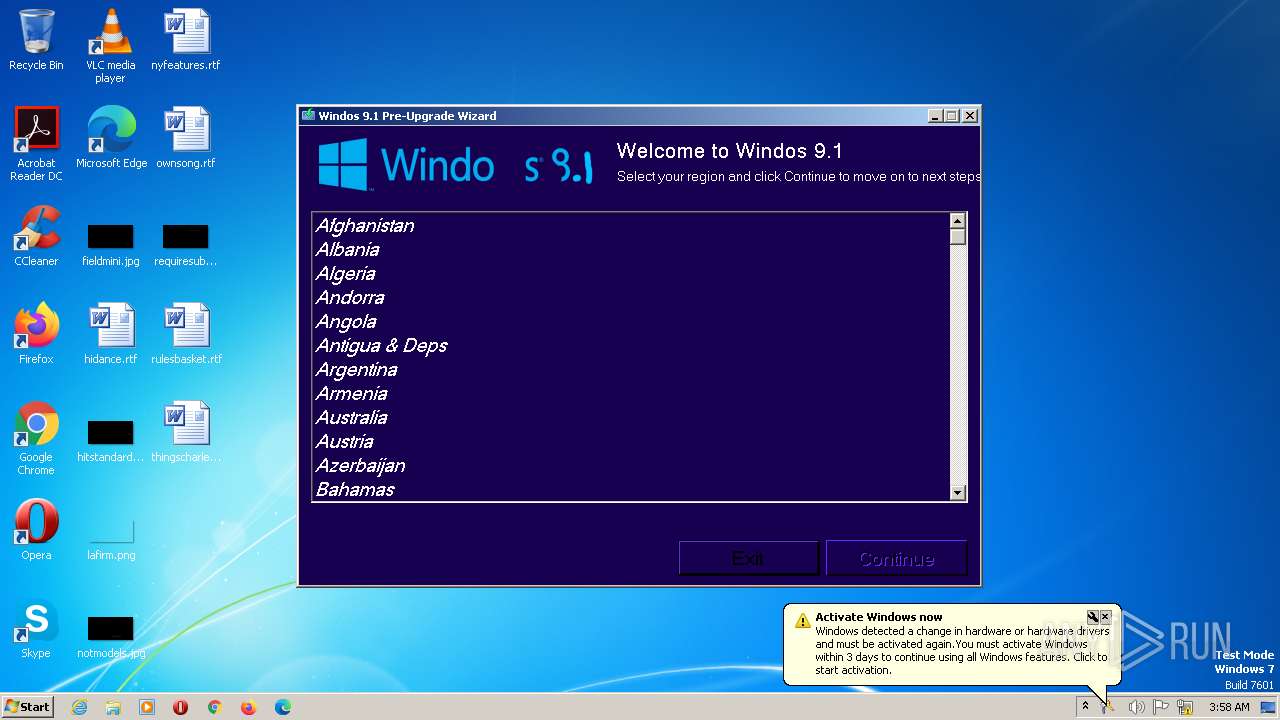
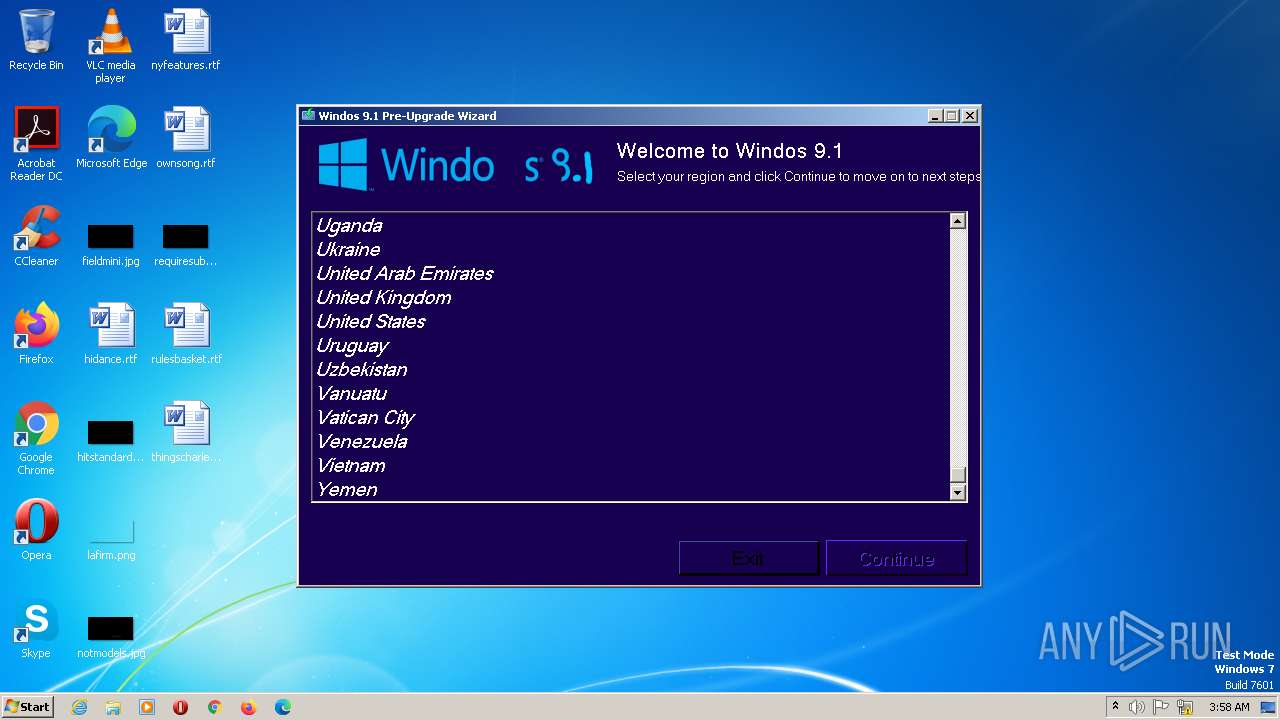
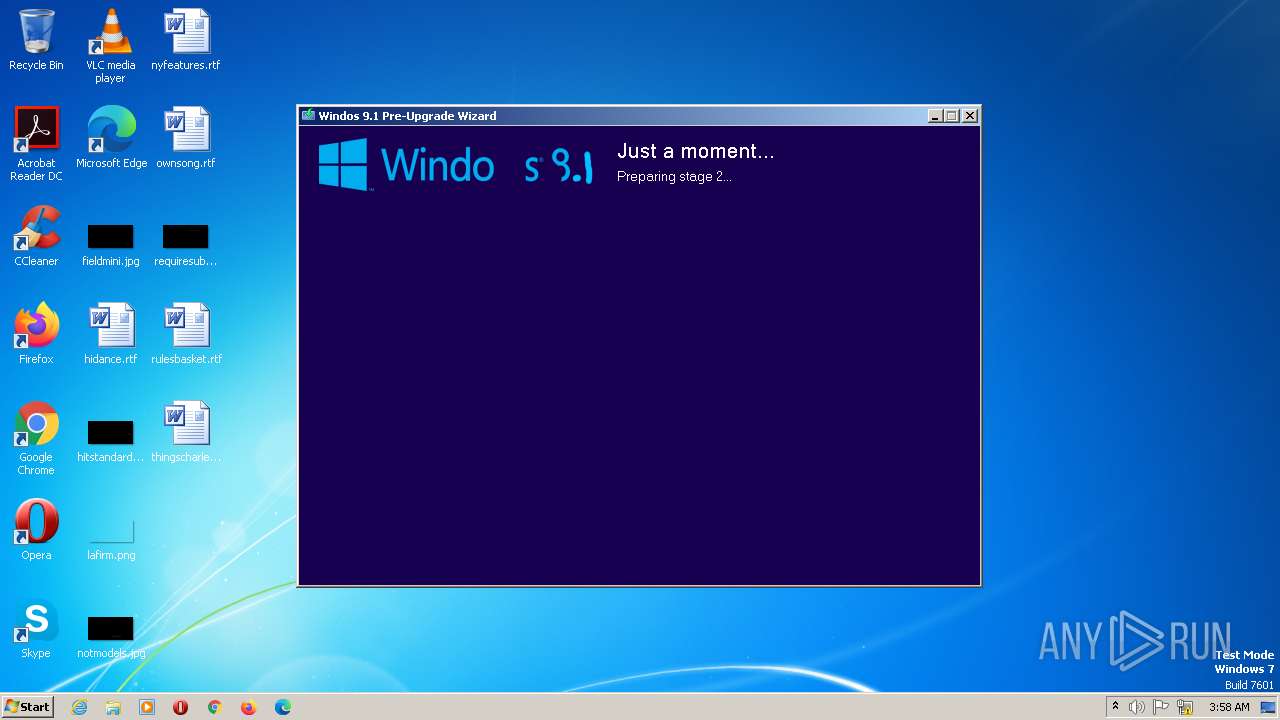
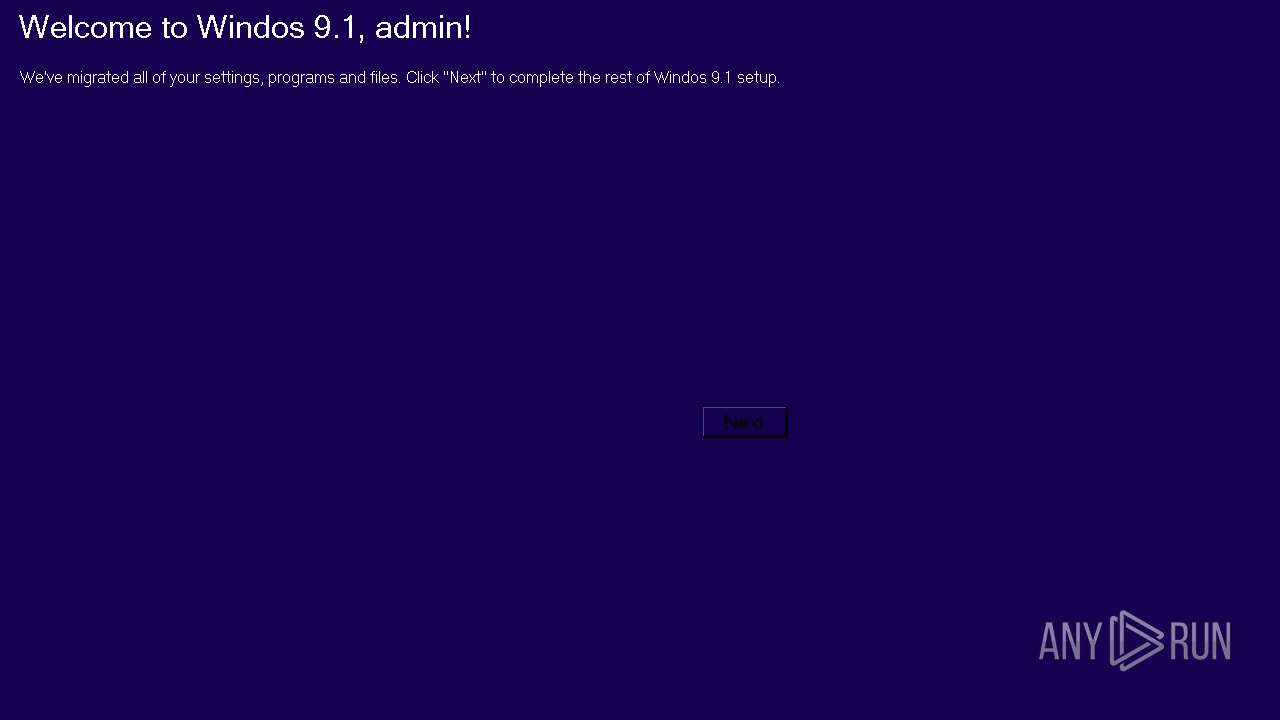
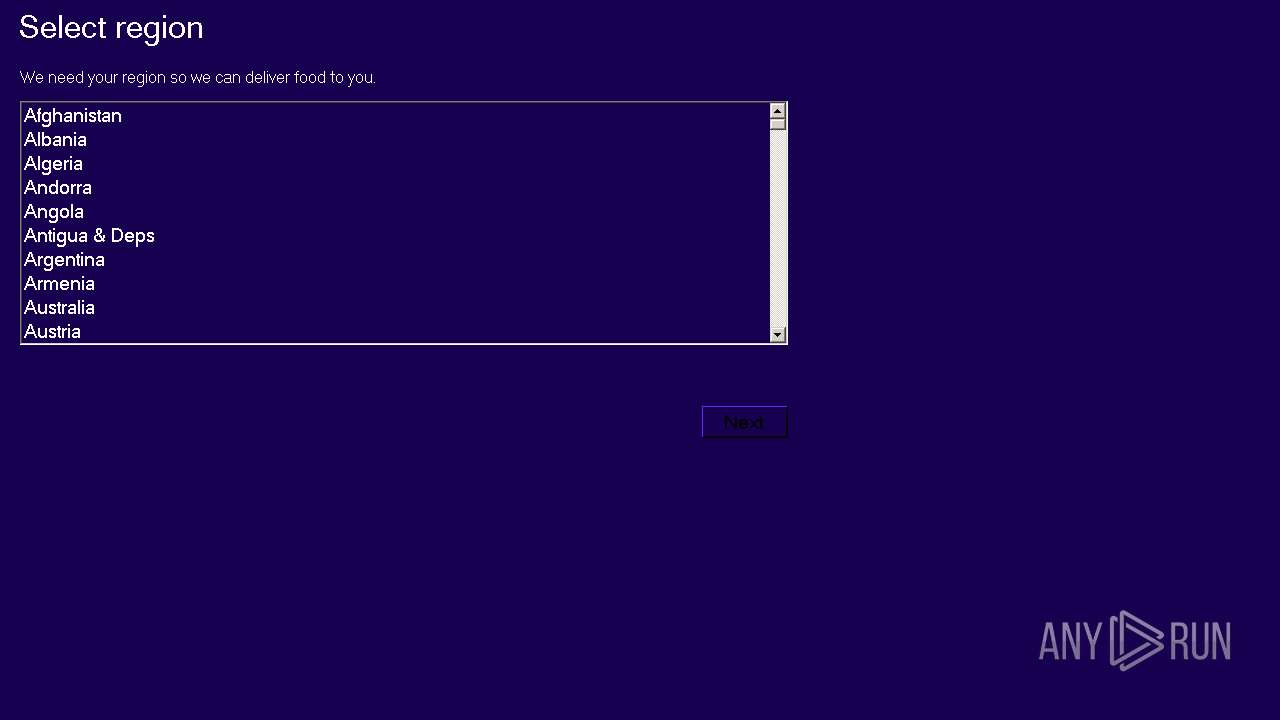
| download: | Windos9.1Setup.exe |
| Full analysis: | https://app.any.run/tasks/24340f06-10d1-48ec-8d99-a0fa29531b2c |
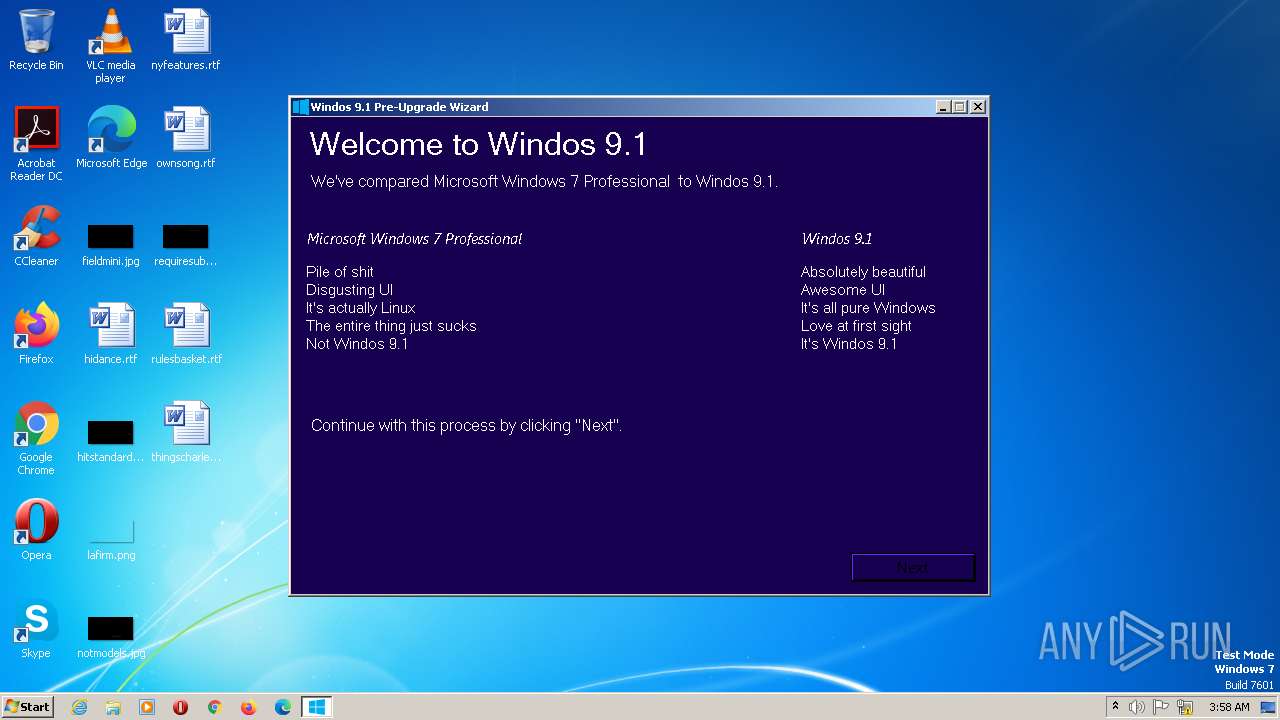
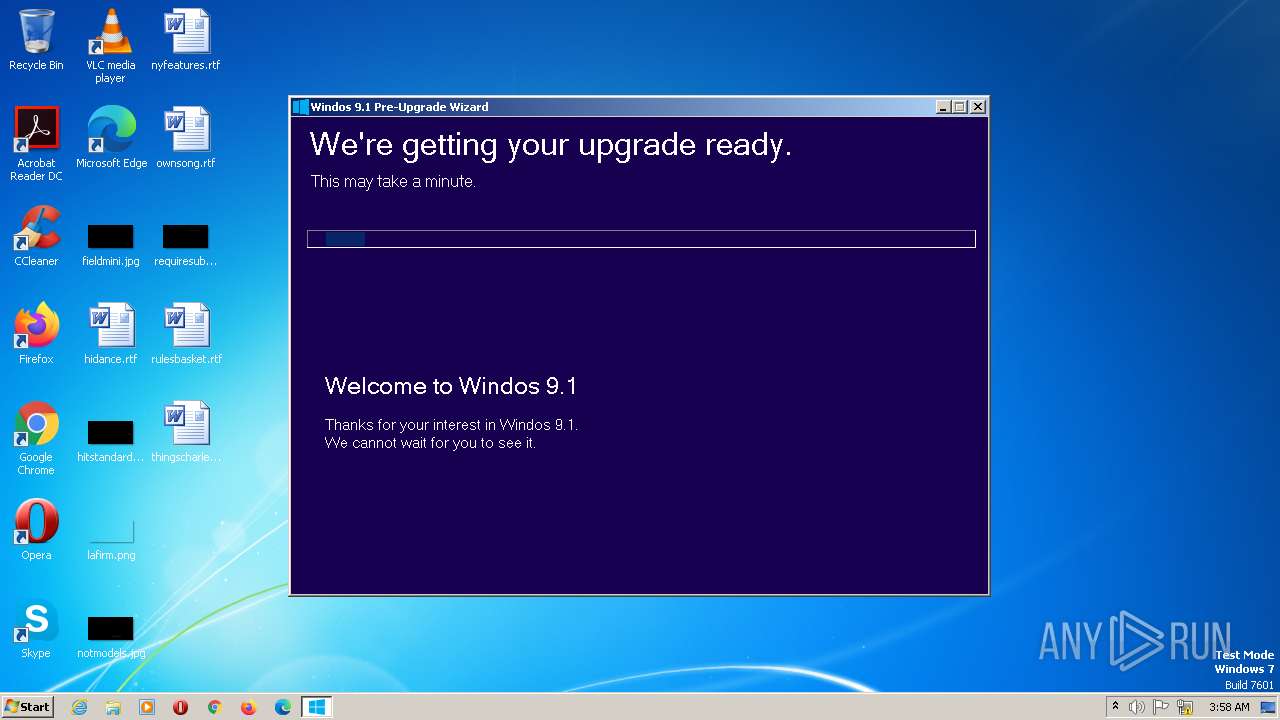
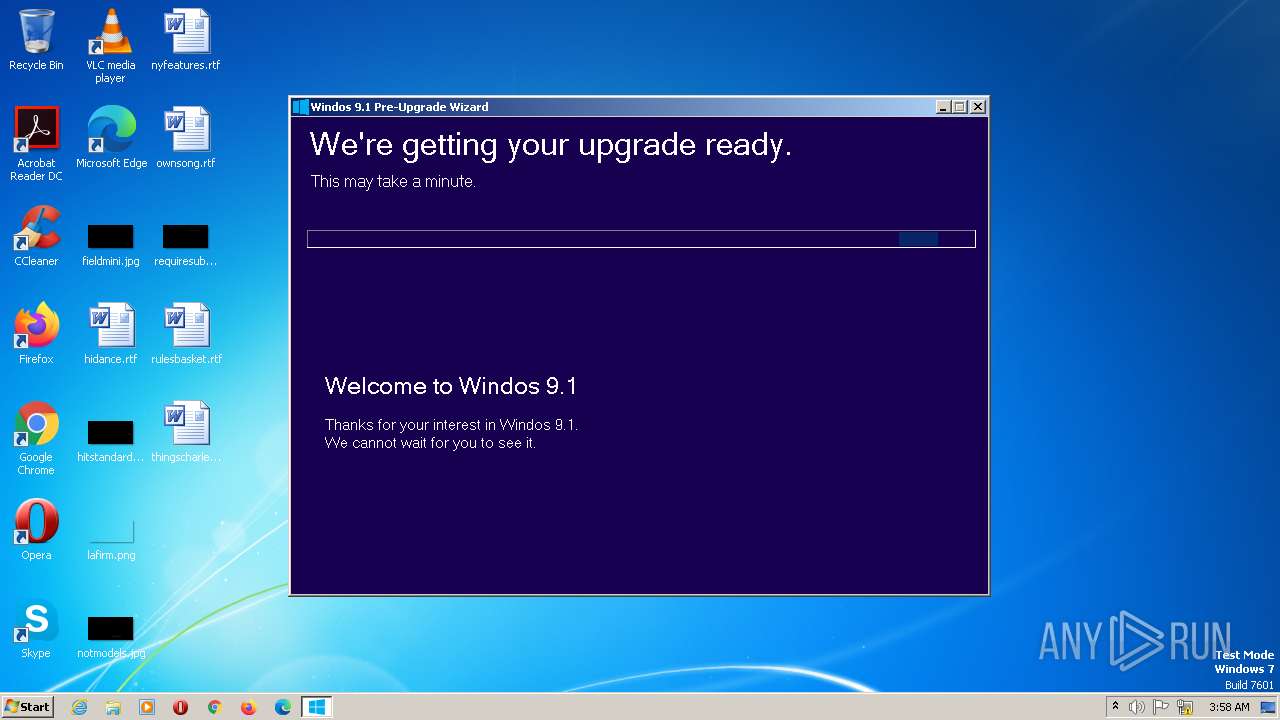
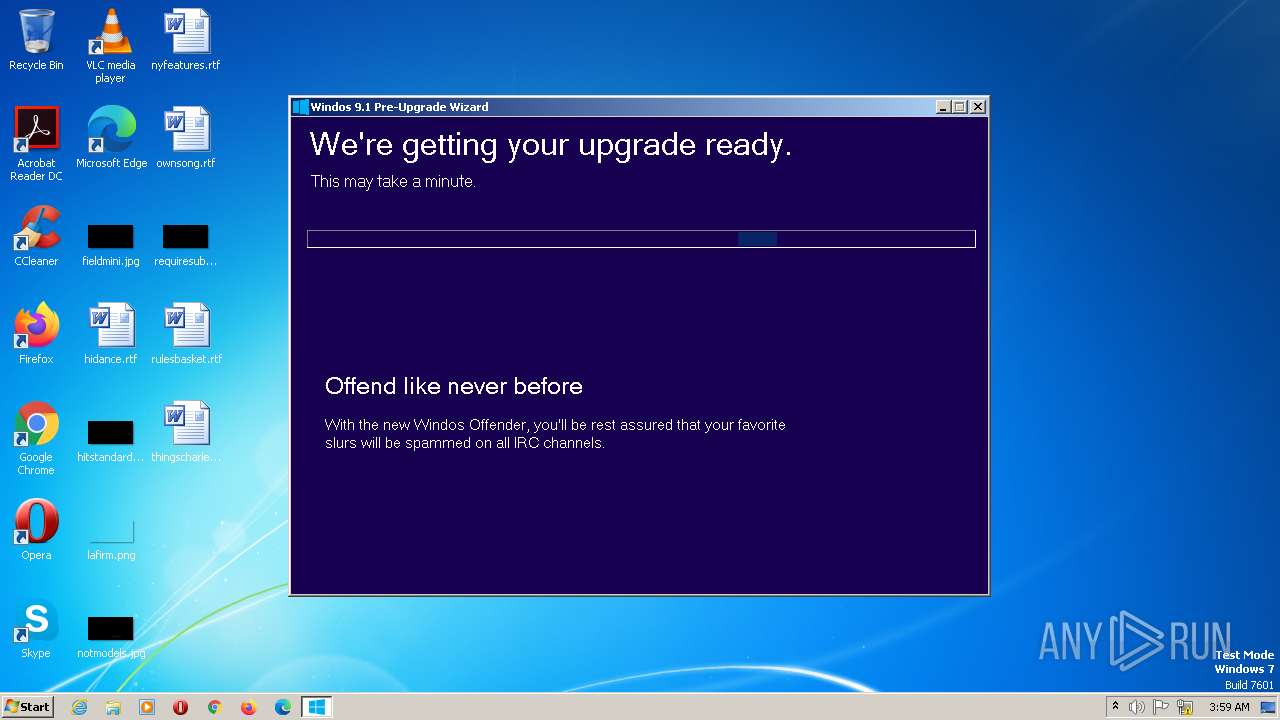
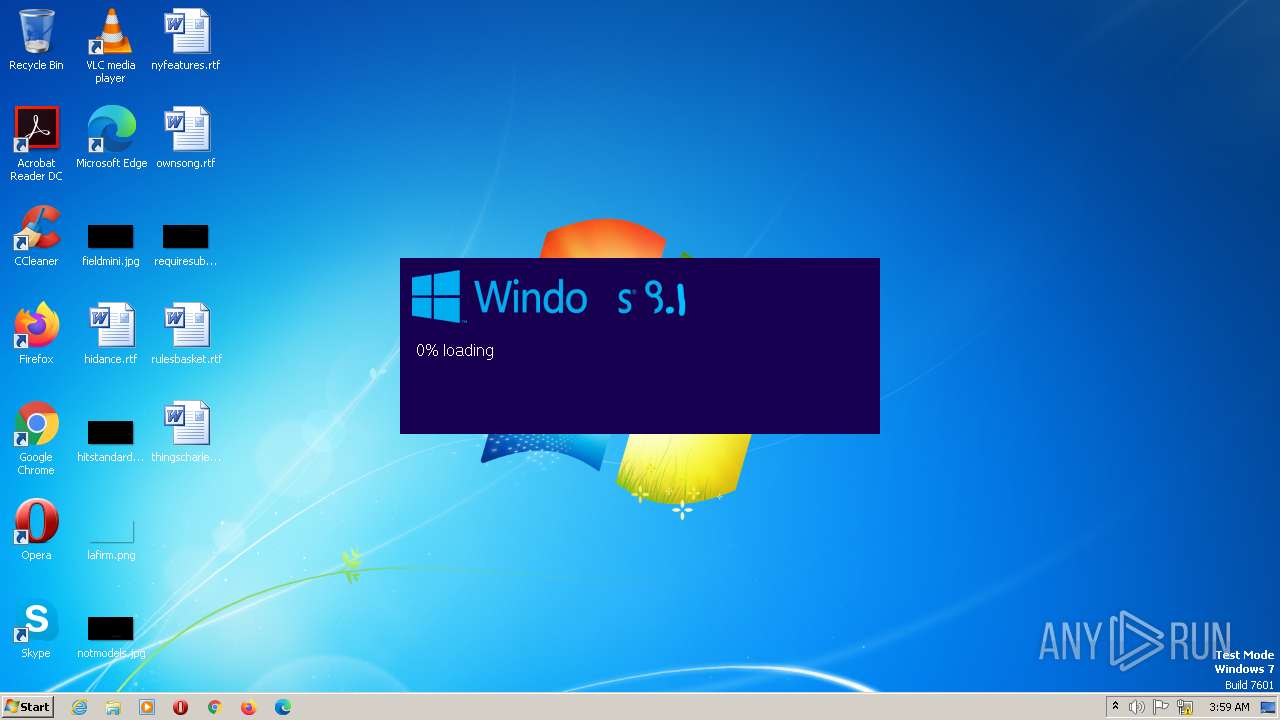
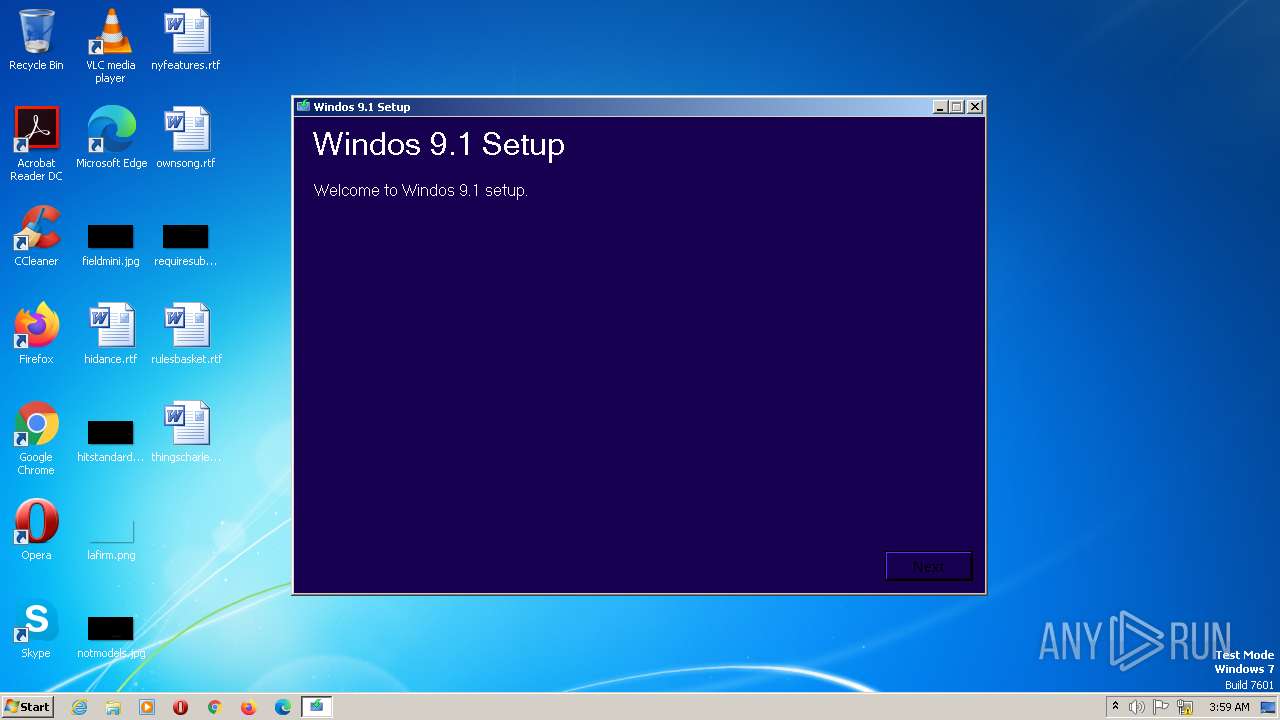
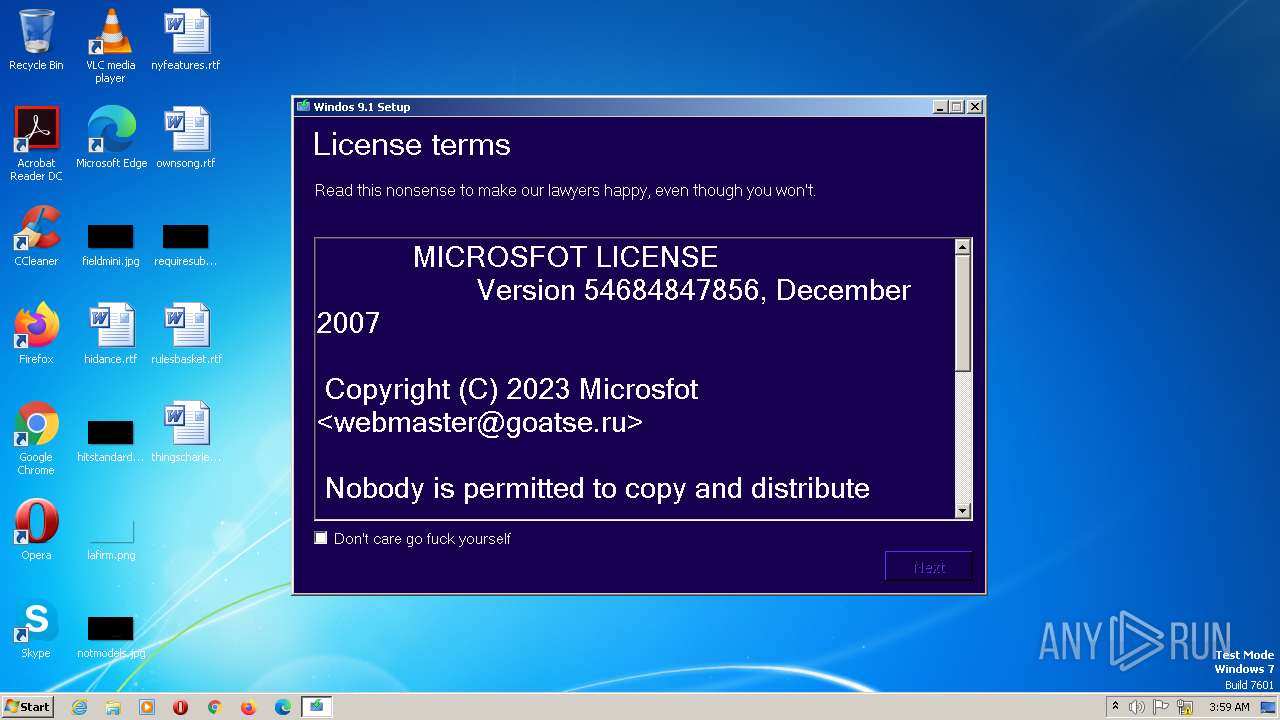
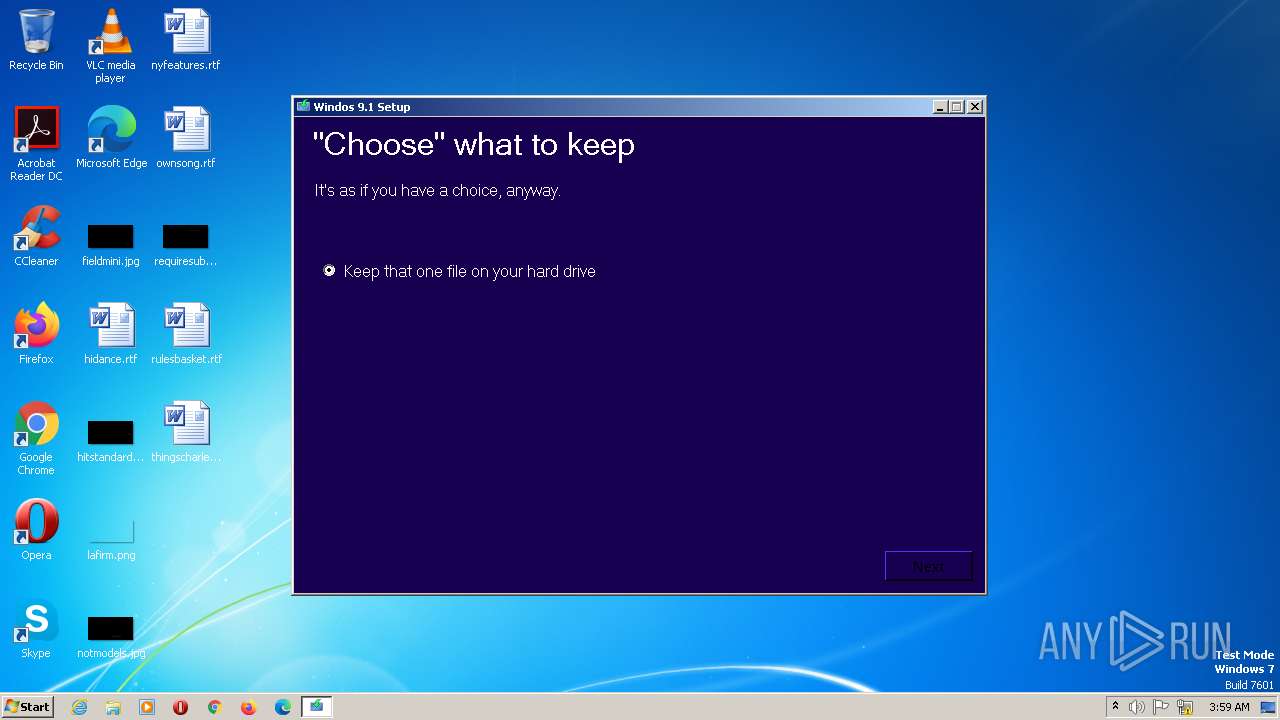
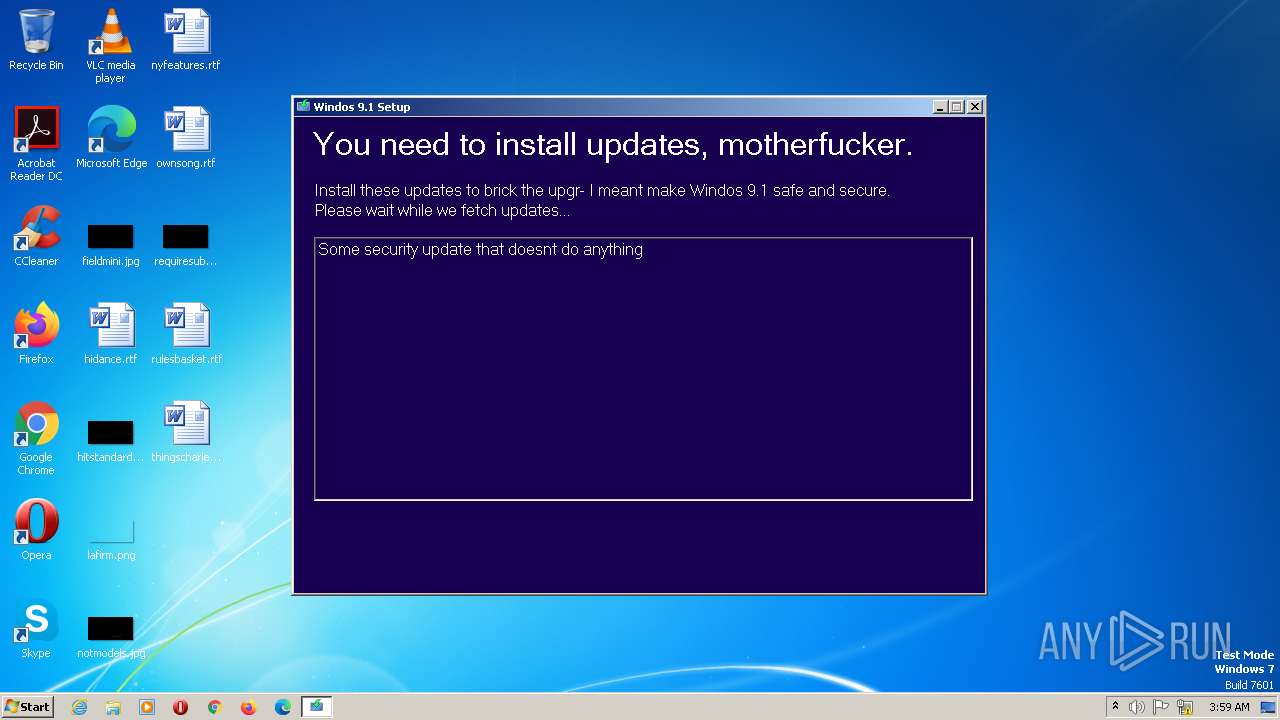
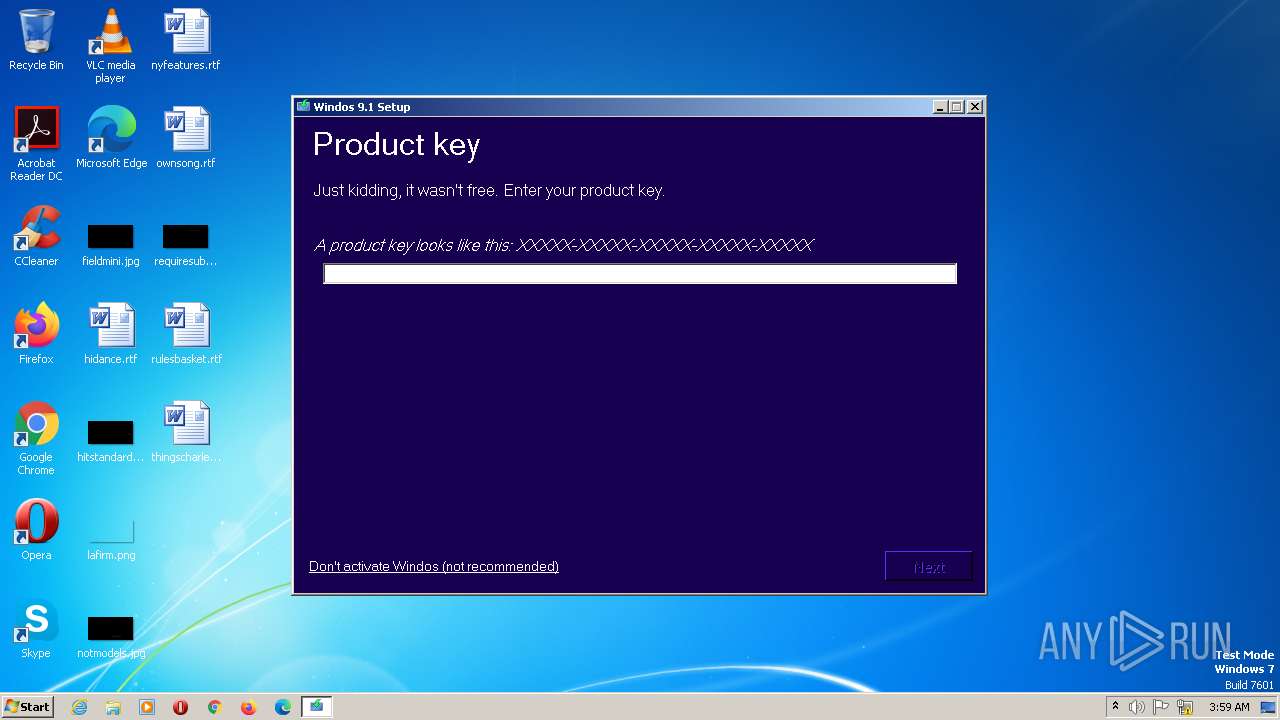
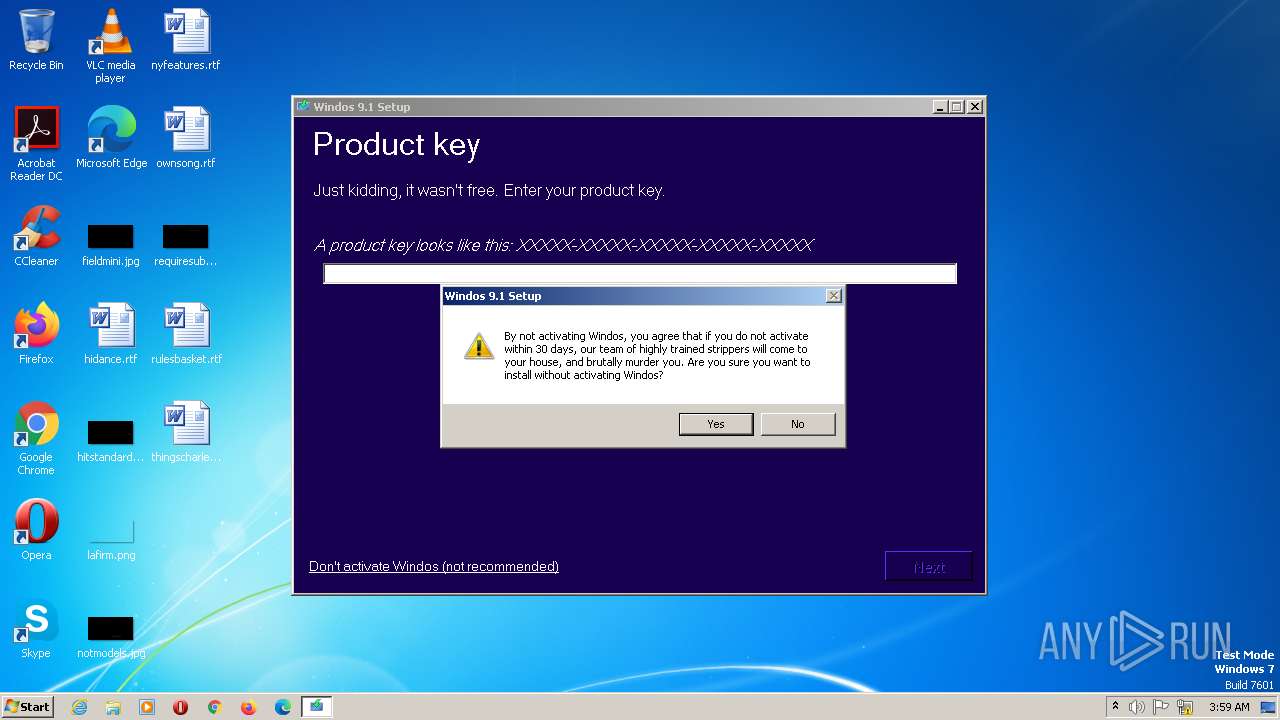
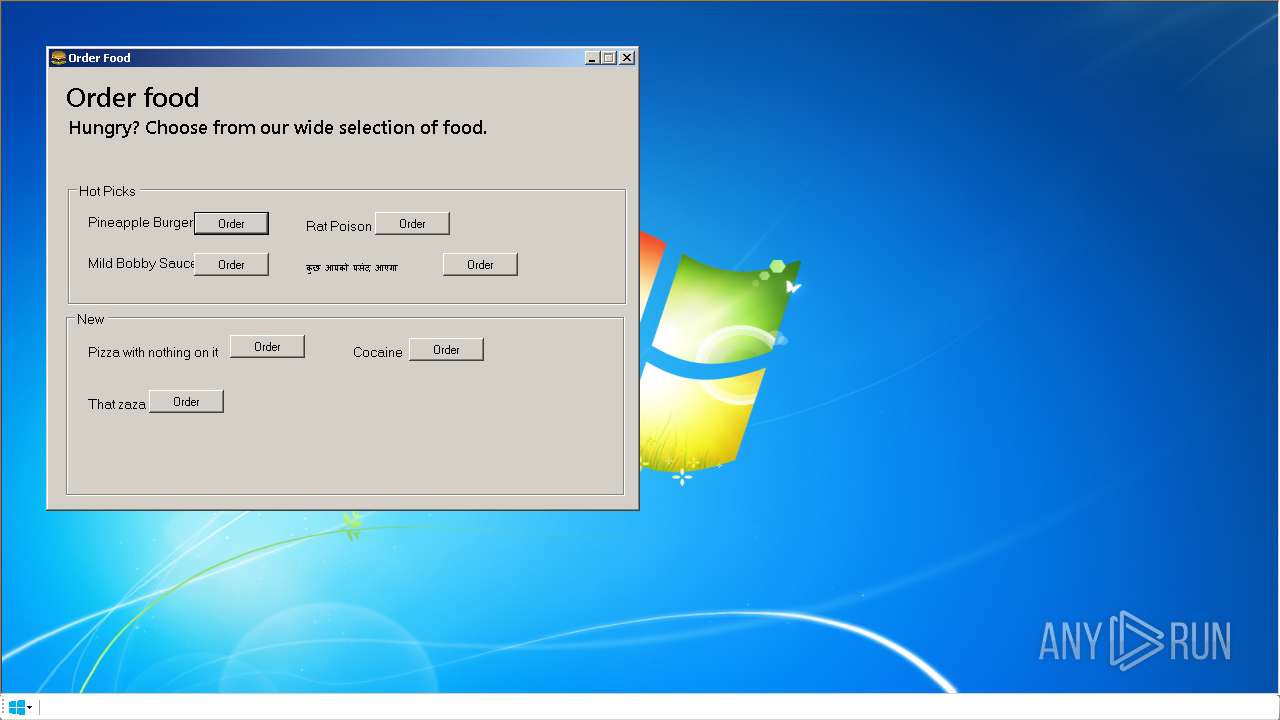
| Verdict: | Malicious activity |
| Analysis date: | July 15, 2023, 03:57:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (GUI) x86-64 Mono/.Net assembly, for MS Windows |
| MD5: | 5409001BFC4308A6CB8C09C4E1E32D1E |
| SHA1: | D47CC20E23E5B2BE27923A34FA85C02B3764C064 |
| SHA256: | 61D311D7A772E2BD670381F733FB9302B6202859ED5D47ACAEDF0BB58D5BC570 |
| SSDEEP: | 49152:QbVUGmpD+/xPfh6q/8kV6K9GCVcVoGiXPylb6rMy4w:QbVepD+/xPfh6yfVzF4b2My |
MALICIOUS
No malicious indicators.SUSPICIOUS
The process executes via Task Scheduler
- MicrosoftEdgeUpdate.exe (PID: 1520)
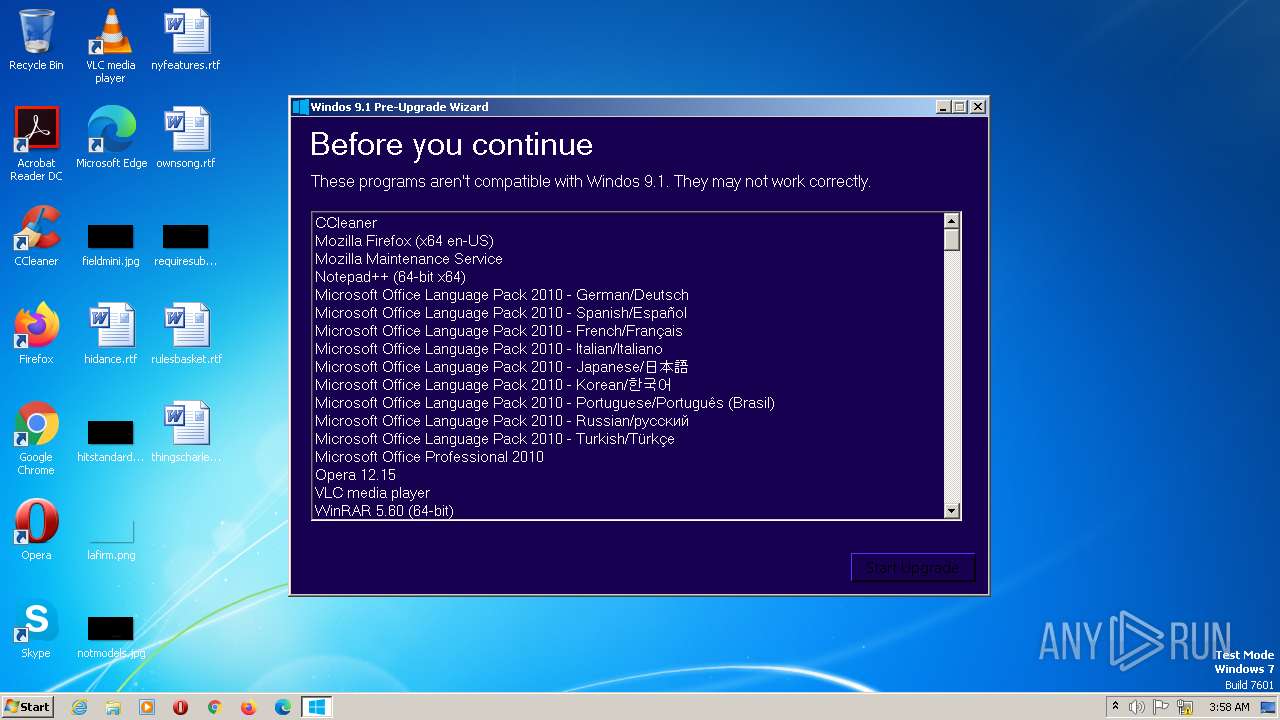
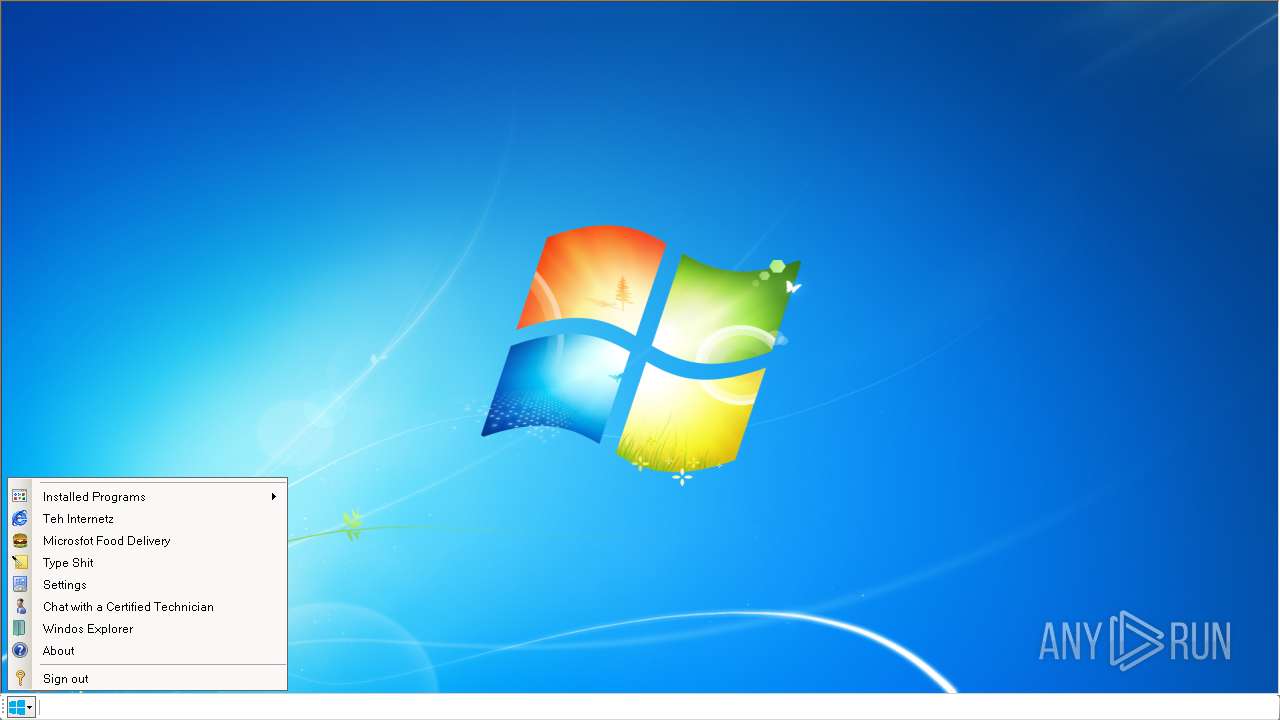
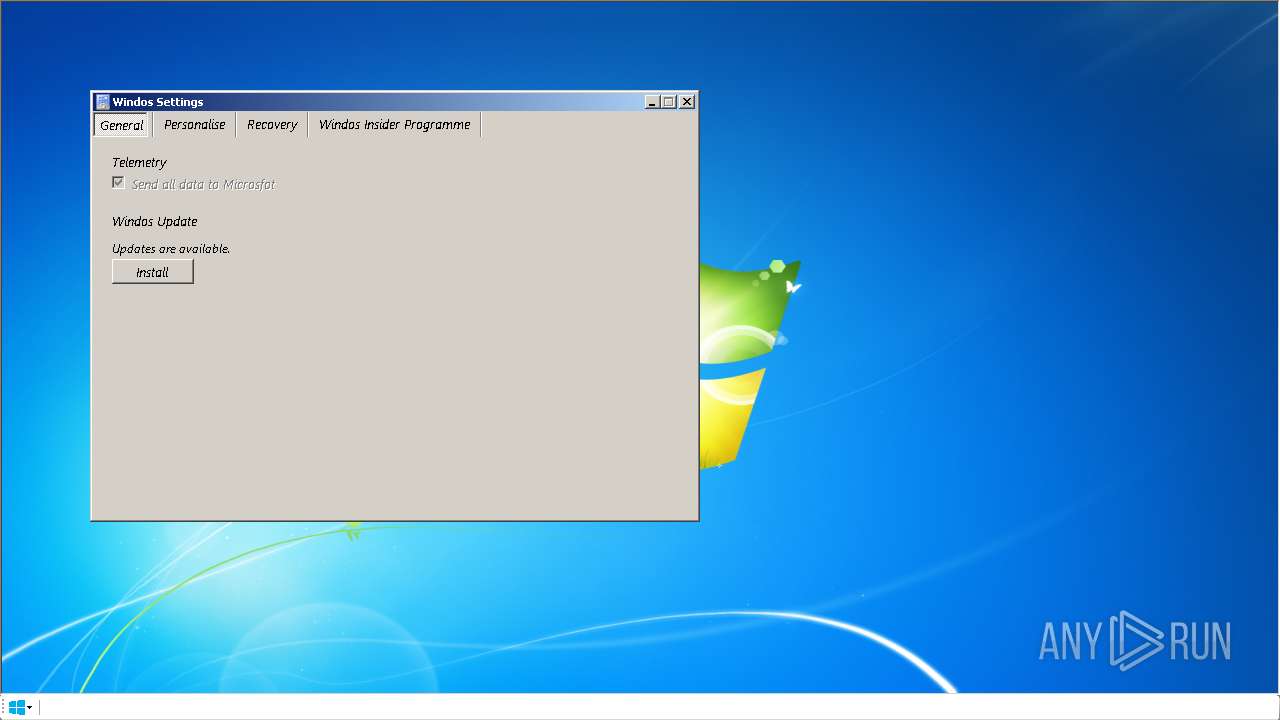
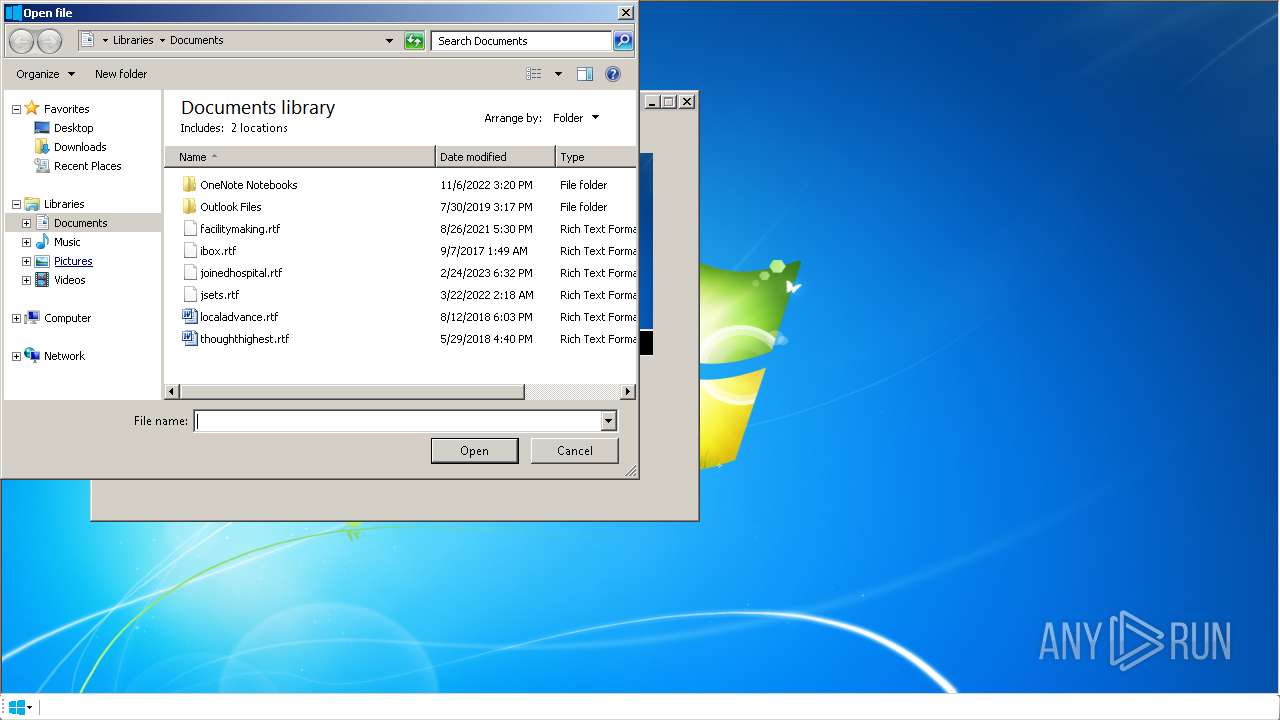
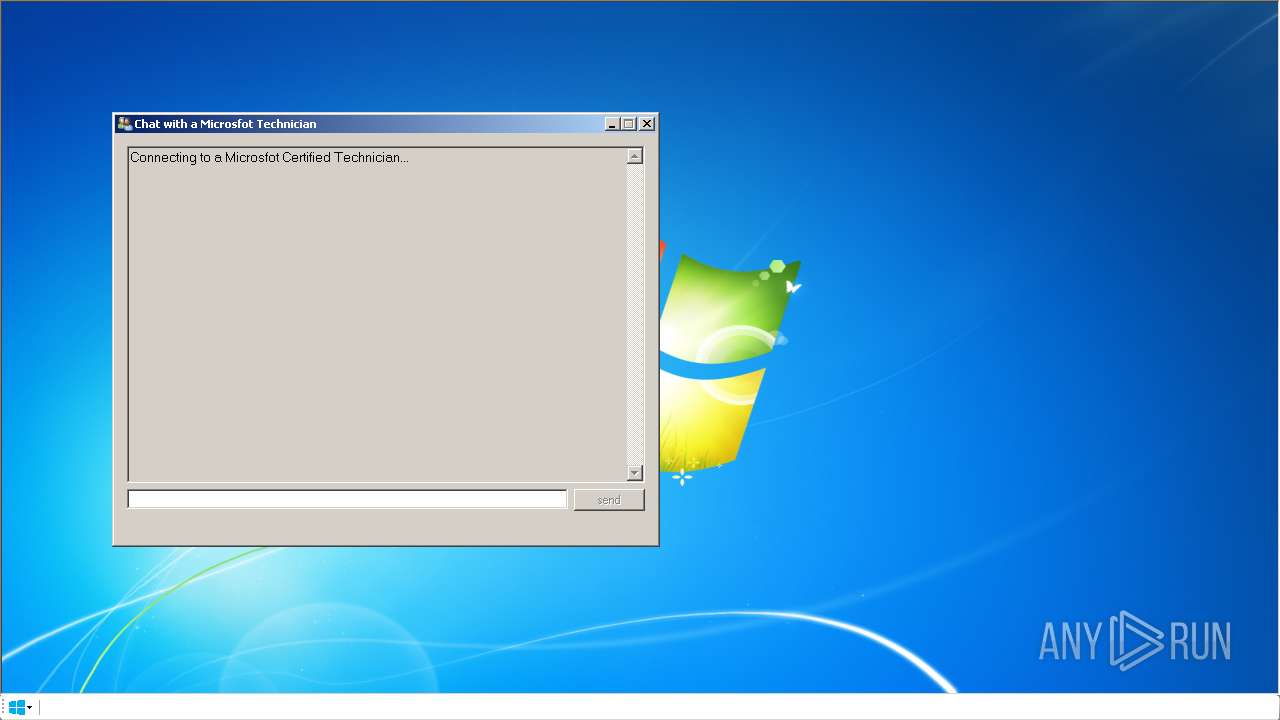
Searches for installed software
- Windos9.1Setup.exe (PID: 1628)
Executes as Windows Service
- MicrosoftEdgeUpdate.exe (PID: 784)
Application launched itself
- MicrosoftEdgeUpdate.exe (PID: 784)
Checks Windows Trust Settings
- MicrosoftEdgeUpdate.exe (PID: 1520)
