B08D0AC4C8B05 | SHA256:338281CFA78430E5A7AF8800B51CE9679D26A4610958E22C108955F333E78504 | |||
| 3780 | svchost.exe | C:\Users\admin\AppData\Local\Temp\C4BA364752455355502D6461 | binary | |
MD5:DAC222F69F2ECCB9ACF40E4740FABBC7 | SHA256:06F261B011970DE5436E659F59066B2838DAD7B76C6500C3F77B30B9F15A8B36 | |||
| 4020 | dllhost.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{25001a01-219c-42a6-8b56-69efa131db41}_OnDiskSnapshotProp | binary | |
MD5:656EC4E32DD0FA07C2F3C811FA6C9AED | SHA256:54148ACF62EFDE64E24EC351BF9C9E5EC4D9F5773A4D6CF7EA8CCE3846B574D0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
10
DNS requests
5
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3780 | svchost.exe | GET | 404 | 49.13.77.253:80 | http://email-auswahl.com/df87vf9.php?id=C4BA364752455355502D&cmd=geo | unknown | — | — | unknown |
3780 | svchost.exe | GET | 404 | 49.13.77.253:80 | http://loteriegewinner.com/fv79df.php?id=C4BA364752455355502D&cmd=geo | unknown | — | — | unknown |
3780 | svchost.exe | GET | 404 | 49.13.77.253:80 | http://email-gewinn.com/dgbfvhi9.php?id=C4BA364752455355502D&cmd=geo | unknown | — | — | unknown |
3780 | svchost.exe | GET | 404 | 49.13.77.253:80 | http://lotto-lottogewin.com/Fiur5sDzx2col.php?id=C4BA364752455355502D&cmd=geo | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3780 | svchost.exe | 49.13.77.253:80 | loteriegewinner.com | Hetzner Online GmbH | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
loteriegewinner.com |
| unknown |
email-auswahl.com |
| unknown |
email-gewinn.com |
| unknown |
lotto-lottogewin.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3780 | svchost.exe | Potential Corporate Privacy Violation | ET INFO Unsupported/Fake Windows NT Version 5.0 |
3780 | svchost.exe | Potential Corporate Privacy Violation | ET INFO Unsupported/Fake Windows NT Version 5.0 |