Reads the Internet Settings
- Windos9.1Setup.exe (PID: 1628)
Reads Microsoft Outlook installation path
- Windos9.1Setup.exe (PID: 1628)
Reads Internet Explorer settings
- Windos9.1Setup.exe (PID: 1628)
INFO
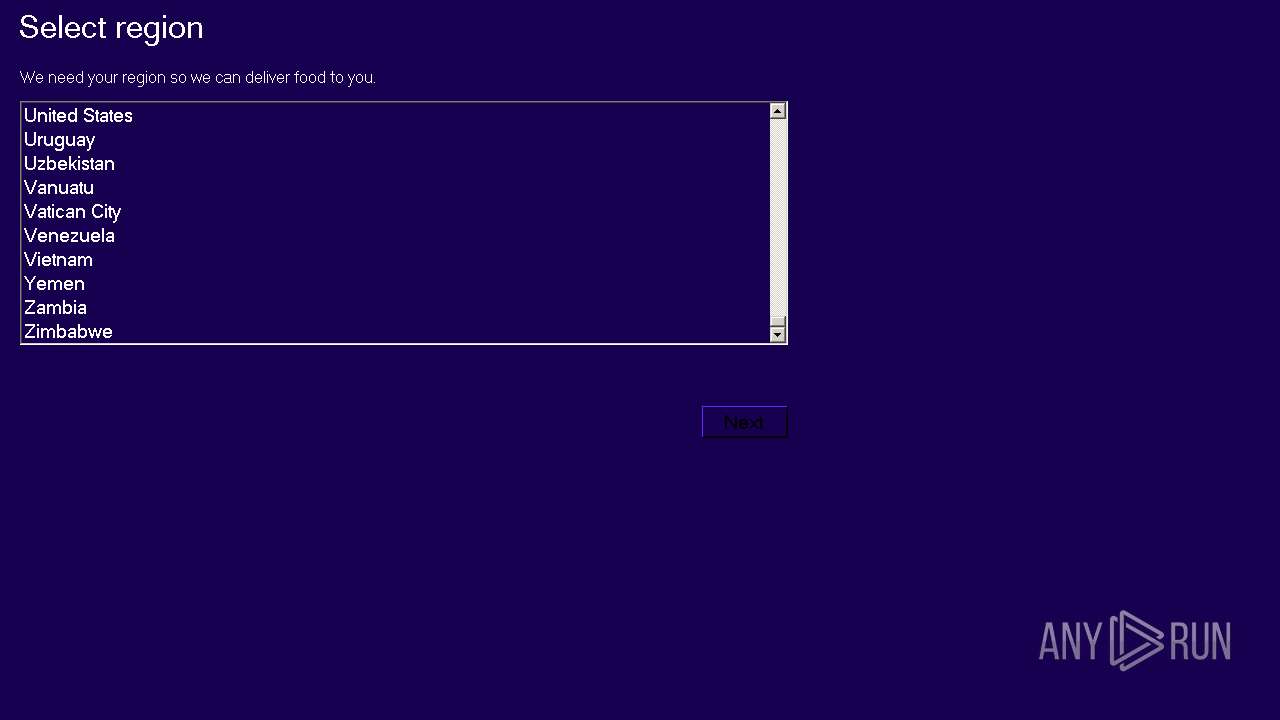
Checks supported languages
- MicrosoftEdgeUpdate.exe (PID: 1520)
- Windos9.1Setup.exe (PID: 1628)
- MicrosoftEdgeUpdate.exe (PID: 784)
- MicrosoftEdgeUpdate.exe (PID: 2960)
Reads the computer name
- Windos9.1Setup.exe (PID: 1628)
- MicrosoftEdgeUpdate.exe (PID: 1520)
- MicrosoftEdgeUpdate.exe (PID: 784)
- MicrosoftEdgeUpdate.exe (PID: 2960)
Reads the machine GUID from the registry
- Windos9.1Setup.exe (PID: 1628)
The process checks LSA protection
- Windos9.1Setup.exe (PID: 1628)
Reads Environment values
- MicrosoftEdgeUpdate.exe (PID: 2960)
- MicrosoftEdgeUpdate.exe (PID: 1520)
Checks proxy server information
- Windos9.1Setup.exe (PID: 1628)
Creates files or folders in the user directory
- Windos9.1Setup.exe (PID: 1628)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| AssemblyVersion: | 1.0.0.0 |
|---|---|
| ProductVersion: | 1.0.0.0 |
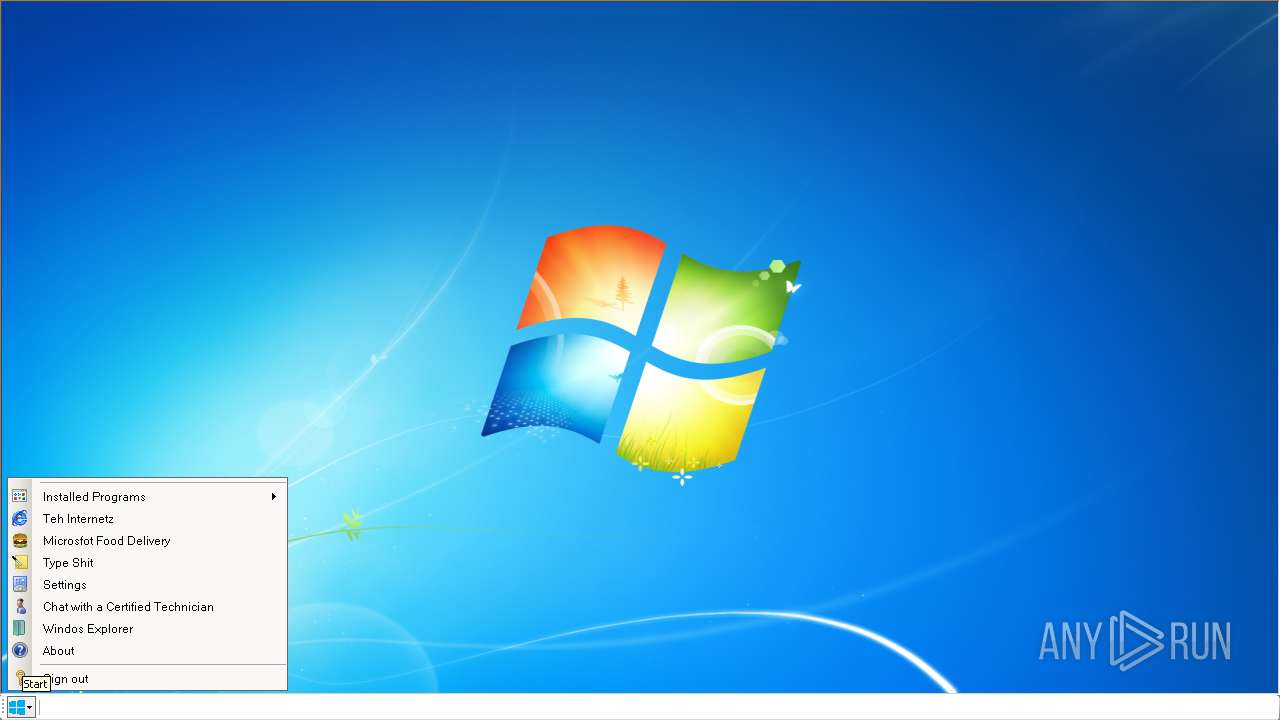
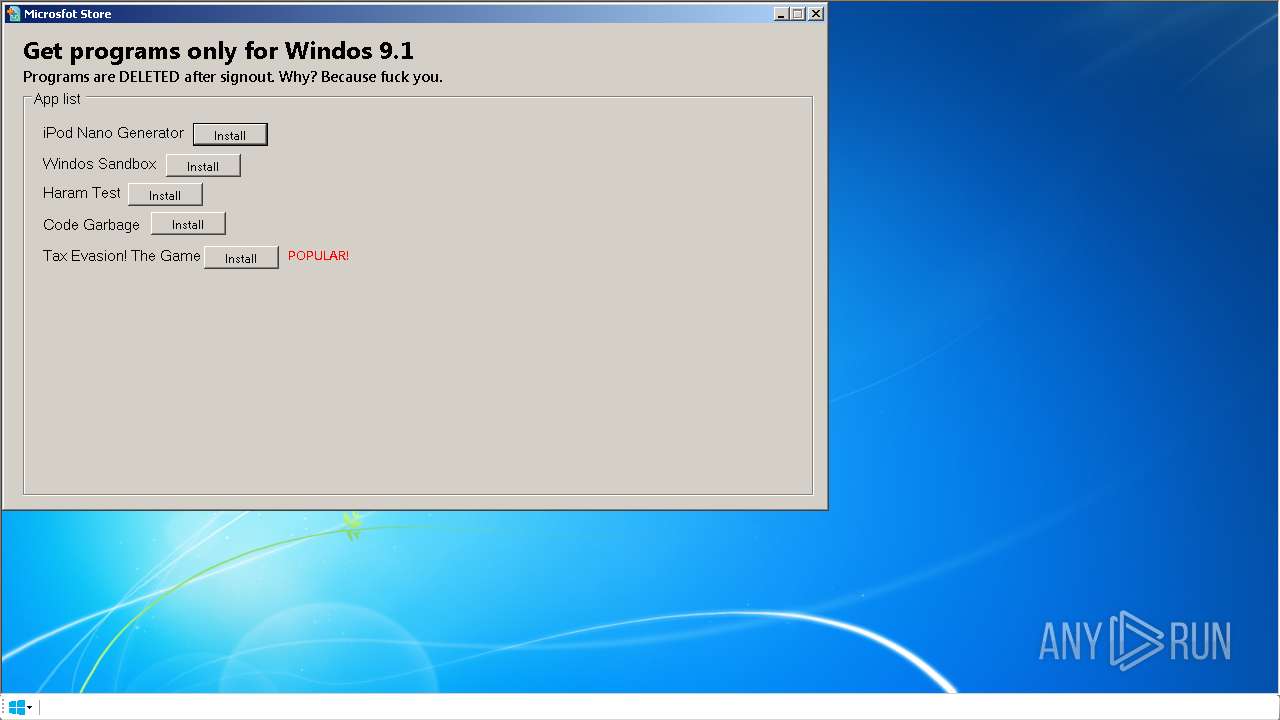
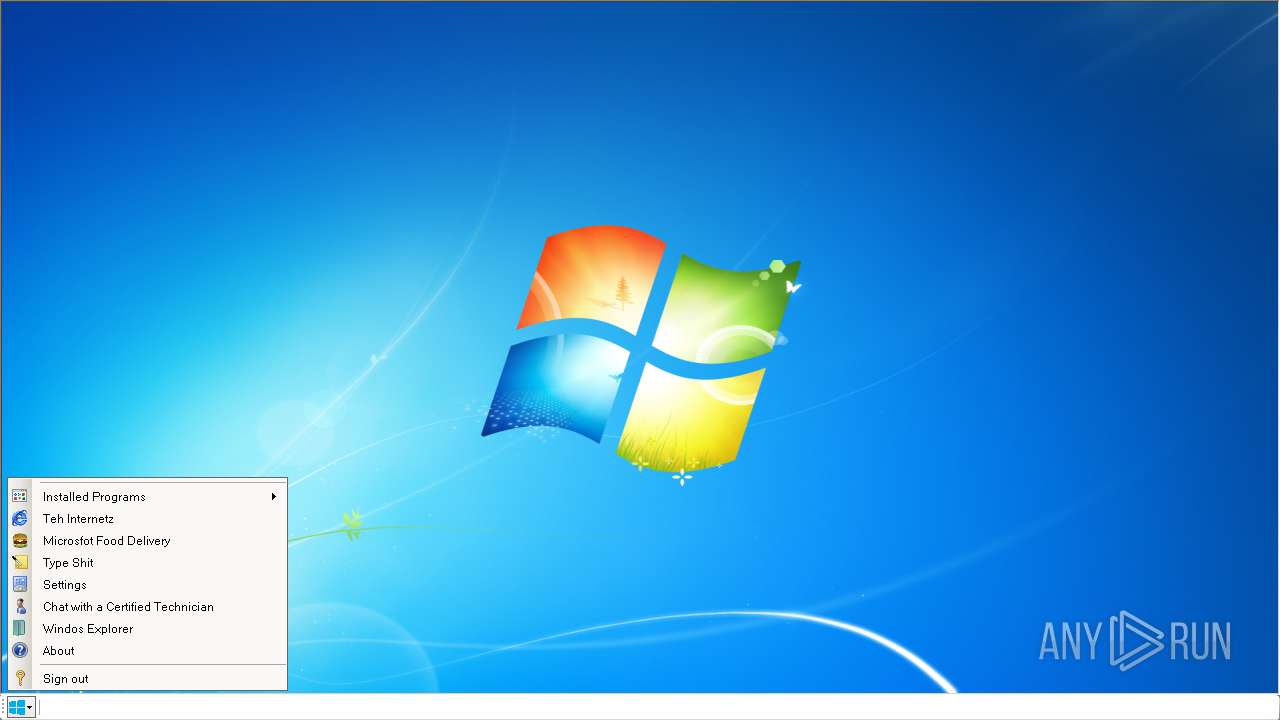
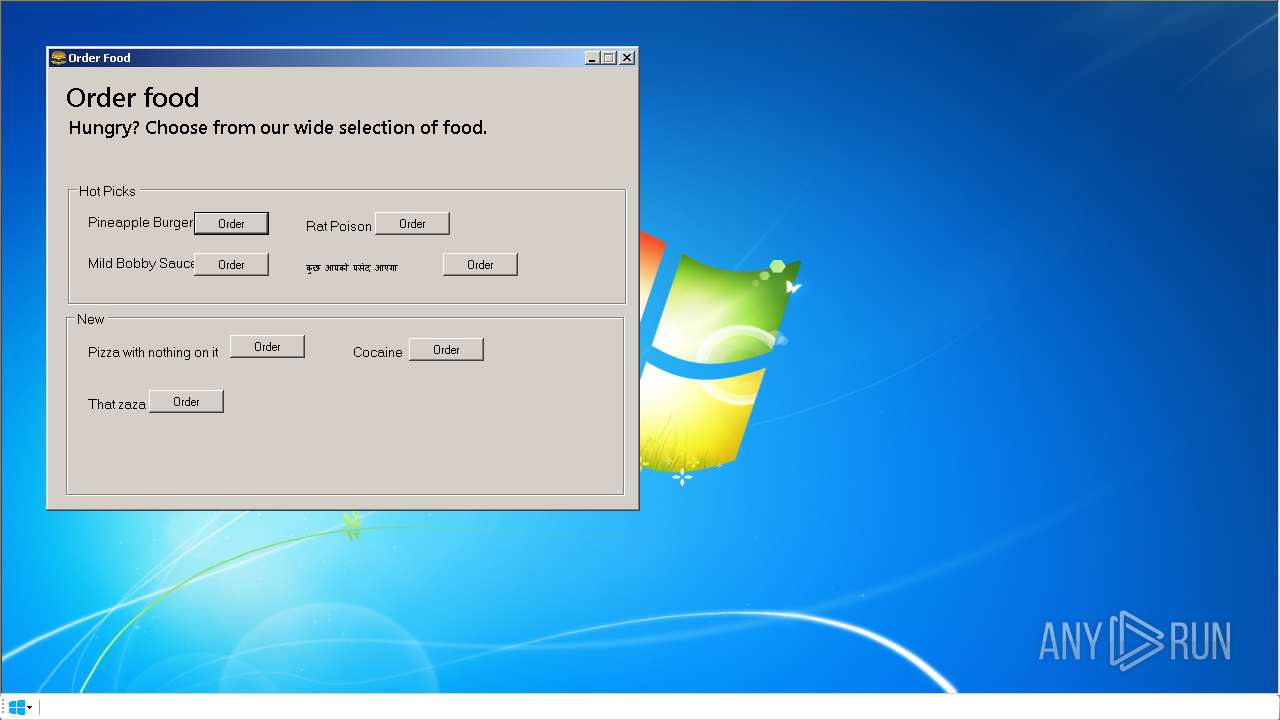
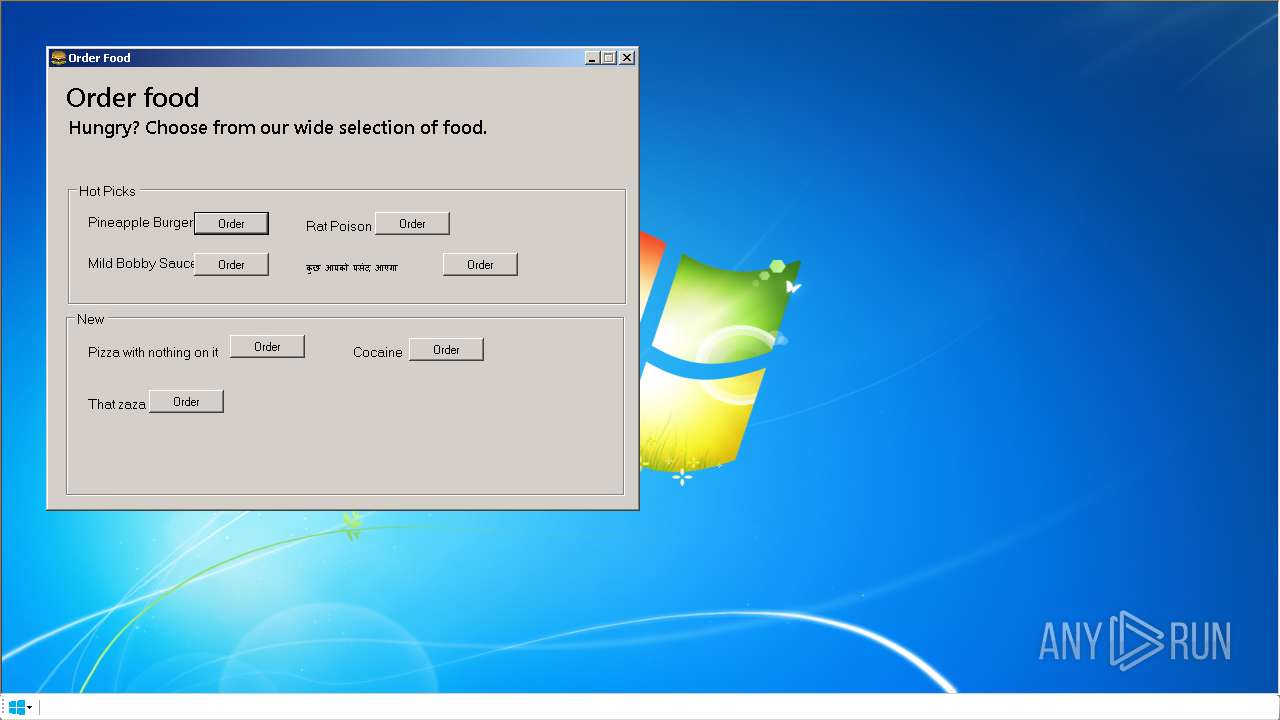
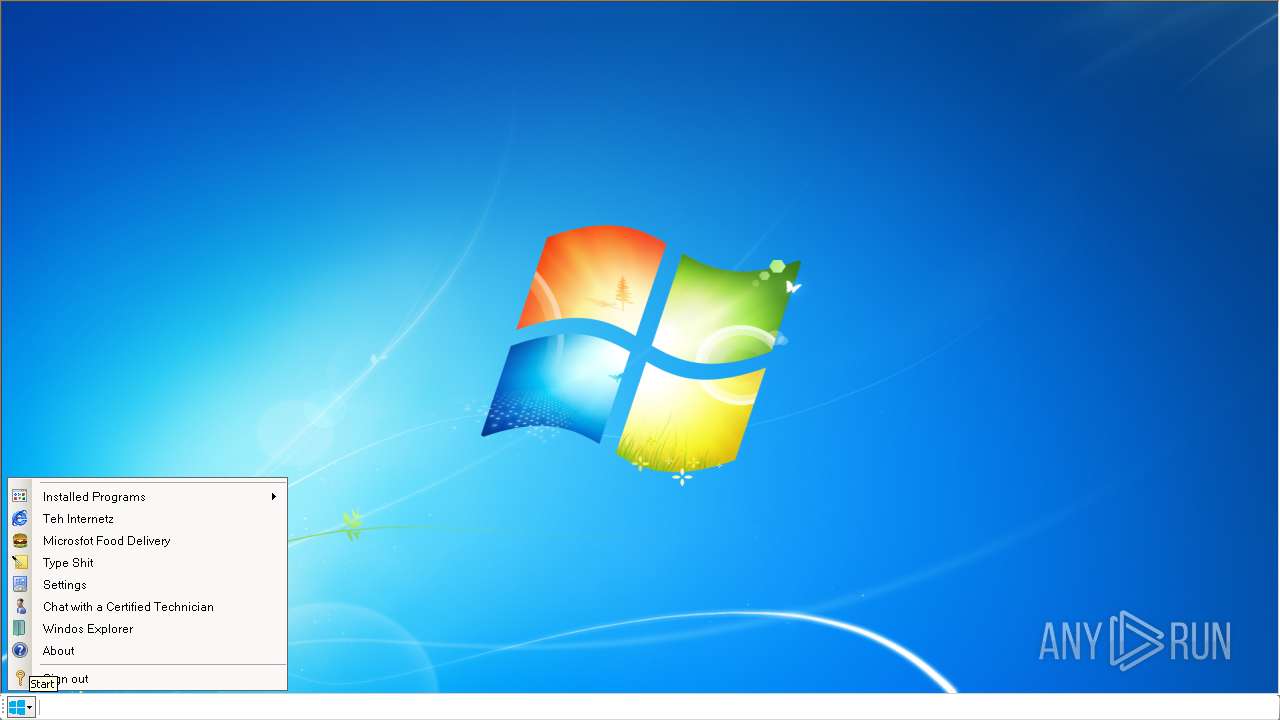
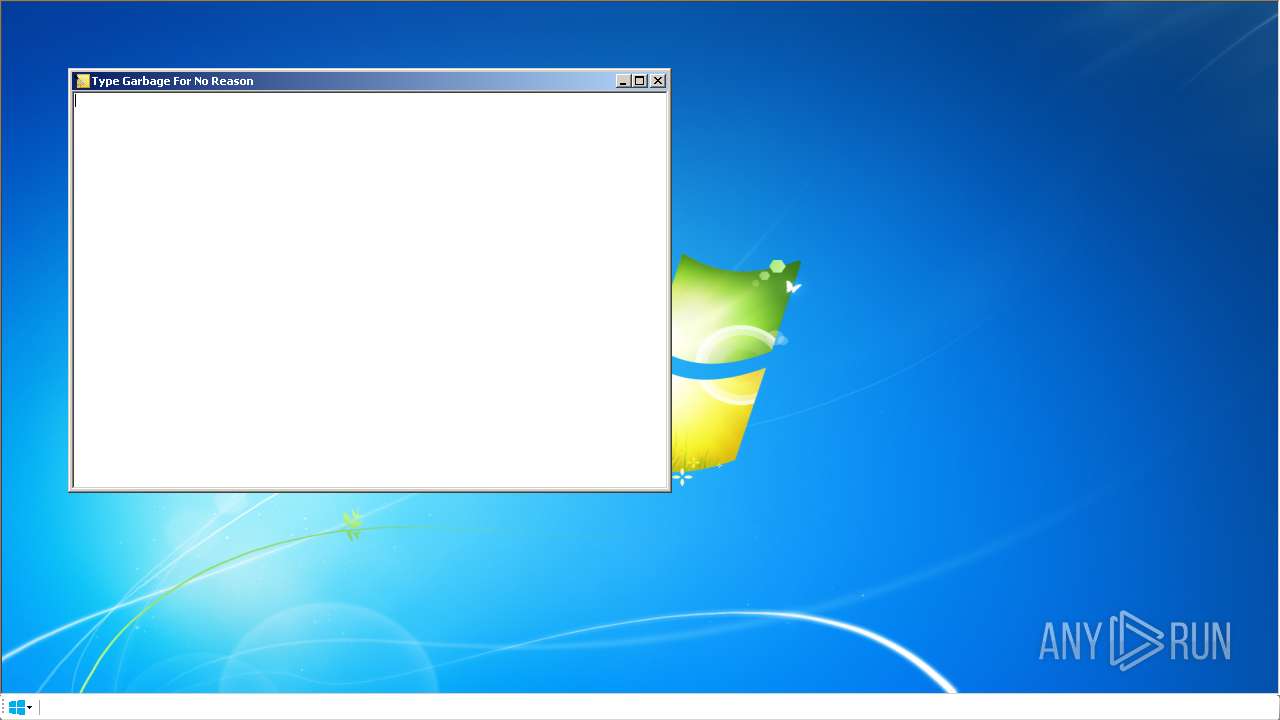
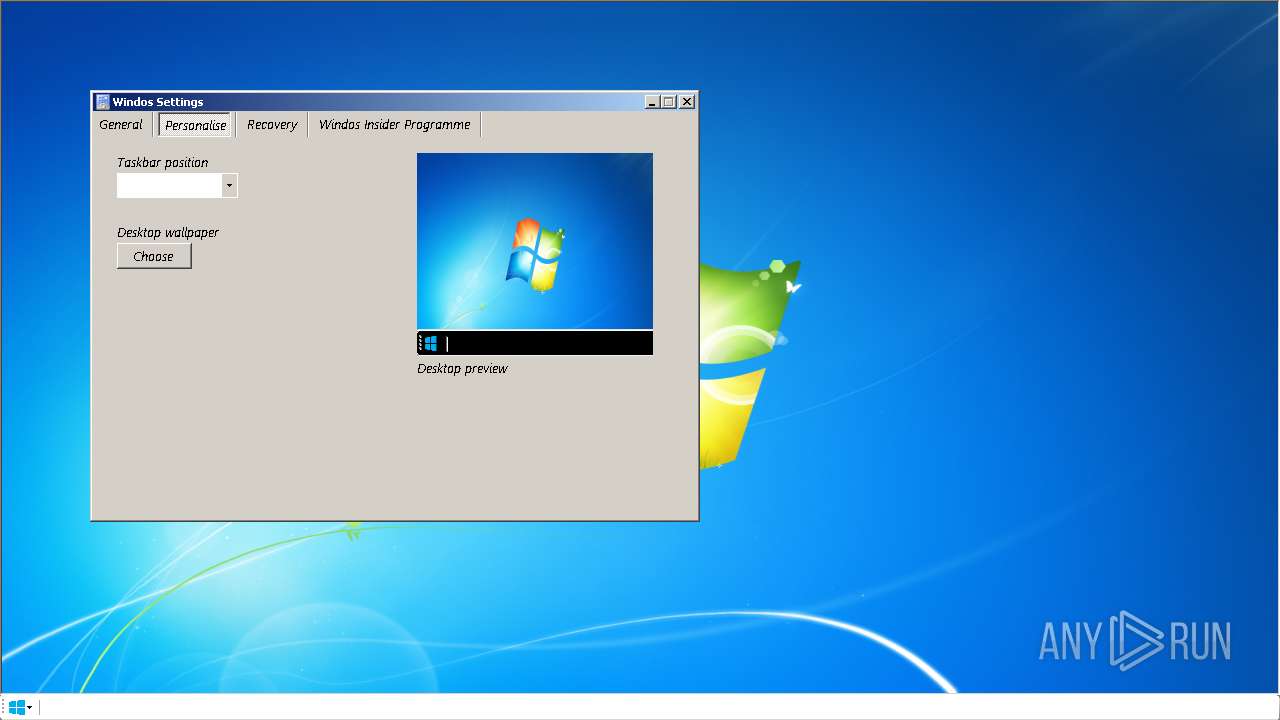
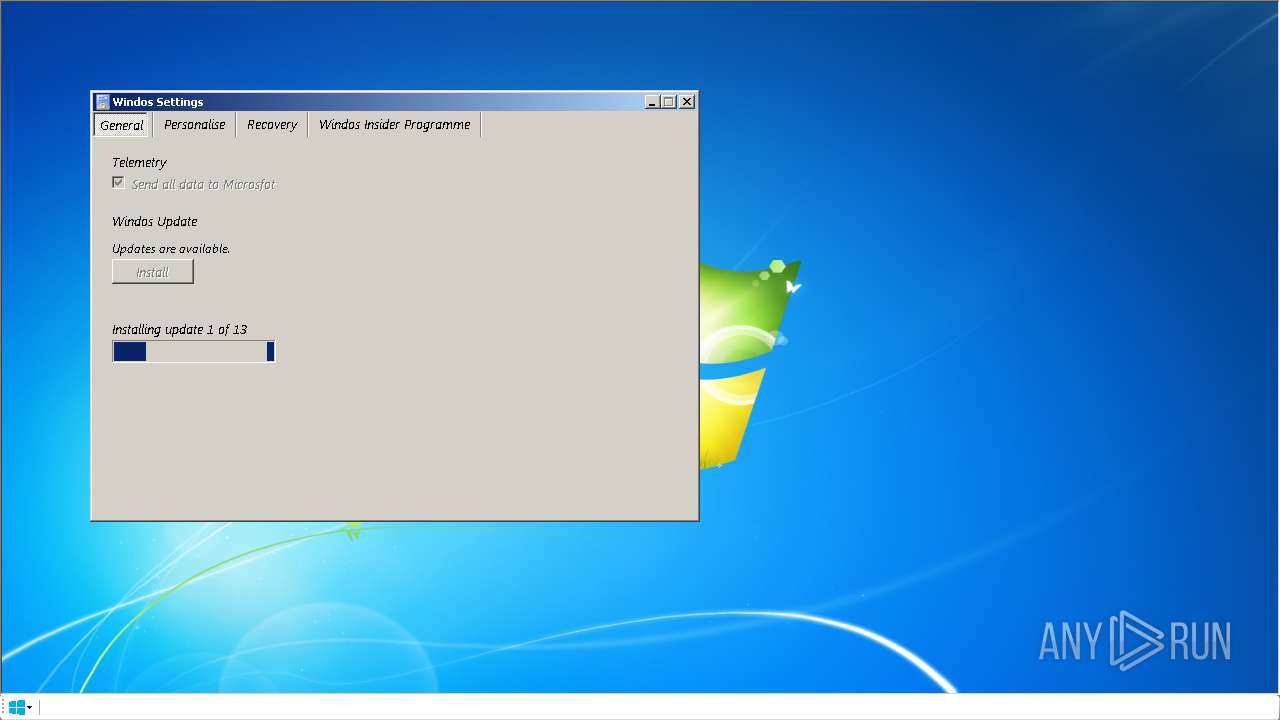
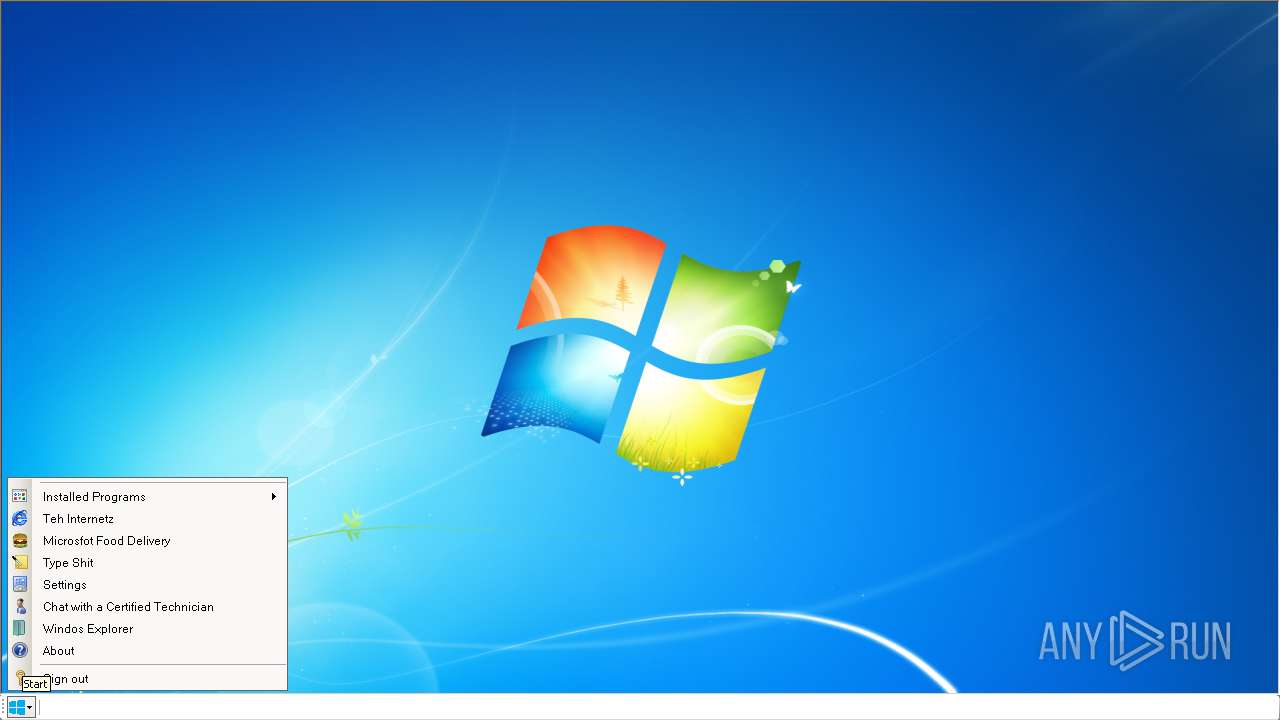
| ProductName: | Windos9Installer |
| OriginalFileName: | Windos9Setup.exe |
| LegalTrademarks: | - |
| LegalCopyright: | Copyright © 2023 |
| InternalName: | Windos9Setup.exe |
| FileVersion: | 1.0.0.0 |
| FileDescription: | Windos9Installer |
| CompanyName: | - |
| Comments: | - |
| CharacterSet: | Unicode |
| LanguageCode: | Neutral |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.0 |
| FileVersionNumber: | 1.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x0000 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 49664 |
| CodeSize: | 2549248 |
| LinkerVersion: | 48 |
| PEType: | PE32+ |
| ImageFileCharacteristics: | Executable, Large address aware |
| TimeStamp: | 2023:01:21 03:23:11+00:00 |
| MachineType: | AMD AMD64 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_AMD64 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 21-Jan-2023 03:23:11 |
| Debug artifacts: |
|
| Comments: | - |
| CompanyName: | - |
| FileDescription: | Windos9Installer |
| FileVersion: | 1.0.0.0 |
| InternalName: | Windos9Setup.exe |
| LegalCopyright: | Copyright © 2023 |
| LegalTrademarks: | - |
| OriginalFilename: | Windos9Setup.exe |
| ProductName: | Windos9Installer |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_AMD64 |
| Number of sections: | 2 |
| Time date stamp: | 21-Jan-2023 03:23:11 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00F0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x0026E4D4 | 0x0026E600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.33347 |
.rsrc | 0x00272000 | 0x0000C038 | 0x0000C200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.58779 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 2.88492 | 744 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 2.61243 | 488 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 2.60227 | 296 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 4.35159 | 3752 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 4.11143 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 3.49375 | 1736 | UNKNOWN | UNKNOWN | RT_ICON |
8 | 2.49145 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
9 | 7.91299 | 16975 | UNKNOWN | UNKNOWN | RT_ICON |
10 | 3.43385 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
Total processes
47
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 784 | "C:\Program Files (x86)\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe" /svc | C:\Program Files (x86)\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Edge Update Exit code: 0 Version: 1.3.175.29 Modules
| |||||||||||||||
| 1520 | "C:\Program Files (x86)\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe" /ua /installsource scheduler | C:\Program Files (x86)\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe | taskeng.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Edge Update Exit code: 0 Version: 1.3.175.29 Modules
| |||||||||||||||
| 1628 | "C:\Users\admin\AppData\Roaming\Windos9.1Setup.exe" | C:\Users\admin\AppData\Roaming\Windos9.1Setup.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Windos9Installer Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2960 | "C:\Program Files (x86)\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe" /ping PD94bWwgdmVyc2lvbj0iMS4wIiBlbmNvZGluZz0iVVRGLTgiPz48cmVxdWVzdCBwcm90b2NvbD0iMy4wIiB1cGRhdGVyPSJPbWFoYSIgdXBkYXRlcnZlcnNpb249IjEuMy4xNzcuMTEiIHNoZWxsX3ZlcnNpb249IjEuMy4xNzUuMjkiIGlzbWFjaGluZT0iMSIgc2Vzc2lvbmlkPSJ7OEIxNjQ4QUUtQThBQy00MzlELUI1NEYtQTYyOTM1NzkxM0NGfSIgdXNlcmlkPSJ7NThCRUVDNjYtM0Y0MS00QTQ4LUFGN0QtOTQ2NkZCRjIwNEI1fSIgaW5zdGFsbHNvdXJjZT0ic2NoZWR1bGVyIiByZXF1ZXN0aWQ9IntBMzA2MUNFNy1CQTE3LTQzQ0QtODU5Mi03RDAwNDZENzcxOEN9IiBkZWR1cD0iY3IiIGRvbWFpbmpvaW5lZD0iMCI-PGh3IGxvZ2ljYWxfY3B1cz0iNCIgcGh5c21lbW9yeT0iNCIgZGlza190eXBlPSIwIiBzc2U9IjEiIHNzZTI9IjEiIHNzZTM9IjEiIHNzc2UzPSIxIiBzc2U0MT0iMSIgc3NlNDI9IjEiIGF2eD0iMSIvPjxvcyBwbGF0Zm9ybT0id2luIiB2ZXJzaW9uPSI2LjEuNzYwMS4wIiBzcD0iU2VydmljZSBQYWNrIDEiIGFyY2g9Ing2NCIgcHJvZHVjdF90eXBlPSI0OCIgaXNfd2lwPSIwIiBpc19pbl9sb2NrZG93bl9tb2RlPSIwIi8-PG9lbSBwcm9kdWN0X21hbnVmYWN0dXJlcj0iREVMTCIgcHJvZHVjdF9uYW1lPSJERUxMIi8-PGV4cCBldGFnPSImcXVvdDtyNDUydDErazJUZ3EvSFh6anZGTkJSaG9wQldSOXNialh4cWVVREg5dVgwPSZxdW90OyIvPjxhcHAgYXBwaWQ9IntGM0M0RkUwMC1FRkQ1LTQwM0ItOTU2OS0zOThBMjBGMUJBNEF9IiB2ZXJzaW9uPSIxLjMuMTc3LjExIiBuZXh0dmVyc2lvbj0iIiBsYW5nPSIiIGJyYW5kPSJNMTAwIiBjbGllbnQ9IiIgZXhwZXJpbWVudHM9ImNvbnNlbnQ9ZmFsc2UiIGluc3RhbGxhZ2U9IjgiIGluc3RhbGxkYXRlPSI2MDI3IiBjb2hvcnQ9InJyZkAwLjkyIj48dXBkYXRlY2hlY2svPjxwaW5nIHI9IjkiIHJkPSI2MDMwIiBwaW5nX2ZyZXNobmVzcz0ie0M1MjQ5MkY0LUMyMTItNEVFMS1BN0QwLTNBREJBQTA0MTEwQX0iLz48L2FwcD48YXBwIGFwcGlkPSJ7NTZFQjE4RjgtQjAwOC00Q0JELUI2RDItOEM5N0ZFN0U5MDYyfSIgdmVyc2lvbj0iMTA5LjAuMTUxOC4xMTUiIG5leHR2ZXJzaW9uPSIiIGxhbmc9ImVuIiBicmFuZD0iTTEwMCIgY2xpZW50PSIiIGluc3RhbGxhZ2U9IjgiIGluc3RhbGxkYXRlPSI2MDI3IiBjb2hvcnQ9InJyZkAwLjc4IiBpc19waW5uZWRfc3lzdGVtPSJ0cnVlIiBsYXN0X2xhdW5jaF9jb3VudD0iMSIgbGFzdF9sYXVuY2hfdGltZT0iMTMzMzMxNTAxMjY5MjE4NzUwIiBmaXJzdF9mcmVfc2Vlbl90aW1lPSIxMzMzMzE1MDEyNjg4OTY0ODAiIGZpcnN0X2ZyZV9zZWVuX3ZlcnNpb249IjEwOS4wLjE1MTguMTE1Ij48dXBkYXRlY2hlY2svPjxwaW5nIGFjdGl2ZT0iMCIgcj0iOSIgcmQ9IjYwMzAiIHBpbmdfZnJlc2huZXNzPSJ7NUQ0Njg1RkEtREQwOS00OEMzLTkwQ0MtNTk1REIwRUYwOEU2fSIvPjwvYXBwPjwvcmVxdWVzdD4 | C:\Program Files (x86)\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe | MicrosoftEdgeUpdate.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Edge Update Exit code: 0 Version: 1.3.175.29 Modules
| |||||||||||||||
Total events
4 878
Read events
4 776
Write events
94
Delete events
8
Modification events
| (PID) Process: | (784) MicrosoftEdgeUpdate.exe | Key: | HKEY_USERS\S-1-5-21-3896776584-4254864009-862391680-1000_CLASSES\Local Settings\MuiCache\155\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (784) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\CurrentState |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (784) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\EdgeUpdate\ClientState\{F3C4FE00-EFD5-403B-9569-398A20F1BA4A}\CurrentState |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (784) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\EdgeUpdate\PersistedPings\{7E229AE7-318B-4AD0-B3CA-D27601C41163} |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (784) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\CurrentState |
| Operation: | write | Name: | StateValue |
Value: 3 | |||
| (PID) Process: | (784) MicrosoftEdgeUpdate.exe | Key: | HKEY_USERS\S-1-5-21-3896776584-4254864009-862391680-1000\Software\Microsoft\EdgeUpdate\proxy |
| Operation: | write | Name: | source |
Value: auto | |||
| (PID) Process: | (784) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\EdgeUpdate |
| Operation: | write | Name: | ConsecutiveCheckFailures |
Value: 0 | |||
| (PID) Process: | (784) MicrosoftEdgeUpdate.exe | Key: | HKEY_USERS\S-1-5-21-3896776584-4254864009-862391680-1000\Software\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 0 | |||
| (PID) Process: | (784) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | DayOfLastRollCall |
Value: 6030 | |||
| (PID) Process: | (784) MicrosoftEdgeUpdate.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Wow6432Node\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | ping_freshness |
Value: {5D4685FA-DD09-48C3-90CC-595DB0EF08E6} | |||
Executable files
0
Suspicious files
4
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1520 | MicrosoftEdgeUpdate.exe | C:\Windows\TEMP\af397ef28e484961ba48646a5d38cf54.db.ses | text | |
MD5:7CA3B8F36E0B6D89820319A21256B7BE | SHA256:FF5091BD27C3A3984DDED93B22FFD810FE6370764C684D47E2AF1AC61701310A | |||
| 1520 | MicrosoftEdgeUpdate.exe | C:\Windows\SysWOW64\config\systemprofile\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\80237EE4964FC9C409AAF55BF996A292_D46D6FA25B74360E1349F9015B5CCE53 | binary | |
MD5:48A5095EFADD4F999CC9230D05664054 | SHA256:E6F7D3F124FF60A052E854E514C90FD5BBD3C6030F7EE23A74F581937C0DED4D | |||
| 1628 | Windos9.1Setup.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\BDW1XBVN\robot[1].png | image | |
MD5:4C9ACF280B47CEF7DEF3FC91A34C7FFE | SHA256:5F9FC5B3FBDDF0E72C5C56CDCFC81C6E10C617D70B1B93FBE1E4679A8797BFF7 | |||
| 1628 | Windos9.1Setup.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\D2U1WPAC\googlelogo_color_150x54dp[1].png | image | |
MD5:9D73B3AA30BCE9D8F166DE5178AE4338 | SHA256:DBEF5E5530003B7233E944856C23D1437902A2D3568CDFD2BEAF2166E9CA9139 | |||
| 784 | MicrosoftEdgeUpdate.exe | C:\ProgramData\Microsoft\EdgeUpdate\Log\MicrosoftEdgeUpdate.log | text | |
MD5:3852318D197EF65760A3F05C43FEA6A7 | SHA256:0D64C2DA0CEF1E1EFB3B3FCA49464FA6FE8715B4714D450929EE43A653B8450A | |||
| 1520 | MicrosoftEdgeUpdate.exe | C:\Windows\SysWOW64\config\systemprofile\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:5745DFD24754FA2FFA4652092A0D90F0 | SHA256:D84ABC1A5B1269B6192674F4A2AFDA7688EAEC2A32461190F4772DAE9B8918C4 | |||
| 1520 | MicrosoftEdgeUpdate.exe | C:\Windows\SysWOW64\config\systemprofile\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\80237EE4964FC9C409AAF55BF996A292_D46D6FA25B74360E1349F9015B5CCE53 | binary | |
MD5:A38AE241ACC99176ECF16BA87F6E2A48 | SHA256:635A2527AA1DEA8519B491CE9161CFB08EB5F17D55DED3F671FEF79014AB92F3 | |||
| 1520 | MicrosoftEdgeUpdate.exe | C:\Windows\SysWOW64\config\systemprofile\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
11
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1520 | MicrosoftEdgeUpdate.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?fd3930e37479b515 | US | compressed | 4.70 Kb | whitelisted |
1520 | MicrosoftEdgeUpdate.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA177el9ggmWelJjG4vdGL0%3D | US | der | 471 b | whitelisted |
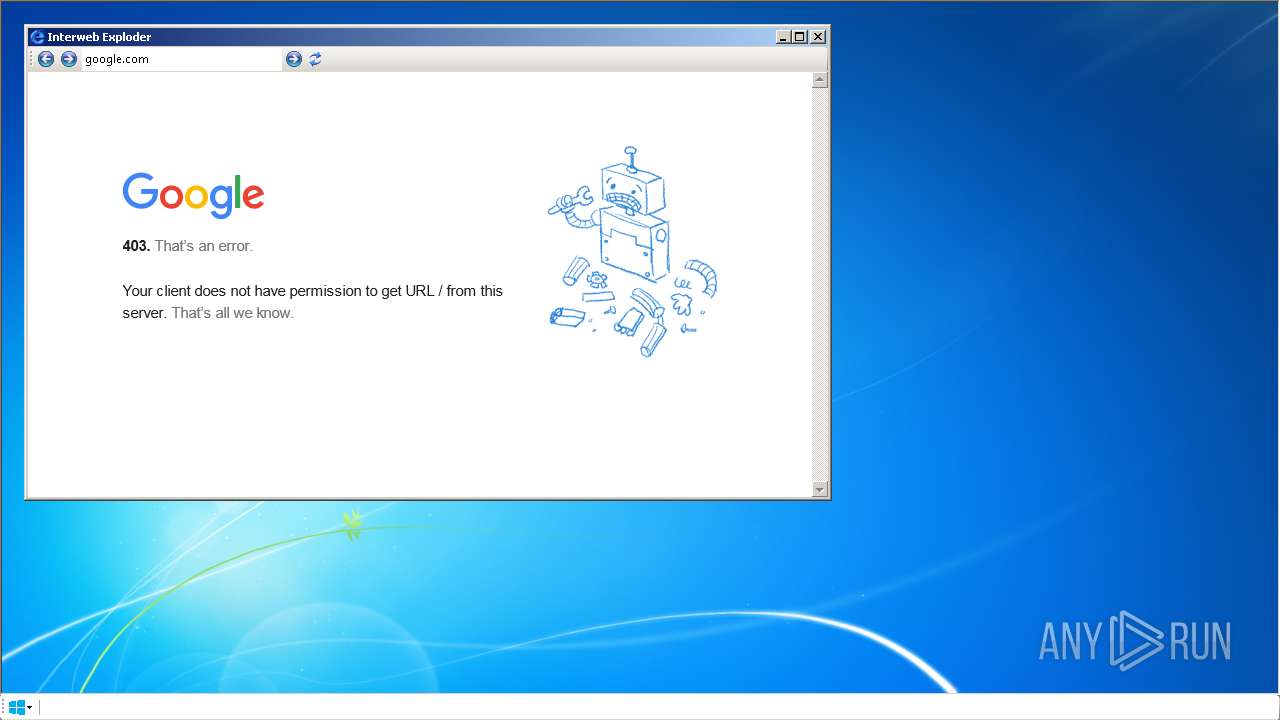
1628 | Windos9.1Setup.exe | GET | 200 | 142.250.186.164:80 | http://www.google.com/images/branding/googlelogo/1x/googlelogo_color_150x54dp.png | US | image | 3.10 Kb | malicious |
1628 | Windos9.1Setup.exe | GET | 200 | 142.250.186.164:80 | http://www.google.com/images/errors/robot.png | US | image | 6.18 Kb | malicious |
1628 | Windos9.1Setup.exe | GET | — | 142.250.186.164:80 | http://www.google.com/images/branding/googlelogo/1x/googlelogo_color_150x54dp.png | US | — | — | malicious |
1628 | Windos9.1Setup.exe | GET | 403 | 142.250.186.78:80 | http://google.com/ | US | html | 1.54 Kb | malicious |
1628 | Windos9.1Setup.exe | GET | — | 142.250.186.164:80 | http://www.google.com/images/errors/robot.png | US | — | — | malicious |
1628 | Windos9.1Setup.exe | GET | 403 | 142.250.186.78:80 | http://google.com/ | US | html | 1.54 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
784 | MicrosoftEdgeUpdate.exe | 23.102.129.60:443 | msedge.api.cdp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
2960 | MicrosoftEdgeUpdate.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1520 | MicrosoftEdgeUpdate.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1628 | Windos9.1Setup.exe | 142.250.186.78:80 | google.com | GOOGLE | US | whitelisted |
1628 | Windos9.1Setup.exe | 142.250.186.164:80 | www.google.com | GOOGLE | US | whitelisted |
1520 | MicrosoftEdgeUpdate.exe | 13.89.179.9:443 | self.events.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | suspicious |
1520 | MicrosoftEdgeUpdate.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
msedge.api.cdp.microsoft.com |
| whitelisted |
config.edge.skype.com |
| malicious |
self.events.data.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
google.com |
| malicious |
www.google.com |
| malicious |